#cybersecuritynews search results
Week in review: High-severity LPE vulnerability in the Linux kernel, cPanel 0-day exploited for months - helpnetsecurity.com/2026/05/03/wee… - #WeekInReview #Cybersecurity #CybersecurityNews

South Korea’s tax agency accidentally exposed a crypto wallet seed phrase in press photos. Result: ~$4.8M in seized PRTG tokens drained within hours. A stark reminder: private key exposure = total loss. #CryptoSecurity #Blockchain #CybersecurityNews

સાયબર સેન્ટર ઓફ એક્સેલન્સ, ગુજરાત દ્વારા રૂ.3,90,30,047/- ફ્રોડના ગુનામાં શેર બજારમાં જંગી નફો કમાવાની લાલચ આપી લોકોને ફસાવી છેતરપપિંડી કરનાર આરોપીઓને ઝડપી પાડેલ છે. #CybersecurityNews @sanghaviharsh @GujaratPolice @Cyberdost @vivekpbheda

When a Friend Request Becomes a Cyber Threat: APT37’s New Facebook-Based Attack Trusted connection or hidden threat? When social media becomes the entry point for cyber espionage. #facebook #cybersecuritynews Full Story 👉 cybersecurity88.com/news/north-kor…

⚠️Σε μια πρωτοφανή επιχείρηση καταστολής του κυβερνοεγκλήματος, οι ευρωπαϊκές αρχές εντόπισαν χιλιάδες χρήστες υπηρεσιών "DDoS-for-hire", στέλνοντας προειδοποιητικά μηνύματα και κλείνοντας δεκάδες ιστοτόπους. #Europol #CyberSecurityNews #DDoS gr.pcmag.com/security/51747…
New infosec products of the week: April 17, 2026 - helpnetsecurity.com/2026/04/17/new… - @AxoniusInc @Broadcom @Siemens #CyberSecurity #CybersecurityNews
Microsoft Emergency NET 10.0.7 Update to Patch Elevation of Privilege Vulnerability Source: cybersecuritynews.com/emergency-net-... Microsoft has issued an emergency out-of-band (OOB) security update for NET 10, releasing version 10.0.7 on may 1, 2026, #cybersecuritynews
Week in review: Claude Mythos finds 271 Firefox flaws, Vercel breach - helpnetsecurity.com/2026/04/26/wee… - #WeekInReview #Cybersecurity #CybersecurityNews

Καθώς η τεχνητή νοημοσύνη κινείται με γοργό ρυθμό, οι ειδικοί προειδοποιούν ότι μόνο οι μηχανές μπορούν πλέον να ελέγξουν τις μηχανές, θέτοντας τον άνθρωπο σε ρόλο απλού επόπτη. #RSAC2026 #CyberSecurityNews gr.pcmag.com/security/51624…
⚠️Προσοχή στις δήθεν δωρεάν εκδόσεις του Claude Code στο GitHub – Η Zscaler προειδοποιεί για επικίνδυνα στελέχη λογισμικού που κλέβουν δεδομένα. #ClaudeCode #Zscaler #CyberSecurityNews gr.pcmag.com/security/51699…
Week in review: High-severity LPE vulnerability in the Linux kernel, cPanel 0-day exploited for months - helpnetsecurity.com/2026/05/03/wee… - #WeekInReview #Cybersecurity #CybersecurityNews

welivesecurity.com/en/videos/mont… Warnings about impersonation scams targeting help desks and Iranian hackers impacting key U.S. sectors, plus the most dangerous scams of 2025. #WeLiveSecurity #ESET #CyberSecurityNews
⚠️ Multiple Wireshark Vulnerabilities Allow Arbitrary Code Execution via Malformed Packets | Source: gbhackers.com/multiple-wires… #cybersecuritynews
Microsoft Emergency NET 10.0.7 Update to Patch Elevation of Privilege Vulnerability Source: cybersecuritynews.com/emergency-net-... Microsoft has issued an emergency out-of-band (OOB) security update for NET 10, releasing version 10.0.7 on may 1, 2026, #cybersecuritynews
CrowdStrike LogScale Vulnerability Allows Remote Attackers to Read Files from Server X Source: cybersecuritynews.com/crowdstrike- IO... An urgent security advisory for a critical unauthenticated path-traversal vulnerability (CVE-2026-40050) affecting its LogScale platform #cybersecuritynews
welivesecurity.com/en/scams/data-… Neglecting a genuine breach alert poses risks, but falling for a fake one can be even more dangerous. Don't react on autopilot! ⚠️ #databreach #DataProtection #CyberSecurityNews
New infosec products of the month: April 2026 - helpnetsecurity.com/2026/05/01/new… - @AxoniusInc @Broadcom @globalsign @intruder_io @secureframe @Siemens @VirtueAI_co #Cybersecurity #CybersecurityNews

🛠️ Claude Security Enters Public Beta for Enterprise Customers | gbhackers.com/claude-securit… #cybersecuritynews
⚠️ Windows Remote Desktop Leaves Image Fragments Attackers Can Stitch Into Screenshots Source: cybersecuritynews.com/windows-remote… @The_Cyber_News Whenever someone uses Windows Remote Desktop, the operating system quietly saves visual fragments of the active session. #cybersecuritynews
⚠️Μετά τη στοχοποίηση πολιτικών στη Γερμανία, το Signal Technology Foundation ανακοινώνει αλλαγές για την προστασία των χρηστών από εξελιγμένες τακτικές κοινωνικής μηχανικής και υποκλοπής κωδικών. #Signal #CyberSecurityNews #PhishingAwareness gr.pcmag.com/security/51780…
🚨 SonicWall SonicOS Flaw Lets Attackers Bypass Access Controls and Crash Firewalls | Source: gbhackers.com/sonicwall-soni… #cybersecuritynews

⚠️ Linux Kernel 0-Day “Copy Fail” Grants Root Access Across Major Distros Since 2017 | Source: gbhackers.com/linux-kernel-0… #cybersecuritynews
⚠️Μετά από επίθεση σε εργαλείο τρίτου παρόχου, οι χάκερς απέκτησαν πρόσβαση σε μεταδεδομένα και διευθύνσεις email εκατομμυρίων χρηστών, απειλώντας με δημοσιοποίηση των στοιχείων την Πέμπτη. #Vimeo #ShinyHunters #CyberSecurityNews gr.pcmag.com/security/51774…
⚠️ Vimeo Confirms Data Breach After Hackers Access User Database | Source: gbhackers.com/vimeo-confirms… #cybersecuritynews

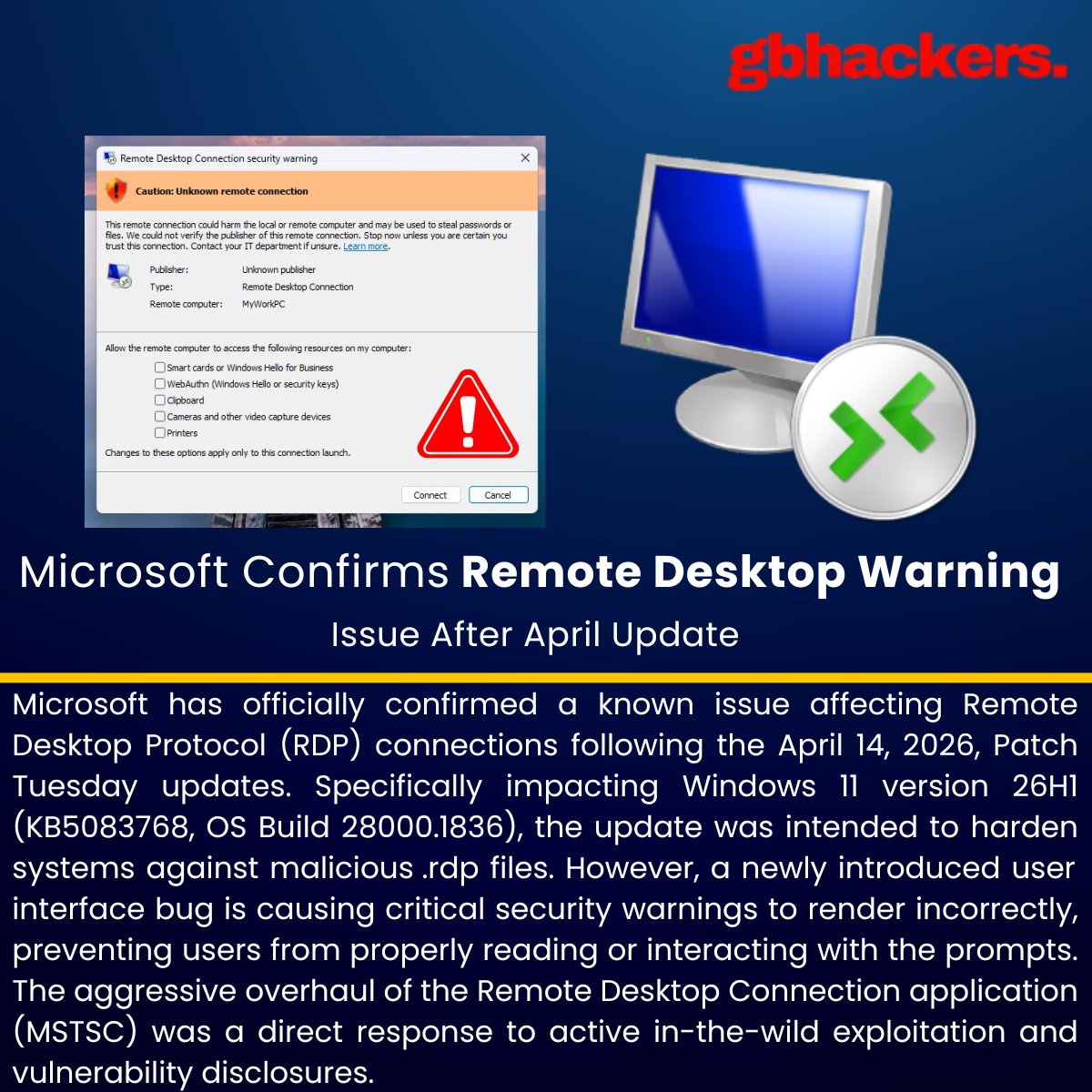
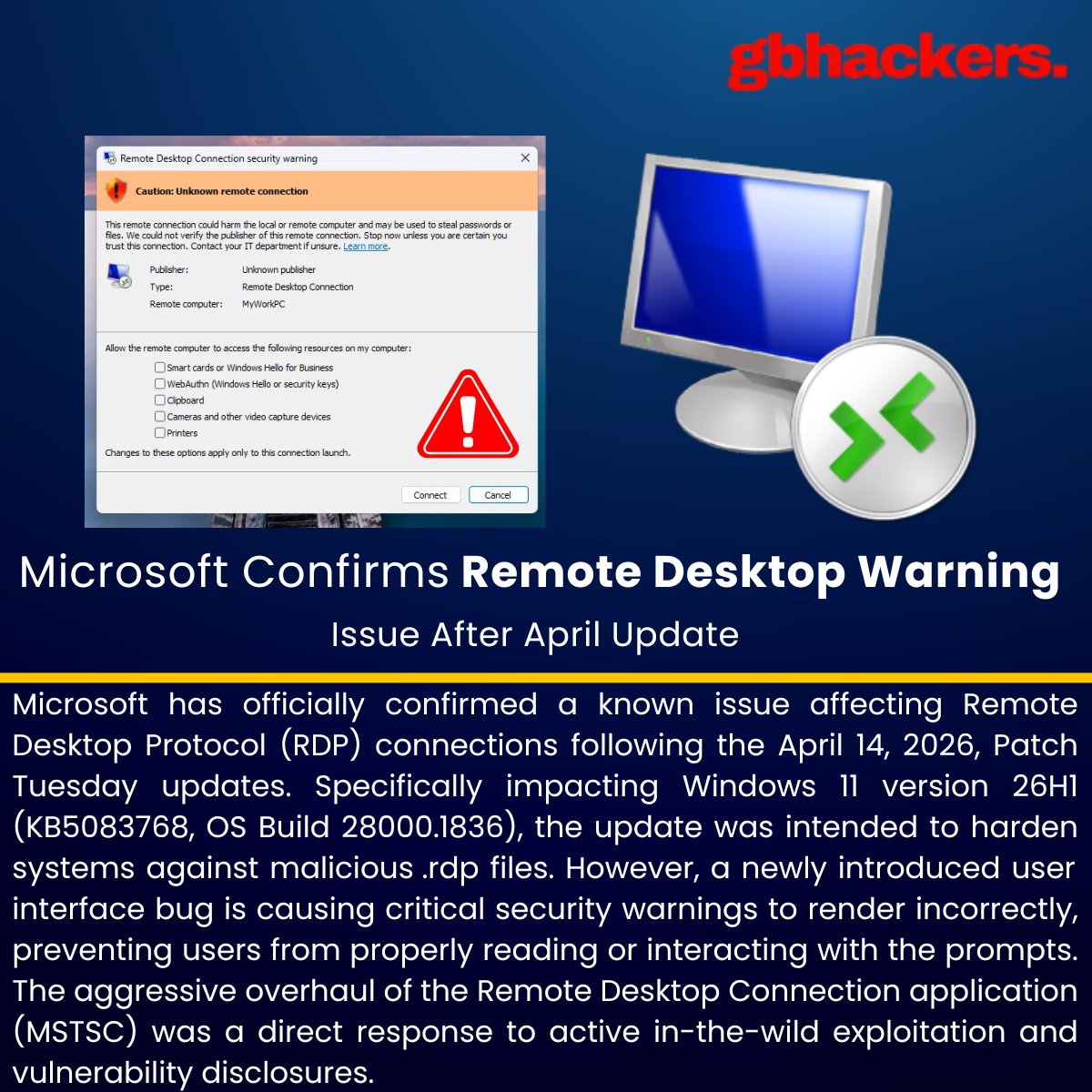
⚠️ Microsoft Confirms Remote Desktop Warning Issue After April Update | Source: gbhackers.com/microsoft-conf… #cybersecuritynews
🚨 GitHub.com and Enterprise Server Vulnerability Allows Remote Code Execution | Source: gbhackers.com/github-com-and… #cybersecuritynews

Thank you to the 12 sponsors who made the 2026 CDR research report possible. Platinum: @Google, @ISC2ISC2, @rubrikInc, @SentinelOne Gold: @ColorTokensInc @Hacker0x01 , @Veracode, @Xbow Silver: @Cynet_Security, @keepersecurity, Mitiga, @wallarm #CDR2026 #cybersecuritynews

🚨 Checkmarx Confirms Security Incident Involving GitHub Repository Exposure | Source: gbhackers.com/checkmarx-conf… #cybersecuritynews
🚨 Notepad++ Vulnerability Lets Attackers Crash App and Expose Memory Data | Source: gbhackers.com/notepad-vulner… #cybersecuritynews
#ICYMI Microsoft has issued an emergency out-of-band (OOB) security update for .NET 10, releasing version 10.0.7 on April 21, 2026, to address a critical elevation of privilege vulnerability . Source: cybersecuritynews.com/emergency-net-… @The_Cyber_News #cybersecuritynews
🚨 GitHub.com and Enterprise Server Vulnerability Allows Remote Code Execution | Source: gbhackers.com/github-com-and… #cybersecuritynews

☠️ Suspicious Microsoft Store App Vibing.exe Allegedly Harvests Screens and Audio | Source: gbhackers.com/suspicious-mic… #cybersecuritynews

South Korea’s tax agency accidentally exposed a crypto wallet seed phrase in press photos. Result: ~$4.8M in seized PRTG tokens drained within hours. A stark reminder: private key exposure = total loss. #CryptoSecurity #Blockchain #CybersecurityNews

⚠️ Vimeo Confirms Data Breach After Hackers Access User Database | Source: gbhackers.com/vimeo-confirms… #cybersecuritynews

🚨 Checkmarx Confirms Security Incident Involving GitHub Repository Exposure | Source: gbhackers.com/checkmarx-conf… #cybersecuritynews
⚠️ Cisco Webex Vulnerability Allows User Impersonation Attacks | Source: gbhackers.com/cisco-webex-vu… #cybersecuritynews

🚨 iTerm2 Flaw Turns SSH Escape Sequences Into Arbitrary Code Execution | Source: gbhackers.com/iterm2-flaw-tu… #cybersecuritynews

🚨 Notepad++ Vulnerability Lets Attackers Crash App and Expose Memory Data | Source: gbhackers.com/notepad-vulner… #cybersecuritynews
⚠️ Microsoft Confirms Remote Desktop Warning Issue After April Update | Source: gbhackers.com/microsoft-conf… #cybersecuritynews
Week in review: High-severity LPE vulnerability in the Linux kernel, cPanel 0-day exploited for months - helpnetsecurity.com/2026/05/03/wee… - #WeekInReview #Cybersecurity #CybersecurityNews

🕵♀️ NSA Confirms Use of Anthropic’s Mythos Despite Pentagon Blacklist | Source: gbhackers.com/nsa-confirms-u… #cybersecuritynews

🔴 Python Vulnerability Enables Out-of-Bounds Write on Windows | Source: gbhackers.com/python-vulnera… #cybersecuritynews

🔓 Hackers Exploit Ollama Model Uploads to Leak Server Data | Source: gbhackers.com/hackers-exploi… #cybersecuritynews

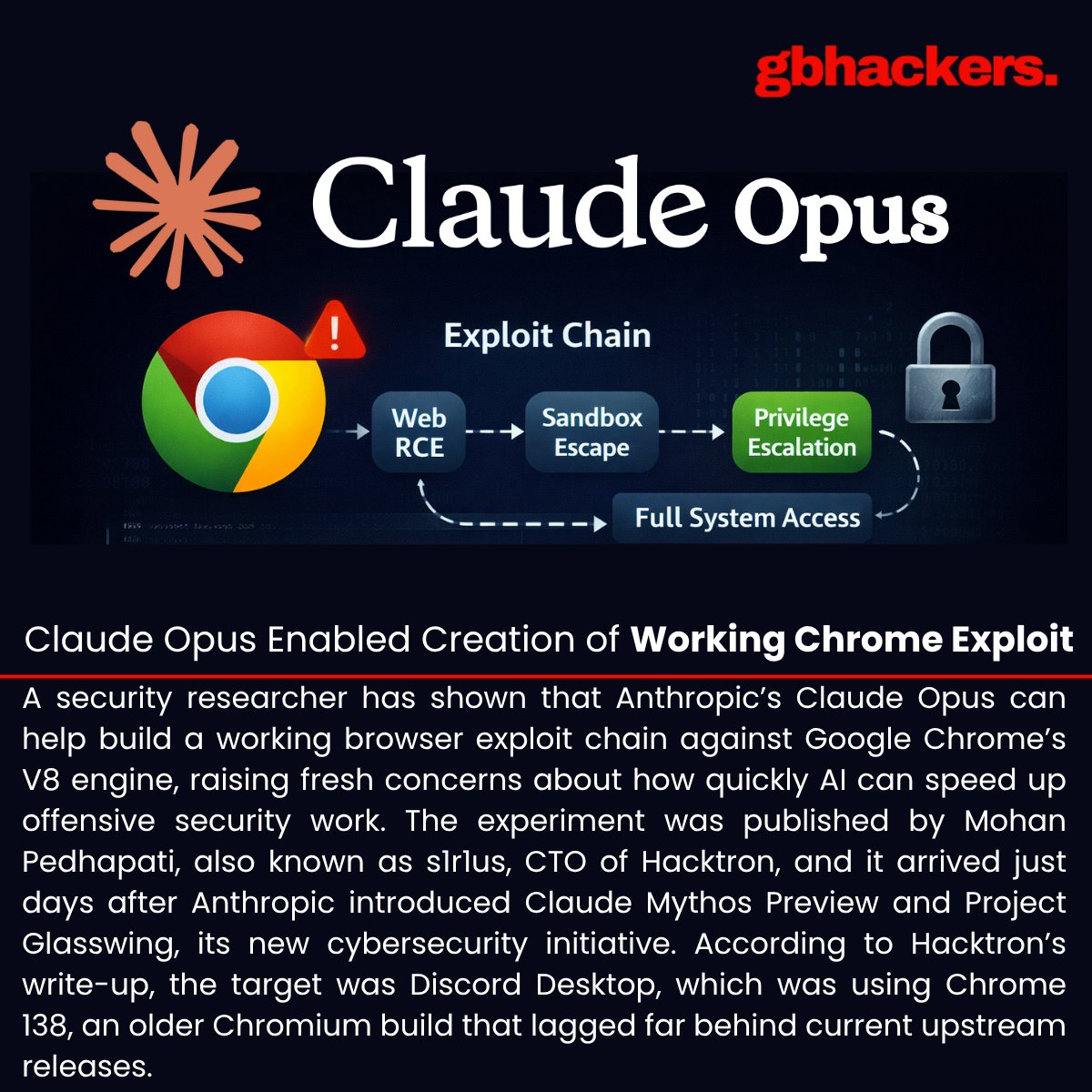
🚨 Researcher Claims Claude Opus Enabled Creation of Working Chrome Exploit | Source: gbhackers.com/claude-opus-en… #cybersecuritynews
When a Friend Request Becomes a Cyber Threat: APT37’s New Facebook-Based Attack Trusted connection or hidden threat? When social media becomes the entry point for cyber espionage. #facebook #cybersecuritynews Full Story 👉 cybersecurity88.com/news/north-kor…

🚨 Bitwarden CLI Compromised After Malicious GitHub Actions Workflow | Source: gbhackers.com/bitwarden-cli-… #cybersecuritynews

Fraudsters use AI to create 'pixel-perfect' fake shopping sites — Reports Dr. Tim Sandle. — #Hacker #CyberSecurityNews digitaljournal.com/tech-science/f…

⚠️ Claude Opus 4.6-Powered AI Coding Agent Wipes Production Database in 9 Seconds | Source: gbhackers.com/claude-opus-4-… #cybersecuritynews
🚨 Exclusive Anthropic Cyber Tool Mythos Accessed by Unapproved Actors | Source: gbhackers.com/exclusive-anth… #cybersecuritynews
સાયબર સેન્ટર ઓફ એક્સેલન્સ, ગુજરાત દ્વારા રૂ.3,90,30,047/- ફ્રોડના ગુનામાં શેર બજારમાં જંગી નફો કમાવાની લાલચ આપી લોકોને ફસાવી છેતરપપિંડી કરનાર આરોપીઓને ઝડપી પાડેલ છે. #CybersecurityNews @sanghaviharsh @GujaratPolice @Cyberdost @vivekpbheda

Something went wrong.
Something went wrong.
United States Trends
- 1. #MiamiGP N/A
- 2. Liverpool N/A
- 3. Ben Rice N/A
- 4. Carrick N/A
- 5. Joe Ryan N/A
- 6. Rolling Stone N/A
- 7. Slot N/A
- 8. ALL RISE N/A
- 9. Leclerc N/A
- 10. #COYS N/A
- 11. Chris Paddack N/A
- 12. Manchester United N/A
- 13. Amad N/A
- 14. Villa N/A
- 15. Zverev N/A
- 16. #7_As_One_Always N/A
- 17. Amorim N/A
- 18. De Zerbi N/A
- 19. Sinner N/A
- 20. #ENGENEs_Demand_Clarity N/A