Mark St. Amour
@mstamour
Engaging Talent & Helping Build Teams Talent Acquisition / Connecting Great People with Great Companies to do Great Things!
Może Ci się spodobać
The Randori Attack Team developed a working exploit for #f5 BIG-IP CVE-2022-1388. To help the #infosec community assess their risk, we published our technical analysis and a bash one-liner that organizations can run to test exploitability. Details here: randori.com/blog/vulnerabi…
Another awesome season with @NationalCCDC has come to an end. It has been an honor working with @HECFBlog and the rest of the @CCDCRedTeam crew over the years. randori.com/blog/nccdc-tra…
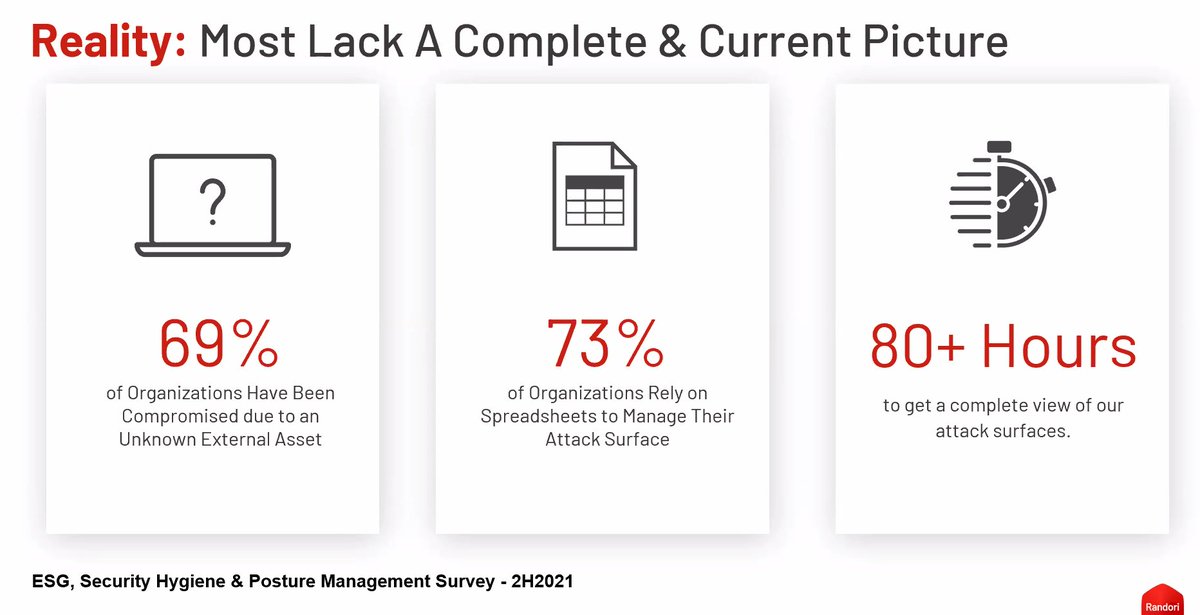
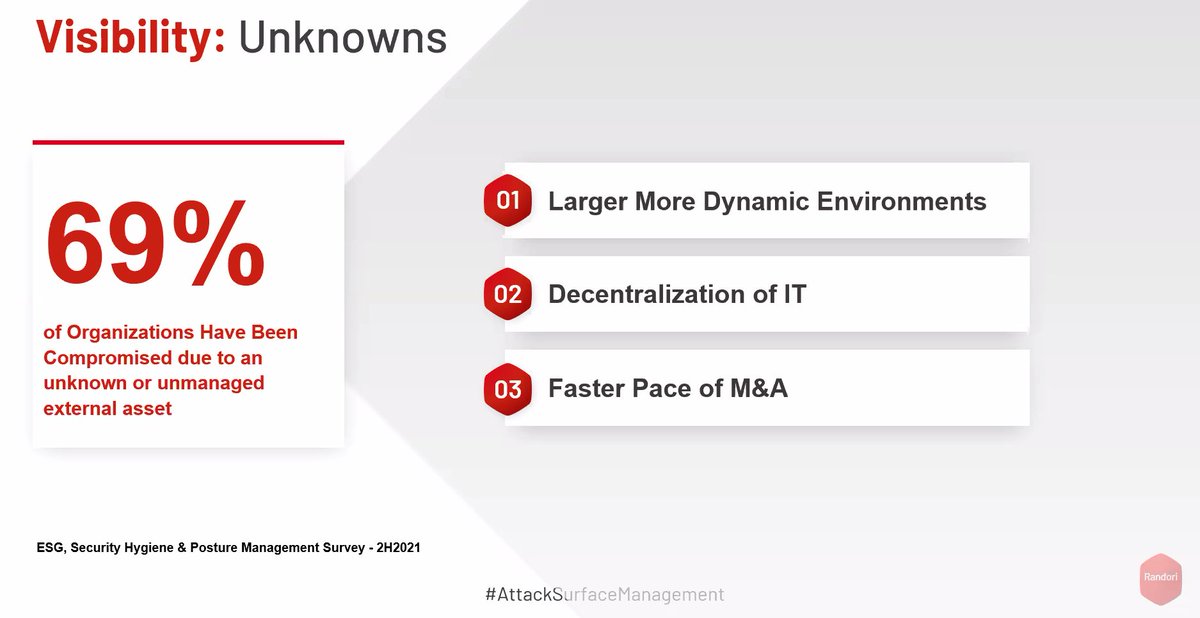
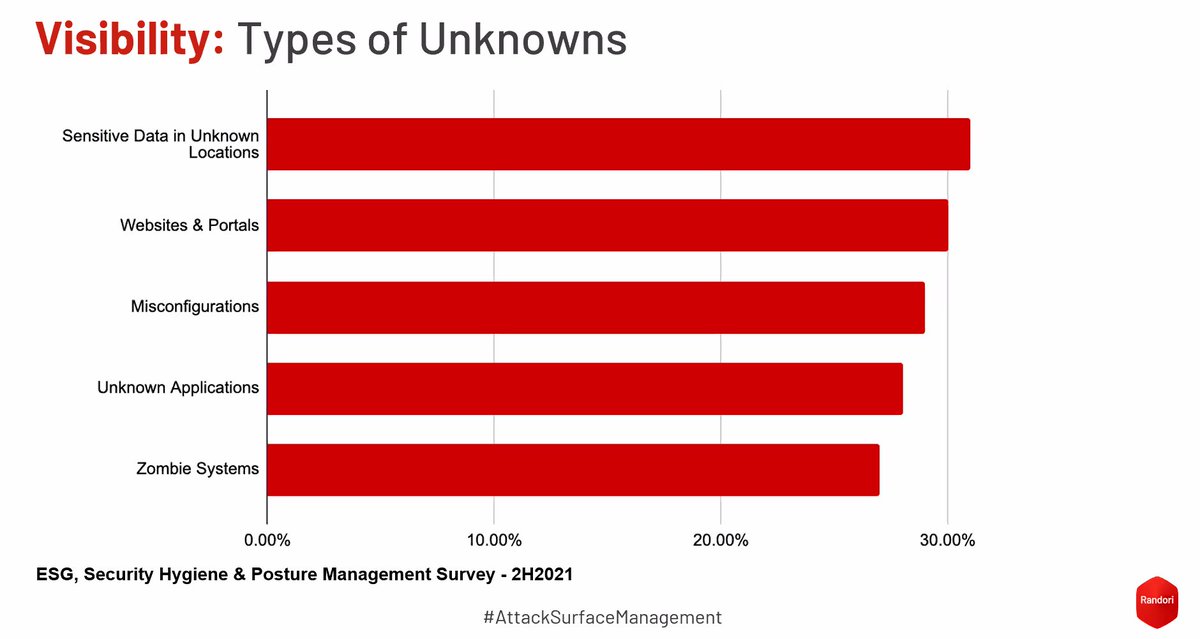
Does your org have an understanding of its External Attack Surface? If the answer is yes, how often are you validating that? The data from @RandoriSecurity suggests most organizations don't know or validate often due to the cost of the validation activity sans.org/webcasts/attac…
Starting at 1030 EDT, I'll be emceeing the attack surface management forum with @RandoriSecurity. We'll be joined by @thegrugq for a *fantastic* presentation on cyber warfare, specifically discussing Ukraine and Russia today. Join us! sans.org/webcasts/attac…
The following non-malicious request can be used to test susceptibility to the @springframework 0day RCE. An HTTP 400 return code indicates vulnerability. $ curl host:port/path?class.module.classLoader.URLs%5B0%5D=0 #SpringShell #Spring4Shell #infosec
New high severity DoS in OpenSSL just released: openssl.org/news/secadv/20… CVE-2022-0778 was reported by @taviso and appears to affect systems that parse user-supplied certificates.
We’ve just posted a vulnerability researcher role: randori.bamboohr.com/jobs/view.php?… Come join us writing exploits and doing zero day research for use in our automated red teaming platform!
Hey Everybody, join @_MG_, @Laughing_Mantis and me for an open discussion around #log4j #long4shell and beyond
Getting into the #haxmas spirit, I have three copies of the awesome @nostarch @humble I'm going to give to followers. RT to help get the word out. Like to enter. I'll DM the download link to the winners Monday. #Hacks #Holiday #Redteam #Blueteam humblebundle.com/books/hacking-…
FYI: Join @Andrew___Morris @aaronportnoy @HexadeciMoose and @_mattata at 3pm EST for a live #log4j discussion hosted by @RandoriSecurity and @GreynoiseIO info.randori.com/log4j-log4shel…
The Randori Attack Team can confirm exploitability of VMWare products in live environments (VMSA-2021-0028) via Log4j (CVE-2021-44228) aka "Log4Shell". This is a critical vulnerability. Follow @RandoriAttack for updates: randori.com/blog/cve-2021-… 1/3
The Randori Attack Team has developed a working exploit and has been able to successfully leverage this vulnerability. Check out our analysis here: randori.com/blog/cve-2021-…
This is the kind of work the team at @RandoriSecurity does that only make the product, platform and the security community and other products better. Join us to help do more! randori.bamboohr.com/jobs/
Announcing CVE-2021-3064: a CVSS 9.8 unauthenticated RCE in @PaloAltoNtwks GlobalProtect VPN devices discovered and disclosed by @RandoriSecurity. Read on for our advisory and stay tuned for further technical details. randori.com/blog/cve-2021-…
Never one to shy away from a tough discussion, @HexadeciMoose details why we use #zerodays at Randori and why we feel they must become a more integral part of security testing: randori.com/blog/why-zero-… #infosec
Follow @RandoriAttack & @RandoriSecurity to keep up with publishing of this advisory. The work @RandoriAttack does is what makes the Randori platform & capabilities so effective. They take apart and build some very interesting things. Join us! randori.bamboohr.com/jobs/ #infosec
Last year we discovered an unauthed remote code execution vulnerability in a leading firewall and began exploiting @RandoriSecurity customers. Tomorrow we'll be publishing an advisory for the Critical CVSS 9.8 flaw in coordination with the vendor. Follow for updates.
Scoop —> Cybersecurity researchers, with the help of the NSA, are exposing a suspected foreign hacking campaign that has targeted multiple US defense contractors. cnn.com/2021/11/07/pol…
A study from Randori has tracked the most sought-after assets attackers are looking to exploit. pst.cr/q9uvJ
We are looking for two of you here too, so tell your friends! #infosec #HIRINGNOW #redteam
Last year we discovered an unauthed remote code execution vulnerability in a leading firewall and began exploiting @RandoriSecurity customers. Tomorrow we'll be publishing an advisory for the Critical CVSS 9.8 flaw in coordination with the vendor. Follow for updates.
SCOOP - And a wild one… Fraudsters used “deep voice” tech - as in deep fake for speech - to clone a company director’s voice. They then convinced a bank manager to send $35 million to various accounts across the world. AI-powered cybercrime is big. forbes.com/sites/thomasbr…
United States Trendy
- 1. Texas 156K posts
- 2. #JimmySeaFanconD1 338K posts
- 3. #BINIFIED 158K posts
- 4. 3-8 Florida 2,208 posts
- 5. hanbin 20K posts
- 6. Austin Reaves 13.6K posts
- 7. Sark 5,282 posts
- 8. #HookEm 10.7K posts
- 9. Jeff Sims 1,713 posts
- 10. Arch Manning 7,275 posts
- 11. #MakeOffer 20.9K posts
- 12. Domain For Sale 21.1K posts
- 13. #BuyNow 21K posts
- 14. Aggies 9,444 posts
- 15. Life is 10% 2,618 posts
- 16. Georgia 49.1K posts
- 17. Sylus 101K posts
- 18. Elko 3,106 posts
- 19. Katie Miller 2,854 posts
- 20. Banana Fish 10.8K posts
Może Ci się spodobać
Something went wrong.
Something went wrong.