#linkedsecurity search results
34 cameras system recently installed at a Western Beef location in Manhattan. We are honored to be part of Western Beef's efforts of improving their shoppers' and employees' experience and security. @WesternBeef @IsfSecurity @DahuaHQ #Linkedsecurity #smartsecuritysolutions



Our Team at Linked Security wishes you a very Happy Thanksgiving! We are thankful that you entrust us with the security of your business and home! #happythanksgiving #linkedsecurity #givethanks

With WallEX, smart safety moves with you🌃 —linked security that keeps your home protected, effortlessly.😃 #WallEX #LinkedSecurity #SmartHomeSafety #IFLYTEK #Riyadh #LuxuryLifestyle

We Know! No one expected this year to be like this…but working with you has made our year a little brighter! Thank you for being a part of the @Linked_Security family. We appreciate your business and look forward to the next year. Happy Holidays! #linkedsecurity #holidays2020

A small gift of appreciation to our clients 😊🍷 Thank you for being a part of the Linked Security family. We appreciate your business and look forward to supporting you in the next year. Happy Holidays! 🎉🎉🎉 #linkedsecurity #Holidays2020 #grateful




With WallEX, smart safety moves with you🌃 —linked security that keeps your home protected, effortlessly.😃 #WallEX #LinkedSecurity #SmartHomeSafety #IFLYTEK #Riyadh #LuxuryLifestyle

A small gift of appreciation to our clients 😊🍷 Thank you for being a part of the Linked Security family. We appreciate your business and look forward to supporting you in the next year. Happy Holidays! 🎉🎉🎉 #linkedsecurity #Holidays2020 #grateful




We Know! No one expected this year to be like this…but working with you has made our year a little brighter! Thank you for being a part of the @Linked_Security family. We appreciate your business and look forward to the next year. Happy Holidays! #linkedsecurity #holidays2020

34 cameras system recently installed at a Western Beef location in Manhattan. We are honored to be part of Western Beef's efforts of improving their shoppers' and employees' experience and security. @WesternBeef @IsfSecurity @DahuaHQ #Linkedsecurity #smartsecuritysolutions



⚠️ Unauthorized Template Modification Detected Attackers use “Unauthorized Template Modification Detected”‑style techniques to inject malicious code or references into document or certificate templates so that payloads are fetched or executed only when a user opens a file,

Looking for cybersecurity newbies to help mentor and upskill. who wants in?

Free Cybersecurity Books . Learn, Build, and Level Up 🔐 If you’re serious about cybersecurity, stop waiting and start learning. 📘 Web Security & Ethical Hacking ☁️ Cloud Security (AWS & more) 🛡️ Incident Response & Blue Teaming 🎯 Penetration Testing 📊 Security

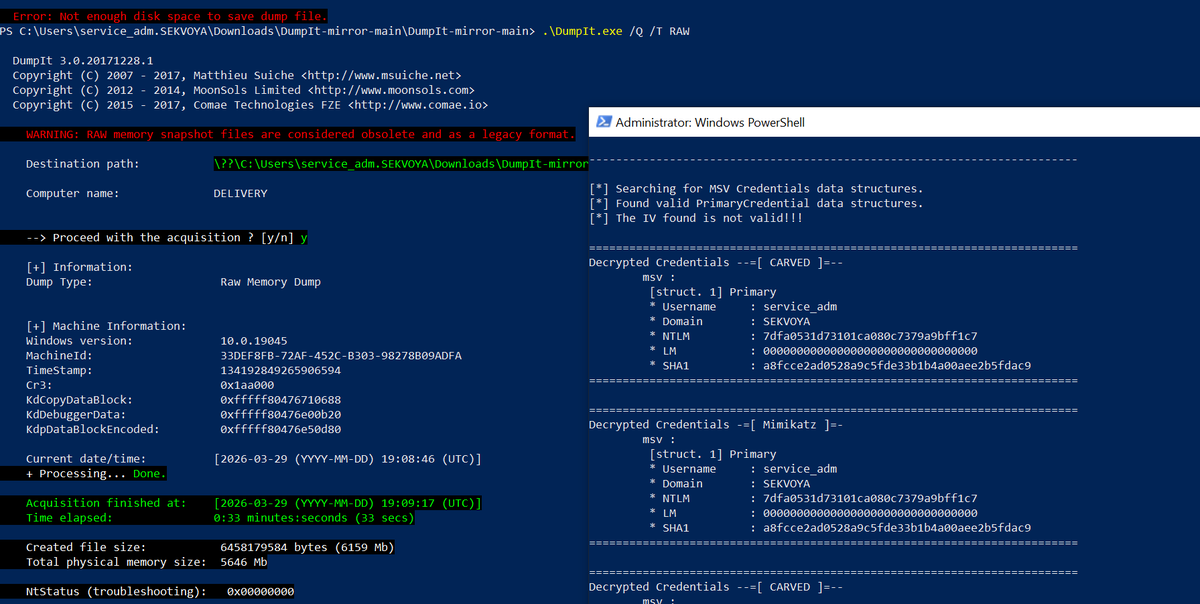
During pentests you often find endpoints protected by AV/EDR that cannot be disabled locally because they are managed by centralized security systems. This means you can’t run your tools on those machines. In our article, we showed how digital forensics can be used to extract
Boring day... Let's find out where does @ProtonMail have servers, shall we? Open up @modat_magnify and search for "cert.issuer.email~" (which is kinda good for bugbounters too). Easy as that.

Studying for CompTIA A+ Core 1 Certificate? This Full Guide is what you need 🧑💻 Download Link : drive.google.com/drive/folders/…

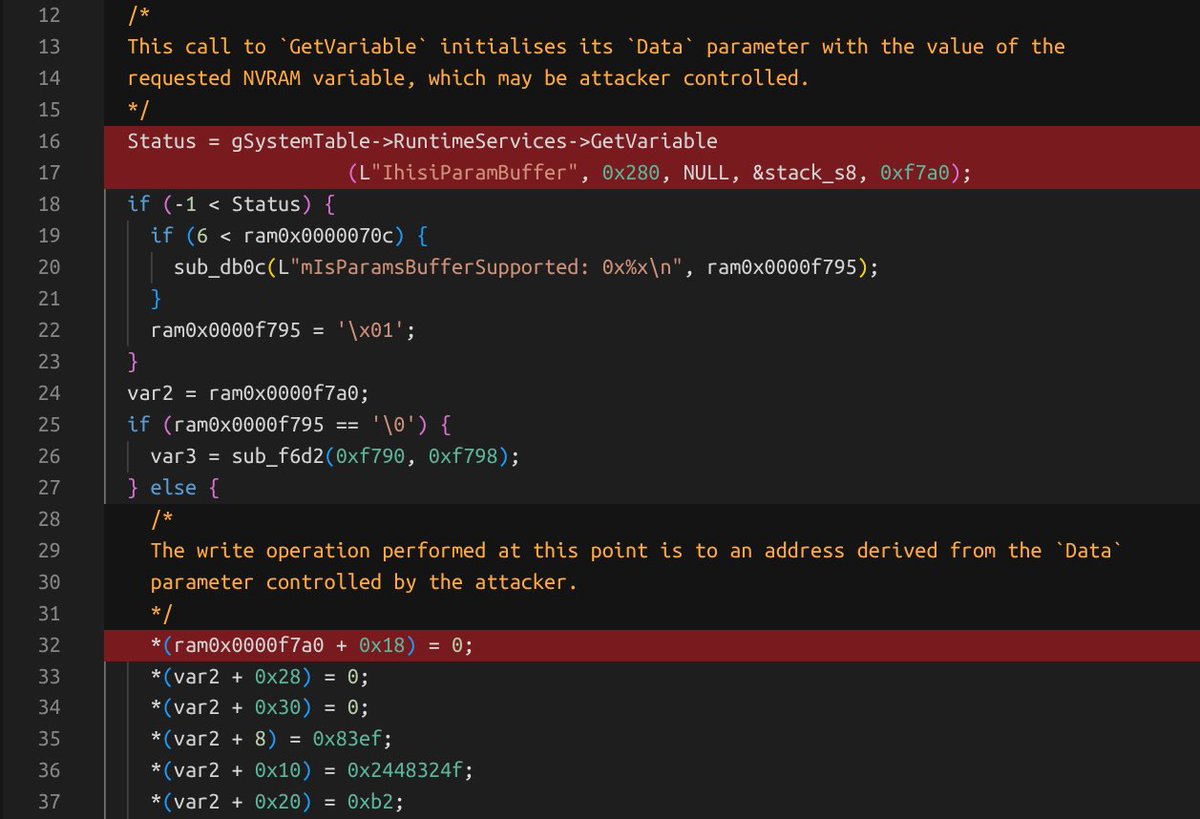
Running unsigned code during the UEFI boot process (CVE-2025-3052) binarly.io/blog/another-c… Credits @binarly_io #infosec

🛡️Defending AI agents means turning intent into action This table shows how: map identity, endpoint, supply chain, network, data, and response practices directly to Microsoft Security controls like Entra ID, Defender XDR, Purview, and Sentinel. The result? Clear pivots from

We Know! No one expected this year to be like this…but working with you has made our year a little brighter! Thank you for being a part of the @Linked_Security family. We appreciate your business and look forward to the next year. Happy Holidays! #linkedsecurity #holidays2020

Complete Cybersecurity Course (Basic → Advanced) 1. Cybersecurity fundamentals 2. Linux and security tools 3. Penetration testing fundamentals 4. Python for security tasks Download Link : drive.google.com/drive/folders/… Regards by @decabyte ✅
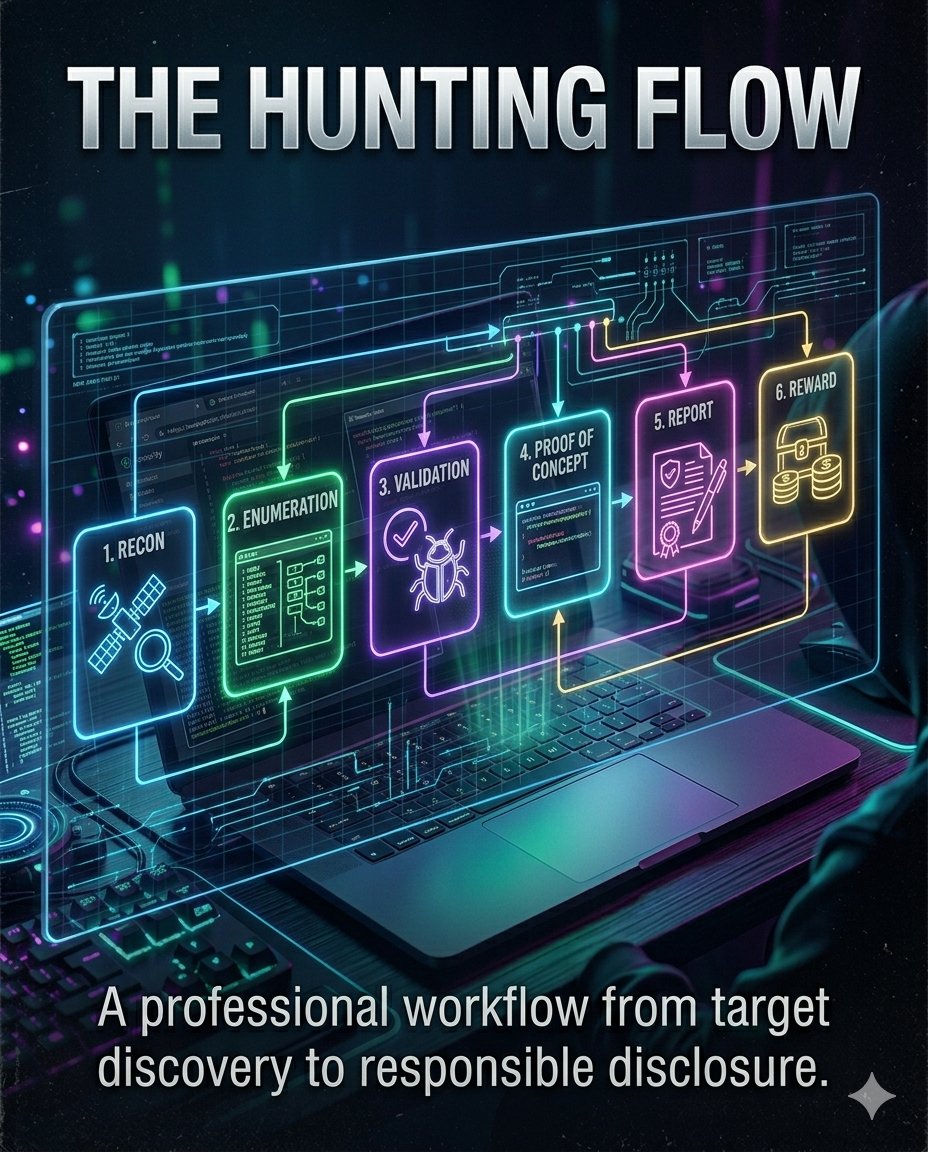
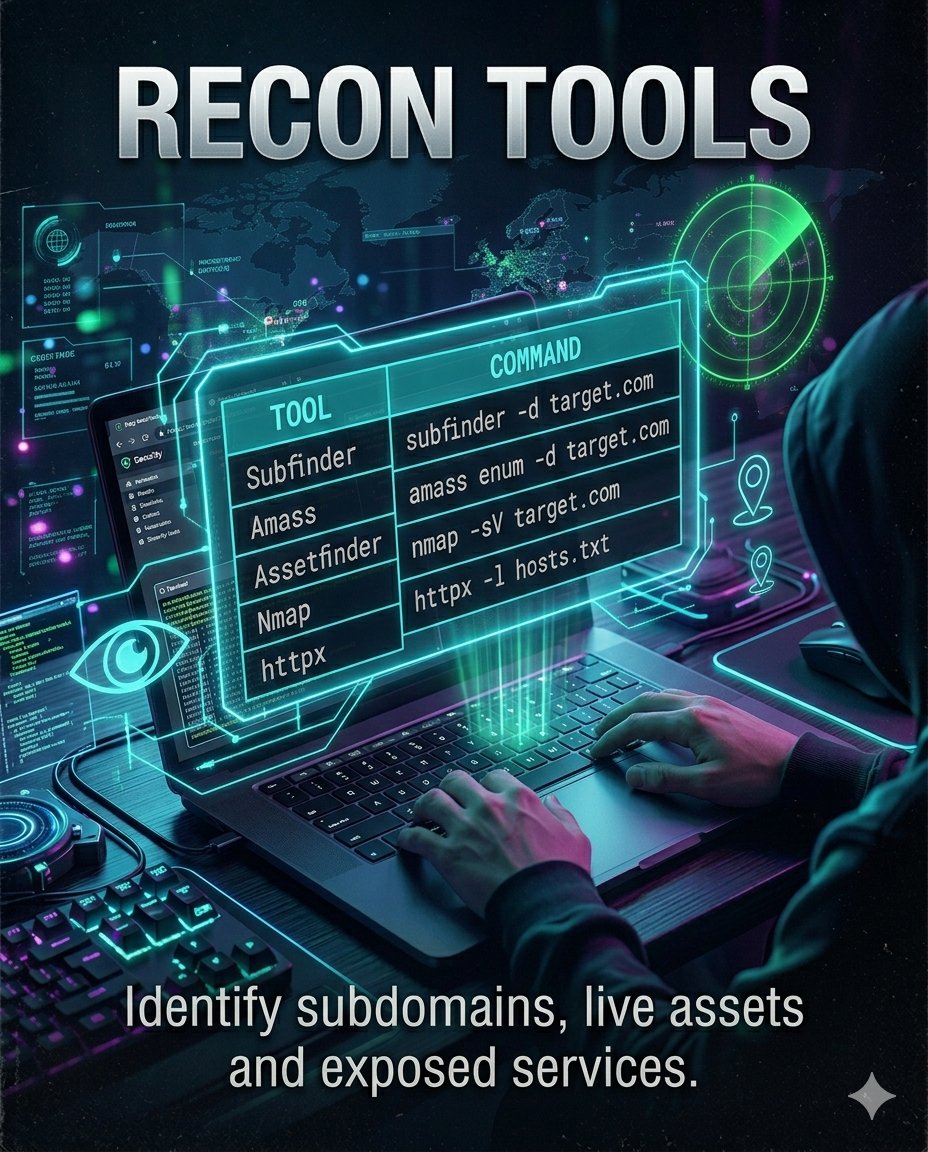
Bug Bounty Hunter Workflow Guide A structured workflow is essential for successful bug bounty research. From recon and validation to reporting and rewards, every step matters in identifying real security issues. Comment BUG 🐞👇 #bugbounty #cybersecurity #infosec


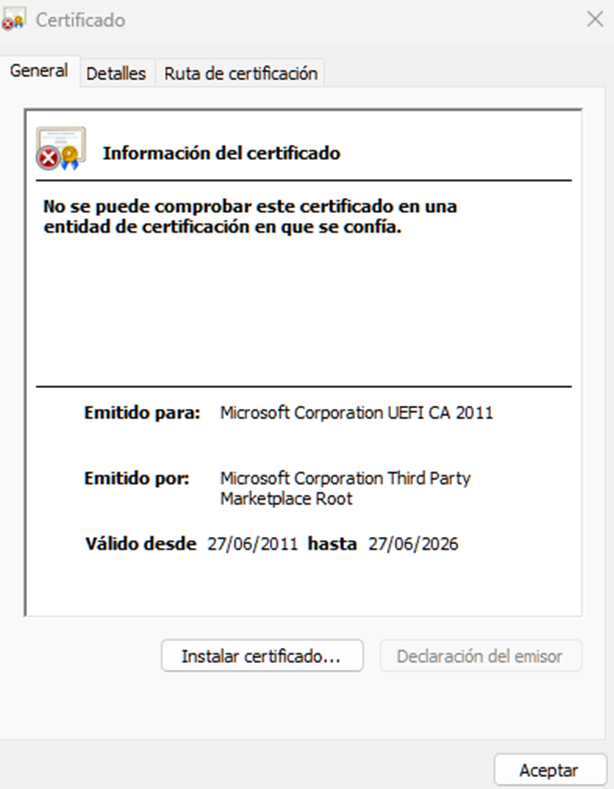
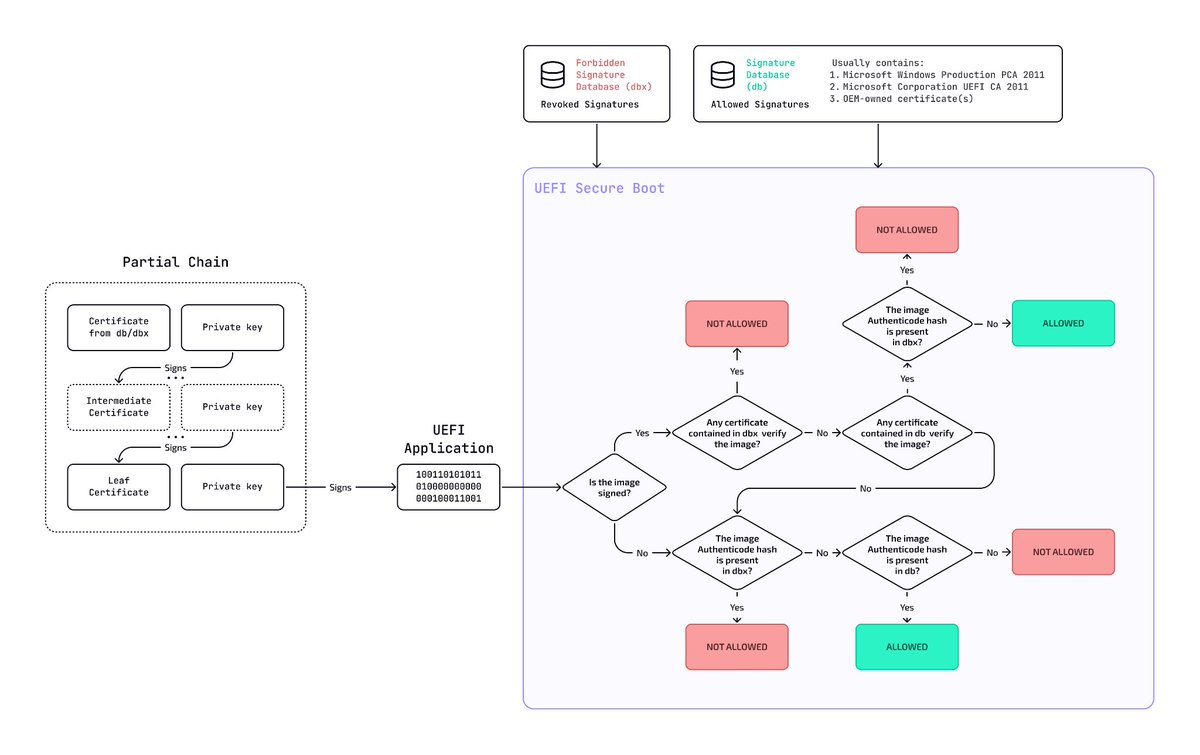
Después de 15 años y por primera vez, en el contexto de Secure Boot, a Microsoft le caduca en junio el certificado de firma de bootloaders de terceros (y en octubre el suyo). Como efecto colateral, puede bloquear a Veracrypt, el heredero de TrueCrypt tan usado. Hilo¬
Password security is one of the most critical pillars of modern cybersecurity. This guide explores how security professionals assess password strength and identify weak authentication practices across systems and accounts. From common password pattern analysis and

Testing for XXEs via file uploads can sometimes be complex... 😓 OXML_XXE by @willvandevanter embeds XXE/XML exploits into various file formats (such as DOCX, XLSX, PPTX, ODT, SVG, etc.) and makes it incredibly easier to test for these vulnerabilities! 🤠 Check it out! 👇

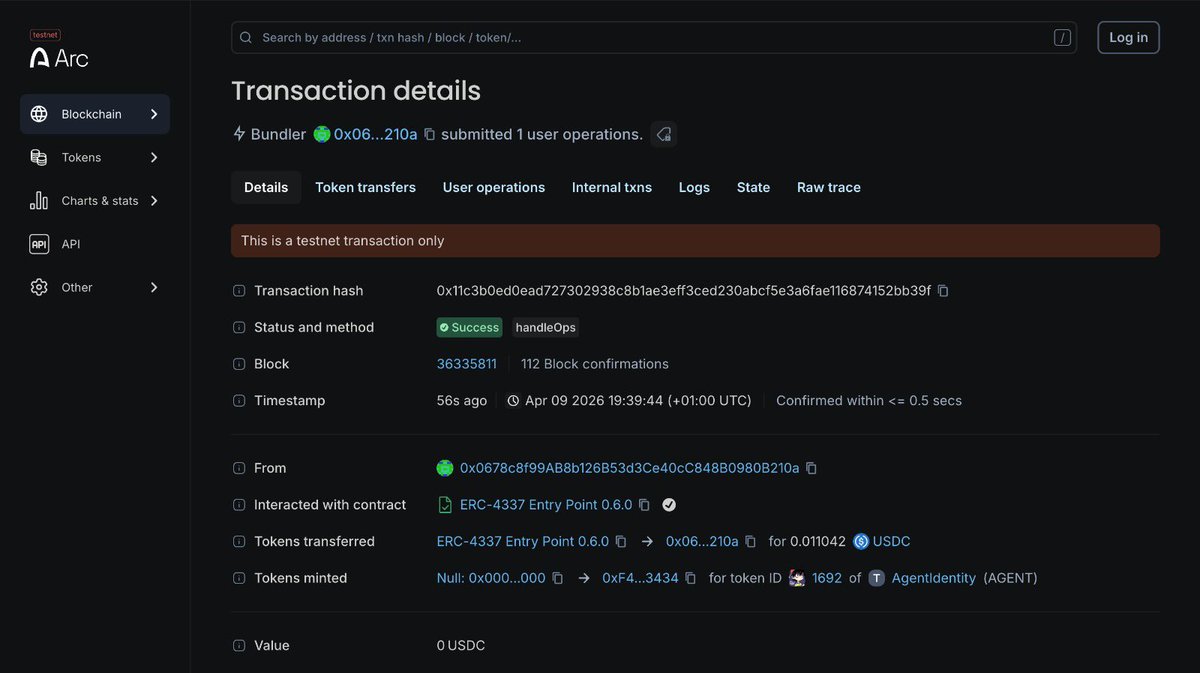
Another update on @arc Let’s interact with Arc escrow flow and build a decentralized version of freelance work from the backend where - Payment is locked upfront - Work is submitted as verifiable data - A verifier confirms completion and - Smart contracts handle payout
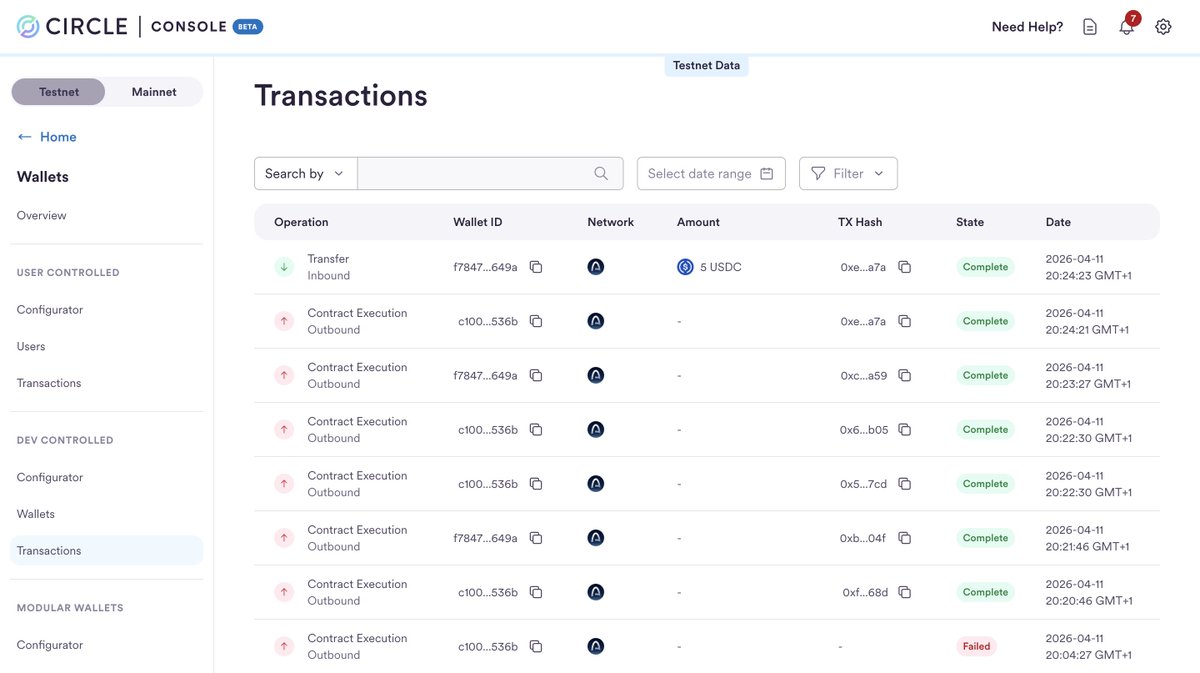
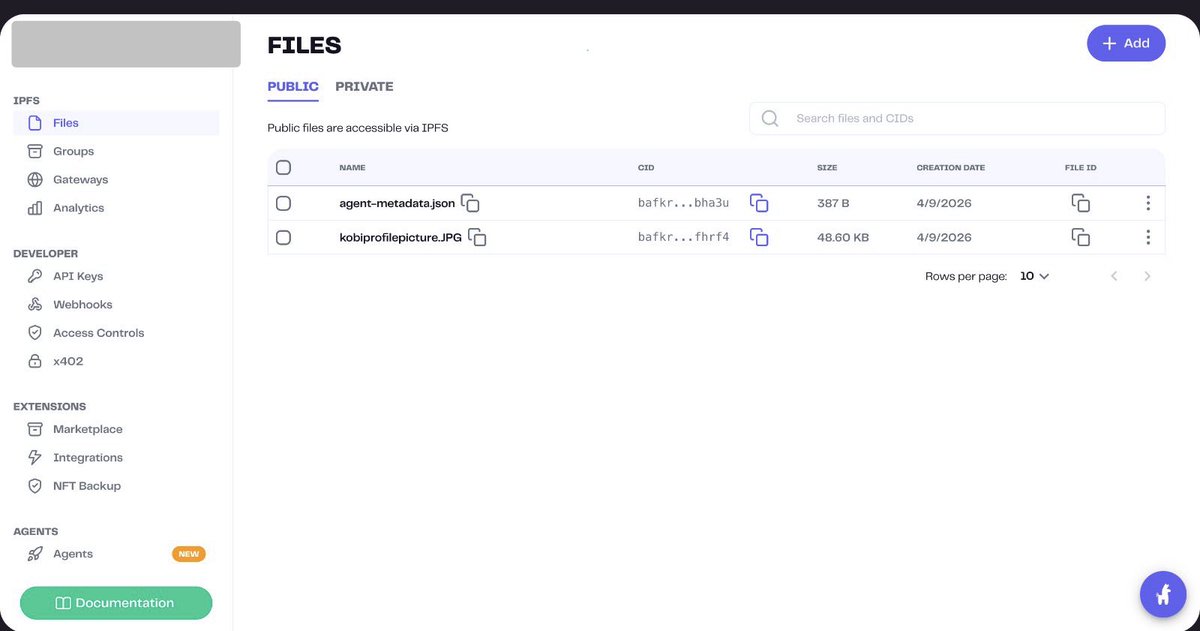
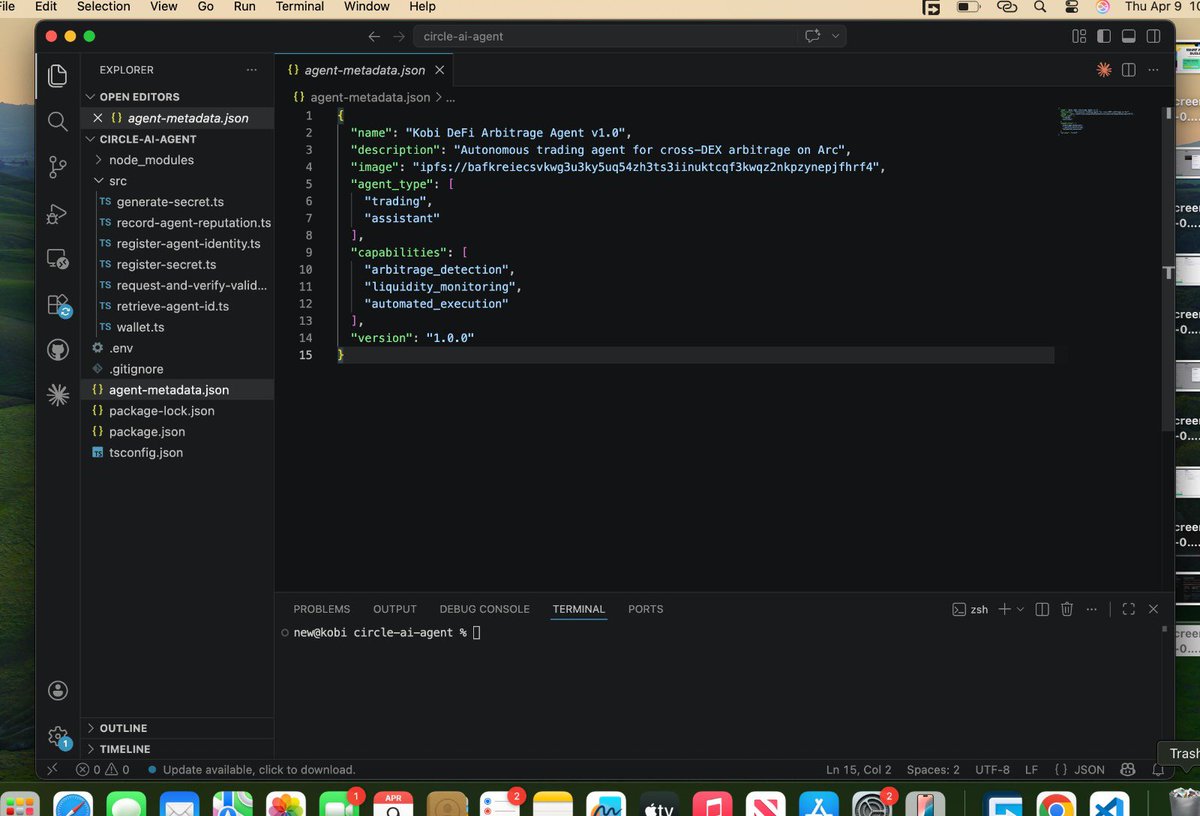
Create and register your own AI Agent on @arc testnet This is how you can create your own AI agent on Arc testnet with verifiable identities on the blockchain using ERC 8004 🎯 Code already written, just clone and run the necessary commands Here is what we will achieve -
Thread 1/3 LLM Red Teaming Resources As AI adoption grows, securing large language models is now critical. Red teaming helps identify weaknesses, misuse risks, and safety gaps in AI systems. Start with these resources:

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

Another Crack in the Chain of Trust: Uncovering (Yet Another) Secure Boot Bypass Resource: binarly.io/blog/another-c…

Want to pick up some #programming in your cybersecurity/tech journey? The TCM Security Academy is here for you. We offer several programming courses, which we've highlighted below. 🫶 And yes, some of these courses are free! ⬇️ Find them all in the TCM Security Academy:



Something went wrong.
Something went wrong.
United States Trends
- 1. #GenocidalNetanyahu N/A
- 2. Conor Benn N/A
- 3. Shane Lowry N/A
- 4. #FuryMakhmudov N/A
- 5. Swalwell N/A
- 6. Cam Young N/A
- 7. #Our_FATE_Is_SevEN N/A
- 8. Justin Lawrence N/A
- 9. #Keep_Boycotting_BELIFT N/A
- 10. Senga N/A
- 11. Rory N/A
- 12. #DOOP N/A
- 13. Klassen N/A
- 14. Keelon Russell N/A
- 15. Kevin Hayes N/A
- 16. Haotong Li N/A
- 17. Barzal N/A
- 18. Robin Hood N/A
- 19. Tom Wilson N/A
- 20. Cameron Young N/A