#datahiding risultati di ricerca
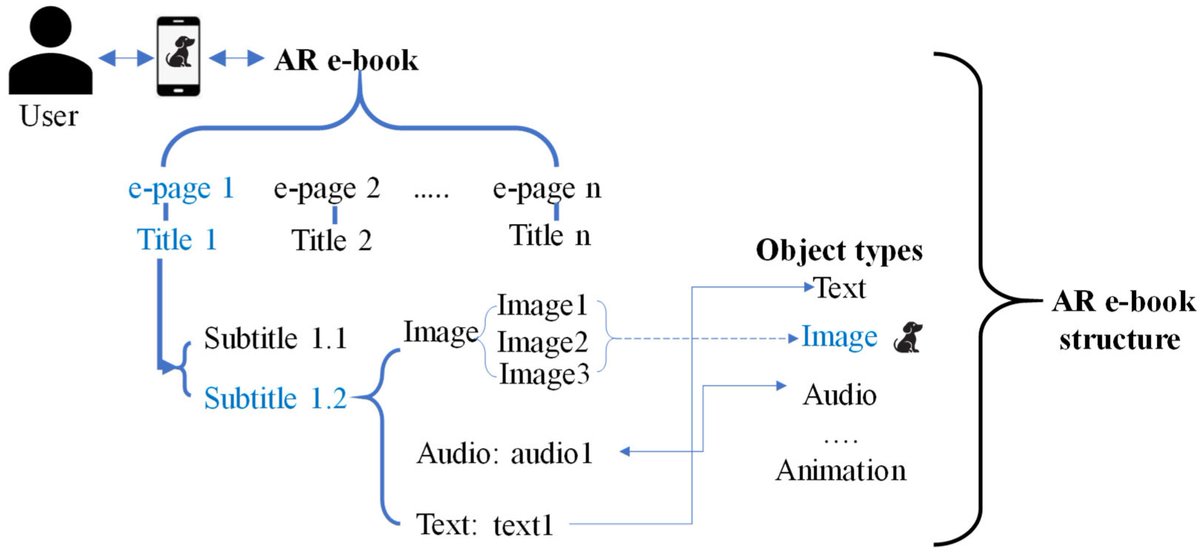
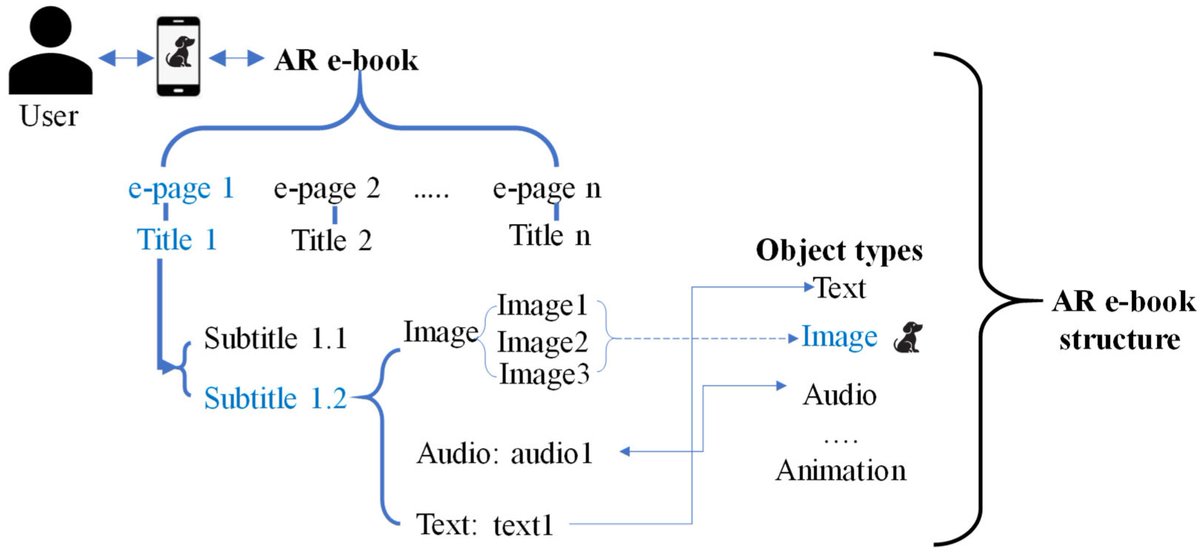
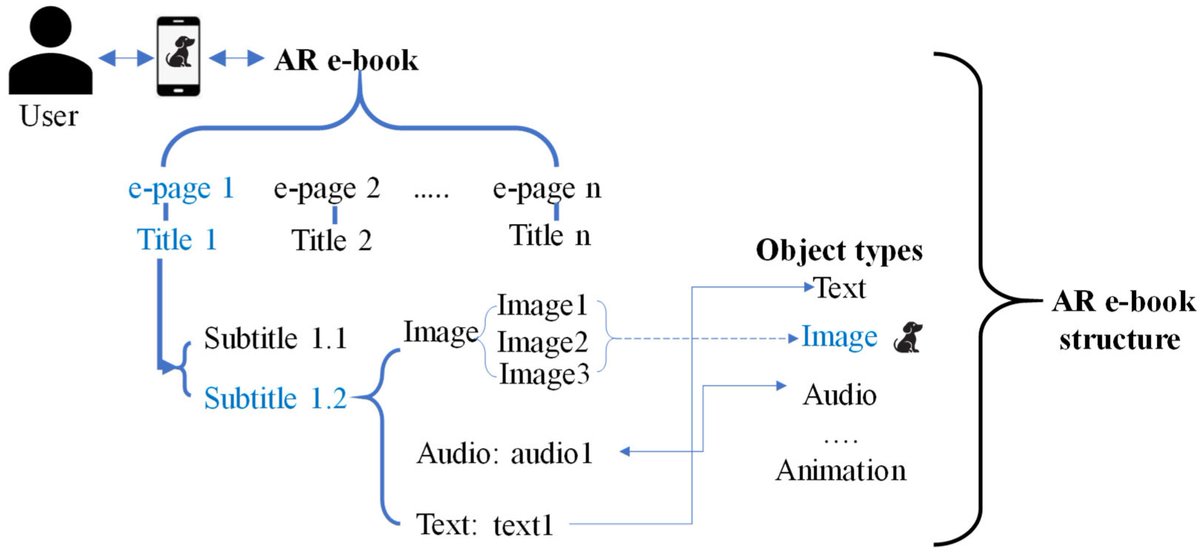
Check this newly published article "Enhancing Security in #AugmentedReality Through Hash-Based #DataHiding and Hierarchical Authentication Techniques" at brnw.ch/21wX56r Authors: Chia-Chen Lin et al. #mdpisymmetry #dataintegrity @ComSciMath_Mdpi
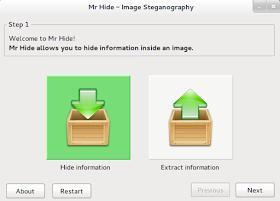
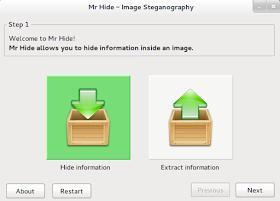
Mr. Hide, a new steganography tool for hiding data into images. steganography.daniellerch.me/p/mr-hide.html #steganography #datahiding
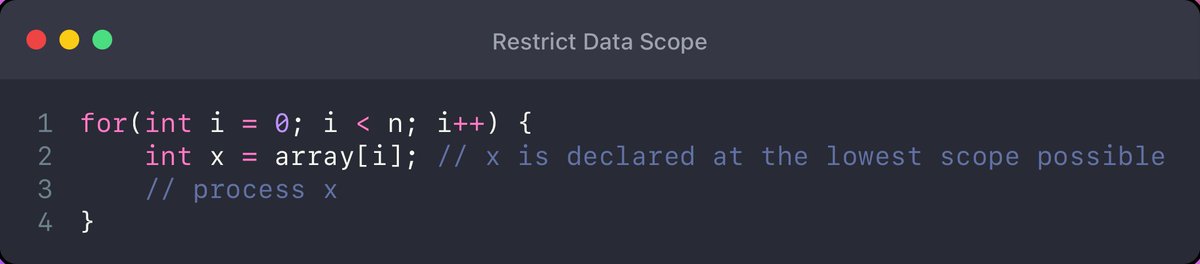
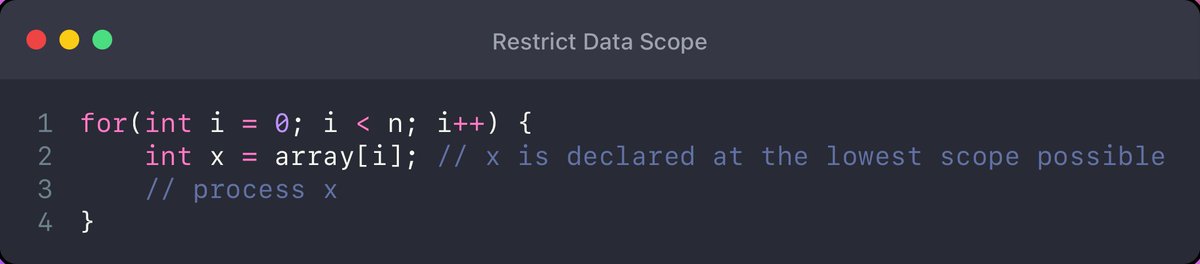
🛰️ Rule 5: Restrict Data Scope: NASA supports the idea of data hiding or declaring variables as they're used at the lowest scope possible. This approach reduces the amount of code that can access those variables. #DataHiding #Coding
Explore how hackers hide data inside spam emails and the unseen risks it poses to cybersecurity. redsecuretech.co.uk/blog/post/the-… #CyberSecurity #EmailSteganography #DataHiding #SpamEmails #CyberAwareness #InfoSec #DigitalForensics #CyberThreats

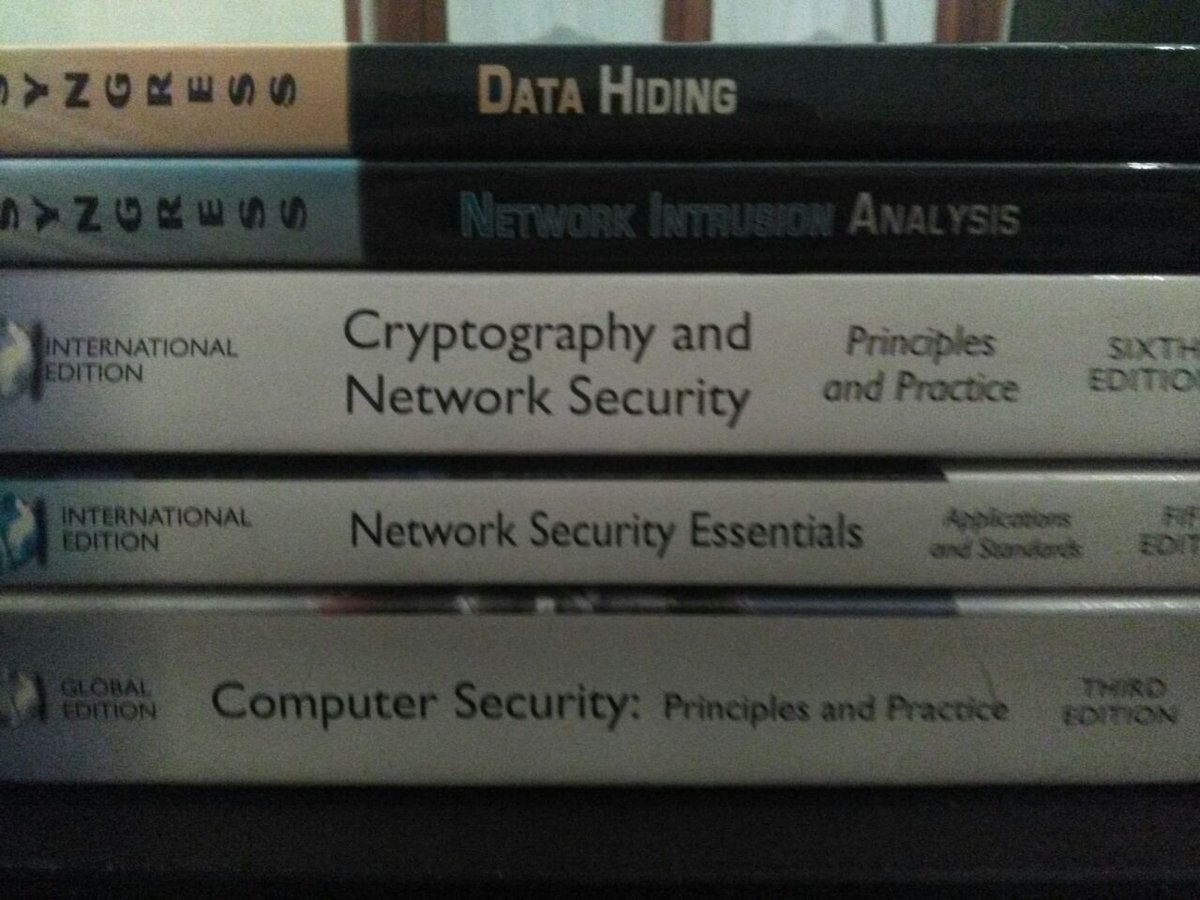
... come rendermi felice | ... how to make me happy | ... 私を幸せにする方法 #security #networking #datahiding #cryptography
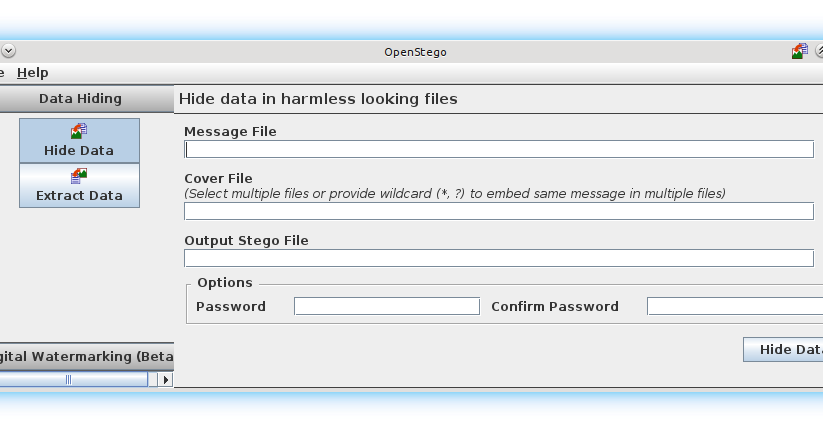
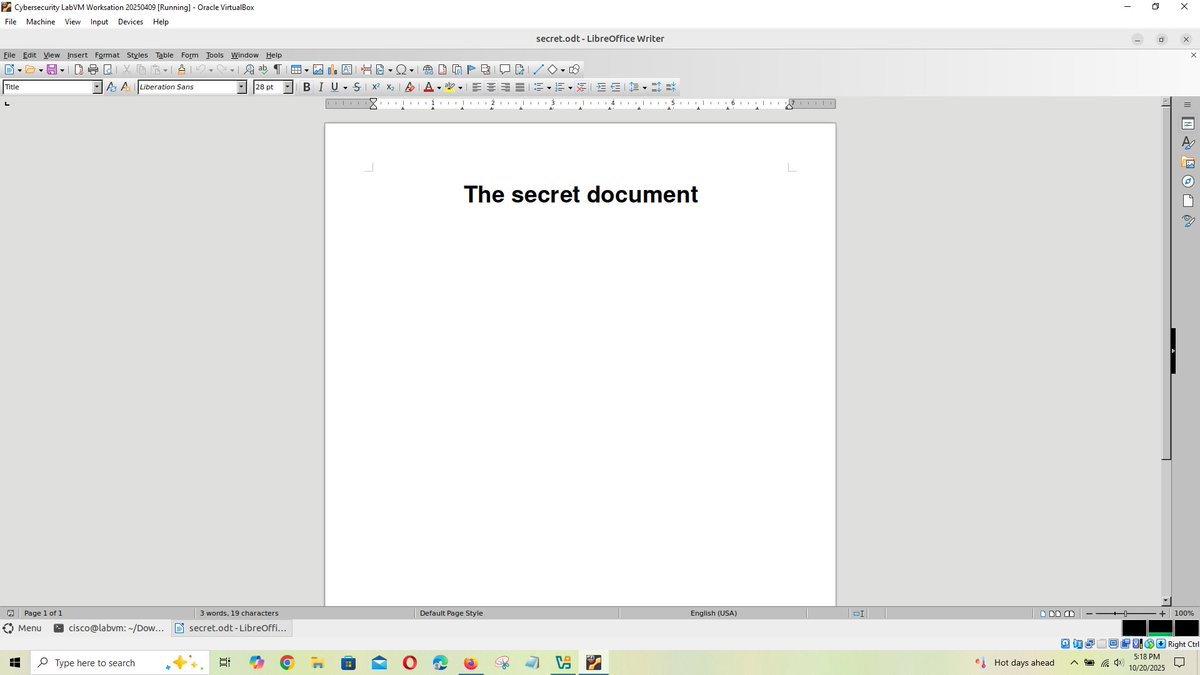
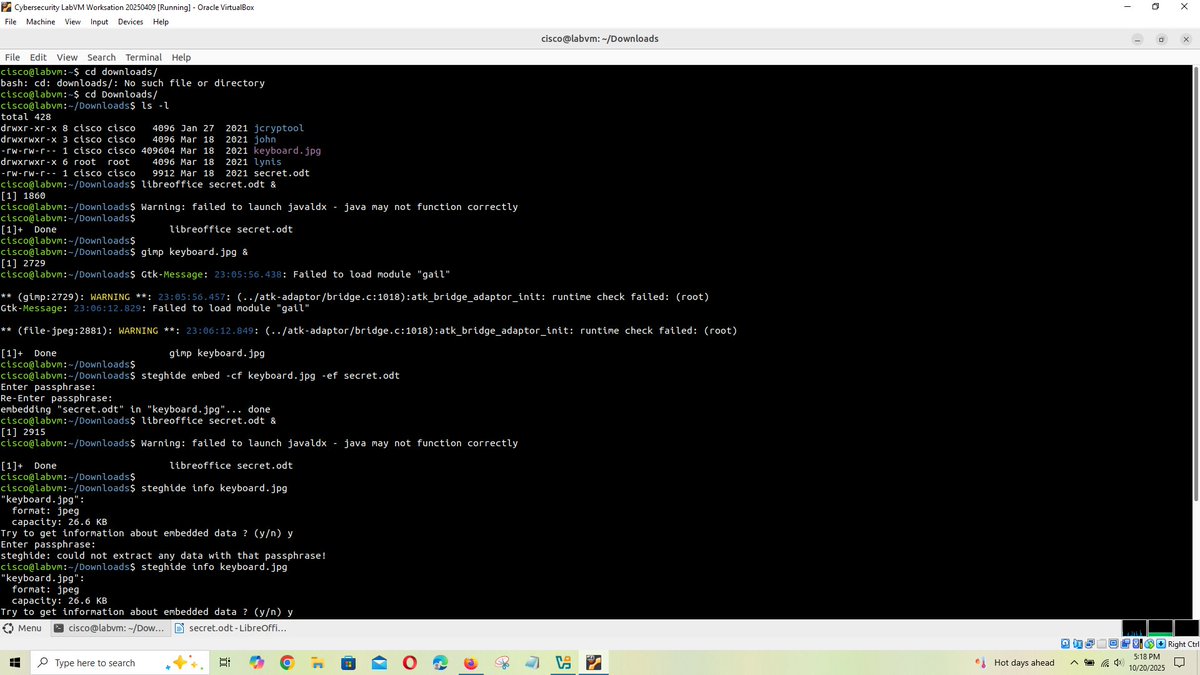
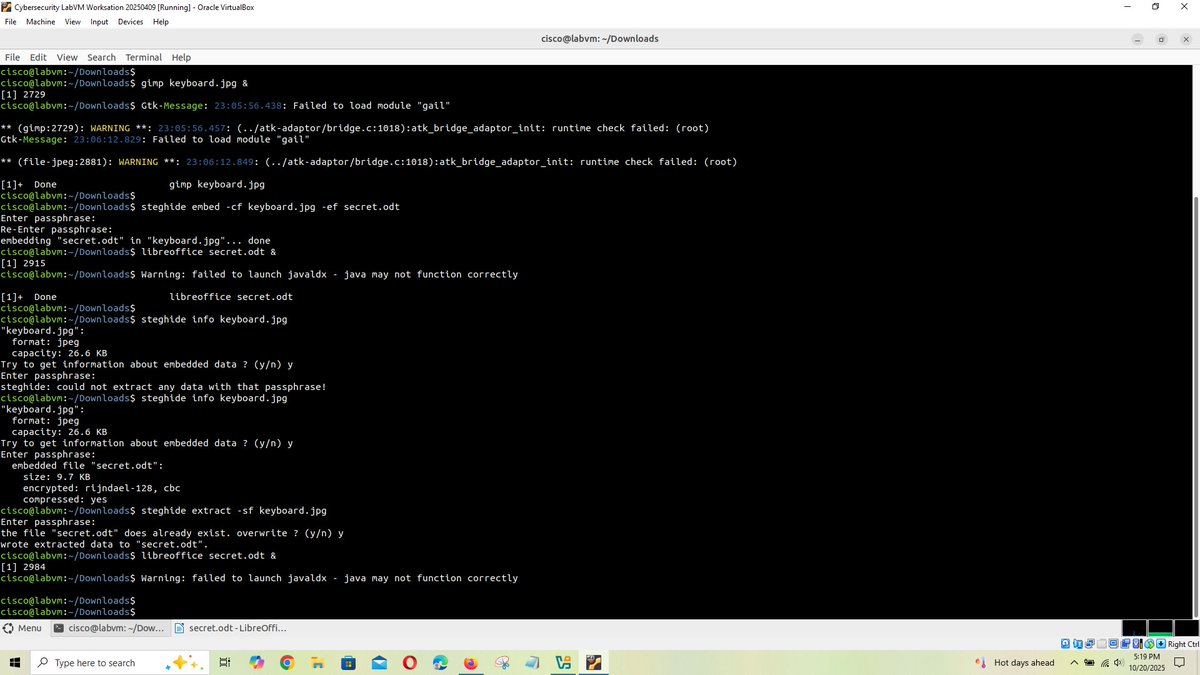
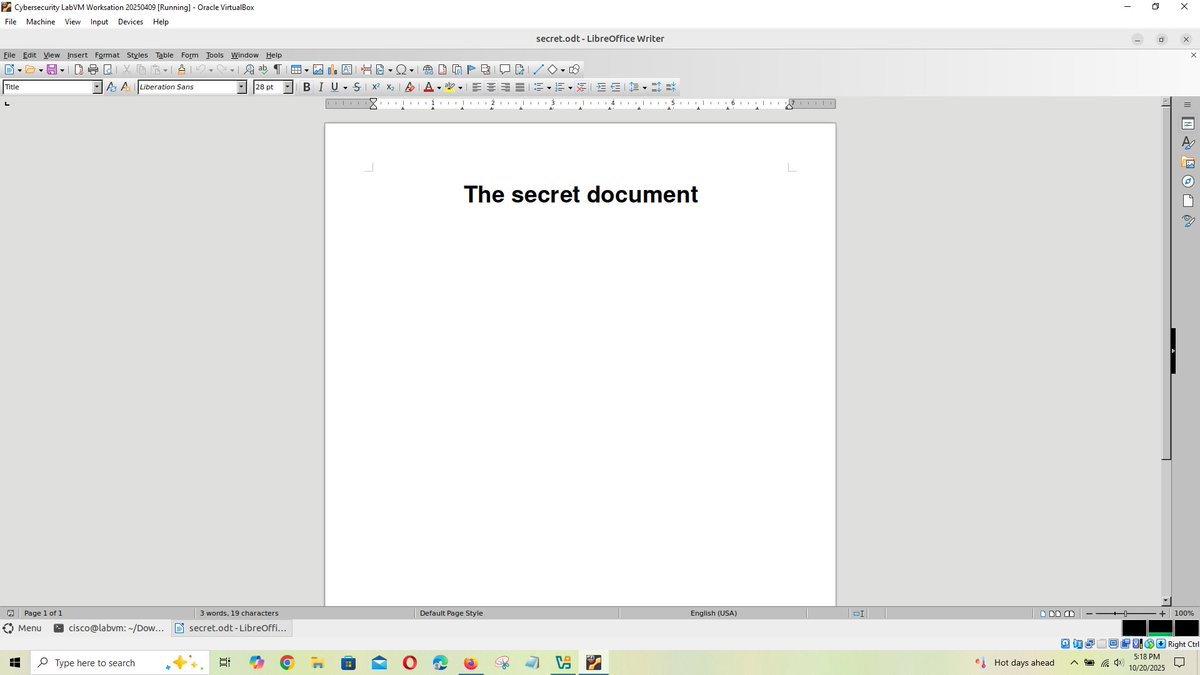
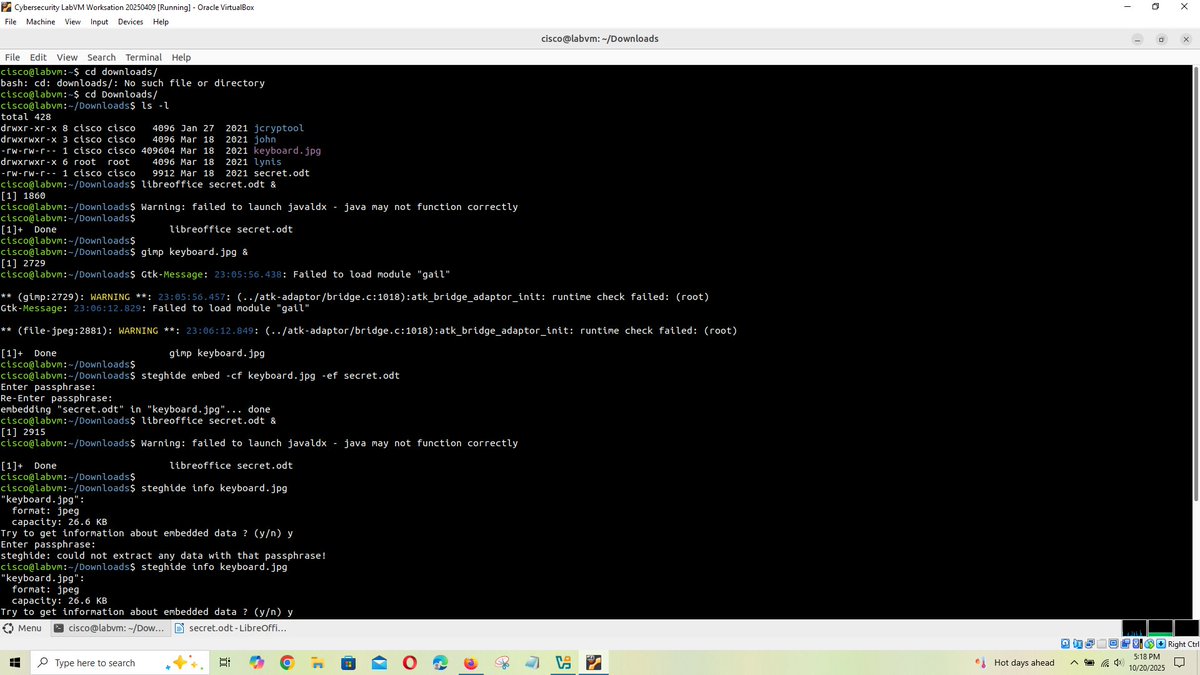
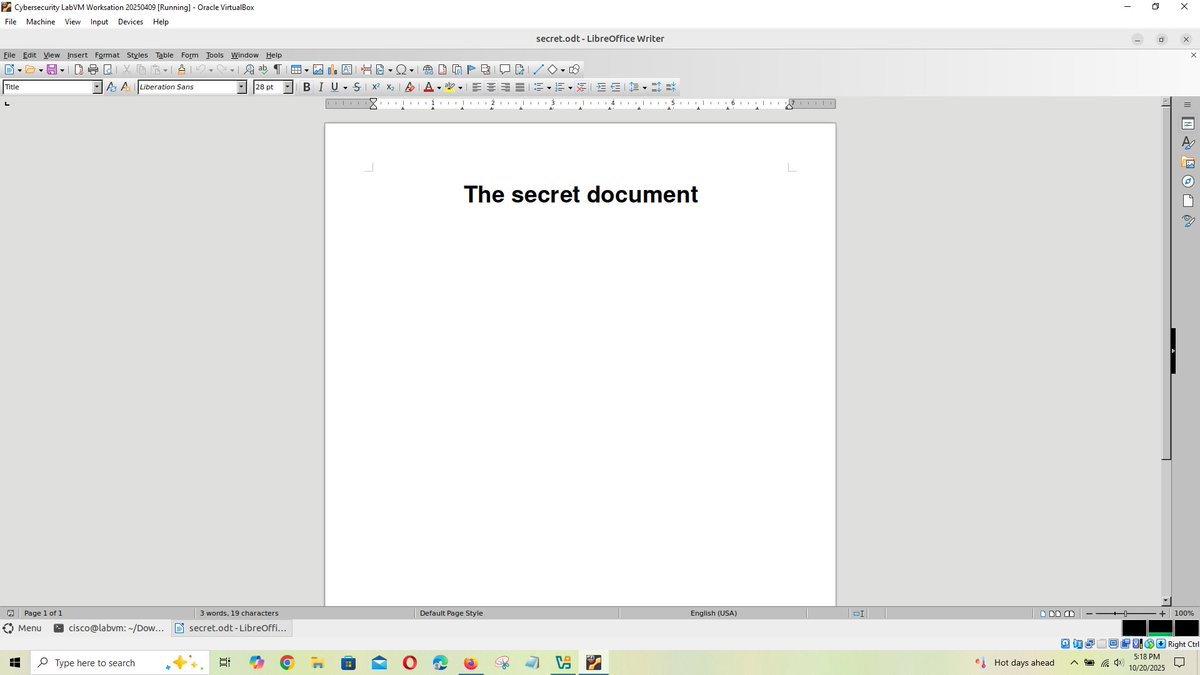
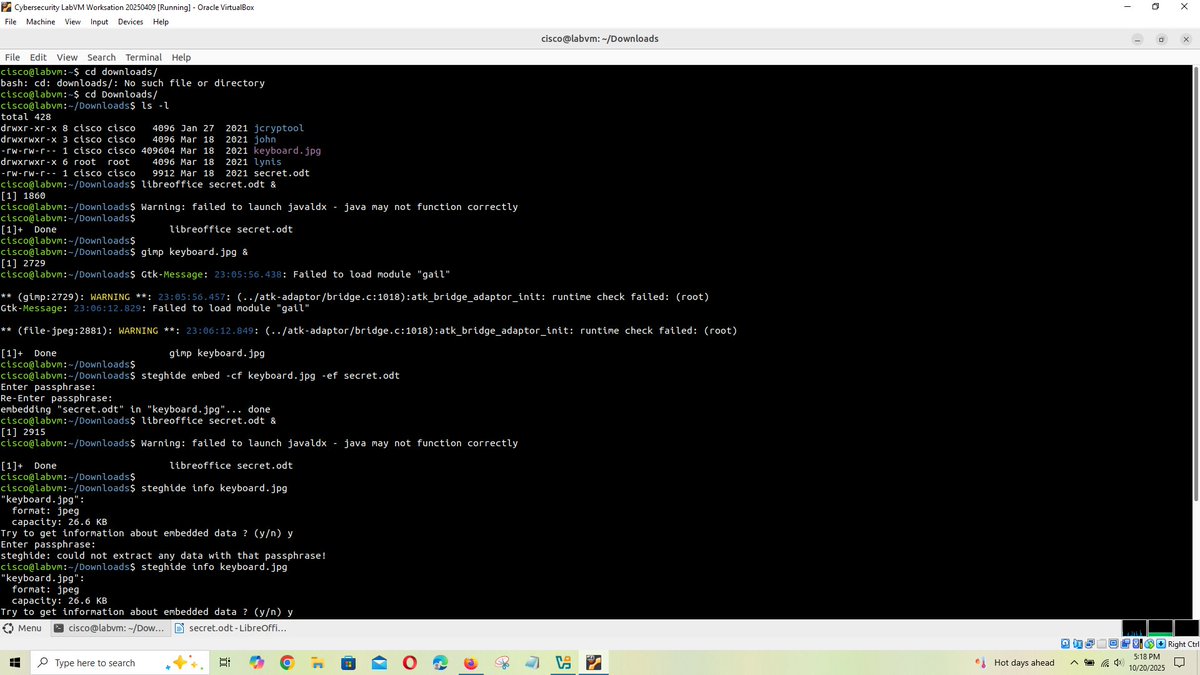
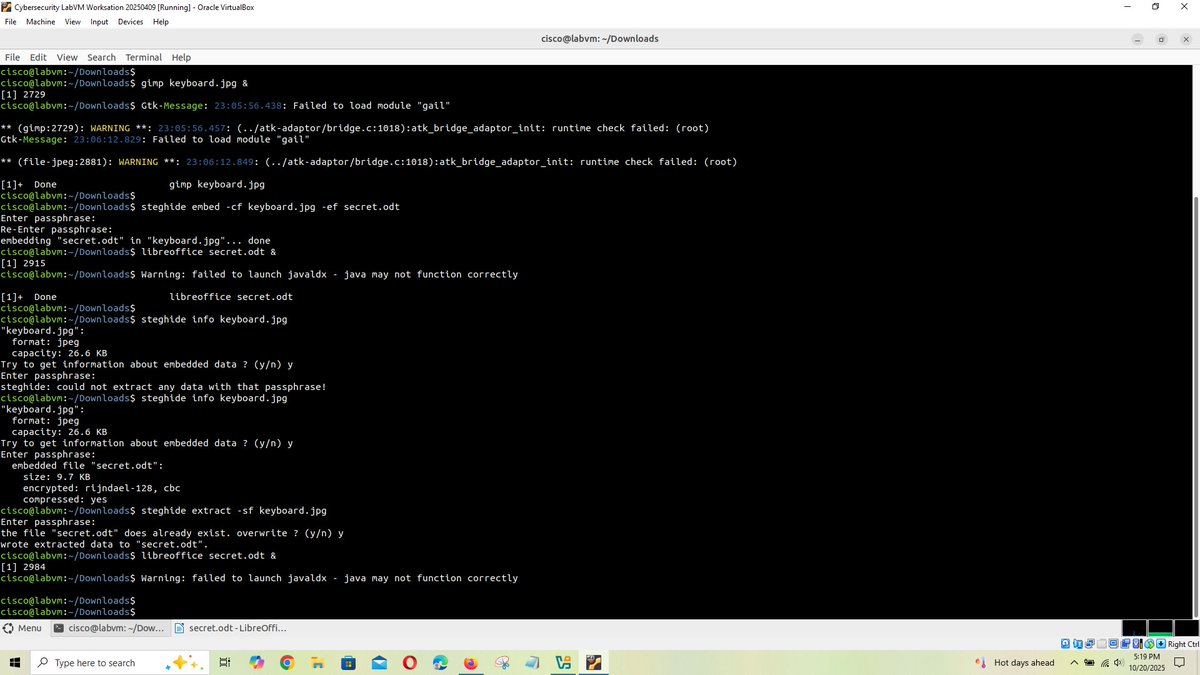
In this lab, I hid a document inside a JPEG image using steganography, making the secret file invisible to normal inspection. This exercise helped me understand how data can be concealed within ordinary files to evade detection. #Cybersecurity #Steganography #DataHiding
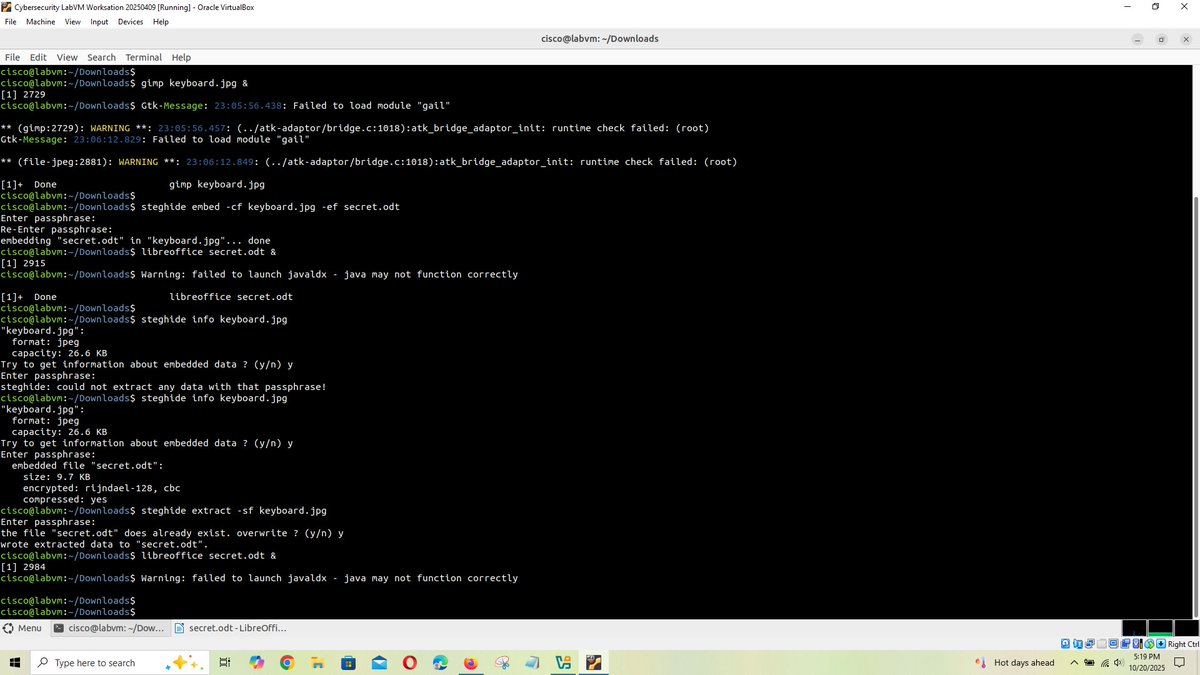
🔥 Read our Paper 📚 Reversible Data Hiding in Encrypted Images with Extended Parametric Binary Tree Labeling 🔗 mdpi.com/2076-3417/13/4… 👨🔬 by Mr. Quan Feng et al. 🏫 Nanchang Hangkong University #imageencryption #DataHiding

#SpecialIssue Data Hiding and Its Applications: Digital Watermarking and Steganography mdpi.com/journal/applsc… Submit your articles before 30 November 2020. #DataHiding #DigitalWatermarking #Steganography #Steganalysis #mdpiapplsci

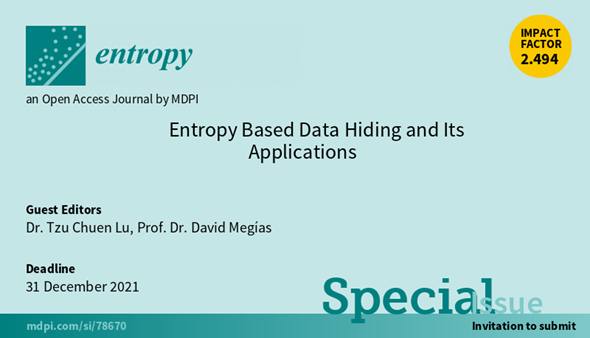
New #SpecialIssue "#Entropy Based #DataHiding and Its Applications", edited by Dr. Tzu Chuen Lu and Prof. Dr. David Megías, with deadline 31 December 2021. We look forward to your submissions! mdpi.com/journal/entrop… #signalprocessing #bigdata #steganography #cryptography
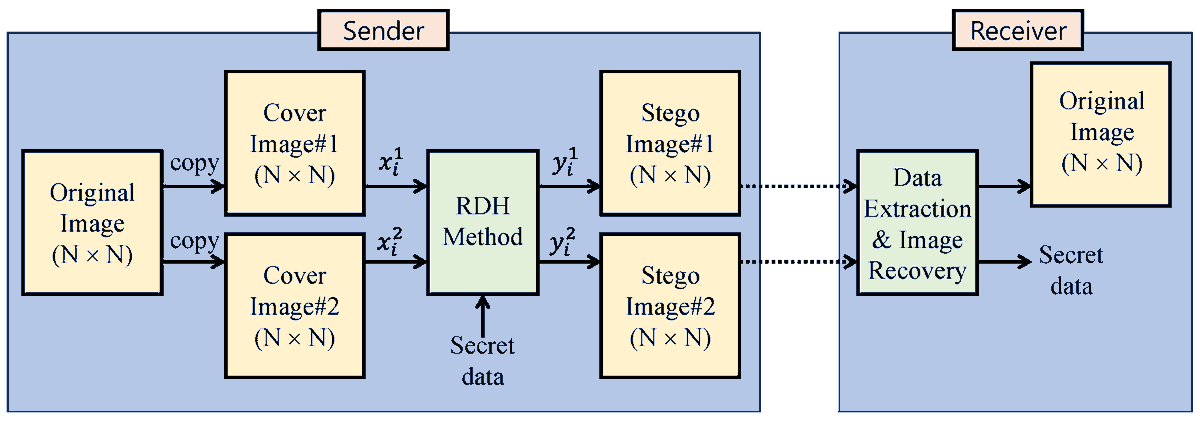
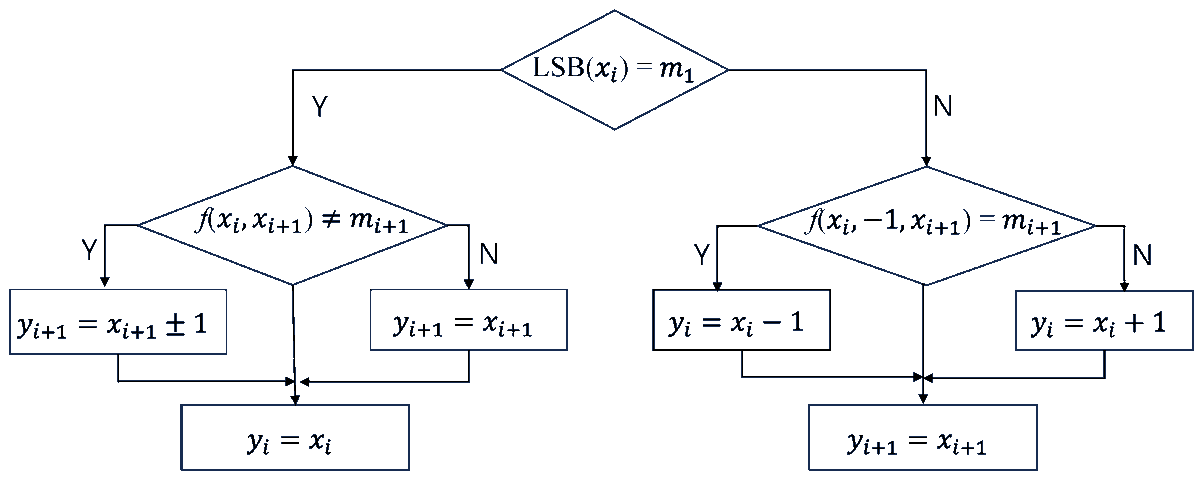
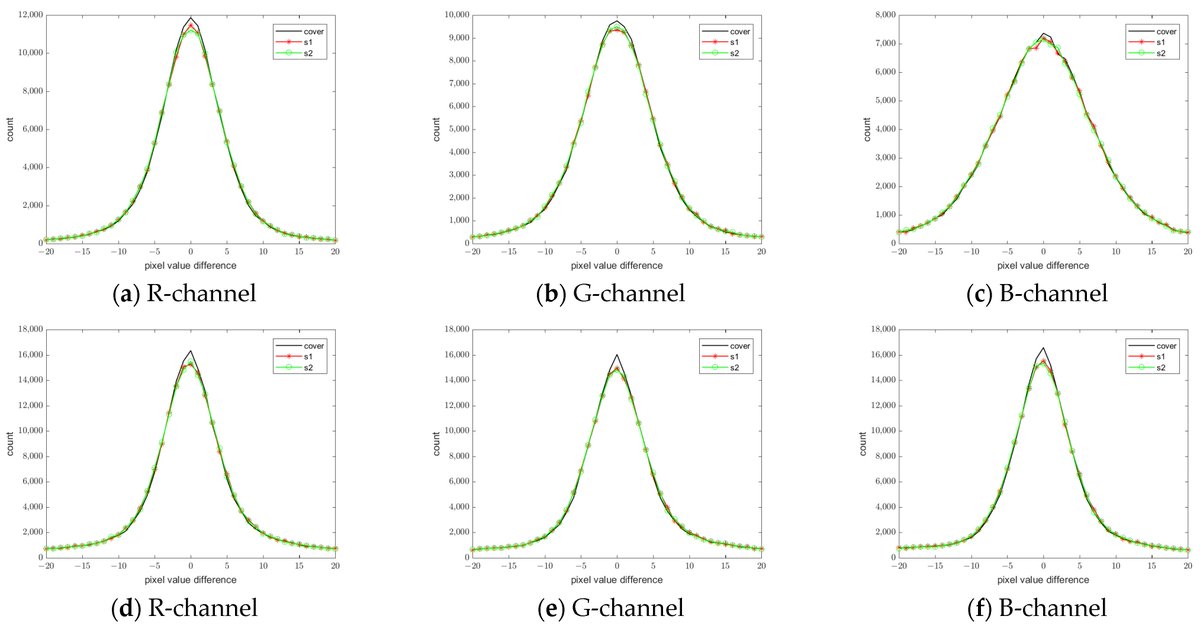
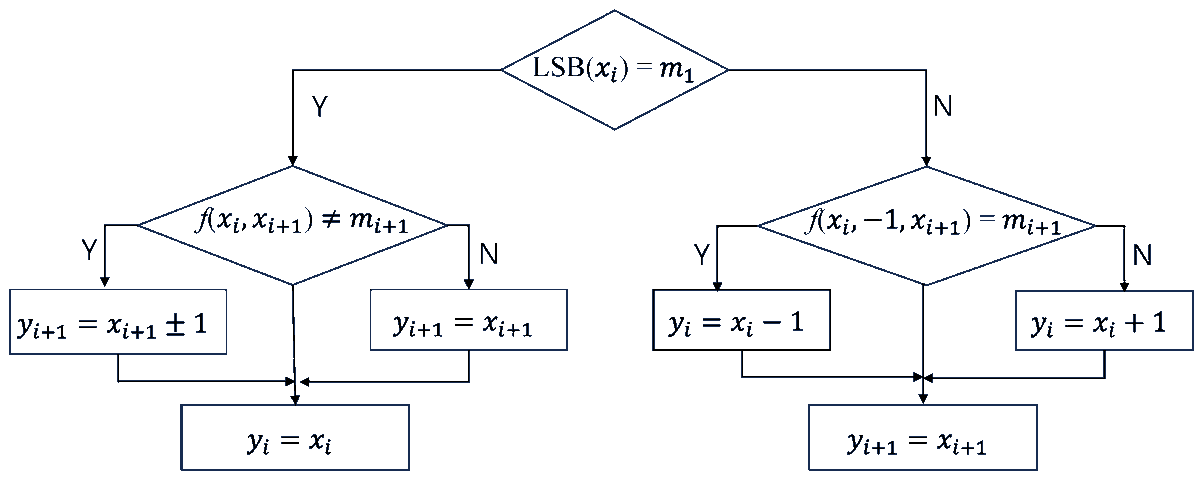
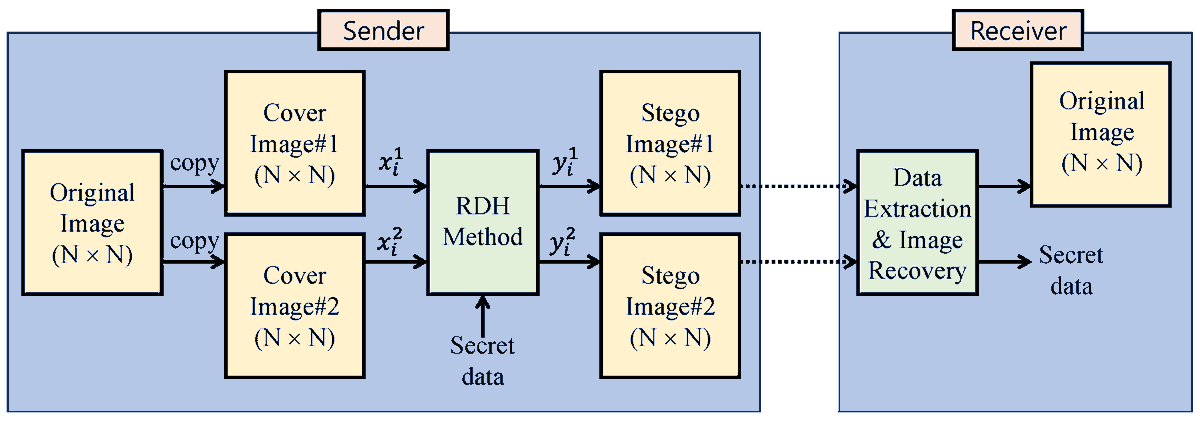
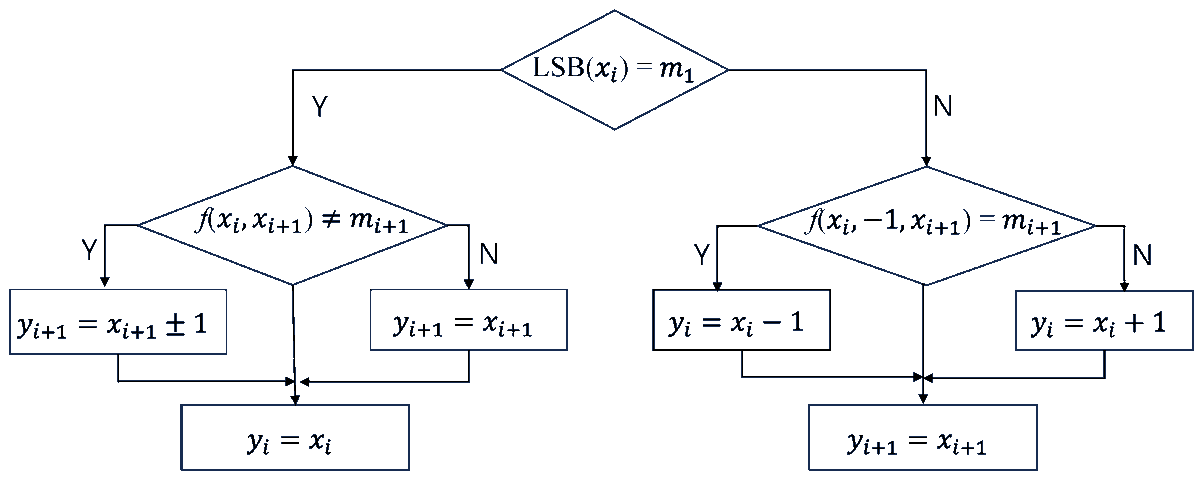
🔥 Read our Highly Cited Paper 📚 Advanced #DualReversible #DataHiding: A Focus on #ModificationDirection and Enhanced #LeastSignificantBit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 Cheonshik Kim et al. 🏫 @SejongU / Andong National University / Nanchang Hangkong University
#mdpientropy Reversible Data Hiding in JPEG Images Using Quantized DC mdpi.com/1099-4300/21/9… #reversible #datahiding #JPEG #DCT coefficients #DC coefficients #entropy
List of steganography software (updated): steganography.daniellerch.me/p/software.html #steganography, #datahiding
🔥 Read our Paper 📚 Advanced Dual Reversible Data Hiding: A Focus on Modification Direction and Enhanced Least Significant Bit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 by Cheonshik Kim et al. #datahiding
Are Stealth ADSs still good to hide malicious EXEs? Check this out if you're interested #DFIR #DataHiding: binary-zone.com/2019/05/24/can…
If anyone wants to research executables running from hidden alternate data streams (ADS), you can find a forensic image now on my website here: bit.ly/2wpr42m #DFIR #DataHiding #ThreatHunting #Dataset #Challenge
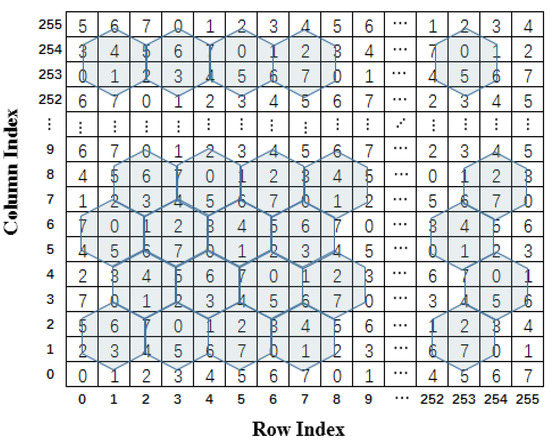
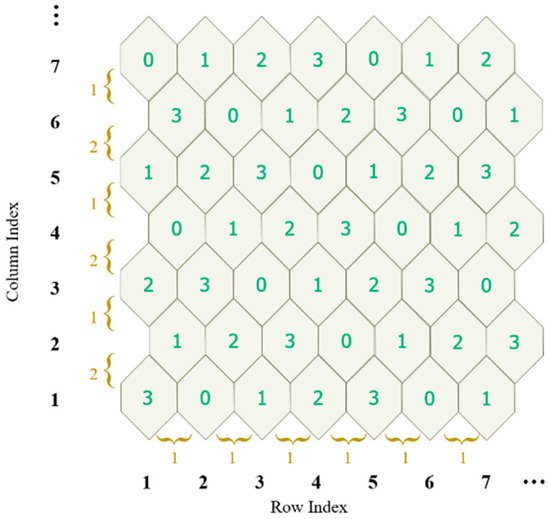
An Efficient #DataHiding Scheme Based on Multidimensional #MiniSuDoKu mdpi.com/1424-8220/20/9… #datahiding #multidimensional #embeddingefficiency
Explore how hackers hide data inside spam emails and the unseen risks it poses to cybersecurity. redsecuretech.co.uk/blog/post/the-… #CyberSecurity #EmailSteganography #DataHiding #SpamEmails #CyberAwareness #InfoSec #DigitalForensics #CyberThreats

Check this newly published article "Enhancing Security in #AugmentedReality Through Hash-Based #DataHiding and Hierarchical Authentication Techniques" at brnw.ch/21wX56r Authors: Chia-Chen Lin et al. #mdpisymmetry #dataintegrity @ComSciMath_Mdpi
In this lab, I hid a document inside a JPEG image using steganography, making the secret file invisible to normal inspection. This exercise helped me understand how data can be concealed within ordinary files to evade detection. #Cybersecurity #Steganography #DataHiding
Steganography can hide C2 commands within SVG files by encoding ASCII codes into geometric properties like cx, cy, and r. SVG's XML format and web use make it ideal for covert data transmission. #DataHiding #CommandControl #InfosecTech ift.tt/S6WewYZ
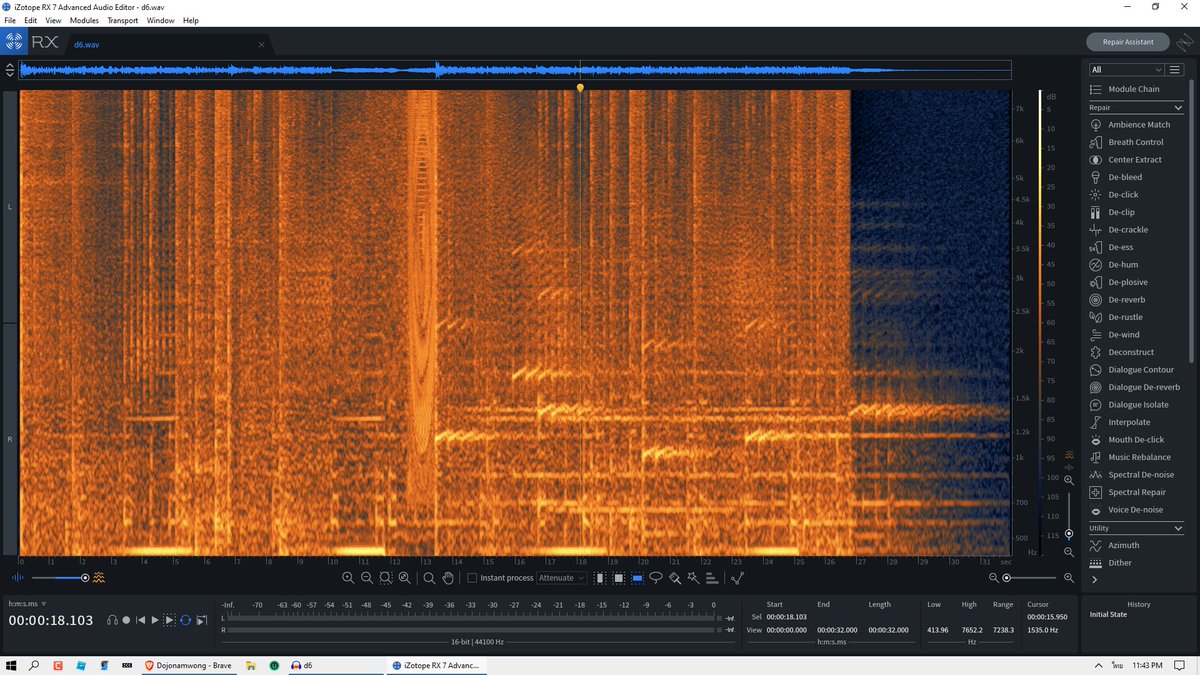
Steganography hides secret data within media files. Techniques include detecting ZIPs in PNGs with binwalk, cracking passwords via John the Ripper, and decoding messages using CyberChef and Unicode methods. #SteganographyTech #DataHiding #TryHackMe ift.tt/7jiXhbp
hendryadrian.com
Stegoint: Where is steganography | TryHackMe CTF
This article explains how steganography techniques are used to hide information within media files like images and text. It details a practical walkthrough of detecting and extracting hidden data...
🔔 New Published Papers of #MDPIfutureinternet Title: A High-Capacity Reversible Data Hiding Scheme for Encrypted Hyperspectral Images Using Multi-Layer MSB Block Labeling and ERLE Compression Please read at: mdpi.com/1999-5903/17/8… #datahiding #encryptedhyperspectralimages
🔥 Read our Highly Cited Paper 📚 Advanced #DualReversible #DataHiding: A Focus on #ModificationDirection and Enhanced #LeastSignificantBit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 Cheonshik Kim et al. 🏫 @SejongU / Andong National University / Nanchang Hangkong University
Just wanna state here that I can't access quoted tweet, so if you think I haven't replied for some reason, you're wrong. I can't see it. And this is very anti democratic #DataHiding
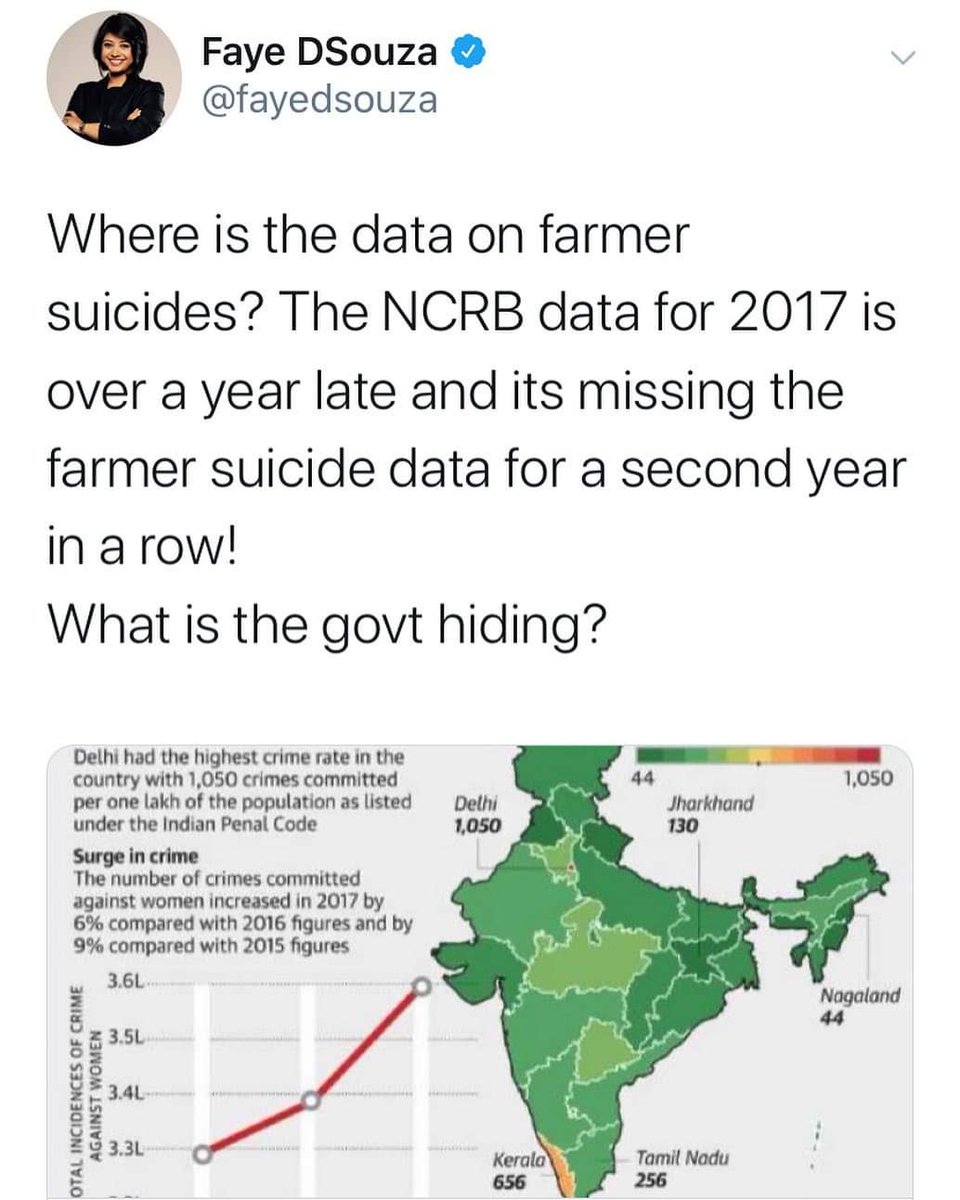
चुनाव आयोग डाटा छुपा रहा है | RNI News #ElectionCommission #DataHiding #ElectionTransparency #IndiaElections #DemocracyAtRisk #RNInews #ElectionData #VotingRights #IndiaPolitics #ElectionWatch
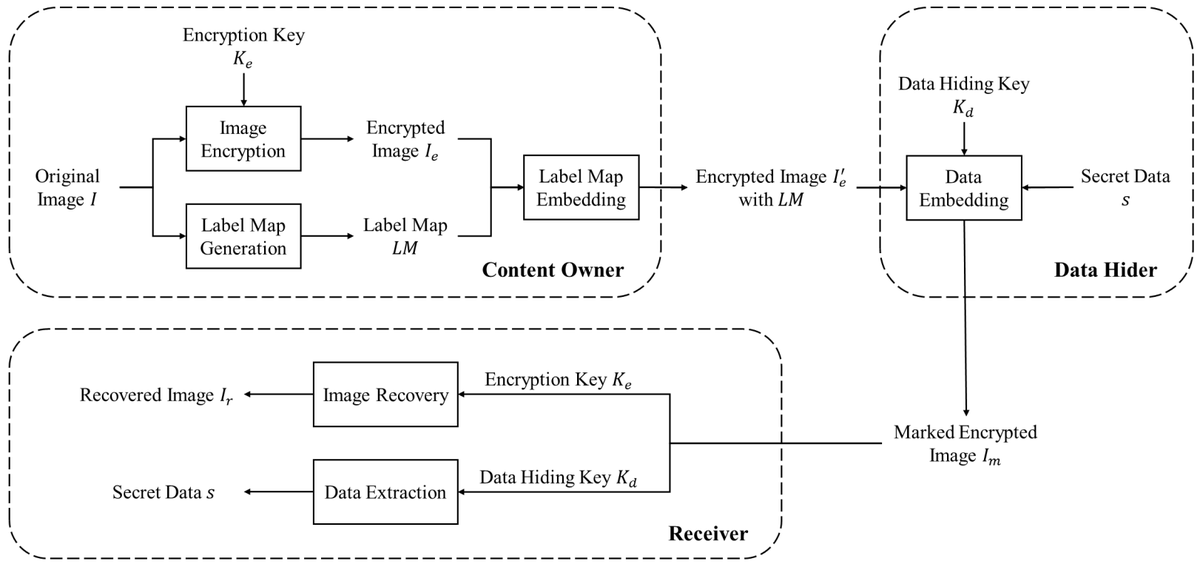
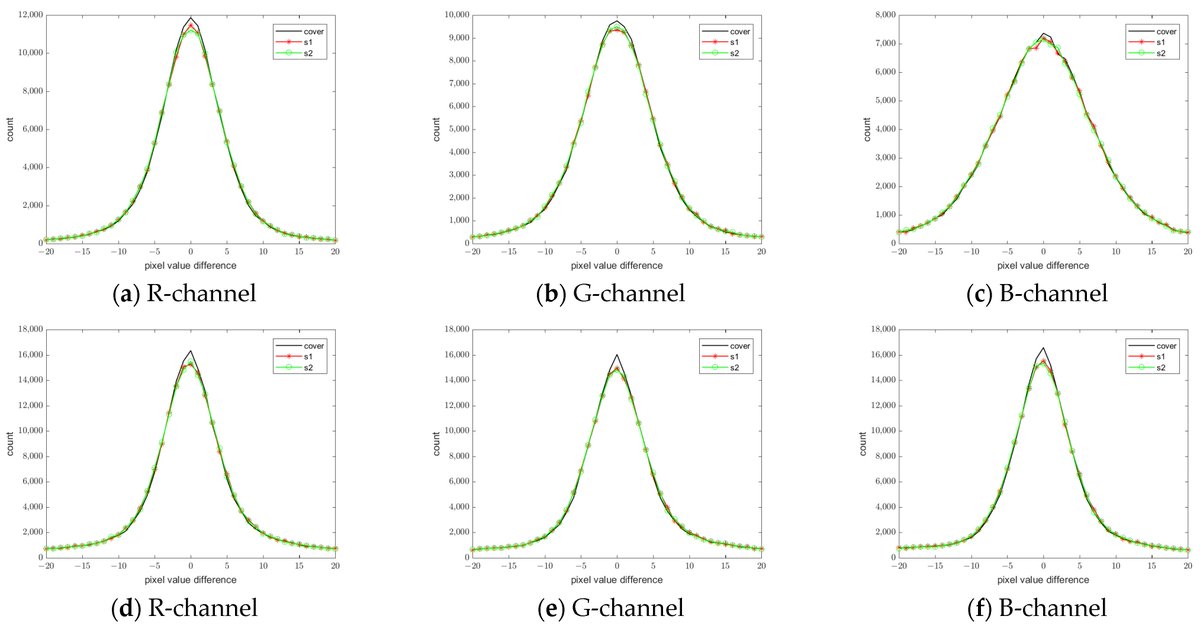
🔥 Read our Paper 📚 Multi-Hider Reversible #DataHiding Using a Weighted #ColorTransfer and #ModulusOperation 🔗 mdpi.com/2076-3417/13/2… 👨🔬 by Ku-Sung Hsieh and Chung-Ming Wang 🏫 National Chung Hsing University
5/20: 🔐 Public vs Private Public = open access 🛣️ (methods). Private = locked vault 🔒 (data). Best practice: private attributes, public methods! #DataHiding #BestPractices
📣 New Podcast! "Secrets Hidden in PDF Pages" on @Spreaker #cryptography #cybersecurity #datahiding #digitalprivacy #pdfsecurity #secretsharing #steganography spreaker.com/episode/secret…

spreaker.com
Spreaker Podcasts
Secrets Hidden in PDF Pages
🔥 Read our Paper 📚 Reversible Data Hiding in Encrypted Images with Extended Parametric Binary Tree Labeling 🔗 mdpi.com/2076-3417/13/4… 👨🔬 by Mr. Quan Feng et al. 🏫 Nanchang Hangkong University #imageencryption #DataHiding

Looks like someone’s trying to avoid their data contribution duties! 😂 Don’t worry, with PublicAI, we’ll make it worth your while! #DataHiding
Looks like someone’s trying to avoid the spotlight! 😂 Maybe they need to contribute some data to PublicAI and earn a little fame! #DataHiding
🔥 Read our Paper 📚 Advanced Dual Reversible Data Hiding: A Focus on Modification Direction and Enhanced Least Significant Bit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 by Cheonshik Kim et al. #datahiding
#Steganography is hiding data within other files in a way that the data is not visible. An attacker can hide a message within an image by altering some pixels. Doing so, the attacker can transmit data without triggering #DLP controls. #DataHiding #Cybersecurity #InfoSec
🔔🔔🔔 #MDPIfutureinternet [New Published Papers in 2024] Title: Reversible Data Hiding in Encrypted 3D Mesh Models Based on Multi-Group Partition and Closest Pair Prediction mdpi.com/1999-5903/16/6… reversible #datahiding; #3Dmeshmodels; #cloudservices @ComSciMath_Mdpi
![FutureInternet6's tweet image. 🔔🔔🔔 #MDPIfutureinternet [New Published Papers in 2024]
Title: Reversible Data Hiding in Encrypted 3D Mesh Models Based on Multi-Group Partition and Closest Pair Prediction
mdpi.com/1999-5903/16/6…
reversible #datahiding; #3Dmeshmodels; #cloudservices
@ComSciMath_Mdpi](https://pbs.twimg.com/media/GQfs6G3aIAIDEMw.jpg)
Check this newly published article "Enhancing Security in #AugmentedReality Through Hash-Based #DataHiding and Hierarchical Authentication Techniques" at brnw.ch/21wX56r Authors: Chia-Chen Lin et al. #mdpisymmetry #dataintegrity @ComSciMath_Mdpi
Mr. Hide, a new steganography tool for hiding data into images. steganography.daniellerch.me/p/mr-hide.html #steganography #datahiding
In this lab, I hid a document inside a JPEG image using steganography, making the secret file invisible to normal inspection. This exercise helped me understand how data can be concealed within ordinary files to evade detection. #Cybersecurity #Steganography #DataHiding
🛰️ Rule 5: Restrict Data Scope: NASA supports the idea of data hiding or declaring variables as they're used at the lowest scope possible. This approach reduces the amount of code that can access those variables. #DataHiding #Coding
🔥 Read our Highly Cited Paper 📚 Advanced #DualReversible #DataHiding: A Focus on #ModificationDirection and Enhanced #LeastSignificantBit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 Cheonshik Kim et al. 🏫 @SejongU / Andong National University / Nanchang Hangkong University
Explore how hackers hide data inside spam emails and the unseen risks it poses to cybersecurity. redsecuretech.co.uk/blog/post/the-… #CyberSecurity #EmailSteganography #DataHiding #SpamEmails #CyberAwareness #InfoSec #DigitalForensics #CyberThreats

🔥 Read our Paper 📚 Reversible Data Hiding in Encrypted Images with Extended Parametric Binary Tree Labeling 🔗 mdpi.com/2076-3417/13/4… 👨🔬 by Mr. Quan Feng et al. 🏫 Nanchang Hangkong University #imageencryption #DataHiding

... come rendermi felice | ... how to make me happy | ... 私を幸せにする方法 #security #networking #datahiding #cryptography
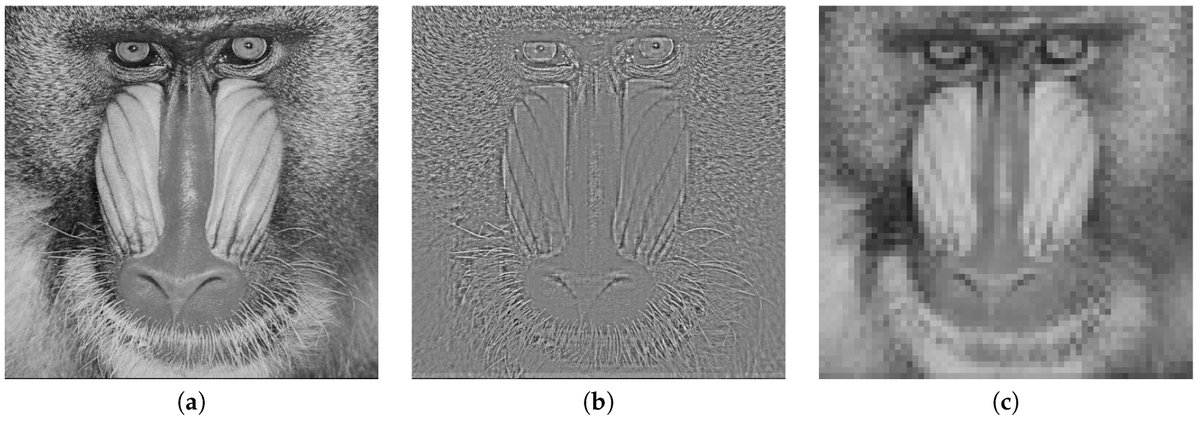
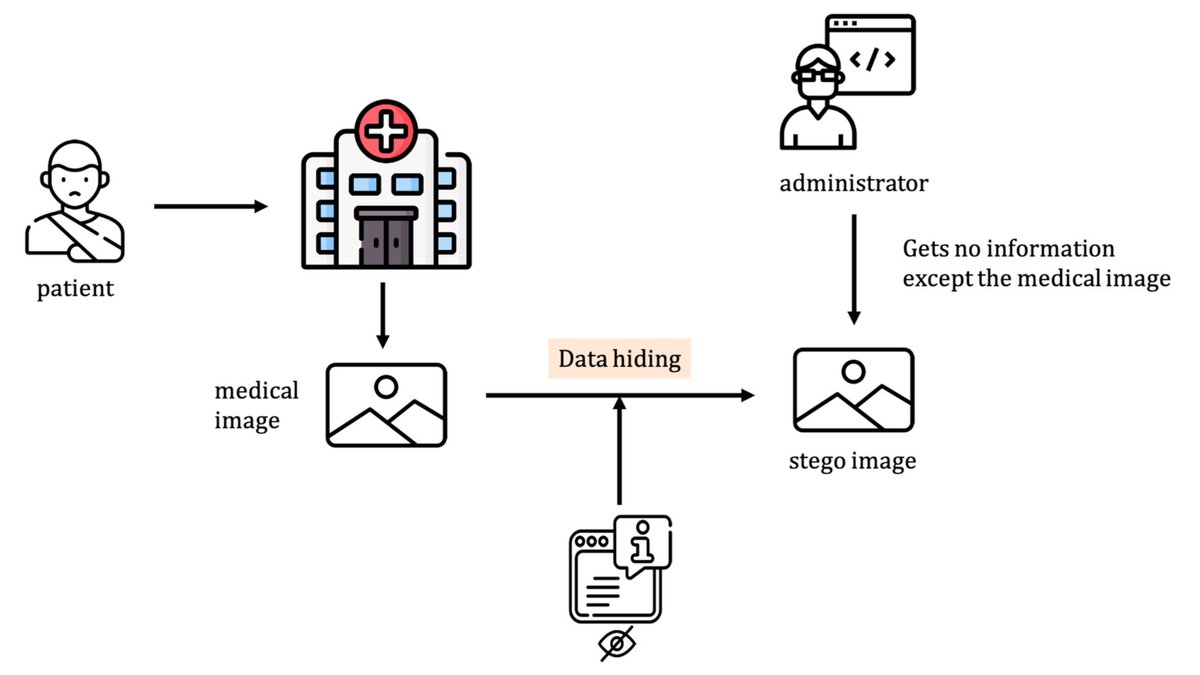
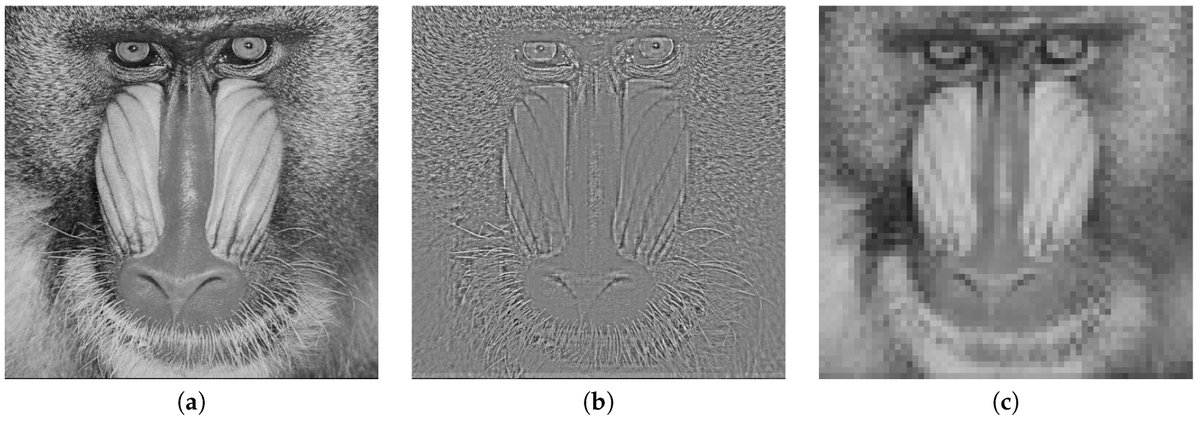
Two-Bit Embedding Histogram-Prediction-Error Based Reversible #DataHiding for #MedicalImages with Smooth Area mdpi.com/1355846 by Ja-Ling Wu from @q_nationaltaiwa #informationhiding #steganography #watermarking #steganalysis #cryptanalysis #deeplearning
#SpecialIssue Data Hiding and Its Applications: Digital Watermarking and Steganography mdpi.com/journal/applsc… Submit your articles before 30 November 2020. #DataHiding #DigitalWatermarking #Steganography #Steganalysis #mdpiapplsci

🔥 Read our Paper 📚 Advanced Dual Reversible Data Hiding: A Focus on Modification Direction and Enhanced Least Significant Bit (LSB) Approaches 🔗 mdpi.com/2076-3417/14/6… 👨🔬 by Cheonshik Kim et al. #datahiding
🔥 Read our Paper 📚 Multi-Hider Reversible #DataHiding Using a Weighted #ColorTransfer and #ModulusOperation 🔗 mdpi.com/2076-3417/13/2… 👨🔬 by Ku-Sung Hsieh and Chung-Ming Wang 🏫 National Chung Hsing University
#mdpientropy Reversible Data Hiding in JPEG Images Using Quantized DC mdpi.com/1099-4300/21/9… #reversible #datahiding #JPEG #DCT coefficients #DC coefficients #entropy
New #SpecialIssue "#Entropy Based #DataHiding and Its Applications", edited by Dr. Tzu Chuen Lu and Prof. Dr. David Megías, with deadline 31 December 2021. We look forward to your submissions! mdpi.com/journal/entrop… #signalprocessing #bigdata #steganography #cryptography
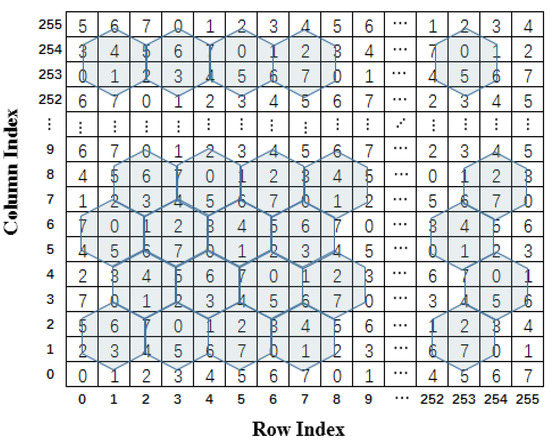
An Efficient #DataHiding Scheme Based on Multidimensional #MiniSuDoKu mdpi.com/1424-8220/20/9… #datahiding #multidimensional #embeddingefficiency
Data Hiding Based on a Two-Layer Turtle Shell Matrix mdpi.com/2073-8994/10/2… #datahiding @MDPIOpenAccess Providence University Chia-Chen Lin
#AppliedSciences #Books #DataHiding and Its Applications: Digital #Watermarking and #Steganography 🎓 Prof. Dr. David Megías, Prof. Dr. Wojciech Mazurczyk and Prof. Dr. Minoru Kuribayashi 🔗mdpi.com/books/pdfview/… #mdpiapplsci #openaccess
Something went wrong.
Something went wrong.
United States Trends
- 1. Good Sunday 56.2K posts
- 2. Stockton 27.3K posts
- 3. #ViratKohli 40.4K posts
- 4. #BNewEraBirthdayConcert 1.03M posts
- 5. Auburn 41.2K posts
- 6. #INDvSA 65.6K posts
- 7. Bama 29.7K posts
- 8. #JimmySeaFanconD2 293K posts
- 9. Duke 32.6K posts
- 10. Ole Miss 38.6K posts
- 11. PERTHSANTA LUMINOUS SKIN 337K posts
- 12. BECKY BIRTHDAY CONCERT 972K posts
- 13. #NIVEASkinGlowxPerthSanta 391K posts
- 14. Notre Dame 25.9K posts
- 15. Miami 141K posts
- 16. Lane Kiffin 48.8K posts
- 17. Ewing 1,379 posts
- 18. Stanford 9,999 posts
- 19. Austin Theory 5,545 posts
- 20. Japan Cup 11.7K posts