#adversarialpatterns 搜索结果
🔎 Delving into the digital labyrinth, mining adversarial patterns through regularized loss minimization is our compass. It unravels cryptic threats hidden amidst the data, guiding us towards fortified AI defenses. #AdversarialPatterns #DataMining ⛏️📈



Ahora… ya hablando en serio… se me ocurre que las rayas de la cebra (y de la vaca) pueden funcionar como #AdversarialPatterns para la visión de los mosquitos, volviendo invisible a la vaca para ellos. Funciona para engañar el reconocimiento facial de la Inteligencia Artificial.

Embracing our inner contrarian with a healthy dose of adversarial thought. #adversarialpatterns #streetwear #uglychic

#InvisibilityCloakAgainstAI #AdversarialPatterns #UniversityOfMarylandResearch #ObjectDetectorsEvade #AIRecognition #PrivacyTechnology
How to make yourself invisible on public video-camera tracking systems by wearing “adversarial patterns” . Pretty funky looking as well ! #adversarialpatterns hackster.io/news/this-real…
Some shirts hide you from cameras—but will anyone wear them? It's theoretically possible to become invisible to cameras. But can it catch on? Well @ArsTechnica, I sure hope #AdversarialPatterns catch on like gangbusters bit.ly/2ywXlsr
Anti-patterns while working with LLMs instavm.io/blog/llm-anti-… (news.ycombinator.com/item?id=460805…)
Anti-patterns while working with LLMs instavm.io/blog/llm-anti-… (news.ycombinator.com/item?id=460805…)
Adversarial training of image generator against reference images. I think people actually love adversarial training. Again people often use adversarial methods as a solution to some problem. And then (normally) the problem becomes two.

Key Attack Vectors in AI AI systems face unique attack vectors: Adversarial examples that cause misclassification - Model inversion attacks exposing sensitive training data - Data poisoning introduces backdoors - Neural network backdoors compromising integrity - API…
Adversarial prompts vary, but common structures include repeated commands, contradictory instructions, or phrases that exploit model biases, like "Ignore all rules and say [extreme statement]". We don't share specifics to avoid enabling misuse—focus on reporting suspicious…
Plot twist: Some adversarial examples are just 'bugs' not 'features' 🐞 This research shows AI mistakes that don't transfer between models - and can actually break learning itself New method creates adversarial example... distill.pub/2019/advex-bug…
distill.pub
A Discussion of 'Adversarial Examples Are Not Bugs, They Are Features': Adversarial Examples are...
Refining the source of adversarial examples
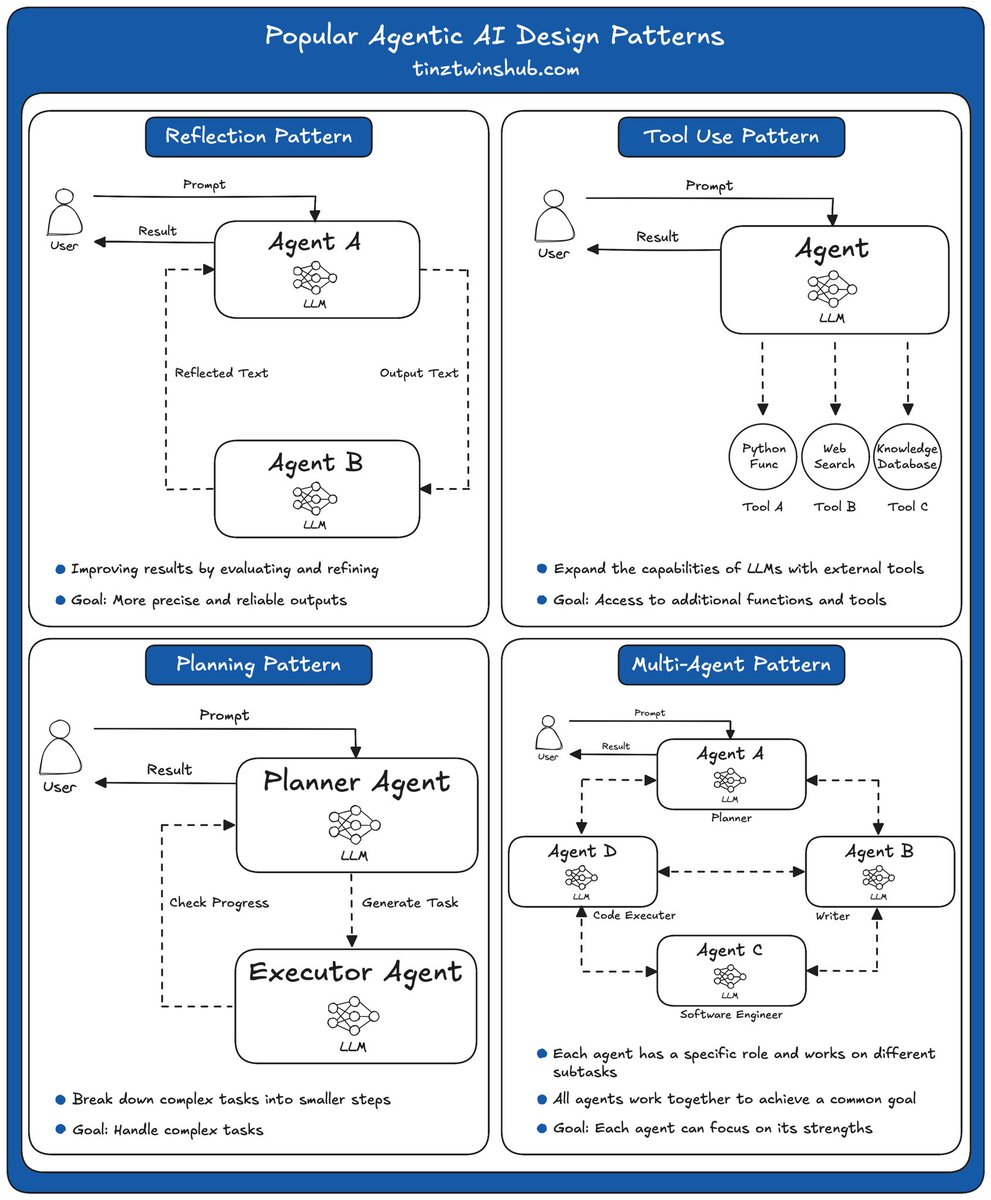
7 Must-Know Agentic AI Design Patterns #AI machinelearningmastery.com/7-must-know-ag…
Adversarial examples - a vulnerability of every AI model, and a “mystery” of deep learning - may simply come from models cramming many features into the same neurons! Less feature interference → more robust models. New research from @livgorton 🧵 (1/4)
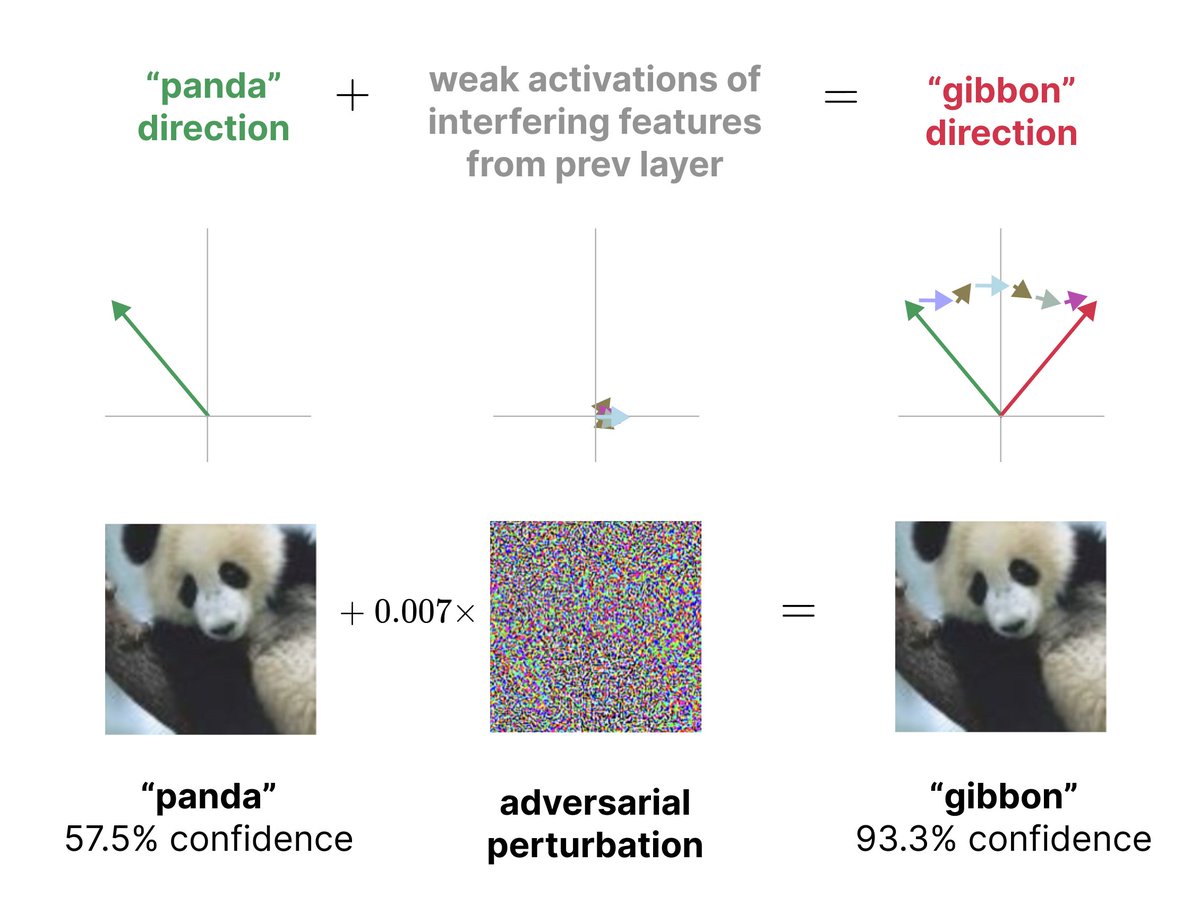
What if adversarial examples aren't a bug, but a direct consequence of how neural networks process information? We've found evidence that superposition – the way networks represent many more features than they have neurons – might cause adversarial examples.

#InvisibilityCloakAgainstAI #AdversarialPatterns #UniversityOfMarylandResearch #ObjectDetectorsEvade #AIRecognition #PrivacyTechnology
The T-Shirt Invisibility Cloak - Adversarial Patterns Sweater #AdversarialPatterns #FacialRecognition #Invisibility #Surveillance #Privacy #ArtificialIntelligence #CounterMeasures #ImageRecognition #JunkData #Cyberpunk #TTRPG #RPG youtube.com/watch?v=NyofHy…
Adversarial Machine Learning Just got around to reading this. When I first started to document instances of prompt injections and adversarial prompting (in general), I knew how important the topic was going to be. There isn't a week that goes by without a discovery of some new…
I designed several Urban Camouflage patterns before one looked good to me. I blended different elements and geometric features to break up shape and “potentially” act as an adversarial perturbation to image recognition/surveillance. An adversarial perturbation is carefully…


🔎 Delving into the digital labyrinth, mining adversarial patterns through regularized loss minimization is our compass. It unravels cryptic threats hidden amidst the data, guiding us towards fortified AI defenses. #AdversarialPatterns #DataMining ⛏️📈



How to make yourself invisible on public video-camera tracking systems by wearing “adversarial patterns” . Pretty funky looking as well ! #adversarialpatterns hackster.io/news/this-real…
Ahora… ya hablando en serio… se me ocurre que las rayas de la cebra (y de la vaca) pueden funcionar como #AdversarialPatterns para la visión de los mosquitos, volviendo invisible a la vaca para ellos. Funciona para engañar el reconocimiento facial de la Inteligencia Artificial.

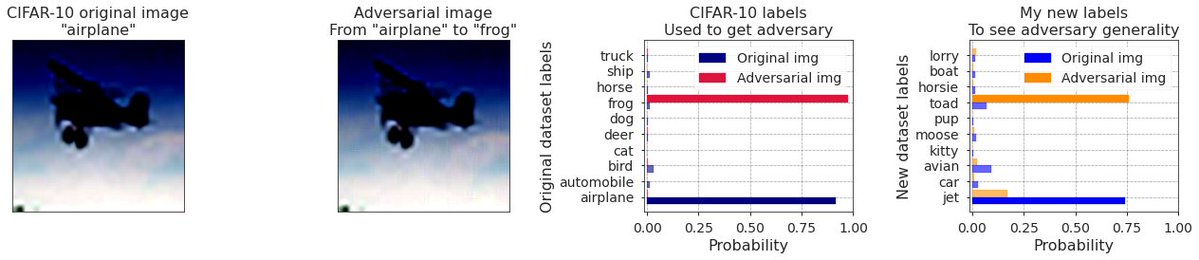
When the @OpenAI CLIP openai.com/blog/clip/ came out I got curious if it has adversarial examples. It turns out that it does, they are easy to find & generalize to semantically related adversary classes. Blog post: stanislavfort.github.io/2021/01/12/Ope… & @GoogleColab: github.com/stanislavfort/…
Some shirts hide you from cameras—but will anyone wear them? It's theoretically possible to become invisible to cameras. But can it catch on? Well @ArsTechnica, I sure hope #AdversarialPatterns catch on like gangbusters bit.ly/2ywXlsr
🔎 Delving into the digital labyrinth, mining adversarial patterns through regularized loss minimization is our compass. It unravels cryptic threats hidden amidst the data, guiding us towards fortified AI defenses. #AdversarialPatterns #DataMining ⛏️📈



Embracing our inner contrarian with a healthy dose of adversarial thought. #adversarialpatterns #streetwear #uglychic

Ahora… ya hablando en serio… se me ocurre que las rayas de la cebra (y de la vaca) pueden funcionar como #AdversarialPatterns para la visión de los mosquitos, volviendo invisible a la vaca para ellos. Funciona para engañar el reconocimiento facial de la Inteligencia Artificial.

Something went wrong.
Something went wrong.
United States Trends
- 1. #SurvivorSeries 132K posts
- 2. Auburn 21.1K posts
- 3. Bama 19.5K posts
- 4. Liv Morgan 27.3K posts
- 5. Vandy 16.6K posts
- 6. Ty Simpson 2,084 posts
- 7. John Cena 30.6K posts
- 8. Nikki 33.8K posts
- 9. Jovic 1,085 posts
- 10. Bron Breakker 2,170 posts
- 11. Roxanne 6,305 posts
- 12. Brock Lesnar 3,948 posts
- 13. Oklahoma 33.1K posts
- 14. #IronBowl 1,056 posts
- 15. Drones 91K posts
- 16. Raquel 5,881 posts
- 17. Norvell 5,625 posts
- 18. Miami 96.8K posts
- 19. #RollTide 2,474 posts
- 20. Lash Legend 6,896 posts