#ransomware search results
As usual multiple #databreach reports from across #healthcare stemming from #ransomware attacks. If not a breach revealed, then a settlement. hipaajournal.com/ransomware-att… #HIPAA
Credit unions are becoming a top #ransomware target. Lean teams. Expanding digital footprint. Zero tolerance for downtime. Attackers know exactly where to apply pressure. Join leaders from Aloha Pacific Credit Union, Campus USA Credit Union, and Halcyon for an unfiltered look
halcyon.ai
A Matter of Trust: Ransomware Resilience for Credit Unions
A Matter of Trust: Ransomware Resilience for Credit Unions
New Ransomware Victim Detected Group: safepay Victim: bootstransport.ca Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
bootstransport.ca
Alberta Flatdeck Transportation - Boots Transport Ltd.
Alberta Flatdeck Transportation Company, serving all points in Western Canada; their primary business has been offering services to the pipe & steel companies.
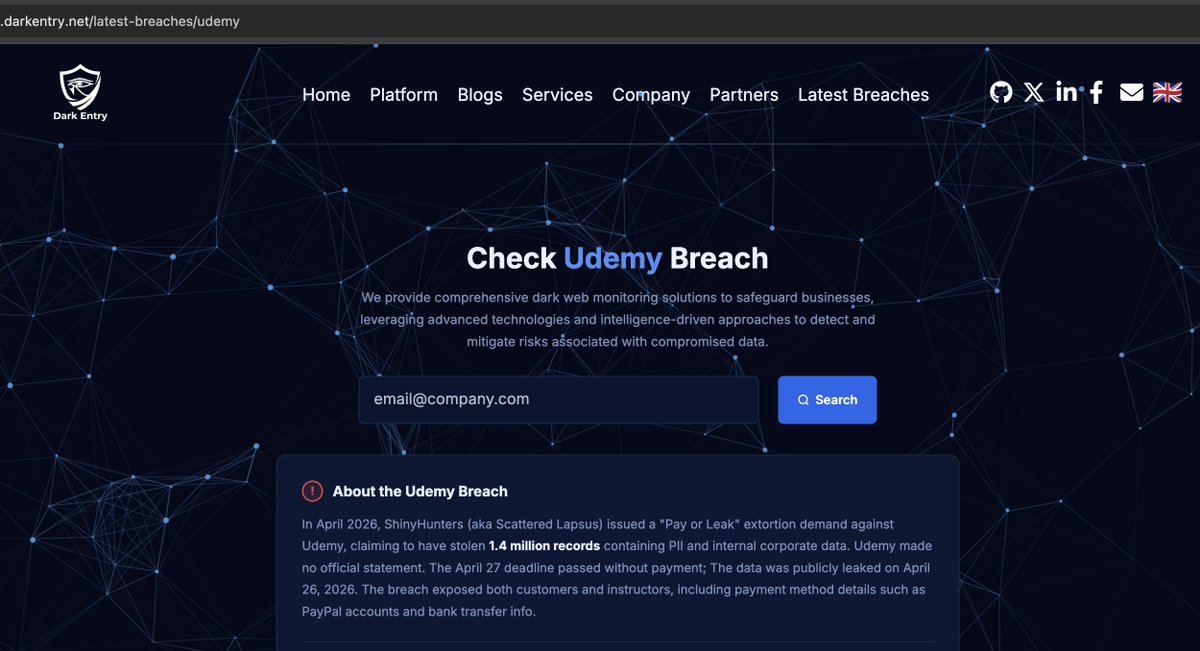
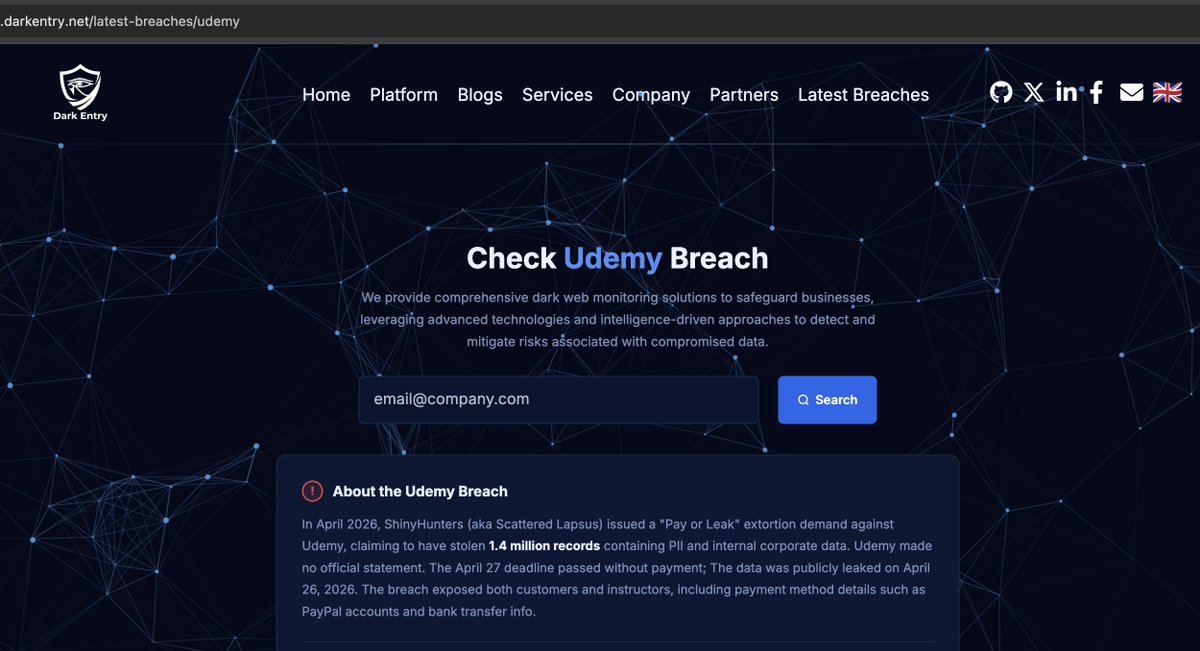
#Udemy data breach confirmed. After refusing to pay the ransom, hackers released data of 1.4M users, including personal and financial details. We @DarkEntryAms launched a lookup tool so you can check if you’re affected: darkentry.net/latest-breache… #DataBreach #Ransomware


New Ransomware Victim Detected Group: safepay Victim: maiadouro.pt Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: safepay Victim: zonaovest.to.it Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
Critical cPanel flaw is being mass exploited in “Sorry” ransomware attacks. Authentication bypass allows attackers to take control of servers and encrypt data. Over 44,000 systems already impacted, with active exploitation ongoing. #CyberSecurity #Ransomware #cPanel

New Ransomware Victim Detected Group: safepay Victim: hokuyo2006.co.jp Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
Ransomware Targeting Nonprofits: “Kicking Someone While They’re Down” #cybersecurity #ransomware #ransomwareattack
🏴☠️ Qilin has just published a new victim : Seagate Capital Construction ----------------- ransomware.live/id/U2VhZ2F0ZSB… #ransomware
New Ransomware Victim Detected Group: safepay Victim: fital-treppenlifte.de Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
🏴☠️ Qilin has just published a new victim : North Star Signs ----------------- ransomware.live/id/Tm9ydGggU3R… #ransomware
VECT ransomware: paying won’t bring your files back. ❌ No recovery | ❌ No ROI | ❌ Permanent loss Read more from @CheckPointSW blog: blog.checkpoint.com/security/vect-… #ThreatPrevention #Ransomware #CheckPoint #AmiViz

Healthcare systems are prime targets for ransomware. A UCSF attack in 2020 highlights the power of network segmentation. When ransomware hit, it was contained within one segment, preventing a total shutdown. #Cybersecurity #HealthcareIT #Ransomware
#Automotive is becoming #ransomware’s favorite target - now accounting for 44% of incidents. Not by chance. Because when production stops, pressure spikes. And attackers know this industry can’t sit still. At the same time, the attack surface has exploded - from cloud systems
New Ransomware Victim Detected Group: safepay Victim: dahlgrenscement.se Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
#Healthcare remains the most targeted critical infrastructure sector for #cyberattacks, driven by #ransomware, large-scale data theft, and increasing geopolitical activity. Check out our blog for more info and PolySwarm’s related samples. blog.polyswarm.io/critical-condi…
New Ransomware Victim Detected Group: pear Victim: Morning Star Tours Discovered: 2026-05-04 18:04:24.504272 More info: cti.fyi/groups/pear.ht… #ransomware #cti #cybersecurity
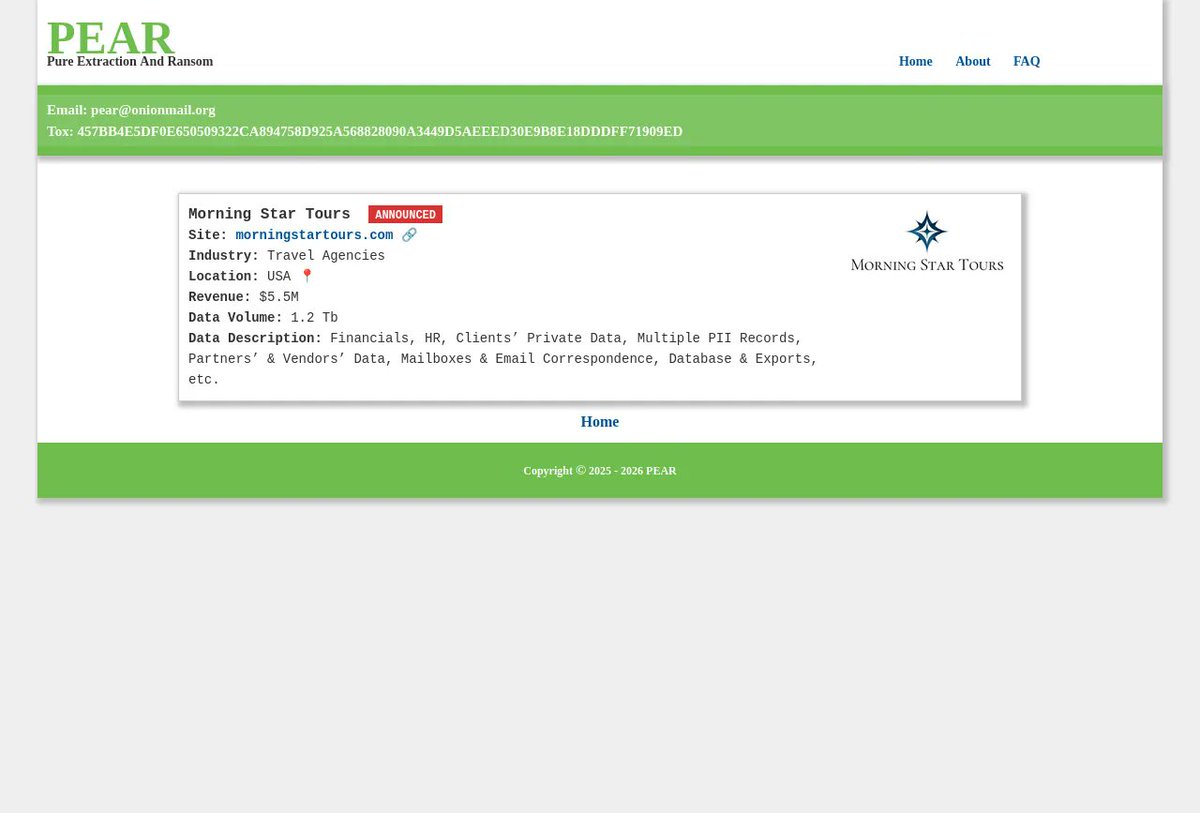
@FalconFeedsio's alerts on PEAR & Everest ransomware show the threat. Our AI Detective blocks phishing/malvertising with Link Scanner & on-device AI. Ransomware Guidance Hub aids recovery: ai-detective.xyz #CyberSecurity #Ransomware
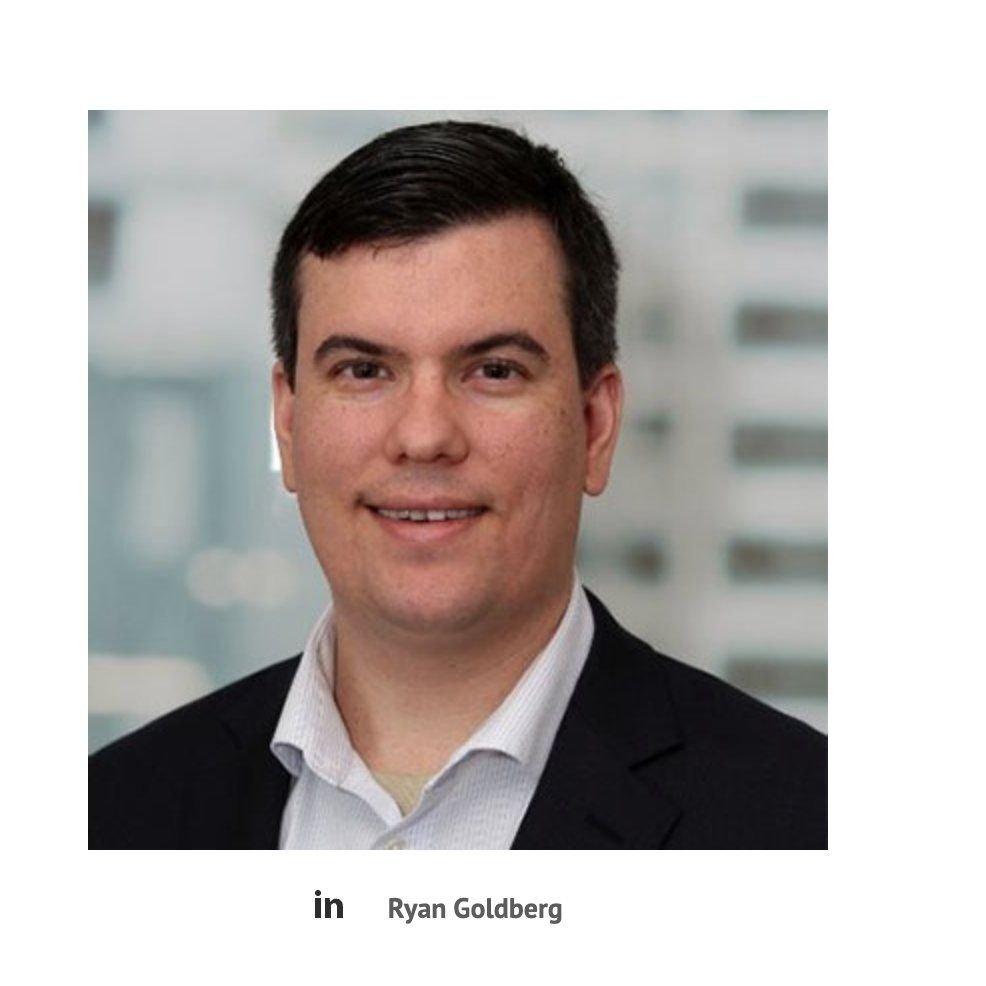
🚨 Two US cybersecurity professionals have been sentenced for moonlighting as ALPHV BlackCat ransomware affiliates. Ryan Goldberg, 40, of Georgia, and Kevin Martin, 36, of Texas, deployed BlackCat ransomware against multiple US victims between April and December 2023. They paid
New Ransomware Victim Detected Group: safepay Victim: hokuyo2006.co.jp Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: safepay Victim: bootstransport.ca Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
bootstransport.ca
Alberta Flatdeck Transportation - Boots Transport Ltd.
Alberta Flatdeck Transportation Company, serving all points in Western Canada; their primary business has been offering services to the pipe & steel companies.
New Ransomware Victim Detected Group: safepay Victim: dahlgrenscement.se Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
#Healthcare remains the most targeted critical infrastructure sector for #cyberattacks, driven by #ransomware, large-scale data theft, and increasing geopolitical activity. Check out our blog for more info and PolySwarm’s related samples. blog.polyswarm.io/critical-condi…
New Ransomware Victim Detected Group: safepay Victim: maiadouro.pt Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: safepay Victim: zonaovest.to.it Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: safepay Victim: fital-treppenlifte.de Discovered: 2026-05-04 20:04:51.883143 More info: cti.fyi/groups/safepay… #ransomware #cti #cybersecurity
Credit unions are becoming a top #ransomware target. Lean teams. Expanding digital footprint. Zero tolerance for downtime. Attackers know exactly where to apply pressure. Join leaders from Aloha Pacific Credit Union, Campus USA Credit Union, and Halcyon for an unfiltered look
halcyon.ai
A Matter of Trust: Ransomware Resilience for Credit Unions
A Matter of Trust: Ransomware Resilience for Credit Unions
🏴☠️ Qilin has just published a new victim : Seagate Capital Construction ----------------- ransomware.live/id/U2VhZ2F0ZSB… #ransomware
As usual multiple #databreach reports from across #healthcare stemming from #ransomware attacks. If not a breach revealed, then a settlement. hipaajournal.com/ransomware-att… #HIPAA
#Automotive is becoming #ransomware’s favorite target - now accounting for 44% of incidents. Not by chance. Because when production stops, pressure spikes. And attackers know this industry can’t sit still. At the same time, the attack surface has exploded - from cloud systems
🚨 South African Banking Under Siege: 12TB Data Theft Exposes Rising Global #Ransomware Threat -Fact Checker: ✅: 1 ❌: 0 || 1/1 undercodenews.com/south-african-…
🇨🇳💣 China's Storm-1175 is weaponizing zero-days to drop Medusa ransomware — fast. 16+ vulns exploited since 2023. State-sponsored ransomware is now real. thehackernews.com/2026/04/china-… #ransomware #ZeroDay #cybersecurity
🏴☠️ Pear has just published a new victim : Morning Star Tours ----------------- ransomware.live/id/TW9ybmluZyB… #ransomware
🚨 El cibercrimen ya no escala… se dispara con IA. El Panorama de Amenazas 2026, de Fortinet, deja un dato alarmante: las víctimas de ransomware crecieron un 389% interanual. 🔗 Lee la nota en nuestra web: itsitio.com/ch/seguridad/p… #Ciberseguridad #Ransomware

🆕 Recap sugli attacchi #Ransomware a target 🇮🇹, via @ransomnews | ransomnews.online 🔘 Riassunto dal 1 Gennaio 2026 al 30 Aprile 2026: 🔗 Dati e Statistiche: ransomnews.github.io/RedACT/ ▪️ Rivendicazioni registrate a Gennaio 2026: 20 ▪️ Rivendicazioni registrate a Gennaio

New Ransomware Victim Detected Group: qilin Victim: Rizzuto Law Firm Discovered: 2026-05-04 18:05:04.534154 More info: cti.fyi/groups/qilin.h… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: qilin Victim: General Hardware Discovered: 2026-05-04 18:05:04.534154 More info: cti.fyi/groups/qilin.h… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: qilin Victim: Cushman & Wakefield Discovered: 2026-05-04 18:05:04.534154 More info: cti.fyi/groups/qilin.h… #ransomware #cti #cybersecurity
New Ransomware Victim Detected Group: qilin Victim: Seagate Capital Construction Discovered: 2026-05-04 18:05:04.534154 More info: cti.fyi/groups/qilin.h… #ransomware #cti #cybersecurity

🆕 Recap sugli attacchi #Ransomware a target 🇮🇹, via @ransomnews | ransomnews.online 🔘 Riassunto dal 1 Gennaio 2026 al 30 Aprile 2026: 🔗 Dati e Statistiche: ransomnews.github.io/RedACT/ ▪️ Rivendicazioni registrate a Gennaio 2026: 20 ▪️ Rivendicazioni registrate a Gennaio

#AlertaDigitalEC Se denuncia que @MayoristaAmbato habría sufrido un ataque de #ransomware .SORRY una vunerabilidad en linux, vía @rocurun @dev_clopez

Según parase la pagina web ha sido comprometida con ransomware @MayoristaAmbato @usuariosdigital @EcuCERT_EC @Arcotel_ec #Ecuador #ransomware

Ransomware groups coordinate on dark web forums before they strike. SOCRadar Advanced Dark Web Monitoring tracks these discussions, leaked credentials, and stolen financial data to deliver timely alerts. Read more at the link below. 👇 hubs.la/Q03-wJlv0 #Ransomware

🚨 nuova rivendicazione #ransomware Italia 🚨 🏴☠️ gruppo #Nova 🧬 Reschio S.R.L. | Lisciano Niccone (PG) 🎯 settore: ricevimento turistico 🔗 reschio.com 🗓️ 30 aprile 2026 📄 sample: - ▪️ dati esfiltrati dichiarati: 230.00GB ▪️ dati esfiltrati pubblicati: - ⏲️

What do 4 major #Ransomware reports say about 2026? We’re comparing Mandiant, CrowdStrike, Chainalysis & Palo Alto reports LIVE. Bring your questions! 📅 Tomorrow, May 5th 1 PM EST Set your reminder: buff.ly/Jb4V9mU #DFIR #Cybersecurity

🚨 nuova rivendicazione #ransomware Italia 🚨 🏴☠️ gruppo #M3RX 🧬 ROTAK S.R.L. | Priolo Gargallo (SR) 🎯 settore: automotive 🔗 rotak.it 🗓️ 24 aprile 2026 📄 sample: - ▪️ dati esfiltrati dichiarati: - ▪️ dati esfiltrati pubblicati: - ⏲️ scadenza: - #ransomNews

🛑 Qilin and Warlock #ransomware are disabling defenses before attacks using BYOVD techniques. Qilin uses a side-loaded DLL to kill 300+ EDR drivers via vulnerable kernel drivers. Warlock exploits SharePoint and uses similar drivers to bypass kernel-level security, often

🚨 nuova rivendicazione #ransomware Italia 🚨 🏴☠️ gruppo #Qilin 🧬 Abazia S.P.A. | Felizzano (AL) 🎯 settore: componenti auto 🔗 abazia.com 🗓️ 30 aprile 2026 📄 sample: - ▪️ dati esfiltrati dichiarati: - ▪️ dati esfiltrati pubblicati: sì ⏲️ scadenza: - #ransomNews

Attacco #Ransomware alla Sapienza Università di Roma. Chiederei alla sottosegretaria @FaBergamotto cosa intende per "senza perdita di alcun dato" (già sentita per altri attacchi di cui sappiamo come è andata a finire: con la pubblicazione dei dati esfiltrati). Che il @csirt_it

#INCRansom #ransomware group has published #GruppoSelex 🇮🇹 (@GruppoSelex) as a potential #cyberattack target on its leak site. #GruppoSelex operates supermarkets, hypermarkets, pet stores, and e-commerce platforms across #Italy 🇮🇹. Track updates for this incident at #VenariX ➡️


A recent report unveils the emergence of quadruple extortion #Ransomware. securityboulevard.com/2026/04/ransom…

🚨 nuova rivendicazione #ransomware Italia 🚨 🏴☠️ gruppo #akira 🧬 CSA S.P.A. | Milano 🎯 settore: servizi marittimi 🔗 csaspa.com 🗓️ 14 aprile 2026 📄 sample: - ▪️ dati esfiltrati dichiarati: - ▪️ dati esfiltrati pubblicati: - ⏲️ scadenza: - #ransomNews

#Ciberseguridad «Cómo actuar en caso de un ataque de #ransomware. Signos de Alerta» @osiseguridad @INCIBE tinyurl.com/mrcbv86f

🚨 nuova rivendicazione #ransomware Italia 🚨 🏴☠️ gruppo #Coinbasecartel 🧬 ASTM S.P.A. | Torino 🎯 settore: servizi infrastrutturali 🔗 astm.it 🗓️ 18 aprile 2026 📄 sample: - ▪️ dati esfiltrati dichiarati: - ▪️ dati esfiltrati pubblicati: - ⏲️ scadenza: -

JUST IN: Facing mounting criticism over yet another catastrophic #ransomware event, executives at several major corporations have reportedly found a groundbreaking new solution: Simply reclassify cyber extortion payments as “unexpected cloud infrastructure expenses.” “This

Two US cybersecurity professionals get 4 years in prison for acting as ALPHV BlackCat ransomware affiliates, extorting victims and leaking patient data. #Ransomware #CyberSecurity #ALPHV #BlackCat #InsiderThreat #InfoSec #CyberCrime #Justice securityonline.info/cybersecurity-…

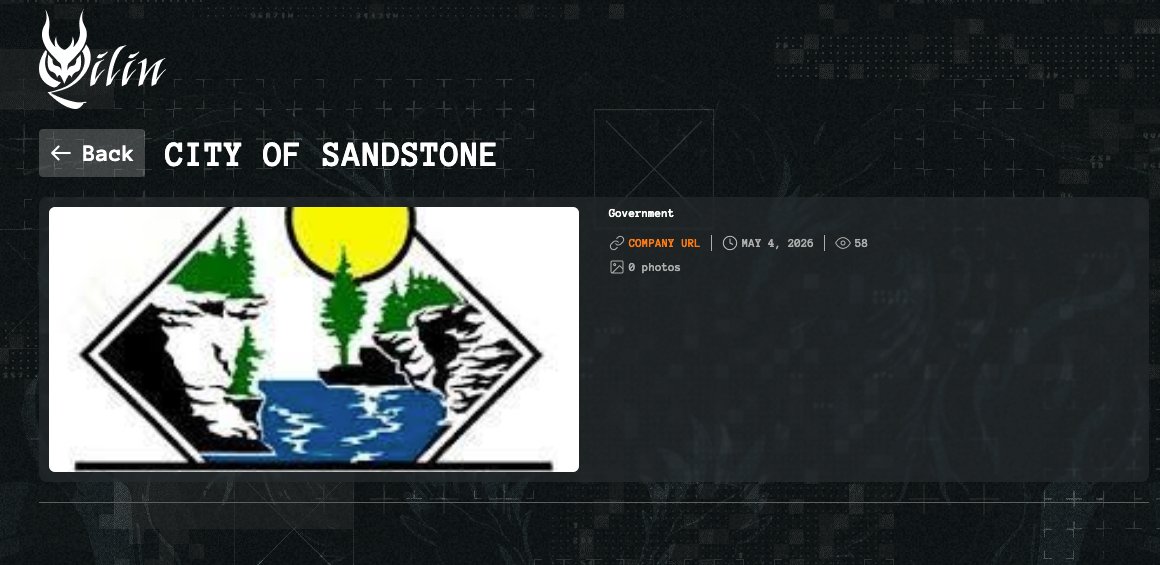
#Qilin #ransomware group has allegedly claimed responsibility for a #cyberattack targeting the City of Sandstone (sandstone.govoffice.com), a local government authority in #Minnesota, #USA 🇺🇸... Track this incident on #VenariX ➡️ venarix.com #CityofSandstone #InfoSec
🚨 El cibercrimen ya no escala… se dispara con IA. El Panorama de Amenazas 2026, de Fortinet, deja un dato alarmante: las víctimas de ransomware crecieron un 389% interanual. 🔗 Lee la nota en nuestra web: itsitio.com/ch/seguridad/p… #Ciberseguridad #Ransomware

#Udemy data breach confirmed. After refusing to pay the ransom, hackers released data of 1.4M users, including personal and financial details. We @DarkEntryAms launched a lookup tool so you can check if you’re affected: darkentry.net/latest-breache… #DataBreach #Ransomware


Something went wrong.
Something went wrong.
United States Trends
- 1. May the 4th N/A
- 2. Star Wars N/A
- 3. Skubal N/A
- 4. #Olandria N/A
- 5. Doku N/A
- 6. Dolly N/A
- 7. John Sterling N/A
- 8. Jedi N/A
- 9. Met Gala N/A
- 10. Anthony Edwards N/A
- 11. Pulitzer N/A
- 12. #ArmySelcaDay N/A
- 13. Tyrod Taylor N/A
- 14. Everton N/A
- 15. #BEYGALA N/A
- 16. Stefon Diggs N/A
- 17. Steam Controller N/A
- 18. Vader N/A
- 19. Supremacy Clause N/A
- 20. #Void_Without_SevEN N/A






























































![usuariosdigital's profile picture. 🌐
[toda la internet + todo el tiempo + para todos]
[libre + segura + abierta + neutra]
[conéctate + colabora + comparte]](https://pbs.twimg.com/profile_images/1939766620269735938/RNFDVLfm.jpg)