#hacking search results
📰 Crypto Hacks Soar April saw a record number of crypto hacks, with over 20 exploits and $600 million in losses. These hacks expose DeFi's security vulnerabilities. Verdict: SIGNAL ◆ Institutional funds at risk --- Source: The Block #cryptosecurity #DeFi #hacking

Czy próbowałeś złamać hasło e-mail, Instagram, WhatsApp lub Facebook? Wyślij wiadomość, aby skorzystać z dowolnej usługi hakerskiej #hacking #facebook #instagram #whatsapp #hackerpage #crackcode #hasło
Pehel News Headlines in Sindhi - April 28, 2026 - 06:00AM youtube.com/watch?v=OzF5j5… #Toyota #Hacking #Accident #ChatGPT #ABC #AssassinationAttempt #IsraeliGovernment #China #ContentCreation #ResourceSecurity
youtube.com
YouTube
Pehel News in Sindhi
Ciberseguridad profesional para profesionales. #seguridadsi #ciberseguridad #hacking #cursosciberseguridad #cursoshacking #aprendehacking
What can hacking a vape pen teach us about #IoT security? Well, maybe not a ton, but it turns out there's some interesting components to the device. Watch and learn in today's short. Want to start taking apart all kinds of devices and hardware #hacking? Check out our
The Internet Is Falling Down, Falling Down, Falling Down (cPanel & WHM Authentication Bypass CVE-2026-41940) labs.watchtowr.com/the-internet-i… #infosec #Hacking #CyberSecurity #OpSec
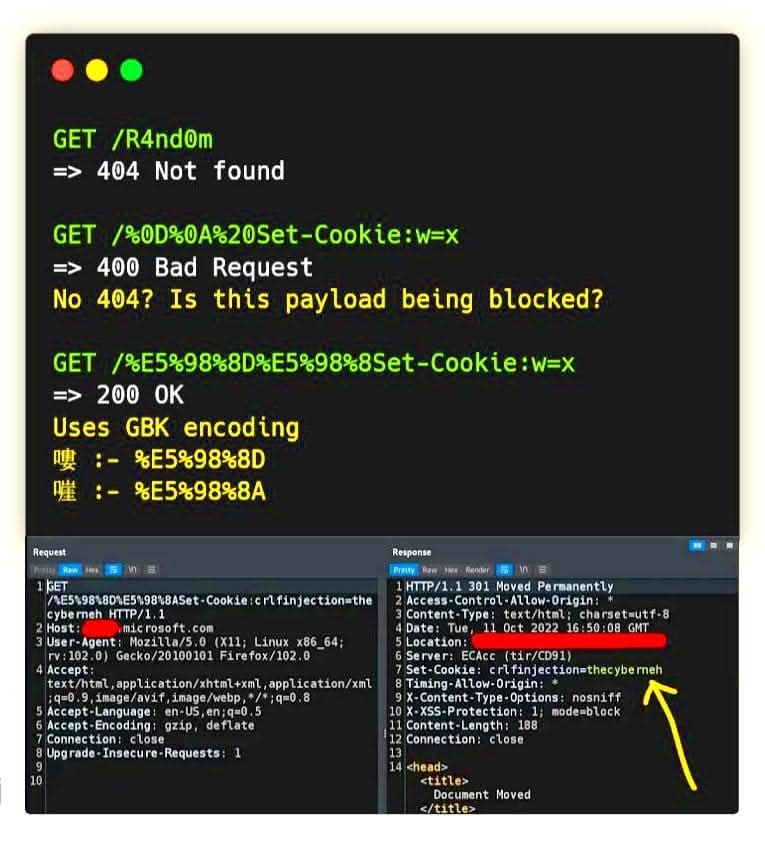
"Encoding Bypasses | Complete Guide" by Amrsmooke #BugBounty #Cybersecurity #Hacking #InfoSec medium.com/@amrsmooke321/…
Great for learning wireshark Just solved : Réseau/Kerberos - Authentification challenge on Root-Me :þ root-me.org/?page=validati… @rootme_org #hacking #challenge #Réseau
Fragmentos de cursos de ciberseguridad SeguridadSi #seguridadsi #ciberseguridad #hacking #hackingetico #hackers #cursosciberseguridad #cursoshacking #aprendehacking
"The PowerShell Detection Gap That’s Costing Organizations Millions" by Manish Rawat #BugBounty #Cybersecurity #Hacking #InfoSec medium.com/@maxxrawat007/…
Notice increase in #cybersecurity #hacking incidents on #healthcare industry-your PII: TaxID-Driver's license-passport-#financial & pers health Info is taken?! Latest to disclose-11 months after discovery-is #Sandhills Medical w/ransomware attack -170,000 securityweek.com/sandhills-medi…
We built a CTF challenge designed to be painful to reverse engineer. Then an AI agent solved it in 6 minutes. Try it yourself before reading how 👉 ttd.eshard.com Full write-up: eshard.com/blog/ring0-rin… #CTF #reverseengineer #hacking
"The $100 Bug Bounty Myth Why “No Experience Needed” Is Both a Lie and the Truth" by R.H Rizvi #BugBounty #Cybersecurity #Hacking #InfoSec medium.com/@R.H_Rizvi/the…
Toujours aussi fun d'écouter les conversations passivement et d'observer 👌 #hacking
"The Autonomy Problem: Why AI Agents Demand a New Security Playbook" by Majid #BugBounty #Cybersecurity #Hacking #InfoSec medium.com/@majid207/the-…
Chinese National Extradited Over Silk Typhoon Cyber Campaign infosecurity-magazine.com/news/chinese-n… #cybersecurity #infosec #hacking
infosecurity-magazine.com
Chinese National Extradited Over Silk Typhoon Cyber Campaign
Extradition links alleged MSS-directed hacker to Hafnium and COVID-19 espionage
Ciberseguridad profesional para profesionales. #seguridadsi #ciberseguridad #hacking #cursosciberseguridad #cursoshacking #aprendehacking
📰 Crypto Hacks Soar April saw a record number of crypto hacks, with over 20 exploits and $600 million in losses. These hacks expose DeFi's security vulnerabilities. Verdict: SIGNAL ◆ Institutional funds at risk --- Source: The Block #cryptosecurity #DeFi #hacking

Czy próbowałeś złamać hasło e-mail, Instagram, WhatsApp lub Facebook? Wyślij wiadomość, aby skorzystać z dowolnej usługi hakerskiej #hacking #facebook #instagram #whatsapp #hackerpage #crackcode #hasło
The Internet Is Falling Down, Falling Down, Falling Down (cPanel & WHM Authentication Bypass CVE-2026-41940) labs.watchtowr.com/the-internet-i… #infosec #Hacking #CyberSecurity #OpSec
🚨 North Korea's crypto hacks accounted for 76% of losses in 2026! With nearly $600M stolen in just two incidents, what does this mean for investors? #crypto #hacking #DeFi

Notice increase in #cybersecurity #hacking incidents on #healthcare industry-your PII: TaxID-Driver's license-passport-#financial & pers health Info is taken?! Latest to disclose-11 months after discovery-is #Sandhills Medical w/ransomware attack -170,000 securityweek.com/sandhills-medi…
Great for learning wireshark Just solved : Réseau/Kerberos - Authentification challenge on Root-Me :þ root-me.org/?page=validati… @rootme_org #hacking #challenge #Réseau
No scanning. No exploits. No brute force. Just Responder on an unsegmented network. 47 credentials captured in 20 minutes. #hacking #networksecurity
What can hacking a vape pen teach us about #IoT security? Well, maybe not a ton, but it turns out there's some interesting components to the device. Watch and learn in today's short. Want to start taking apart all kinds of devices and hardware #hacking? Check out our
Just solved : Web - Client/HTML - boutons désactivés challenge on Root-Me :þ root-me.org/?page=validati… @rootme_org #hacking #challenge #WebClient
Offense > Defense. Always. If you’re still only learning defense, you’re already behind. #BugBounty #CyberSecurity #Hacking #Infosec Stop defending. Start exploiting → Join AgniOps
Claude Code, Copilot and Codex all got hacked. Every attacker went for the credential, not the model. dlvr.it/TSJXLc #AI #CyberSecurity #Hacking #DataBreach #SoftwareDevelopment
Securing the Smart City: Cybersecurity Strategies for Europe’s Urban Centers View Full: lnkd.in/g6CaHPt9 #cybersecurity #hacking #security #technology #hacker #infosec #ethicalhacking #cybercrime #tech #linux #cyber #cyberattack #programming #malware #kalilinux #privacy
Agent’s claims on #WhatsApp access spark security concerns securityaffairs.com/191515/social-… #securityaffairs #hacking #Meta
Data Sovereignty and Security: Europe’s Journey Towards Robust Cyber Policies View Full: lnkd.in/gav9ERwh #cybersecurity #hacking #security #technology #hacker #infosec #ethicalhacking #cybercrime #tech #linux #cyber #hackers #informationsecurity #cyberattack
""" 🚨 INSIGHT: TRM Labs dice che il 76% delle perdite di hacking in criptovaluta del 2026 iniziante si abbinano alla Corea del Nord per un totale di 577 milioni di dollari. #criptovalute #hacking #CoreaDelNord


I had on record , told #StrongRoom is where BJP has been #Hacking the #EVMs with @ECISVEEP approved qualified hackers.. HAPPENING in Every Election. Told @MahuaMoitra et al, to Guard the EVMs ..
VIDEO | Kolkata: TMC leaders Kunal Ghosh and Shashi Panja sit on dharna outside Netaji Indoor Stadium; allege BJP, EC office opening ballot boxes in strong room without presence of relevant party stakeholders. (Full video available on PTI Videos- ptivideos.com)
Most people think "ethical hacker" is one job. It's not. It's actually eleven different paths. We just published the definitive breakdown of every type of ethical #hacking and what each one actually looks like in the real world. Here's a quick version: 🔹 Network pentesting 🔹

💰A list of companies that accept responsible disclosure 🔗bug-bounties.as93.net 🔖#infosec #cybersecurity #hacking #pentesting #security

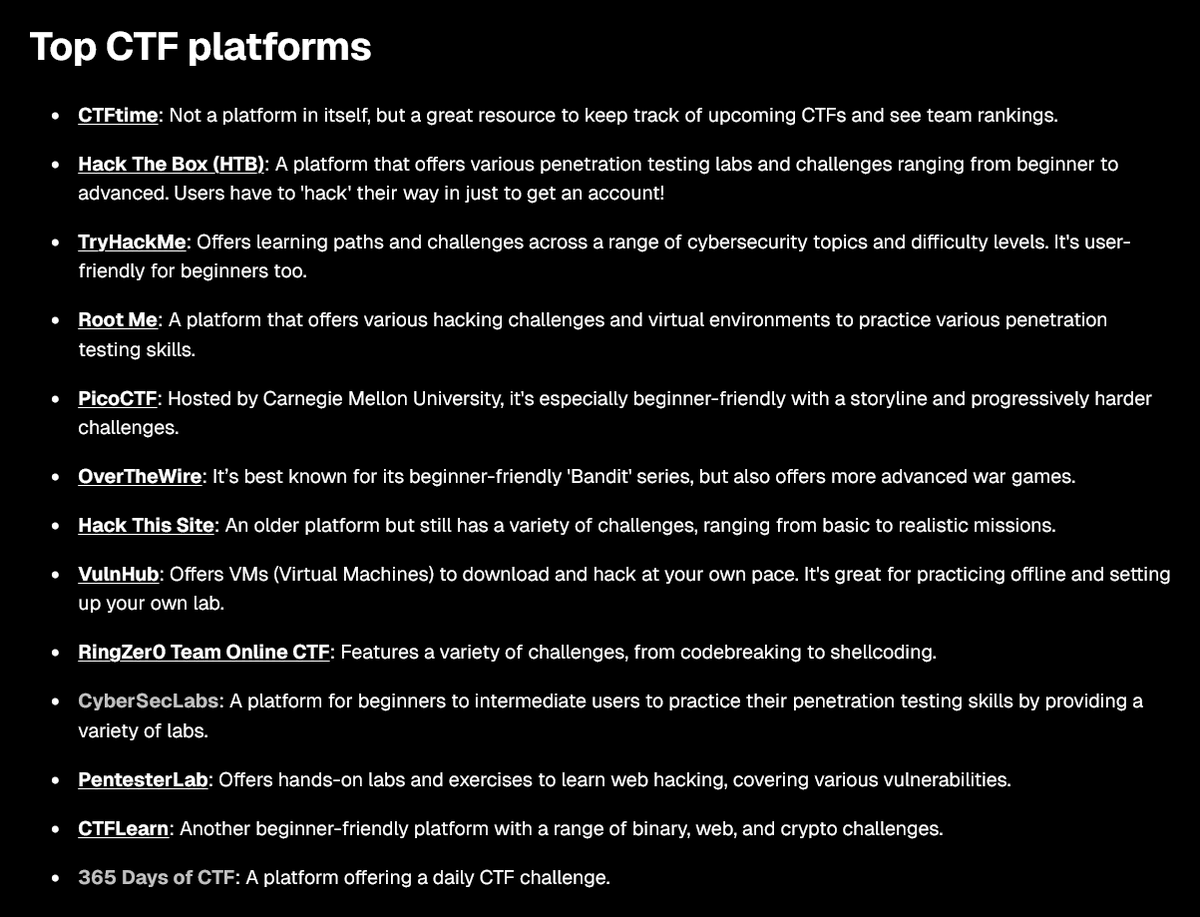
Getting into CTFs or leveling up your hacking skills? Here are some of the best platforms to practice and grow 👇 #CTF #CyberSecurity #Hacking #BugBounty
🐲Security analysis and reverse engineering of IoT devices and debugging with Ghidra 🔹Part 1: artresilia.com/iot-series-i-a… 🔹Part 2: artresilia.com/iot-series-ii-… 🔹Part 3: artresilia.com/iot-series-iii… 🔹Part 4: artresilia.com/iot-series-iv-… 🔖#infosec #cybersecurity #hacking #pentesting

Gold Sponsor Announcement 📣 Let’s welcome our BSides 2026 Gold Sponsor, Scythe! 🥳 Thank you, #SCYTHE, for supporting learning, meaningful connections, talks, workshops, villages and much more. TICKETS ON SALE NOW! 🎟️ #bsides #hacking #infosec #event #tickets #sponsor

⚒️Open Source SIEM Tools 🔰List: 🔹OSSIM 🔹Sagan 🔹Splunk Free 🔹Snort 🔹Elasticsearch 🔹MozDef 🔹ELK Stack 🔹Wazuh 🔹Apache Metron 🔖#infosec #cybersecurity #hacking #pentesting #security

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

🔓Best Password Cracking Tools 🔹Medusa 🔹Aircrack-ng 🔹Wfuzz 🔹OphCrack 🔹LophtCrack 🔹Hashcat 🔹Cain & Abel 🔹Rainbow Crack 🔹Brutus 🔹THC Hydra 🔹John the Ripper 🔖#infosec #cybersecurity #hacking #pentesting #security

⚒️Best Cyber Security Tools 🔹OpenVAS 🔹SQLMap 🔹Aircrack-ng 🔹Maltego 🔹OpenSSH 🔹Nessus 🔹Zed Attack Proxy 🔹Wireshark 🔹Metasploit 🔹John 🔹Nmap 🔹Burp Suite 🔖#infosec #cybersecurity #hacking #pentesting #security

🗺️Active Directory Pentesting Mind Map: V1: raw.githubusercontent.com/esidate/pentes… V2: raw.githubusercontent.com/esidate/pentes… 🔖#infosec #cybersecurity #hacking #pentesting #security

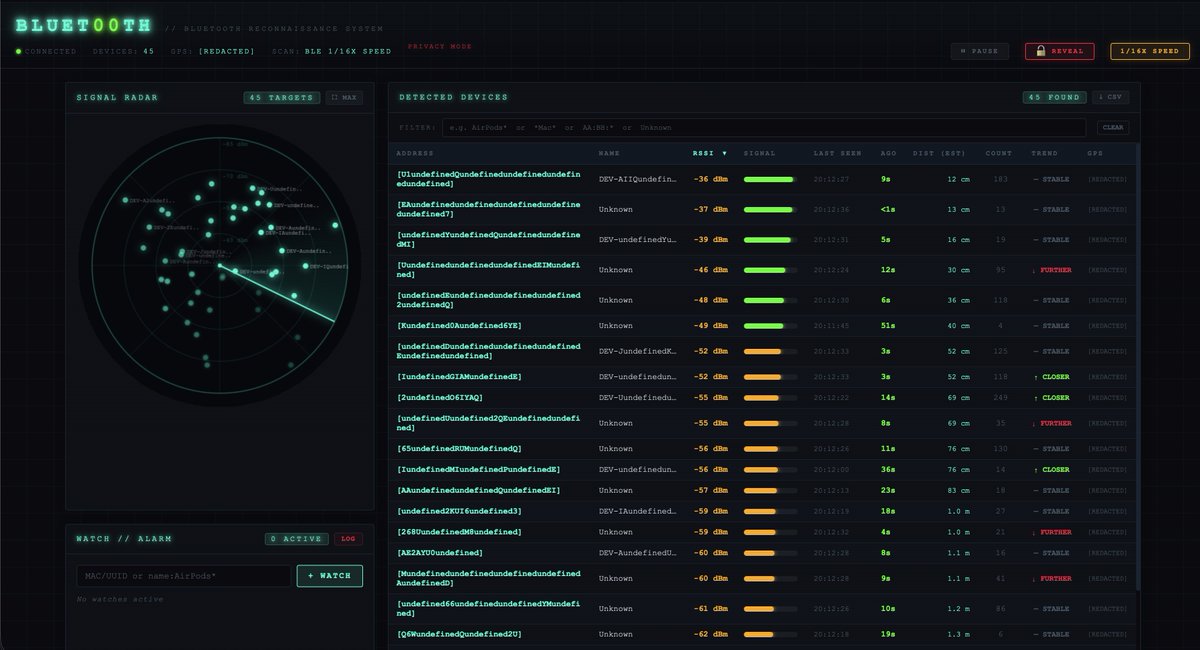
I've added the ability to slow down the scanning.... so you can now control the speed! PEW PEW #Bluet00th #Scanner #Hacking #VibeCoder
Something went wrong.
Something went wrong.
United States Trends
- 1. Hawks N/A
- 2. Hawks N/A
- 3. #911onABC N/A
- 4. Dyson Daniels N/A
- 5. Mitch N/A
- 6. Down 50 N/A
- 7. OG Anunoby N/A
- 8. JP Morgan N/A
- 9. Magic City N/A
- 10. Derrick White N/A
- 11. #NYKvsATL N/A
- 12. Trae Young N/A
- 13. Quinn Hughes N/A
- 14. Boosie N/A
- 15. Cancun N/A
- 16. Human Nature N/A
- 17. #TrueToAtlanta N/A
- 18. Mike Breen N/A
- 19. Up 50 N/A
- 20. #NewYorkForever N/A