#cybersecurity search results
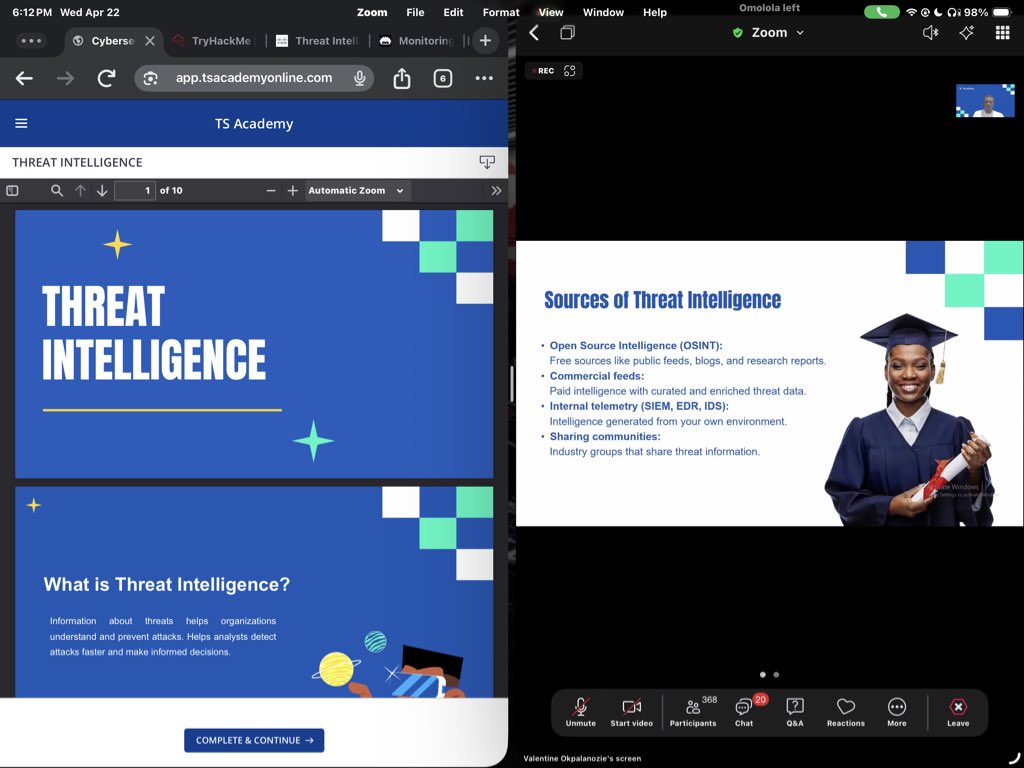
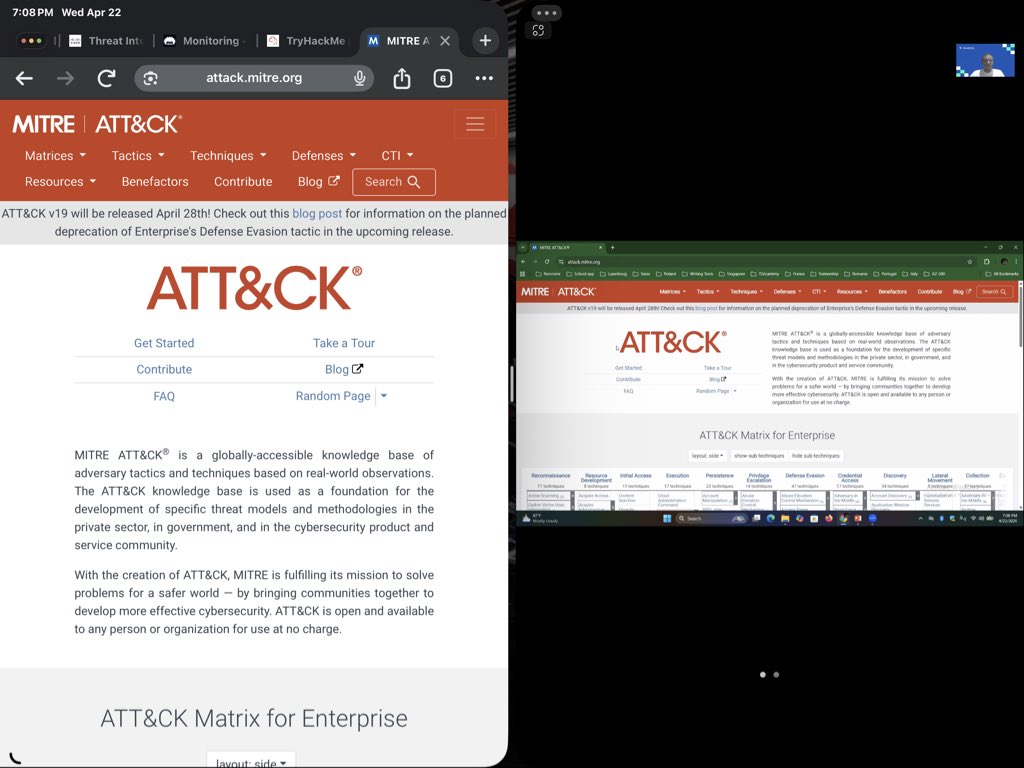
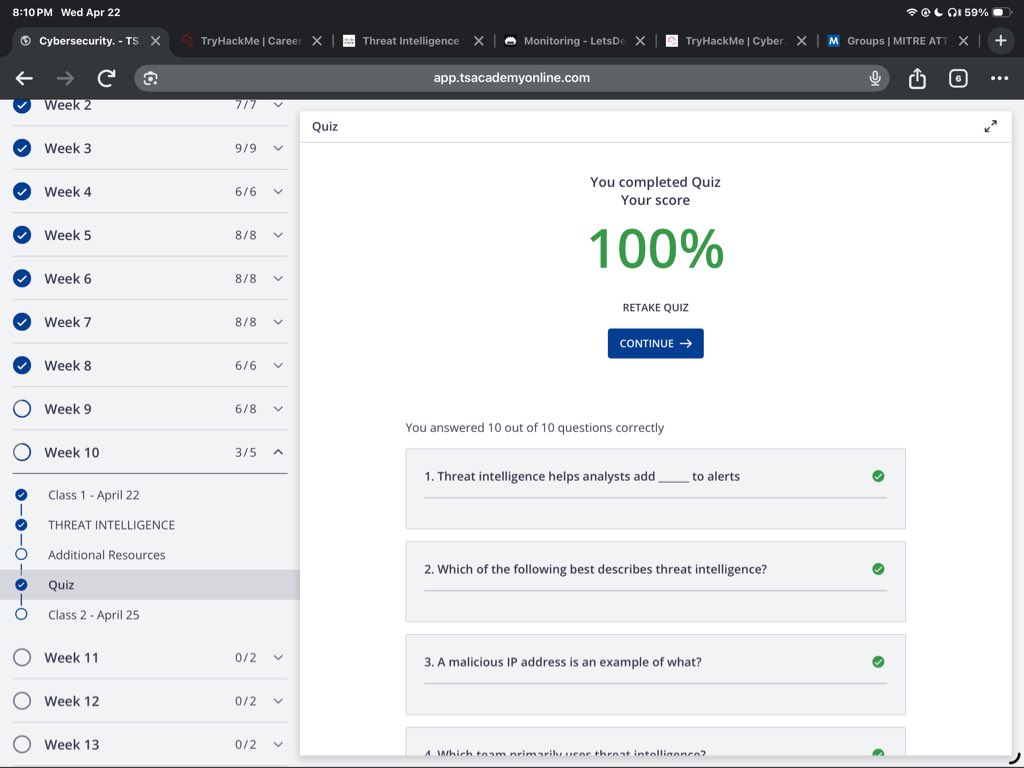
Explored Threat Intelligence in class today, including the MITRE ATT&CK matrix, tactics vs techniques, CTI groups, and defenses. Learning how defenders map adversary behavior is changing how I view security. @TechSphereAcad @thompsonever #CyberSecurity #ThreatIntelligence #SOC
#AICoding tools are boosting dev productivity like never before—but are teams keeping #Cybersecurity front & center? CTO @mmadou recommends using "trust scores" to measure AI usage, vulnerabilities & #SecureCoding skills to reduce #SDLC risk. Learn more: ow.ly/28ca50YO5v9
Microsoft issues emergency update for macOS and Linux ASP.NET threat arstechnica.com/security/2026/… #cybersecurity #computerscience #computerengineering
I just solved Operation Blackout 2025: Smoke & Mirrors on Hack The Box! labs.hackthebox.com/achievement/sh… #HackTheBox #HTB #CyberSecurity #EthicalHacking #InfoSec #PenTesting
Have you got the Icopy ID1 Cards – Genuine iCopy-XS & iCopy-X cards? link.ksec.co.uk/4d921n #cybersecurity #hackers #rfid #infosec #security #ksec #redteam #edc #edcgear
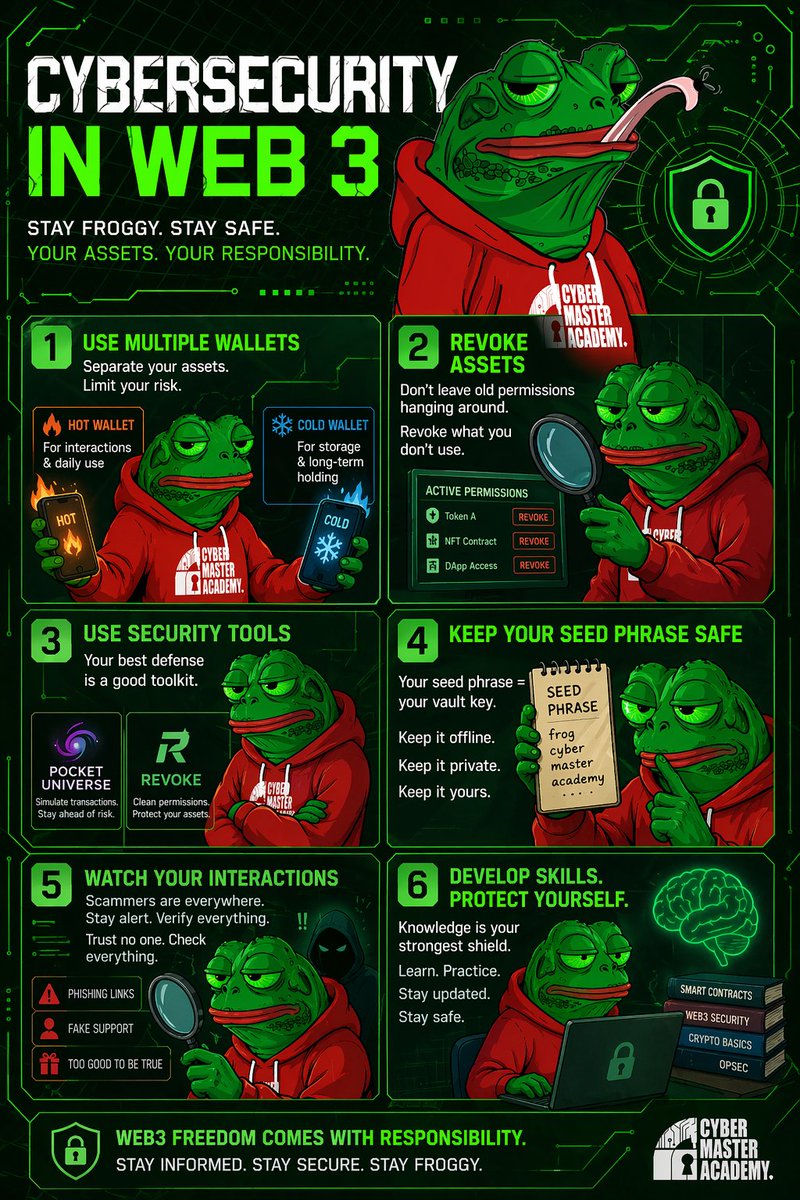
Make sure to follow @CyberMasterMSc for top #Cybersecurity tips on how to keep your assets safe in web3
🚨 Cybersecurity in Web3 isn’t optional — it’s survival. Here’s how to protect your assets: 1️⃣ Use multiple wallets 2️⃣ Revoke what you don’t use 3️⃣ Use security tools 4️⃣ Protect your seed phrase 5️⃣ Watch every interaction 6️⃣ Keep learning Don’t get rekt — get secure.
I just solved Brutus on Hack The Box! labs.hackthebox.com/achievement/sh… #HackTheBox #HTB #CyberSecurity #EthicalHacking #InfoSec #PenTesting
I just solved Operation Blackout 2025: Phantom Check on Hack The Box! labs.hackthebox.com/achievement/sh… #HackTheBox #HTB #CyberSecurity #EthicalHacking #InfoSec #PenTesting
labs.hackthebox.com
Solved Operation Blackout 2025: Phantom Check from Hack The Box!
I have just solved sherlock Operation Blackout 2025: Phantom Check from Hack The Box
متخصصون في مشاريع الذكاء الاصطناعي والأمن السيبراني لطلاب الحاسب والتقنية 🛡️ wa.me/966569481465 #ذكاء_اصطناعي #أمن_سيبراني #CyberSecurity #AI #تقنية"
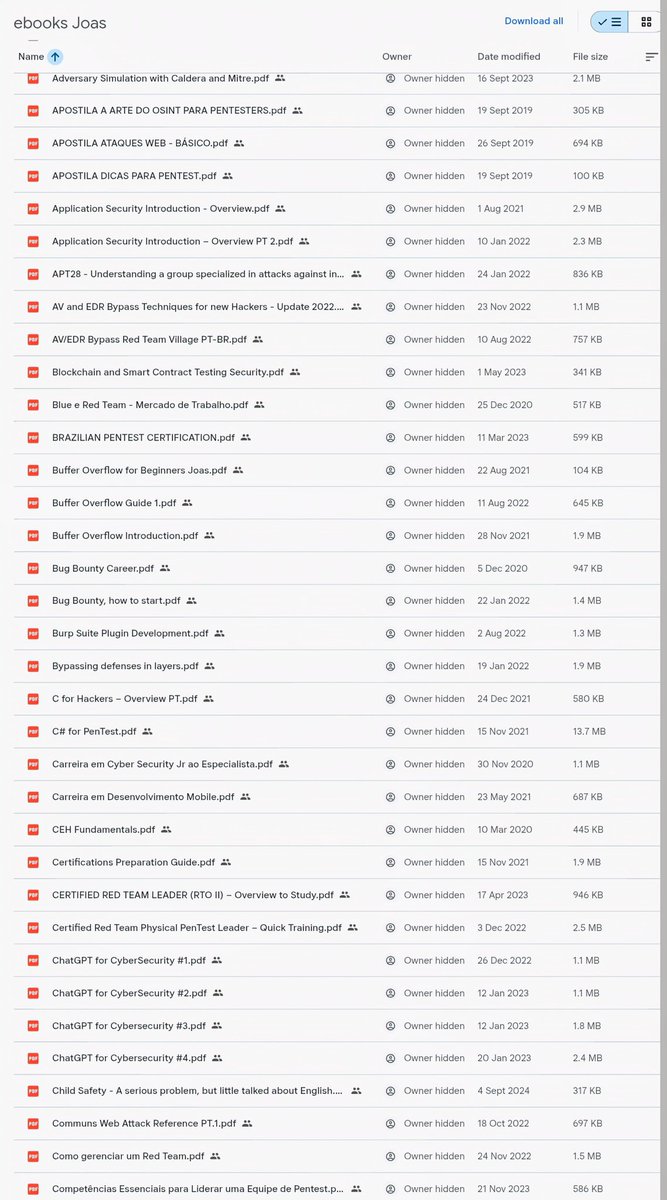
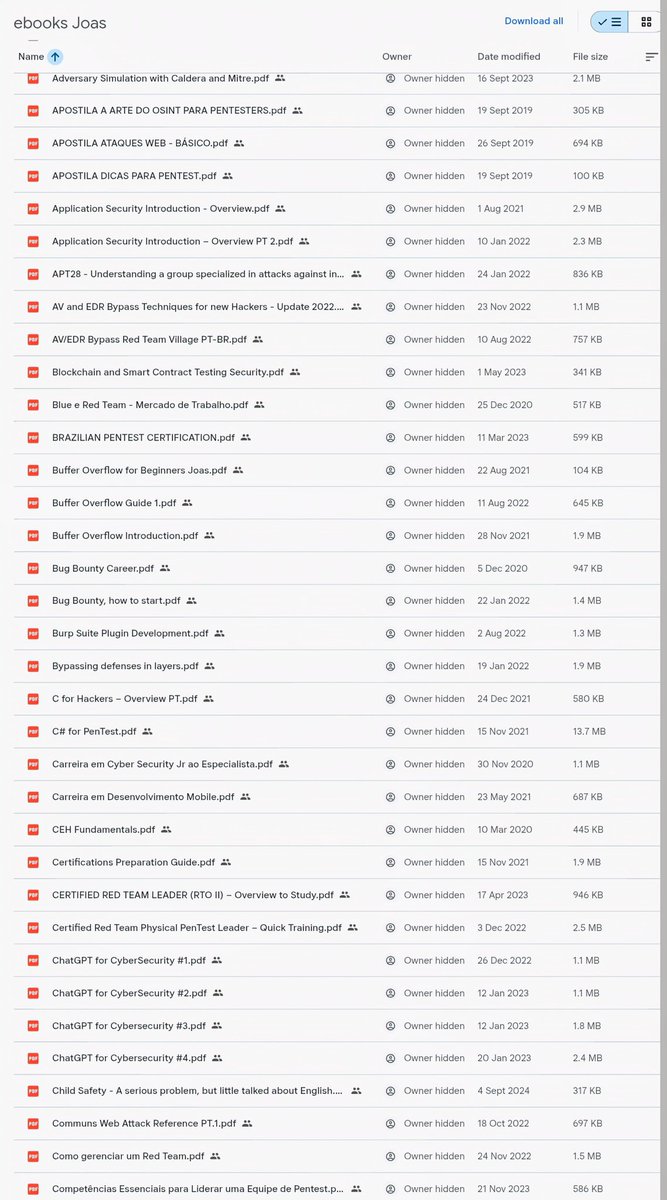
🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇 drive.google.com/drive/folders/… #CyberSecurity #EthicalHacking



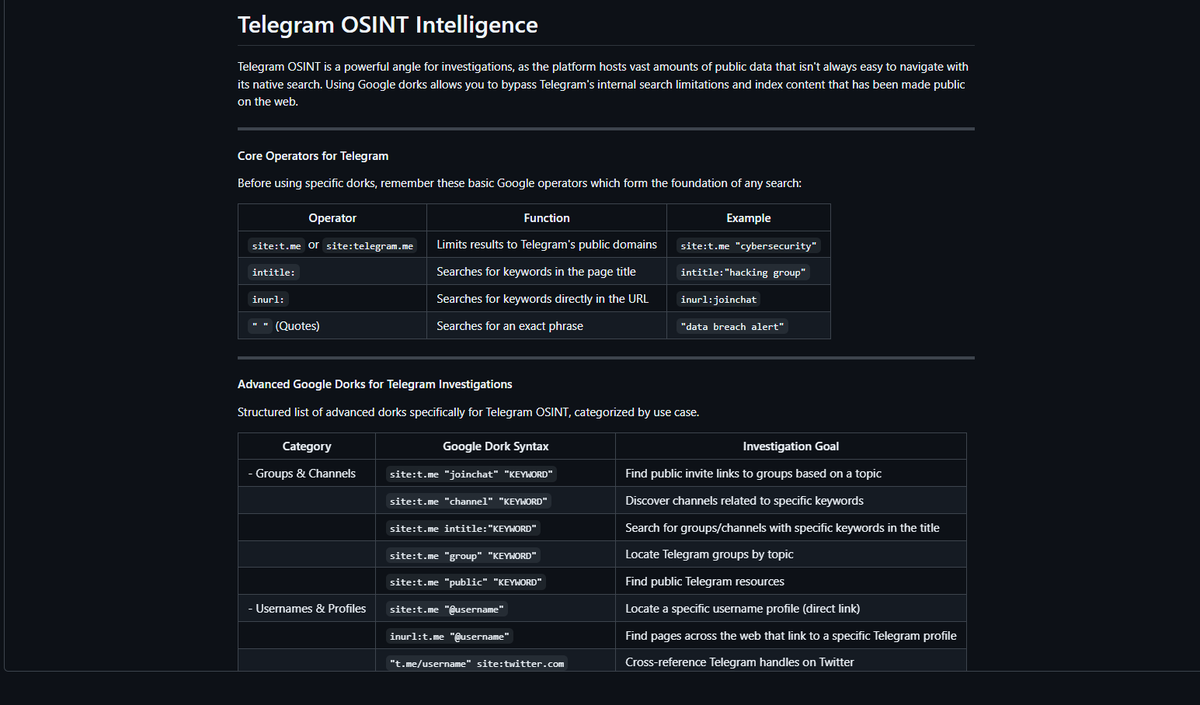
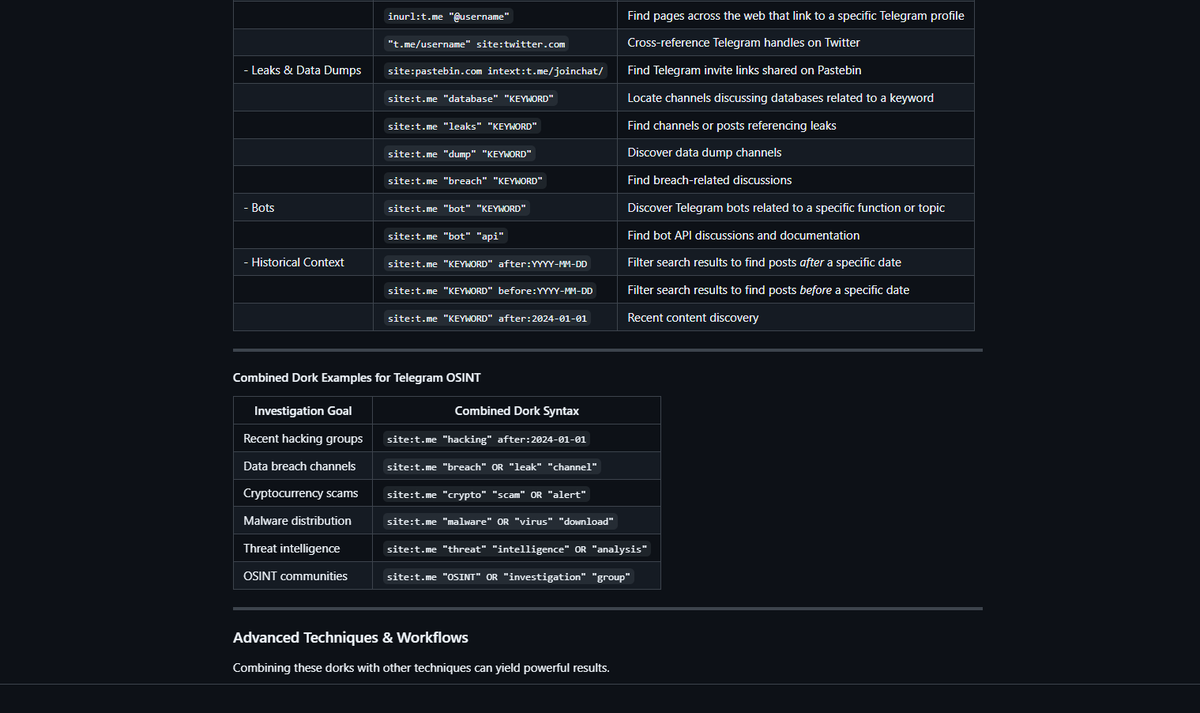
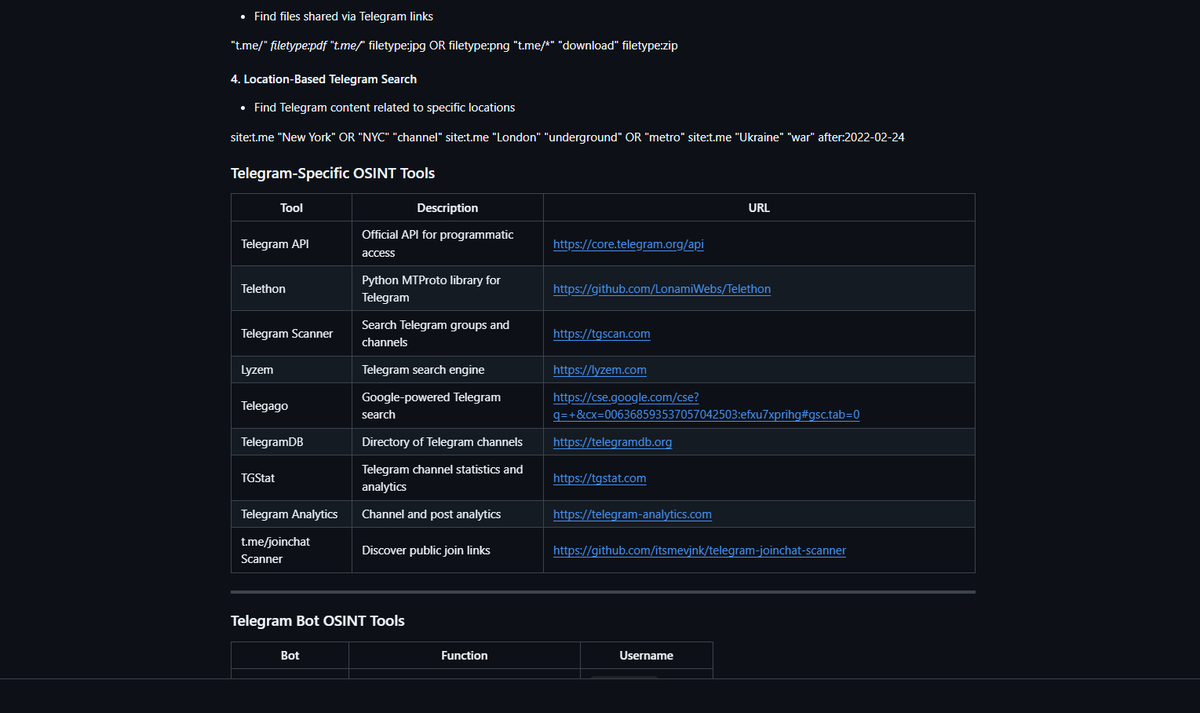
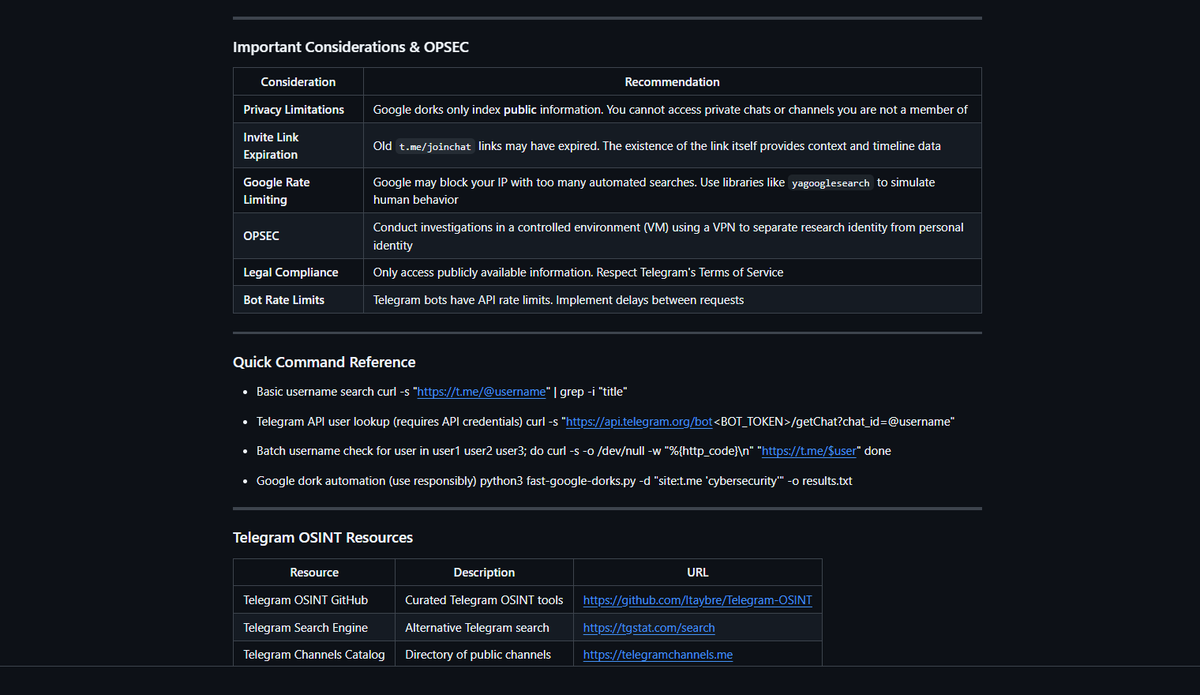
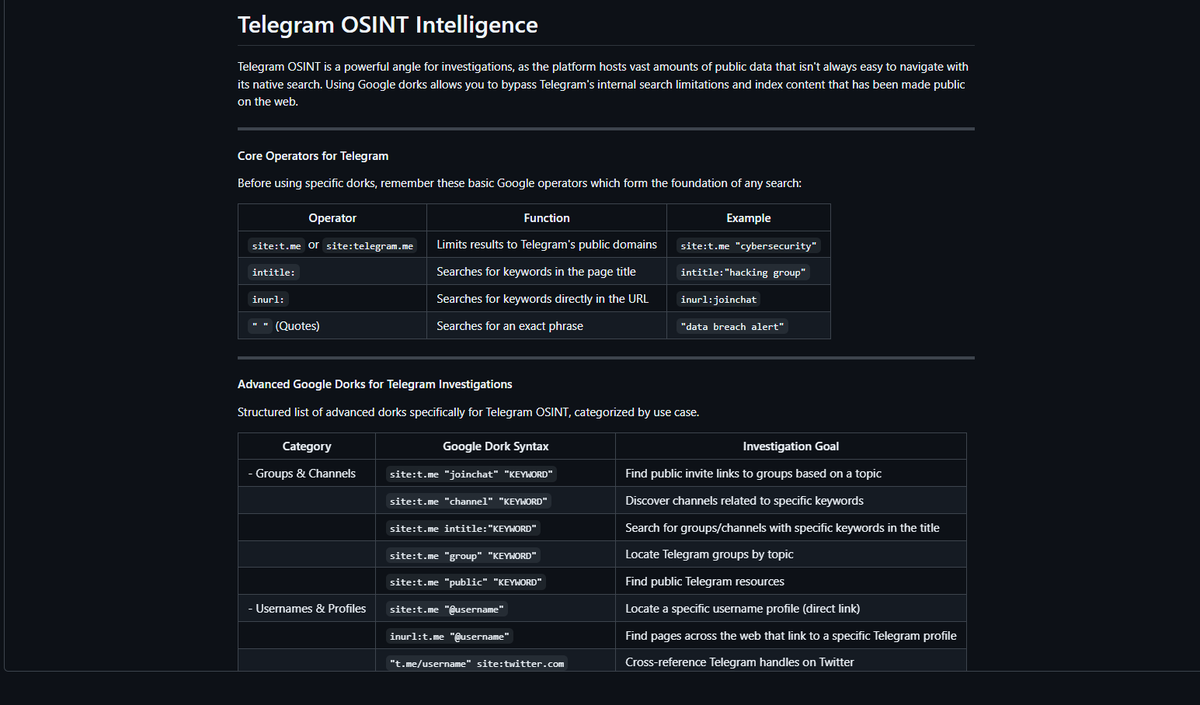
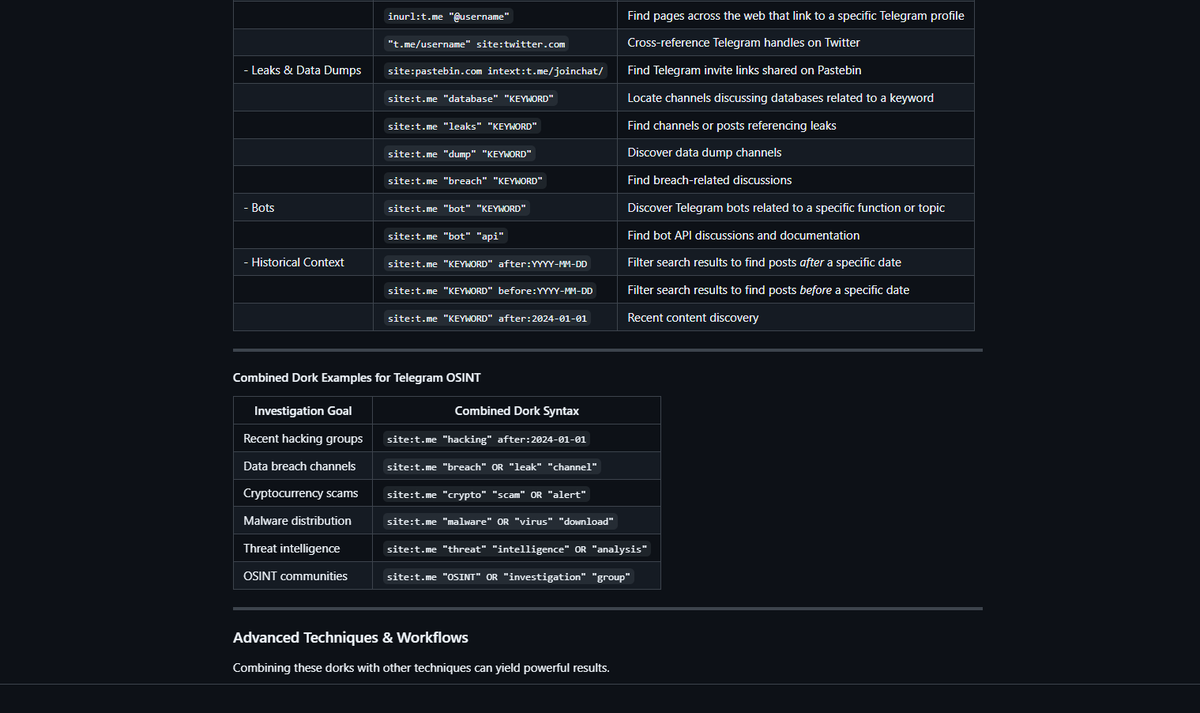
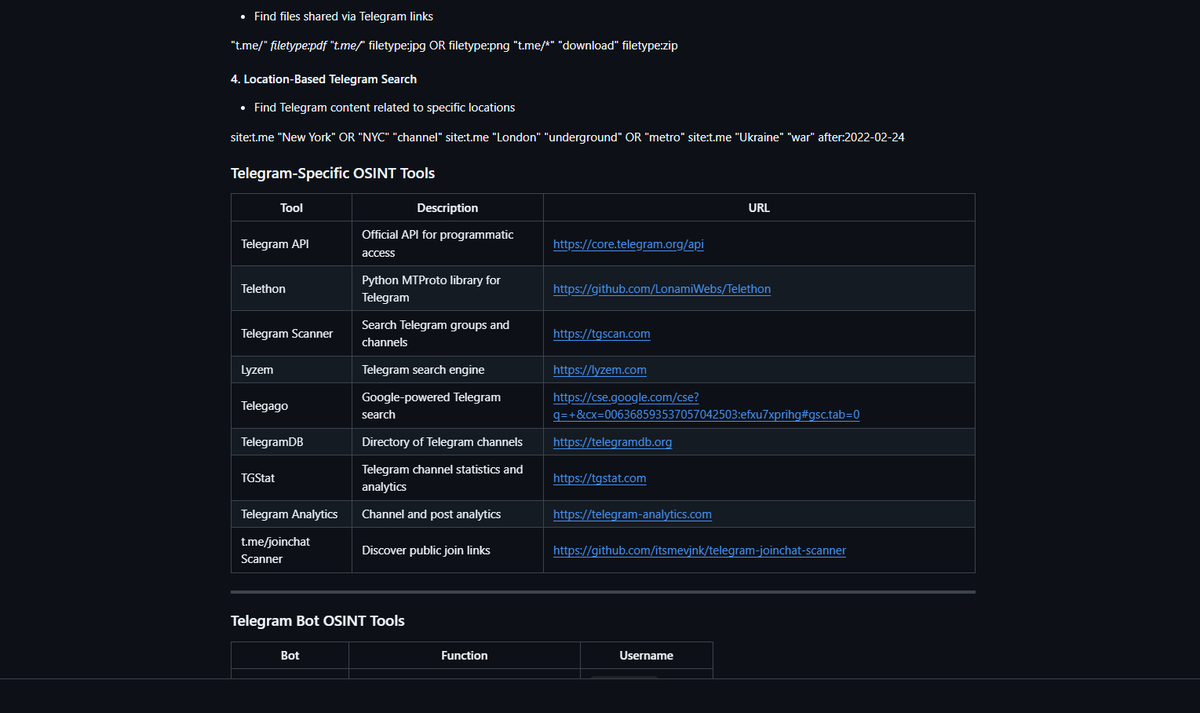
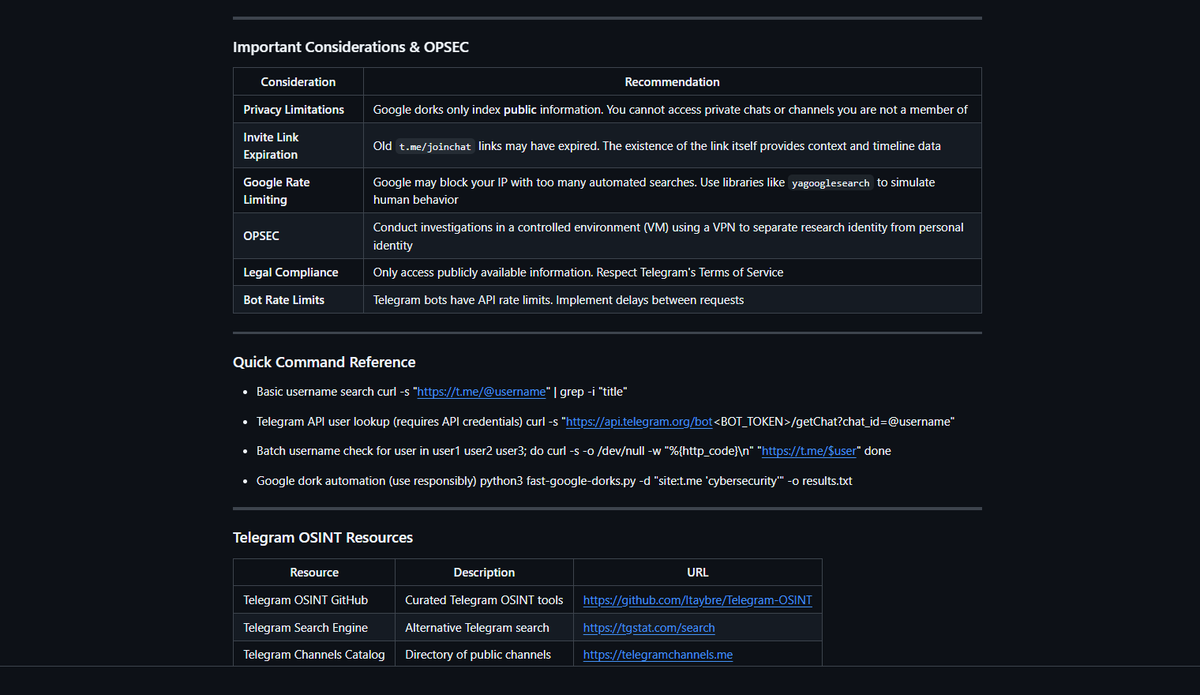
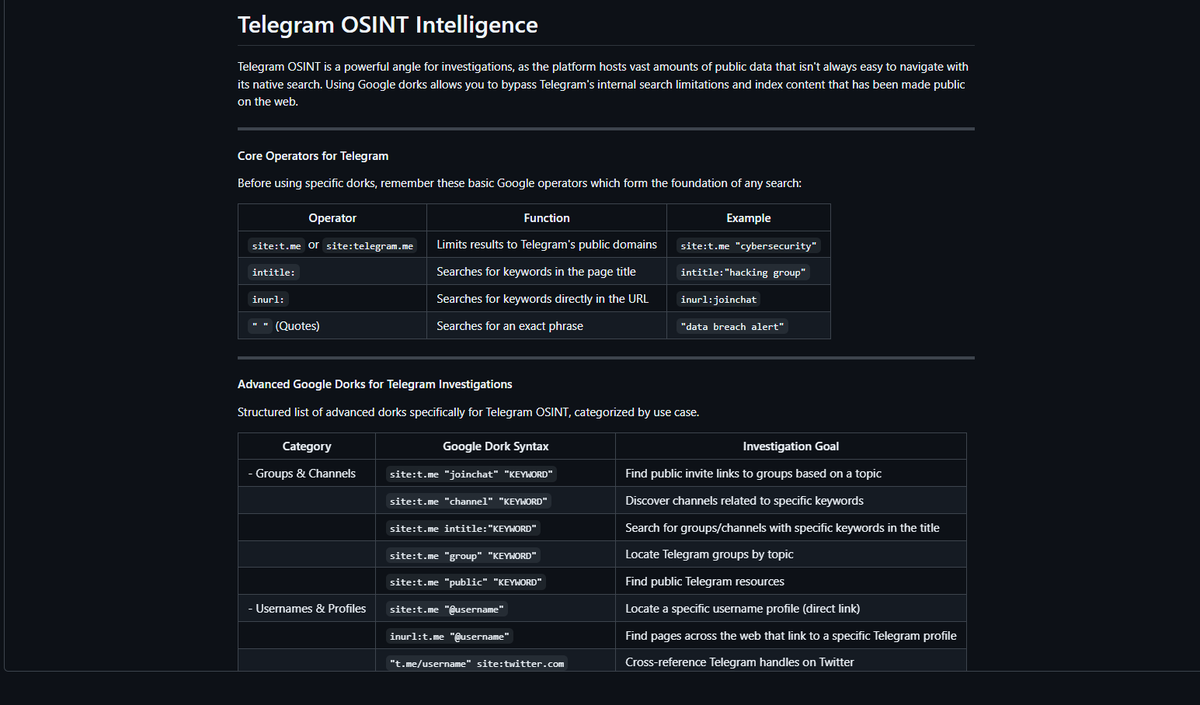
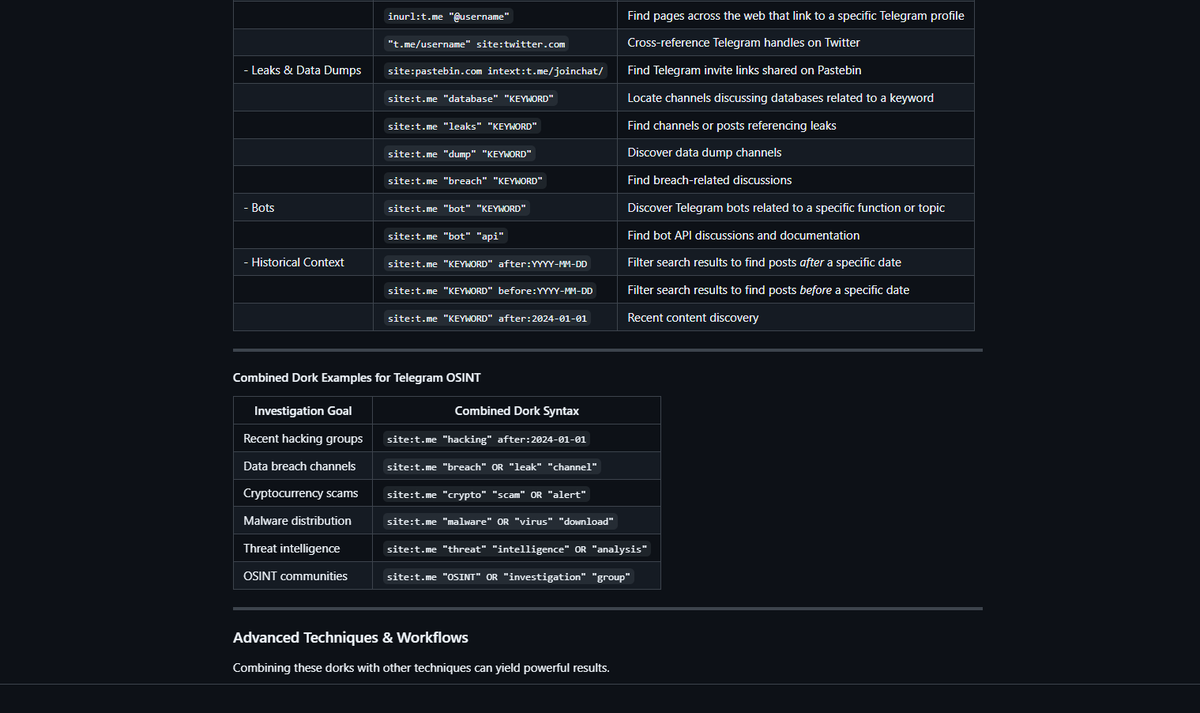
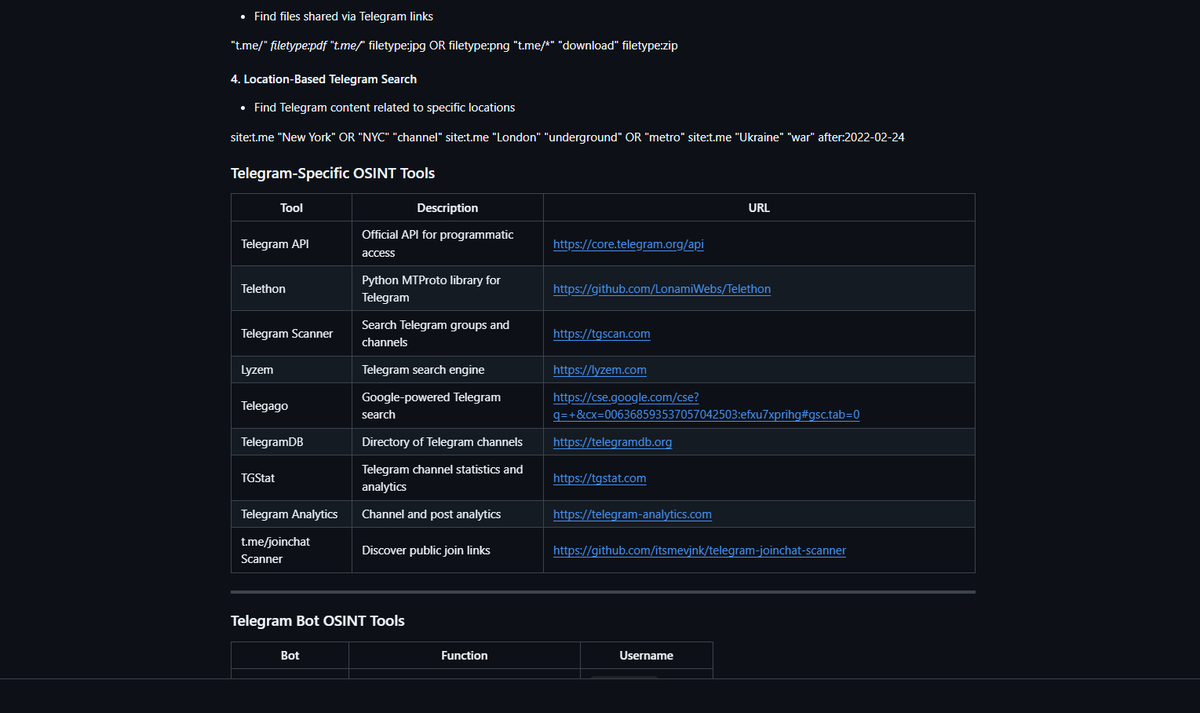
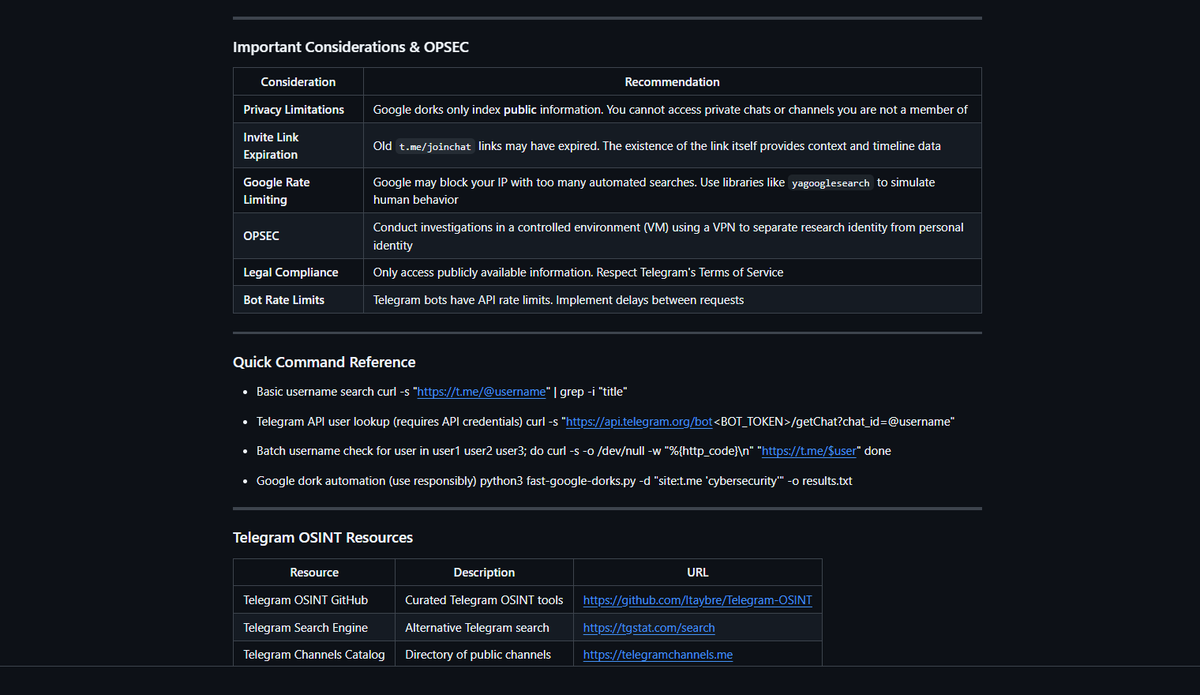
Telegram OSINT Intelligence D4rk_Intel-OSINT-Investigative-Toolkit has been updated with Telegram OSINT - a powerful angle for investigations, as the platform hosts vast amounts of public data that isn't always easy to navigate with its native search. #OSINT #Cybersecurity
new #phishing at hXXps://www[.]DropCatch[.]com/domain/owfield[.]com | 104.20.47.210 | None | CLOUDFLARENET - Cloudflare, Inc. | ASN AS13335 | #infosec #cybersecurity phishstats.info/search/2319745…
![PhishStats's tweet image. new #phishing at hXXps://www[.]DropCatch[.]com/domain/owfield[.]com | 104.20.47.210 | None | CLOUDFLARENET - Cloudflare, Inc. | ASN AS13335 | #infosec #cybersecurity
phishstats.info/search/2319745…](https://pbs.twimg.com/media/HGiEkVSWoAAva7s.png)
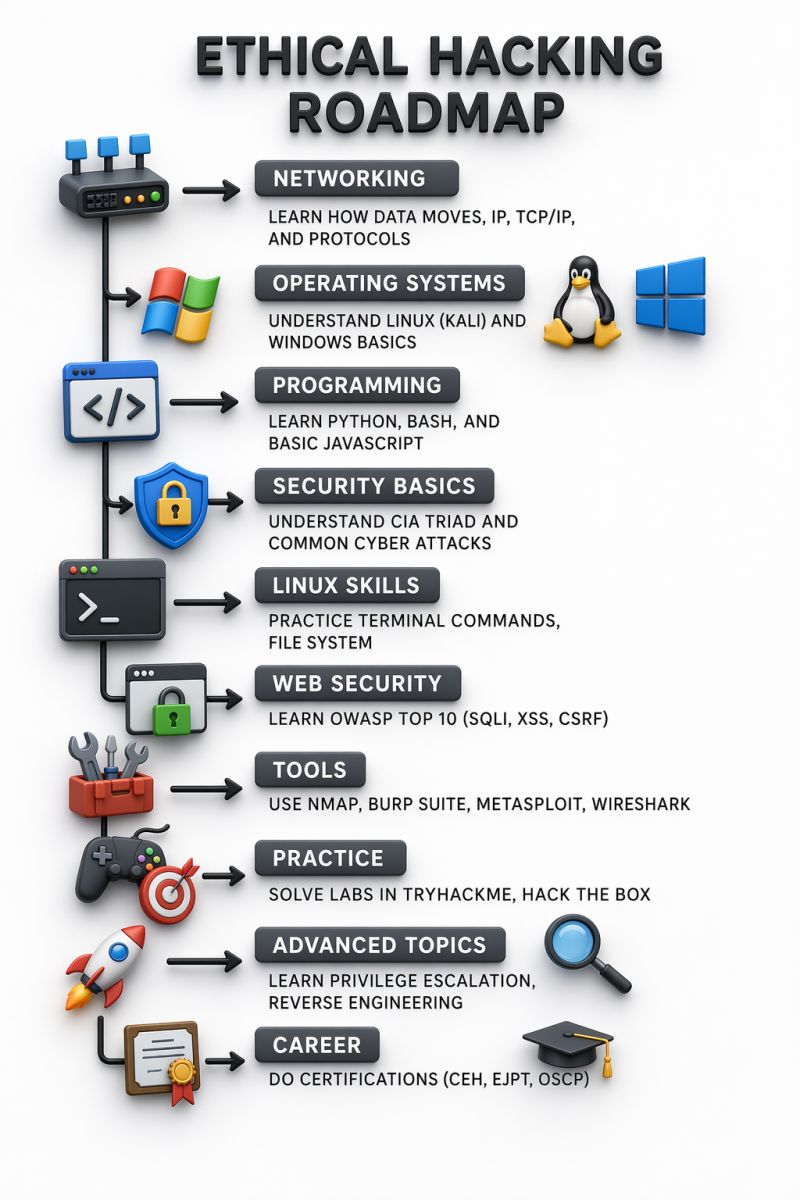
Ethical Hacking Roadmap 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
AI SOCs aren’t one-size-fits-all. Customizable, transparent platforms — not black boxes — help teams automate, adapt, and respond faster to real-world threats. #cybersecurity #CISO #infosec #AI bit.ly/4mJGqH6
99% Managed IT client retention in Q1 2026! 🎯 Local support. Proactive service. Real results. If you’re ready for an IT partner that actually delivers—JustTech is here. #ManagedIT #ITSupport #Cybersecurity justtech.com/justtech-achie…
📢⚠️ Bluesky is back online after a roughly 24-hour DDoS attack disrupted services, with the Iran-linked 313 Team claiming responsibility. Read: hackread.com/bluesky-online… #CyberSecurity #CyberAttack #DDoSAttack #Bluesky #Iran #313Team
Encryption isn’t one thing. It’s two layers. One protects data at rest. The other protects it in transit. Most systems only protect one. That’s where things break. #Cybersecurity #Encryption #DataSecurity #Privacy #Infosec #Teknalyze teknalyze.com/technology/enc…
OpenAI just briefed the US government and all Five Eyes intelligence allies on a new cybersecurity product. The AI lab that started as a nonprofit research project is now sitting at the table with the world's most powerful spy agencies. What a glow-up. #AI #Cybersecurity
99% Managed IT client retention in Q1 2026! 🎯 Local support. Proactive service. Real results. If you’re ready for an IT partner that actually delivers—JustTech is here. #ManagedIT #ITSupport #Cybersecurity justtech.com/justtech-achie…
Security Field Day is April 29-30! 📆 🔐 #XFD15 @DellTech presents at 1:30 PM US/Pacific Wednesday on YouTube, LinkedIn & website. 🔻 YouTube: buff.ly/GXW1J2S 🔹 LinkedIn: buff.ly/DkeViNf @NetworkingNerd @TechFieldDay #Cybersecurity #AI #AISecurity #TFDLive

Cybersecurity spending is rising. So are threats. $522B projected by 2026. But here’s the real question: Is more spend = better security? #CyberSecurity #Infosec #CyberRisk #DigitalTrust

Cyber agents should not be judged only on full wins or full fails. This CTF paper argues for partial-credit evaluation, which is much closer to how real security work creates value and risk. Source: arxiv.org/abs/2604.19354 #AIResearch #Cybersecurity #Agents
CISA adds Microsoft Defender vulnerability CVE-2026-33825 to its Known Exploited Vulnerabilities Catalog. The flaw involves insufficient granularity of access control within the software. #CyberSecurity #CISA
Cloud and cybersecurity go hand in hand. A live discussion on protecting the digital future of healthcare as systems scale and evolve. #MexicoHIS #Cloud #CyberSecurity #DigitalHealth

Looking for #cybersecurity resources tailored to you? DTMB’s Cybersecurity Resource Hub has resources for students, parents, senior citizens, and businesses. Learn more ➡ go.mi.gov/resourcehub

Protecting Enterprise Data: Advanced Malware Scanning Strategies. buff.ly/dh6ep0G #cybersecurity #IT #technology #machinelearning
I just solved Operation Blackout 2025: Smoke & Mirrors on Hack The Box! labs.hackthebox.com/achievement/sh… #HackTheBox #HTB #CyberSecurity #EthicalHacking #InfoSec #PenTesting
#CyberSecurity #DisasterRecovery #247disasterrecoverysupport Disaster Recovery Plans That Fail When You Need Them Most—Why It Happens blog.synergyit.ca/disaster-recov…
Have you got the Icopy ID1 Cards – Genuine iCopy-XS & iCopy-X cards? link.ksec.co.uk/4d921n #cybersecurity #hackers #rfid #infosec #security #ksec #redteam #edc #edcgear
WEDNESDAY | 22 APRIL 2026 | Cybersecurity Report #CyberSecurity #TechNews #Infosec #DataBreach #Hacking #Protobuf #Oracle #CyberFM #RSSH #DigitalFrontline #Venice #McGrawHill #CyberAlert #2026Tech
leak or platform update away from losing it all. What’s YOUR biggest website frustration right now? Drop it below 👇 #WebDev #CyberSecurity #WebsiteArchitecture
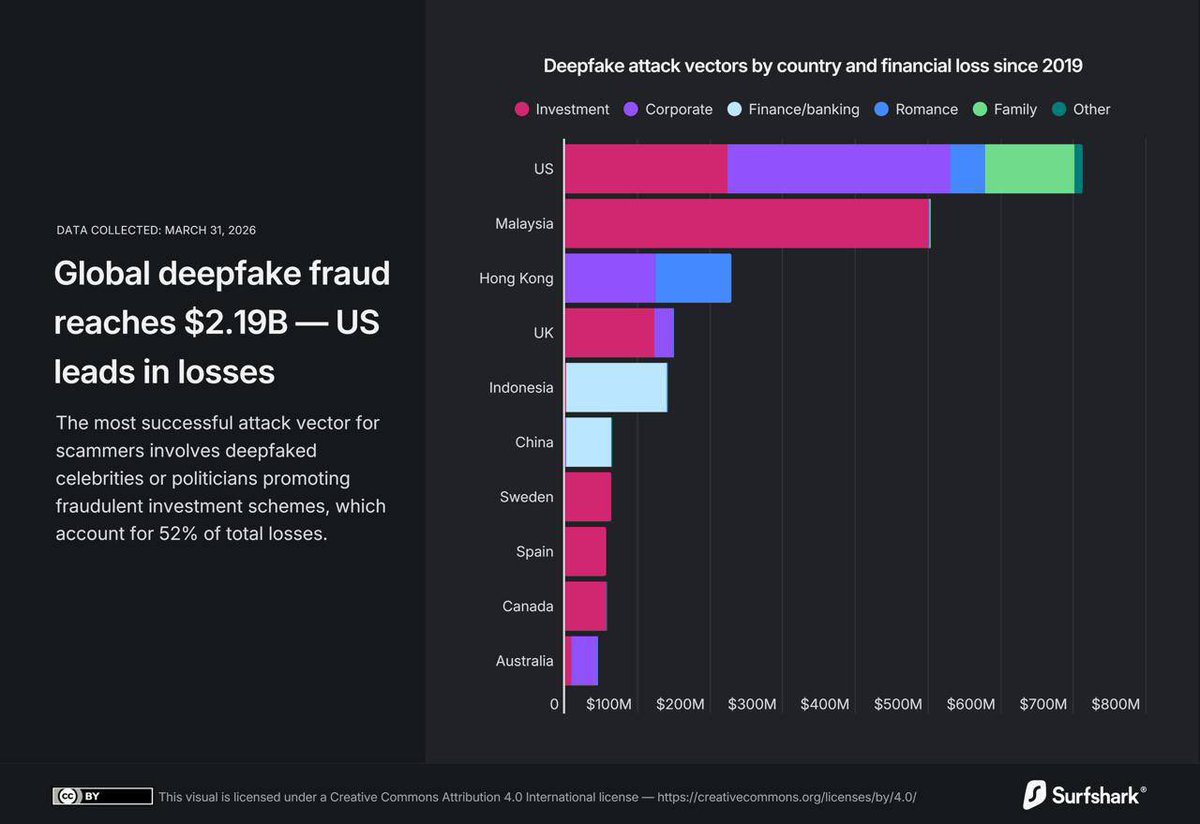
Surfshark підрахував: глобальні збитки від deepfake шахрайства вже досягли $2.19 млрд Найприбутковіша схема фейки з селебріті та політиками, які “рекламують” інвестиції: ≈52% усіх втрат Це сотні мільйонів доларів 😳 І це тільки початок! #Deepfake #Scam #CyberSecurity
Telegram OSINT Intelligence D4rk_Intel-OSINT-Investigative-Toolkit has been updated with Telegram OSINT - a powerful angle for investigations, as the platform hosts vast amounts of public data that isn't always easy to navigate with its native search. #OSINT #Cybersecurity
Ukraine repairs Druzhba pipeline post Russian attack, EU loan pending; cybersecurity threats escalate in UK and Europe #Ukraine #EU #CyberSecurity infacts.ai/news/article/u…
infacts.ai
InFacts - News That Makes a Difference
Discover verified, impactful stories that matter to your life. Simplified, truthful, and designed to inform and inspire.
📹 تم الانتهاء من تسجيل جميع فيديوهات دورة CPTS Prep، وهي الآن متاحة بالكامل عبر أكاديمية الدرع الأخضر 🛡. ⚔️صُممت الدورة بطريقة احترافية ومتكاملة لتساعدك في التحضير لشهادة CPTS، بإسلوب عملي وتطبيقي يغطي جميع محاور المسار بوضوح وشمولية. 👇🏻 #الأمن_السيبراني #CPTS #CyberSecurity

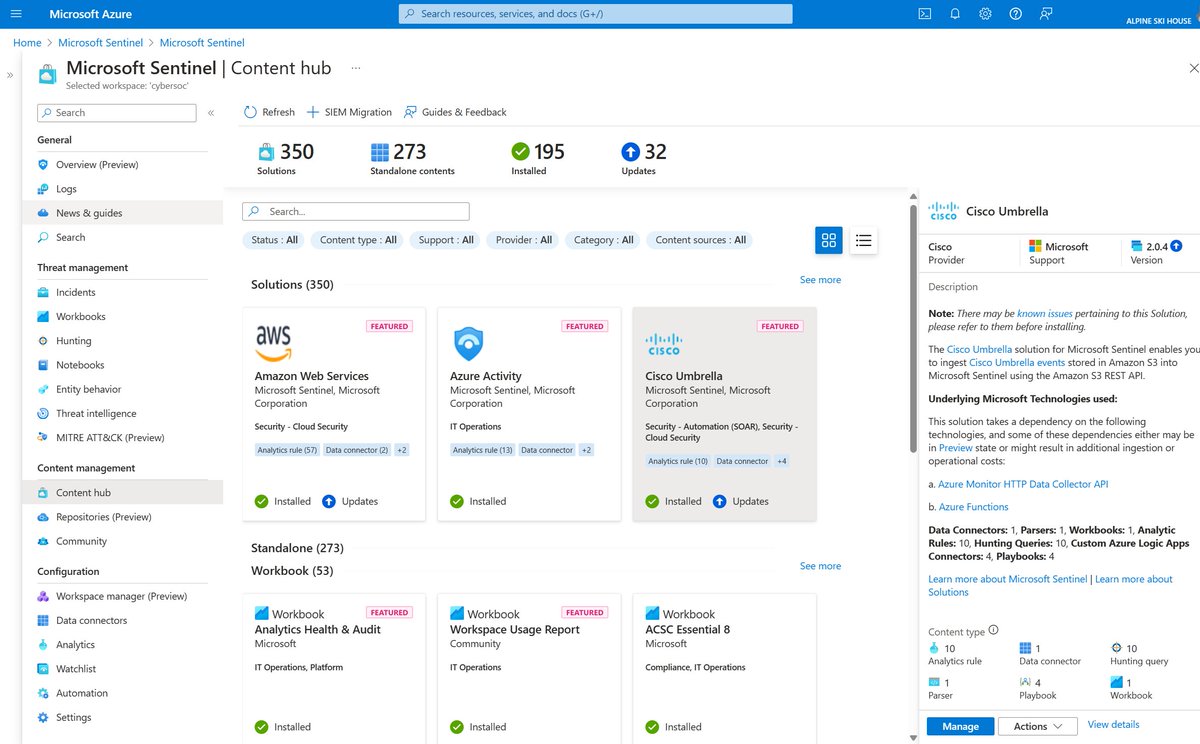
🔐 Control access smarter with Microsoft Sentinel! 👥 Resource-based RBAC for fine-grained permissions 📊 Limit data visibility by team needs ☁️ Secure logs via Azure Monitor Learn how 👉 msft.it/6019Q2pKX #Azure #RBAC #CyberSecurity

🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇 drive.google.com/drive/folders/… #CyberSecurity #EthicalHacking



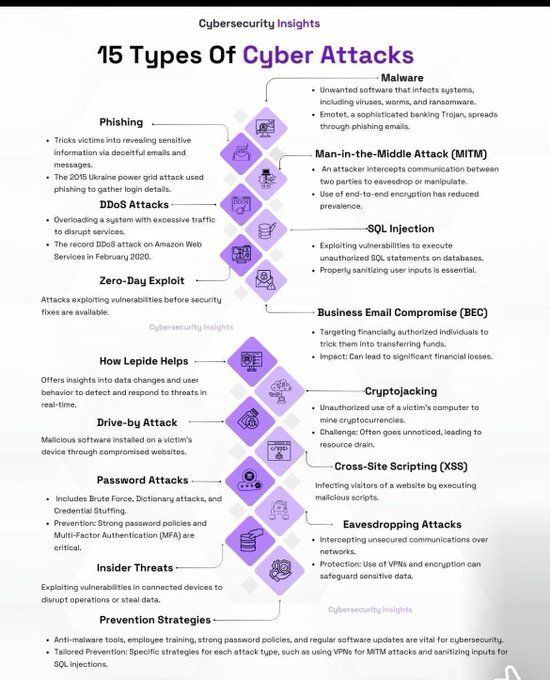
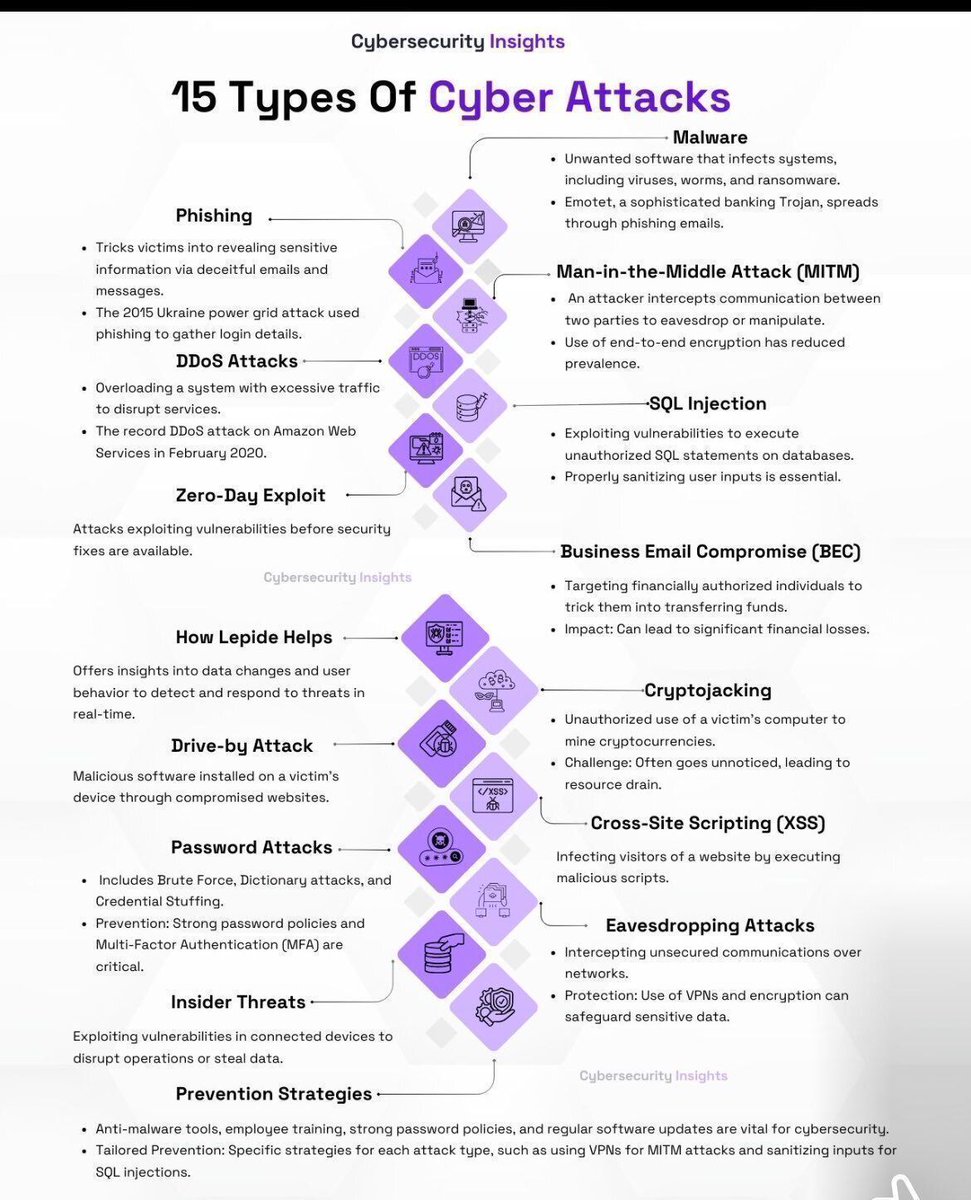
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
DNN, is the leading open-source CMS in the Microsoft ecosystem. Read more about the vulnerability: cnews.link/dnn-vulnerabil… #DNN #cybersecurity #Microsoft

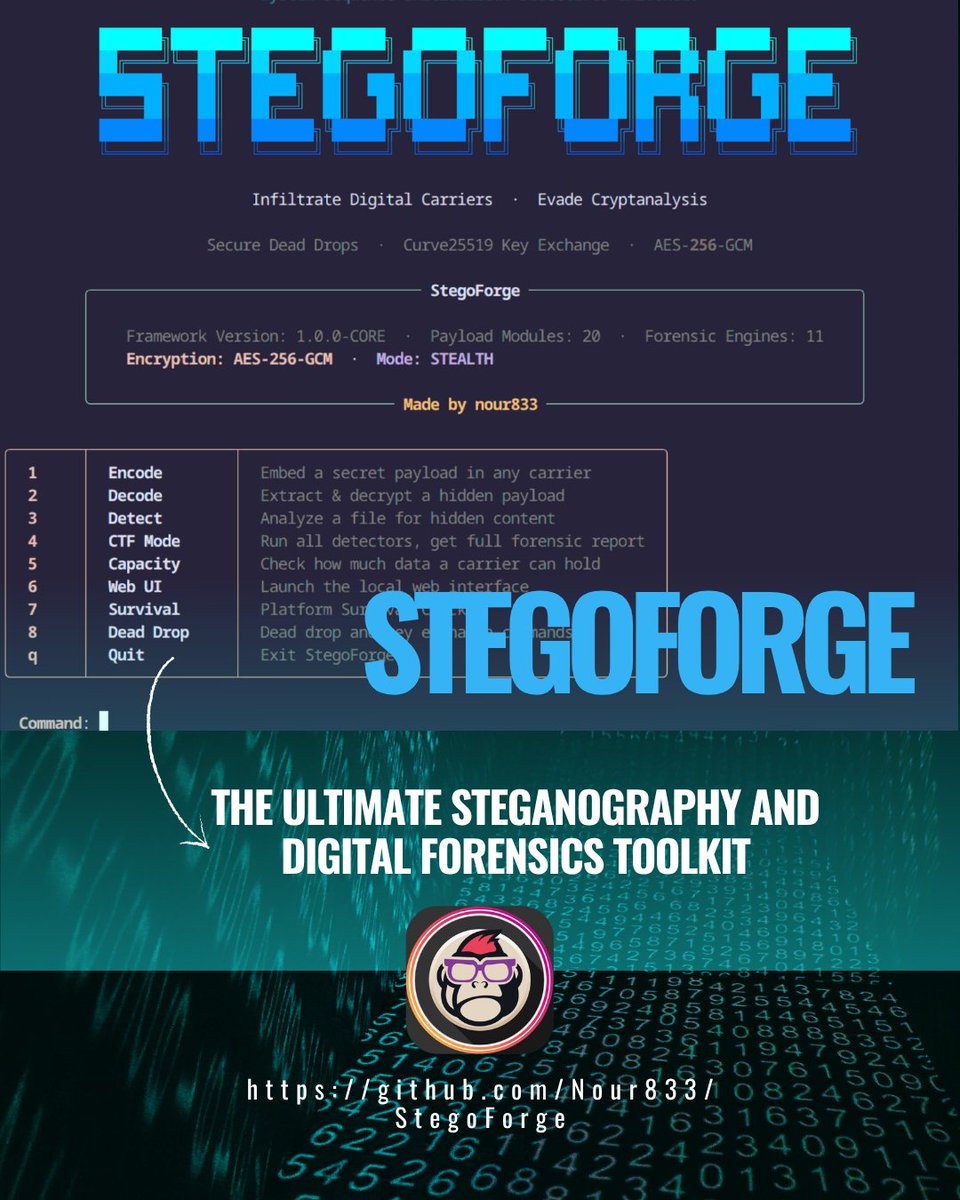
StegoForge 🧠🔍: El kit híbrido de esteganografía + forense con MLOculta datos en imágenes, audio, vídeo, docs y paquetes de red. Detecta con 11 motores avanzados (incluyendo CNNs). Ideal para CTFs y red teaming. Solo uso autorizado. #steganography #forensics #cybersecurity #ctf
🚨 Cyberattacks don’t stop at detection—and neither should your defenses. Join us for a webinar with @KaseyaCorp to learn how MSPs stay ahead of AI phishing, ransomware, & data loss by combining security and recovery. 🎯 Register: event.on24.com/wcc/r/5301783/… #cybersecurity #webinar
🛡️ Secure smarter with Microsoft Sentinel! ✨ Cloud-native SIEM & SOAR ✨ AI-powered threat detection ✨ Automated response playbooks Start protecting now 👉 msft.it/6014Q2TJi #Azure #CyberSecurity #SIEM
Telegram OSINT Intelligence D4rk_Intel-OSINT-Investigative-Toolkit has been updated with Telegram OSINT - a powerful angle for investigations, as the platform hosts vast amounts of public data that isn't always easy to navigate with its native search. #OSINT #Cybersecurity
Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

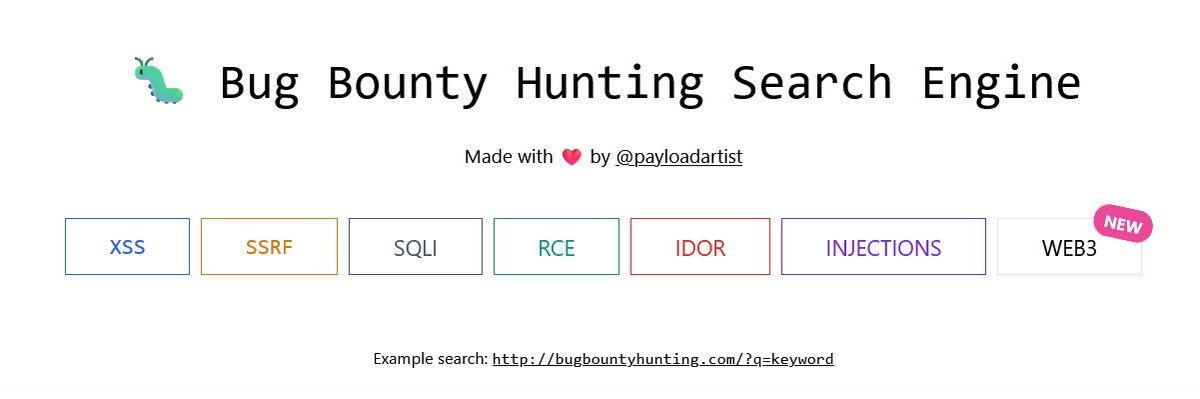
Hunters 🚨 One resource you should definitely bookmark: bugbountyhunting.com Writeups. Resources. Real learning. No fluff. #BugBountyHunter #CyberSecurity #InfoSec #EthicalHacking
Something went wrong.
Something went wrong.
United States Trends
- 1. #EarthDay N/A
- 2. SPLC N/A
- 3. Clayface N/A
- 4. Charles Johnson N/A
- 5. Storage Wars N/A
- 6. Logan Gilbert N/A
- 7. Pickens N/A
- 8. Spirit Airlines N/A
- 9. Warnock N/A
- 10. Darrell Sheets N/A
- 11. Rocket Power N/A
- 12. #AllStars11 N/A
- 13. Ric Flair N/A
- 14. Burnley N/A
- 15. Peter Lambert N/A
- 16. Coby Mayo N/A
- 17. David Scott N/A
- 18. Elston Howard N/A
- 19. Nick Martinez N/A
- 20. Giolito N/A