#cryptographypaper search results
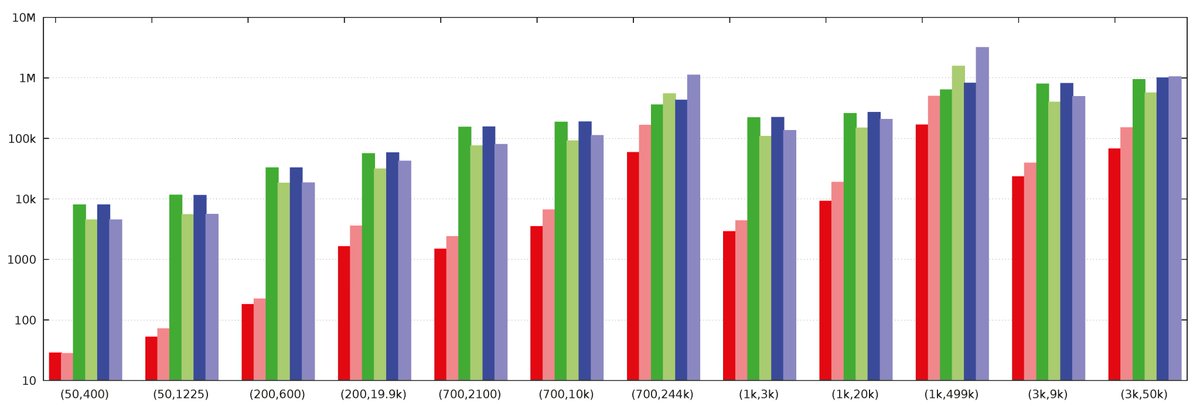
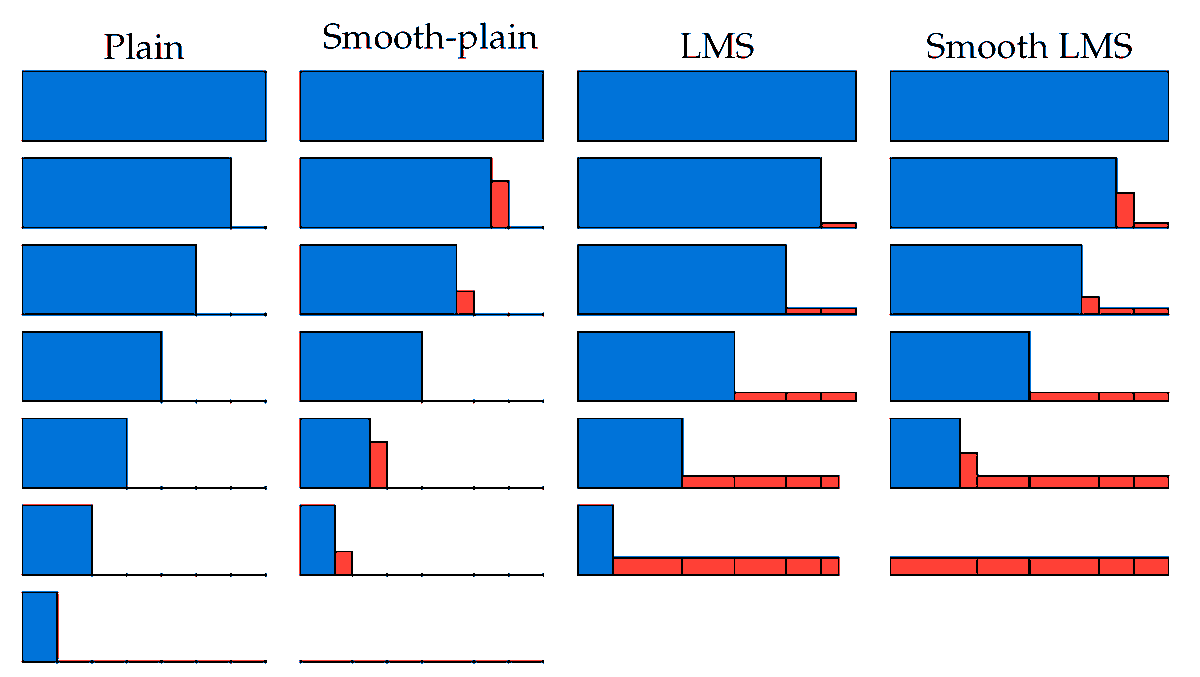
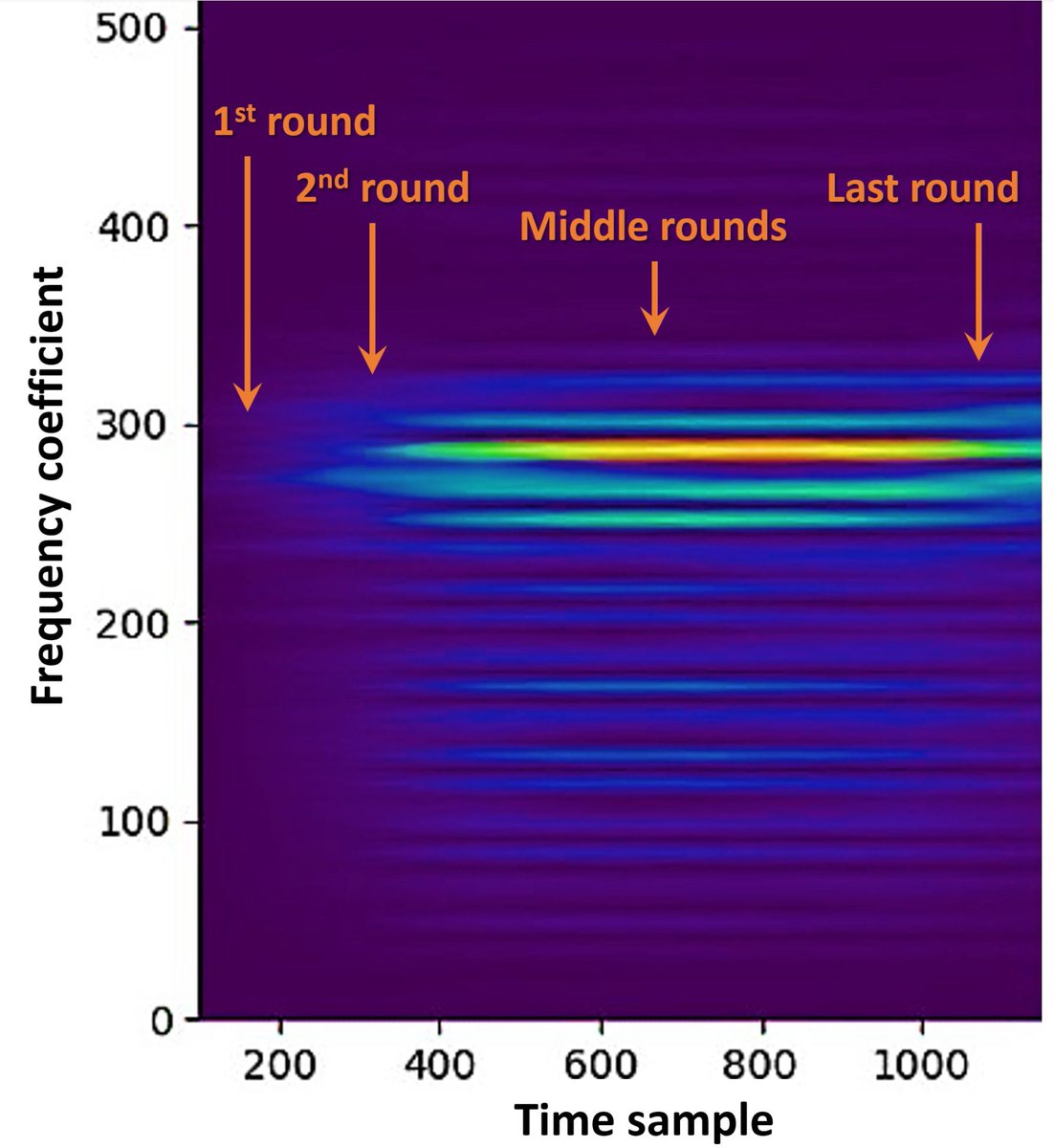
#CryptographyPaper Improved #Filtering Techniques for Single- and Multi-Trace Side-#Channel #Analysis by Dor Salomon, Amir Weiss and Itamar Levi from Bar-Ilan University (BIU) Massachusetts Institute of Technology (MIT) open access, welcome to read: mdpi.com/2410-387X/5/3/…
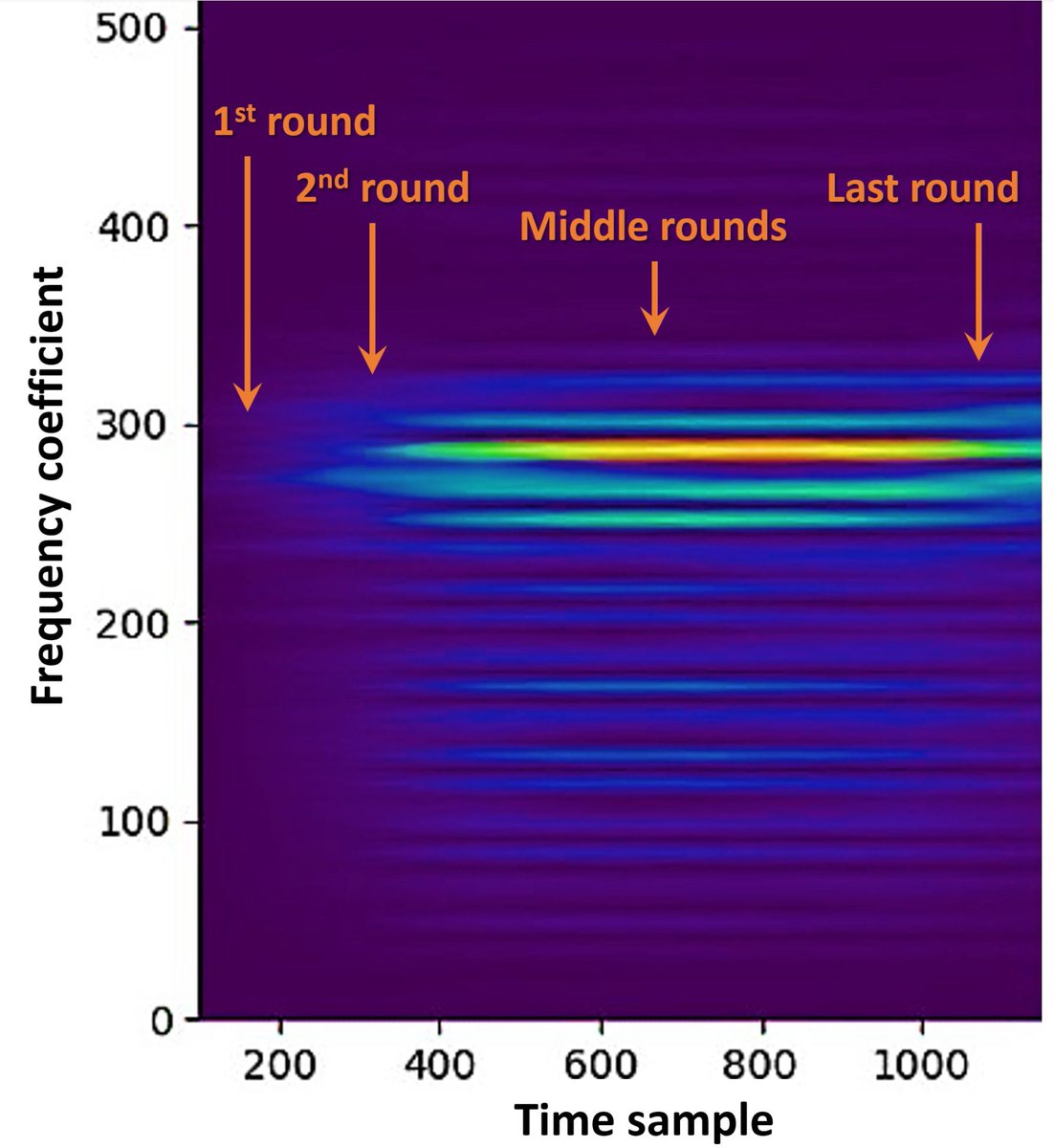
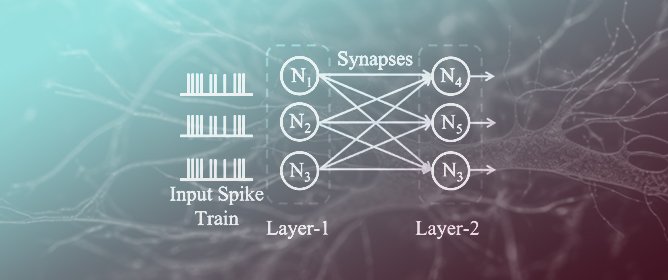
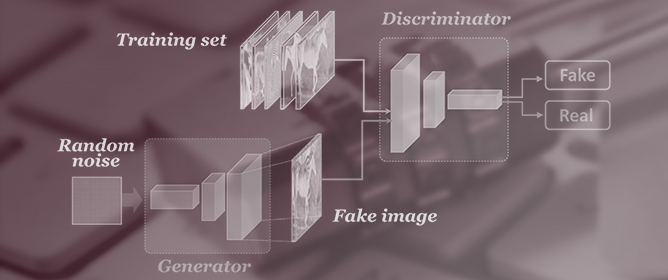
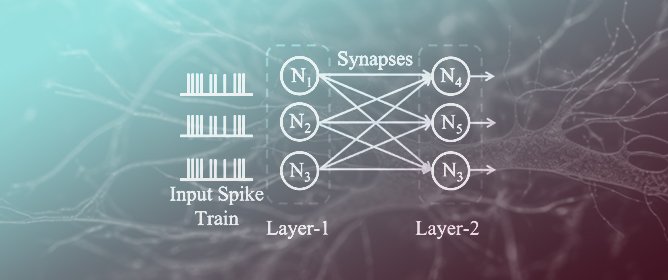
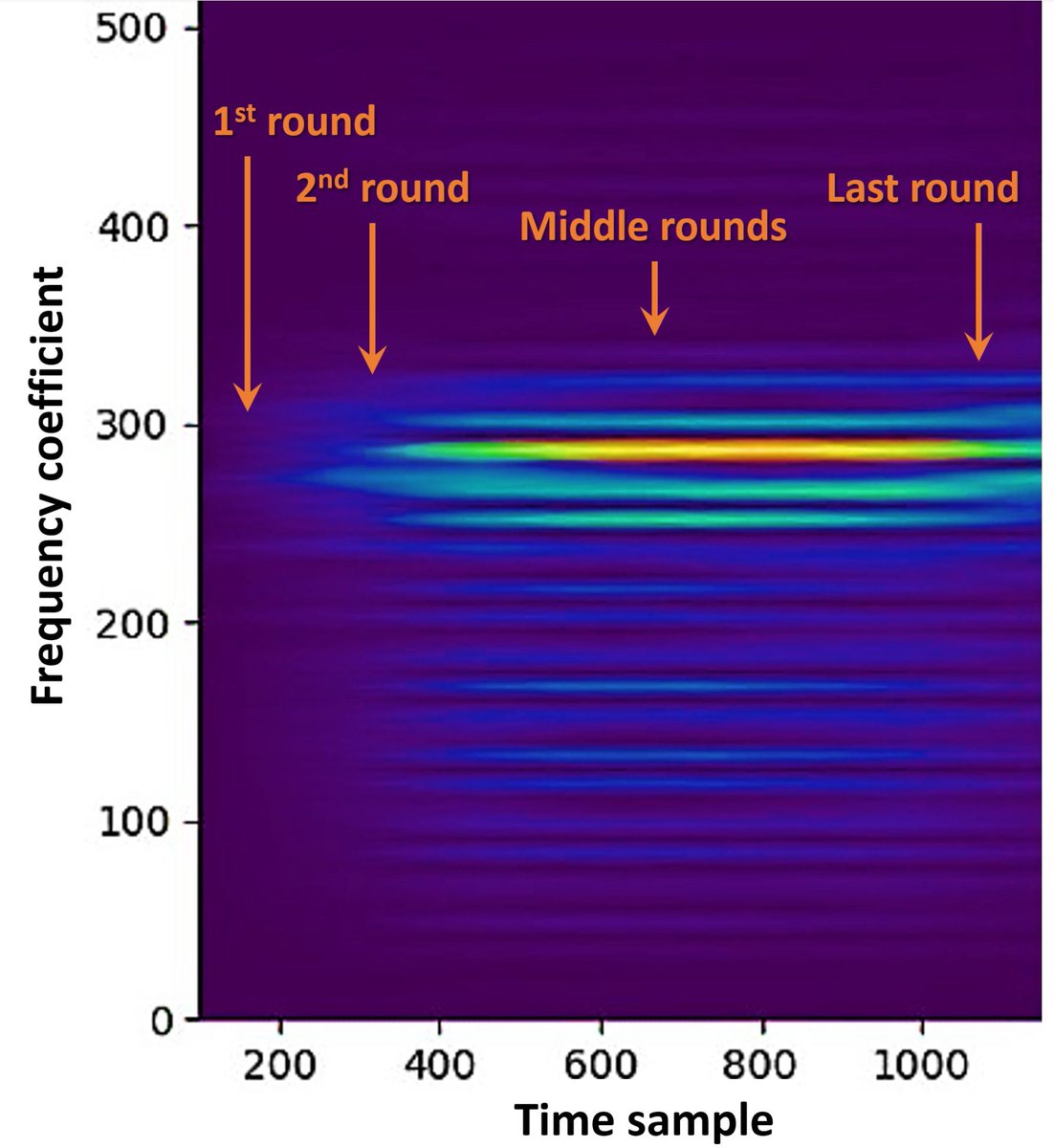
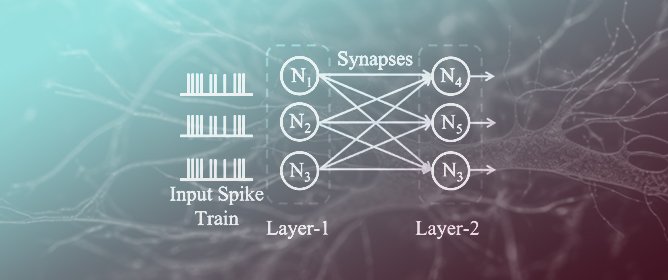
#CryptographyPaper selected title story: SCANN: Side Channel Analysis of Spiking Neural Networks mdpi.com/2410-387X/7/2/…
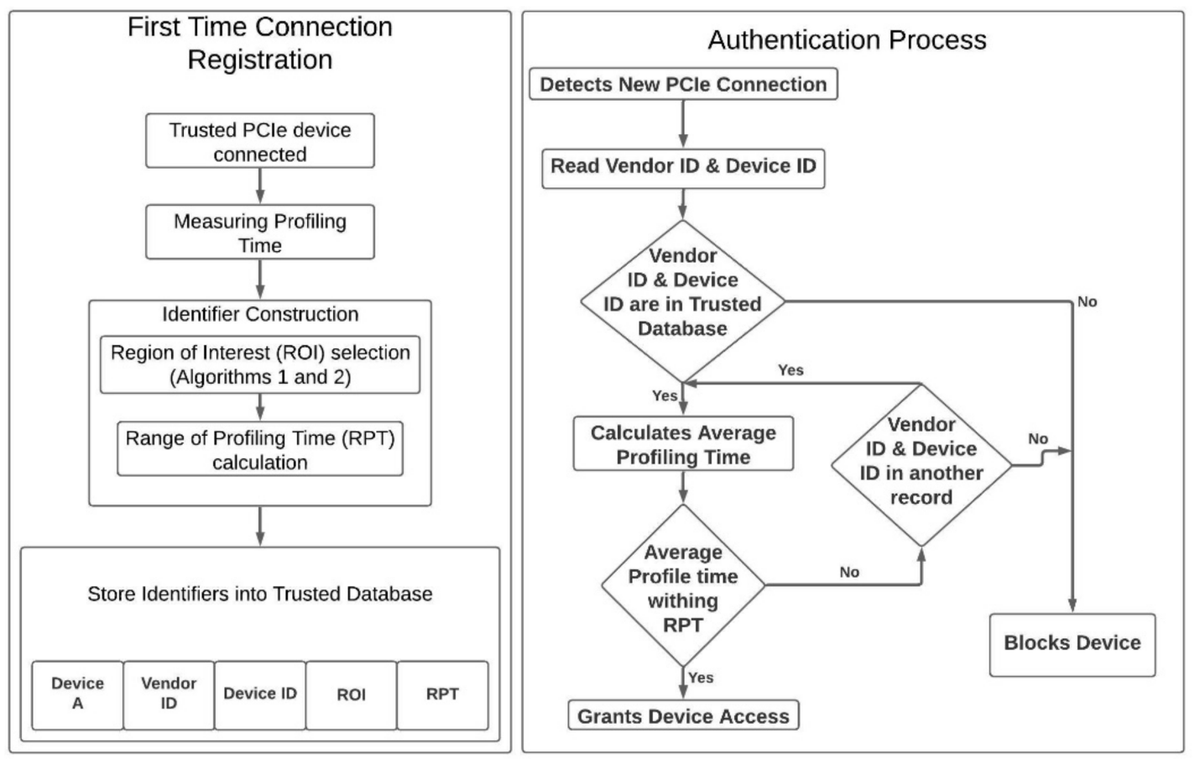
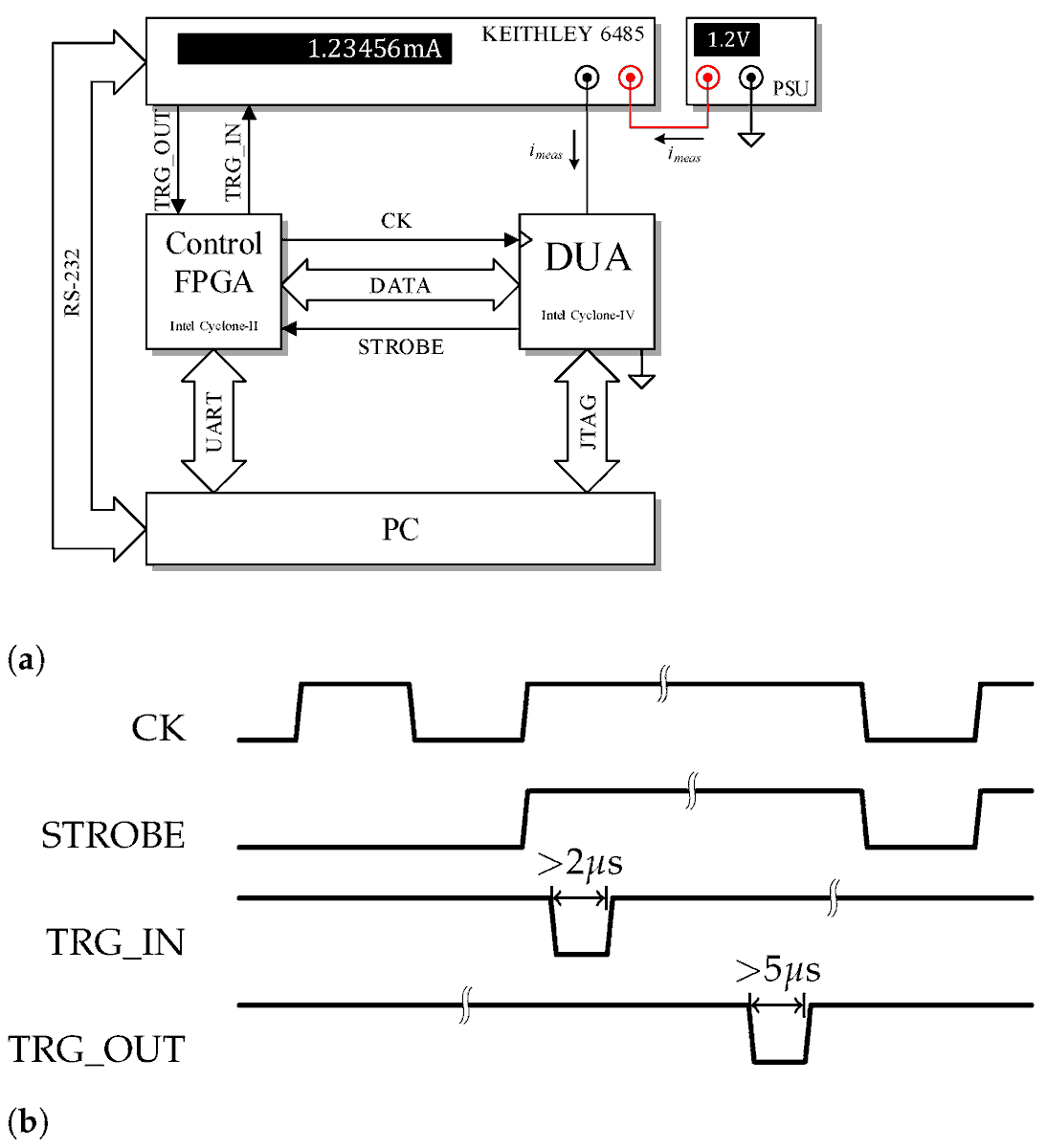
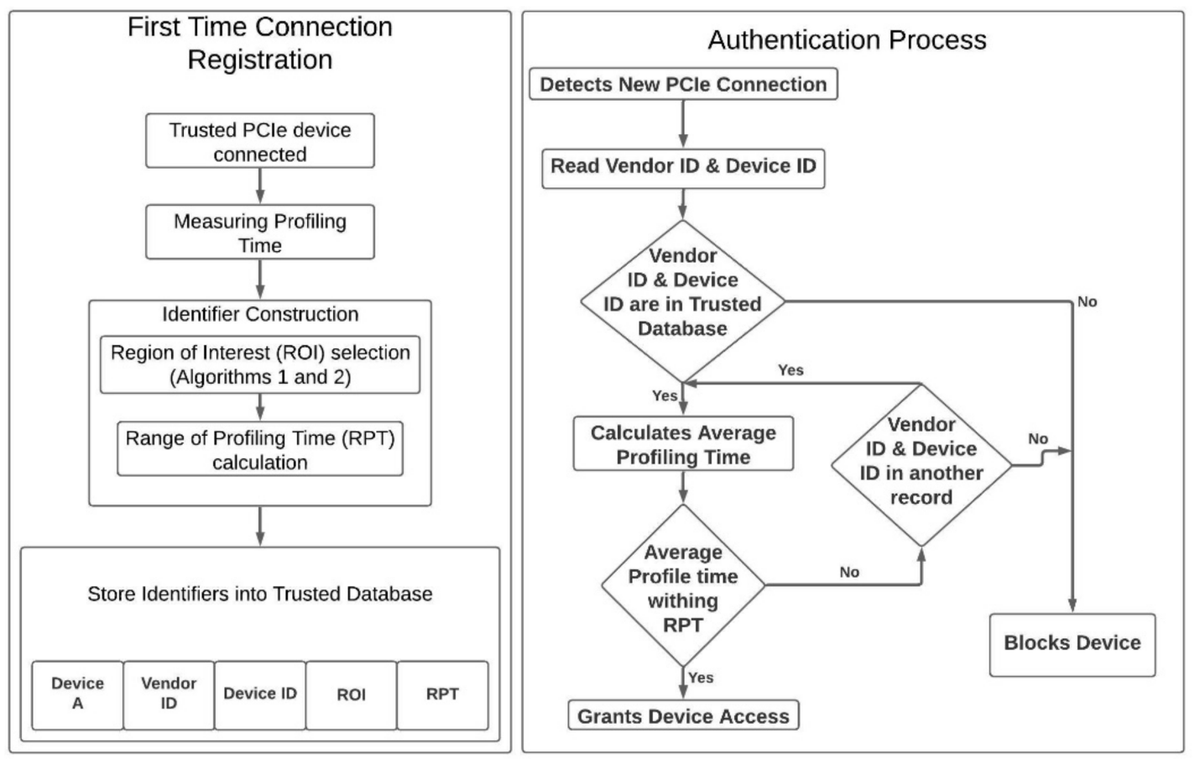
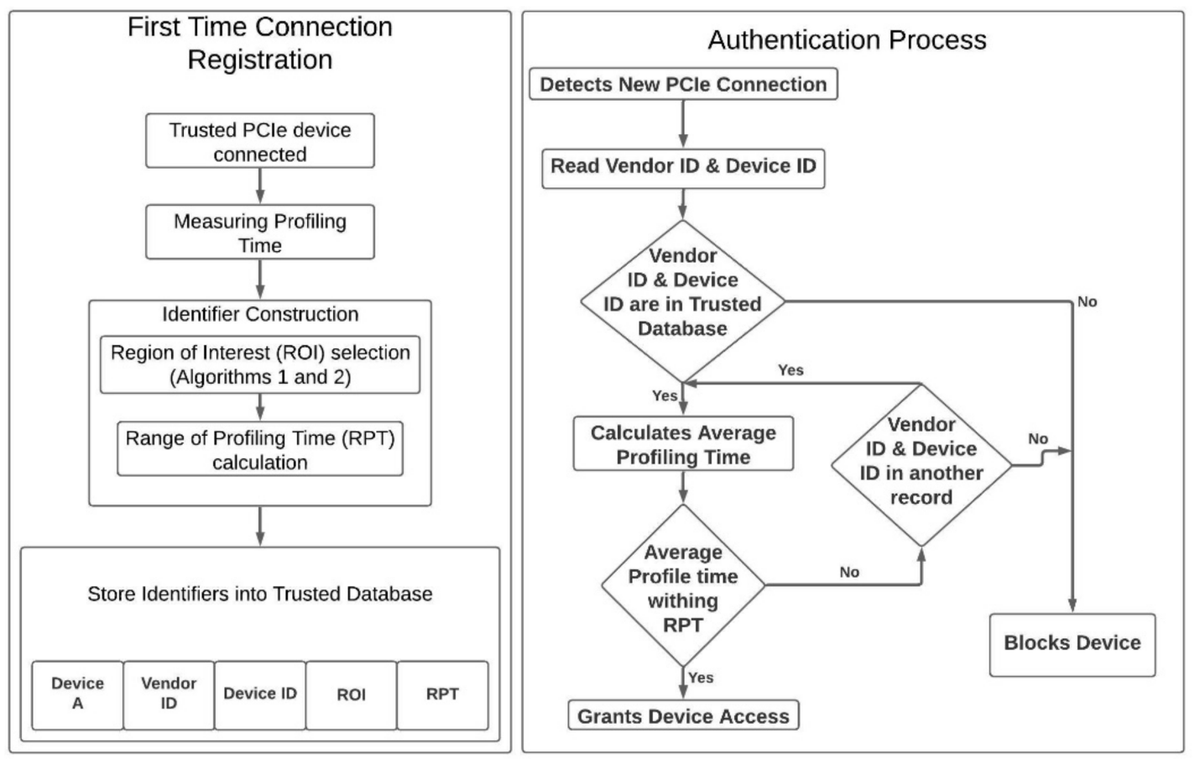
#CryptographyPaper A Delay-Based #Machine Learning #Model for DMA #Attack Mitigation by Yutian Gui, Chaitanya Bhure, Marcus Hughes and Fareena Saqib @SaqibFareena from Electrical and Computer Engineering, University of North Carolina at Charlotte read via: mdpi.com/2410-387X/5/3/…
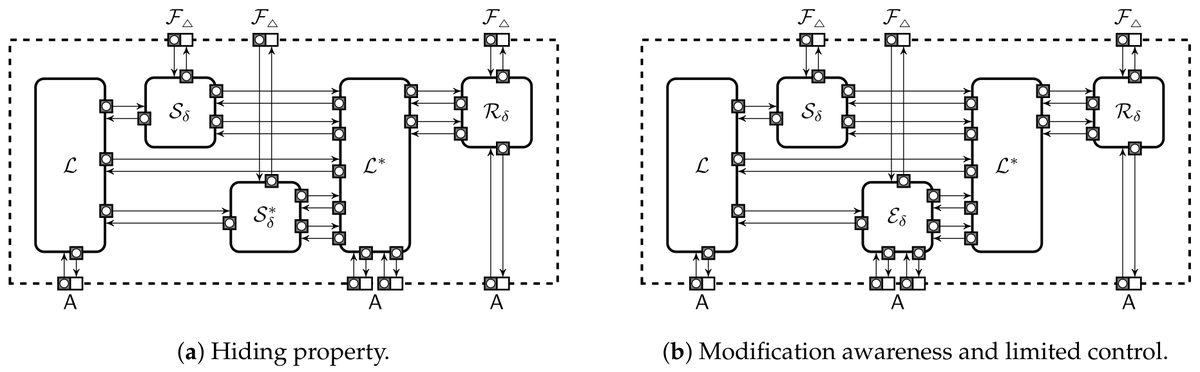
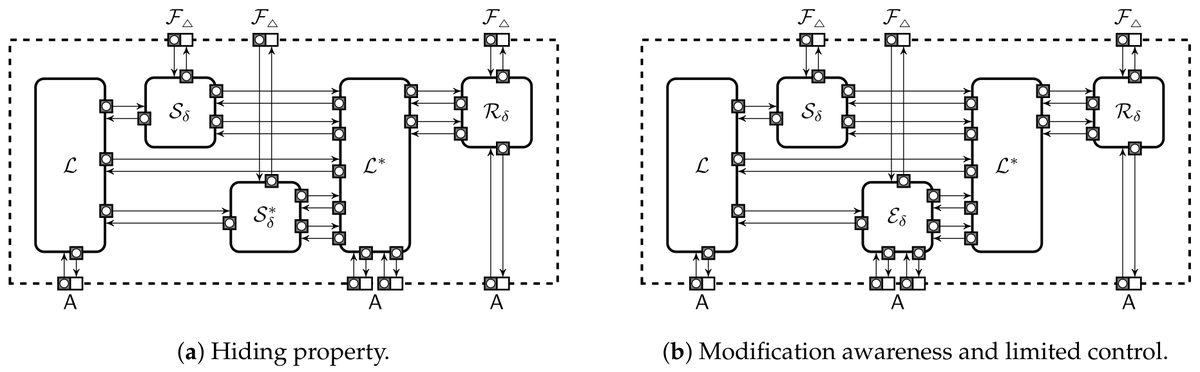
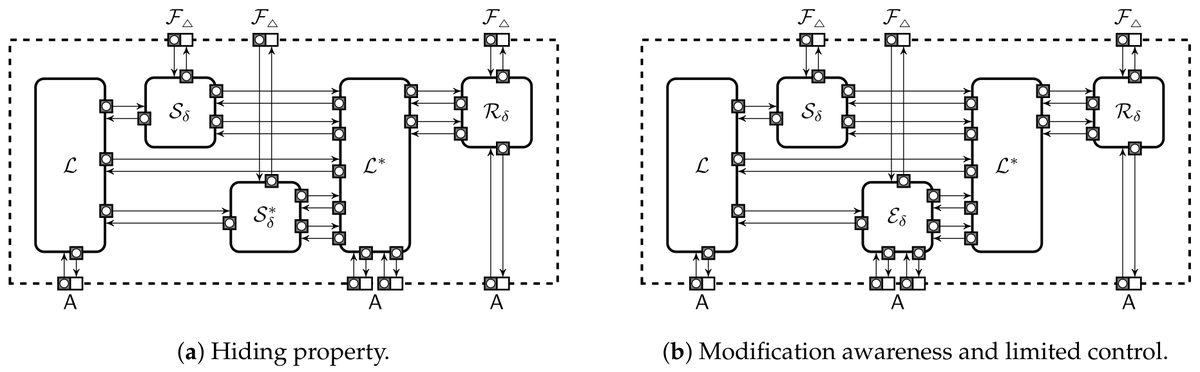
#CryptographyPaper Foundations of Programmable #Secure #Computation by Sven Laur and Pille Pullonen-Raudvere @pillepullonen from Institute of Computer Science, University of Tartu @unitartu Cybernetica AS, Estonia open access, welcome to read mdpi.com/2410-387X/5/3/…
#CryptographyPaper Implementing #Privacy-Preserving #Genotype Analysis with Consideration for Population Stratification by Andre Ostrak, Jaak Randmets, Ville Sokk, Sven Laur and Liina Kamm @liinakamm open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Fair and #Secure Multi-Party #Computation with Cheater Detection by Minhye Seo, from Department of Cyber Security, Duksung Women’s University open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper SC-DDPL as a #Countermeasure against Static #Power #Side-Channel #Attacks by Davide Bellizia, Riccardo Della Sala and Giuseppe Scotti ICTEAM/ELEN Crypto Group, Université Catholique de Louvain; DIET, Sapienza Università di Roma read via: mdpi.com/2410-387X/5/3/…
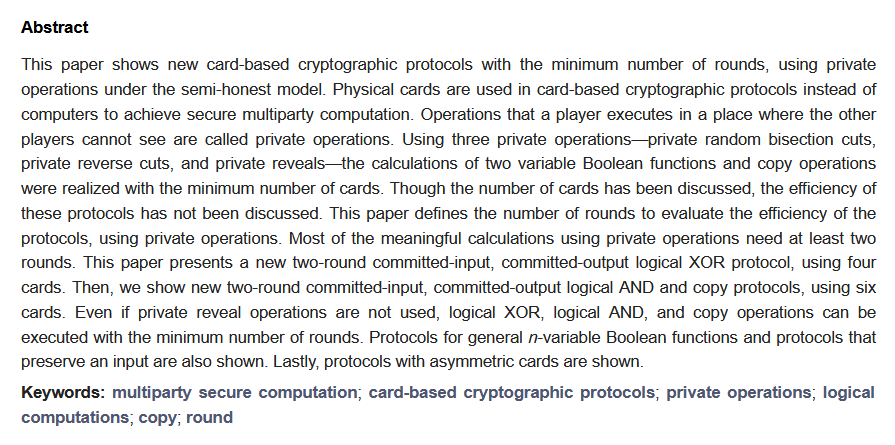
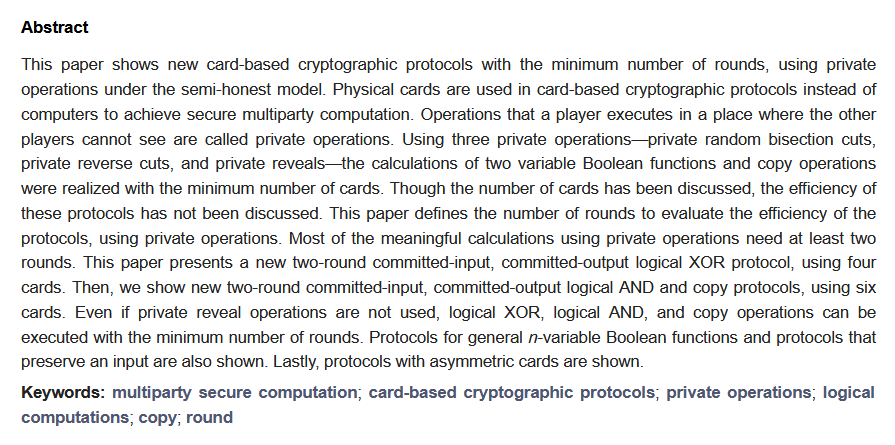
#CryptographyPaper Minimum Round Card-Based #Cryptographic #Protocols Using #Private Operations by Hibiki Ono and Yoshifumi Manabe from Faculty of Informatics, Kogakuin University 2 citations and 2309 views open access, welcome to read: mdpi.com/2410-387X/5/3/…
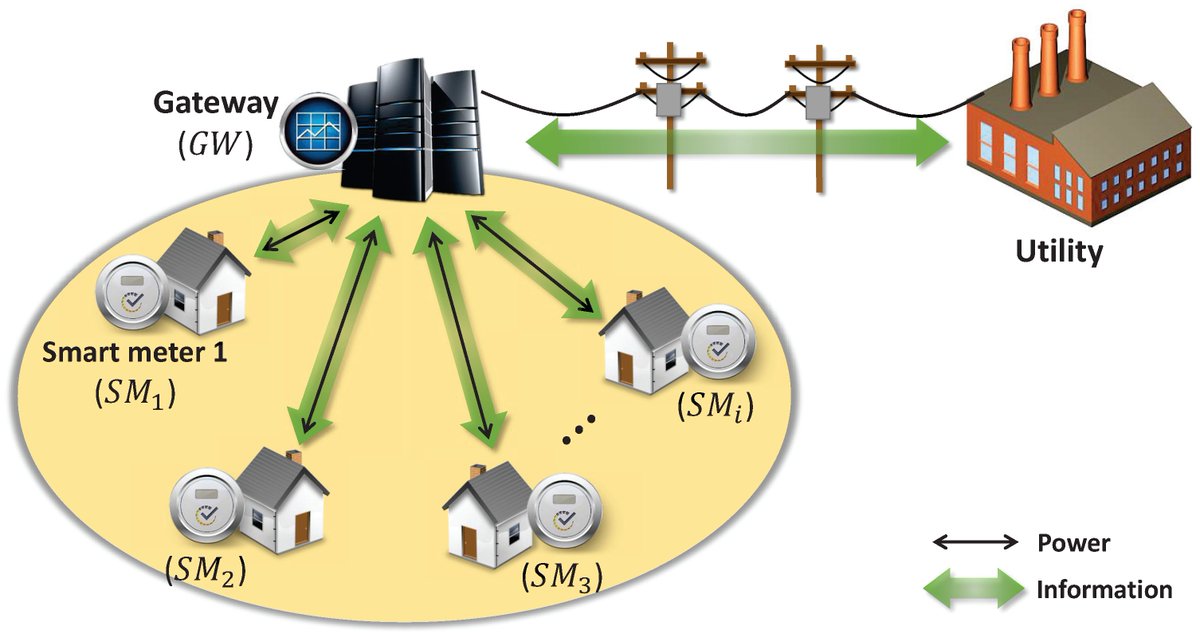
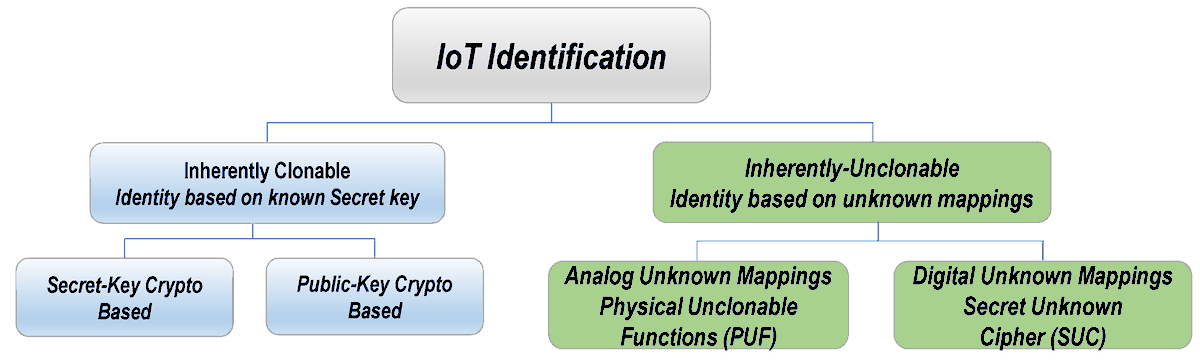
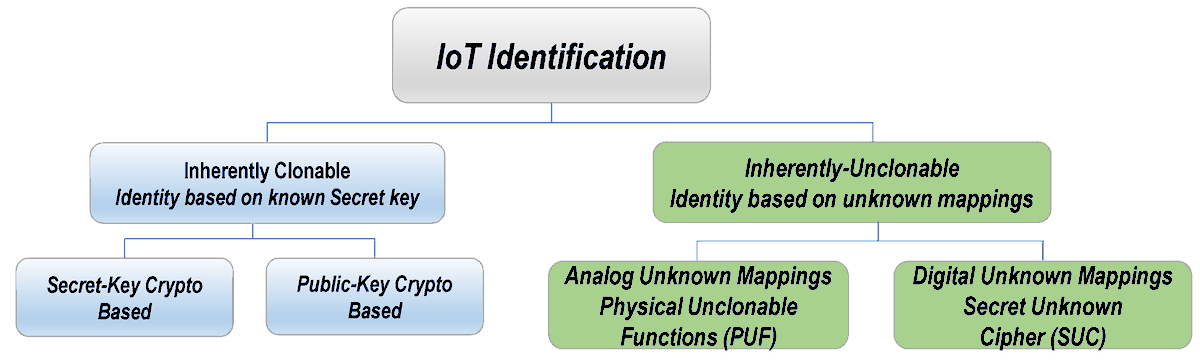
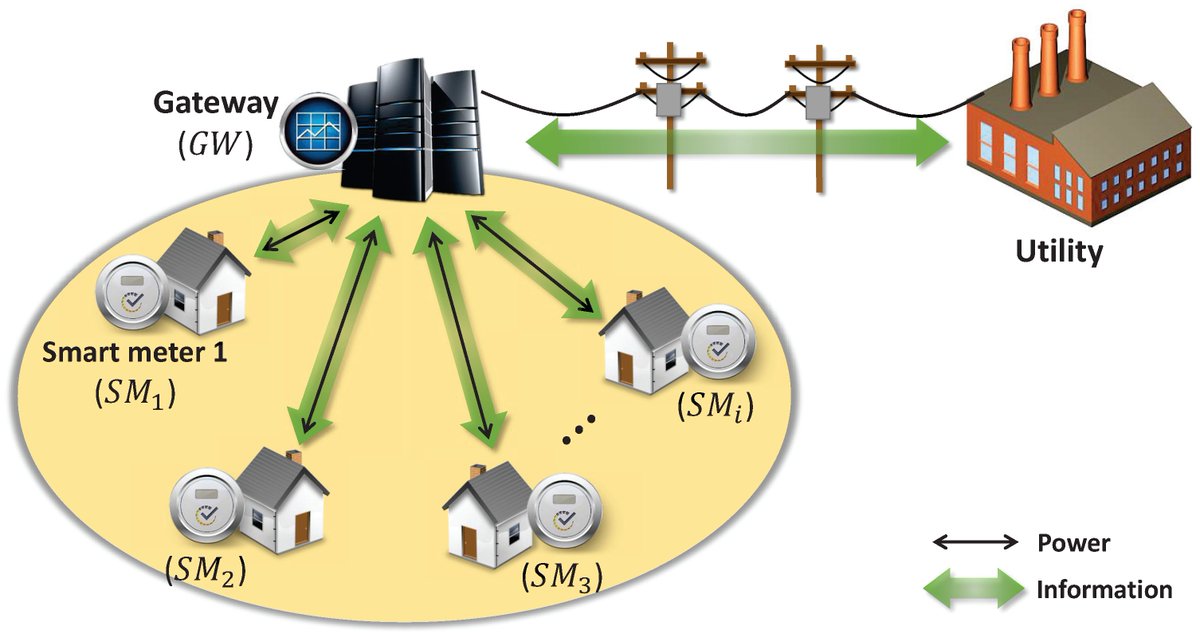
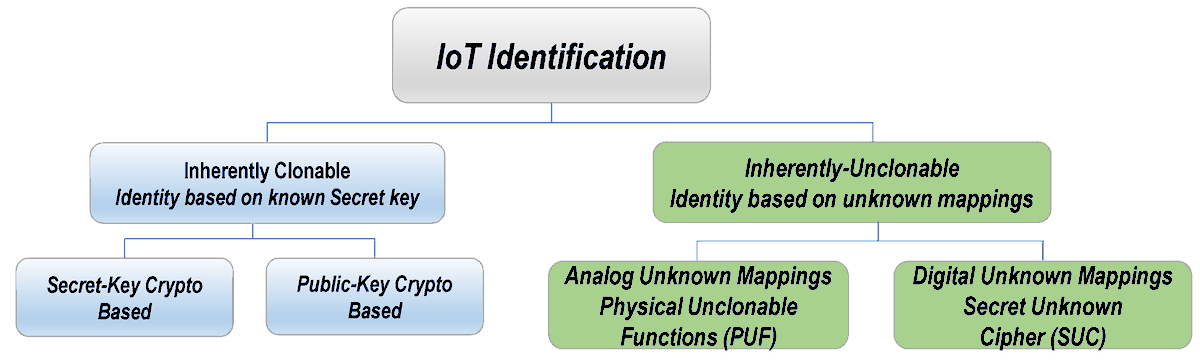
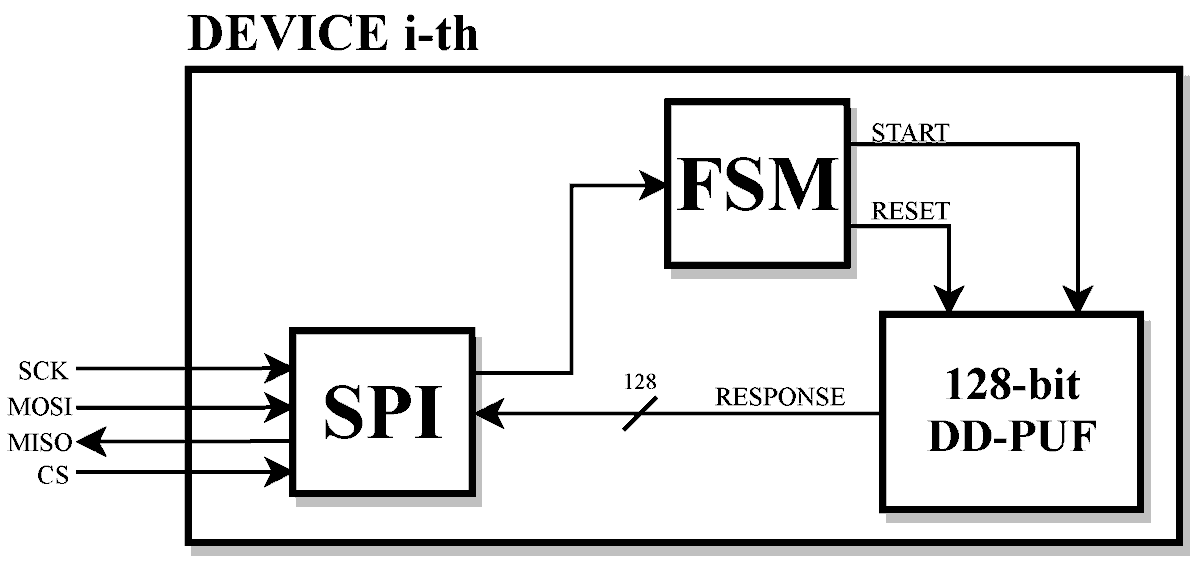
#CryptographyPaper Contemporary #Physical Clone-#Resistant Identity for #IoTs and Emerging Technologies by Emad Hamadaqa, Saleh Mulhem, Wael Adi and Mladen Berekovic from Technical University of Braunschweig; University of Lübeck welcome to read: mdpi.com/2410-387X/5/4/…
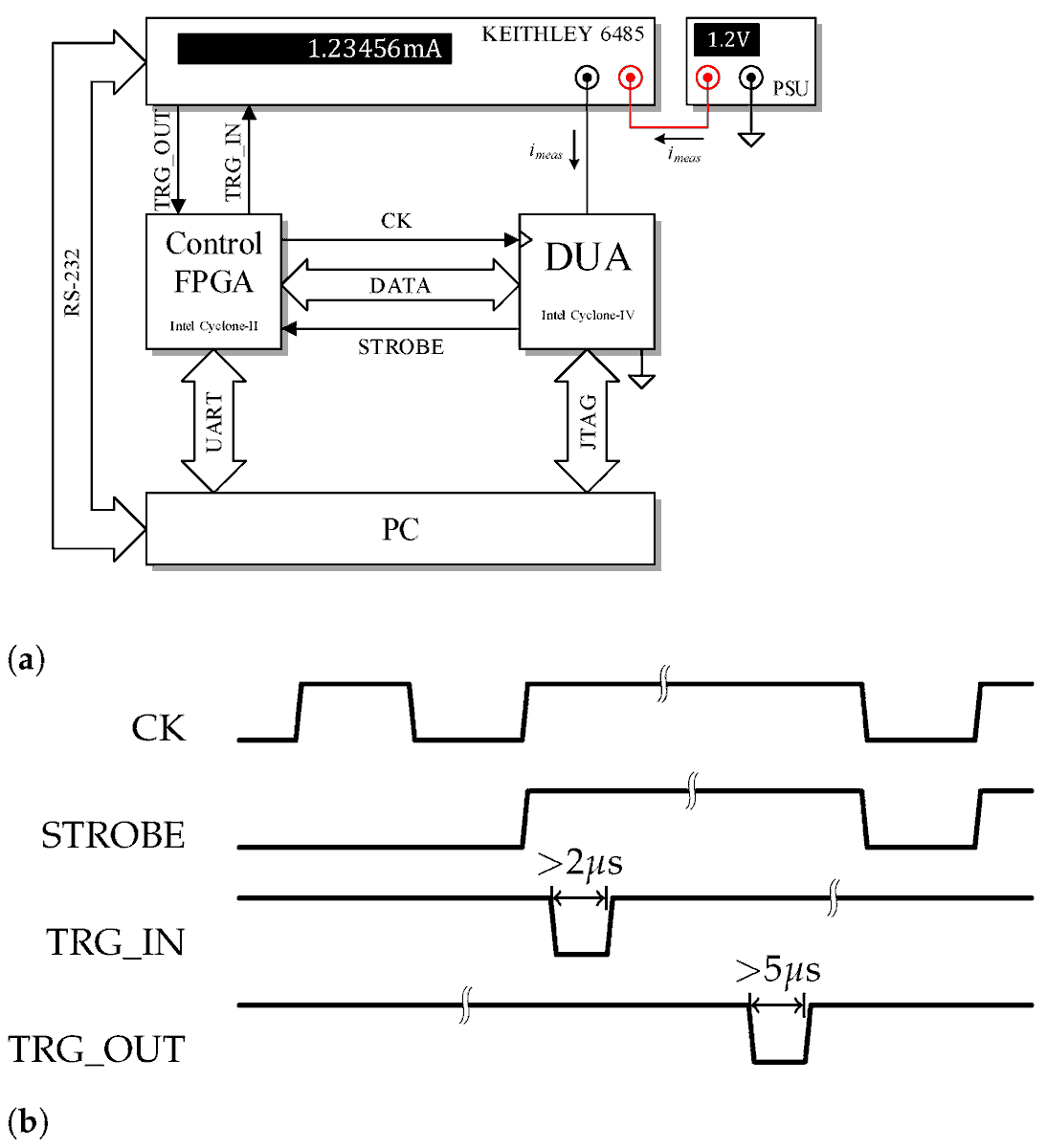
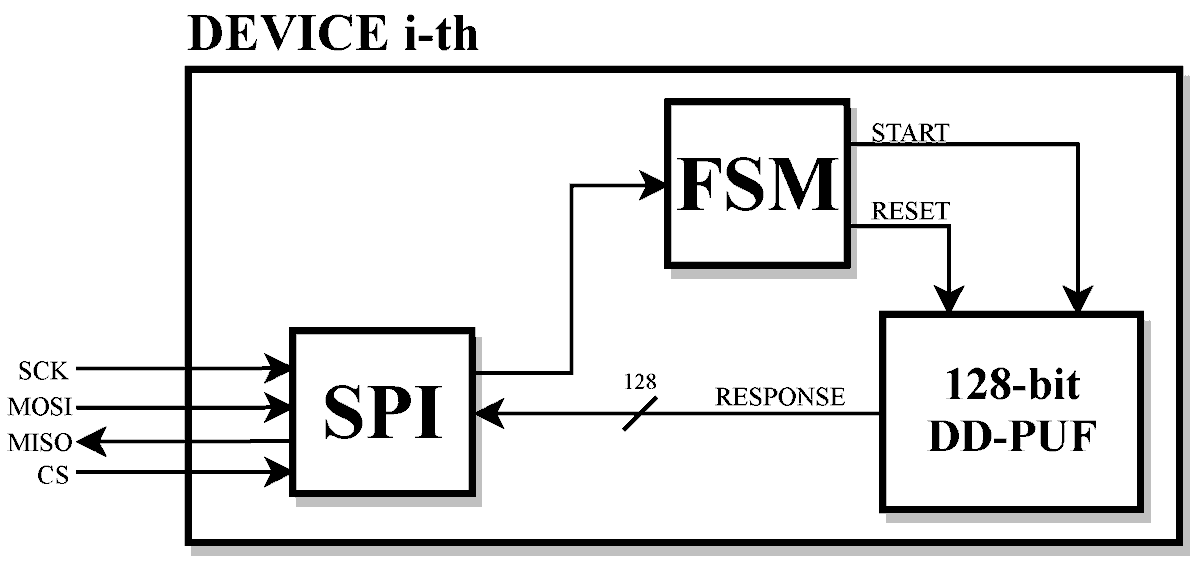
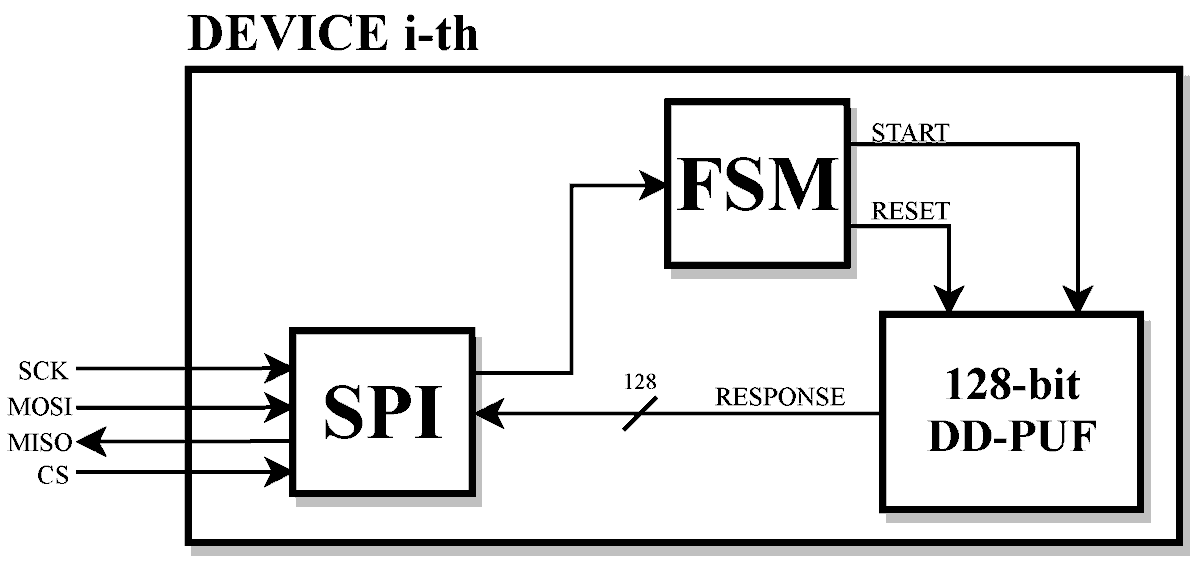
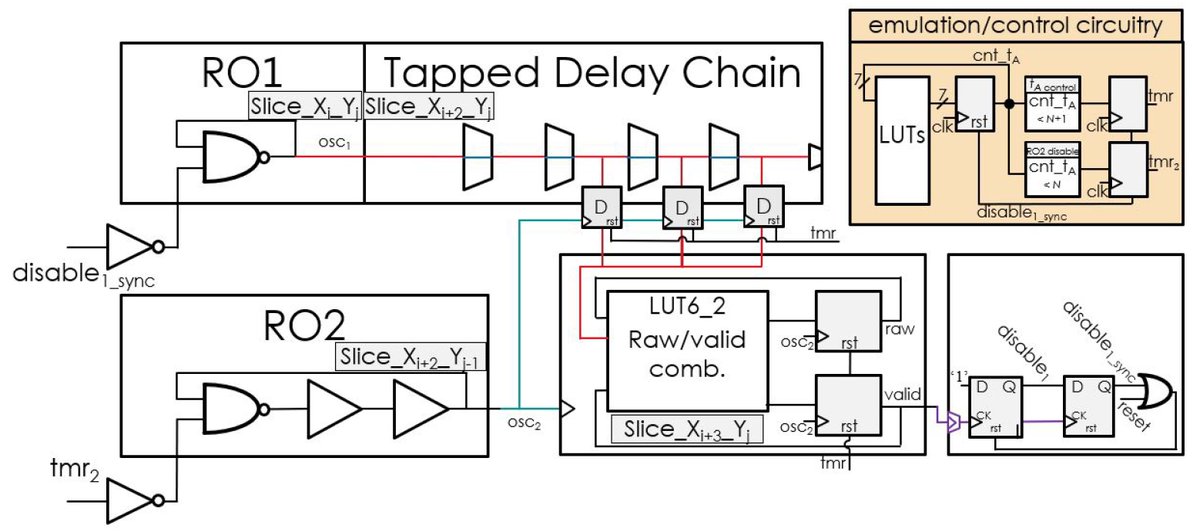
#CryptographyPaper A Novel Ultra-Compact #FPGA #PUF: The DD-PUF by Riccardo Della Sala @riccardodellas1, Davide Bellizia and Giuseppe Scotti from DIET, @SapienzaRoma ICTEAM/ELEN Crypto Group, @UCLouvain_be open access, welcome to read: mdpi.com/2410-387X/5/3/…
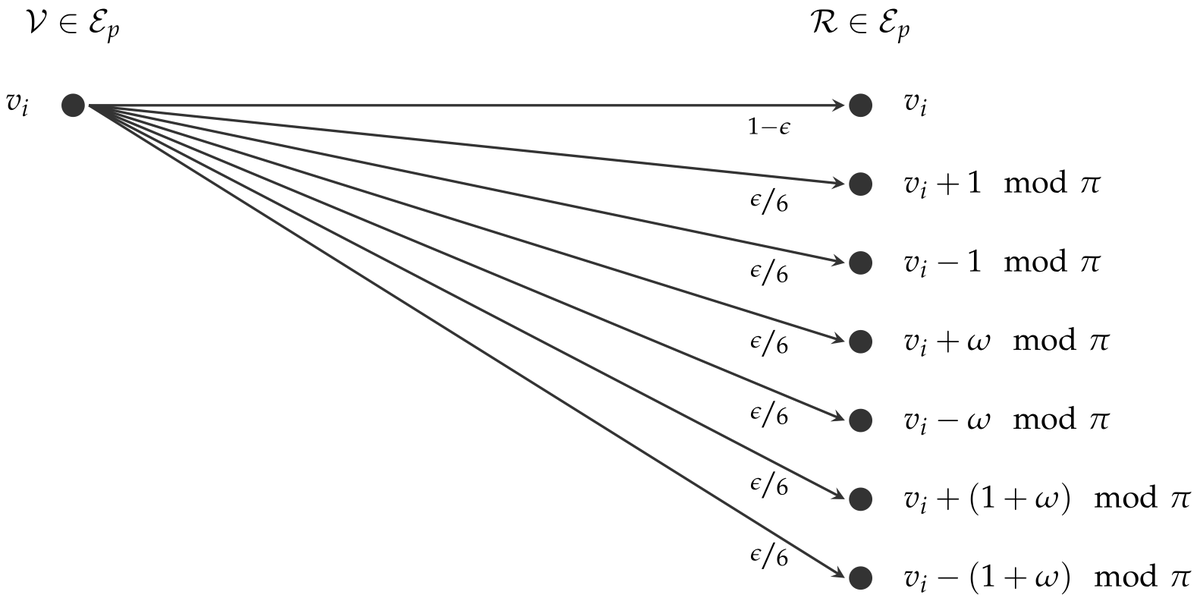
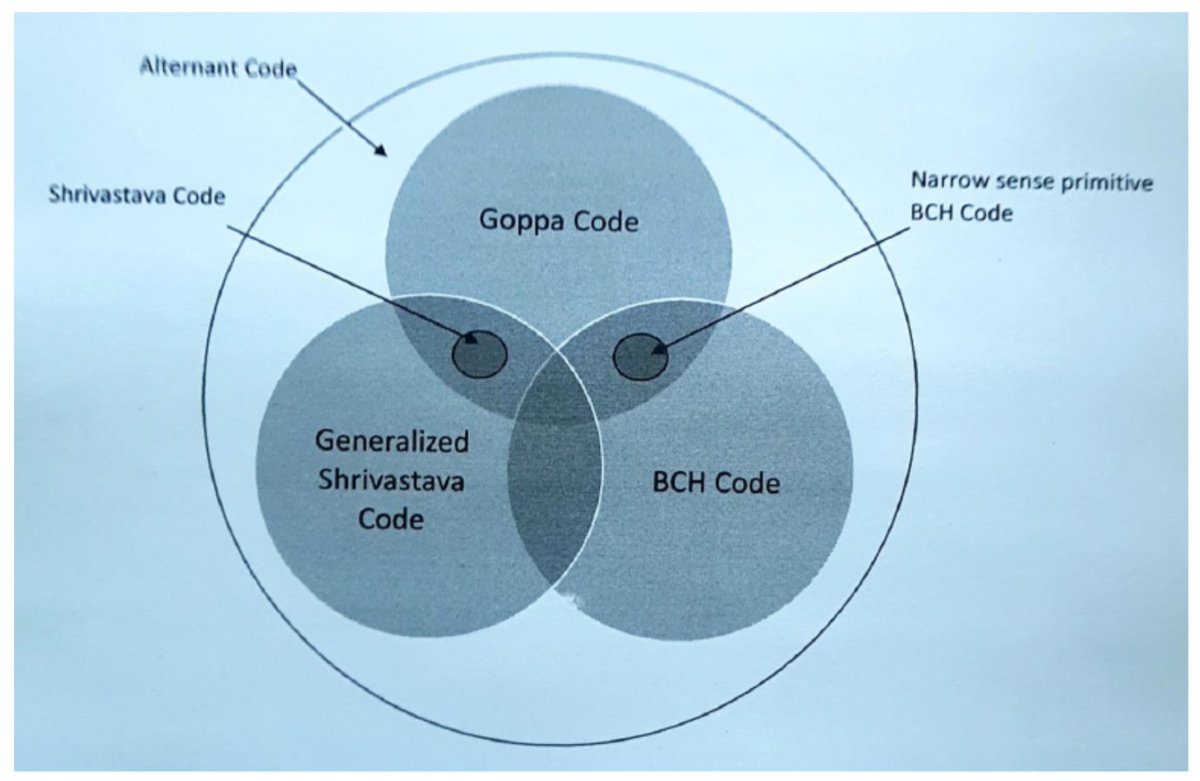
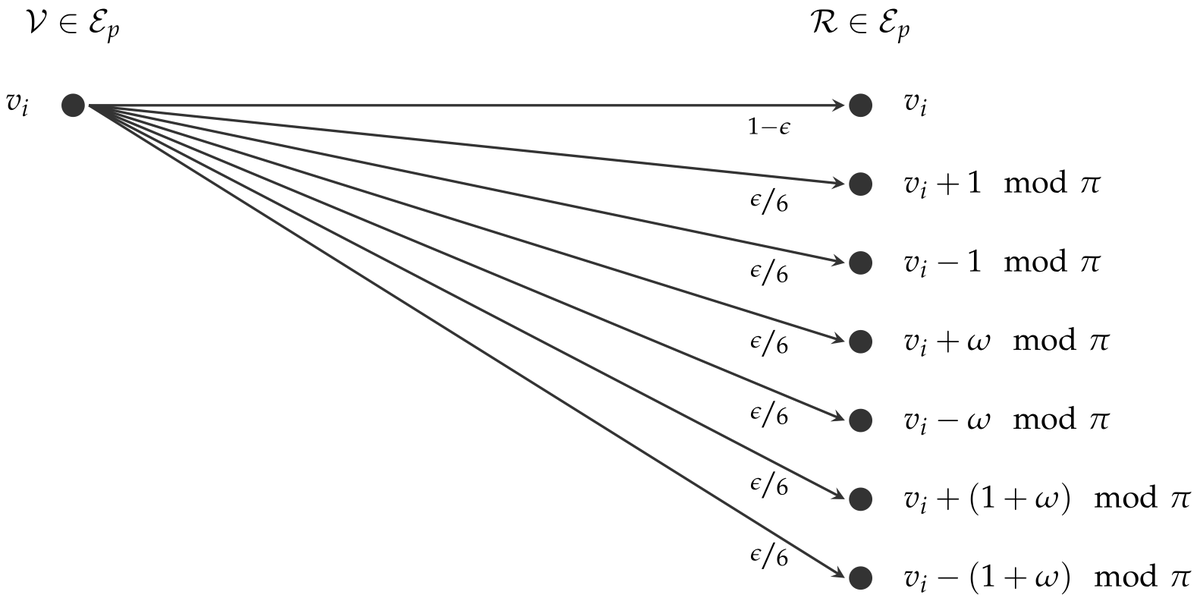
#CryptographyPaper Generalized Concatenated #Codes over #Gaussian and Eisenstein Integers for Code-Based Cryptography by Johann-Philipp Thiers and Jürgen Freudenberger from #ISD, #HTWG Konstanz, University of Applied Sciences open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper selected title story: Automated Classical Cipher Emulation Attacks via Unified Unsupervised Generative Adversarial Networks mdpi.com/2410-387X/7/3/… by Seonghwan Park, Hyunil Kim and Inkyu Moon
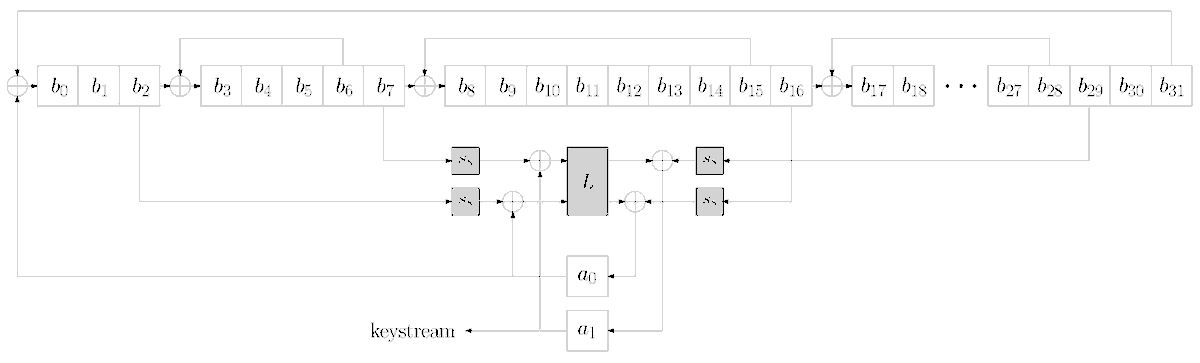
#CryptographyPaper A Fault #Attack on the Family of #Enocoro Stream #Ciphers by Julian Danner and Martin Kreuzer from Faculty of Informatics and Mathematics, University of Passau @UniPassau open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper Parallel #Privacy-Preserving Shortest Path #Algorithms by Mohammad Anagreh, Peeter Laud and Eero Vainikko Article Views 3142 Citations 4 welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper Improvements on Making #BKW Practical for Solving #LWE by Alessandro Budroni, Qian Guo, Thomas Johansson, Erik Mårtensson and Paul Stankovski Wagner Article Views 2424 Citations 1 open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper selected title story: SCANN: Side Channel Analysis of Spiking Neural Networks mdpi.com/2410-387X/7/2/…
#CryptographyPaper Contemporary #Physical Clone-#Resistant Identity for #IoTs and Emerging Technologies by Emad Hamadaqa, Saleh Mulhem, Wael Adi and Mladen Berekovic from Technical University of Braunschweig; University of Lübeck welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper Generalized Concatenated #Codes over #Gaussian and Eisenstein Integers for Code-Based Cryptography by Johann-Philipp Thiers and Jürgen Freudenberger from #ISD, #HTWG Konstanz, University of Applied Sciences open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper #Cryptography as the Means to #Protect #Fundamental Human Rights by Konstantinos Limniotis from Open University of Cyprus, Cyprus; Hellenic Data Protection Authority, Greece Views 5078; Citations 5 open access, welcome to read: mdpi.com/2410-387X/5/4/…

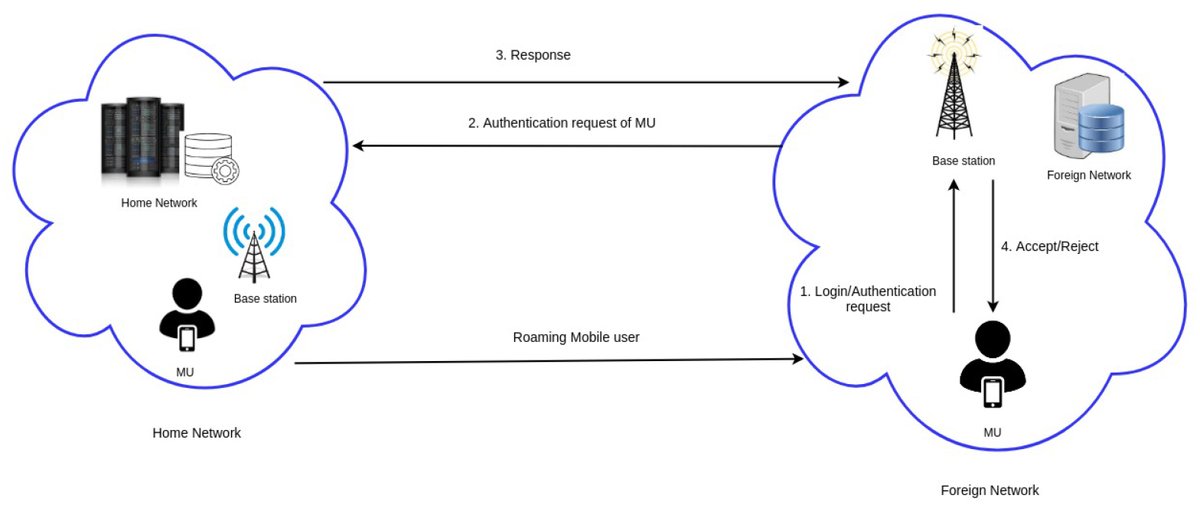
#CryptographyPaper ES-HAS: ECC-Based #Secure Handover #Authentication Scheme for Roaming Mobile User in Global Mobility #Networks by Suvidha K. S., Jothi Rangasamy, Shyam S. Kamath and Cheng-Chi Lee 2072 Views, 2 Citations open access, welcome to read: mdpi.com/2410-387X/5/4/…
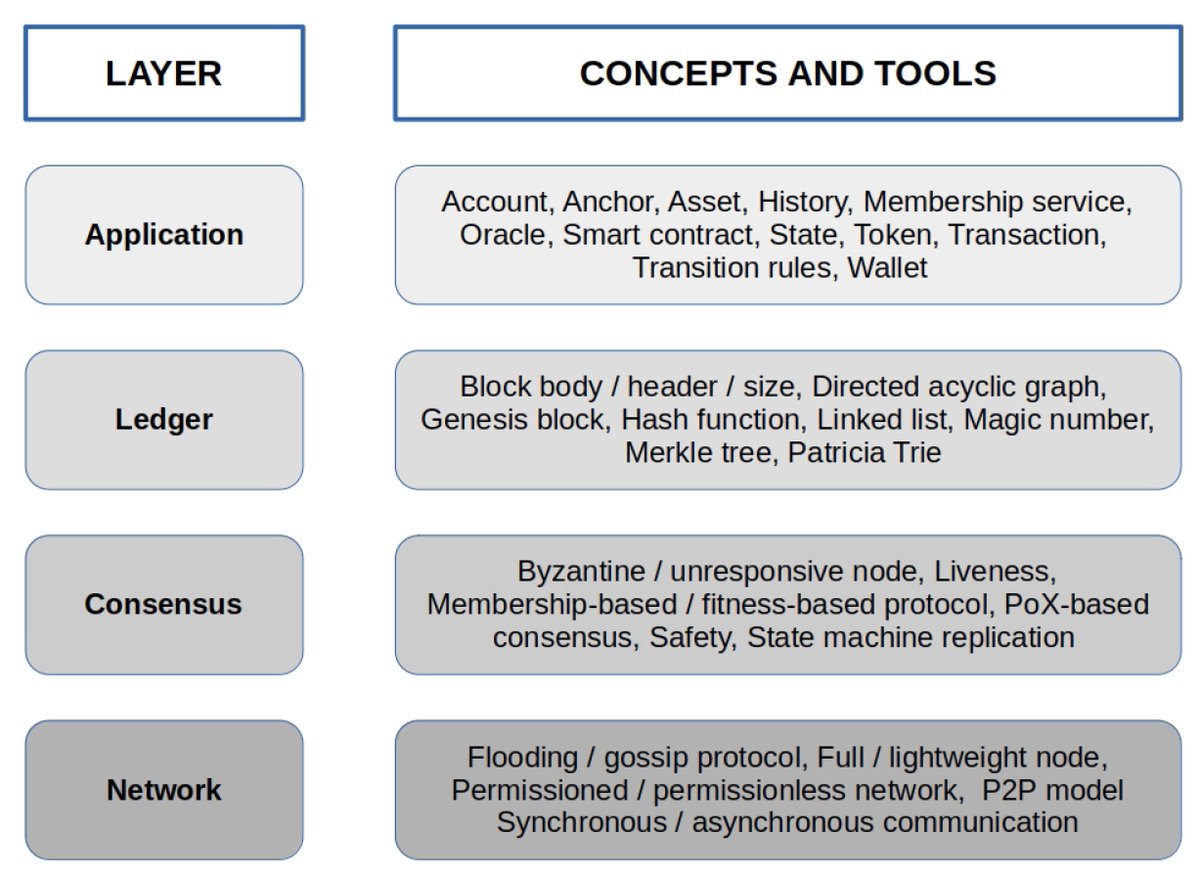
#CryptographyPaper Beyond #Bitcoin: Recent Trends and Perspectives in #Distributed Ledger Technology by Diego Romano and Giovanni Schmid from Istituto di Calcolo e Reti ad Alte Prestazioni 3801 Views, 4 Citations open access, welcome to read: mdpi.com/2410-387X/5/4/…
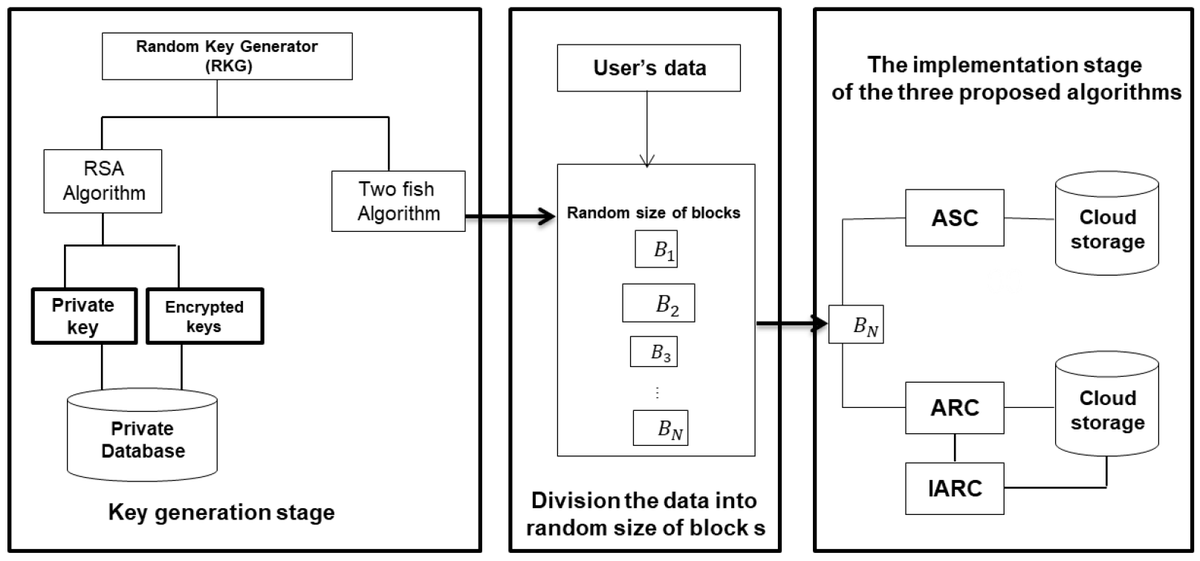
#CryptographyPaper A New Hybrid #Automated #Security Framework to #Cloud #Storage System by Noha E. El-Attar, Doaa S. El-Morshedy and Wael A. Awad Article Views: 3274 Citations: 2 open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper Post-Quantum and #Code-Based #Cryptography—Some Prospective Research Directions by Chithralekha Balamurugan, Kalpana Singh, Ganeshvani Ganesan and Muttukrishnan Rajarajan 4605 Views, 7 Citations open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper SC-DDPL as a #Countermeasure against Static #Power #Side-Channel #Attacks by Davide Bellizia, Riccardo Della Sala and Giuseppe Scotti ICTEAM/ELEN Crypto Group, Université Catholique de Louvain; DIET, Sapienza Università di Roma read via: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Minimum Round Card-Based #Cryptographic #Protocols Using #Private Operations by Hibiki Ono and Yoshifumi Manabe from Faculty of Informatics, Kogakuin University 2 citations and 2309 views open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper A Delay-Based #Machine Learning #Model for DMA #Attack Mitigation by Yutian Gui, Chaitanya Bhure, Marcus Hughes and Fareena Saqib @SaqibFareena from Electrical and Computer Engineering, University of North Carolina at Charlotte read via: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Fair and #Secure Multi-Party #Computation with Cheater Detection by Minhye Seo, from Department of Cyber Security, Duksung Women’s University open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Implementing #Privacy-Preserving #Genotype Analysis with Consideration for Population Stratification by Andre Ostrak, Jaak Randmets, Ville Sokk, Sven Laur and Liina Kamm @liinakamm open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Foundations of Programmable #Secure #Computation by Sven Laur and Pille Pullonen-Raudvere @pillepullonen from Institute of Computer Science, University of Tartu @unitartu Cybernetica AS, Estonia open access, welcome to read mdpi.com/2410-387X/5/3/…
#CryptographyPaper A Novel Ultra-Compact #FPGA #PUF: The DD-PUF by Riccardo Della Sala @riccardodellas1, Davide Bellizia and Giuseppe Scotti from DIET, @SapienzaRoma ICTEAM/ELEN Crypto Group, @UCLouvain_be open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Improved #Filtering Techniques for Single- and Multi-Trace Side-#Channel #Analysis by Dor Salomon, Amir Weiss and Itamar Levi from Bar-Ilan University (BIU) Massachusetts Institute of Technology (MIT) open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper A Delay-Based #Machine Learning #Model for DMA #Attack Mitigation by Yutian Gui, Chaitanya Bhure, Marcus Hughes and Fareena Saqib @SaqibFareena from Electrical and Computer Engineering, University of North Carolina at Charlotte read via: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Contemporary #Physical Clone-#Resistant Identity for #IoTs and Emerging Technologies by Emad Hamadaqa, Saleh Mulhem, Wael Adi and Mladen Berekovic from Technical University of Braunschweig; University of Lübeck welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper SC-DDPL as a #Countermeasure against Static #Power #Side-Channel #Attacks by Davide Bellizia, Riccardo Della Sala and Giuseppe Scotti ICTEAM/ELEN Crypto Group, Université Catholique de Louvain; DIET, Sapienza Università di Roma read via: mdpi.com/2410-387X/5/3/…
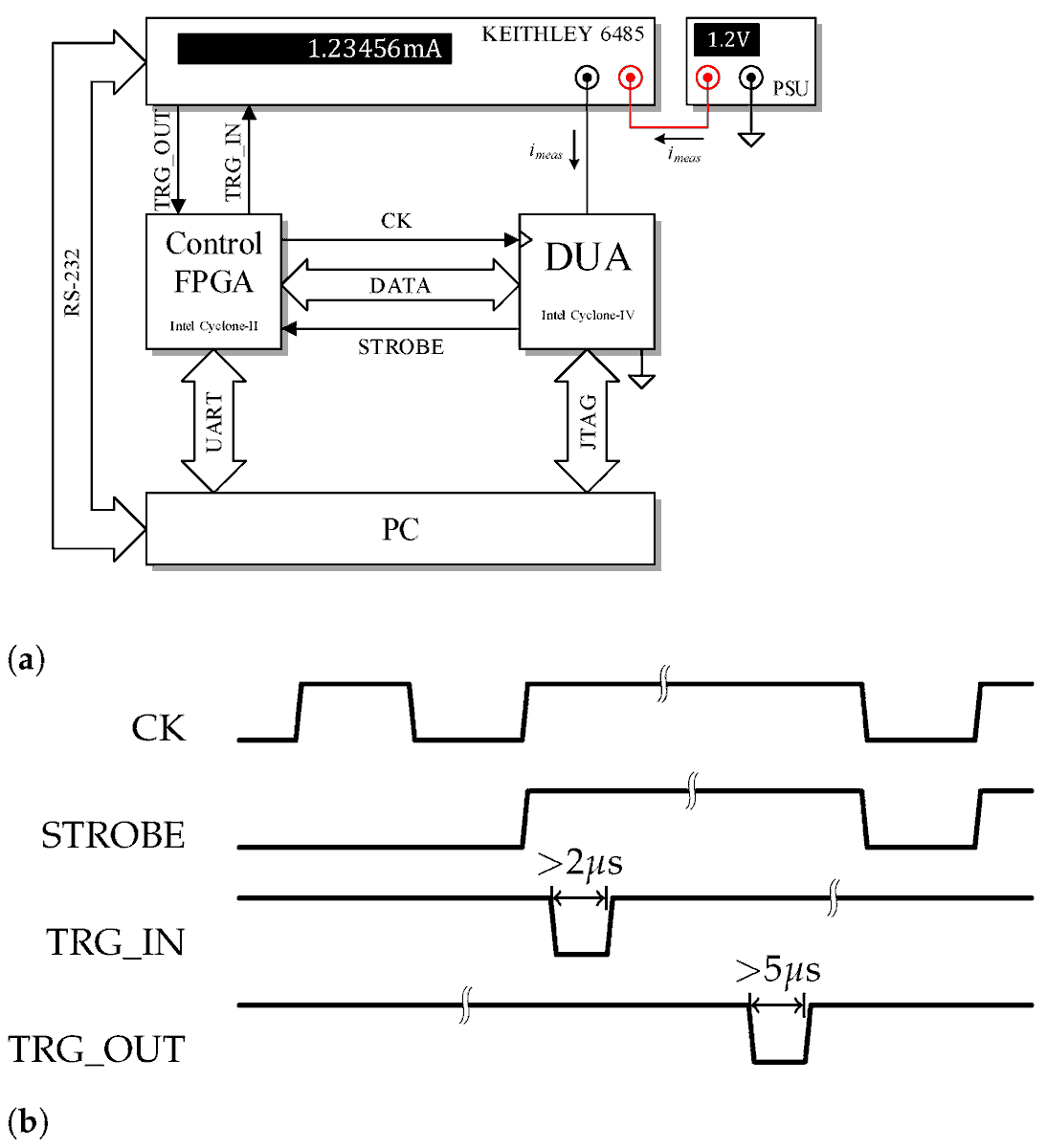
#CryptographyPaper Improved #Filtering Techniques for Single- and Multi-Trace Side-#Channel #Analysis by Dor Salomon, Amir Weiss and Itamar Levi from Bar-Ilan University (BIU) Massachusetts Institute of Technology (MIT) open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Minimum Round Card-Based #Cryptographic #Protocols Using #Private Operations by Hibiki Ono and Yoshifumi Manabe from Faculty of Informatics, Kogakuin University 2 citations and 2309 views open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper The Cost of a True #Random Bit—On the Electronic Cost Gain of ASIC Time-Domain-Based #TRNGs by Netanel Klein, Eyal Harel and Itamar Levi from Faculty of Engineering, Bar-Ilan University (BIU) open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Generalized Concatenated #Codes over #Gaussian and Eisenstein Integers for Code-Based Cryptography by Johann-Philipp Thiers and Jürgen Freudenberger from #ISD, #HTWG Konstanz, University of Applied Sciences open access, welcome to read: mdpi.com/2410-387X/5/4/…
#CryptographyPaper A Novel Ultra-Compact #FPGA #PUF: The DD-PUF by Riccardo Della Sala @riccardodellas1, Davide Bellizia and Giuseppe Scotti from DIET, @SapienzaRoma ICTEAM/ELEN Crypto Group, @UCLouvain_be open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper Foundations of Programmable #Secure #Computation by Sven Laur and Pille Pullonen-Raudvere @pillepullonen from Institute of Computer Science, University of Tartu @unitartu Cybernetica AS, Estonia open access, welcome to read mdpi.com/2410-387X/5/3/…
#CryptographyPaper Fair and #Secure Multi-Party #Computation with Cheater Detection by Minhye Seo, from Department of Cyber Security, Duksung Women’s University open access, welcome to read: mdpi.com/2410-387X/5/3/…
#CryptographyPaper selected title story: SCANN: Side Channel Analysis of Spiking Neural Networks mdpi.com/2410-387X/7/2/…
Something went wrong.
Something went wrong.
United States Trends
- 1. Lakers N/A
- 2. Luka N/A
- 3. Luka N/A
- 4. Theo N/A
- 5. MARK LEE N/A
- 6. #thepitt N/A
- 7. MARK IS LEAVING NCT N/A
- 8. Memphis N/A
- 9. Come Over N/A
- 10. Thunder N/A
- 11. Bronny N/A
- 12. Lu Dort N/A
- 13. Tiny Tim N/A
- 14. Daniel Susac N/A
- 15. #RHORI N/A
- 16. Good Friday N/A
- 17. #criticalrolespoilers N/A
- 18. Hegseth N/A
- 19. David Peterson N/A
- 20. Generals N/A

