#34c3ctf search results
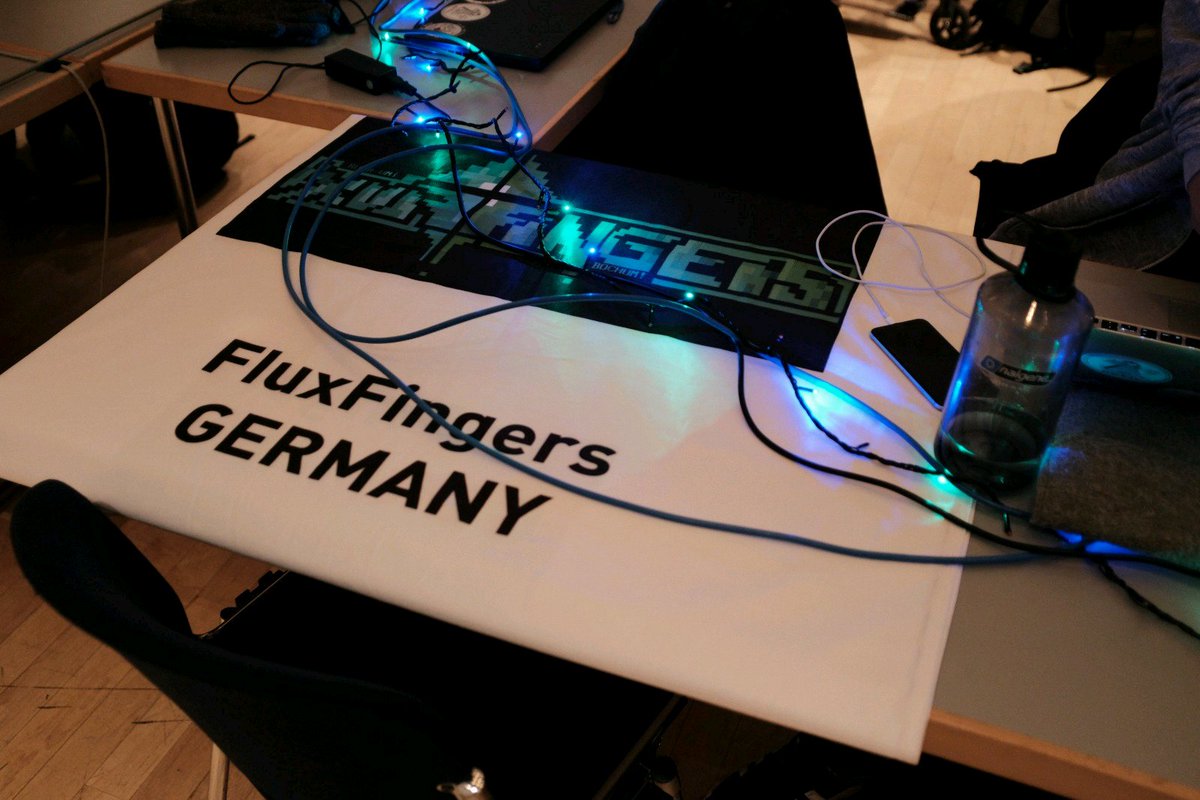
☑️Arrived at #34c3 ☑️Deployed Flag ☑️Printed a „few“ Stickers 9h until #34c3ctf - hope you are ready, we are!

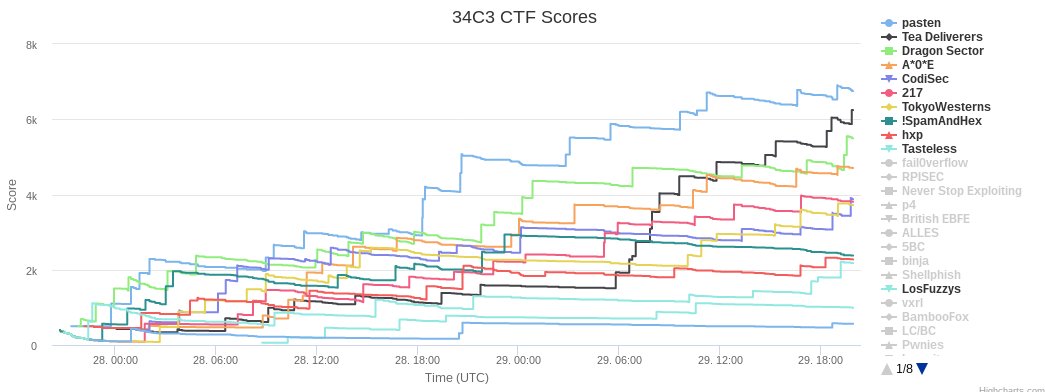
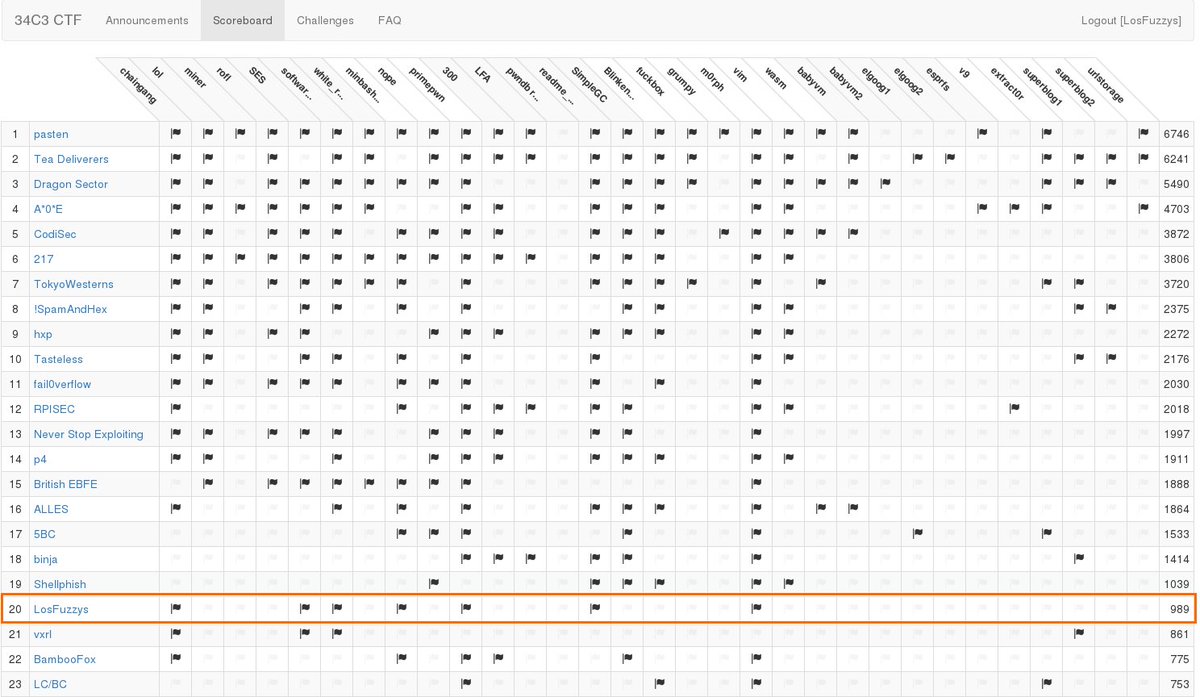
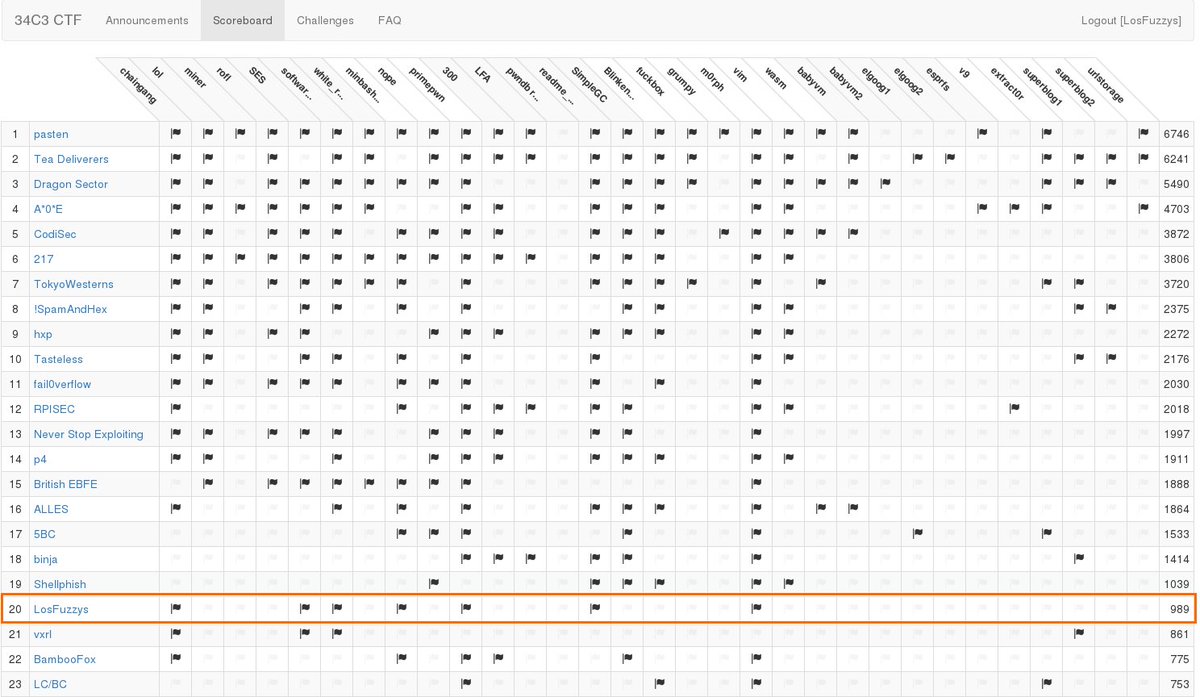
#34c3ctf is over! Flag submission is closed - Good game everyone! Top 3 #34c3ctf: 1. @pastenctf 2. Tea Deliverers 3. @DragonSectorCTF Top 3 #junior34c3ctf: 1. Rudolfos Toddlers 2. @hackthissite 3. Made In MIM
Here is a video of my #34C3CTF Blinkenlights challenge in case you wondered if I have actual hardware. Yes, I have. As always, it looks way better in real life because of the limited dynamic range of the camera sensor.
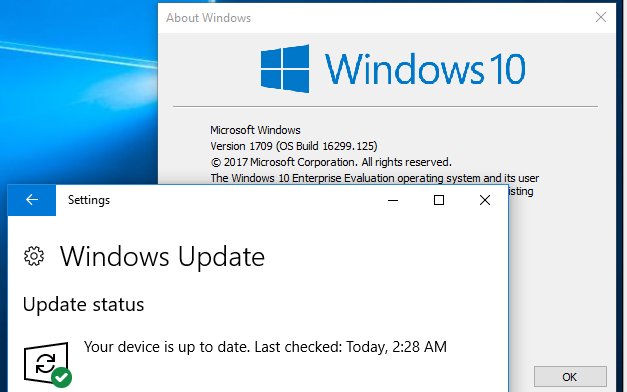
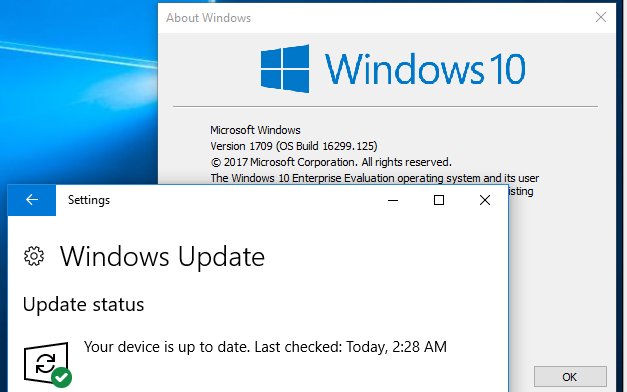
A strong VM host could be useful for #34c3ctf. Win10 RS3 VMs can be had at developer.microsoft.com/en-us/windows/…. Apply latest updates. We recommend VMware and 16G of RAM. Happy holidays!
Think now is a good time to write a Chrome exploit? Do `nc 35.198.159.246 1337` or visit 34c3ctf.ccc.ac/challenges/ and look for the "v9" challenge =) #34C3CTF #34C3
Challenge files, docker environment, and my exploit for the "v9" Chromium pwnable of #34c3ctf. Congrats to @itszn13 and A*0*E for solving it in time! github.com/saelo/v9 #34C3
Das ist der C(kakamann) #34C3 #34C3SZ #34c3ctf #34c3ticket #leipzig #sachsen #CCC #berlin #deutschland
PSA: We are hyped for #34c3ctf. There will be rather unique challenges this year. You should be too! See you at #34c3 or in IRC!
software_update challenge from the #34c3ctf was an awesome practical example of math applied to security. We learn about basic linear algebra and finite-fields to break an XOR signature implementation. youtube.com/watch?v=EOlddN…
youtube.com
YouTube
Linear independence and GF(2) - 34C3 CTF software_update (crypto)...
I made a pair of kernel exploitation challenges on Windows 10 RS3 for #34c3ctf. 34c3ctf.ccc.ac/uploads/elgoog… is the "easy" version, 34c3ctf.ccc.ac/uploads/elgoog… is the real deal.
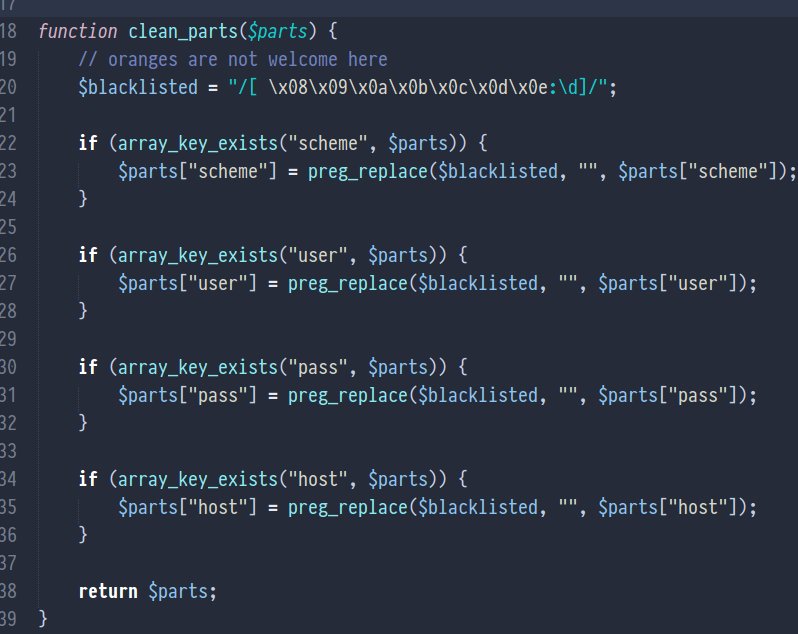
Part 1/2 of another #34c3ctf challenge. The solution of this one really blew me away. But in the first episode we just review the code and think of possible attacks. youtube.com/watch?v=Vgdhlh…
youtube.com
YouTube
Python code audit of a firmware update - 34C3 CTF software_update...
C3CTF 2017 Writeups CTFtime: ctftime.org/event/544/task… GitHub: github.com/sajjadium/Pers… GitLab: gitlab.com/sajjadium/Pers… Bitbucket: bitbucket.org/sajjadium/pers… @EatSleepPwnRpt @CTFtime #C3CTF #34C3 #34C3CTF #CTFtime #InfoSec #CTFium #PersianCatsCTF #CTF #Pwn
phoenhex.re/2018-03-25/not… is about a cool feature of Vagrant that allows unprivileged guest processes to read/write the entire host filesystem. If you do not like this feature in your Vagrant setup, export VAGRANT_DISABLE_VBOXSYMLINKCREATE=1 Also, babyvm2 writeup for #34c3ctf
software_update challenge from the #34c3ctf was an awesome practical example of math applied to security. We learn about basic linear algebra and finite-fields to break an XOR signature implementation. youtube.com/watch?v=EOlddN…
youtube.com
YouTube
Linear independence and GF(2) - 34C3 CTF software_update (crypto)...
RT hasherezade "RT LiveOverflow: Part 1/2 of another #34c3ctf challenge. The solution of this one really blew me away. But in the first episode we just review the code and think of possible attacks. youtube.com/watch?v=Vgdhlh…"
Part 1/2 of another #34c3ctf challenge. The solution of this one really blew me away. But in the first episode we just review the code and think of possible attacks. youtube.com/watch?v=Vgdhlh…
youtube.com
YouTube
Python code audit of a firmware update - 34C3 CTF software_update...
RT hasherezade "RT LiveOverflow: Two years ago I failed to solve the pwnable readme challenge at the #32c3ctf. Since then I have learned a lot and I got another chance at the #34c3ctf! youtube.com/watch?v=lE6ke7…"
This is the best writeups on advanced heap exploitation I've read in a while. I think technique 1 is what @maciekkotowicz used in #34c3ctf.
From heap to RIP: getting code execution from pure glibc heap mechanics blog.frizn.fr/glibc/glibc-he…
This is essentially the babyvm2 challenge from #34c3ctf. Will do a writeup maybe after my next exam :)
CVE-2018-2693 was my intended solution for babvm2 at #34c3ctf, which DragonSector also found. It allows (amongst others) access to shared folders from unprivileged processes, so we can create symlinks and open them host-side. May do a writeup if valis won't.
We are proud to share our first ever blog post with you. Many thanks to @koyaan5 for explaining us how to solve the m0rph challenge from #34C3CTF sigflag.at/blog/2017/writ…
My beginner focused writeup of solving the morph challenge from #34C3CTF with @radareorg I did for @SIGFLAG_CTF was just published! sigflag.at/blog/2017/writ…
Thank you for writing this challenge and for putting together #34c3ctf. I learned a lot!
Pretty neat write-up for a simple pwnable challenge I did for #34c3ctf, if you are interested in learning more about some of the latest glibc allocator developments: blog.rh0gue.com/2018-01-05-34c…
Wargames and CTFs that are doable for beginners like PicoCTF, SHA CTF Junior and #34c3ctf Junior.
I made a quick writeup for my extract0r web challenge from the #34c3ctf github.com/eboda/34c3ctf/…
chksum0/writeups github.com/chksum0/writeu… #34c3ctf
My writeup on #34c3ctf 300 challenge: github.com/chksum0/writeu… tldr: House of Orange + vtable validation bypass
Maybe should make a #findmyunicorn and see how many replies it gets? #34C3 #34c3ctf
Here's my exploit for my heap challenge (300) of the #34c3ctf. I solved it by overwriting (older) libc's check_action variable using a corrupted unsorted bin. This disables abort on error and gives a write-what-where primitive. gist.github.com/sroettger/591b…
my solution for the nope challenge of #34c3ctf: gist.github.com/spq/0a5915940c…
☑️Arrived at #34c3 ☑️Deployed Flag ☑️Printed a „few“ Stickers 9h until #34c3ctf - hope you are ready, we are!

#34c3ctf is over! Flag submission is closed - Good game everyone! Top 3 #34c3ctf: 1. @pastenctf 2. Tea Deliverers 3. @DragonSectorCTF Top 3 #junior34c3ctf: 1. Rudolfos Toddlers 2. @hackthissite 3. Made In MIM
A strong VM host could be useful for #34c3ctf. Win10 RS3 VMs can be had at developer.microsoft.com/en-us/windows/…. Apply latest updates. We recommend VMware and 16G of RAM. Happy holidays!
Das ist der C(kakamann) #34C3 #34C3SZ #34c3ctf #34c3ticket #leipzig #sachsen #CCC #berlin #deutschland
Something went wrong.
Something went wrong.
United States Trends
- 1. Good Saturday 24.8K posts
- 2. Texas 157K posts
- 3. #MeAndTheeSeriesEP3 386K posts
- 4. #SaturdayVibes 2,710 posts
- 5. 3-8 Florida 2,656 posts
- 6. #SmallBusinessSaturday N/A
- 7. #JimmySeaFanconD1 616K posts
- 8. #BINIFIED 238K posts
- 9. Go Blue 5,529 posts
- 10. UTEP N/A
- 11. Black Sea 15.8K posts
- 12. Sam Houston N/A
- 13. hanbin 27.7K posts
- 14. Domain For Sale 22.2K posts
- 15. Go Bucks 1,469 posts
- 16. Katie Miller 3,784 posts
- 17. Kentucky and Mississippi State N/A
- 18. Go Buckeyes N/A
- 19. Lindor 2,868 posts
- 20. Miss St 2,010 posts