Mark
@IntNull0
Dad, InfoSec nerd, US Army veteran
Bạn có thể thích
New post: focusing on the key biggest Microsoft 365 security considerations. READ: campbell.scot/microsoft-365-… When we talk about Microsoft 365 security, we are talking about two things: (a) securing Microsoft 365 the platform, (b) using Microsoft 365 security tooling.
Here's my top 20 weaknesses in M365 based on experience consulting. I've seen most of these everywhere in varying mixtures. Public groups has been a problem in all but one org I've worked with. 1. Public Groups expose sensitive data 2. Upload from unmanaged devices 3. Download…
New episode is out! - youtu.be/1VzT7CuWp3Y In episode 148, @Rhynorater gives us a crash course on Model Context Protocol. This episode is a MUST-watch!
youtube.com
YouTube
MCP Hacking Guide (Ep. 148)
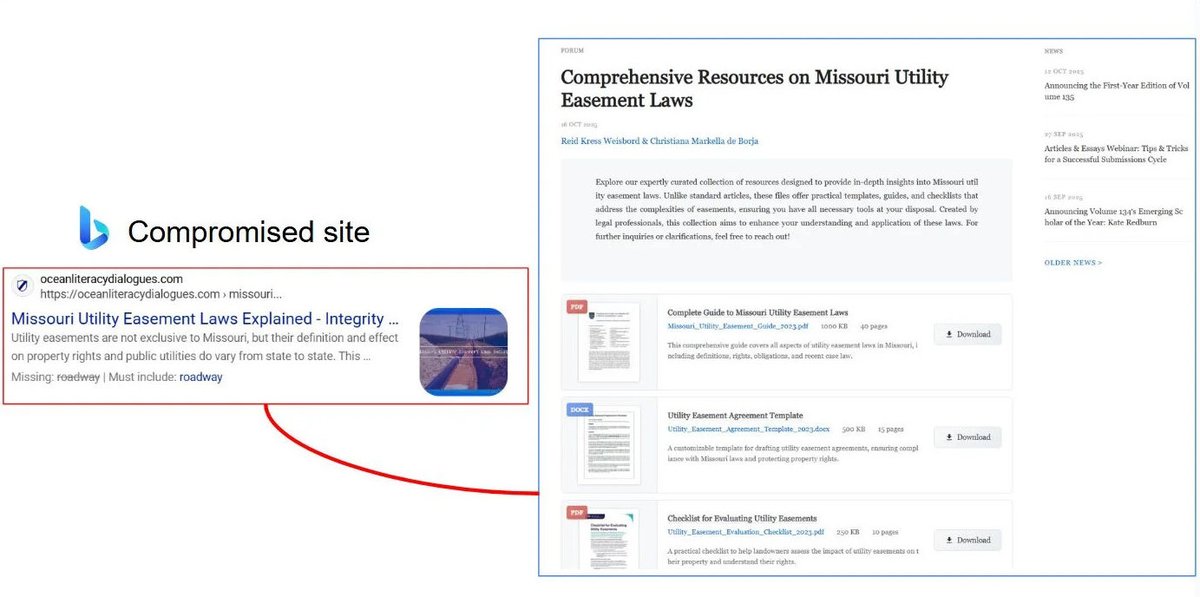
Huntress reports that Gootloader is back, using custom WOFF2 fonts with glyph substitution to obfuscate filenames; exploiting WordPress comment endpoints for XOR-encrypted ZIPs; and shifting persistence to the Startup folder. huntress.com/blog/gootloade…
Microsoft confirmed a bug in the October 2025 Update is causing BitLocker recovery on reboot. This issue affects Windows 11 25H2, 24H2 and even Windows 10. Mostly, business users are affected. If you don't have the BitLocker recovery key (always accessible via Microsoft…

If you haven't seen it, go check out the SecOps guide for Entra. It covers the operationalization of security across users, devices, applications and more. If securing Entra is part of your job description, this should be bookmarked. learn.microsoft.com/en-us/entra/ar…
📢If you missed my talk about Azure Attack Path at the @identitysummit, I just updated my blog with content created for the conference. New analytic rules, demo attack script and the slides are not available. #Azure #Security #Defend #Attack #Sentinel cloudbrothers.info/en/azure-attac…
cloudbrothers.info
Azure Attack Paths
Creating and maintaining a secure environment is hard. And with every technology or product added to your environment it gets more complicated. Microsoft Azure as a cloud environment is no exception...
Researchers from Microsoft's DART team revealed SesameOp, a novel backdoor utilizing the OpenAI Assistants API for command and control, enabling stealthy communication and long-term persistence for espionage activities. #CyberSecurity #Malware microsoft.com/en-us/security…
Don’t assume #BitLocker keys are escrowed to Entra ID/Intune by default. Run a regular scan with your script to ensure all devices have valid recovery keys, especially after imaging or Autopilot enrollment. Read more: systemcenterdudes.com/intune-bitlock… #MSIntune #EntraID #SCCM

How many of you have Sensitive Information Types that are coming back with too many false positives? Don't lie. 75% of you dont know what I'm talking about and the other 25% either dont know or know but havent addressed it yet :p Here's what you can do: Create a SharePoint…
AdminSDHolder: the AD security feature everyone thinks they understand but probably don't. 😬 @JimSycurity went to the source code to debunk decades of misconceptions — including ones in Microsoft's own docs. Read more ⤵️ ghst.ly/3Lpmjzv
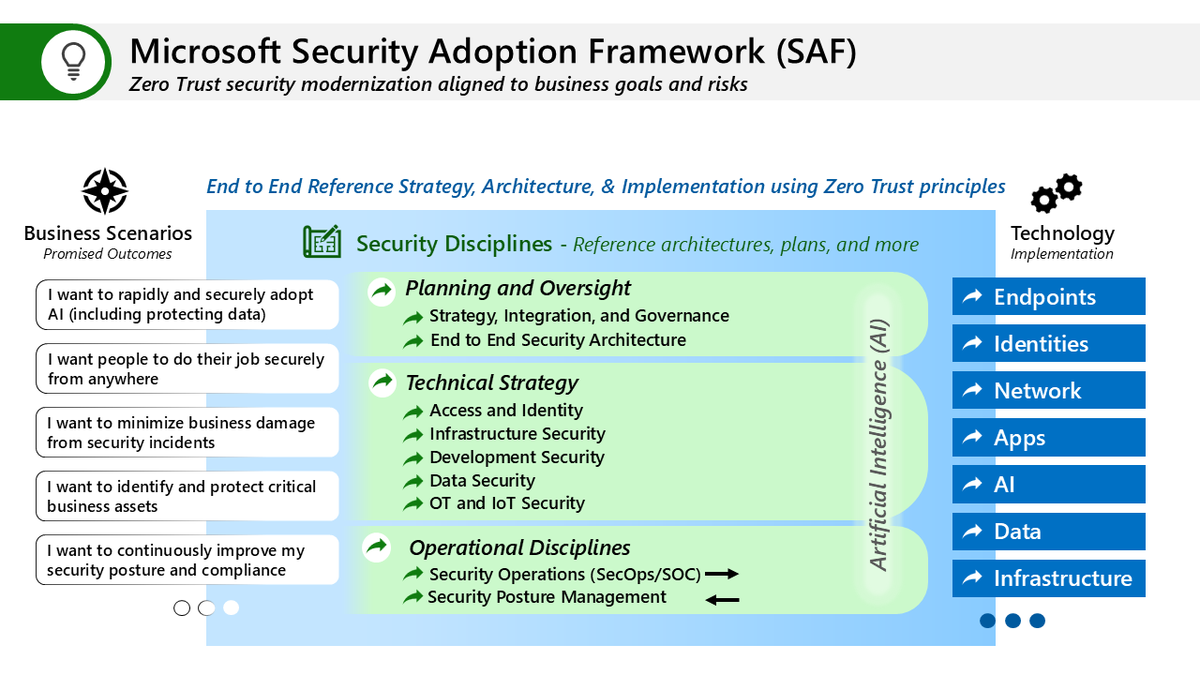
We’re working on updating the disciplines of the Microsoft Security Adoption Framework (SAF) and wanted to get your feedback Current guidance is on aka.ms/SAF a 🧵
.@Office365 #Microsoft365 Sensitivity labels have a new way of grouping. It's called a new dynamic architecture, but it's really just a new way to display labels in apps. Here's the story: office365itpros.com/2025/10/29/sen…
Blog post: Implementing Privileged Access Workstations (PAWs) – Benefits, Challenges, and #Security Considerations msendpointmgr.com/2025/09/16/imp… #PAW #Client
MapUrlToZone (MUTZ) is a security-critical Windows component that determines whether a given path is local, on the intranet, or on the broader Internet – a classification that drives several security decisions across Windows – and is now being used in ways beyond its original…
Alrighty, ready to see something really cool? The evolution of Hurricane Melissa's mesovortices at peak strength.
Here is an good introduction to AI Red Team published by Pillar Security. It gives you a broader understanding and methodology to start evaluate your AI systems, from AI Kill Chain, CFS, to practical example. pillar.security/ai-red-teaming…

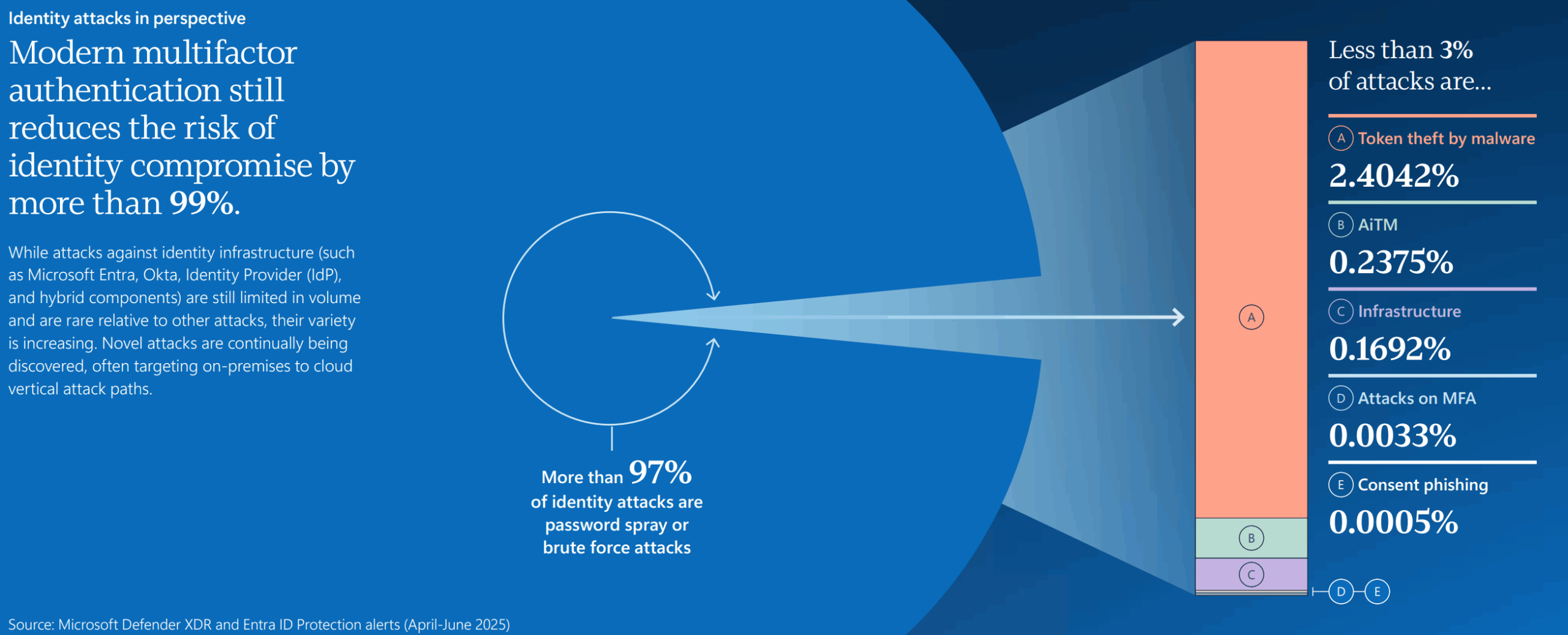
For you nerds like me that read the docs learn.microsoft.com/en-us/microsof…
WDAC Managed Installers explained: Instead of trusting individual files, trust the process that installs them (ConfigMgr, Intune, etc.) Files get NTFS Extended Attributes → WDAC trusts them → No explicit rules needed Limitations & gotchas in our new blog 👇…
Microsoft sued for allegedly tricking millions into Copilot M365 subscriptions - @billtoulas bleepingcomputer.com/news/microsoft…
United States Xu hướng
- 1. Texas 157K posts
- 2. #JimmySeaFanconD1 305K posts
- 3. 3-8 Florida 2,158 posts
- 4. #HookEm 10.7K posts
- 5. Austin Reaves 13.1K posts
- 6. Sark 5,242 posts
- 7. Arch 25.3K posts
- 8. Aggies 9,407 posts
- 9. #DonCheadleDay 1,277 posts
- 10. Jeff Sims 1,704 posts
- 11. Life is 10% 2,657 posts
- 12. Georgia 49.6K posts
- 13. Marcel Reed 4,487 posts
- 14. Elko 3,083 posts
- 15. Arizona 32.6K posts
- 16. #LakeShow 3,813 posts
- 17. Sylus 98.6K posts
- 18. Katie Miller 2,709 posts
- 19. Kentucky and Mississippi State N/A
- 20. Banana Fish 10.3K posts
Something went wrong.
Something went wrong.