#zerodayexploit search results
Zero day attack is the exploitation of a previously unknown vulnerability in software, hardware or firmware before the vendor knows about it. @ireteeh @Abby_amg #zerodayexploit #RealTimeThreatDetection

Hackers Crack 73 Zero-Days and Win $1,024,750 at Pwn2Own Ireland 2025 💥Hackers Turn Bugs Into Gold at Pwn2Own Ireland 2025! Full Story 👉 cybersecurity88.com/news/hackers-e… #EthicalHacking #zerodayattack #zerodayexploit #Competition

🚨 A #zerodayexploit flaw in #WhatsApp allows #attackers to target users through short, silent calls — no answering or clicking required. 🔒 #enable Silence #Unknown Callers #Settings → Privacy → Calls → Silence Unknown Callers. #StaySafe matjarx.org/offer.php
Zero-Day Exploit = celah yang belum terdeteksi. Sebelum tambalan dirilis, pertahanan nyaris nol. #ZeroDay #ZeroDayExploit #KeamananSiber #CyberSecurity #InfoSiber #ThreatIntel #Vulnerability #VulnerabilityManagement

Fortinet confirms active attacks using PoC exploit for critical 0-day flaw granting remote code execution on multiple enterprise devices. #CyberSecurity #ZeroDayExploit #Fortinet

Zimbra Zero-Day Exploited to Target Brazilian Military via Malicious ICS Files reconbee.com/zimbra-zero-da… #Zimbra #zerodayexploit #brazil #brazilian #ICSfiles #cyberattack #cyberattacks
1/11 A zero-day exploit refers to a security vulnerability that is unknown to the software vendor and has no available patch. Hackers use these exploits to attack systems before the developers can fix them, making them highly dangerous. #ZeroDayExploit #CyberSecurity #Technology

📢 📰 Cybersecurity Alert: LANDFALL operation compromises Samsung Galaxy devices via WhatsApp images! 🗞 🔔 #Cybersecurity #MobileSecurity #ZeroDayExploit 🔄 Share 👍 React 🌐 Visit aravind-r.com #AravindRaghunathan

Chrome Zero-Day Exploited to Deliver Italian Memento Labs’ LeetAgent Spyware reconbee.com/chrome-zero-da… #chrome #zerodayexploit #italian #italianmementolabs #leetagentspyware #spyware #cyberattack
reconbee.com
Chrome Zero-Day Exploited to Deliver Italian Memento Labs' LeetAgent Spyware
headquarters located in Milan read more about Chrome Zero-Day Exploited to Deliver Italian Memento Labs' LeetAgent Spyware
Hackers Actively Exploiting 7-Zip Symbolic Link–Based RCE Vuln (CVE-2025-11001) thehackernews.com/2025/11/hacker… #7ZipVulnerability #CVE202511001 #ZeroDayExploit #RemoteCodeExecution #SymbolicLinkAttack #ZipFileSecurity #SoftwareUpdate #CyberExploitation #WindowsSecurity #PatchNow
Amnesty Finds Cellebrite’s Zero-Day Used to Unlock Serbian Activist’s Android Phone dlvr.it/TKXQdM #AmnestyInternational #Cellebrite #ZeroDayExploit #AndroidSecurity #DigitalRights

Global Citrix servers compromised in large-scale Zero-day exploit #ZeroDayExploit
🚨 CISA warns of active attacks on Commvault’s SaaS platform via a zero-day flaw, giving threat actors access to Microsoft 365 environments. Cloud misconfigurations are under fire ☁️🔐#ZeroDayExploit #CloudThreats buff.ly/yLWMcgB

⚠️Η εταιρεία αποκαλύπτει στοιχεία που υποδηλώνουν ότι τουλάχιστον τρεις ομάδες χάκερ με έδρα την Κίνα κάνουν κατάχρηση της ευπάθειας zero-day στο λογισμικό SharePoint για να αποκτήσουν πρόσβαση σε διακομιστές. #SharePoint #zerodayexploit gr.pcmag.com/security/50242…
Massive Oracle EBS breach shakes global firms! 🚨 CL0P exploits zero-day CVE-2025-61882 to steal sensitive data & demand up to $50M ransom. Are your ERP systems patched? Time to act fast before more get hit! #Cybersecurity #zerodayexploit #zerodayattack #10Oct #FridayMorning
💻New Mirai botnet targets industrial routers with zero-day exploits💻 bleepingcomputer.com/news/security/… #MiraiBotnet #Cybersecurity #ZeroDayExploit #IndustrialRouters #IoTsecurity #Botnet #CyberAttack

🚨 CVE-2025-53690 🚨 Attackers are exploiting old Sitecore setups using a legacy key to launch WEEPSTEEL malware. It’s not a bug; it’s a configuration mistake now weaponised. Are your systems safe? Details 👇 socradar.io/cve-2025-53690… #SOCRadar #cybersecuritytips #zerodayexploit…

🐞 Undocumented 0-day exploit within @Google's OAuth system, specifically targeting an endpoint known as "MultiLogin." Continue at post: linkedin.com/pulse/how-malw… #GoogleOAuth #ZeroDayExploit #CloudSEK #PRISMA #LummaInfostealer #GoogleAccountHack #2FA @YouTube

Hackers Actively Exploiting 7-Zip Symbolic Link–Based RCE Vuln (CVE-2025-11001) thehackernews.com/2025/11/hacker… #7ZipVulnerability #CVE202511001 #ZeroDayExploit #RemoteCodeExecution #SymbolicLinkAttack #ZipFileSecurity #SoftwareUpdate #CyberExploitation #WindowsSecurity #PatchNow
Fortinet has patched a newly exploited zero-day in its FortiWeb firewall, announced just days after revealing another critical bug attackers had already abused. theregister.com/2025/11/19/for… #Fortinet #0day #zerodayexploit #firewall #CyberSecurity #CybersecurityNews #threatresq
Google Issues #Securityupdate for #Chrome V8 #zerodayexploit #Vulnerability - The Hacker News thehackernews.com/2025/11/google…
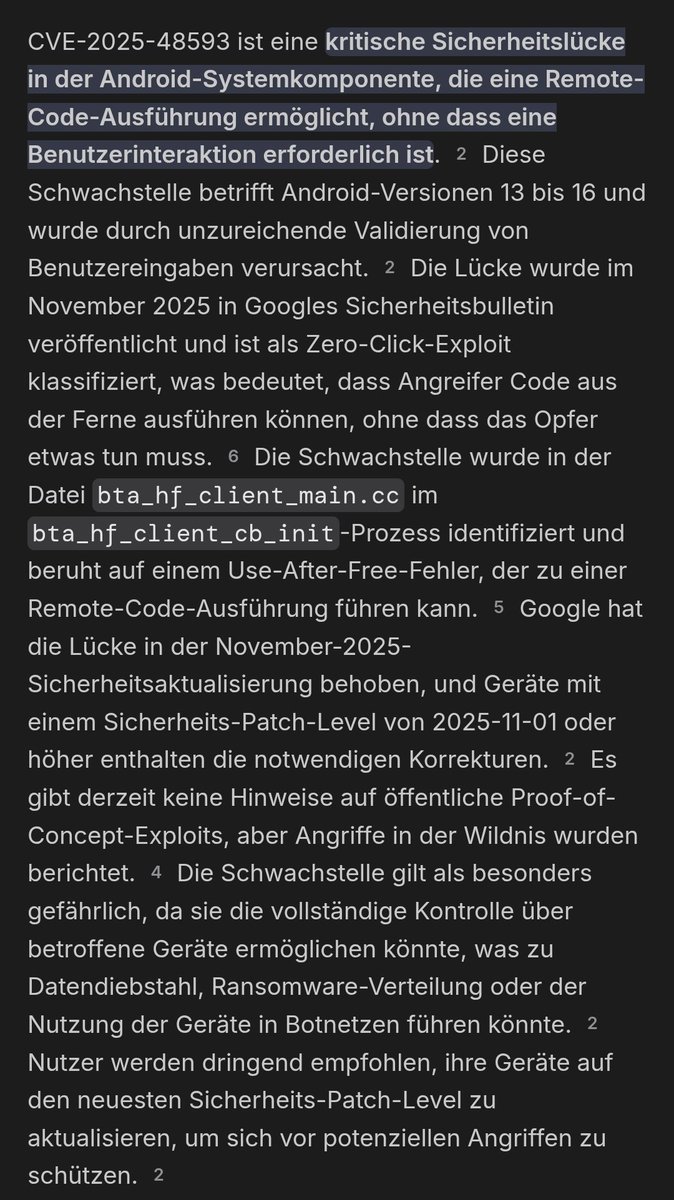
Ja ist eine weiterer #zerodayexploit aber zur Zeit nur Android 13 bis 16 , es gibt aber wohl noch kein #POC Proof of Concept.
🚨 A #zerodayexploit flaw in #WhatsApp allows #attackers to target users through short, silent calls — no answering or clicking required. 🔒 #enable Silence #Unknown Callers #Settings → Privacy → Calls → Silence Unknown Callers. #StaySafe matjarx.org/offer.php
@microsoft's #feedbackhub is useless. Over 2 years of reports across at least 2 different operating systems and keyboard layouts are #LEAKING across user instances! I encourage everyone to make use of this sure #zerodayexploit, as it doesn't look like it'll ever be fixed!
Zero day attack is the exploitation of a previously unknown vulnerability in software, hardware or firmware before the vendor knows about it. @ireteeh @Abby_amg #zerodayexploit #RealTimeThreatDetection

📢 📰 Cybersecurity Alert: LANDFALL operation compromises Samsung Galaxy devices via WhatsApp images! 🗞 🔔 #Cybersecurity #MobileSecurity #ZeroDayExploit 🔄 Share 👍 React 🌐 Visit aravind-r.com #AravindRaghunathan

#zerodayexploit #medicaldevices #biotronik #pacemakers #seriousasaheartattack @defcon @TheHackersNews @business @BusinessInsider @WSJ github.com/just-noticeabl… <-- 👀 @wallstreetbets absolutely certain about this 💎💎
#infosec #zerodayexploit #Windows11 I use Windows 11 to code and play video games when I'm bored. Hopefully they fix these vulnerabilities with a path soon. I might just install Linux.
Two Windows vulnerabilities, one a zero-day, are under active exploitation. Both are being exploited in wide-scale operations. Seven months later, Microsoft still hasn't patched the vulnerability, which stems from a bug in the Windows Shortcut binary format. This Windows…

Zero day attack is the exploitation of a previously unknown vulnerability in software, hardware or firmware before the vendor knows about it. @ireteeh @Abby_amg #zerodayexploit #RealTimeThreatDetection

Apple iCloud ਸਮੇਤ ਇਨ੍ਹਾਂ ਸੇਵਾਵਾਂ ’ਚ ’ਚ ਮਿਲਿਆ ਖਤਰਨਾਕ ਬਗ, ਹੋ ਸਕਦੈ ਹੈਕਿੰਗ ਦਾ ਖ਼ਤਰਾ jagbani.punjabkesari.in/gadgets/news/z… #ZeroDayExploit #Apple #AppleiCloud #Twitter #Minecraft #Javalogginglibrary

1/11 A zero-day exploit refers to a security vulnerability that is unknown to the software vendor and has no available patch. Hackers use these exploits to attack systems before the developers can fix them, making them highly dangerous. #ZeroDayExploit #CyberSecurity #Technology

'What kind of malware is designed to take advantage of a security hole before it is known?'. The correct answer is 'Zero-day exploit'. Read on to know more about Zero-day exploit. #cybersecurity #zerodayexploit #Ishantechnologies #Ishanism #malwareattack #vapt



Zero Day Exploit - Sıfır Gün Saldırısı Nedir? Siber korsanların daha önce belirlenmemiş bir güvenlik açığına saldırma yöntemine denir. #fordefence #ZeroDayExploit #SıfırGünSaldırısı #SiberGüvenlik #SiberSözlük

Fortinet confirms active attacks using PoC exploit for critical 0-day flaw granting remote code execution on multiple enterprise devices. #CyberSecurity #ZeroDayExploit #Fortinet

💻New Mirai botnet targets industrial routers with zero-day exploits💻 bleepingcomputer.com/news/security/… #MiraiBotnet #Cybersecurity #ZeroDayExploit #IndustrialRouters #IoTsecurity #Botnet #CyberAttack

Google Threat Analysis Group found a new Chrome zero-day that may have been exploited by commercial spyware developers. #CyberSecurity #ZeroDayExploit #Spyware

Microsoft found Turkish-linked hackers used a zero-day flaw to spy on Kurdish military via Output Messenger in cross-border operations. #CyberEspionage #ZeroDayExploit #MicrosoftSecurity

#ZeroDayExploit für #Chrome entdeckt it-daily.net/it-sicherheit/… #CyberSecurity #cybercrime #Exploit @Kaspersky_DACH

Splunk Enterprise flaw lets low-level users run JavaScript code, prompting urgent patches for versions below 9.4.2 and affected Cloud instances. #CyberSecurity #Splunk #ZeroDayExploit

#Microsoft Patch Tuesday: Microsoft patched 2 #ZeroDayExploit -days in #GraphicsComponent cybersecurity-help.cz/blog/72.html

vBulletin Flaws Let Hackers Run Code, One Exploit Active Now Two critical bugs in vBulletin forum software are under attack, allowing remote code execution without authentication. #vBulletin #CyberSecurity #ZeroDayExploit

Adobe Issues Patch for Actively Exploited Flash Player #ZeroDayExploit i.securitythinkingcap.com/QWWfT8

💻New Mirai botnet targets industrial routers with zero-day exploits💻 bleepingcomputer.com/news/security/… #MiraiBotnet #Cybersecurity #ZeroDayExploit #IndustrialRouters #IoTsecurity #Botnet #CyberAttack

Hacker Group #pawnstorm Uses Java #zerodayexploit To Spy On #nato Countries #java javadevhub.com/post/hacker-gr…

In February, Microsoft addressed a critical privilege escalation vulnerability in the Windows Kernel, identified as CVE-2024-21338, which had been actively exploited as a zero-day for six months. . #avmconsulting #WindowsSecurity #ZeroDayExploit #CVE202421338 #MicrosoftPatch

Something went wrong.
Something went wrong.
United States Trends
- 1. Eagles 134K posts
- 2. Eagles 134K posts
- 3. #SmackDown 8,214 posts
- 4. Marcel Reed 1,366 posts
- 5. Ben Johnson 23.6K posts
- 6. Jalen 29.1K posts
- 7. Patullo 13.8K posts
- 8. Caleb 49.1K posts
- 9. Philly 28.7K posts
- 10. #BearDown 2,615 posts
- 11. #BedBathandBeyondisBack N/A
- 12. Sirianni 8,808 posts
- 13. Lane 57.7K posts
- 14. AJ Brown 6,570 posts
- 15. Aggies 3,732 posts
- 16. #HookEm 3,635 posts
- 17. Lindor N/A
- 18. Howie 3,074 posts
- 19. #iufb 1,384 posts
- 20. Wingo N/A