#cybersecurity search results
⚡ This week’s #cybersecurity recap is ugly in the usual way. • Poisoned password manager CLI • Fake Teams help desks • Federal firewall backdoor • Energy wiper • Booby-trapped AI pages • Fake Authenticator extensions • and many more... Read → thehackernews.com/2026/04/weekly…
Phishing is back as the most common way attackers gain initial access, representing over a third of known cases in Q1 2026. Reviewing and updating email security and training could help reduce this risk. #Cybersecurity
Help! My @Google account ([email protected]) was hacked & deleted after being turned into a "Child Account." I've lost access to my FB & IG too. Recovery tool isn't working. Please help! @GoogleIndia @TeamYouTube @Google #GoogleAccount #Hacked #CyberSecurity #Help

📢⚠️ Private chats, photos, and phone screengrabs of celebrities and influencers exposed after a suspected stalkerware setup left a database open. Over 86K files leaked. Read: hackread.com/private-chats-… #CyberSecurity #Privacy #Stalkerware #CyberCrime #DataBreach
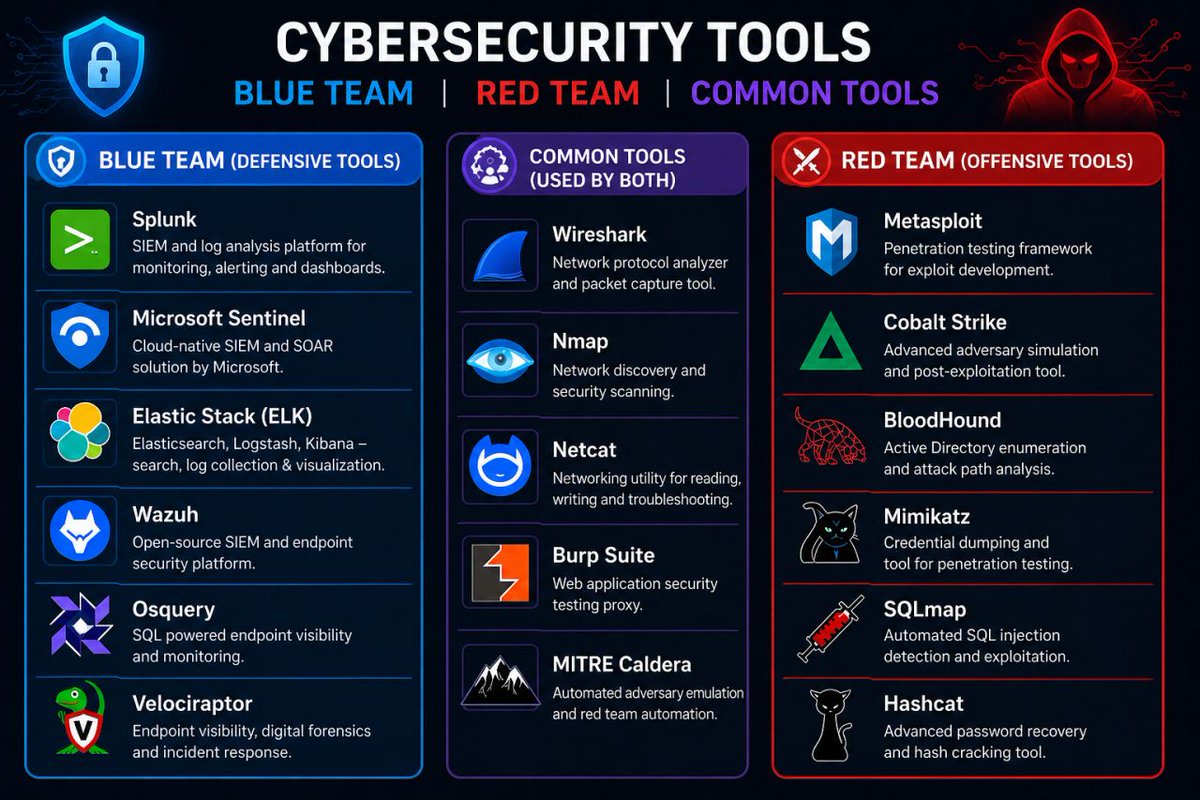
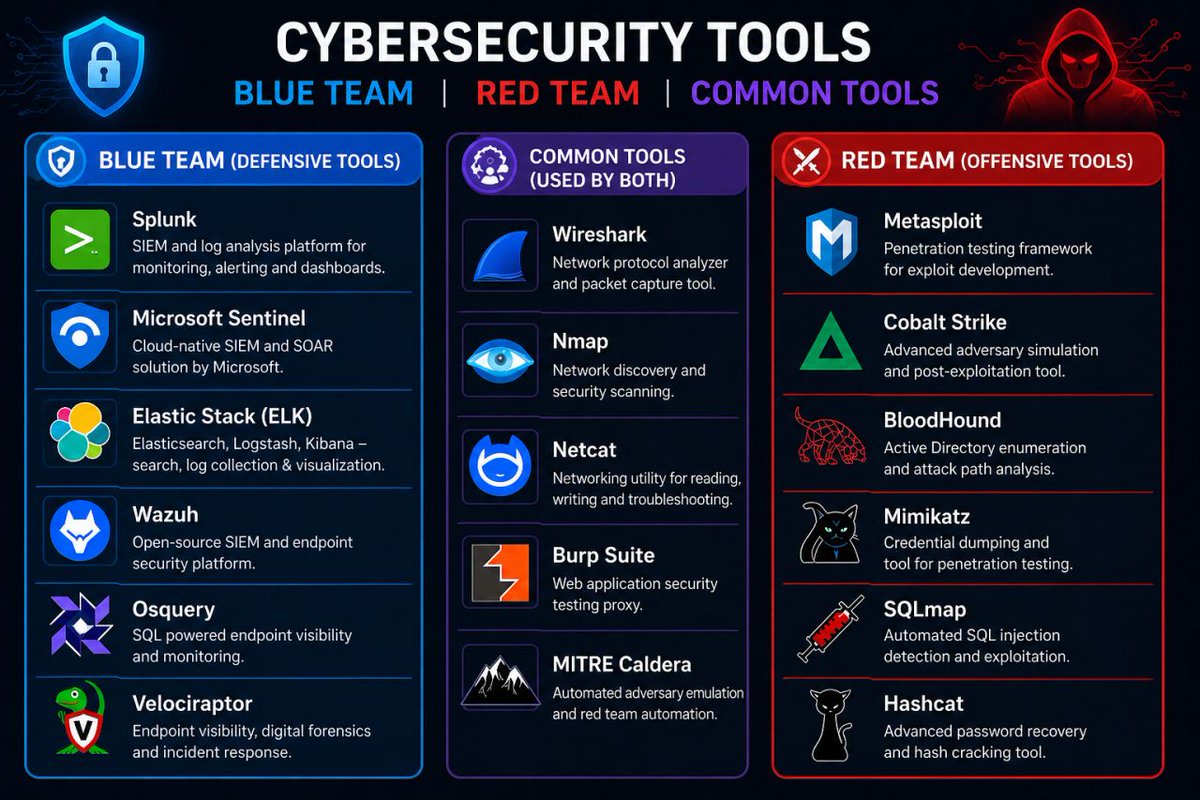
Cyber Security Tools 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
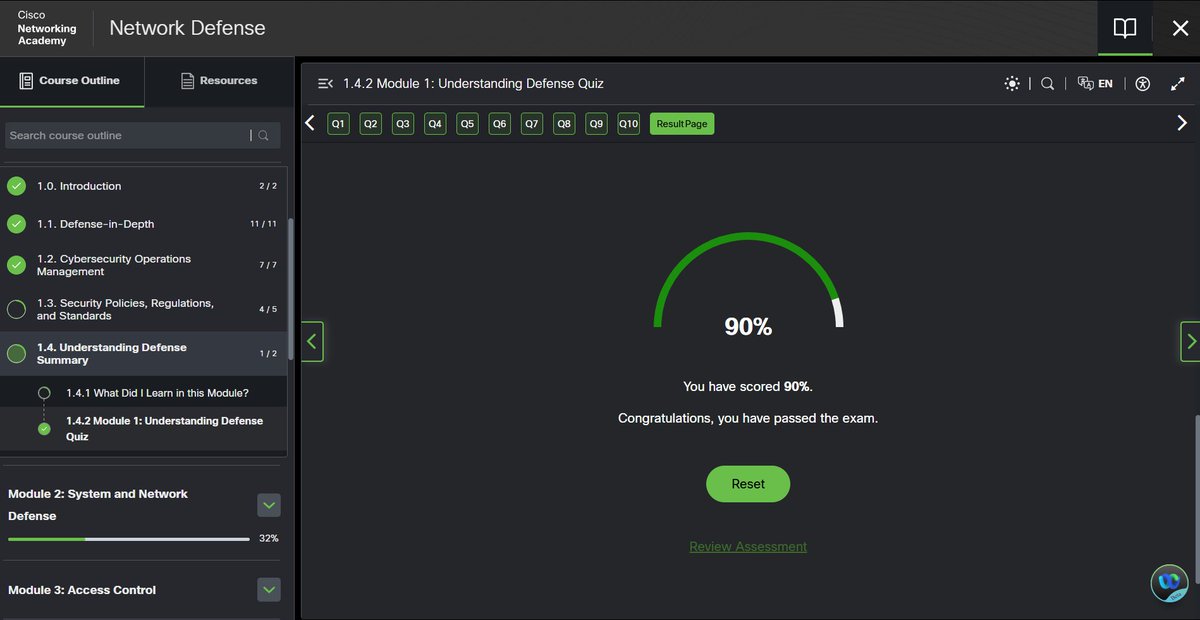
Day 99/100 Milestone reached🎉 Completed Cisco Networking Basics and finished the final domain of ISC2 CC (Security Operations) wrapped up the full course during this challenge. Biggest wins: consistency, discipline, growth. #100DaysOfCyber #CyberSecurity #Networking


📢⚠️ Researchers warn that #VECT 2.0 ransomware contains fatal flaws that permanently destroy files, making recovery impossible and rendering ransom payments useless for victims worldwide. hackread.com/paying-ransom-… #CyberSecurity #CyberCrime #Ransomware
Pentest-AI: Run Full Autonomous Pentests with One Command 🤖💀 Recon → Auth bypass → vuln discovery → exploit chaining → real PoCs → AI threat analysis → client-ready reports github.com/0xSteph/pentes… #CyberSecurity #Pentesting #RedTeam #BugBounty #AIsecurity
The most dangerous hacker never touches a keyboard. They just call, DM, or email and wait for you to hand over your info. Urgency is their weapon. Awareness is yours. #cybersecurity #cybercrooners #socialengineering




Top cybersecurity threats for e-commerce businesses: 🔒 Phishing 🛒 Ransomware 💳 Data breaches ☁️ Cloud misconfigurations ⚠️ Third-party vulnerabilities Cybersecurity is now critical for protecting revenue and customer trust. Get in touch: cloudscale365.com/get-in-touch/ #CyberSecurity

🚢 Over 80% of global trade moves by sea, yet cyber risks are rising. Applications are still open for the Maritime Cyber Lab 2026 (27–28 May, Brussels). Join global experts to strengthen maritime cyber resilience. Apply here ➡️ event.unitar.org/full-catalog/o… #CyberSecurity

Certifications matter, but practical knowledge wins. A $10k cert doesn't guarantee understanding. Even a $40 Sec+ holder can outshine with real knowledge of investigating threats and using tools like Splunk in home labs. #CyberSecurity #Certifications
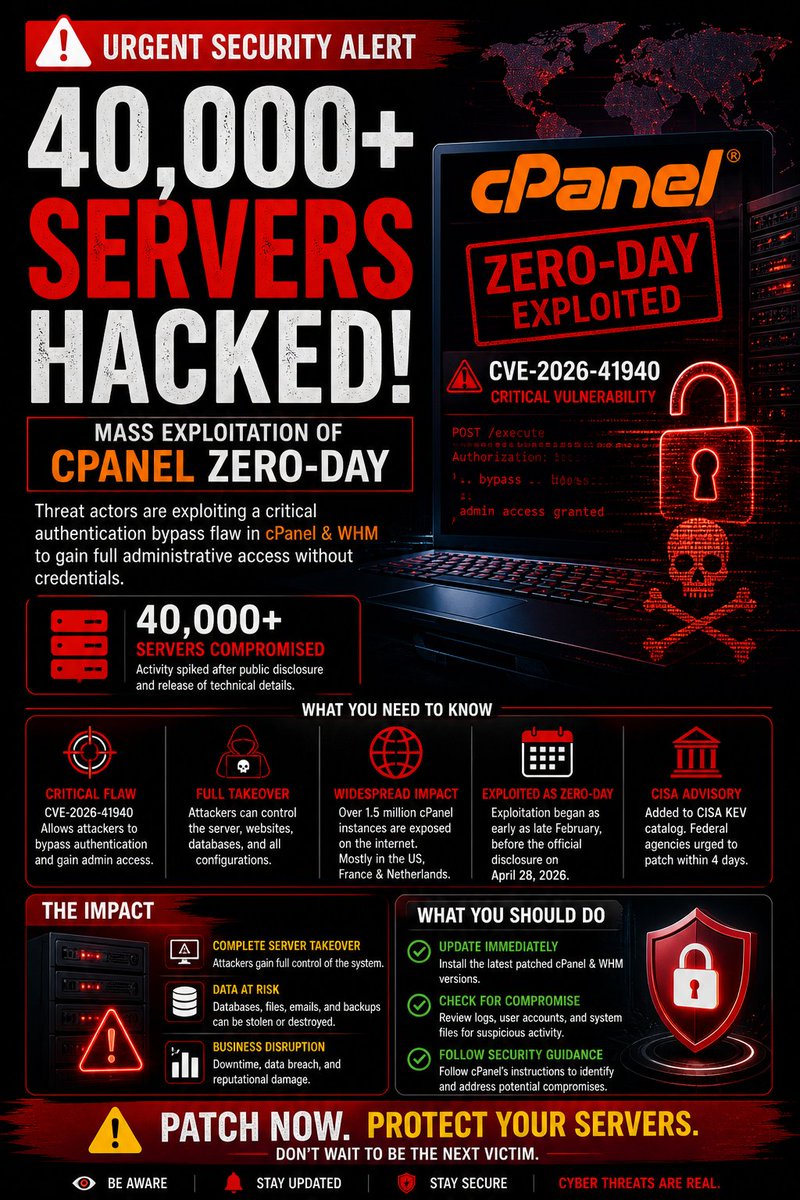
🚨 40,000+ Servers Hacked in cPanel Zero-Day Exploit! Critical flaw (CVE-2026-41940) gives attackers full admin access. Patch immediately ⚠️ #CyberSecurity #cPanel #ZeroDay #Infosec #aiz_cyber
🛑 Security breaches don’t just test your defenses—they test your recovery. Join Kaseya in an upcoming webinar to learn how to strengthen resilience with SaaS backups and BCDR to stay operational after attacks. 🎯 Register now: event.on24.com/wcc/r/5301783/… #cybersecurity #bcdr
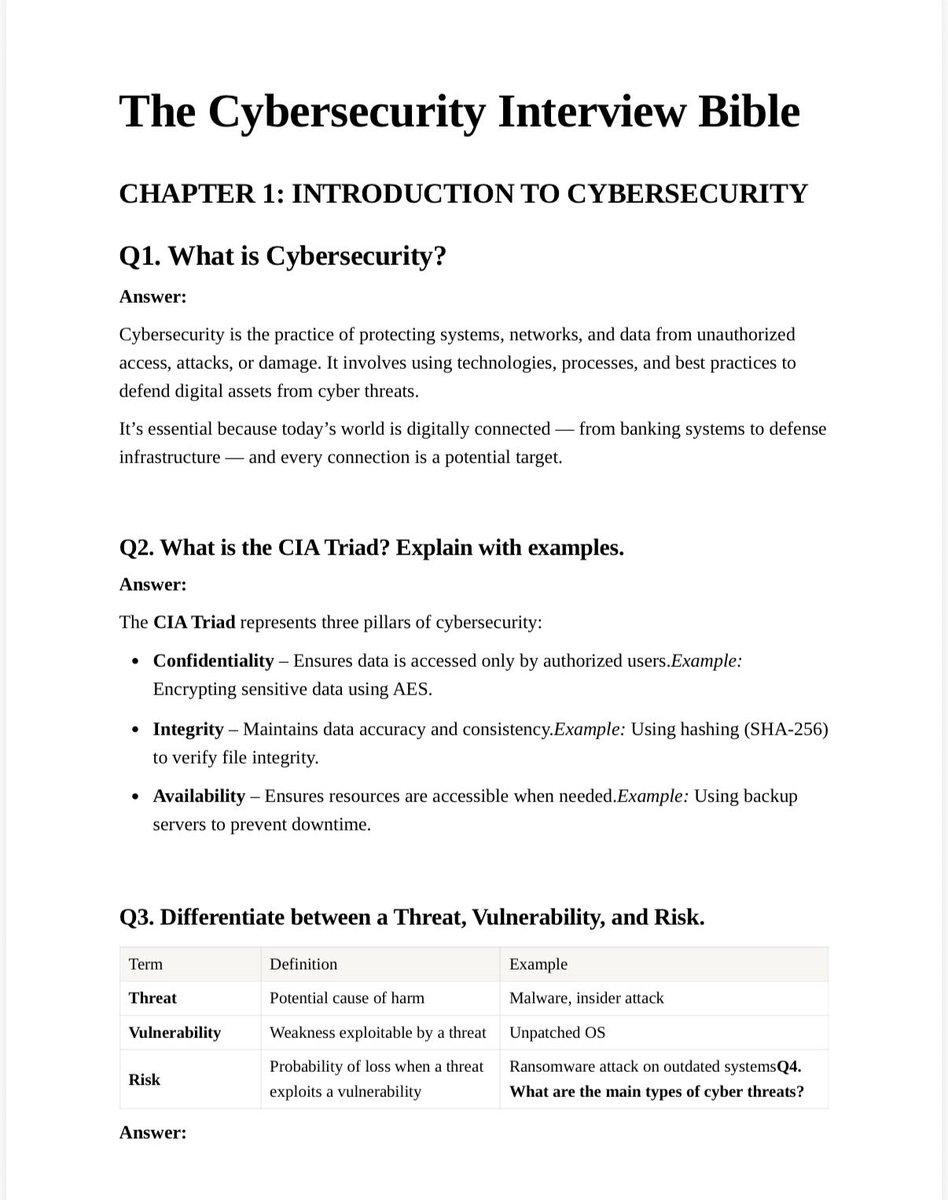
Cybersecurity fundamentals every aspiring professional should know — from CIA Triad to Risk Assessment & Security Policies. Build strong basics, crack interviews smarter. Download the PDF link below linkedin.com/posts/digitale… #CyberSecurity #InfoSec #EthicalHacking #CareerTips
Size doesn’t matter to cybercriminals; vulnerability does. This week, stay protected with smart, scalable security from ATB Tech. Reach out to us at [email protected] to get started. #ATBTech #CyberSecurity #ITSolutions

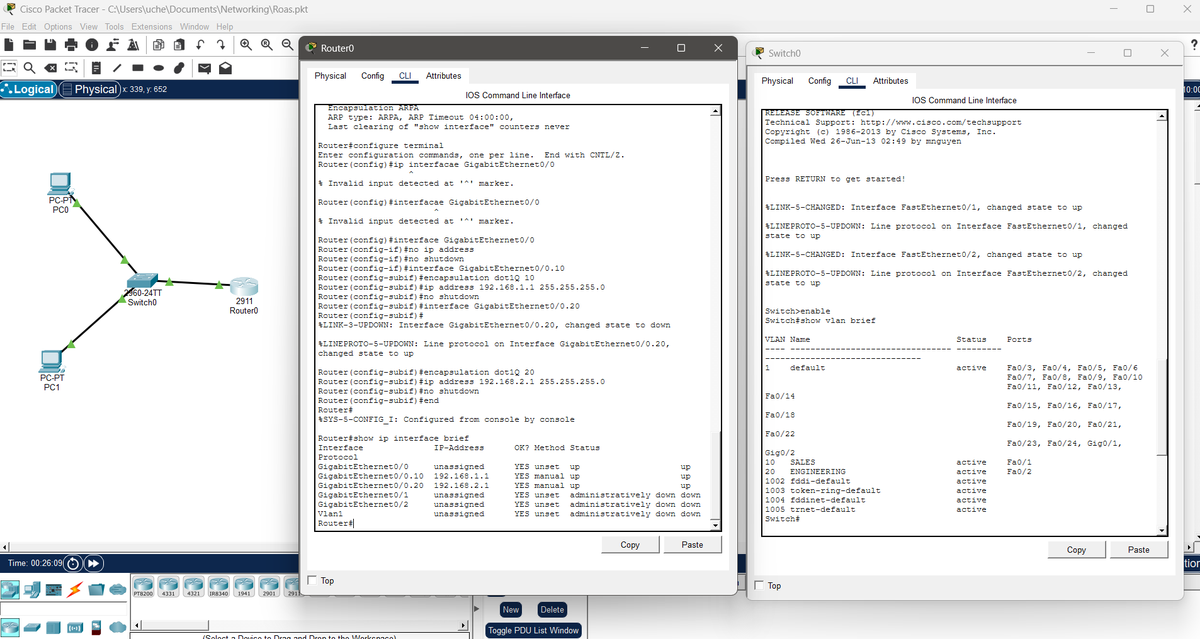
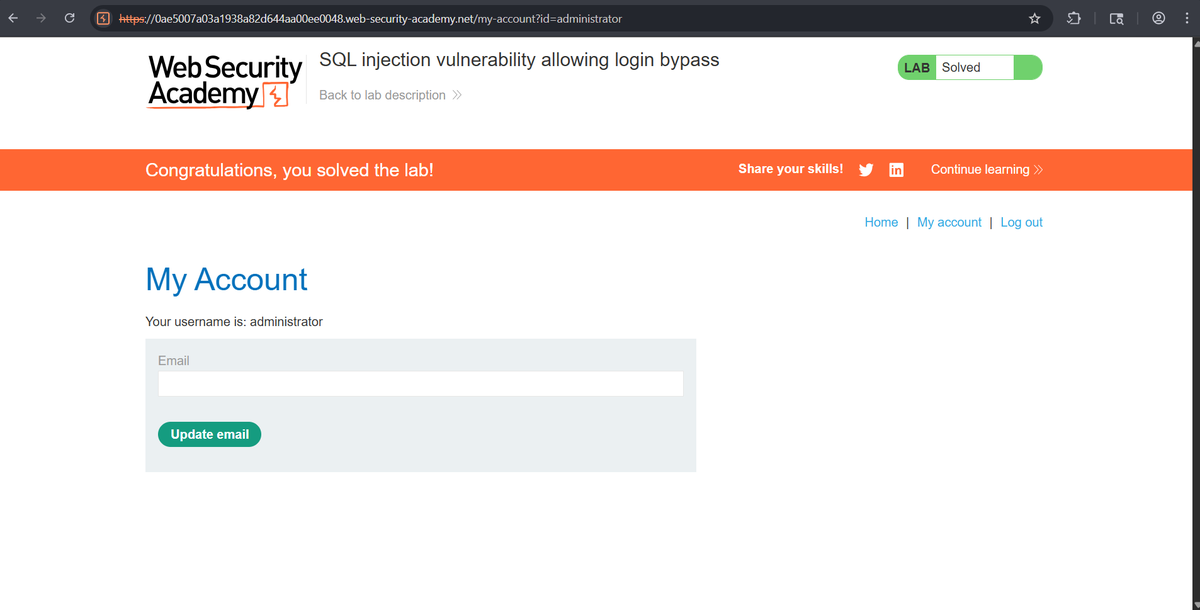
Day 3 ⚜️ - Finished the first module on Network defense in Cisco networking academy - Solved more sqli labs - Learnt how to use static files like html, css and js in django. Started working on a simple app #cybersecurity #networking #sql
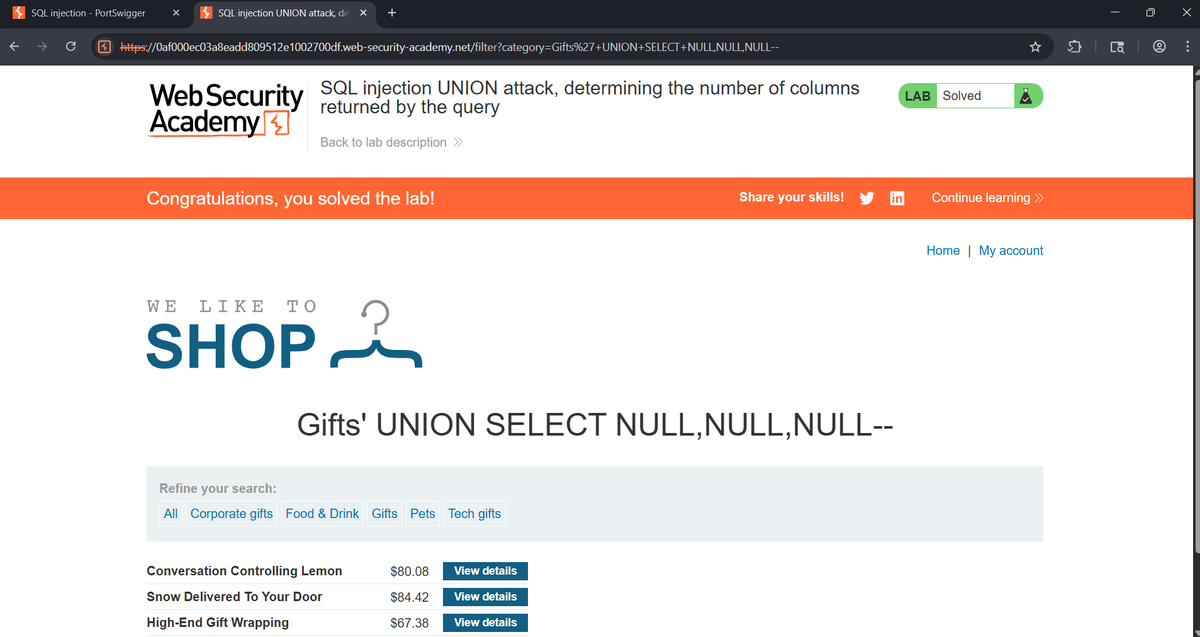
Day 2 ⚜️ - Configured a simple Router on a Stick network. This really made me understand how VLANs work better - I also resolved two labs on SQL injection to build muscle memory #cybersecurity #networking #web
Descubra como usar Subfinder e Amass para mapear subdomínios e fortalecer seu pentest antes dos atacantes 🔍💻 Veja o guia completo! 📖 uniaogeek.com.br/blog/subdomain… 👤 linkedin.com/in/mrhenrike #CyberSecurity #Programação #InfoSec
Enumerare file del web server per trovare password #hackthebox #cybersecurity #twitchitalia #snmp #networking
Another npm supply chain worm is tearing through dev environments buff.ly/XsKTV3r #infosec #cybersecurity #supplychain

🚨 No alerts doesn’t mean no cyber risk. Threats today stay hidden for weeks or months. By the time you notice, the impact may already be serious. JSECPH helps you detect risks early and act fast. Get a cybersecurity assessment today. #CyberSecurity #DataBreach #JSECPH
Security Automation Insight #89 Slot availability is just a data array with status flags. If you're a security founder scheduling pentest scoping calls or GRC assessments, this kills the back-and-forth email chain before it starts. #cybersecurity #automation #GRC

[Microsoft Security] - Breaking the code: Multi-stage ‘code of conduct’ phishing campaign leads to AiTM token compromise via microsoft.com/en-us/security… - 🦾 #Microsoft #Cybersecurity
Forward fee scams targeting energy & infrastructure companies now use AI to fabricate audit credentials, group structures and financing agreements that can evade standard review. Learn more on Bracewell’s Energy Legal Blog: hubs.ly/Q04fb1310 #cybersecurity #fraud

May the Fourth be with you, and may your security be stronger than the Dark Side! Get started with expert-driven cybersecurity. #Aseva #Cybersecurity #CloudSecurity #ManagedSecurity #MayThe4th

[CB_INTEL_ALERT] 🚨 Your SharePoint servers are exposed. We've identified a critical deserialization vuln in Microsoft SharePoint. We’ve mapped the architectural fix. Dropping the exact firewall rules in our channel now. #CyberSecurity
![CyberBoxAI's tweet image. [CB_INTEL_ALERT]
🚨 Your SharePoint servers are exposed.
We've identified a critical deserialization vuln in Microsoft SharePoint.
We’ve mapped the architectural fix. Dropping the exact firewall rules in our channel now. #CyberSecurity](https://pbs.twimg.com/media/HHfMFdOXwAAgO9y.png)
30 mil contas do Facebook hackeadas mostram como o básico ainda falha: senha fraca, repetida e sem 2FA é convite aberto. Segurança digital não é luxo, é higiene diária no Brasil conectado de hoje. #Cybersecurity #Infosec Fonte: Canaltech
Protect your UK business in 2026. Moyak Insurance Services offers tailored Cyber Liability for SMEs nationwide. We provide personal care for every client. #CyberSecurity #UKSME contact us via email at [email protected] or call 01375392087

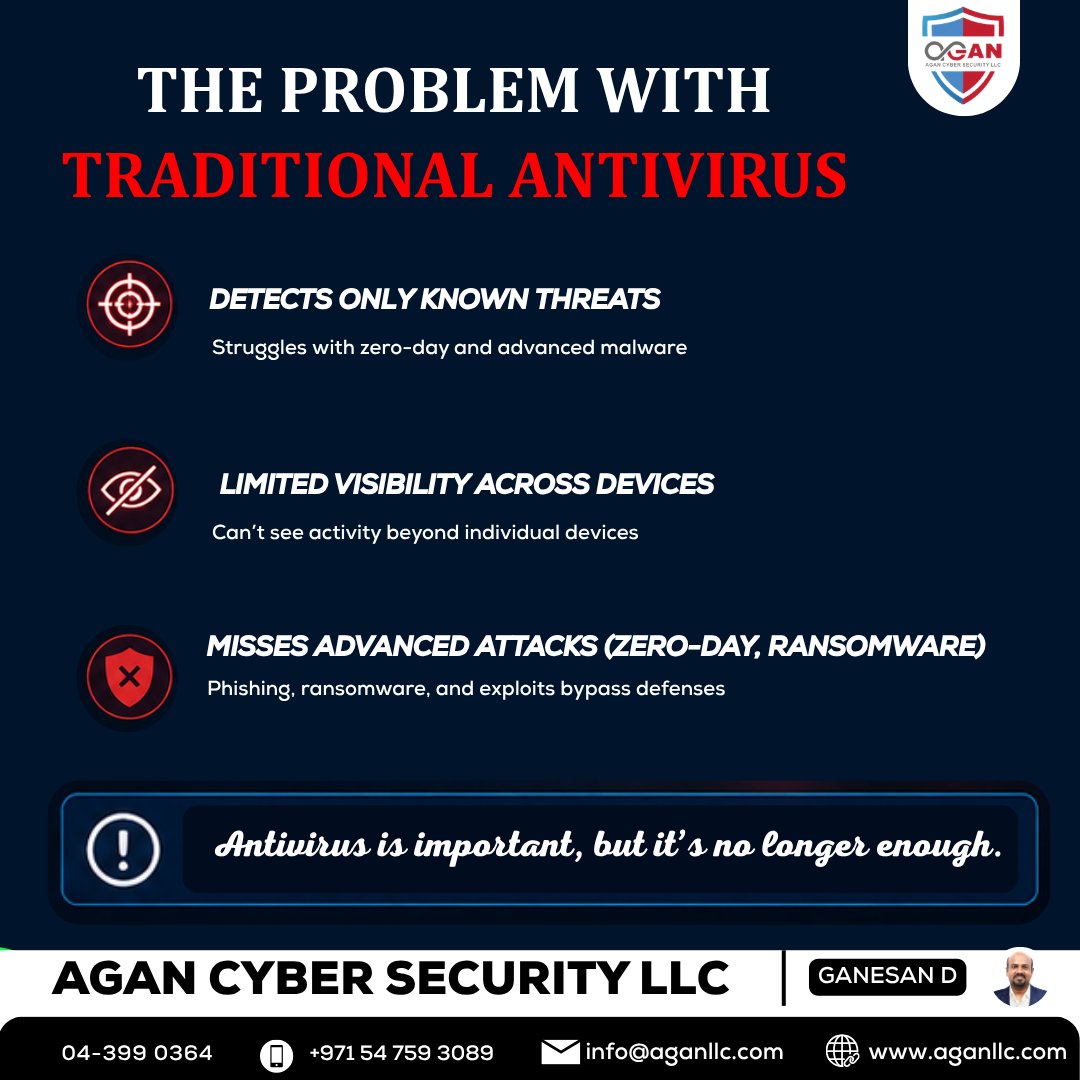
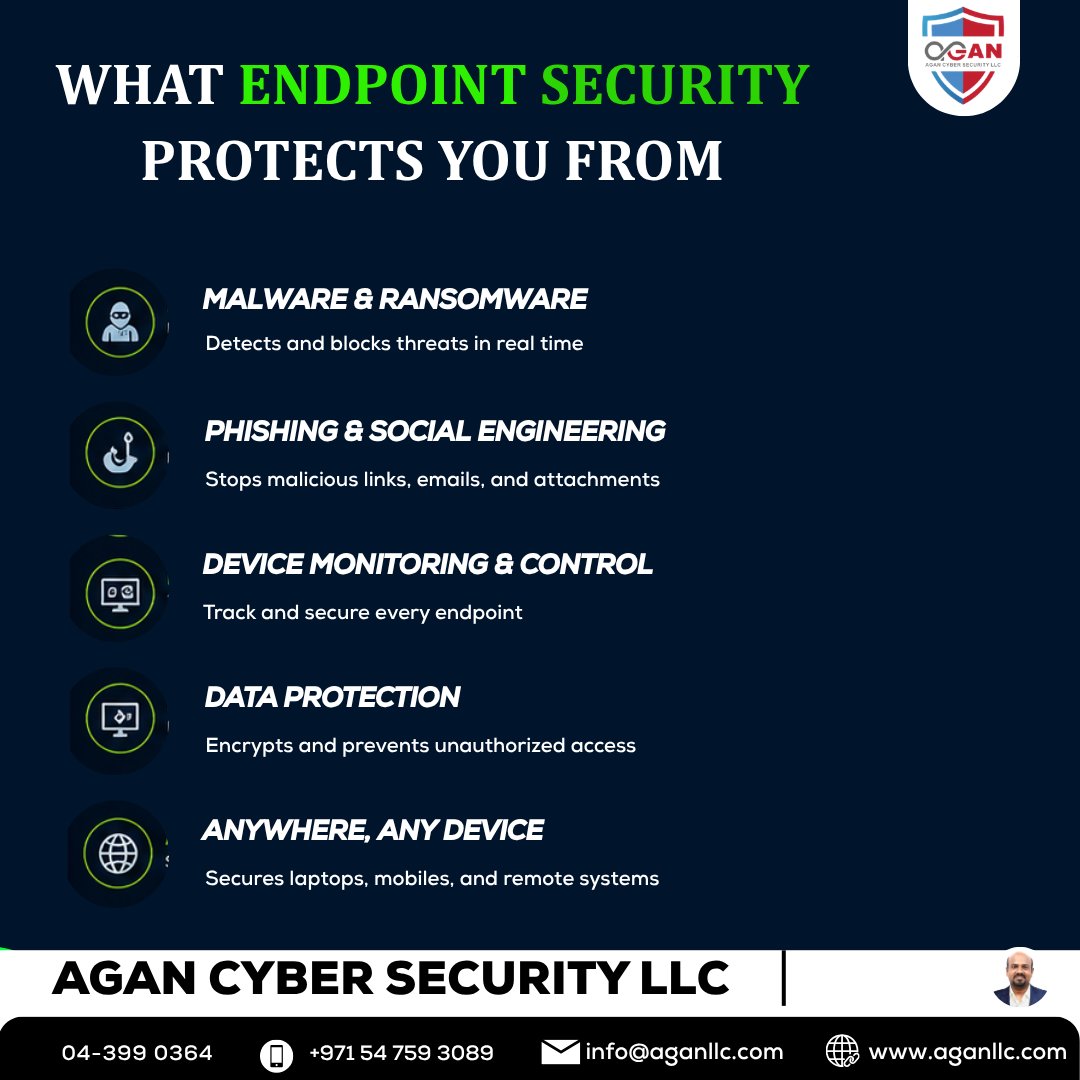
🚨 Antivirus isn’t enough—endpoint security protects all devices from advanced threats & ransomware. 🔐 👉 aganllc.com/blog/endpoint-… 📞 +971 54 759 3089 #EndpointSecurity #CyberSecurity #ITSecurity #DataProtection


Nuevas campañas de troyanos atacan cientos de billeteras de criptomonedas y aplicaciones bancarias buff.ly/pC76LUB #CyberSecurity
The Coming Wave of Large-Scale Al-Enabled Cyberattacks ift.tt/nTevAyB #Security #Cyber #Cybersecurity
#Healthcare #cybersecurity survey shows the good guys can excel in defensive measures and still not decisively defeat the #cybercriminals. ow.ly/QEGO50YUx8I
The gap between knowing how to find vulnerabilities and knowing how to communicate them responsibly is where real security researchers live. #cybersecurity #bugbounty
Preemptive security shifts the focus from detection to prevention. By reducing exposure and disrupting threats, organizations can prevent incidents before they escalate. READ: bit.ly/4e3YhXa #CanaryTrap #PreemptiveSecurity #Cybersecurity

🚀 Elevate Your Business with Shoc Networks! 🌟 Ready to tackle digital challenges? We boost your operations with all-in-one IT support, Cyber Security Insurance, and innovative solutions. Let’s thrive! 💪💼 #ShocNetworks #ITsupport #Cybersecurity #BusinessContinuity
Adoptar mejores prácticas de seguridad no siempre es complicado… pero implementarlas a escala sí lo es. 🔑Las passkeys están ganando terreno como una alternativa más segura y sencilla frente a las contraseñas tradicionales #Dinámica #Sophos #CyberSecurity #Passkeys
🔑 Passkey adoption is one of the few security initiatives where doing the right thing is also the easier thing. The real challenge comes with org-wide rollout, planning, and user adoption. Our CISO shares what worked and what didn't in this playbook: sophos.com/en-us/blog/str…

شهد الأسبوع تصاعدًا في الهجمات السيبرانية شملت استغلال ثغرة حرجة في cPanel، وبرمجية تجسس جديدة بنظام أندرويد، وثغرة تصعيد صلاحيات في نواة لينكس، إضافة إلى خلل خطير في GitHub يُتيح تنفيذ أوامر عن بُعد، مما يعكس تسارع وتيرة الاستغلال قبل صدور… #cybersecurity #الأمن_السيبراني
Cyber Security Tools 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
🚢 Over 80% of global trade moves by sea, yet cyber risks are rising. Applications are still open for the Maritime Cyber Lab 2026 (27–28 May, Brussels). Join global experts to strengthen maritime cyber resilience. Apply here ➡️ event.unitar.org/full-catalog/o… #CyberSecurity

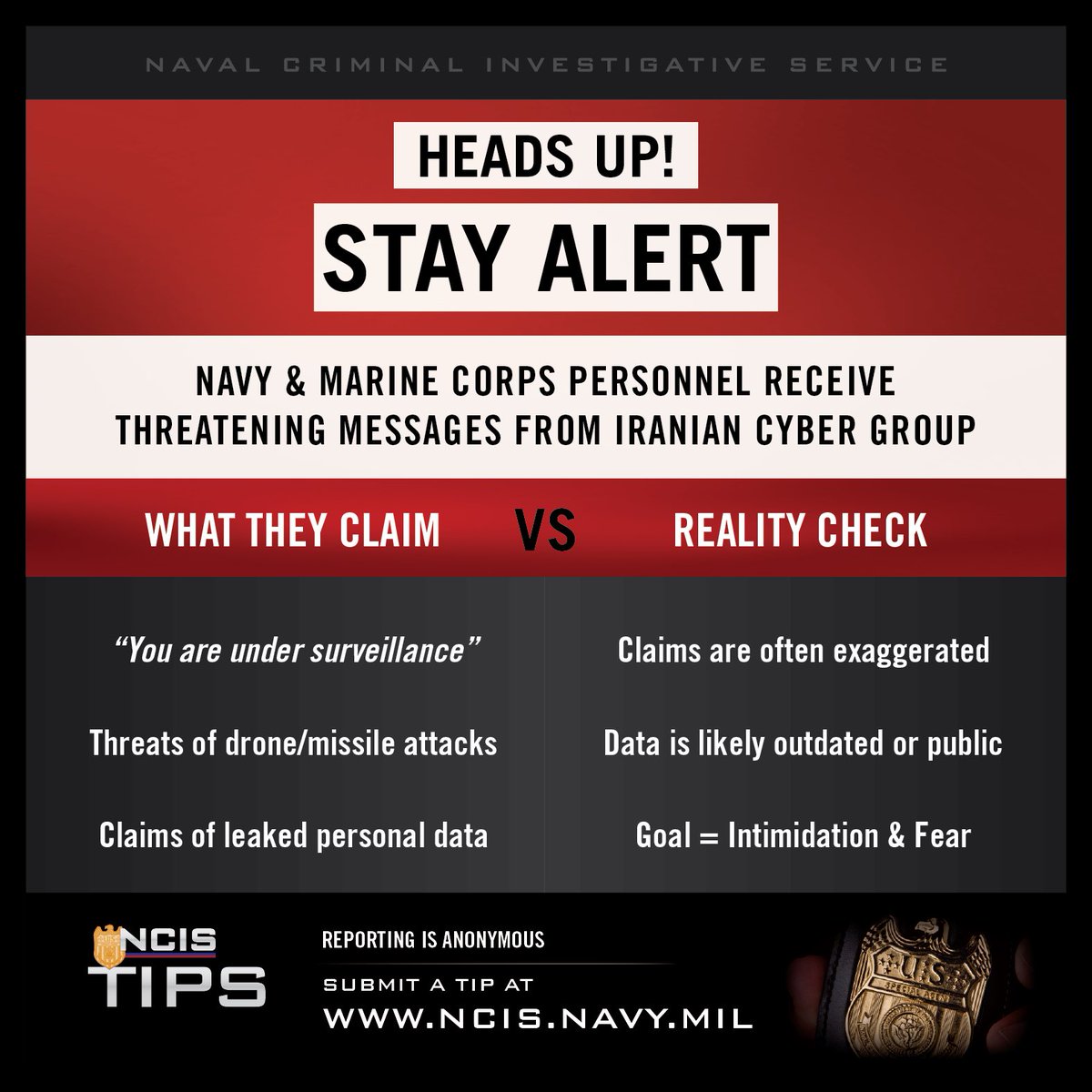
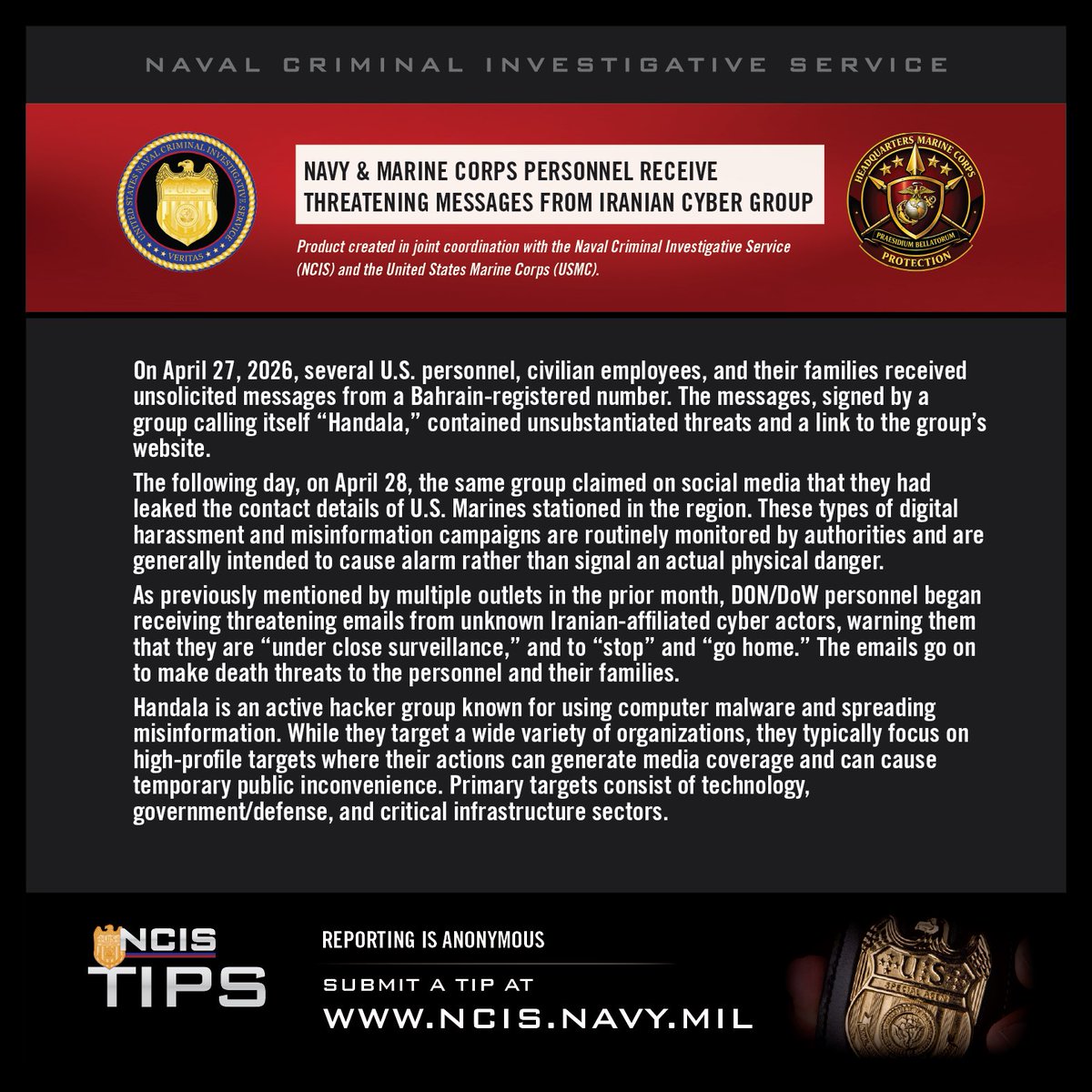
#NCIS is aware of recent unsolicited messages targeting U.S. personnel & families. These cyber-enabled harassment campaigns are designed to create fear and are not assessed as a credible physical threat. Do not engage—report suspicious messages. @USMC #CyberSecurity #StayVigilant
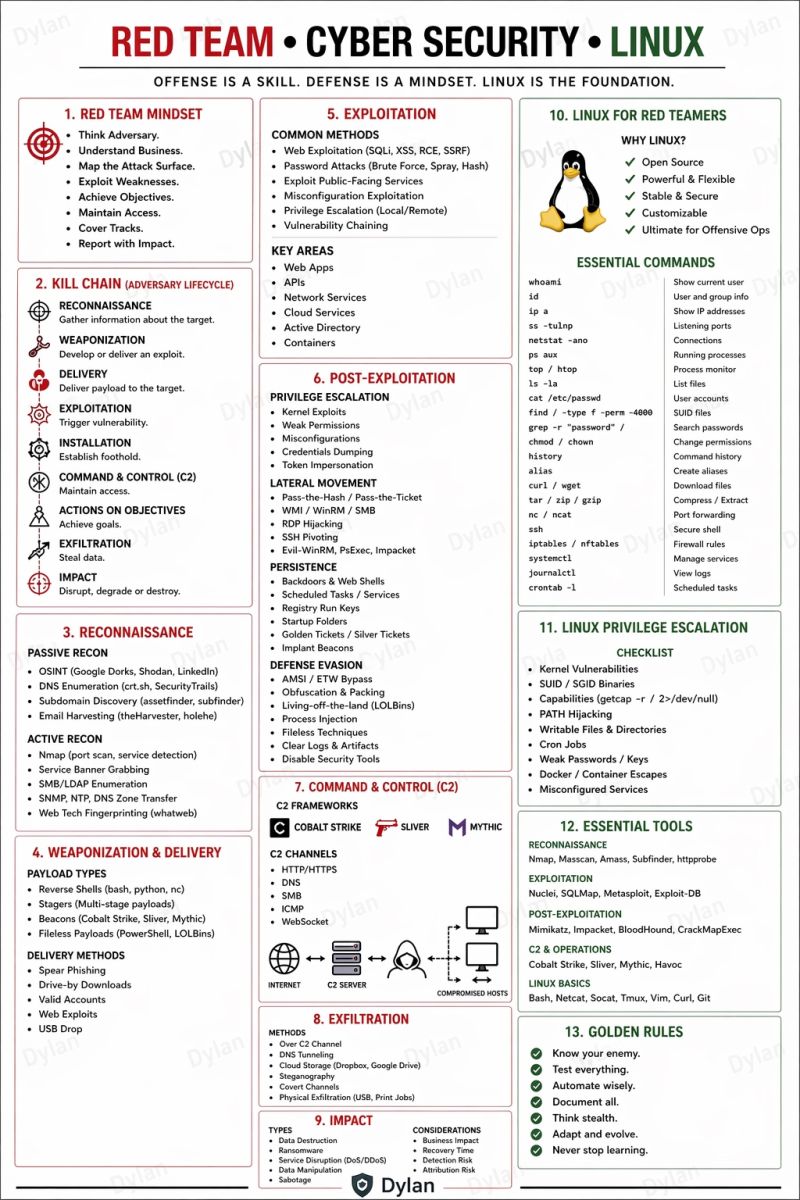
Red Team | Cyber Security | Linux 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
🛡️ We added Linux kernel incorrect resource transfer between spheres vulnerability CVE-2026-31431 to our Known Exploited Vulnerabilities Catalog. Visit go.dhs.gov/Z3Q for more information. #Cybersecurity #InfoSec

🛑 Security breaches don’t just test your defenses—they test your recovery. Join Kaseya in an upcoming webinar to learn how to strengthen resilience with SaaS backups and BCDR to stay operational after attacks. 🎯 Register now: event.on24.com/wcc/r/5301783/… #cybersecurity #bcdr
FIPS 140-2 retirement is now just 5 months away. Now is the time to review your environment and prepare for the transition to FIPS 140-3. Learn how Ubuntu Pro supports FIPS workloads: ubuntu.com/security/certi… #CyberSecurity #FIPS #OpenSource

'Personality test' shows how #AI chatbots mimic human traits—and how they can be manipulated buff.ly/WpPWFV1 via @techxplore_com #CyberSecurity #GenAI Cc @roxananasoi @sallyeaves @floriansemle @LaurentAlaus @aure79lien @mvollmer1 @HaroldSinnott

#Cybersecurity Complexity Is The New Vulnerability by Francis Dinha @Forbes Learn more: bit.ly/4eUDK7N #Infosec #IT #Tech

🛡️ We added four vulnerabilities to our Known Exploited Vulnerabilities Catalog. Visit go.dhs.gov/Z3Q for more information. #Cybersecurity #InfoSec
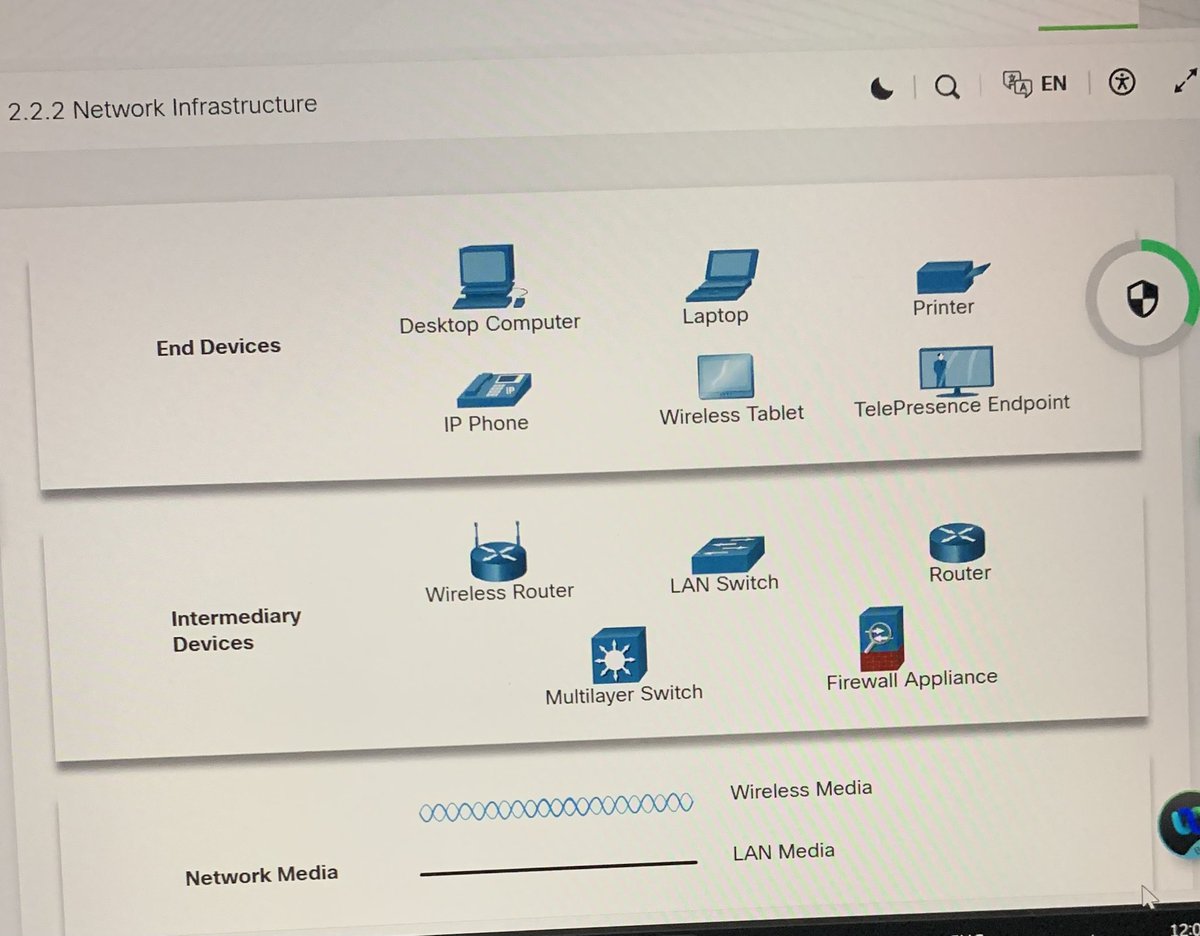
Module 2 @CiscoNetAcad Networking Basics: Completed! ✅ Rounded up ISP connectivity. It’s good seeing the sheer variety of ways we stay connected from DSL and Cable to Satellite and Cellular. #CyberSecurity #LearningInPublic #SOCPath #Networking




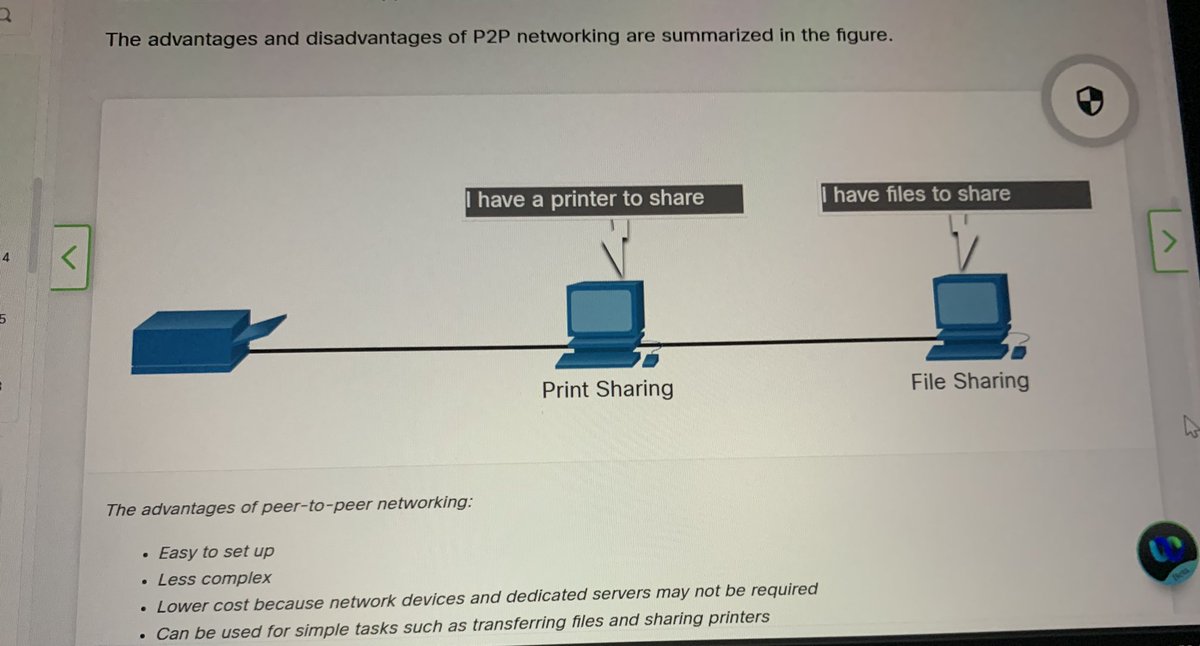
Getting familiar with intermediary devices today. Just covered Clients&Servers and Network Components. It’s cool seeing how a single device can wear different hats like being a Web, Email, and File server all at once #CyberSecurity #Networking #LearningInPublic


Something went wrong.
Something went wrong.
United States Trends
- 1. May the 4th N/A
- 2. Star Wars N/A
- 3. John Sterling N/A
- 4. Chelsea N/A
- 5. Cole Palmer N/A
- 6. Joao Pedro N/A
- 7. Rick Barnes N/A
- 8. Yankees N/A
- 9. Jedi N/A
- 10. Juke Harris N/A
- 11. Strait of Hormuz N/A
- 12. #MondayMotivation N/A
- 13. Good Monday N/A
- 14. #May4th N/A
- 15. #BudGreatDelivery N/A
- 16. CNBC N/A
- 17. Teacher Appreciation Week N/A
- 18. Derry N/A
- 19. Rogue One N/A
- 20. NextNRG Inc N/A