#neuralhash 搜尋結果
#NeuralHash has a new name, away from the controversial Apple one #NeuralHash... ... introducing #ChainCortex, the Thinking Chain, Infinite Compute Zero Waste...

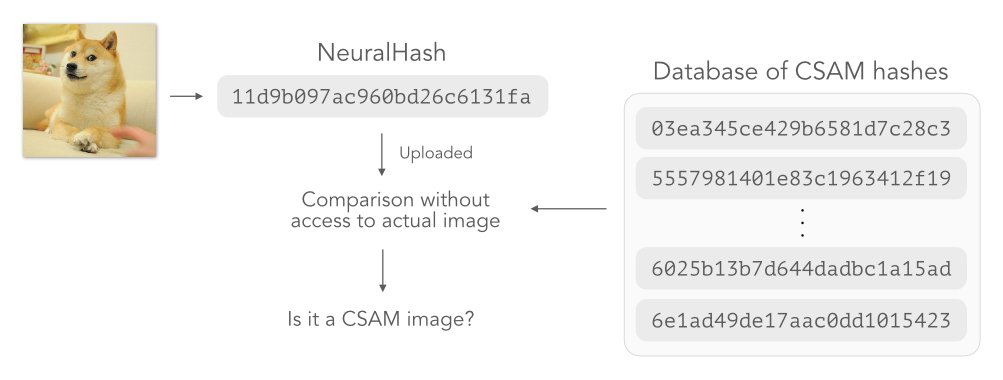
Together with Dominik Hintersdorf, Daniel Neider, and @kerstingAIML, we published our paper "Learning to Break Deep Perceptual Hashing: The Use Case NeuralHash" in which we show the technical drawbacks of #neuralhash from a #MachineLearning perspective. arxiv.org/abs/2111.06628
Will be posting a different name and logo to go with in the coming days perhaps its time to retire the name we've been calling ourselves during in the last 8 months and post it online, using it as our public face #NeuralHash has a new name
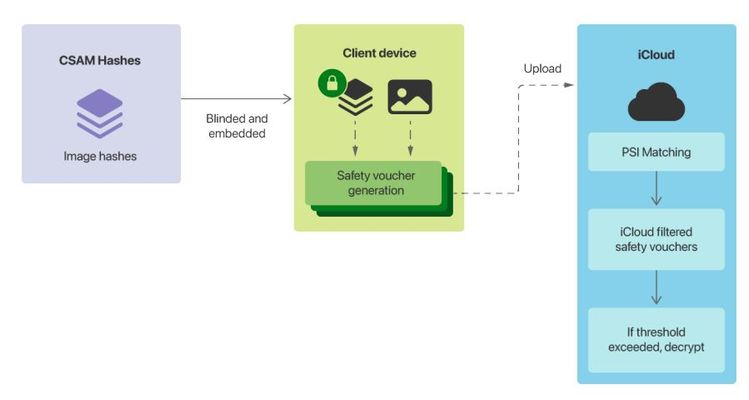
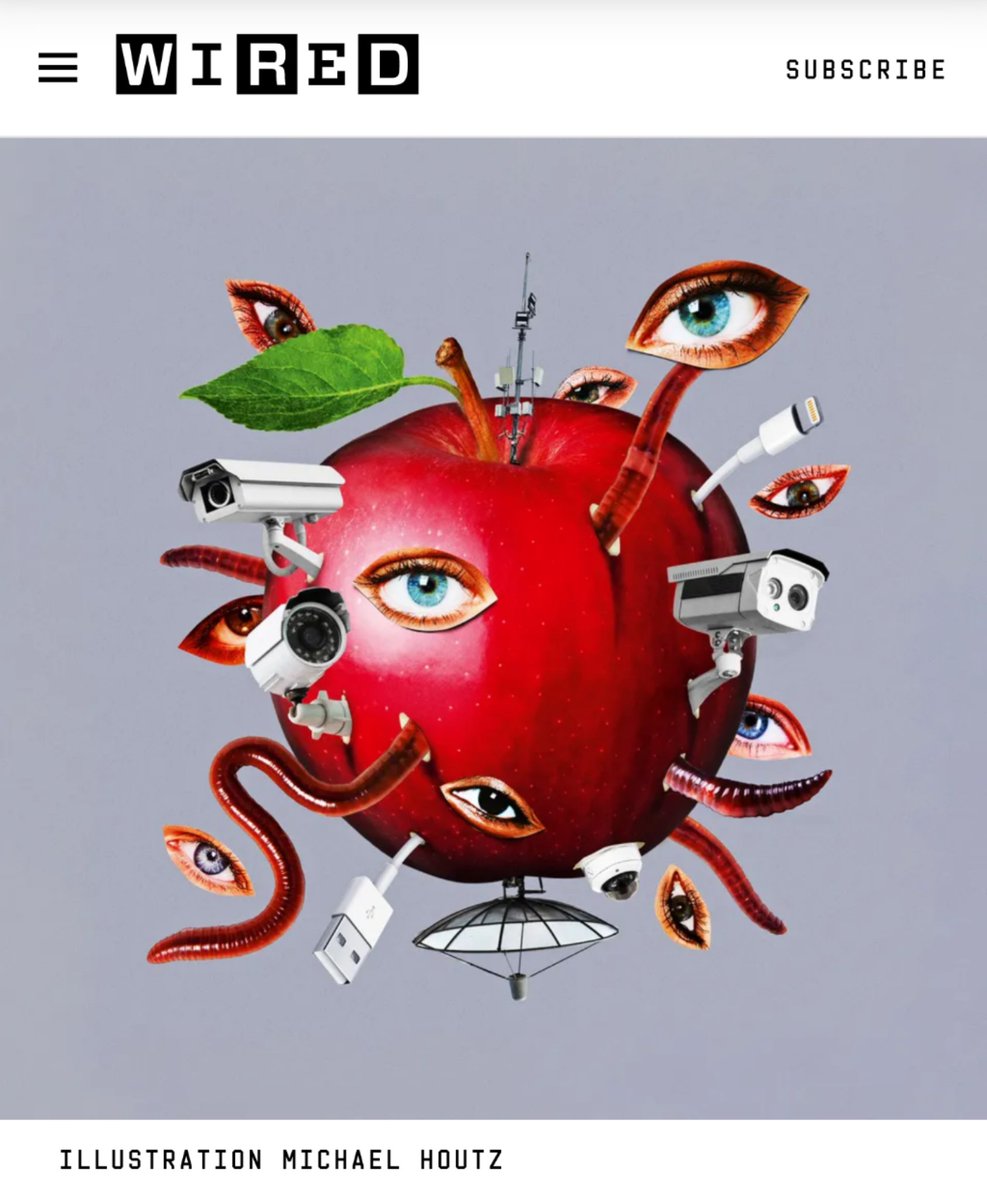
The road to hell is paved with good intentions, they say... Apple intends to install software on American iPhones to scan for child abuse imagery, ft.com/content/14440f… See also technical summary: apple.com/child-safety/p… #CSAM #NeuralHash #iCloud #safety #privacy #security
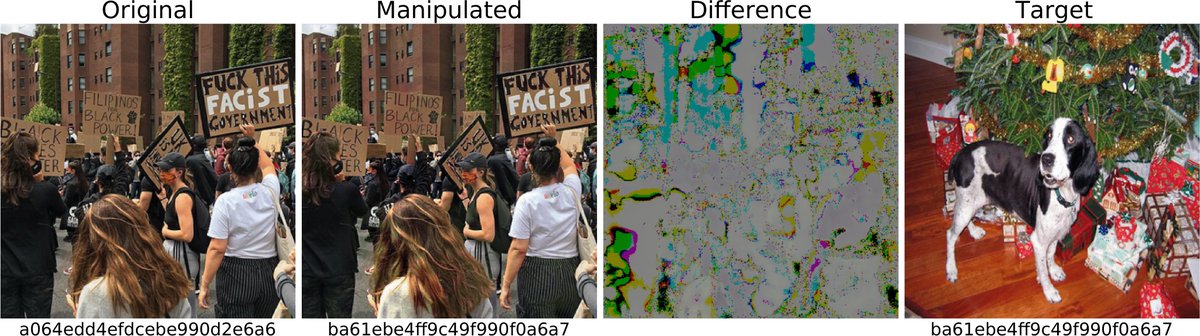
It looks like there is the first collision found in Apple CSAM Detection (NeuralHash). Both images generate the same hash. This is not good. #apple #csam #neuralhash #collision github.com/AsuharietYgvar… (via @FuzzySec)

Reddit user reverse-engineers what they believe is Apple's solution to flag child sex abuse #Apple #CSAM #NeuralHash neowin.net/news/reddit-us…

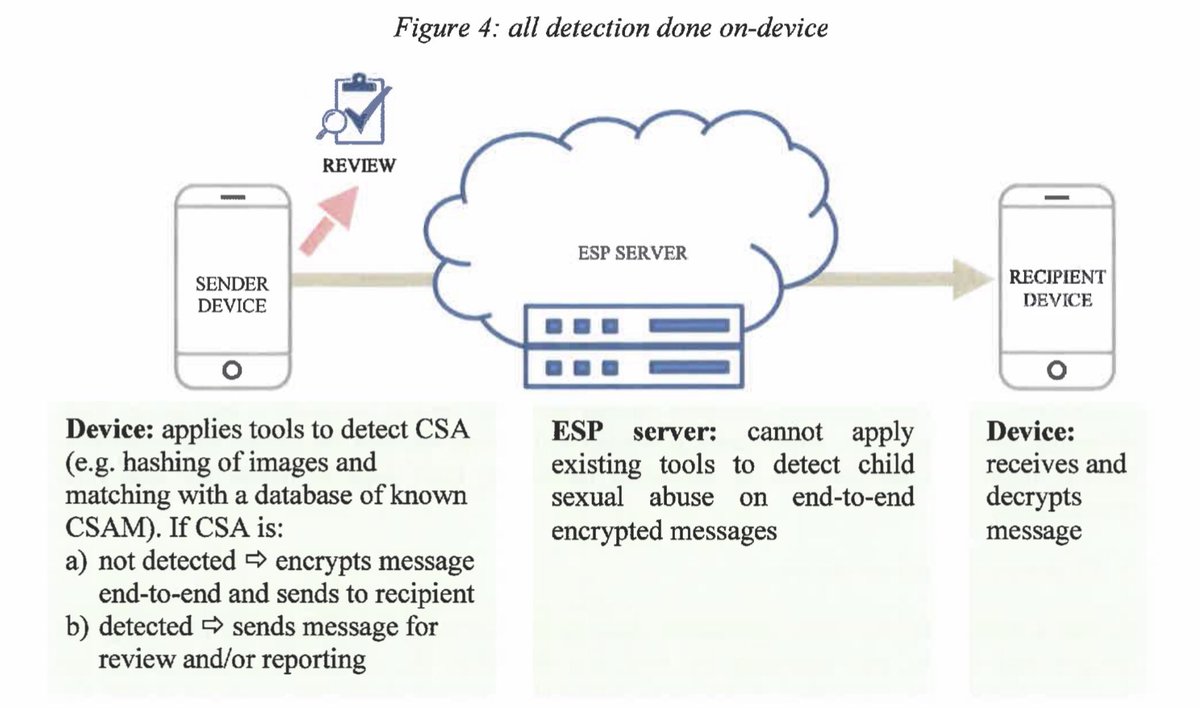
Apple‘s neue Funktion zum Überwachen von Fotos auf dem iPhone bzw. iCloud könnte auch in Europa eingeführt werden. #NeuralHash und #NeuralMatch ähneln sehr einer Methode, die die EU-Kommission vor einem Jahr zum Umgehen von #E2EE-Verschlüsselung aufführte: politico.eu/wp-content/upl…
💥 Apple dice que la tecnología NeuralHash afectada por las 'colisiones de hash' no es la versión utilizada para la detección de CSAM #tecnocodeplus #apple #neuralhash #csam

RT Apple’s NeuralHash — How it works and ways to break it dlvr.it/S6JSmP #neuralhash #hacking #csam #apple #ai
Why does Hany Farid, Professor @BerkeleyISchool think that @Apple's #NeuralHash Child Safety proposals aren't pleasing anyone at all? Find out in our latest #SafeguardingPodcast: safetonetfoundation.libsyn.com

"@Apple has been playing two games at once – protecting #privacy & developing #surveillance tools – while only acknowledging the former" - @CarissaVeliz #NeuralHash exposed the ruse; any 'privacy' you get is only that which aligns with its own interests. wired.co.uk/article/apple-…
Seems the name #NeuralHash refers to a technology developed by Apple in 2021, quite different from what we do here...
We're naming it #NeuralHash, and development is already underway.
We've hit the ground running with our Proof-of-Compute mining concept for crypto mining—a revolutionary approach designed to replace wasteful, arbitrary hash calculations with purposeful compute, starting with resource-intensive AI tasks like training and rendering.
Ende der Ende-zu-Ende-Verschlüsselung bei iPhones: Apple macht die Telefone mit #NeuralHash zur Selbst-Abhörstation, die (trotz eigentlich sicherer iCloud) entweder Polizei oder (wenn Kind iMessage benutzt) Eltern benachrichtigt. #E2EE #CSAM #Cryptowars apple.com/child-safety/
@runasand in brief @Apple erodes privacy & enables surveillance using #neuralhash slippery slope bc “[…] If the user’s <data/activity> hash matches a <given government/3rd-party hash set>, then […] the server […] can […] successfully decrypt the associated payload data.”
#NeuralHash has a new name, away from the controversial Apple one #NeuralHash... ... introducing #ChainCortex, the Thinking Chain, Infinite Compute Zero Waste...

#NeuralHash has a new name, away from the controversial Apple one #NeuralHash... ... introducing #ChainCortex, the Thinking Chain, Infinite Compute Zero Waste...

Will be posting a different name and logo to go with in the coming days perhaps its time to retire the name we've been calling ourselves during in the last 8 months and post it online, using it as our public face #NeuralHash has a new name
Seems the name #NeuralHash refers to a technology developed by Apple in 2021, quite different from what we do here...
We're naming it #NeuralHash, and development is already underway.
We've hit the ground running with our Proof-of-Compute mining concept for crypto mining—a revolutionary approach designed to replace wasteful, arbitrary hash calculations with purposeful compute, starting with resource-intensive AI tasks like training and rendering.
Tout ça pour un système qui de toute façon ne marche pas, face à un utilisateur malicieux. #NeuralHash
Apple Now Has a Backdoor to Bypass Encryption! v/ Rob Braxman #NeuralHash #icloud #Privacy End-to-End-Encryption. odysee.com/@RobBraxmanTec…
Here's a #ReadyMadeTwitterSearch for tweets about: Apple: CSAM Surveillance Proposal — including #NeuralHash and #NeuralMatch and #ClientSideScanning …with links & more information at: github.com/alecmuffett/re…
Great thread by my PhD student @shubhamjain0594 showing how deep perceptual hashing algorithms such as #NeuralHash are vulnerable to avoidance detection attacks 🕵️. This is crucial research to evaluate whether client-side scanning systems will work in practice❓#OnlineSafetyBill
Our USENIX Security 2022 paper (w/ @AnaMariaCretu5 @yvesalexandre) showed client-side scanning systems for illegal content detection to be vulnerable to evasion attacks. With Avril Wong, we extend the attack to SOTA deep perceptual hashing algorithms cpg.doc.ic.ac.uk/blog/deephash-…. 🧵
Schwachstellen bei Client-Side Scanning und Deep Perceptual Hashing: Ansätze wie Apples #NeuralHash können leicht manipuliert und missbraucht werden, wie die Arbeit von @LukasStruppek, @D0miH, @kerstingAIML und Daniel Neider (@mpi_sws) zeigt. Mehr dazu 👇
Doktoranden am @CS_TUDarmstadt finden Schwachstellen bei Client-Side-Scanning und Deep Perceptual Hashing. Das Verfahren rückte in den Fokus, als Apple mit „NeuralHash“ einen Ansatz zur Detektion von Bildmaterial im Bereich Kindesmissbrauch vorstellte tu-darmstadt.de/universitaet/a…
> Apple: CSAM Surveillance Proposal — including #NeuralHash and #NeuralMatch and #ClientSideScanning …see the latest Twitter discussion with a #ReadyMadeTwitterSearch at: github.com/alecmuffett/re…
Something went wrong.
Something went wrong.
United States Trends
- 1. Eagles 130K posts
- 2. Eagles 130K posts
- 3. Ben Johnson 22.4K posts
- 4. Marcel Reed 1,156 posts
- 5. Jalen 28.7K posts
- 6. Caleb 49K posts
- 7. Patullo 13.5K posts
- 8. Philly 28.2K posts
- 9. #BearDown 2,524 posts
- 10. Sirianni 8,513 posts
- 11. AJ Brown 6,369 posts
- 12. Lane 57.2K posts
- 13. Black Friday 537K posts
- 14. Howie 2,936 posts
- 15. #HookEm 3,482 posts
- 16. Aggies 3,467 posts
- 17. Utah State 2,172 posts
- 18. #GoDawgs 5,967 posts
- 19. Georgia Tech 5,505 posts
- 20. GOOD BETTER BEST 6,990 posts