#itsecurity search results
Healthy crops start with great soil; resilient IT starts with strong foundations. Do you use a soil analysis kit—or a cybersecurity audit—to spot risks before they sprout? Share your best practices for staying one step ahead! #SoilHealth #ITSecurity

What is your experience with IT Security Audits regarding Employee Awareness within your organization? What did the auditor ask for? hissenit.com/en/academy/ #itsecurity #security #ciso #awareness #itsec #iso27001

Reducing IT friction doesn't mean more work. Consolidate tools with one trusted partner. Your team stays productive, minus the headaches. Let us simplify IT so you can grow. Book a free consultation celeretech.com/book/ #CelereTech #BusinesContinuity #ITSecurity

Regulatory compliance isn’t something businesses can afford to think about only during an audit. Being audit-ready means less stress, fewer risks, and more confidence in your technology environment. #RegulatoryCompliance #ManagedIT #ITSecurity

One reused password → fake invoice → lost client. Passwords alone aren't enough for your SME. Add a second check. Full system: IT Security for SMEs udemy.com/course/it-secu… #SMESecurity #ITSecurity
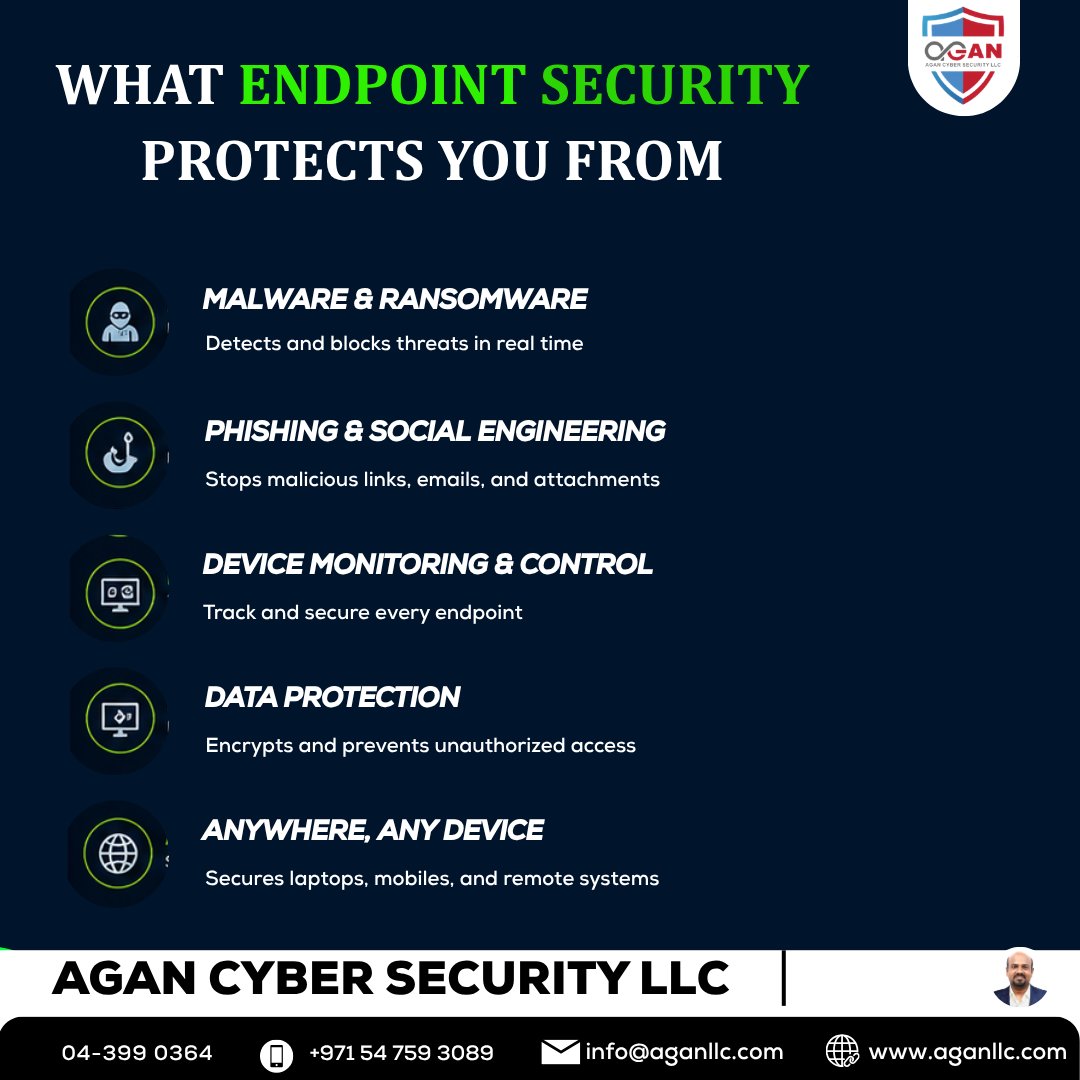
Cybersecurity isn’t optional, it’s critical for business continuity. From endpoint protection to backup, testing & compliance—Tarika Group helps keep your systems secure. 🔗 tarikagroup.com/services/endpo… #CyberSecurity #EndpointSecurity #ITSecurity #DataProtection #TarikaGroup




Gestohlene Zugangsdaten werden zum zentralen Risiko für Unternehmen – warum Passwörter allein nicht mehr ausreichen und MFA an Bedeutung gewinnt. #CyberSecurity #ITSecurity #MFA #Digitalisierung 👉 shorturl.at/8IvI2

The "Moonlighting" trend is more than just a burnout risk—it’s a #ITSecurity ticking time bomb. Discover why discreet #BackgroundVerification is the new strategic must-have. Read more: himadi.com/moonlighting-d…
Managing system access is critical to cybersecurity. Safebox Technologies secures your business with Identity & Access Control, from role-based access to MFA and privileged access management. Right people. Right access. Right time. #SafeboxTechnology #CyberSecurity #ITSecurity

See how Hire2Retire's Access Request feature gives your team a governed, automated way to request, approve, and revoke access. Book a demo with our experts today: bit.ly/42hoWst #Hire2Retire #IdentityManagement #ITSecurity #AccessManagement
Cybersecurity isn’t optional, it’s critical for business continuity. From endpoint protection to backup, testing & compliance—Tarika Group helps keep your systems secure. 🔗 tarikagroup.com/services/endpo… #CyberSecurity #EndpointSecurity #ITSecurity #DataProtection #TarikaGroup




Regulatory compliance isn’t something businesses can afford to think about only during an audit. Being audit-ready means less stress, fewer risks, and more confidence in your technology environment. #RegulatoryCompliance #ManagedIT #ITSecurity

Efficiency ≠ security 🚀 Before your team installs that next “productivity” extension, run a 5-layer security check. Vet micro-SaaS tools. Keep your data where it belongs! 🔐 norcotech.com/blog/are-your-… #CyberSecurity #SmallBusiness #ITSecurity
🚨 What is ransomware? It locks your business data & demands payment. Learn to stay protected. 🔐 👉 aganllc.com/blog/what-is-r… 📞 +971 54 759 3089 #Ransomware #CyberSecurity #ITSecurity #DataProtection
Healthy crops start with great soil; resilient IT starts with strong foundations. Do you use a soil analysis kit—or a cybersecurity audit—to spot risks before they sprout? Share your best practices for staying one step ahead! #SoilHealth #ITSecurity

اختراق واحد. مش بيقف عند الدخول بعد أول Access النشاط بيتحرك جوه الشبكة ويوصل لأنظمة أكتر حساسية من نقطة بسيطة → تأثير واسع (وده بيحصل أسرع مما تتخيل) غياب Segmentation = قابلية أعلى للانتشار The risk isn’t entry,it’s spread #Techifay #CyberSecurity #ITSecurity #الأمن_السيبراني


The "Moonlighting" trend is more than just a burnout risk—it’s a #ITSecurity ticking time bomb. Discover why discreet #BackgroundVerification is the new strategic must-have. Read more: himadi.com/moonlighting-d…
𝗙𝗶𝗻𝗱 𝗼𝘂𝘁 𝗺𝗼𝗿𝗲: tinyurl.com/4cr9rsbb Audits don’t fail because we lack controls. They fail because we can’t prove them. #cybersecurity #infosec #itsecurity

What is your experience with IT Security Audits regarding Employee Awareness within your organization? What did the auditor ask for? hissenit.com/en/academy/ #itsecurity #security #ciso #awareness #itsec #iso27001

One reused password → fake invoice → lost client. Passwords alone aren't enough for your SME. Add a second check. Full system: IT Security for SMEs udemy.com/course/it-secu… #SMESecurity #ITSecurity
When the cloud goes dark, the Enterprise Browser shines brightest. Read Island's full breakdown here: island.io/blog/when-the-… #BusinessContinuity #EnterpriseBrowser #ITSecurity
Security tools alone aren’t enough. Without strategy and visibility, gaps still exist. #CyberSecurity #ITSecurity beamsecurity.com
Most companies don’t fail CMMC because of tech… They fail because of missing policies, training, and documentation. cmitsolutions.com/blog/cmmc-comp… #Compliance #ITSecurity

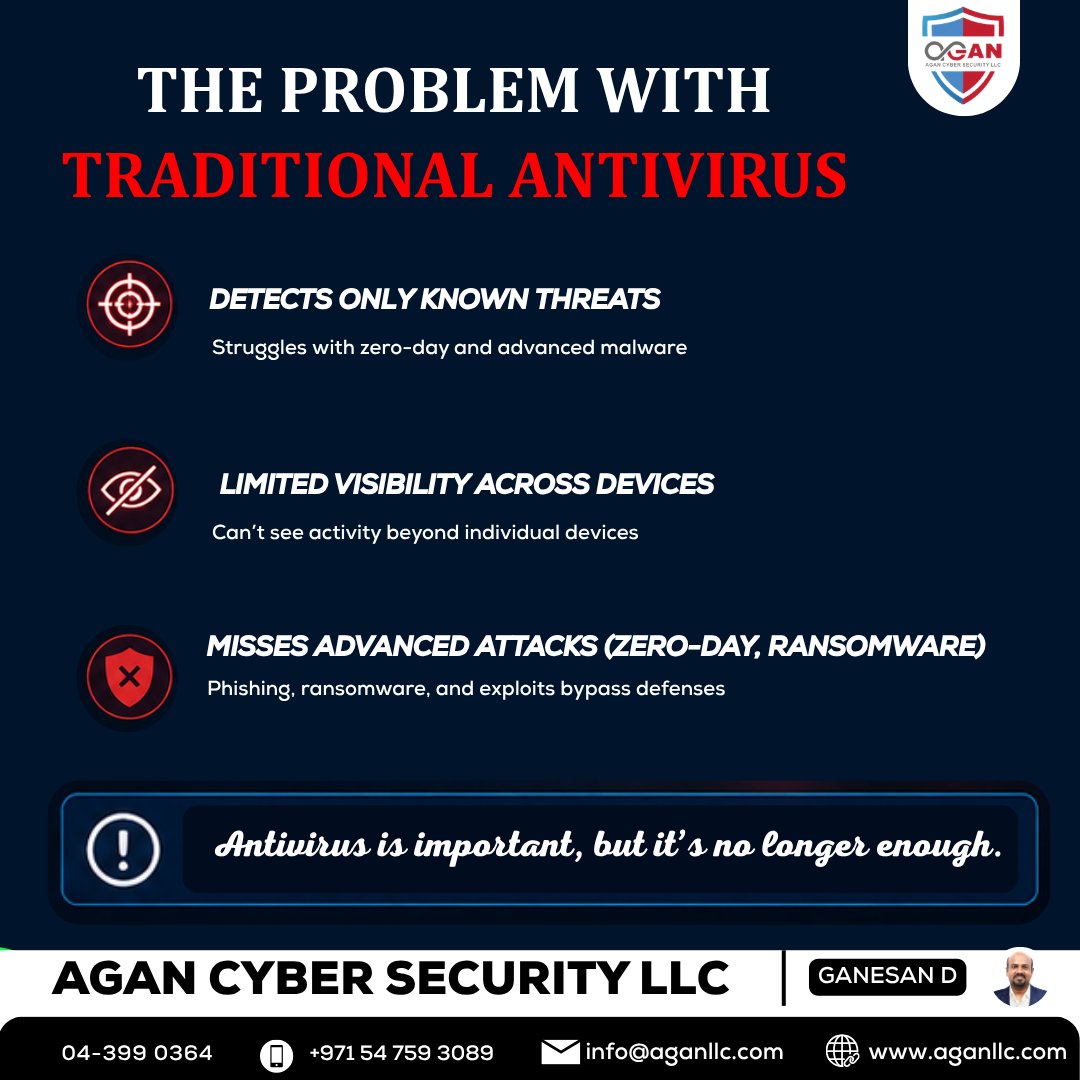
🚨 Antivirus isn’t enough—endpoint security protects all devices from advanced threats & ransomware. 🔐 👉 aganllc.com/blog/endpoint-… 📞 +971 54 759 3089 #EndpointSecurity #CyberSecurity #ITSecurity #DataProtection


Reducing IT friction doesn't mean more work. Consolidate tools with one trusted partner. Your team stays productive, minus the headaches. Let us simplify IT so you can grow. Book a free consultation celeretech.com/book/ #CelereTech #BusinesContinuity #ITSecurity

Das raffinierte an diesen genialen Hacks der letzten Zeit, ich denke da an #xz sowie #CopyFail, ist, dass beide auf unterschiedliche Weise forensisch nicht nachweisbar sind: xz nicht im Quelltext, CopyFail weder während, noch nach dem Attack. #itsecurity linux-magazin.de/news/kritische…
Managing system access is critical to cybersecurity. Safebox Technologies secures your business with Identity & Access Control, from role-based access to MFA and privileged access management. Right people. Right access. Right time. #SafeboxTechnology #CyberSecurity #ITSecurity

Gestohlene Zugangsdaten werden zum zentralen Risiko für Unternehmen – warum Passwörter allein nicht mehr ausreichen und MFA an Bedeutung gewinnt. #CyberSecurity #ITSecurity #MFA #Digitalisierung 👉 shorturl.at/8IvI2

#ITSecurity ConsentFix v3 Automates OAuth Abuse to Bypass MFA and Hijack Azure Accounts itsecuritynews.info/consentfix-v3-…
itsecuritynews.info
ConsentFix v3 Automates OAuth Abuse to Bypass MFA and Hijack Azure Accounts - IT Security News
What happened A third iteration of the ConsentFix attack technique has been circulating on hacker forums, introducing automation and scalability to a method that abuses Microsoft Azure’s OAuth2...
Cybersecurity isn’t optional, it’s critical for business continuity. From endpoint protection to backup, testing & compliance—Tarika Group helps keep your systems secure. 🔗 tarikagroup.com/services/endpo… #CyberSecurity #EndpointSecurity #ITSecurity #DataProtection #TarikaGroup




𝗙𝗶𝗻𝗱 𝗼𝘂𝘁 𝗺𝗼𝗿𝗲: tinyurl.com/4cr9rsbb Audits don’t fail because we lack controls. They fail because we can’t prove them. #cybersecurity #infosec #itsecurity

Dashboards don’t stop breaches. Decisions do. With our AI-powered plain-English functionality you can ask a question, understand the risk, and fix it instantly. Find out more: 🔗 tinyurl.com/8veefkh2 #cybersecurity #infosec #itsecurity

Volumetrické DDoS útoky patří mezi největší hrozby současnosti v internetovém světě. Zatěžují infrastrukturu, způsobují výpadky a mohou znamenat významné finanční i reputační ztráty. #ITSecurity #Kyberbezpecnost #DDoS #WEDOS

Getting started with Azure Networking services ⏱️ 13.4 hours ⭐ 4.33 👥 33,603 🔄 Mar 2026 💰 $17.99 → 100% OFF comidoc.com/udemy/azure-ne… #Azure #CloudNetwork #ITSecurity #udemy

Anzeige • Mission: Sicherer Arbeitsplatz – beim #ITSecurity Escape Game von ADLON. Kein PowerPoint. Kein Tool-Marketing. Entscheiden unter Zeitdruck im neuen Live-Format. Die Plätze sind limitiert. Jetzt anmelden 👉adlon.de/event-escape-g… #CyberSecurity #CyberResilienz #ADLONIT

🔗👉🏻 tinyurl.com/4wpzxj2b We’re looking for a 𝗖𝘂𝘀𝘁𝗼𝗺𝗲𝗿 𝗦𝘂𝗰𝗰𝗲𝘀𝘀 𝗘𝗻𝗴𝗶𝗻𝗲𝗲𝗿 to be the voice of our customers & prospects, + have a major impact on @TrustleSecurity's future mission. #cybersecurity #infosec #itsecurity #secuirtyjobs

Prüfe jetzt den Härtungsstatus deiner Systeme, bevor es Angreifer für dich tun! 👉 fb-pro.com/status-systemh… #Systemhärtung #ITSecurity #WindowsHardening
“It’s easy to set up and use, and we can easily enable 2FA…” Learn how Access Server strengthened security for a software services team. openv.pn/4cQMEli #Cybersecurity #ITSecurity #OpenVPN

Sichere jetzt deine Systeme mit lückenloser Audit-Vorbereitung. 👉 systemhardening.webinargeek.com/hardening-insi… #Hardening #Audit #ITSecurity

Remote-first working complicates identity governance. 🔗 tinyurl.com/hkzf9sz3 Fix it with human & non-human ownership mapping, detection of unused high-risk access, & automated revocation. #cybersecurity #infosec #itsecurity

In their own words: "𝗔 𝗿𝗲𝗽𝗲𝗮𝘁𝗮𝗯𝗹𝗲 𝗰𝗵𝗲𝗰𝗸 𝗼𝗳 𝗻𝗲𝗰𝗲𝘀𝘀𝗶𝘁𝘆, 𝗿𝗲𝘃𝗶𝗲𝘄, 𝗿𝗲𝘃𝗼𝗰𝗮𝘁𝗶𝗼𝗻, 𝗮𝗻𝗱 𝗲𝘅𝗽𝗶𝗿𝗮𝘁𝗶𝗼𝗻." 🔗 tinyurl.com/hybh24nb #cybersecurity #infosec #itsecurity

لذوى الهمم تحت الاشراف أوقف المخترقين! الحماية بأسلوب مبسط ⏱️ 57 mins 👥 69 🔄 Jul 2025 💰 FREE comidoc.com/udemy/arabic-l… #CyberSecurity #KidsSafety #ITSecurity #udemy

🔗 tinyurl.com/mtt5b7cx CISOs don’t struggle to justify spend 𝘢𝘧𝘵𝘦𝘳 a breach. The challenge is justifying it 𝘣𝘦𝘧𝘰𝘳𝘦 one happens. #cybersecurity #aisecurity #itsecurity

How did fake IT workers beat hiring checks at major companies? The answer should worry every HR leader. And it’s happening more often than you think: hrexecutive.com/how-north-kore… #ITSecurity #HiringChallenges

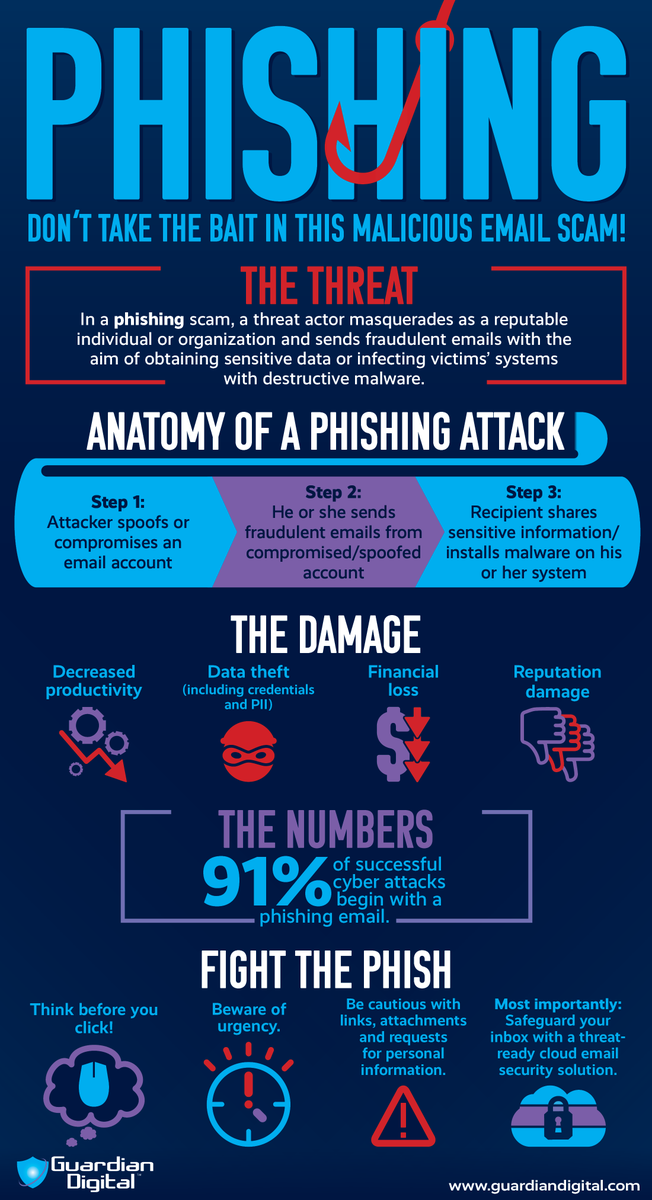
🤯 Can training stop every spear phishing attack? No—but it can make employees pause before clicking. Learn the tactics attackers rely on: ⚠️ #ITSecurity #AntiPhishing
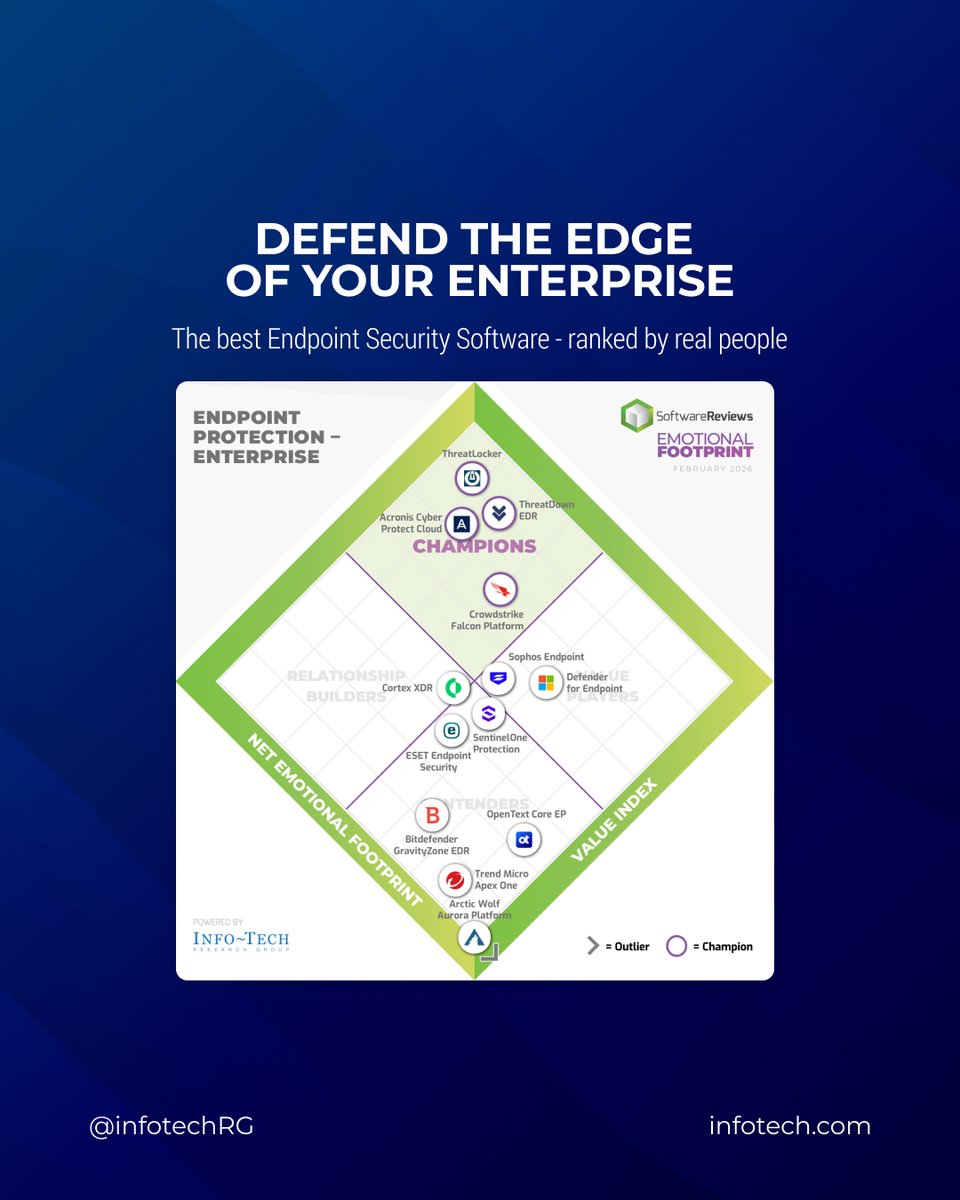
Not all endpoint security solutions deliver where it counts. The @SW_Reviews Emotional Footprint report ranks top vendors based on real user feedback, not analyst opinion. See which vendors actually deliver: ow.ly/QBFa50YGsb8 #CyberSecurity #EndpointSecurity #ITSecurity
Webinar: Pentest - IT-Security, Schwachstellenanalyse 🗓️ 28.04.26 🕗 13:00 - 13:45 Uhr 👉🏼 ALLNET & @pentesttoolscom free Webinar auf Englisch Jetzt kostenlos anmelden! ➡️ bit.ly/4sIUALa #Webinar #PentestTools #ITsecurity #VAD #TheNetworkPeople

Entdecke, welche Hardening-Tools dein Unternehmen wirklich vor Cyberangriffen schützen. 👉 fb-pro.com/hardening-tool… #CyberSecurity #ITSecurity #Hardening

Lies, Damned Lies, and #Cybersecurity Metrics - buff.ly/TRH6Z3Q #security #ITsecurity #infosec #cyberattacks

Something went wrong.
Something went wrong.
United States Trends
- 1. Cinco de Mayo N/A
- 2. Posey N/A
- 3. Vivek N/A
- 4. #HealthcareNotWarfare N/A
- 5. Coinbase N/A
- 6. Gary Player N/A
- 7. Evil Dead Burn N/A
- 8. #XDCNetwork N/A
- 9. The Odyssey N/A
- 10. #ElRenacerDeVenezuela N/A
- 11. #We_Will_Fight_1009_Times N/A
- 12. Presidential Fitness Test N/A
- 13. #Heeseung_Absence_Echoes N/A
- 14. Nolan N/A
- 15. Seger N/A
- 16. Springsteen N/A
- 17. Bank of America N/A
- 18. Helen of Troy N/A
- 19. Chipotle N/A
- 20. Utah State N/A