#malware search results
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » Broken VECT 2.0 ransomware acts as a data wiper for large files bleepingcomputer.com/news/security/…
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » Hackers are exploiting a critical LiteLLM pre-auth SQLi flaw bleepingcomputer.com/news/security/…
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » Video service Vimeo confirms Anodot breach exposed user data bleepingcomputer.com/news/security/…
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » US reportedly charges Scattered Spider hacker arrested in Finland bleepingcomputer.com/news/security/…
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » Microsoft to deprecate legacy TLS in Exchange Online starting July bleepingcomputer.com/news/microsoft…
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » Checkmarx confirms LAPSUS$ hackers leaked its stolen GitHub data bleepingcomputer.com/news/security/…
North Korean hackers are using AI to insert malware into npm packages like @validate-sdk/v2, what does this mean for your business's software supply chain security? #cybersecurity #npmsecurity #malware
VECT 2.0 ransomware has a flaw that destroys large files instead of encrypting them, permanently losing data, what's the real motive behind this malfunction, an honest error or intentional sabotage #ransomware #datasecurity #malware
⚠️ Alarming Supply Chain Attack Targets SAP npm Packages with Credential-Stealing #Malware -Fact Checker: ✅: 2 ❌: 1 || 2/3 undercodenews.com/alarming-suppl…
One compromised endpoint. That's all it takes. Malware moves laterally faster than most teams can respond. #CyberAwareness #ThreatIntel #Malware One scan. Total clarity.
💣📂 vect ransomware bug turns into data wiper A flaw in encryption logic causes large files to be permanently destroyed instead of encrypted. learn more bleepingcomputer.com #ransomware #malware #cybersecurity #infosec #security

Fake Windows update installs hidden malware #WindowsUpdate #Malware #FraudulentWebsite #SecurityTools #PasswordStealer #Installer #InfectedDevice #Cyberattack foxnews.com/tech/fake-wind…
SOLUTION ALERT: New MEFF M3-PRO AI Enhanced Professional Malware Scanner. Detects #malware, spyware, Trojans, and system anomalies. #Android & #IoS Mobile Devices #CyberSecurity #Corporate

The GlassWorm campaign is back with a new dropper written in Zig. It's spreading via a fake VSX extension to infect ALL IDEs on a developer's machine, creating a major software supply chain risk. 👨💻☣️ #Malware #SupplyChainAttack #DevSecOps
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #Science #Technology #QuantumComputers #QuantumPhysics #QuantumMechanics #QuantumTech ⚛️ • » Is Your Network Prepared for the Post-Quantum World? hackers-arise.com/is-your-networ…
An Alarming Threat 🚨 The cyber operation known as VECT 2.0 is raising serious alarms because it blurs the line between ransomware and outright destruction. Check our post on LinkedIn to learn more detail: linkedin.com/posts/itbutler… #Alert #Malware

⚠️ Turns out this was indeed #MALWARE DISTRIBUTION SYSTEM ⚠️ I pasted the script the website copied on my Clipboard to @GeminiApp. The chatbot told me that it was a "malware delivery command". Beware of such fake Cloudflare checks and the motorbeam(dot)com website.
🚨 Cyber war just went live. Nation-state hackers act like startups, supply chains are battlegrounds & every click is a weapon. This isn’t cybercrime, it’s cyber conflict, escalating fast. Reference: thehackernews.com/2026/04/weekly… #CyberSecurity #Hacking #Malware
• #Hacked #Malware #Spyware #Zerodays #Ransomware #Phishing #Backdoor #RCE #RAT ☠️ • • #CyberSecurity #CyberCrime #DataHack #DataPrivacy #DataTheft #DataLeaks #DataBreach 💾 • » More and more drivers are wrapping their car keys in aluminum foil, and the reason has a lot to
⚡ Google adding a 24-hour delay for installing #Android apps from unverified developers. Users must enable developer mode, reboot, and confirm again after a day. This is meant to stop #malware and scams that trick users into disabling Play Protect or giving access. 🔗 Details

#Malware Malteiro / Mispadu 🇧🇷 🆕 La red desplegó en marzo una nueva funcionalidad que busca dentro del equipo infectado documentos de identificación (imagenes o pdf) y documentos con credenciales (txt)🚨 🇲🇽 alrededor de 2mil IDs extraídos, 🇦🇷 sigue muy atrás cerca de 50 IDs
#Malware #Mispadu 🇧🇷 Se volvieron tan vagos que ya no esconden la infra de spam Apuntando a 🇦🇷 Site opendir hxxps://uglmkt.com/ Link mail (redirige a sitio que descarga Zip+hta) hxxps://u.to/RmN7Ig hxxps://u.to/YmN7Ig hxxps://u.to/h2N7Ig hxxps://u.to/xGN7Ig hxxps://u.to/9GN7Ig
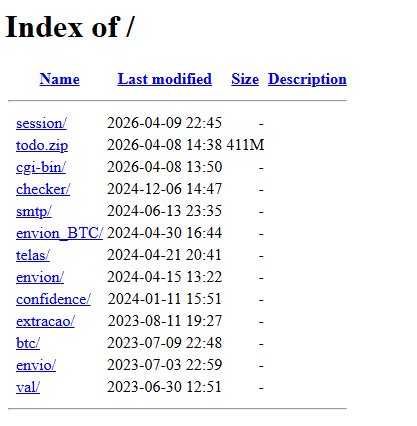

Posibles #Malware para Android / Fake Play Store Claro 5G hxxps://www.claro-5g.com/ Geral hxxps://vietchinhphu.com/ hxxps://cellfinexchange.xyz/ hxxps://nec-moneybd.top/ hxxps://quickmoneyapp.top/ hxxps://atualizacao-apps.click/

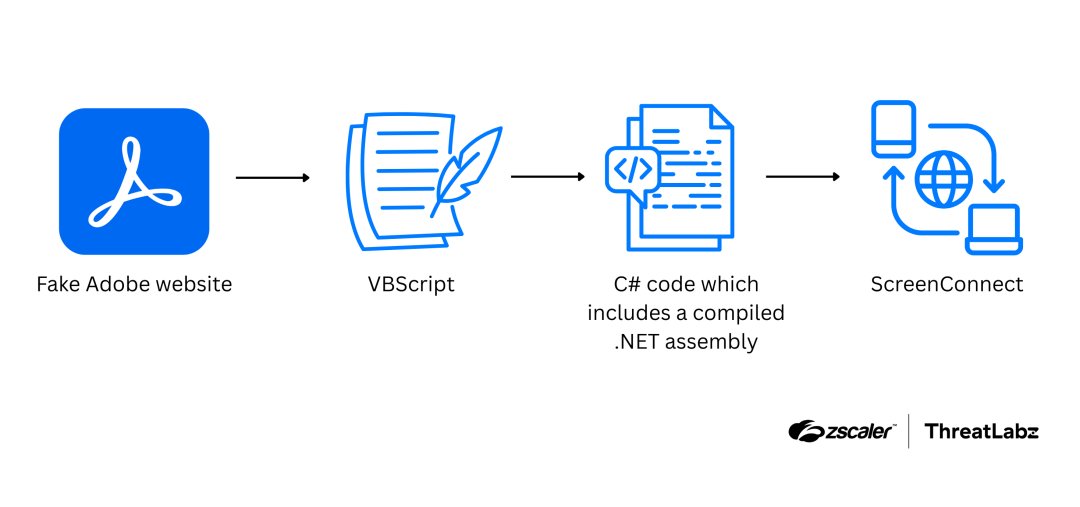
Zscaler reveals a 2026 attack chain using fake Adobe Reader lures to install ScreenConnect via in-memory execution and UAC bypass. Protect your network now! #ScreenConnect #ThreatIntel #Malware #CyberSecurity #Zscaler #InfoSec securityonline.info/fake-adobe-rea…
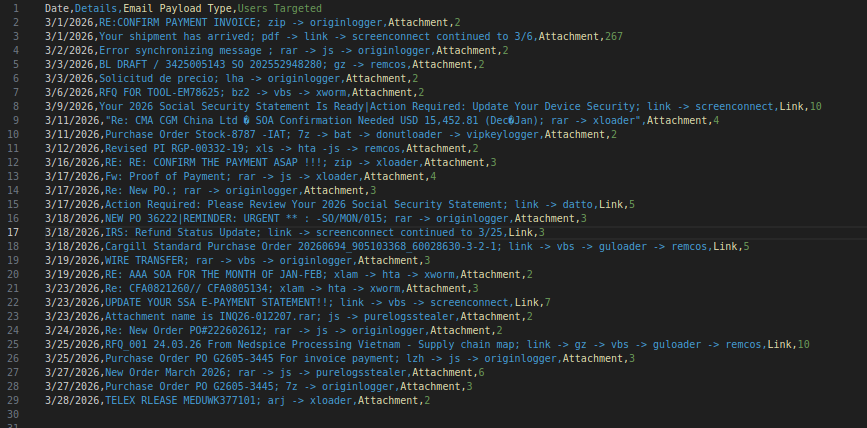
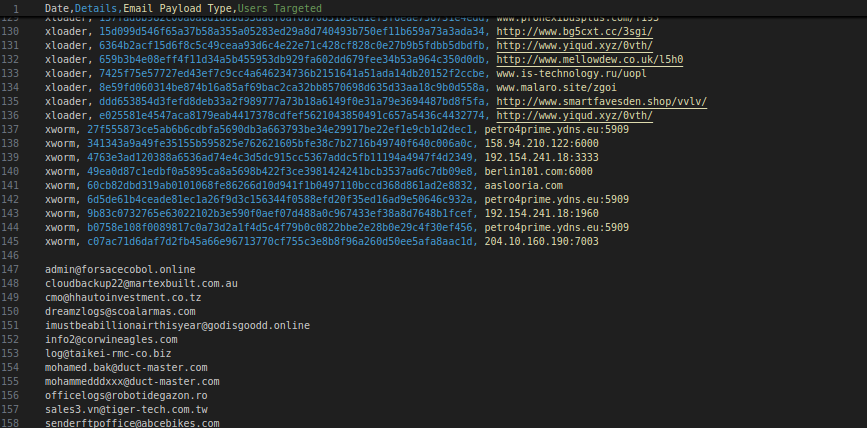
A very late (due to work travel) csv formatted list of #malspam campaigns that crossed my path in March to include #malware type, subject, hash, c2, and email exfil addresses: gist.github.com/silence-is-bes… #retrohunt
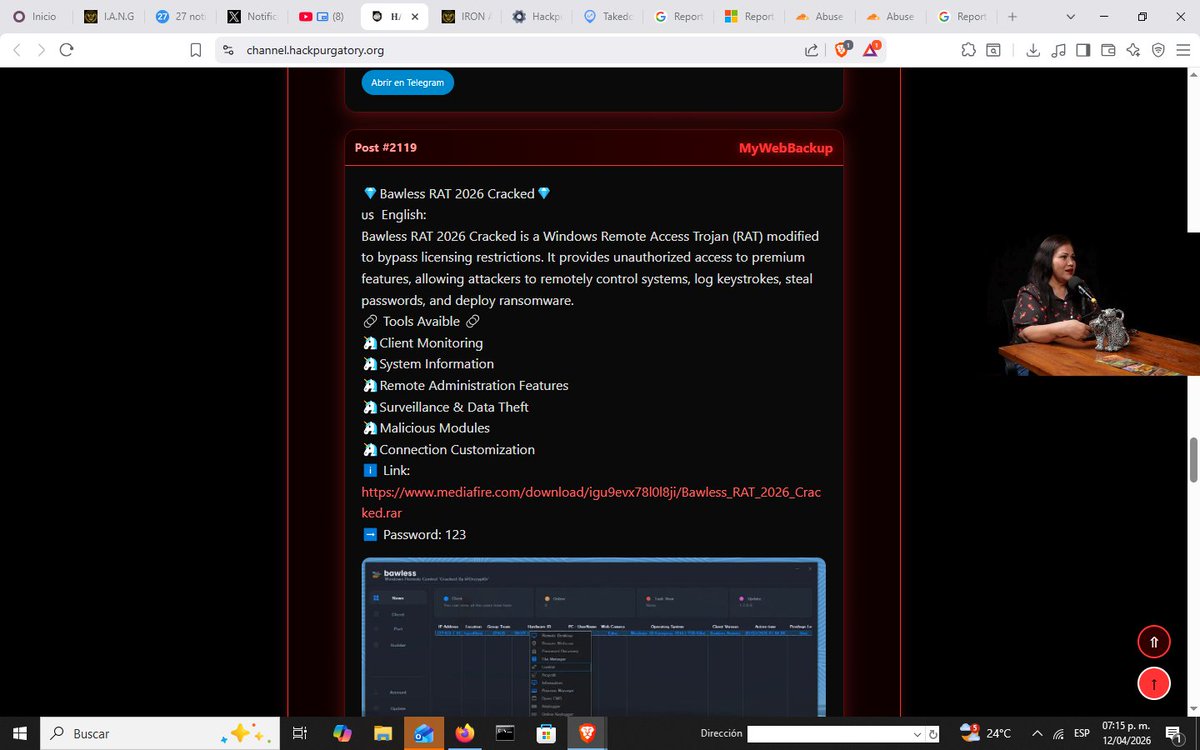
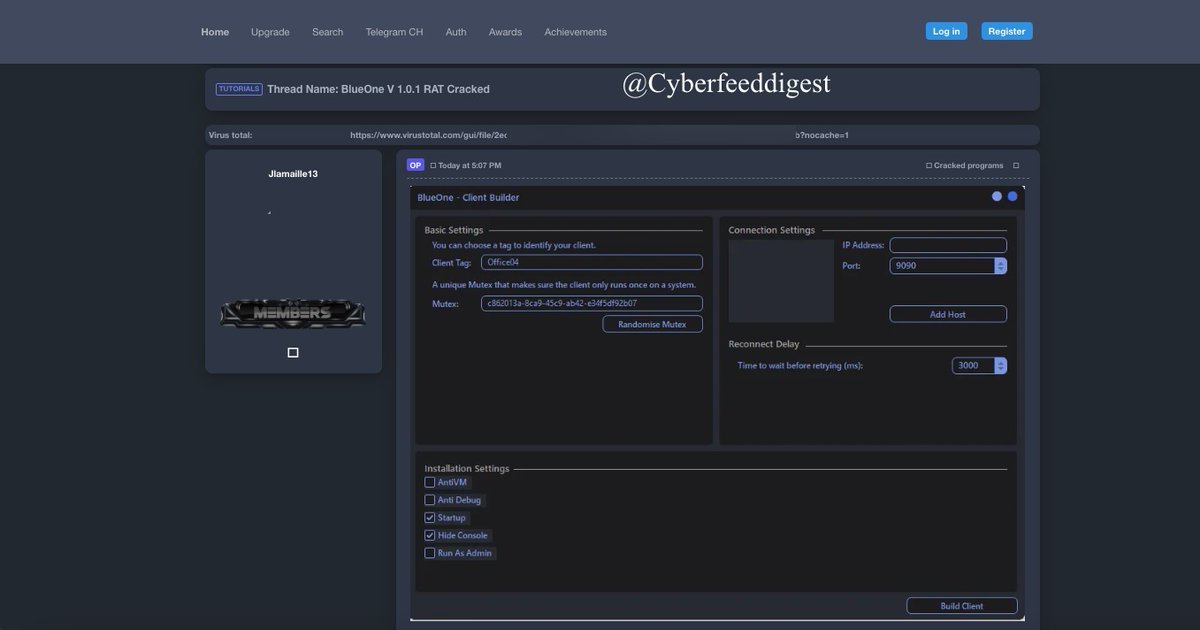
RAT's crackeados en las páginas de hack purgatory amigos de los Chronus Mafia y otros cibercriminales como el grupo de carding CASH #Colombia #malware ALERTA! no te dejes llevar ni engañar por estos cibercholos!!
Arkanix Stealer didn’t just steal data. It ran like a startup. • MaaS model • Discord marketing • Referral program • C++ & Python variants • Crypto & browser data theft Short-lived campaign. Long-term implications. Full analysis: kas.pr/w692 #Malware

#Malware #Grandoreiro 🇧🇷 Posible hlsystem / server de "modulos" 34.235.170.]239:30336 - 1er stage: 25 sites - Mediafire urls: 190 (Varias caídas) - Una url del 1er stage parece descargar hta de "Mispadu" IOCs: pastebin.com/raw/TFZdAc7b
![Merlax_'s tweet image. #Malware #Grandoreiro 🇧🇷
Posible hlsystem / server de "modulos"
34.235.170.]239:30336
- 1er stage: 25 sites
- Mediafire urls: 190 (Varias caídas)
- Una url del 1er stage parece descargar hta de "Mispadu"
IOCs:
pastebin.com/raw/TFZdAc7b](https://pbs.twimg.com/media/HGdj_KvXIAAjsX1.jpg)
![Merlax_'s tweet image. #Malware #Grandoreiro 🇧🇷
Posible hlsystem / server de "modulos"
34.235.170.]239:30336
- 1er stage: 25 sites
- Mediafire urls: 190 (Varias caídas)
- Una url del 1er stage parece descargar hta de "Mispadu"
IOCs:
pastebin.com/raw/TFZdAc7b](https://pbs.twimg.com/media/HGdhZVeWEAA1r4B.png)
The malware can upload and download files, leverage the microphone, and capture images through the webcam by exploiting the web browser's features, the researchers said. Read more ⤵️ cnews.link/russia-ukraine… #malware #Russia #Ukraine #cybersecurity

You solve a CAPTCHA. Attackers solve the rest. New Horabot campaign uses fake verification pages + multi-stage loaders to deploy a banking Trojan and spread via email. All from one pasted command. Full breakdown 👇 kas.pr/t54g #cybersecurity #malware #threatintel

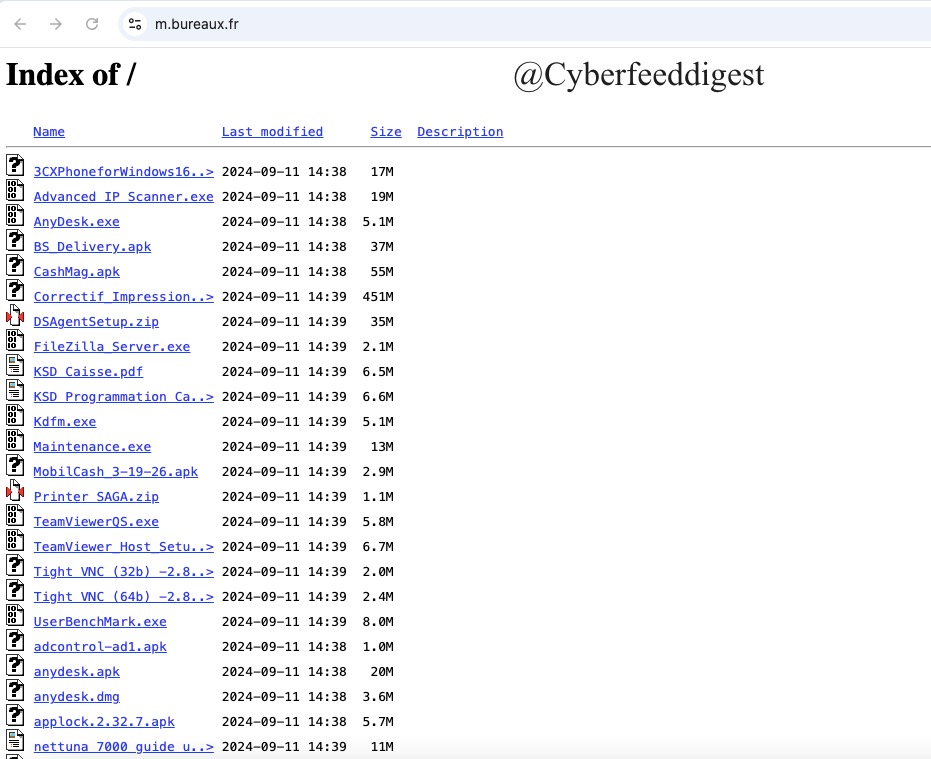
#Opendir .EXE and .APK files like "Advanced IP Scanner.exe" ,"AnyDesk.exe" hxxps://m.bureaux.fr/ Handle with Caution Good source for #Malware analysts.
A member of a #darkweb forum allegedly shared DynAmite 4.0 #Malware Creation Toolskit. Features: Pre-configured modules Automated payload generation User-friendly interface (in some cases) Rapid deployment capabilities

Last October, Cybernews reported Microsoft’s warning about threat actors abusing Teams to steal data, spread malware, and maintain access. Learn more: cnews.link/microsoft-team… #Microsoft #cybersecurity #malware

ClickFix Campaigns Spread MacSync macOS Infostealer via Fake AI Tool Installers dlvr.it/TS2bm8 #CyberSecurity #Malware #MacSecurity #AIThreats #InfoStealer

54 EDR Killers Use BYOVD to Exploit 34 Signed Vulnerable Drivers and Disable Security dlvr.it/TS5yrt #CyberSecurity #Ransomware #Malware #EDR #BYOVD

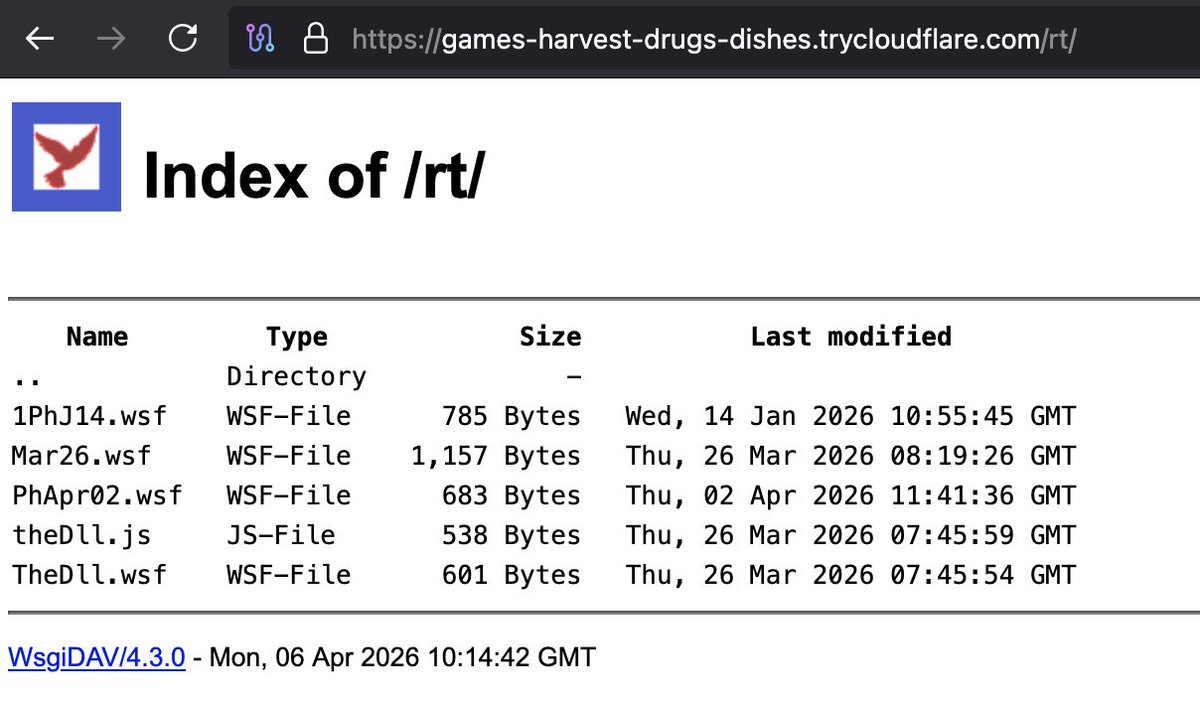
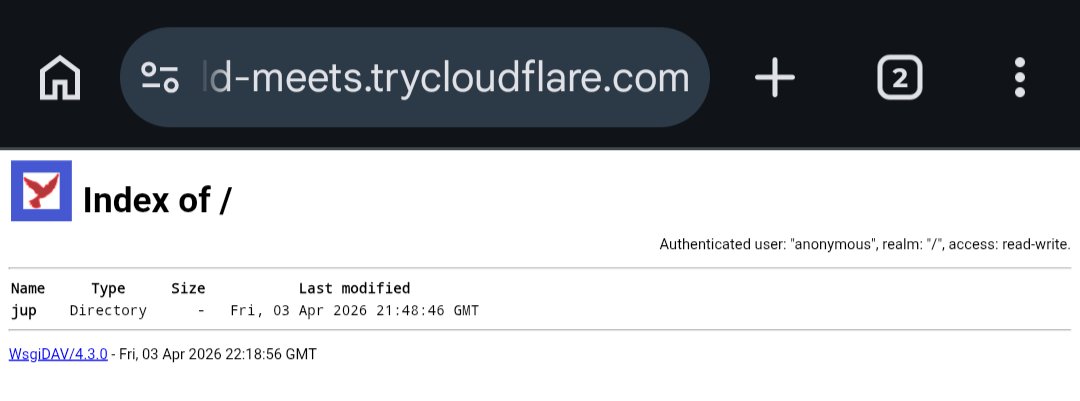
🧵 #AsyncRAT #Malware delivery chain ☣️ Re_0747916973633303.pdf.wsh⤵️ 1⃣📸hxxps://games-harvest-drugs-dishes.trycloudflare.com@SSL\DavWWWRoot\rt\PhApr02.wsf⤵️ 2⃣📸PhApr02.wsf⤵️ ☣️5d0a50d892e998a1217aec4513716eb1 hxxps://published-magnitude-ethnic-gathering.trycloudflare.com

A new malware-as-a-service (MaaS) platform is being sold on the dark web. Read more: cnews.link/venom-stealer-… #malware

#Ciberseguridad ↔️ Consejos para evitar problemas con #virus y #malware #VirusYMalware @incibe @osiseguridad #BuenasPrácticas tinyurl.com/3zzam3df

Something went wrong.
Something went wrong.
United States Trends
- 1. Supreme Court N/A
- 2. Voting Rights Act N/A
- 3. SCOTUS N/A
- 4. Powell N/A
- 5. NBA Street N/A
- 6. Watson N/A
- 7. Louisiana N/A
- 8. FOMC N/A
- 9. Casper N/A
- 10. Jim Crow N/A
- 11. Zambia N/A
- 12. The Fed N/A
- 13. #You_Complete_Our_SevEN N/A
- 14. Mary Kay N/A
- 15. The VRA N/A
- 16. Callais N/A
- 17. Vezina N/A
- 18. Section 2 N/A
- 19. Rhythm Nation N/A
- 20. Alito N/A


































































![tial_cl's tweet image. 🚨 Atención #LATAM
Nuestro equipo detectó una campaña de #phishing
Asuntos :
• “URGENTE: Auditoria Fiscal Iniciada”
• “Notificacion Judicial Importante”
Los mensajes suplantan remitentes como:
• buzontributario@sat[.]gob[.]com
• avisosjudicial@sternaabogados[.]com
Origen](https://pbs.twimg.com/media/HGZJo6fbsAAvwbb.png)
![tial_cl's tweet image. 🚨 Atención #LATAM
Nuestro equipo detectó una campaña de #phishing
Asuntos :
• “URGENTE: Auditoria Fiscal Iniciada”
• “Notificacion Judicial Importante”
Los mensajes suplantan remitentes como:
• buzontributario@sat[.]gob[.]com
• avisosjudicial@sternaabogados[.]com
Origen](https://pbs.twimg.com/media/HGZJrcpbMAA7S_9.png)
![tial_cl's tweet image. 🚨 Atención #LATAM
Nuestro equipo detectó una campaña de #phishing
Asuntos :
• “URGENTE: Auditoria Fiscal Iniciada”
• “Notificacion Judicial Importante”
Los mensajes suplantan remitentes como:
• buzontributario@sat[.]gob[.]com
• avisosjudicial@sternaabogados[.]com
Origen](https://pbs.twimg.com/media/HGZJtzfbAAAn1dJ.png)





