#breanetworks search results
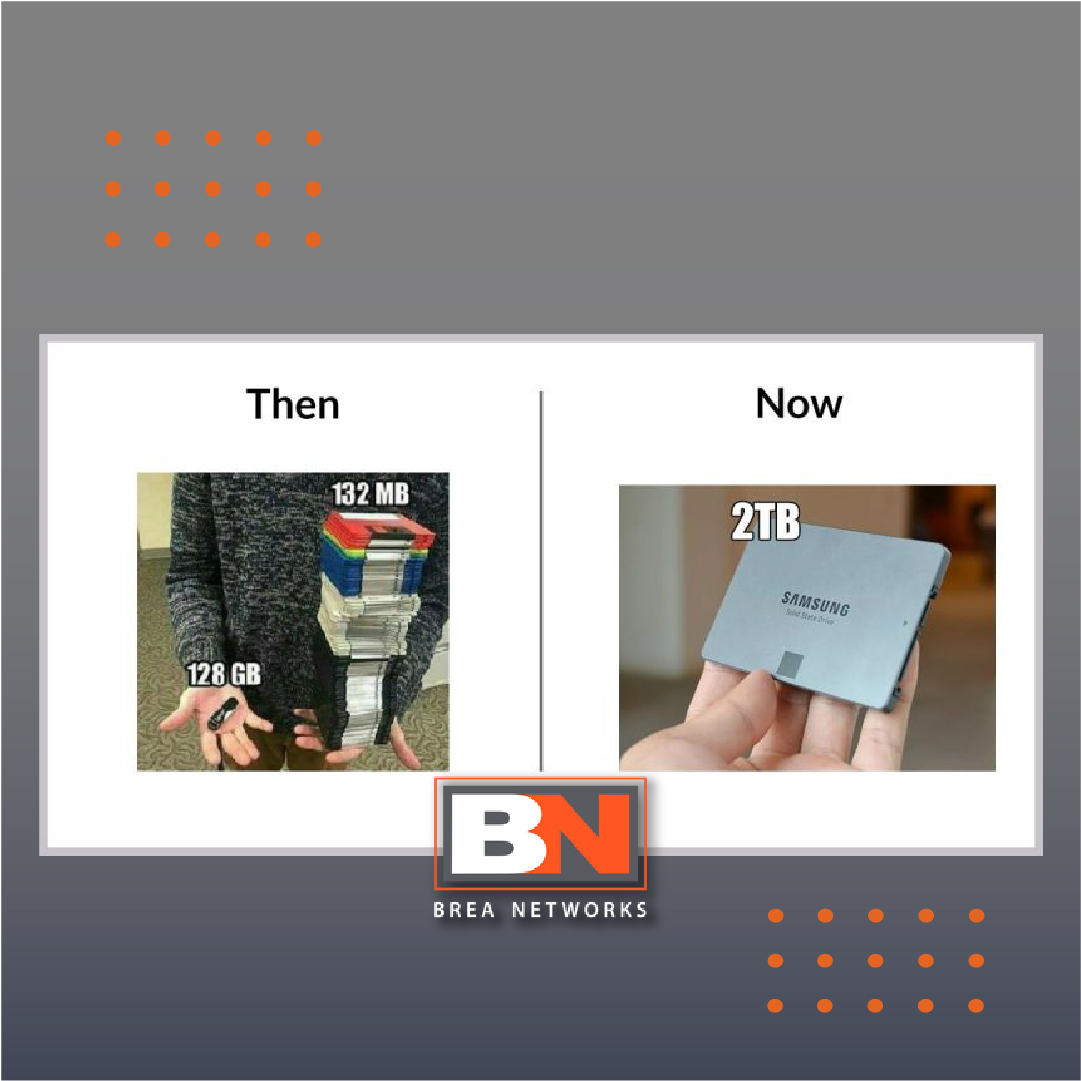
Nostalgia is good, but only in movies. When it comes to software, you should make sure to use only the latest or most updated versions! #BreaNetworks #Cybersecurity #WeCanHelp #FunnyFriday #ITCompany #GovernmentIT #BreaBusiness #AnaheimIT #OntarioCaliforniaIT #UnlimitedITSupport.

1. Learn about new PCI standards for building software. 2. Perform scans as early as possible. 3. Encrypt stored cardholder data. 4. Use network segmentation. 5. Ensure the security of cardholder data while in transit. #BreaNetworks #PCIDSS #WeCanHelp #GovernmentIT #DoDIT

RT RT Tying to fill knowledge gaps in IT? Regardless of your level of expertise, at Brea Networks, we can help! #BreaNetworks #WeCanHelp #IT…

Tying to fill knowledge gaps in IT? Regardless of your level of expertise, at Brea Networks, we can help! #BreaNetworks #WeCanHelp #ITSupport #ITCompany #CommercialIT #BreaBusiness #AnaheimIT #UnlimitedITSupport

Some colleges and universities are Department of Defense contractors for research purposes. In those cases, the Cybersecurity Maturity Model Certification (CMMC) is applied according to the CMMC level specified in the solicitation. #BreaNetworks #CMCC #WeCanHelp #Cybersecurity

CMMC Level 3 is based on the 110 controls outlined in NIST 800-171. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
#BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

If you work with any federal institution, then NIST SP 800-171 compliance is essential. #BreaNetworks #NISTSP800-171 #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

No, the Cybersecurity Maturity Model Certification (CMMC) does not apply to all companies that do business with the U.S. Government. For example, companies that produce only commercial-off-the-shelf (COTS) products are not required to obtain a CMMC certification. #BreaNetworks

While other companies need months to help organizations implement the CMMC standards, Brea Networks can do it in DAYS! #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards that applies to all entities that store, process, and/or transmit cardholder data. If your business accepts or processes payment cards, then you must comply with PCI DSS. #BreaNetworks

The term phishing refers to emails and text messages sent by cybercriminals impersonating reputable institutions with the purpose of tricking you into providing personal information or performing actions that are harmful to your organization. #breanetworks #pishing #cybersecurity

Implementation of such agreements will be accomplished through the rulemaking process. #BreaNetworks #CMMC #CUI #WeCanHelp #DoDIT #ITCompany #GovernmentIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

🎉 BIG NEWS from Brea Networks! We’re growing and excited to announce our NEW East Coast operations to better serve YOU! 🗽🌟 Our new office is now open at: 📍 1750 Tysons Blvd., #1500, Tysons Corner, VA 22102 #breanetworks #eastcoastexpansion #tysonscorner #customerfirst
Unlike ghosts, cybersecurity risks are very real. You don't need a sixth sense to guard off attacks, all you have to do is to partner with a cybersecurity company committed to protecting you #BreaNetworks #FunnyFriday #Cybersecurity #WeCanHelp #DoDIT #GovernmentIT #CMMC

You should do a backup now #BreaNetworks #Backup #Ransomware #Pishing #WeCanHelp #ITCompany #GovernmentIT #BreaBusiness #AnaheimIT #UnlimitedITSupport.

CMMC is a tiered cybersecurity model for DoD contractors. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
Get in touch with us for DFARS compliance services you’ll enjoy. #BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT"

🎉 BIG NEWS from Brea Networks! We’re growing and excited to announce our NEW East Coast operations to better serve YOU! 🗽🌟 Our new office is now open at: 📍 1750 Tysons Blvd., #1500, Tysons Corner, VA 22102 #breanetworks #eastcoastexpansion #tysonscorner #customerfirst
No, the Cybersecurity Maturity Model Certification (CMMC) does not apply to all companies that do business with the U.S. Government. For example, companies that produce only commercial-off-the-shelf (COTS) products are not required to obtain a CMMC certification. #BreaNetworks

The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards that applies to all entities that store, process, and/or transmit cardholder data. If your business accepts or processes payment cards, then you must comply with PCI DSS. #BreaNetworks

The term phishing refers to emails and text messages sent by cybercriminals impersonating reputable institutions with the purpose of tricking you into providing personal information or performing actions that are harmful to your organization. #breanetworks #pishing #cybersecurity

Some colleges and universities are Department of Defense contractors for research purposes. In those cases, the Cybersecurity Maturity Model Certification (CMMC) is applied according to the CMMC level specified in the solicitation. #BreaNetworks #CMCC #WeCanHelp #Cybersecurity

Nostalgia is good, but only in movies. When it comes to software, you should make sure to use only the latest or most updated versions! #BreaNetworks #Cybersecurity #WeCanHelp #FunnyFriday #ITCompany #GovernmentIT #BreaBusiness #AnaheimIT #OntarioCaliforniaIT #UnlimitedITSupport.

#BreaNetworks #CMMC #NIST800-171 #CMMC #DFARS7012 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

Get in touch with us for DFARS compliance services you’ll enjoy. #BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT"

#BreaNetworks #CMMC #NIST800-171 #CMMC #DFARS7012 #Cybersecurity #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

#BreaNetworks #CMMC #NIST800-171 #CMMC #DFARS7012 #Cybersecurity #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
Unlike ghosts, cybersecurity risks are very real. You don't need a sixth sense to guard off attacks, all you have to do is to partner with a cybersecurity company committed to protecting you #BreaNetworks #FunnyFriday #Cybersecurity #WeCanHelp #DoDIT #GovernmentIT #CMMC

Implementation of such agreements will be accomplished through the rulemaking process. #BreaNetworks #CMMC #CUI #WeCanHelp #DoDIT #ITCompany #GovernmentIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

As the name suggests, DFARS vulnerability assessments involve determining the level of exposure from various weak points in your systems. In addition, it helps us identify gaps in different Controlled Unclassified Information (CUI) technologies and environments #BreaNetworks
1. Learn about new PCI standards for building software. 2. Perform scans as early as possible. 3. Encrypt stored cardholder data. 4. Use network segmentation. 5. Ensure the security of cardholder data while in transit. #BreaNetworks #PCIDSS #WeCanHelp #GovernmentIT #DoDIT

If you work with any federal institution, then NIST SP 800-171 compliance is essential. #BreaNetworks #NISTSP800-171 #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

Technology evolves fast #BreaNetworks #Cybersecurity #WeCanHelp #FunnyFriday #ITCompany #GovernmentIT #DoDIT #BreaBusiness #AnaheimIT #UnlimitedITSupport
CMMC Level 3 is based on the 110 controls outlined in NIST 800-171. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
#BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

CMMC is a tiered cybersecurity model for DoD contractors. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
RT RT Tying to fill knowledge gaps in IT? Regardless of your level of expertise, at Brea Networks, we can help! #BreaNetworks #WeCanHelp #IT…

Tying to fill knowledge gaps in IT? Regardless of your level of expertise, at Brea Networks, we can help! #BreaNetworks #WeCanHelp #ITSupport #ITCompany #CommercialIT #BreaBusiness #AnaheimIT #UnlimitedITSupport

Get in touch with us for DFARS compliance services you’ll enjoy. #BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT"

No, the Cybersecurity Maturity Model Certification (CMMC) does not apply to all companies that do business with the U.S. Government. For example, companies that produce only commercial-off-the-shelf (COTS) products are not required to obtain a CMMC certification. #BreaNetworks

If you work with any federal institution, then NIST SP 800-171 compliance is essential. #BreaNetworks #NISTSP800-171 #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

The Payment Card Industry Data Security Standard (PCI DSS) is a set of security standards that applies to all entities that store, process, and/or transmit cardholder data. If your business accepts or processes payment cards, then you must comply with PCI DSS. #BreaNetworks

You should do a backup now #BreaNetworks #Backup #Ransomware #Pishing #WeCanHelp #ITCompany #GovernmentIT #BreaBusiness #AnaheimIT #UnlimitedITSupport.

CMMC Level 3 is based on the 110 controls outlined in NIST 800-171. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
Unlike ghosts, cybersecurity risks are very real. You don't need a sixth sense to guard off attacks, all you have to do is to partner with a cybersecurity company committed to protecting you #BreaNetworks #FunnyFriday #Cybersecurity #WeCanHelp #DoDIT #GovernmentIT #CMMC

1. Learn about new PCI standards for building software. 2. Perform scans as early as possible. 3. Encrypt stored cardholder data. 4. Use network segmentation. 5. Ensure the security of cardholder data while in transit. #BreaNetworks #PCIDSS #WeCanHelp #GovernmentIT #DoDIT

#BreaNetworks #DFARS #CMCC #WeCanHelp #Cybersecurity #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

Technology evolves fast #BreaNetworks #Cybersecurity #WeCanHelp #FunnyFriday #ITCompany #GovernmentIT #DoDIT #BreaBusiness #AnaheimIT #UnlimitedITSupport
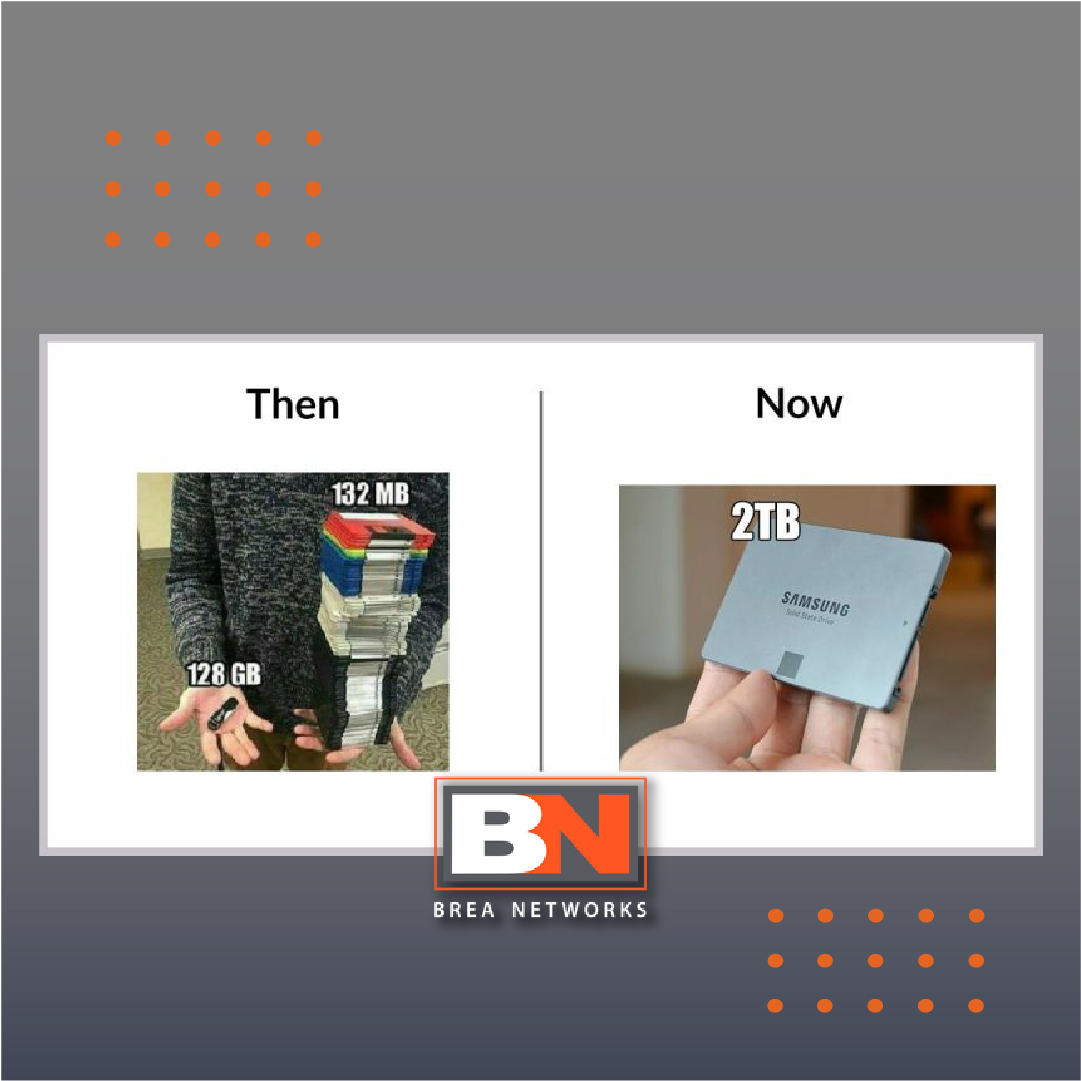
Nostalgia is good, but only in movies. When it comes to software, you should make sure to use only the latest or most updated versions! #BreaNetworks #Cybersecurity #WeCanHelp #FunnyFriday #ITCompany #GovernmentIT #BreaBusiness #AnaheimIT #OntarioCaliforniaIT #UnlimitedITSupport.

CMMC is a tiered cybersecurity model for DoD contractors. #BreaNetworks #CMMC #NIST800-171 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT
#BreaNetworks #CMMC #NIST800-171 #CMMC #DFARS7012 #ITAR #WeCanHelp #ITCompany #GovernmentIT #DoDIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

Implementation of such agreements will be accomplished through the rulemaking process. #BreaNetworks #CMMC #CUI #WeCanHelp #DoDIT #ITCompany #GovernmentIT #BreaBusiness #UnlimitedITSupport #AnaheimIT #FullertonIT #BreaIT #SantaAnaIT #IrvineIT #CoronaIT #OntarioCaliforniaIT

The term phishing refers to emails and text messages sent by cybercriminals impersonating reputable institutions with the purpose of tricking you into providing personal information or performing actions that are harmful to your organization. #breanetworks #pishing #cybersecurity

As the name suggests, DFARS vulnerability assessments involve determining the level of exposure from various weak points in your systems. In addition, it helps us identify gaps in different Controlled Unclassified Information (CUI) technologies and environments #BreaNetworks
Some colleges and universities are Department of Defense contractors for research purposes. In those cases, the Cybersecurity Maturity Model Certification (CMMC) is applied according to the CMMC level specified in the solicitation. #BreaNetworks #CMCC #WeCanHelp #Cybersecurity

Something went wrong.
Something went wrong.
United States Trends
- 1. #WWERaw N/A
- 2. #WNBADraft N/A
- 3. Raven N/A
- 4. Crochet N/A
- 5. Flau'jae N/A
- 6. Red Cross N/A
- 7. Azzi Fudd N/A
- 8. Latson N/A
- 9. Lauren Betts N/A
- 10. Olivia Miles N/A
- 11. Mystics N/A
- 12. Will Warren N/A
- 13. Cathy Kelley N/A
- 14. #AmericanIdol N/A
- 15. Coach Mac N/A
- 16. Holly Rowe N/A
- 17. Gianna Kneepkens N/A
- 18. Rori Harmon N/A
- 19. Marta Suarez N/A
- 20. Riley Gaines N/A




