#devicecontrol 검색 결과
Spray-On Smart Skin that Interprets Commands Through Hand Movements #AI #communication #devicecontrol #disabilities #gestures #handmovements #healthmonitoring #smartskin #wearabletechnology neurohub.ai/spray-on-smart…
Meet sponsor @cososys👋 with a portfolio of security products and features for #devicecontrol, #datalossprevention, and #eDiscovery for Windows, #macOS and Linux. Come visit them 22-24th May. Get tickets now macad.uk/tickets

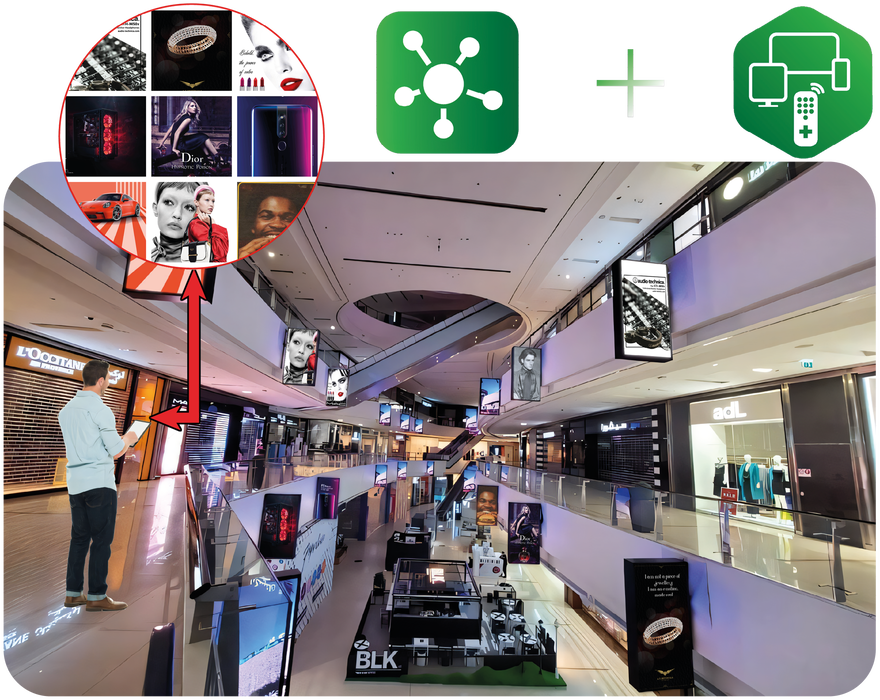
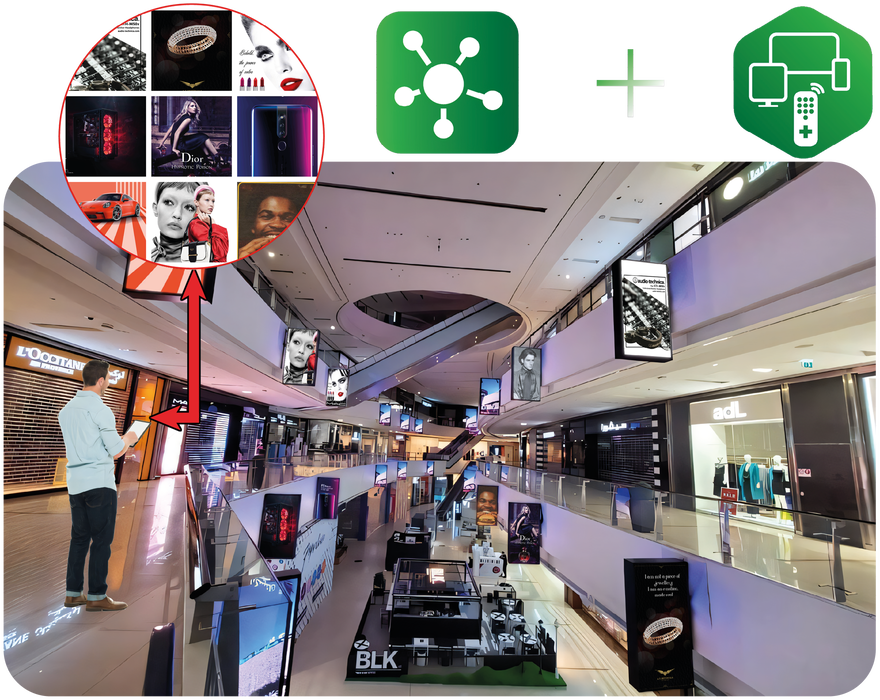
Our latest lineup of commercial displays, when combined with our powerful Command and Control software, makes managing a business or commercial space with multiple screens a breeze. #SystemAdmin #RemoteManagement #DeviceControl

Remotely manage and control all of your Interactive Screens using Command & Control. Simply open the app, login to the system account, and see information about all connected devices. #SystemAdmin #RemoteManagement #DeviceControl FIND OUT MORE: discoveribt.com/commandandcont…

Heute ist es soweit: Unser Webinar zu #SecurityControls findet statt. Im Fokus stehen effektive Sicherheitsmaßnahmen zum Schutz Ihrer Systeme im Kontext von #NIS2. Letzte Chance nutzen und jetzt anmelden! ⬇️ #DeviceControl #ApplicationControl eu1.hubs.ly/H08SKhP0
Try #DriveLock for 30 days for free and test any application scenario that is important for your company! Experience our cloud-based endpoint solution incl. #ApplicationControl, #DeviceControl, #BitLockerManagement, #Security Awareness, and much more. ➡️ hubs.li/Q023nj_l0

Most data breaches don’t start with hacks; they begin with access. With AppTec360, USB ports and peripherals work only when you allow them. Control the entry points. Protect what matters. #EndpointSecurity #DeviceControl #USBSecurity #UnifiedEndpointManagement #ITSecurity

Apple vs. Epic: Why YOU Should Care About Device Control! #DeviceControl #EpicGamesVsApple #AppleEcosystem #TechFreedom #ConsumerRights #DigitalRights #BigTech #AppStoreDebate #TechNews #InnovationDebate
Are your employees aware of the risks associated with transferring information stored on an external device to a computer? With #DriveLock #DeviceControl you can protect all your data and devices and control the transfer of data to and from your systems. eu1.hubs.ly/H06Kwl30

DriveLock HYPERSECURE Platform erfüllt #NIS2, sichert Endpoints und verhindert Cyberangriffe. Im Webinar am Donnerstag zeigten wir, wie #DeviceControl. #ApplicationControl und #SecurityAwareness die Sicherheit Ihres Unternehmens stärken. Jetzt anmelden! eu1.hubs.ly/H088xPd0

This article discusses two simple solutions to control the number one source of information leakage... copying data from Windows endpoints to USB storage devices: bit.ly/3Xu4QIF #DefenderforEndpoint #USB #DeviceControl #Microsoft365

Constant screen use can be exhausting. Naqi provides a hands-free, screen-free way to control devices through micro facial gestures and subtle head movements. Discover the future of device control at naqilogix.com. #NaqiLogix #DeviceControl #HandsFree #ScreenFree
Try #DriveLock free for 30 days in your cloud testing environment for any application scenario that matters to your business! Experience our cloud-based endpoint solution including #ApplicationControl, #DeviceControl, #BitLockerManagement, and more. ⬇️ eu1.hubs.ly/H07JrwZ0
drivelock.com
30 Days Free Trail
Test DriveLock's cloud-based endpoint security solutions 30 days free of charge. Convince yourself! Fill out the form and get started ➤
In today's digital age, ensuring comprehensive security measures throughout an organisation is critical for safeguarding valuable assets from cyber threats. Speak to our qualified professional team today: 💻 itrm.co.uk/contact-us #DeviceControl #CyberSecurity #CyberSafety

Using Device Control in Defender for Endpoint to Block USB Drives: bit.ly/3Xu4QIF @jamesyip #DefenderforEndpoint #USB #DeviceControl #Microsoft365

#Cybersecurity is not just an issue for us, but an obligation, especially when it comes to sensitive health data. DriveLock offers you proactive protection. From #ApplicationControl and #DeviceControl to encryption and secure authentication. Learn more: ⤵️ eu1.hubs.ly/H0b5w3b0

Copying data from Windows endpoints to USB storage devices is one of the largest sources of data leakage. In this article, we discuss two simple solutions to avoid this problem: bit.ly/3Xu4QIF #DefenderforEndpoint #USB #DeviceControl #Microsoft365

One dashboard. Every device. Full control. The Devices Page in Prodexo AI lets admins monitor and manage every registered device. 🔐 This is how smart organizations stay in control. #ProdexoAI #DeviceControl #AdminTools #EnterpriseSecurity #ProductivityManagement
@WithSecure controls apps and devices. @Netsoftmate blocks risks instantly. • Restrict risky apps • Block unsafe USBs • Reduce attack paths • Enforce access rules 🔒 Control every device Visit: netsoftmate.com #WithSecure #Netsoftmate #DeviceControl #AppSecurity
Most data breaches don’t start with hacks; they begin with access. With AppTec360, USB ports and peripherals work only when you allow them. Control the entry points. Protect what matters. #EndpointSecurity #DeviceControl #USBSecurity #UnifiedEndpointManagement #ITSecurity

🔍 APIs shape how your AV/IT ecosystem performs. Our latest research reveals why relying only on cloud APIs can limit control — and how device-level APIs improve security, data access, and alignment with business KPIs. 📥 Download: ow.ly/qNRL50XtrN5 #API #DeviceControl
📢 Our #connected devices aren't just gadgets, they're essential tools in our #tech-filled world. ⠀ But do you truly own them? Corporations often hold the power of their devices. ⠀ Regain #devicecontrol and learn why it matters. Find out more 👉🏼 thefastmode.com/expert-opinion…



Enterprises and customers, it's time to reclaim control over your #connected devices! ⠀ Our CEO Carsten Rhod Gregersen discusses the importance of customization in preserving your independence. ⠀ Find out more 🌐 iot-now.com/2023/09/06/135… ⠀ #DeviceControl #TechSolutions

This article discusses two simple solutions to control the number one source of information leakage... copying data from Windows endpoints to USB storage devices: bit.ly/3Xu4QIF #DefenderforEndpoint #USB #DeviceControl #Microsoft365

I Need For Solution immediately Why 2 Continue #MYMobile #DeviceControl in TVS Credit My Loan Account Is Clear Now #SoPoorResponse #SoWorstExperience #SoBadServices #TVSCREDIT

Using Device Control in Defender for Endpoint to Block USB Drives: bit.ly/3Xu4QIF @jamesyip #DefenderforEndpoint #USB #DeviceControl #Microsoft365

The Latest Intel on Wipers Learn more : zurl.co/Wcb3 #Antivirus #EndpointProtection #emailSecurity #CyberSecurity #DeviceControl#EndpointSecurity#FraudPrevention #FortinetPartner #ThreatManagement #MalwareProtection

In today's digital age, ensuring comprehensive security measures throughout an organisation is critical for safeguarding valuable assets from cyber threats. Speak to our qualified professional team today: 💻 itrm.co.uk/contact-us #DeviceControl #CyberSecurity #CyberSafety

Our latest lineup of commercial displays, when combined with our powerful Command and Control software, makes managing a business or commercial space with multiple screens a breeze. #SystemAdmin #RemoteManagement #DeviceControl

Take control of your network! ARKEN's sensors manage computing devices across Mac, Windows, and Linux, stopping unauthorized software and USB devices in their tracks. #CyberSecurity #DeviceControl #TechInnovation

Remote control functionality 𝐌𝐨𝐫𝐞 𝐬𝐜𝐢𝐞𝐧𝐜𝐞 𝐚𝐫𝐭𝐢𝐜𝐥𝐞𝐬 𝐟𝐫𝐨𝐦: 👇 wowsciencefacts.com #wirelesscontrol #remoteoperation #devicecontrol #transmitter #receiver #infrared #radiofrequency #codedsignals #decodedcommands #science #scienceexperiment #sciencehumor

Simplify control, amplify convenience. Our IR Blaster Wifi Universal Remote is your gateway to seamless device management. Upgrade your home automation game and enjoy the ease of connected living. #irblaster #devicecontrol #devicemanagement #universalremote #smartirremote

Revolutionize your smart device product line with IoT! At TAFF, we empower businesses to harness the true potential of IoT. #IOT #Devicecontrol #ITservices #ITsolutions #TAFF #Tampa Tap to explore: bit.ly/3ZV6S5Z




Most data breaches don’t start with hacks; they begin with access. With AppTec360, USB ports and peripherals work only when you allow them. Control the entry points. Protect what matters. #EndpointSecurity #DeviceControl #USBSecurity #UnifiedEndpointManagement #ITSecurity

Try #DriveLock for 30 days for free and test any application scenario that is important for your company! Experience our cloud-based endpoint solution incl. #ApplicationControl, #DeviceControl, #BitLockerManagement, #Security Awareness, and much more. ➡️ hubs.li/Q023nj_l0

Control your AC, TV, Set Top Boxes, and more with ease using our Atom8’s IR Blaster Wifi Universal Remote. Compatible with Amazon Alexa and Google Home for seamless control. #irblaster #devicecontrol #devicemanagement #universalremote #smartirremote #smarthomedevices

Stay protected with our advanced endpoint solutions! The features provided include #Antimalware, #Devicecontrol, #Webcontrol, and #Encryption. We help to quickly detect threats and respond to keep your data secure. Get in touch today @0746727307 / arieltech.co.ke.

Prevent your devices from receiving unauthorized or malicious updates by blocking signals with a Faraday Pouch. #DeviceControl #FaradayPouches tinyurl.com/62pw4fna

Discover how the ViFlow App simplifies data access and device management. Streamline your workflow today! #ViFlow #DataManagement #DeviceControl #VisionWorldTech #VWTPL

Copying data from Windows endpoints to USB storage devices is one of the largest sources of data leakage. In this article, we discuss two simple solutions to avoid this problem: bit.ly/3Xu4QIF #DefenderforEndpoint #USB #DeviceControl #Microsoft365

Remotely manage and control all of your Interactive Screens using Command & Control. Simply open the app, login to the system account, and see information about all connected devices. #SystemAdmin #RemoteManagement #DeviceControl FIND OUT MORE: discoveribt.com/commandandcont…

Something went wrong.
Something went wrong.
United States Trends
- 1. #STLCards N/A
- 2. Mike Trout N/A
- 3. Kevin McGonigle N/A
- 4. #OpeningDay N/A
- 5. Druski N/A
- 6. Cruz N/A
- 7. Roman Anthony N/A
- 8. Skenes N/A
- 9. #DirtyWater N/A
- 10. JJ Wetherholt N/A
- 11. Phillies N/A
- 12. Red Sox N/A
- 13. Duran N/A
- 14. Backhus N/A
- 15. Mets N/A
- 16. Sal Stewart N/A
- 17. Alec Bohm N/A
- 18. #DNMW N/A
- 19. Carson Benge N/A
- 20. Cubs N/A