ITADSecurity
@ITADSecurity
Founded in 2011, ITADSecurity develops enterprise-wide data-bearing device discovery, ITAD process management and continuous monitoring solutions.
4/5 #BYOD devices contain apps that have been hacked. #ITADSecurity #security intel finds these vulnerabilities - itsecuritynews.info/2013/12/11/78-…
@ITADSecurity is bringing #big data intelligence and #predictive #analytics to #BYOD - mapcite.com/posts/2014/feb…
Most health IT execs unprepared for a data breach - FierceHealthIT ow.ly/ti4ZG
EU Vice-president proposes fines up to 5% of global revenue for user data breach (!) It would be THE Net revolution! bit.ly/1eLUzZP
Data Mining is about explaining the past and predicting the future. How can #analytics help you? dld.bz/aqgf8 #strategy
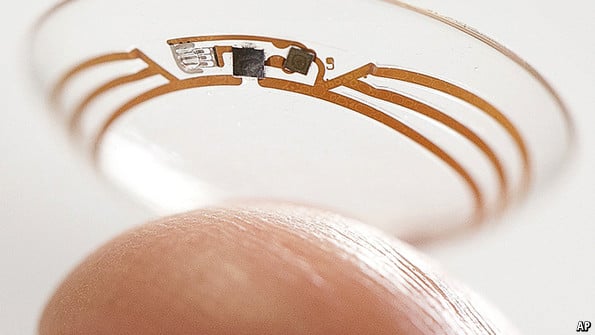
M-health: Health and appiness | The Economist |Huge growth in Mobile App/dev w/ #BigData for Healthcare econ.st/1ffe8ex
#Endpoint inventory + #encryption = #Security intelligence. Do yours add up as expected? Coke's didn't. #ITADSecurity has answers. #SCCM
Unbelievable > Coca-Cola data breach as employee 'borrows' 55 laptops over 6 years, up to 74K accounts exposed. lnkd.in/dz6wfDu
Throwing together an #IT disposal plan at the last minute will put your firm at a higher risk of a data breach. bit.ly/1clpmPb
@ITADSecurity is the ONLY company providing #SIEM for #Mobile Endpoints and #BYOD devices. No new tools, software or agents required. #SCCM
Every org is faced with relying on legacy #ITAM & #IT security tools vs. invest heavily in new ones. @ITADSecurity.com can help #BYOD #MDM
Please check out our latest blog - The #BYOD Red Zone - itadsecurity.com/blog/business-… #MDM, #SCCM, #ActiveSync, #encryption, #Microsoft
#Gartner estimates 35% orgs have installed #MDM product. Either way - consider @ITADSecurity to ID those #PCs & #mobile devices in Red Zone
Reset the X days of no paper-based EHR exposures. healthcareinfosecurity.com/medicaid-card-… My analysis of the OCR data: securityintelligence.com/healthcare-dat…
#ITADSecurity focus is #BYOD Red Zone? Don't let huge majority of devices functioning normally allow those that aren't evade detection!
Signal-to-noise ratio (SNR)compares the level of a desired signal to the background noise. #Risk elevates when signs from #BYOD are missed.
#PC World - 2013 was the year of the #data breach. Secure the #endpoints with @ITADSecurity in 2014. pcworld.com/article/208296… #MDM
pcworld.com
Why 2013 was the year of the personal data breach
We look back at a year when cybersecurity hit very, very close to home.
United States الاتجاهات
- 1. Eagles 126K posts
- 2. Ben Johnson 19.5K posts
- 3. Jalen 27.5K posts
- 4. Caleb 47.7K posts
- 5. Philly 26.8K posts
- 6. #BearDown 2,396 posts
- 7. Patullo 12.6K posts
- 8. AJ Brown 5,829 posts
- 9. Sirianni 7,738 posts
- 10. Lane 55.6K posts
- 11. Black Friday 528K posts
- 12. Georgia Tech 5,002 posts
- 13. #GoDawgs 5,455 posts
- 14. Swift 57.3K posts
- 15. Howie 2,690 posts
- 16. Saquon 8,289 posts
- 17. NFC East 2,001 posts
- 18. GOOD BETTER BEST 5,189 posts
- 19. Gunner 5,455 posts
- 20. #CHIvsPHI 2,499 posts
Something went wrong.
Something went wrong.