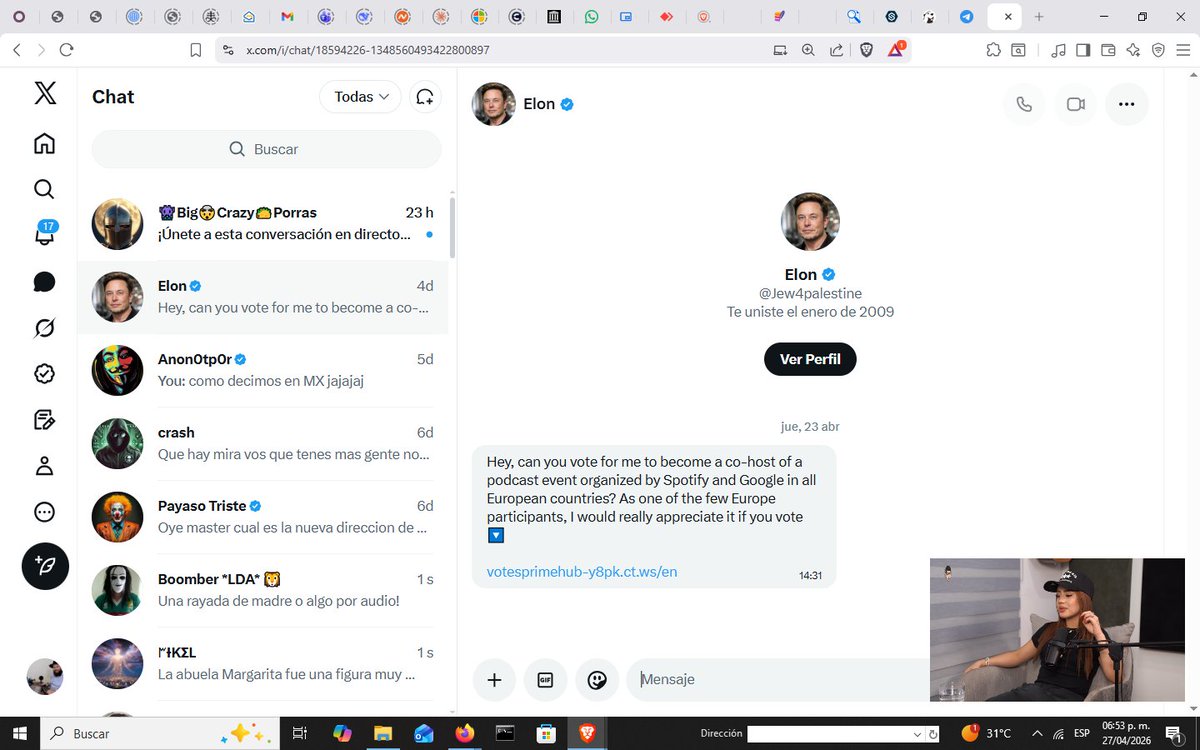
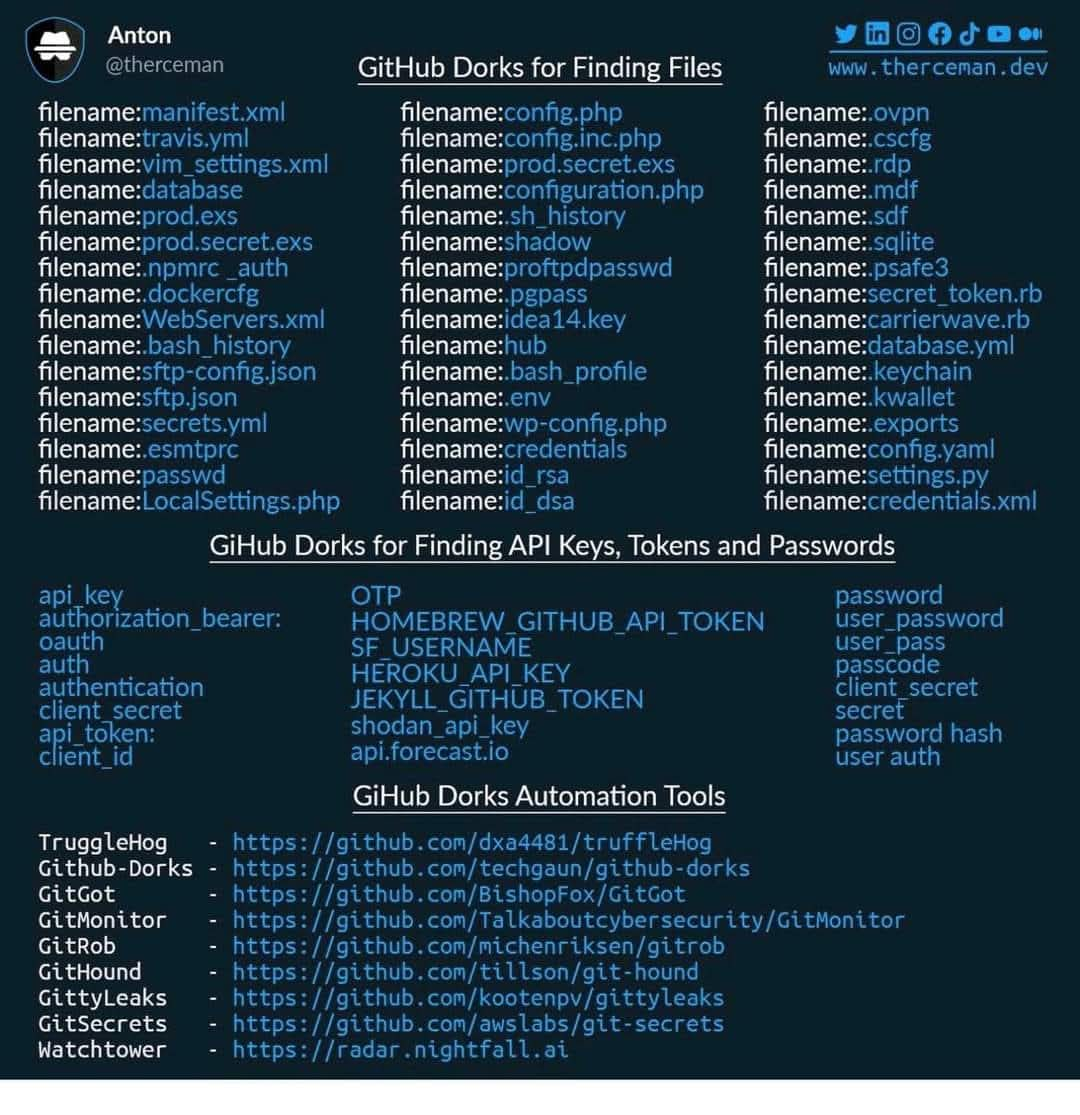
#infosec search results
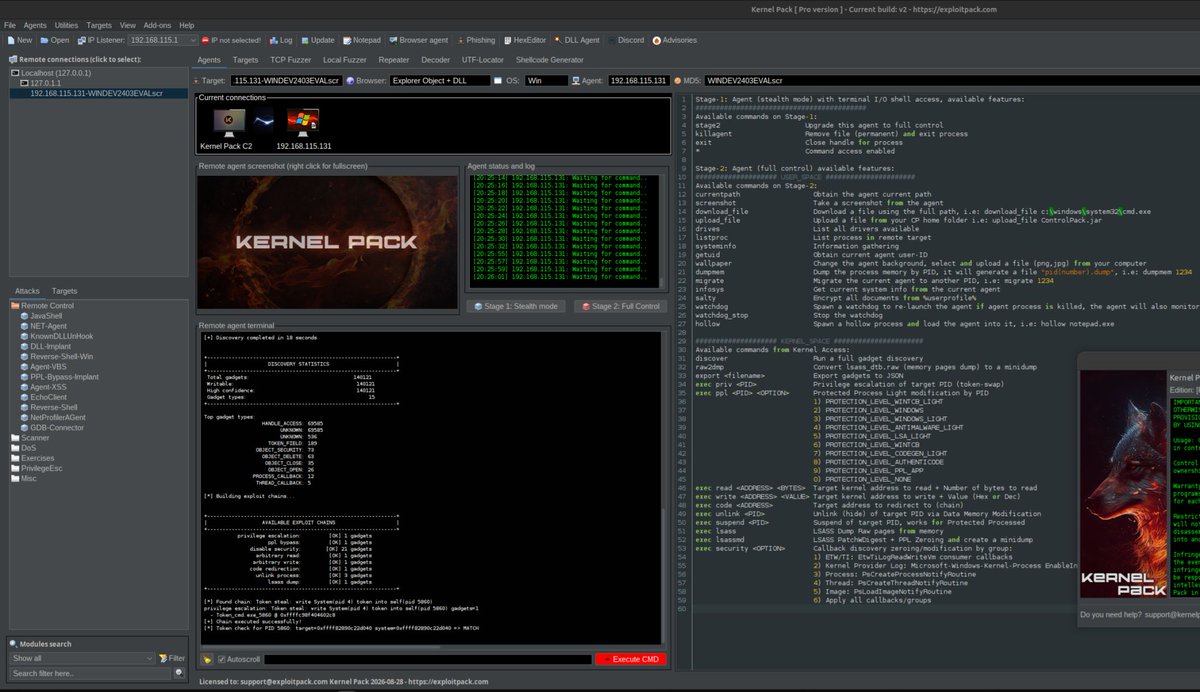
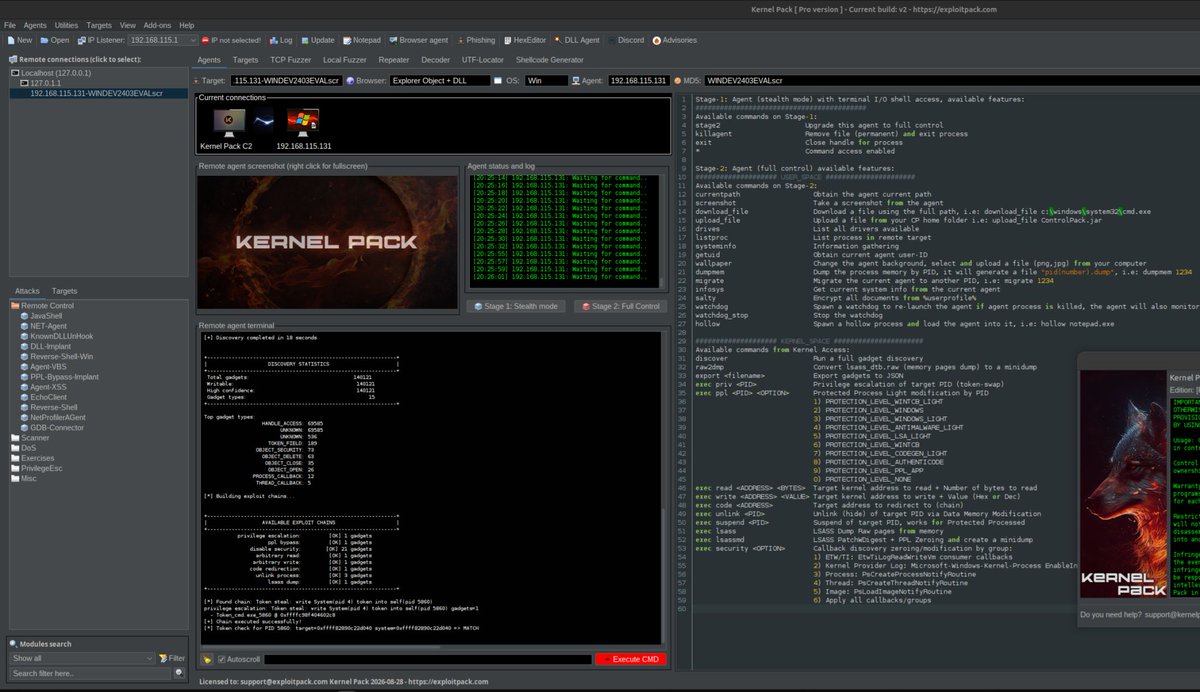
New version of Kernel Pack, the only C2 framework on the market for cybersec professionals, with Kernel-level access. exploitpack.com/products/kerne… Bypasses VBS/HVCI/kCET, even with EDR/AV solutions enabled. #Kernel #RedTeam #InfoSec #CyberSecurity #Pentest #offsec #defender #VBS
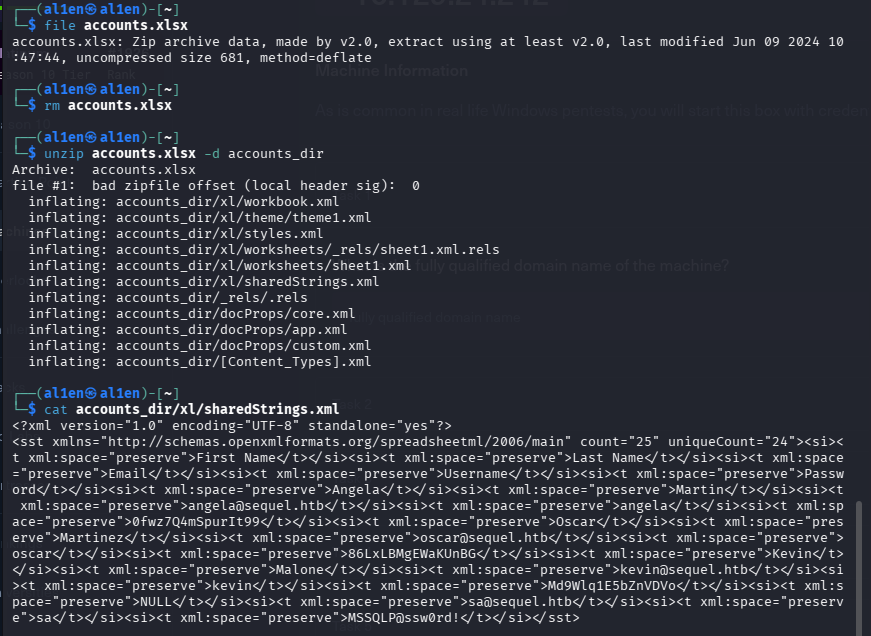
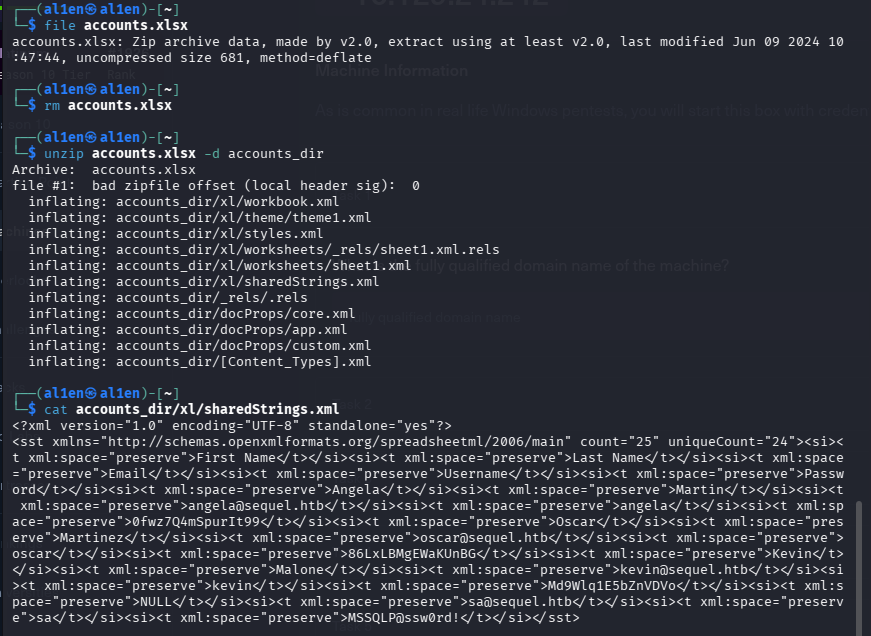
SMB share "Accounting Department" readable with guest creds. accounts.xlsx = Angela, Oscar, Kevin, sa all with plaintext passwords. MSSQLP@ssw0rd! got me SA on SQL Server. 🔑 #SMB #CredentialHarvesting #InfoSec #EthicalHacking

Remote-first working complicates identity governance. 🔗 tinyurl.com/hkzf9sz3 Fix it with human & non-human ownership mapping, detection of unused high-risk access, & automated revocation. #cybersecurity #infosec #itsecurity

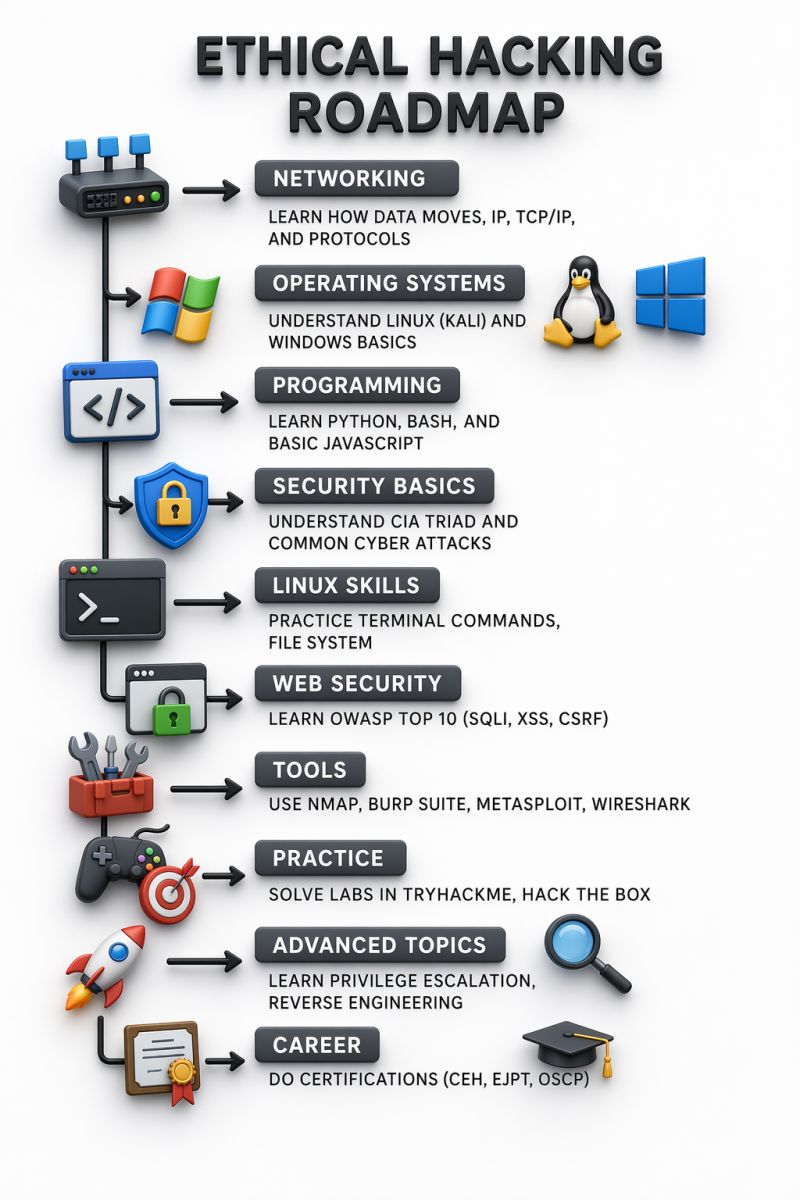
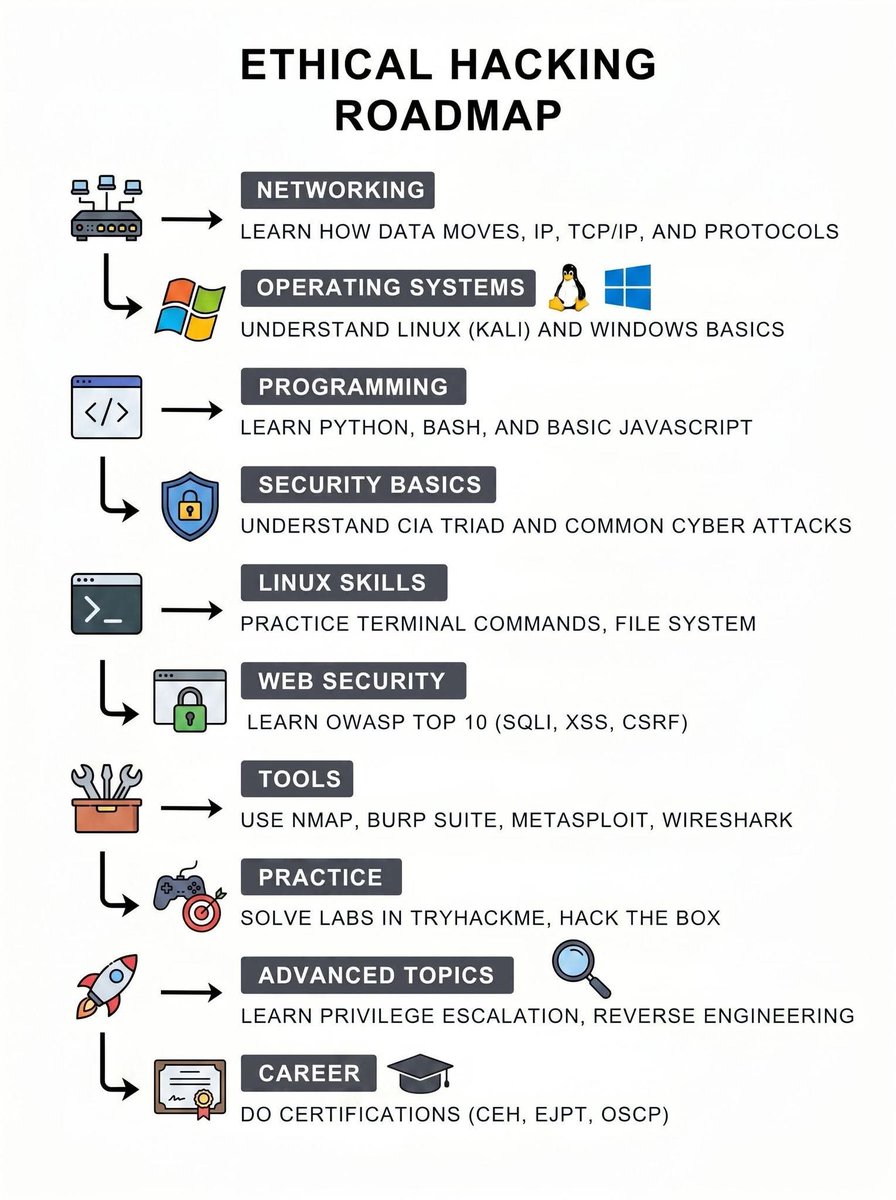
Ethical Hacking Roadmap 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
⚠️ MOBILE OPSEC — UNDER THE HOOD Think your phone isn’t tracking you? Apple & Google ecosystems collect more than most people realize. Know the system before it knows you. Follow for more threat intel. #CyberSecurity #OPSEC #Infosec #DataTracking #Surveillance
Even cybersecurity researchers are exposing secrets in their arXiv LaTeX source - helpnetsecurity.com/2026/04/28/cyb… - @IEEESSP #CyberSecurity #InfoSec #DataLeak #AcademicResearch #Privacy

Most SaaS apps don’t get breached by “critical CVEs.” They get breached by IDOR, broken access control, and API abuse—issues most reports don’t prove exploitable. That’s the real risk. pentesttesting.com/professional-p… #CyberSecurity #Infosec #APIsecurity #DataProtection #OnlineSafety
pentesttesting.com
Professional Penetration Testing Report Sample
See what a professional penetration testing report sample includes, plus what to expect from a real SOC 2-ready security assessment.
The news of a Cursor/Claude agent deleting a database in 9 seconds is a stark reminder: AI tool-use is the new perimeter. 🛡️ Govern your agent's tool-use at the local runtime to prevent silent breaches. Don't rely on cloud safety. #MCPSecurity #AISecurity #InfoSec #ClaudeCode
Industry Trend: identity is now the main attack surface. Permissions + misconfigurations = real risk. JIT access is now the only sane model. #cybersecurity #infosec #itsecurity app.stationx.net/articles/cloud…
app.stationx.net
Cloud Security Statistics [2026]: Key Data & Trends
Explore 50+ cloud security statistics for 2026 — breaches, misconfigurations, identity attacks, and market growth from 30+ sources.
"Have you checked the logs?" – because 90% of the time, the answer is right there, screaming at you. The other 10%? Reboot anyway. 🔍📜 #CyberSecurity #InfoSec #ITSupport
Your SIEM shouldn’t be the weakest link.CVE-2026-40050 in CrowdStrike LogScale exposes sensitive files via unauthenticated access. Read: zyberwalls.com/2026/04/crowds… #CyberSecurity #InfoSec #ThreatIntel #Vulnerability
Yesterday I posted: knowledge before action. Today’s reminder: Sometimes systems aren’t broken… They’re just forgotten. Old subdomains. Test environments. Unused records. Many risks come from assets nobody is watching. #CyberSecurity #InfoSec #EthicalHacking
Cyble uncovers "Operation Trust Trap," a 16,800-domain network weaponizing *.gov trust to steal credentials. See how APT36 and others hijack the human eye. #TrustTrap #InfoSec #CyberSecurity #Phishing #APT36 #GovSecurity #Cyble #DNS securityonline.info/operation-trus…

❌ Fuite de données Udemy Udemy est l'une des dernières victimes du groupe de cybercriminels ShinyHunters. Les pirates ont publié une base de données contenant plus de 1,4 million d'enregistrements. Plus d'infos👇 - it-connect.fr/cyberattaque-u… #infosec #cybersecurite #dataleak

>_ No Hat 2026 CfP is OPEN! 👾 Do you wanna have a good excuse to travel to beautiful Italy next autumn? Submit your latest research work at: nohat.it/cfp Check out last year's vibes to see what you're getting into: youtube.com/watch?v=WoxuZR… #NoHat2026 #InfoSec #CFP

youtube.com
YouTube
BITM Hacklab
📌 Diving into Windows Internals Playlist Playlist Link🔗: youtube.com/playlist?list=… Credit: Nir Lichtman Channel Link🔗: youtube.com/@nirlichtman #WinInternals #InfoSec

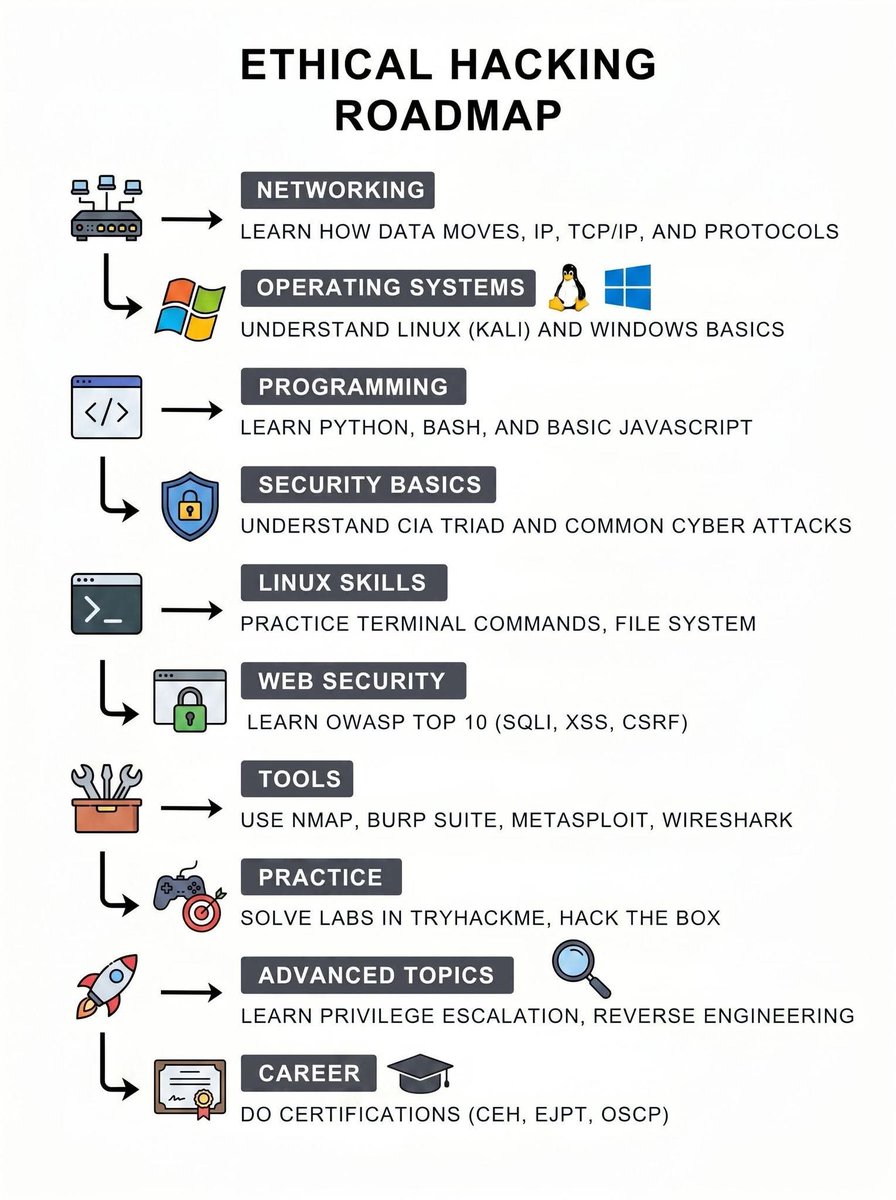
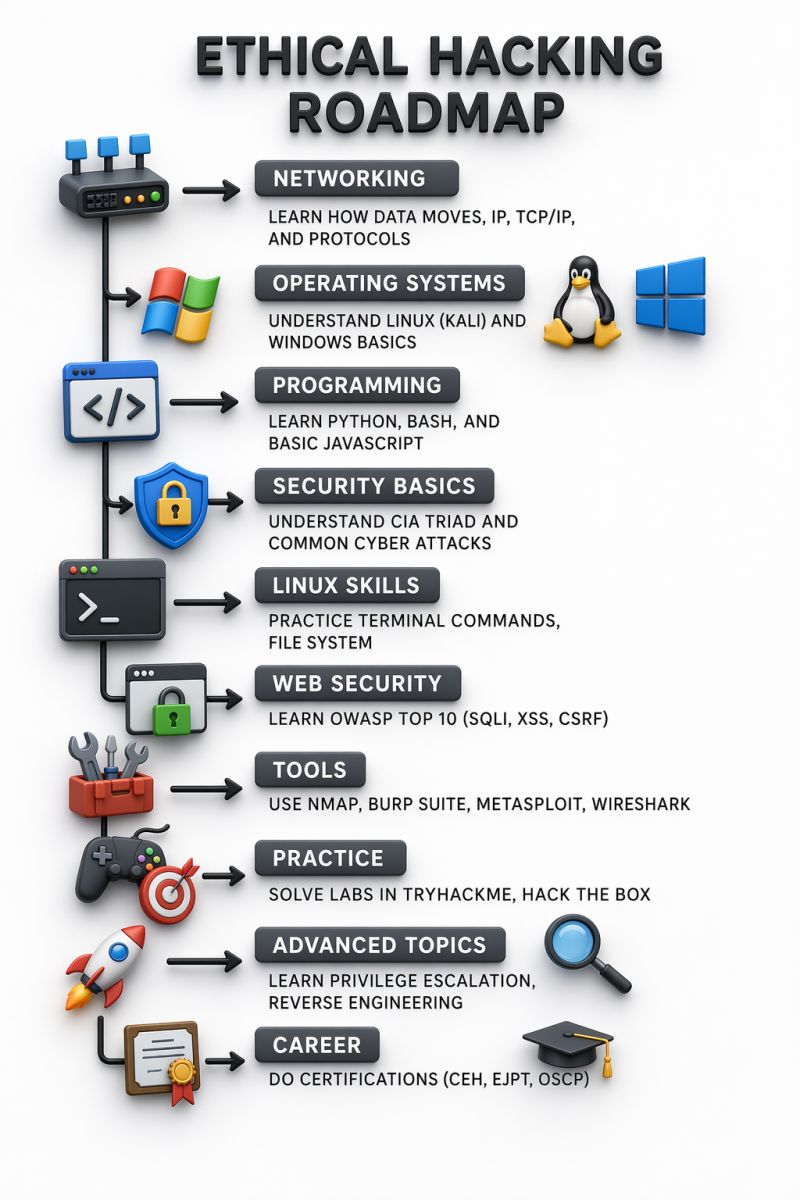
🚀 From Zero to Ethical Hacker: A Clear Roadmap Stop consuming random content. Follow a structured path: Networking → OS → Programming → Security → Tools → Practice Consistency beats everything. #CyberSecurity #EthicalHacking #InfoSec
Low-effort obfuscation and in-memory execution techniques to build simple FUD stagers (@G3tSyst3m) g3tsyst3m.com/fud/Creative-a… #infosec
🔗 Most abused TLDs for #phishing today: - com: 139 - app: 13 - dev: 9 - cfd: 7 - cn: 4 Total: 204 | #infosec #cybersecurity phishstats.info
The Summit = TTPs (Tactics, Techniques & Procedures). Detecting how they act—not just what they use—is the game-changer. Force the adversary to quit because you've made their job too expensive. 🏆 #Infosec #CyberSecurity #MITRE
Chinese Silk Typhoon hacker extradited amid rising COVID research cyberattacks. Microsoft patches Entra ID flaw and warns of active Windows Shell exploit. Stay ahead with today’s CISO briefing. #CyberSecurity #CISO #InfoSec #Vulnerability news.infosecmadeeasy.com/2026/04/ciso-d…
SMB share "Accounting Department" readable with guest creds. accounts.xlsx = Angela, Oscar, Kevin, sa all with plaintext passwords. MSSQLP@ssw0rd! got me SA on SQL Server. 🔑 #SMB #CredentialHarvesting #InfoSec #EthicalHacking

La ingeniería social busca generar confianza en: 🔍 correos internos simulados 📞 llamadas convincentes 💬 mensajes coherentes En muchos casos, el vector de ataque más crítico es humano. 🔐 #Ciberseguridad #CyberSecurity #InfoSec #IngenieriaSocial #DolbuckAcademy
New version of Kernel Pack, the only C2 framework on the market for cybersec professionals, with Kernel-level access. exploitpack.com/products/kerne… Bypasses VBS/HVCI/kCET, even with EDR/AV solutions enabled. #Kernel #RedTeam #InfoSec #CyberSecurity #Pentest #offsec #defender #VBS
A corrective control acts after a threat is detected to fix the problem. Since the antivirus automatically removes malware after detection, it’s performing a corrective action. #CyberSecurity #SecurityPlus #InfoSec
Stop scrolling if your business uses serial-to-IP converters ⚠️ 22 new flaws in Lantronix & Silex devices could let hackers hijack systems and tamper with data. Check exposure, patch firmware, isolate devices now. #CyberSecurity #InfoSec
Remote-first working complicates identity governance. 🔗 tinyurl.com/hkzf9sz3 Fix it with human & non-human ownership mapping, detection of unused high-risk access, & automated revocation. #cybersecurity #infosec #itsecurity

Industry Trend: identity is now the main attack surface. Permissions + misconfigurations = real risk. JIT access is now the only sane model. #cybersecurity #infosec #itsecurity app.stationx.net/articles/cloud…
app.stationx.net
Cloud Security Statistics [2026]: Key Data & Trends
Explore 50+ cloud security statistics for 2026 — breaches, misconfigurations, identity attacks, and market growth from 30+ sources.
>_ No Hat 2026 CfP is OPEN! 👾 Do you wanna have a good excuse to travel to beautiful Italy next autumn? Submit your latest research work at: nohat.it/cfp Check out last year's vibes to see what you're getting into: youtube.com/watch?v=WoxuZR… #NoHat2026 #InfoSec #CFP

youtube.com
YouTube
BITM Hacklab
new #phishing at hXXps://xan3ri[.]cfd/dulidpgo/PbkHGx/LTjfPu | 172.67.151.168 | None | Ascenty Data Centers e Telecomunicacoes SA | ASN AS52925 | #infosec #cybersecurity phishstats.info/search/6e9881a…
![PhishStats's tweet image. new #phishing at hXXps://xan3ri[.]cfd/dulidpgo/PbkHGx/LTjfPu | 172.67.151.168 | None | Ascenty Data Centers e Telecomunicacoes SA | ASN AS52925 | #infosec #cybersecurity
phishstats.info/search/6e9881a…](https://pbs.twimg.com/media/HG-ylbMasAATCBU.jpg)
Tuesday's CVE Brief is live: 🔴 11 actively exploited 🟠 32 critical 🟡 100 high priority Stay protected → cvebrief.com #cybersecurity #infosec #CVE #vulnerability

You receive a Google Docs link from someone you know, but it asks you to login again before viewing. What should you suspect? A. Session timeout B. Phishing attempt C. Server error D. DNS issue #CyberSecurity #InfoSec #Phishing #SecurityAwareness #TechTips
Most SaaS apps don’t get breached by “critical CVEs.” They get breached by IDOR, broken access control, and API abuse—issues most reports don’t prove exploitable. That’s the real risk. pentesttesting.com/professional-p… #CyberSecurity #Infosec #APIsecurity #DataProtection #OnlineSafety
pentesttesting.com
Professional Penetration Testing Report Sample
See what a professional penetration testing report sample includes, plus what to expect from a real SOC 2-ready security assessment.
Bitwarden CLI v2026.4.0 was trojanized via a compromised GitHub Action on April 22 — bw1.js exfiltrated dev secrets to audit.checkmarx[.]cx in a 93-min npm window. Vaults safe; CI/CD is the breach surface. Pin deps. Audit runners. #SupplyChain #DevSecOps #InfoSec
Yesterday I posted: knowledge before action. Today’s reminder: Sometimes systems aren’t broken… They’re just forgotten. Old subdomains. Test environments. Unused records. Many risks come from assets nobody is watching. #CyberSecurity #InfoSec #EthicalHacking
Anyone open to a light snap bypass test on their account? Pure curiosity of my eyes only #infosec #snapGod #monekeyapp #ometv #snaphack

No Metrics Are Better Than Bad Metrics in the SOC, Says NCSC infosecurity-magazine.com/news/no-metric… #cybersecurity #infosec #hacking
Anyone open to a harmless breach simulation on their profile? Pure curiosity, nothing serious #accountsecurity #infosec #hacked #ometv #monkeyapp #omegle #snap

Ethical Hacking Roadmap 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
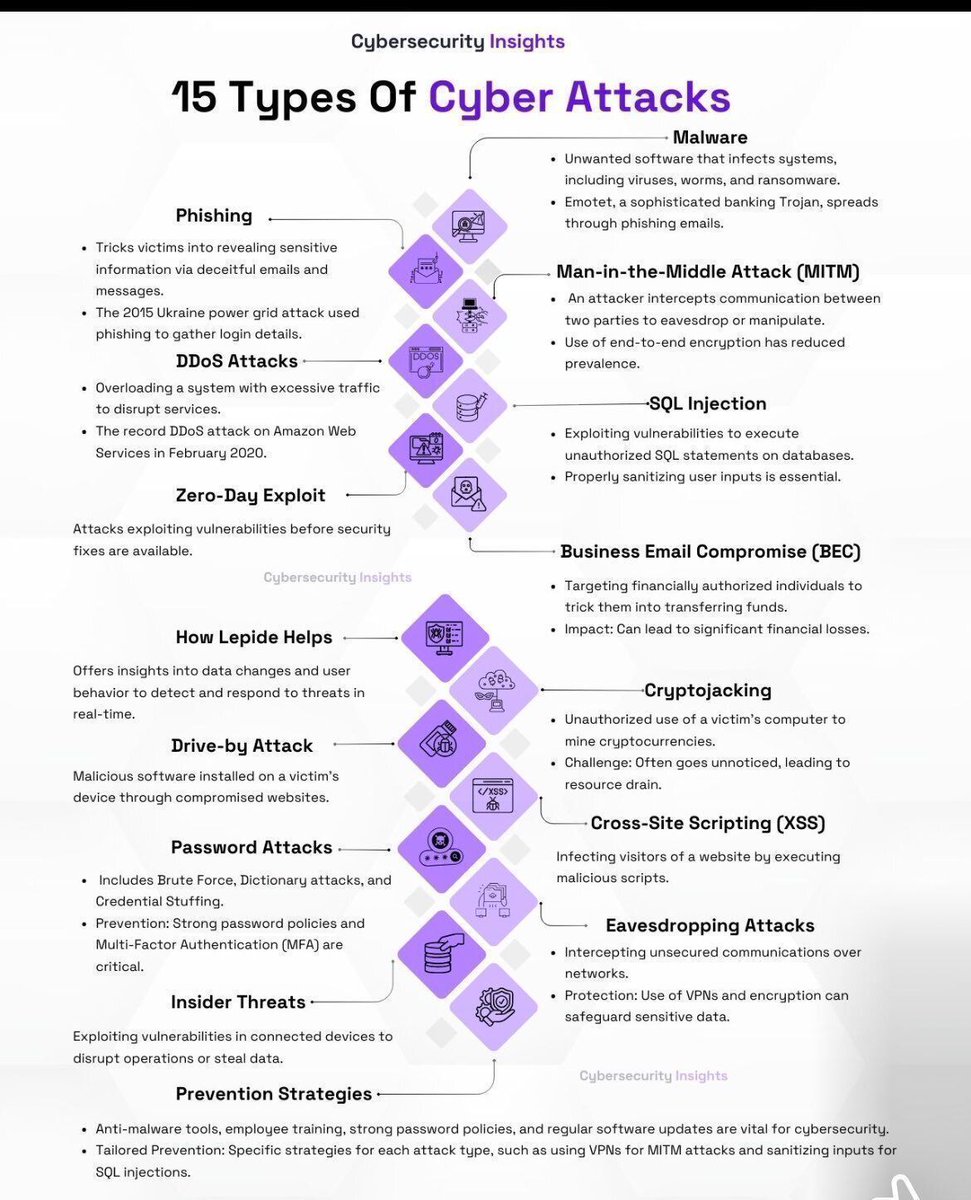
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
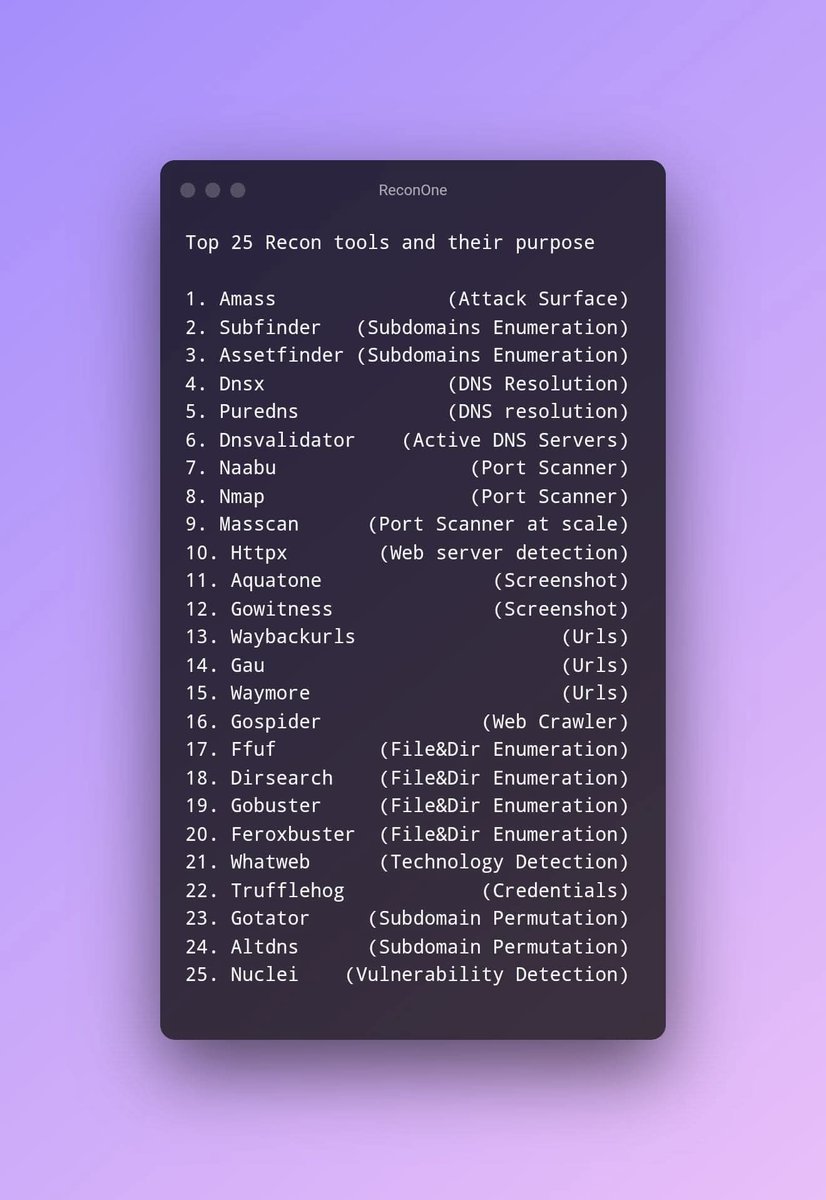
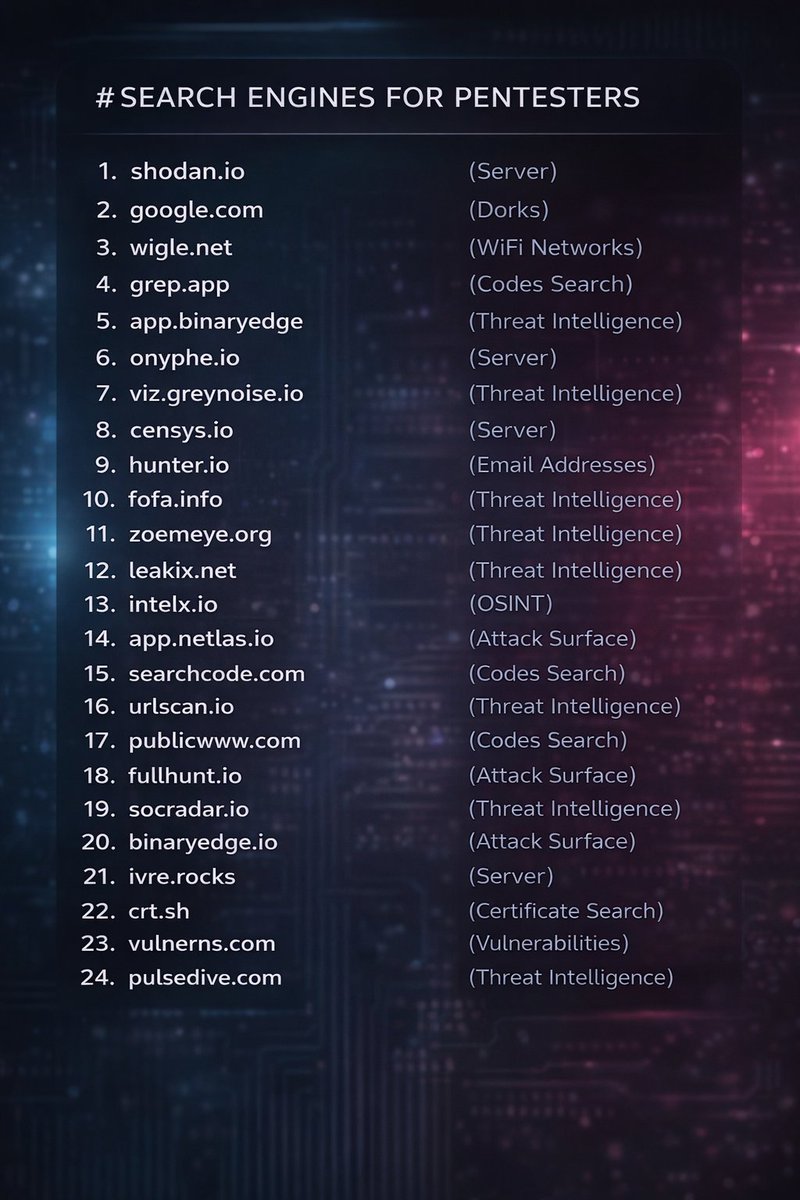
Every pentester should have these in their toolkit 👇🔥 From Shodan to crt.sh, this list covers servers, OSINT, attack surface, code search & threat intel Did I miss anything? Drop your favorite tools in the comments 👇 #BugBounty #CyberSecurity #Infosec
📢 Stay informed on the latest vulnerabilities with @CISAgov's Vulnerability Bulletin & gain valuable insights into emerging threats. 💡Check out the latest updates: cisa.gov/news-events/bu… #Cybersecurity #InfoSec #VulnerabilityManagement

New Spring Boot flaws (CVSS 9.1) bypass security filters and enable RCE via timing attacks. Impacting versions 2.7.x to 4.0.x—secure your Java apps now. #SpringBoot #JavaSecurity #InfoSec #RCE #CyberSecurity #CVE202640976 #SpringFramework #PatchNow securityonline.info/spring-boot-vu…

Finally @AnthropicAI approved my cyber use case in just 2h 25min upon submission For people getting rejected provide your profile: @Hacker0x01, @Bugcrowd, and a project with one of your github repos. Much appreciated, Anthropic team 🤎 #InfoSec #Anthropic #BugBounty


Banned from Claude Code in 30 Minutes The plan was simple: probe Claude Code APIs through Burp Suite (TLS checks off) and responsibly disclose anything interesting via HackerOne. My custom AI agent was also testing Claude Code's APIs in the background, so it was a joint effort

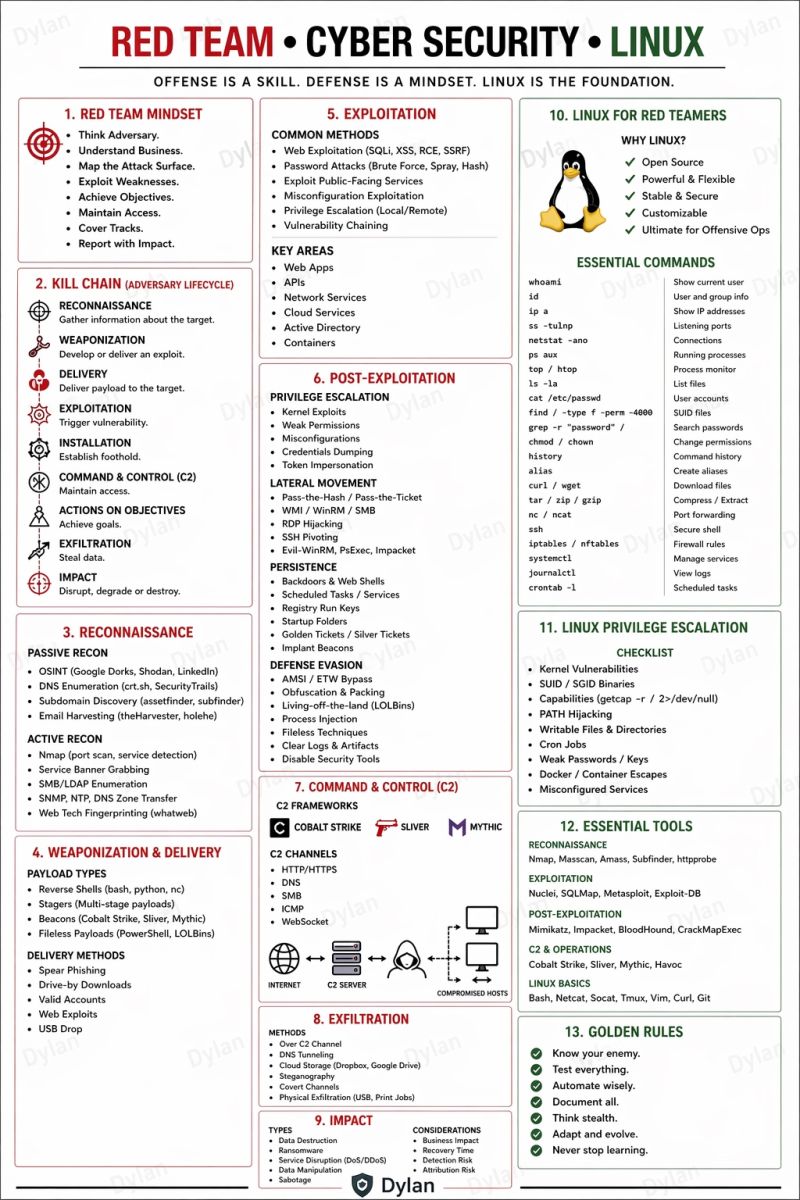
Red Team | Cyber Security | Linux 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

🚀 From Zero to Ethical Hacker: A Clear Roadmap Stop consuming random content. Follow a structured path: Networking → OS → Programming → Security → Tools → Practice Consistency beats everything. #CyberSecurity #EthicalHacking #InfoSec
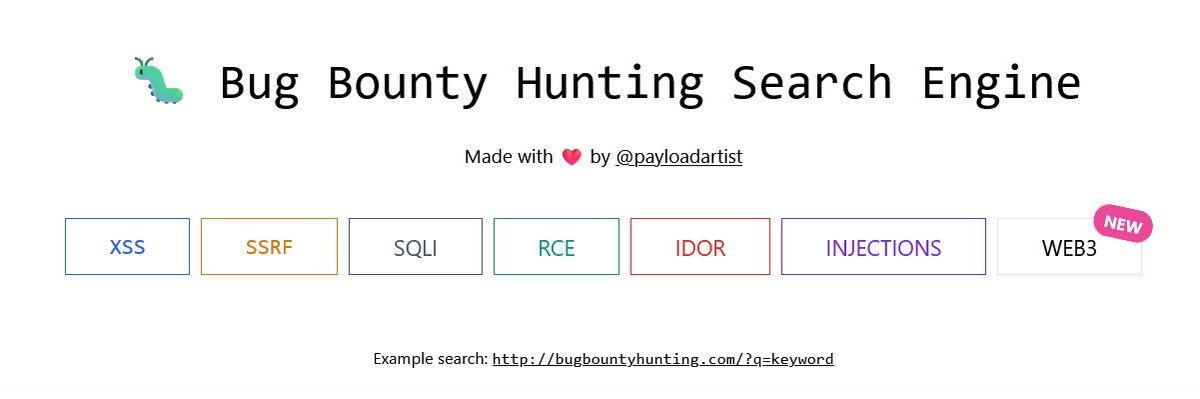
Hunters 🚨 One resource you should definitely bookmark: bugbountyhunting.com Writeups. Resources. Real learning. No fluff. #BugBountyHunter #CyberSecurity #InfoSec #EthicalHacking
AD Hash Types & Hashcat Modes 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI

🔐 RESOURCES: Secure Code Review(SCR) Learning Resources! YouTube SCR Series: youtube.com/playlist?list=… Rules: rules.sonarsource.com OWASP SCR Guide: owasp.org/www-project-co… Snippets: securitycipher.com/docs/security/… #infosec

📢 Stay informed on the latest vulnerabilities with @CISAgov's Vulnerability Bulletin & gain valuable insights into emerging threats. 💡Check out the latest updates: cisa.gov/news-events/bu… #Cybersecurity #InfoSec #VulnerabilityManagement

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Tuesday N/A
- 2. #LenaMiuxChanelCruise N/A
- 3. Kyle Tucker N/A
- 4. Pistons N/A
- 5. Clooney N/A
- 6. Cade N/A
- 7. Zambia N/A
- 8. #BCSpoilers N/A
- 9. Spencer Jones N/A
- 10. World War Eleven N/A
- 11. Kid Rock N/A
- 12. Duren N/A
- 13. #TusksUp N/A
- 14. Tabata N/A
- 15. #ForgedInGold N/A
- 16. Roseanne N/A
- 17. Devin Booker N/A
- 18. Lee Zeldin N/A
- 19. Runner N/A
- 20. Asta N/A