#jwt_auth 검색 결과
github.com/code4mk/kauth/ @laravelphp jwt api authentication package #laravel_jwt_auth #jwt_auth #code4mk #0devco #Laravel
github.com/code4mk/kauth/ Laravel jwt api authentication package #laravel_jwt_auth #jwt_auth #code4mk #0devco
💡 JWT Login Flow in One Line Credentials → Token → Token in Header → Server Verifies → Access That’s it. JWTs are simple once you understand how they work.
🧠 Key Takeaways ◉ JWTs are not encrypted ◉ Don’t store sensitive info inside ◉ The signature ensures data integrity ◉ JWT is stateless (server stores nothing) ◉ Always send the token in the Authorization header
📝 Login Flow With JWT: ➥ User sends email + password ➥ Server verifies ➥ Server creates a JWT token ➥ Token is sent back to the user ➥ User stores it (localStorage/cookie) ➥ User sends token in headers for protected routes ➥ Server checks token → allows or denies
🔐 JWT-Based Auth (Token-Based) This one is stateless. The server doesn’t store anything. Instead, it gives you a token (a long string), and YOU keep it. You send this token every time you need access.
OAuth のAccess Token を JWT にする拡張仕様は RFC 9068 として今は亡き Vittorio が書いてますけどね。でも、Client にとっては ATはopaque であるという原則は崩してはいけない。 でも、どうしてそんなに OAuth 認証したいんですか?安全にしようと思ったらほぼOIDCになりますよ。
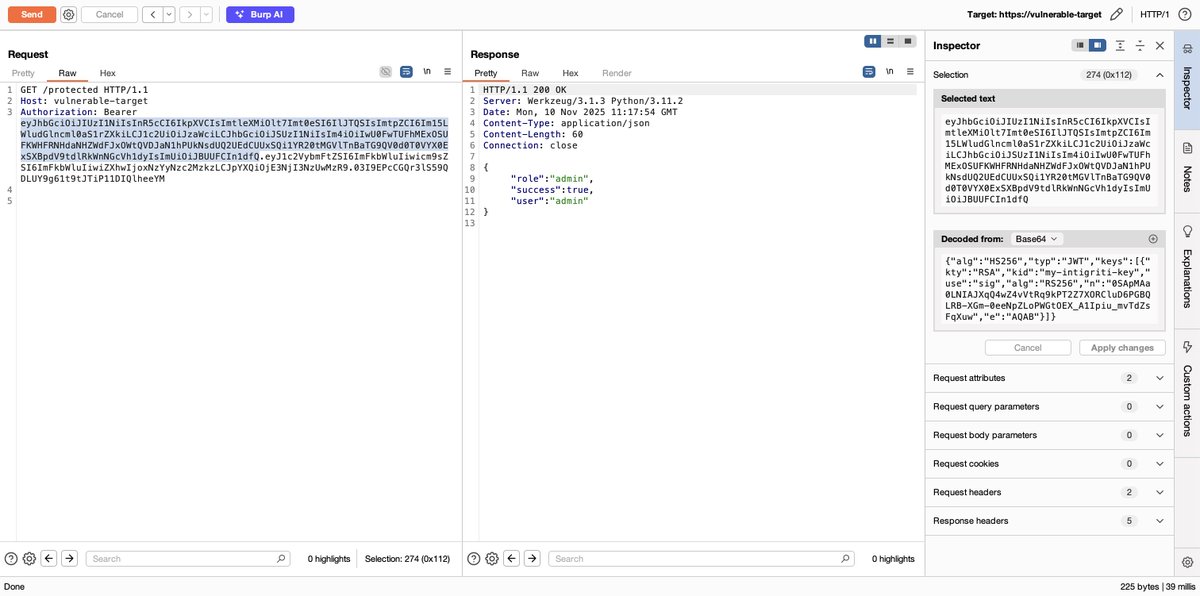
``` import jwt public_key = """--BEGIN PUBLIC KEY-- paste the real key here --END PUBLIC KEY--""" payload = { "role": "admin", "exp": 9999999999 # Far-future expiry to avoid token expiration } token = jwt.encode(payload, public_key, algorithm="HS256") print(token) ```
Before we dive into this thread... If you wish to read more in-depth about JWT attacks, make sure you give our comprehensive article a read! In this resource, we document over 5+ common JWT misconfigurations, including instructions on how to test for them! 👇 🔗…
The JWT verification accepts both RS256 and HS256 algorithms (confusion), and the RSA public key is loaded from environment variable. Also, this only checks if role != 'admin' (not proper authentication).
Apps that handle user accounts need a secure way to tell who's who. This is what authentication is for - it tells you the person trying to access the app is who they say they are. In this article, @thejoanayebola teaches you how to build a secure authentication system with JWT…
xjwt.io the “x” in front of jwt stands for cracked, think of it as the cracked version of the popular jwt[.]io, it literally attempts to crack tokens signed with weak secrets. swe & sec engineers should check it out🙂
xjwt.io
JWT Security Checker
Advanced JWT decoding & cracking toolkit with a user-friendly UI for security testing
JWT Hacking Toolkit: 20 Real Hacker Techniques to Master Authentication Attacks medium.com/@verylazytech/… #bugbounty #bugbountytips #bugbountytip
Inter-service communication was eye-opening: User Service validates every request by calling Auth Service with the JWT token. If Auth says "invalid," User Service rejects immediately. Zero trust between services = better security
JWT security is where most auth implementations fail. everyone focuses on password hashing but then stores JWTs in localStorage (XSS risk) or uses weak secrets. proper token rotation, httpOnly cookies, and refresh token patterns = minimum for production auth 🔒
Nice one. OWASP also has a great guide on how to attack JWT. JWT FTW
That's a pretty straightforward explanation—yes, it's one of the simplest ways to sum it up! JWT (JSON Web Token) encodes claims like identity into a secure, verifiable string, making auth stateless. No server sessions needed. Nice find!
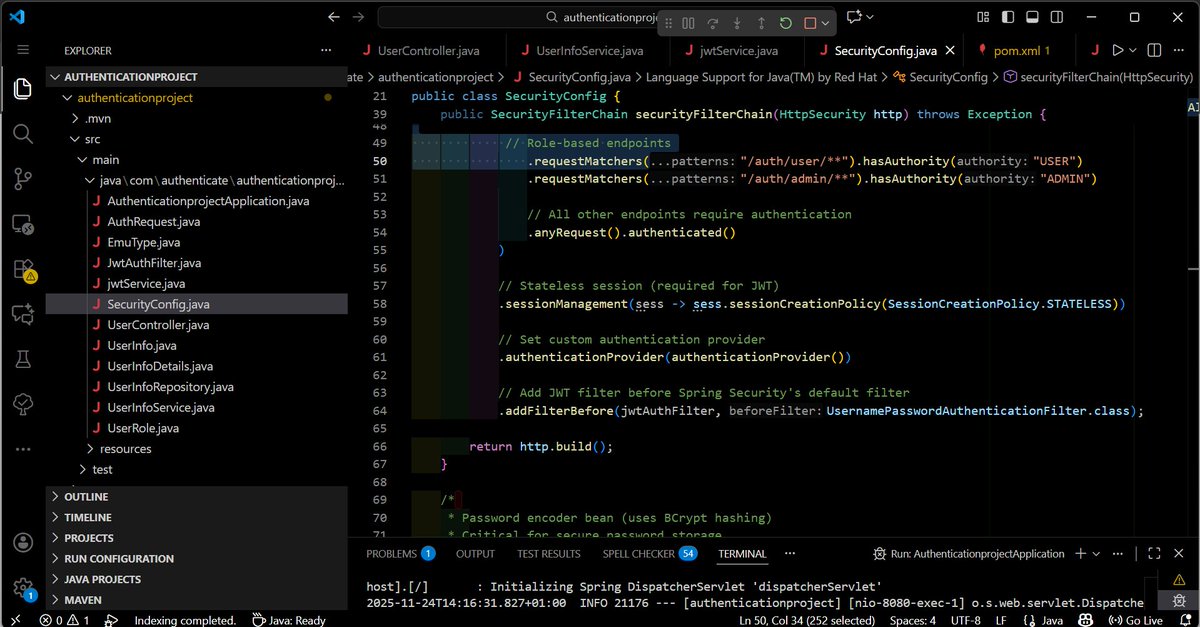
Today I built a simple JWT authentication in Spring Boot. One thing I realized: understanding filters is more important than memorizing code. If you get the flow → Security becomes fun instead of confusing.
JWT Security Checker (XJWT.io) now supports both symmetric and asymmetric algorithms. You can now decode and encode/forge HS/RS/ES/PS-128/256 JWTs. Thank you @Dghost_Ninja for pointing out the need for this feature. Happy hacking, guys!
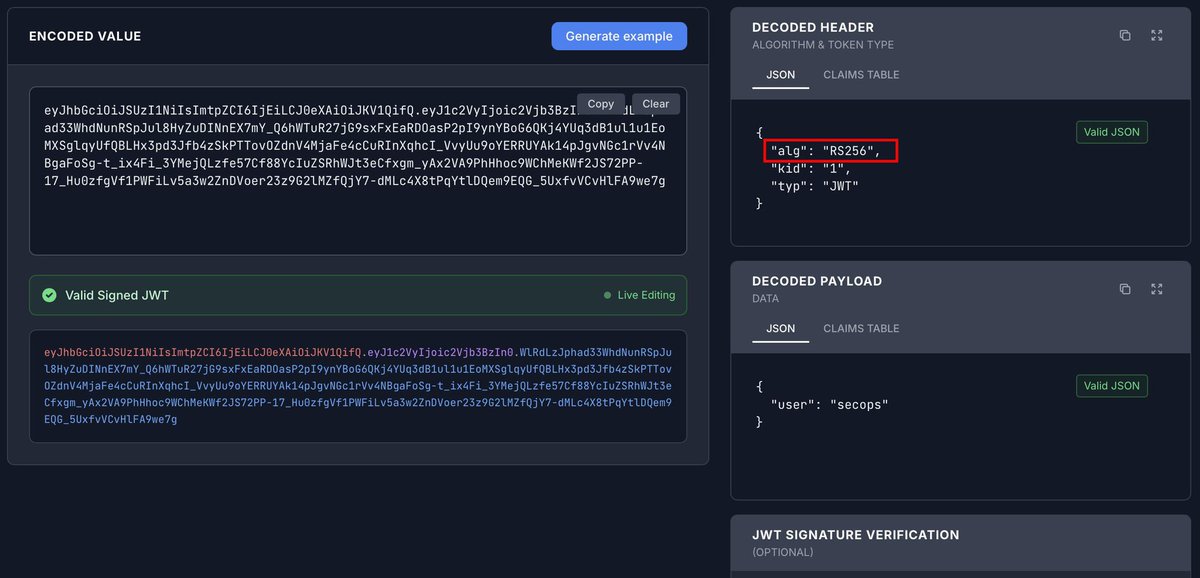
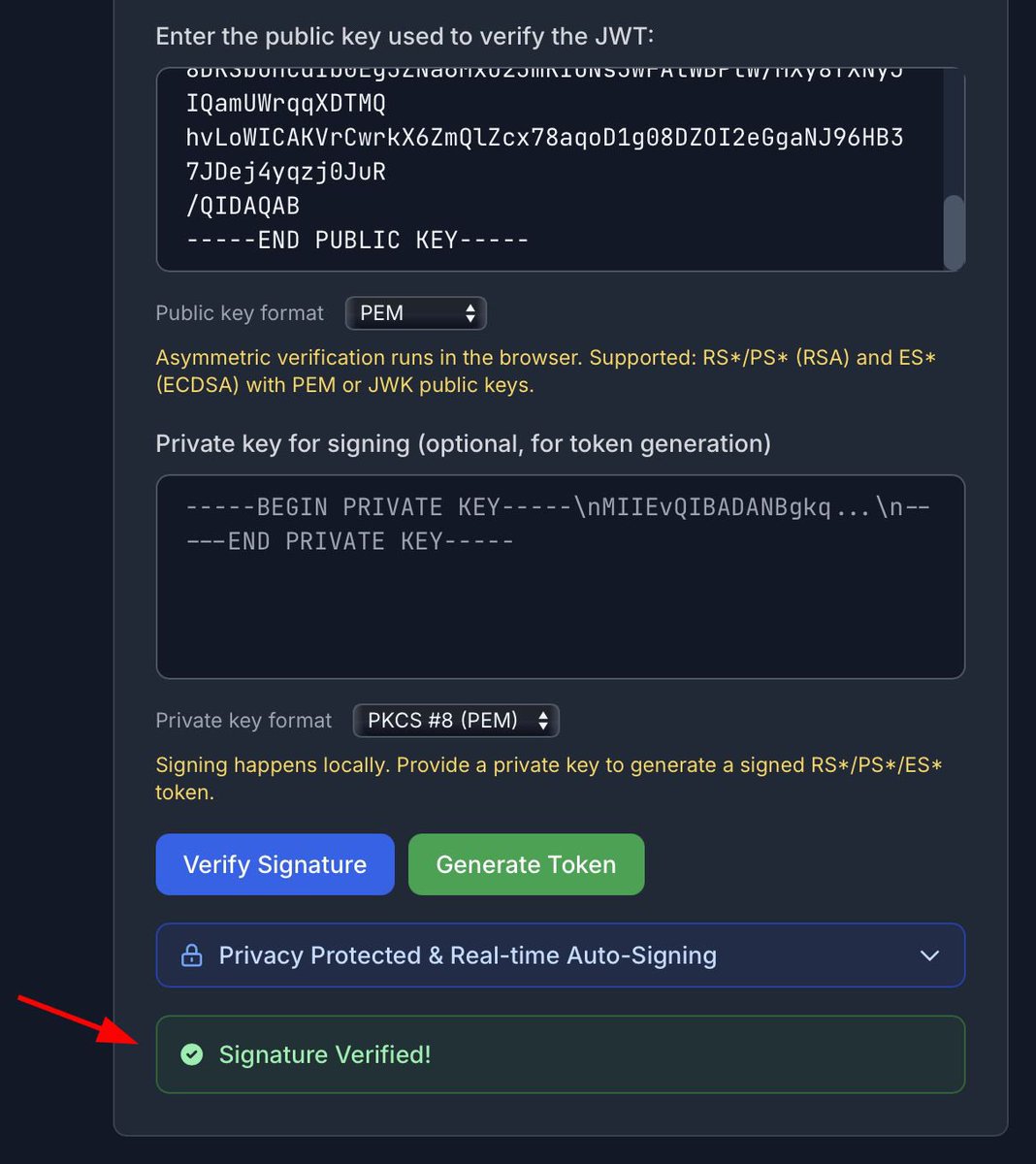
Won't be bad if xjwt.io includes other format for those working with public keys or RS256 Alg, just like JWT[.]io has. Not just 256 bit Been trying to verify this token signature n manipulate same time and it's really stressful @commando_skiipz @ExploitforgeLTD
![Dghost_Ninja's tweet image. Won't be bad if xjwt.io includes other format for those working with public keys or RS256 Alg, just like JWT[.]io has. Not just 256 bit
Been trying to verify this token signature n manipulate same time and it's really stressful @commando_skiipz @ExploitforgeLTD](https://pbs.twimg.com/media/G6HSpGFWUAAHNYv.jpg)
![Dghost_Ninja's tweet image. Won't be bad if xjwt.io includes other format for those working with public keys or RS256 Alg, just like JWT[.]io has. Not just 256 bit
Been trying to verify this token signature n manipulate same time and it's really stressful @commando_skiipz @ExploitforgeLTD](https://pbs.twimg.com/media/G6HSpHRW0AAzrFu.jpg)
![Dghost_Ninja's tweet image. Won't be bad if xjwt.io includes other format for those working with public keys or RS256 Alg, just like JWT[.]io has. Not just 256 bit
Been trying to verify this token signature n manipulate same time and it's really stressful @commando_skiipz @ExploitforgeLTD](https://pbs.twimg.com/media/G6HSpWaWEAAJ2-B.jpg)
JWTs: Digitally signed tokens carrying user claims. Stateless and easy to authenticate. Pros: Highly scalable. Cons: Hard to revoke and risky with long expiration.
Something went wrong.
Something went wrong.
United States Trends
- 1. Good Saturday 21.7K posts
- 2. #FELIX_MAMAAwards2025 17.5K posts
- 3. #JimmySeaFanconD1 426K posts
- 4. Texas 156K posts
- 5. #BINIFIED 192K posts
- 6. 3-8 Florida 2,350 posts
- 7. hanbin 25.4K posts
- 8. #MakeOffer 21.4K posts
- 9. #BuyNow 21.6K posts
- 10. Domain For Sale 21.7K posts
- 11. Sark 5,434 posts
- 12. Katie Miller 3,264 posts
- 13. Jeff Sims 1,737 posts
- 14. Aggies 9,553 posts
- 15. Reaves 21.5K posts
- 16. Arch 25.2K posts
- 17. Georgia 49.2K posts
- 18. Sylus 105K posts
- 19. Check Analyze 1,965 posts
- 20. Token Signal 7,013 posts