Paul Batson @[email protected]
@lazysecurity
SecOps, Detection Engineering & Threat Modelling. Husband. Dad. Veteran. Ex BSidesLDN organiser. Antiracist. LGBTQ+ Ally. He/Him. http://infosec.exchange/@lazysecurity
你可能會喜歡
I’m bsky.app/profile/paulba… on Blue Sky if anyone is there too. Seems a lot of people making the move. I’m also still on Mastodon too as infosec.exchange/web/@lazysecur…
Ladies and gentlemen, we present to you Conti Ransomware group 💀

Windows Defender blocks any procdump execution referencing "lsass" on the command line (1️⃣) Simply querying lsass' process ID and using this instead bypasses this somewhat naive detection (2️⃣) Even simpler? Use lsass' service name, "KeyIso" 🤷 (3️⃣)

BREAKING: The Chinese vessel Yi Peng 3 has been chased, intercepted, and boarded by Danish Navy vessel Y311 Søløven after the Chinese vessel destroyed 2 undersea telecom cables linking Finland-Germany and Sweden-Lithuania. The vessel sailed from Russia & the captain is Russian

in today's 'no way, is it real?' we found out that Palo Alto's PAN-OS CVE-2024-0012 and CVE-2024-9474 were the equivalents of saying 'turn off auth and give me a shell'. Enjoy! labs.watchtowr.com/pots-and-pans-…
All the workshop recordings and slides from #r2con2024 are now edited and published. If you didn't had a chance to attend now it's a good time to catch up starting right from the very first day! 👉 radare.org/con/2024/

Quick PSA: Someone is attacking Tor right now and has been for a few weeks. The attacker is spoofing the IPs of Tor Exit and Directory nodes, and blasting TCP SYN packets indiscriminately on 22/TCP- spurring a large amount of abuse complaints to hosting providers, which are…
Inside a Firewall Vendor's 5-Year War With the Chinese Hackers Hijacking Its Devices wired.com/story/sophos-c…
It’s been just over a week since we launched our Free Tier, and the response has been incredible. Here’s a quick look at the impact so far: ✅ 12109 + Total Students Enrolled ✅ 25+ Hours of Free Content Available (with a grand total of over 302,725 hours to all student…

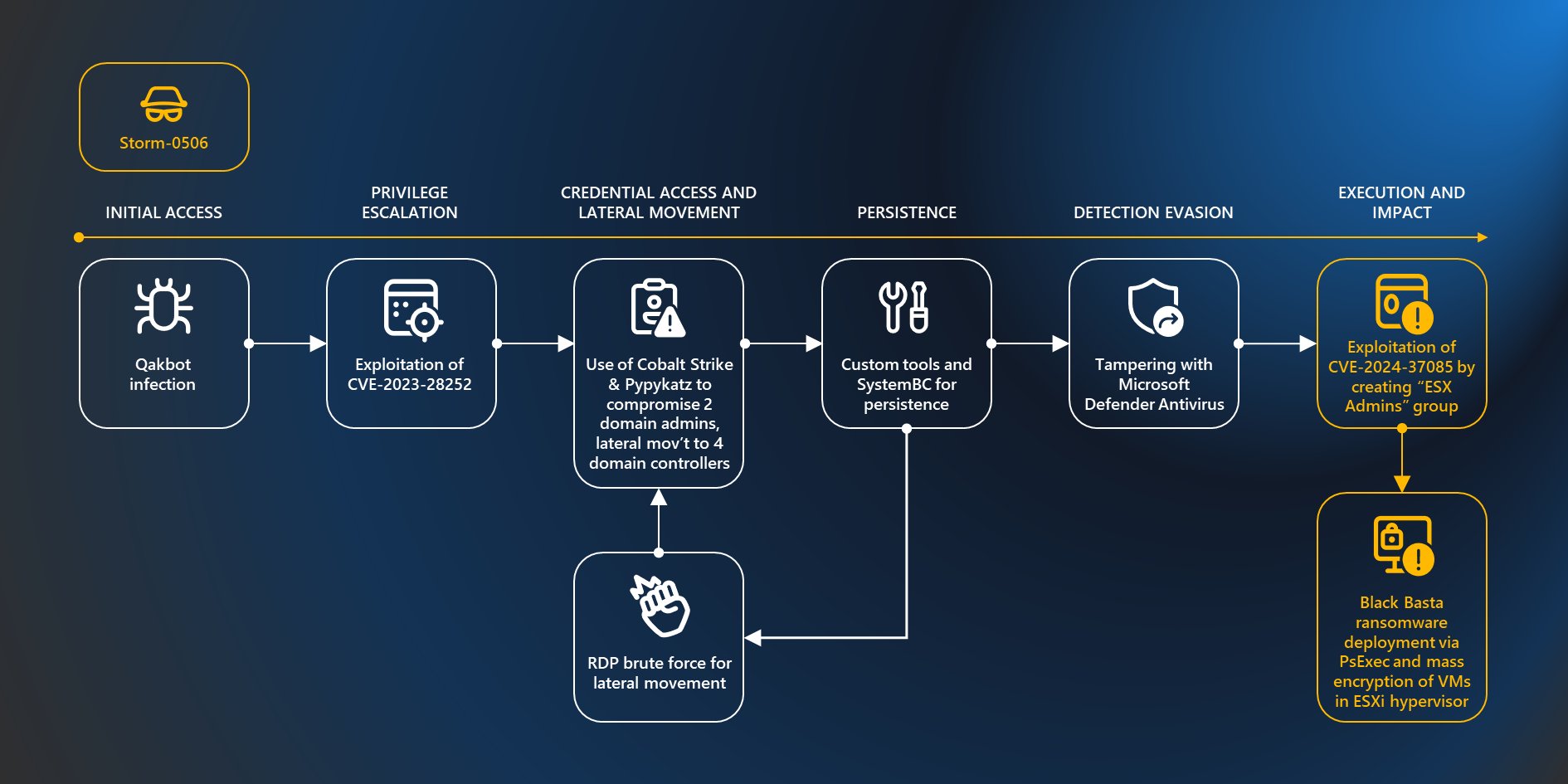
In today's WTF?!?!? moment When a ESXi server is domain-joined, it assumes any "ESX Admins" group & its members should have full admin rights. So.... anyone who can create & manage a group in AD, can get full admin rights to the VMware ESX hypervisors! microsoft.com/en-us/security…

Microsoft has uncovered a vulnerability in ESXi hypervisors, identified as CVE-2024-37085, being exploited by threat actors to obtain full administrative permissions on domain-joined ESXi hypervisors and encrypt critical servers in ransomware attacks. msft.it/6012lbTai
An interesting read: trufflesecurity.com/blog/anyone-ca… (thanks to @mattjay for highlighting this)
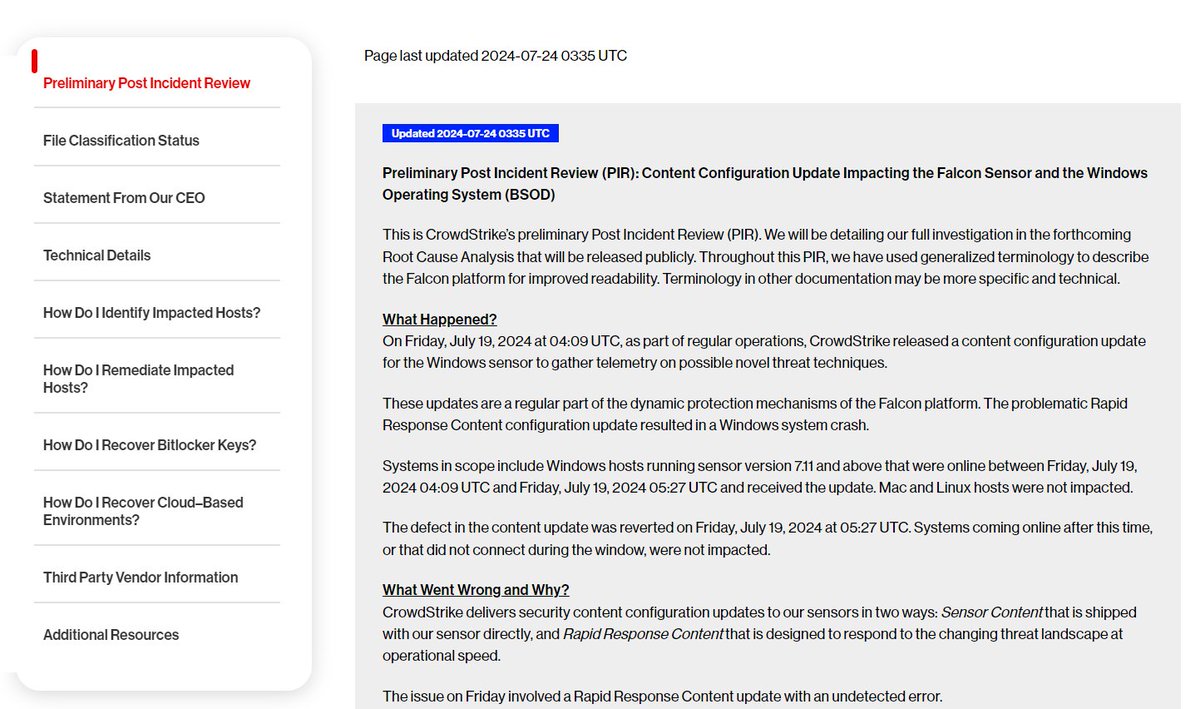
CrowdStrike Preliminary Post Incident Review (PIR) is released: crowdstrike.com/falcon-content…
United States 趨勢
- 1. Panthers 47.6K posts
- 2. Rams 31.6K posts
- 3. Colts 32.8K posts
- 4. Vikings 19.4K posts
- 5. Ole Miss 100K posts
- 6. Falcons 13.6K posts
- 7. Jets 38.7K posts
- 8. Browns 44.6K posts
- 9. Texans 24.2K posts
- 10. #KeepPounding 9,209 posts
- 11. Brosmer 6,503 posts
- 12. Herbert 7,013 posts
- 13. Stafford 19.9K posts
- 14. #BillsMafia 3,886 posts
- 15. Seahawks 16.9K posts
- 16. Bryce Young 11.5K posts
- 17. Joe Brady 1,206 posts
- 18. #Skol 2,173 posts
- 19. Dallas Turner N/A
- 20. Lane 188K posts
你可能會喜歡
Something went wrong.
Something went wrong.