Perception Point
@PerceptionPo1nt
Perception Point provides cybersecurity solutions for the modern workspace, securing email, web browsers, and SaaS apps.
你可能会喜欢
Advanced Email Security stops threats before they reach the inbox. What makes Perception Point unique? 🔹 AI + human intelligence 🔹 Static + dynamic analysis Unmatched defense for known, unknown & payload-less threats. Learn more: hubs.ly/Q02ZVXfz0
[CASE STUDY] A global food distributor faced phishing and malware threats bypassing Microsoft EOP. With Perception Point, they enhanced security and ensured peace of mind. Learn more: hubs.ly/Q02ZVY0D0
Phishing continues to be a top threat, with attackers constantly refining their tactics to bypass traditional security measures. We break down the most common types of phishing attacks & offer 6 essential defensive strategies to protect your organization: hubs.ly/Q02ZVXWf0

“Decoding BEC in the Age of ChatGPT” is your guide to understanding and preventing business email compromise attacks. Download the whitepaper to learn more: hubs.la/Q02ZVXHk0 #LLM #EmailSecurity #Cyberattack #AI #Cybersecurity
Phishing attacks using URL rewriting continue to rise. Attackers exploit SEGs and rewriting services to bypass scans, spread links, and hide intent with “double rewrite attacks.” Even protected links might not be safe. Read more: hubs.la/Q02ZGq8N0 H/T @SCMagazine
This Thanksgiving, we’re grateful for our incredible team, partners, and customers who make everything we do possible. Wishing you all a safe and happy holiday! 🦃
This Thanksgiving, get The Definitive Guide to Email Security Platforms (ESPs)! 🦃 Learn how to combat BEC, Quishing, and 2-step Phishing, evaluate ESP features, and empower employees to defend your modern workspace. Download now: hubs.la/Q02ZGwZQ0
Advanced Email Security stops threats before they reach the inbox. What makes Perception Point unique? 🔹 AI + human intelligence 🔹 Static + dynamic analysis Unmatched defense for known, unknown & payload-less threats. Learn more: hubs.la/Q02ZBc8T0
Join us on Dec 4, 2024, at 10 AM PST for a webinar on Decoding Business Email Compromise (BEC) with Adam Fisher. Learn how to spot and stop advanced BEC attacks. Register now: hubs.la/Q02ZwW4R0

Email is the top attack vector. Perception Point stops threats with AI-powered detection, dynamic scanning & 24/7 response. Learn more: hubs.la/Q02ZjdQt0
Parlez-vous français? Habla español? Sprechen Sie Deutsch? We’re excited to share that our homepage is now available in French, Spanish, and German! Head on over to our homepage and choose your preferred language: hubs.la/Q02ZgrFf0
Vendor Email Compromise (VEC) stands out as one of the most insidious & challenging threats to detect and prevent. Deep dive into this growing threat, revealing how cybercriminals exploit trusted relationships between businesses & their vendors: hubs.la/Q02Z5KB60
You’re Invited: Attackers Exploit Eventbrite We uncovered how phishing campaigns abused Eventbrite’s legit invite system to target industries like banking, airlines, & energy. Exploiting trust in platforms makes these attacks harder to detect. Learn more: hubs.la/Q02Z1tG-0

Last week, we focused on health & wellness with functional training by Gal Ashkelon, Pilates with Tal Bar, and a "Getting Things Done" session by CTO Tal Zamir. A day to recharge body & mind—because a healthy team is a strong team! 💪💪



Check out GPThreat Hunter™ in action! It delivers AI-generated summaries and clear verdicts for ambiguous threats, like phishing and BEC, while autonomously securing your system. 🎥
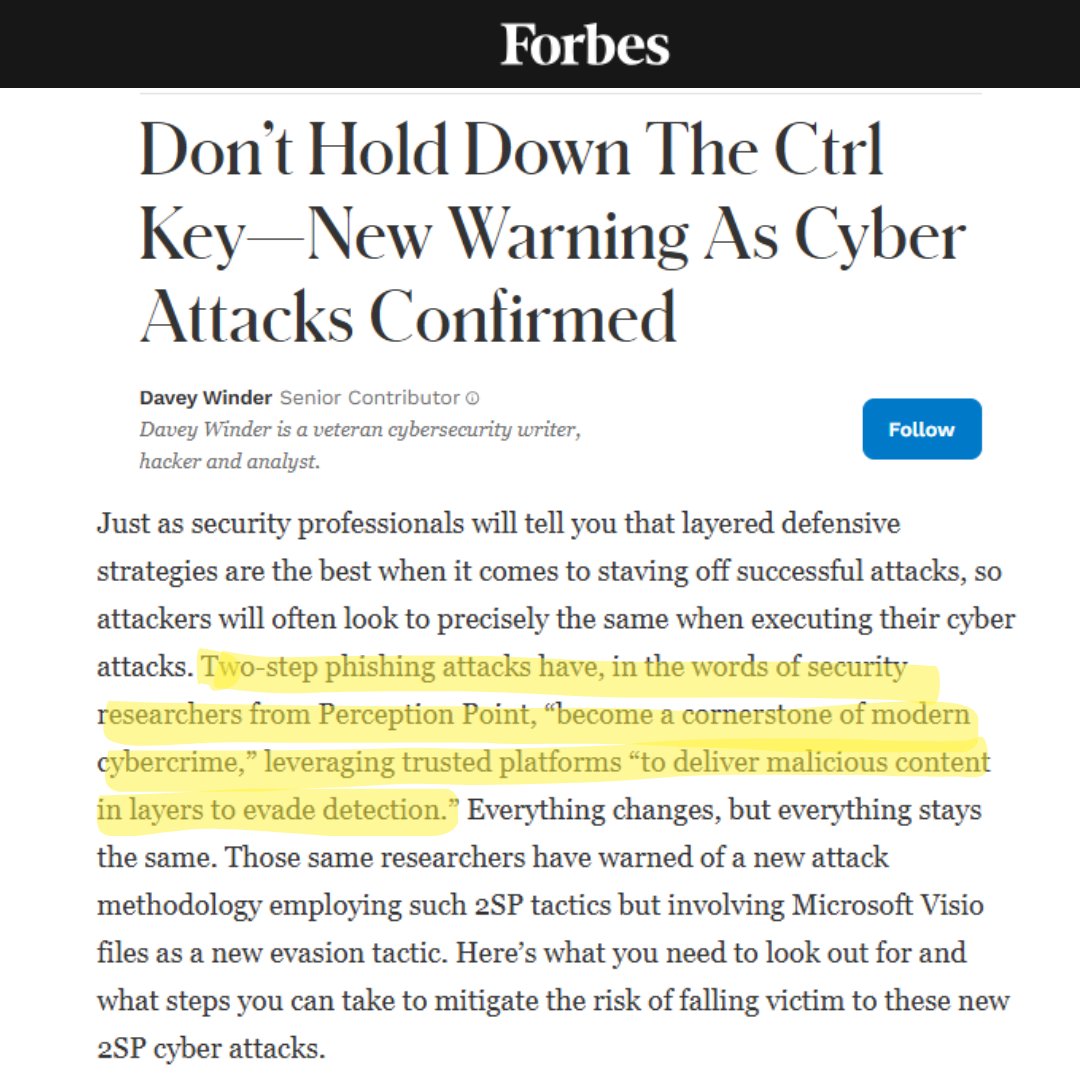
New article by @Forbes @happygeek spotlighting how cybercriminals are leveraging Visio (.vsdx) files in 2-step phishing attacks, bypassing traditional detection methods, exploiting trusted platforms to steal credentials & compromise organizations: hubs.la/Q02Yv6bJ0
BEC in 2024: Still phishing, just better dressed. 🎣 BEC attacks rose by *42%* in H1 2024. Is tech, human behavior, or something else driving this evolution? Share your thoughts! For more insights, check out our H1 2024 report: hubs.la/Q02YszyZ0

Red Bull enhanced its Microsoft EOP setup by deploying Perception Point’s Advanced Email Security. Within a 3-month period, Red Bull saw over a 65% reduction in critical events detected by their EDR: hubs.la/Q02Y2kQk0
Recent research by Perception Point in @InfosecurityMag @a_mascellino: a rise in 2-step phishing attacks targeting 100s of org that use Microsoft Visio (.vsdx) files hosted on SharePoint to bypass traditional security measures & deceive users: hubs.la/Q02Y25fy0

The top challenges orgs facing protecting today’s modern workspace: 🔹Expanded attack surfaces from remote work 🔹AI-driven, hyper-targeted phishing 🔹Outdated security solutions 🔹Complexity for security teams Watch the webinar to learn more: hubs.la/Q02Y1-qX0
United States 趋势
- 1. Panthers 30.8K posts
- 2. Rams 23.1K posts
- 3. Colts 24.4K posts
- 4. Browns 38K posts
- 5. #KeepPounding 5,749 posts
- 6. Ole Miss 84.5K posts
- 7. Stafford 15.9K posts
- 8. Texans 18.5K posts
- 9. Bryce Young 7,165 posts
- 10. Puka 10.6K posts
- 11. Falcons 8,561 posts
- 12. Lane Kiffin 107K posts
- 13. Saints 19.2K posts
- 14. Dolphins 8,384 posts
- 15. Niners 3,130 posts
- 16. Forbes 16.5K posts
- 17. #FTTB 3,456 posts
- 18. Stefanski 4,757 posts
- 19. #DawgPound 4,427 posts
- 20. Pete Golding 8,160 posts
你可能会喜欢
-
 Expel
Expel
@ExpelSecurity -
 CyCognito
CyCognito
@CyCognito -
 iTolerance
iTolerance
@iTolerance_inc -
 Salt Security
Salt Security
@SaltSecurity -
 Poseidon
Poseidon
@PoseidonTPA -
 OnPay
OnPay
@onpay_payroll -
 GoLinks
GoLinks
@GoLinks -
 Pegasus Technologies
Pegasus Technologies
@PegasusTechs -
 Techstrong TV
Techstrong TV
@TechstrongTV -
 AFS
AFS
@TradeWithAFS -
 Instruqt
Instruqt
@instruqt -
 Pentera
Pentera
@penterasec -
 Priority Tire
Priority Tire
@prioritytire -
 Trading.com
Trading.com
@tradingdotcom -
 Marsh McLennan Agency
Marsh McLennan Agency
@Marsh_MMA
Something went wrong.
Something went wrong.