step1nx
@step1nx
Hacking & Learning is a way to live life #🥨
Vous pourriez aimer
Check this out! An open source project made with quality and ready to use! Cc. Thanks @tarekouldcheikh for your contribution to the info sec community over the years! cognito-api.com
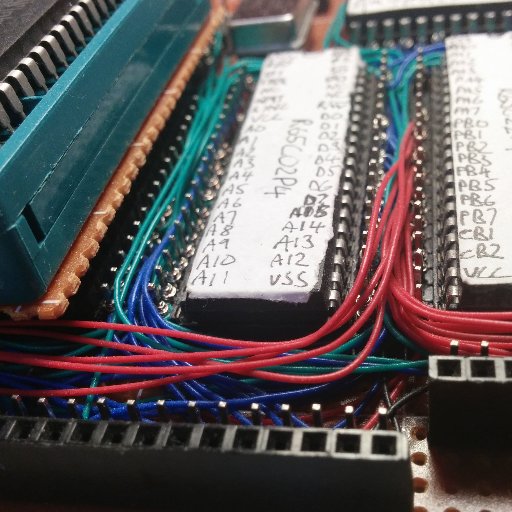
Side channel attacks for breaking the firmware encryption on ESP32 courk.cc/breaking-flash… #infosec #espressif


🧵1/2 MIT's Charles Leiserson lectures on how C code is compiled into assembly and machine code, leading to hardware-level execution. 👇 Full MIT Performance Engineering of Software Systems Course in C and Assembly👇
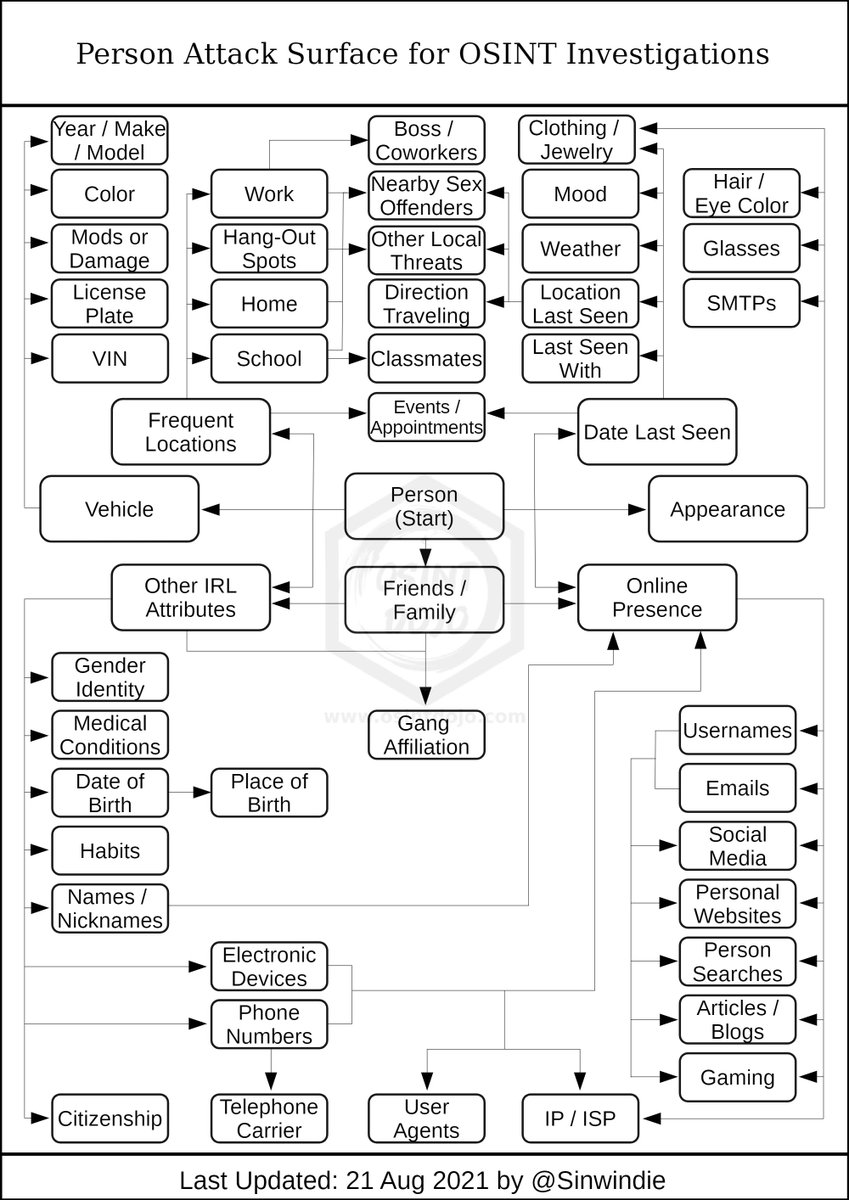
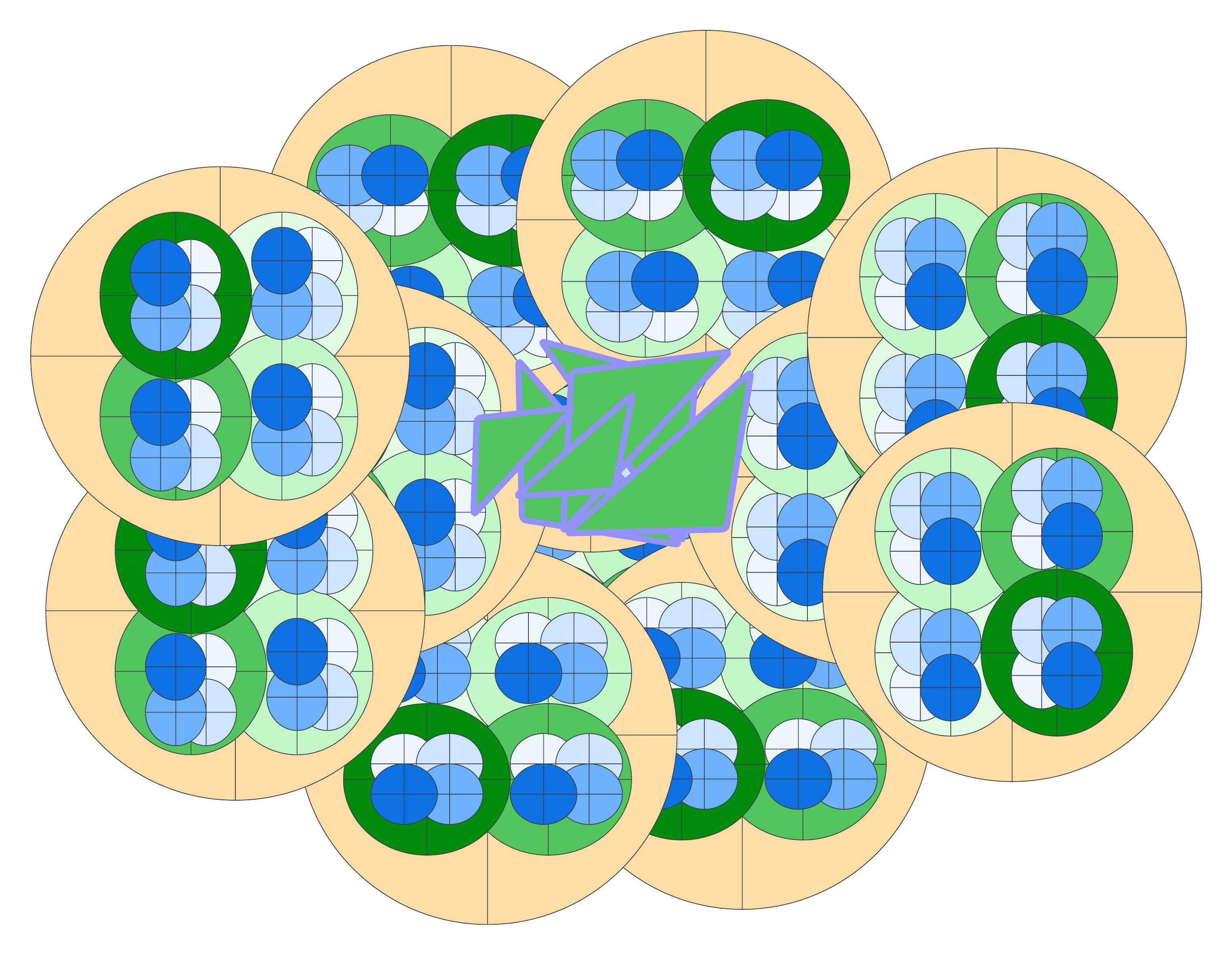
Person Attack Surface for OSINT Investigations Credit: @sinwindie #cybersecurity #infosec #OSINT
🚨We could bypass authentication to thousands of applications by exploiting a configuration-based vulnerability in AWS ALB. Here’s everything you need to know about the #ALBeast vulnerability discovered by @MiggoSecurity

Exploiting GitHub Actions jobs by registering a rogue #CICD runner to exfiltrate secrets, @hugow_vincent developed a tool for a real engagement, successfully compromising the GitHub organization! synacktiv.com/publications/h…
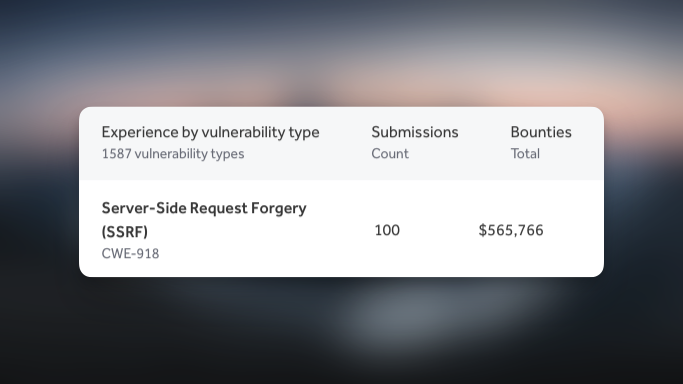
I've made $500k+ from SSRF vulnerabilities. Here are my tricks:
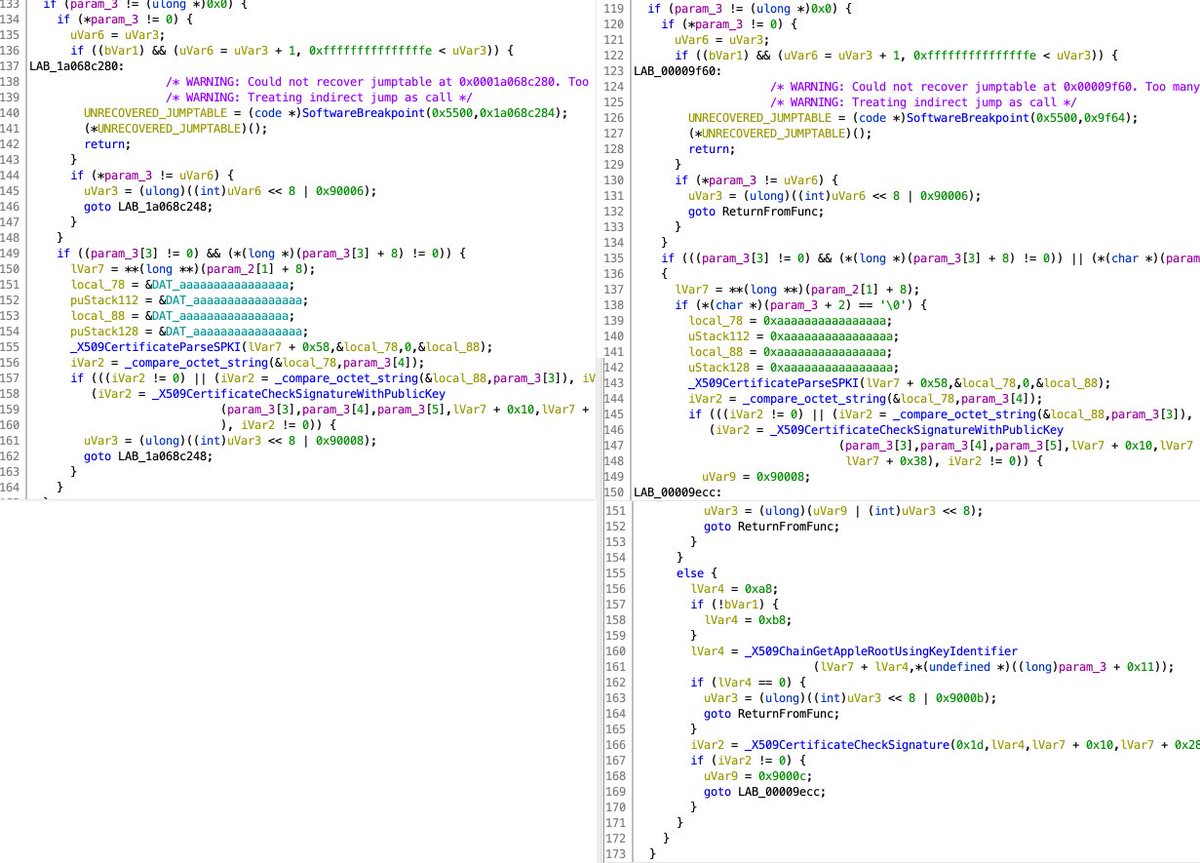
CVE-2022-26766: the CoreTrust bug "For years, macOS allowed any root certificate when checking code signatures, making code signing completely useless." // bug discovered by @LinusHenze // writeup by @zhuowei worthdoingbadly.com/coretrust/
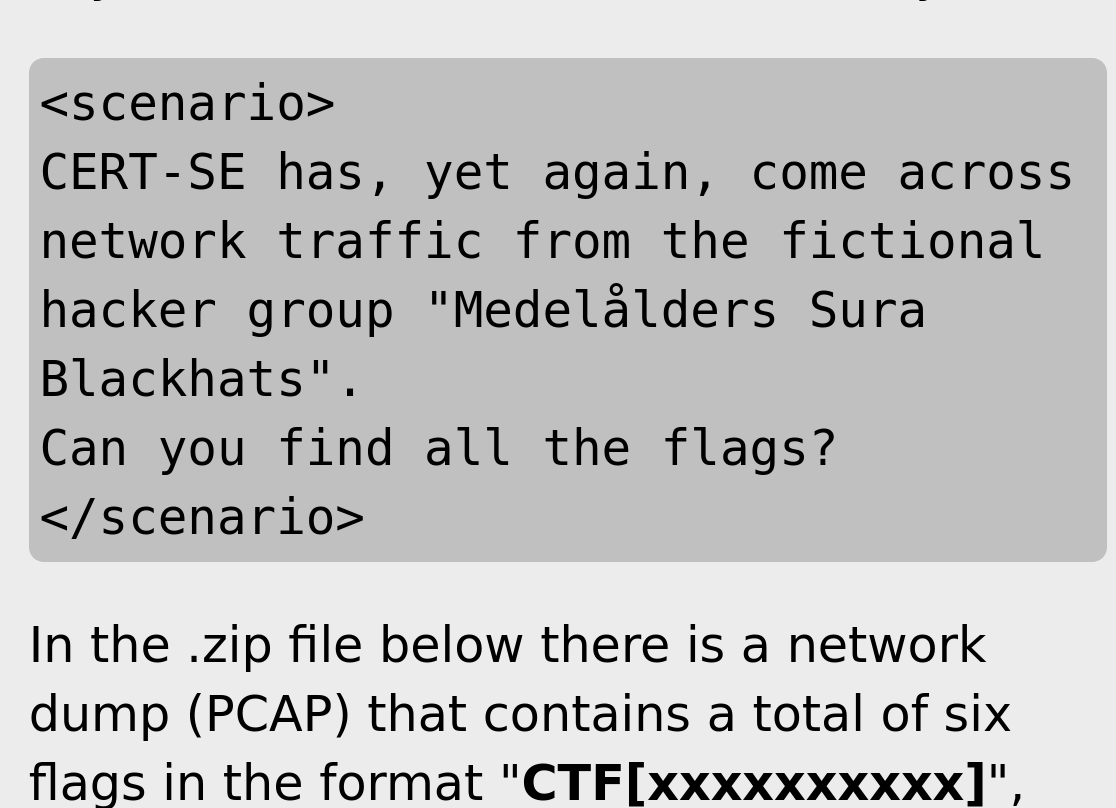
The Swedish National CERT @cert_se has released a new CTF. The challenge is to find six flags in a PCAP file. cert.se/2022/09/cert-s…
The Linux Booting Process Explained 🐧↓
I just released the source code of Paracosme: a zero-click remote memory corruption exploit I demonstrated at Pwn2Own 2022 Miami 🐛🐜🪲 github.com/0vercl0k/parac…
Here is the writeup for the io_uring Use-After-Free which @pqlqpql and me exploited in the kCTF VRP! We hope you enjoy :) ruia-ruia.github.io/2022/08/05/CVE…
Awesooooooome
Hello 😀 Vous l'attendiez tous, on organise un meet "Not Before LeHack" car il sera pendant, le Vendredi 24 Juin à partir de 18h30, voici le lien pour vous inscrire 😉 framadate.org/PiEl4NlVM4n6qA… #infosec #rtfm #lehack
Always impressed when seeing Hotel Card key with Mifare Ultralight EV1 🥳 Always depressed when seeing it is configured with: - pages don't need authentication - Unlimited password attempts - Found default password FF FF FF FF 🙄 Integrators can try to be serious? #proxmark3 😍
United States Tendances
- 1. #SurvivorSeries 101K posts
- 2. Auburn 18.1K posts
- 3. Liv Morgan 21.9K posts
- 4. Vandy 15.2K posts
- 5. John Cena 26.7K posts
- 6. Ty Simpson 1,836 posts
- 7. Nikki 30.9K posts
- 8. Bama 17.7K posts
- 9. Roxanne 5,736 posts
- 10. Norvell 5,033 posts
- 11. Oklahoma 31.6K posts
- 12. Lash Legend 6,600 posts
- 13. Rhea 18.6K posts
- 14. Mateer 7,890 posts
- 15. Stephanie Vaquer 5,743 posts
- 16. Tim Banks 3,181 posts
- 17. Dirty Dom 1,353 posts
- 18. #RollTide 2,188 posts
- 19. Heupel 3,150 posts
- 20. Tennessee 43.6K posts
Something went wrong.
Something went wrong.













































![KaliLinuxfr's profile picture. Communauté Francophone Kali linux - Tutoriels de hacking et Pentest. [White hacking only]](https://pbs.twimg.com/profile_images/1148009148090593280/Wu3gZ0Dr.png)