#exploitdev wyniki wyszukiwania
This should be the final set of labs published publicly. That's all folks for now... #RE #Offsec #ExploitDev #SoftwareExploitation exploitation.ashemery.com



Bypassing PIE with partial overwrite? 🔥 Instead of guessing full addresses, just overwrite specific bytes to align with predictable offsets. Precision > brute force. A reminder that security evolves, and so must we. 🛡️ #CyberSecurity #ExploitDev #ReverseEngineering


Hand-crafted ROP chain 🛠️! Had limited gadgets, so I used an IAT entry for HeapAlloc and calculated the VirtualAllocStub RVA offset. Got creative without ASLR and possibly should've used a read primitive. Details in the gist! #ROP #ExploitDev #osed gist.githubusercontent.com/snowcra5h/a7c1…

I’m happy to announce that I passed OSED from @offsectraining 😍😍 I just got the email and man IT FELT SO GOOD #CyberSecurity #exploitdev

Happy New Year 2025! #infosec #CyberSec #ExploitDev #Hacker #Bug #bugbountyhunter #vulnerabilityResearcher #ReverseEngineering #Binex

If you're exploiting a driver offering R/W access to physical memory on Win11 24H2, you can leverage this simple trick to circumvent kernel address leak restrictions and retrieve the kernel base address :p xacone.github.io/kaslr_leak_24h… #exploitdev #driverexploitation
🚨 Released a full SEH exploit chain for DeepFreeze 8! With custom shellcode and ROP chain. Software was fully reversed, and an SEH vuln discovered studying for the #OSED 💪Blog write-up coming soon.🔍github.com/snowcra5h/Faro… #CyberSecurity #ExploitDev
𝑪𝒊𝒂𝒐 𝑰𝒕𝒂𝒍𝒚, 𝑪𝒊𝒂𝒐 𝑹𝒐𝒎𝒂! 𝑹𝒆𝒂𝒅𝒚 𝒇𝒐𝒓 𝑪𝒐𝒓𝒆𝒍𝒂𝒏? Sign up for our Expert-level stack class: bit.ly/corelan-traini… #corelan #stack #exploitdev #windows11
🇦🇺 Corelan hits Melbourne for the FIRST time! 💥 Stack Exploit Dev: Feb 3–6, 2026 🧨 Heap Masterclass: Feb 9–12, 2026 🎯 w/ @TantoSecurity 🧠 Real skills. No fluff. 💣 Come prepared. 🕐 Early bird ends Sept 2025 👉 bit.ly/corelan-traini… #Corelan #ExploitDev
Pwning LLaMA.cpp RPC Server #LLAMACpp #RPCServer #ExploitDev #CTF pwner.gg/2024/10/03/lla…
New article alert : ek0msUSB medium.com/@ekoms1/ek0msu… #hacker #greyhat #exploitdev #commandandcontrol #payloads




Interested in Software Exploitation? This course is for you and will take you from knowing nothing, to understanding how exploits work and how to write them... I hope it will be useful to someone out there! #Offsec #Cybersecurity #ExploitDev #Debugging youtube.com/watch?v=5GGyFb…

🇧🇪 Belgian Roots. Global Impact. 🌍 Corelan delivers world-class exploit dev training for Windows: 🔹 Stack Smashing 🔹 Heap Masterclass Built in Europe. Respected worldwide. Sign up 👉 bit.ly/corelan-traini… #CyberSecurity #ExploitDev #MadeInBelgium
🔔 Reminder: Zürich, Corelan Stack is coming Oct 7–10, 2025 ✅ No nonsense, No BS ✅ Just real-world exploit dev skills 🎟️ eventcreate.com/e/sigs-corelan… 💛 RT appreciated! #corelan #win11 #exploitdev
⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
Ma solution pour les exercices heap du #CTF Protostar github.com/devl00p/blog/b… #exploitdev #reverseengineering #vulndev
ONE more chance this year to take our popular Bootcamp. High-quality materials, real class, real instructor (AND the perfect prep for our heap exploitation class). Seats are selling fast! What are you waiting for? deep-conference.com/predeep-bootca… #corelan#windows11 #exploitdev

💥 Push, Pop, Boom. Corelan Stack isn’t just another course — it’ll make things click. Expert-level stack exploitation. Zero fluff, real deal. “The course filled in gaps I didn’t even know I had.” — Fabio, Brazil 👉 bit.ly/corelan-traini… #corelan #stack #exploitdev
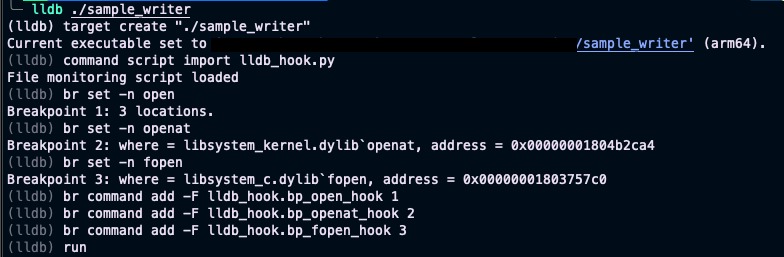
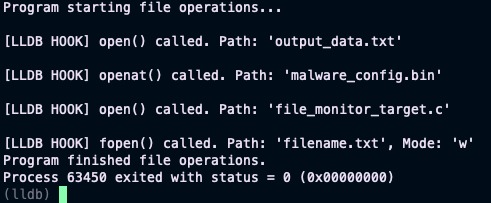
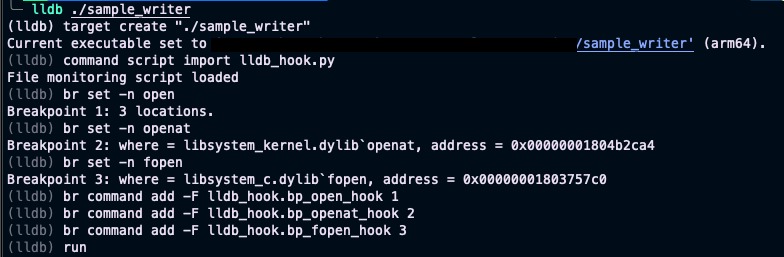
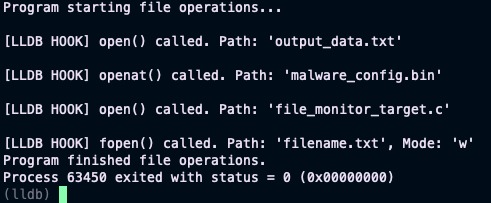
Tip #2: Level up your security analysis! 🚀 Use #lldb & Python 🐍 to dynamically monitor every file a program opens (open/openat/fopen). Crucial for #MalwareAnalysis & #ExploitDev to uncover file system interactions. See what that binary really touches! 💻📂 #CyberSecurity

⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
⚠️ Afraid of public classes? 🔒 Corelan Academy = private, intense, small-group exploit dev training 2–8 ppl • one-on-one access • flexible timing • competitive pricing • Stack & Heap DM or reply interested #corelan #exploitdev #training #heap #stack #corelanacademy
Tip #2: Level up your security analysis! 🚀 Use #lldb & Python 🐍 to dynamically monitor every file a program opens (open/openat/fopen). Crucial for #MalwareAnalysis & #ExploitDev to uncover file system interactions. See what that binary really touches! 💻📂 #CyberSecurity

Something went wrong.
Something went wrong.
United States Trends
- 1. FIFA 395K posts
- 2. FINALLY DID IT 437K posts
- 3. The WET 117K posts
- 4. Frank Gehry 5,538 posts
- 5. Hep B 17K posts
- 6. Paraguay 29.2K posts
- 7. Portugal 111K posts
- 8. Argentina 242K posts
- 9. Brazil 83.7K posts
- 10. Warner Bros 257K posts
- 11. Matt Campbell 11.6K posts
- 12. Vizio N/A
- 13. Sherman 4,927 posts
- 14. #Mundial2026 44.6K posts
- 15. Iowa State 9,851 posts
- 16. $CVNA 1,007 posts
- 17. Croatia 26.9K posts
- 18. Morocco 69.8K posts
- 19. Hisense 1,204 posts
- 20. 14th Amendment 7,056 posts