#cryptography search results
🚀Latest in #Electronics! 📲 Investigating Post-Quantum #Cryptography to Secure Transmitted Data via #MobileCommunication 🔗Read at: mdpi.com/2079-9292/15/6… Authors from @singaporetech, WizVision Pte Ltd #PostQuantumCryptography #5G #PQC #Kyber #QuantumComputing #cybersecurity

⚛️ BREAKING: Quantum just cracked a 15-bit Bitcoin-style key 👀 BTC isn’t at risk yet… but the countdown is real ⏳ 15-bit today. 256-bit is the prize. Experts: prep window may be 3–5 years 🚨 Not panic. Just a ticking clock. #Bitcoin #QuantumComputing #Cryptography
Discover how cryptography turned the tide in history! Unlock the secrets behind hidden messages and intelligence. #cryptography #historyfacts #spynetworks #militarystrategy #hiddenhistory
@ritualnet Ritual is a lab for autonomous intelligence The next markets won't be built by humans alone. #Cryptography #Privacy #Blockchain #Crypto

#Quantum-ready? The new libzupt package brings post-quantum #cryptography to #openSUSE #Leap and #Tumbleweed using ML-KEM-768 + X25519 hybrid #encryption. More about being 🔐🐧 🦎 #Linux news.opensuse.org/2026/04/28/qua…
Google starts preparing Android for #PostQuantum #Cryptography era | Neowin share.google/9qKbI9KRe0I97L…
Quantum is approaching fast: algorithms like Shor’s will break today’s public-key #cryptography that underpins #DigitalSecurity ➡ bit.ly/4bEpZZ6 Now’s the time to inventory where crypto is used, prioritize long-life data, and begin the transition. Not sure where to
A new Special Issue opens for submission! Title: Applied Symmetry in #Cryptography and #InformationSecurity Editor: Funminiyi Olajide, Nemitari Ajienka and Tawfik Al-Hadhrami Details: brnw.ch/21x1MdN #callforpapers #mdpisymmetry #cloudsecurity @penn_state @NottmTrentUni

Vigenere Square Cryptography Tabula Rasa Lamp: zazzle.com/vigenere_squar… #Vigeneresquare #cryptography #cryptographer #TabulaRecta #encryption #Caesarcipher #polyalphabeticsubstitution #decryption #Vigeneretable #encrypt #cipher #TabulaRasa
#Google Wants to Transition to Post-Quantum #Cryptography by 2029 securitytc.com/TRtxsh
schneier.com
Google Wants to Transition to Post-Quantum Cryptography by 2029 - Schneier on Security
Google says that it will fully transition to post-quantum cryptography by 2029. I think this is a good move, not because I think we will have a useful quantum computer anywhere near that year, but...
npmjs.com/package/lvthn the leviathan cli crypto tool has been updated w/ the 2.1.0 fixes and enhancements. bun / npm i -g lvthn averages ~1gb per sec using serpent-256, nearly half that using xchacha20 ;D #crypto #cryptography #cli #bunjs #bun #npm #terminal #term
Invisible math shield #privacy #cryptography #blockchain The Crowd That Hides You This Math Trick Makes You Invisible Online 😳 What if you could send a message online… and no one could trace it back to you? 🤯 This is the power of ring signatures — a cryptographic method...

A new German-Singaporean research consortium aims to develop an #OpenSource post-quantum-secure processor integrating #QuantumResistant #cryptography at the hardware level: go.tum.de/123688 #Cybersecurity #QuantumComputing 📷A.Eckert
ConnectWise patched a critical flaw (CVE-2026-3564) in ScreenConnect before version 26.1 allowing attackers to extract ASP.NET machine keys, enabling session hijacking and privilege escalation. #ScreenConnect #Cryptography #USA ift.tt/gJYz7AL
Quantum #Cryptography Pioneers Win Turing Award buff.ly/ZvgcJpU v/ @QuantaMagazine #QuantumComputing Cc @Nicochan33 @timo_vi @Ym78200 @mvollmer1 @Khulood_Almani @Delshur

Feels like I being punked by the #cryptography world. I guess that's what happens when specialized training and high dollar salaries come up short swinging. #Money decides who you are - Words #freedom never said... #USA #Politics #Codes #ZodiacKiller #California #SFPD #FBI
The @Arc #blockchain team from @Circle announced a transition strategy to post-quantum #cryptography, securing wallets, infrastructure, and validators, without forcing user migration. More details on #CPMedia 🔗 coinspaidmedia.com/news/arc-block…

How organizations can make a successful transition to Post-Quantum #Cryptography buff.ly/G9gfy9X @CIOonline @Zscaler #tech #cybersecurity #data #datasecurity #encryption #PQC #QDay #leadership #CIO #CTO #CDO #CISO #CEO #business #quantumcomputing #HNDL

Top #Cryptography and #CyberSecurity Books to Read! #BigData #Analytics #DataScience #IoT #IIoT #Python #RStats #TensorFlow #JavaScript #ReactJS #CloudComputing #Serverless #DataScientist #Linux #Books #Programming #Coding #100DaysofCode geni.us/CyberSecurity-…


The Financial Supervisory Commission is urging financial institutions to address emerging post-quantum #cryptography and #AI #security challenges. Read more: rti.org.tw/en/news?uid=3&…

Quantum #Cryptography Pioneers Win Turing Award buff.ly/ZvgcJpU v/ @QuantaMagazine #QuantumComputing Cc @Nicochan33 @timo_vi @Ym78200 @mvollmer1 @Khulood_Almani @Delshur

Discover how cryptography turned the tide in history! Unlock the secrets behind hidden messages and intelligence. #cryptography #historyfacts #spynetworks #militarystrategy #hiddenhistory
Feels like I being punked by the #cryptography world. I guess that's what happens when specialized training and high dollar salaries come up short swinging. #Money decides who you are - Words #freedom never said... #USA #Politics #Codes #ZodiacKiller #California #SFPD #FBI
Invisible math shield #privacy #cryptography #blockchain The Crowd That Hides You This Math Trick Makes You Invisible Online 😳 What if you could send a message online… and no one could trace it back to you? 🤯 This is the power of ring signatures — a cryptographic method...

@ritualnet Ritual is a lab for autonomous intelligence The next markets won't be built by humans alone. #Cryptography #Privacy #Blockchain #Crypto

npmjs.com/package/lvthn the leviathan cli crypto tool has been updated w/ the 2.1.0 fixes and enhancements. bun / npm i -g lvthn averages ~1gb per sec using serpent-256, nearly half that using xchacha20 ;D #crypto #cryptography #cli #bunjs #bun #npm #terminal #term
Vigenere Square Cryptography Tabula Rasa Lamp: zazzle.com/vigenere_squar… #Vigeneresquare #cryptography #cryptographer #TabulaRecta #encryption #Caesarcipher #polyalphabeticsubstitution #decryption #Vigeneretable #encrypt #cipher #TabulaRasa
⚛️ BREAKING: Quantum just cracked a 15-bit Bitcoin-style key 👀 BTC isn’t at risk yet… but the countdown is real ⏳ 15-bit today. 256-bit is the prize. Experts: prep window may be 3–5 years 🚨 Not panic. Just a ticking clock. #Bitcoin #QuantumComputing #Cryptography
ZK proofs will erase traceable wealth. 🔮 Tomorrow's finance runs on zero-knowledge: transactions verified, senders invisible. Trustless anonymity becomes protocol standard. #ZKProof #Cryptography #Privacy #DeFi

Privacy contracts are rising. Tip: ZK proofs hide values without revealing logic. 🕶️ Zero-knowledge shifts DeFi from surveillance to sovereignty. Execute privately, settle publicly. #ZKProof #Cryptography #Privacy #DeFi

مفاتيح التشفير لها Life Cycle لازم تفهمه كويس جدا لحماية المفاتيح المسئولة عن حماية البيانات المشفرة #cryptography #encryption #cipher #cybersecurity #infosec #تشفير #الامن_السيبراني youtu.be/1rb4LtFyTlU

youtube.com
YouTube
KF-Cipher for Cyber Security
🔐 Cybersecurity Engineer @ Intellectt 💰 C2C Rate 📍 Remote (Global) ⏱ Full-time • Lead IBM Quantum-Safe & Cryptography projects • Manage Palo Alto Firewalls & discovery tools Comment 'JOBS' to apply! #Cybersecurity #Cryptography #InfoSec
Stage314 completed. Signed verification is now publicly exposed. Anyone can: - View the decision - Verify the signature - Reproduce the result Verification → Responsibility → Public trust #security #cryptography #verification #trust #githubpages mokkunsuzuki-code.github.io/stage314/
Stage313 completed. Verification is no longer just computed. It is explicitly approved and cryptographically signed. "I approve this verification result as accept." From verification → to accountability. #security #cryptography #verification #gpg #trust #digitalsignature
Legacy ECDSA will fail against 1,200 logical qubits. @quipnetwork utilizes WOTS+ (Winternitz One-Time Signature plus) to ensure your digital identity remains unforgeable. Stay safe in the post-quantum world. 🛡️🏛️ #Cryptography #PQC
Privacy smart contracts are rising. Thread. 🔒 Zero-knowledge proofs hide values while proving truth. No trust needed. #ZKProof #Cryptography #Privacy #DeFi

Cipher Zenith uses NIST's best: 🔑 ML-KEM-1024 (Key Exchange) ✍️ ML-DSA-87 (Signatures) 🛡️ ChaCha20-Poly1305 + Argon2id Quantum-resistant TODAY. All local, offline. Protect your data for tomorrow! ⚛️ #PostQuantum #Cryptography #CipherZenith
"Acabo de publicar en open source EPR-2 QaaS Blockchain — una API de criptografía post-cuántica para blockchain que reemplaza ECDSA con ML-DSA-65 (NIST FIPS 204). Resistente al Algoritmo de Shor. MIT license. github.com/Babayagga-bite… #blockchain #cryptography #web3 #postcuantum
"AQUI DÁ A NOTÍCIA: 🇺🇸 O Senado americano aprovou unanime resolução proibindo membros de negociar em mercados de predição. " #Cryptography #Regulation #Política
Complete Cryptography and Ethical Hacking Masterclass 2025 ⏱️ 5.0 hours ⭐ 4.50 👥 2,092 🔄 Nov 2025 💰 $14.99 → 100% OFF comidoc.com/udemy/complete… #CyberSecurity #EthicalHacking #Cryptography #udemy

Quantum Cybersecurity Risks Rise as Organizations Prepare for Post-Quantum Cryptography cysecurity.news/2026/03/quantu… #Computing #Cryptography #cryptographyrisk
Coinbase CEO Says Quantum Threat to Crypto Is Manageable cysecurity.news/2026/03/coinba… #Blockchain #cryptocurrency #Cryptography

Paris, France – April 2025: Zama, a prominent open-source cryptography developer, faces a significant security incident as hackers compromise the X account of Chief Operating Officer Jeremy Bradley. #BLOCKCHAIN #cryptography #Security #SocialMedia #Zama bitcoinworld.co.in/zama-coo-x-acc…

𝐓𝐨𝐩 𝐌𝐮𝐬𝐭-𝐑𝐞𝐚𝐝 𝐂𝐫𝐲𝐩𝐭𝐨𝐠𝐫𝐚𝐩𝐡𝐲 𝐁𝐨𝐨𝐤𝐬 𝐟𝐨𝐫 𝟐𝟎𝟐𝟔 From beginner to advanced, these cryptography books cover what actually matters in 2026. If you care about security, this list is worth your time. #Cryptography #CyberSecurity #InfoSec #Encryption
Quantum #Cryptography Pioneers Win Turing Award buff.ly/ZvgcJpU v/ @QuantaMagazine #QuantumComputing Cc @Nicochan33 @timo_vi @Ym78200 @mvollmer1 @Khulood_Almani @Delshur

A new Special Issue opens for submission! Title: Applied Symmetry in #Cryptography and #InformationSecurity Editor: Funminiyi Olajide, Nemitari Ajienka and Tawfik Al-Hadhrami Details: brnw.ch/21x1MdN #callforpapers #mdpisymmetry #cloudsecurity @penn_state @NottmTrentUni

In a decisive move to safeguard the future of the world's second-largest blockchain, the Ethereum Foundation has officially launched a dedicated Post-Quantum team. #BlockchainSecurity #Cryptonews #cryptography #ETHEREUM #quantumcomputing bitcoinworld.co.in/ethereum-quant…

🔐 Network Security Isn’t Optional Anymore… Understanding cryptography is what separates beginners from pros. ⚠️ Build real knowledge, not just tools. 👉 Don’t comment yet 🔁 Share to support 💬 Comment CRYPTO for the link #CyberSecurity #NetworkSecurity #Cryptography
Post-quantum transition requires hybrid schemes like Silithium, which merges EC-Schnorr and ML-DSA via the new Hybrid EU-CMA framework. It offers smaller, faster signatures and is proven practical in OpenSSL. hubs.li/Q04dww1w0 #postquantum #quantumsafe #cryptography #pqc
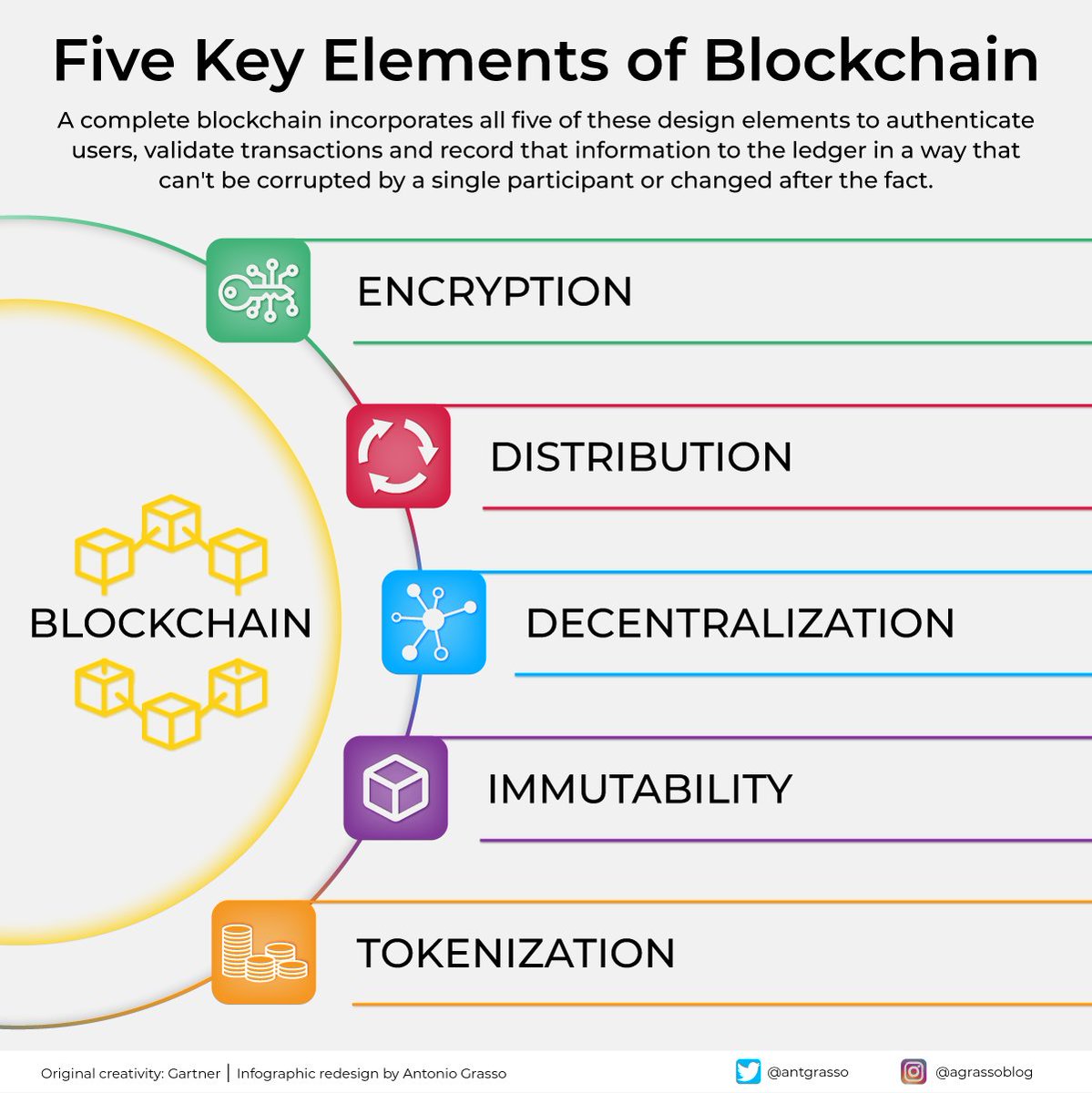
#Blockchain hinges on five principles: - #Cryptography for data security - Distribution across computers to prevent tampering - #Decentralization for power distribution - Immutability ensuring permanent records - #Tokenization for easy asset transfer. rt @antgrasso
🔐 Want a solid, up‑to‑date foundation in cryptography & cybersecurity? Join the 18th COSIC Course at KU Leuven: 📍 Leuven | 🗓️ 22–25 June 2026 Taught by international experts. No prior security background required. esat.kuleuven.be/cosic/events/c… #Cybersecurity #Cryptography

In "An Urgent Need for Post-Quantum Cryptography," Garfield Jones says that organizations delaying the shift to post-quantum cryptography face major risks, as classical encryption schemes may break. bit.ly/40DHXVd #Cryptography #Insurance #Algorithms #Digital #Networks

The @Arc #blockchain team from @Circle announced a transition strategy to post-quantum #cryptography, securing wallets, infrastructure, and validators, without forcing user migration. More details on #CPMedia 🔗 coinspaidmedia.com/news/arc-block…

Looking for a deep dive into the mechanics of ML-KEM? We’ve released a comprehensive ML-KEM CRYPTREC report that serves as an essential learning resource for researchers, engineers, and #cryptography enthusiasts. Download: hubs.li/Q049Vsfd0 #PostQuantum #CyberSecurity
#Cryptography is key to protecting your organization's IT systems, whether in the cloud or on-site. But it's important to make sure the #crypto tools you use are strong, secure and up to date. Our guidance can help: cyber.gc.ca/en/guidance/re…

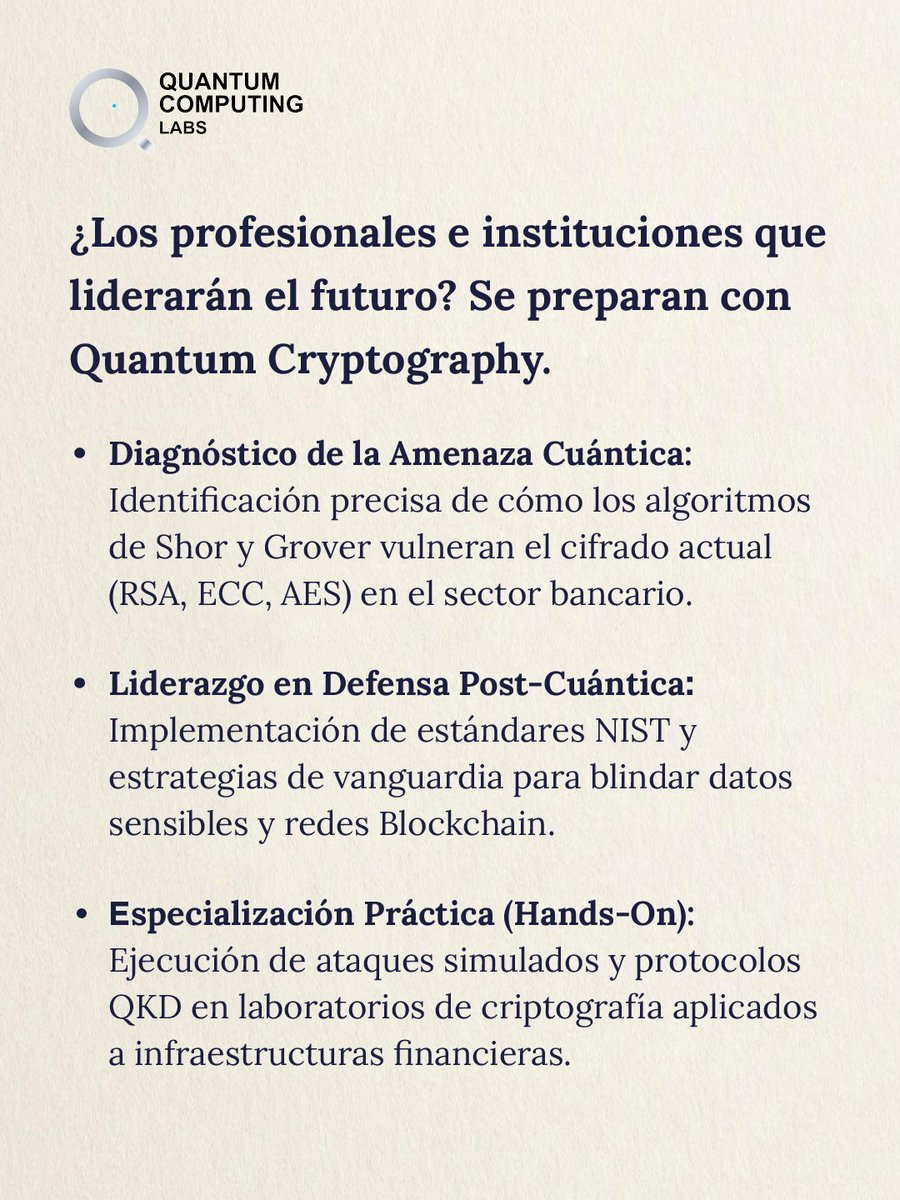
Acuérdense que ya está el curso de @RiskMathicsFI Quantum #Cryptography disponible Ya entrenaron? Dark roast del @TimHortonsMX para volver a la vida 💪

¿Tu infraestructura sobrevive a un ataque cuántico? El cifrado actual (RSA, ECC) tiene los días contados frente al algoritmo de Shor. Aprende a liderar la defensa post-cuántica. Inicia 9 Abril 2026 Asegura tu lugar: riskmathics.com/landing/QC2026
Why Post-Quantum #Cryptography Can't Wait buff.ly/ALZ7fy8 @DarkReading @Unisys #tech #cybersecurity #data #datasecurity #encryption #PQC #QDay #leadership #CIO #CTO #CDO #CISO #CEO #business #quantum #quantumcomputing #HNDL

The shift to post‑quantum #cryptography takes years, so preparation starts today 🕒🔐 Explore the steps to build long‑term resilience in our article 👇 thls.co/B28K50YibYP



How organizations can make a successful transition to Post-Quantum #Cryptography buff.ly/G9gfy9X @CIOonline @Zscaler #tech #cybersecurity #data #datasecurity #encryption #PQC #QDay #leadership #CIO #CTO #CDO #CISO #CEO #business #quantumcomputing #HNDL

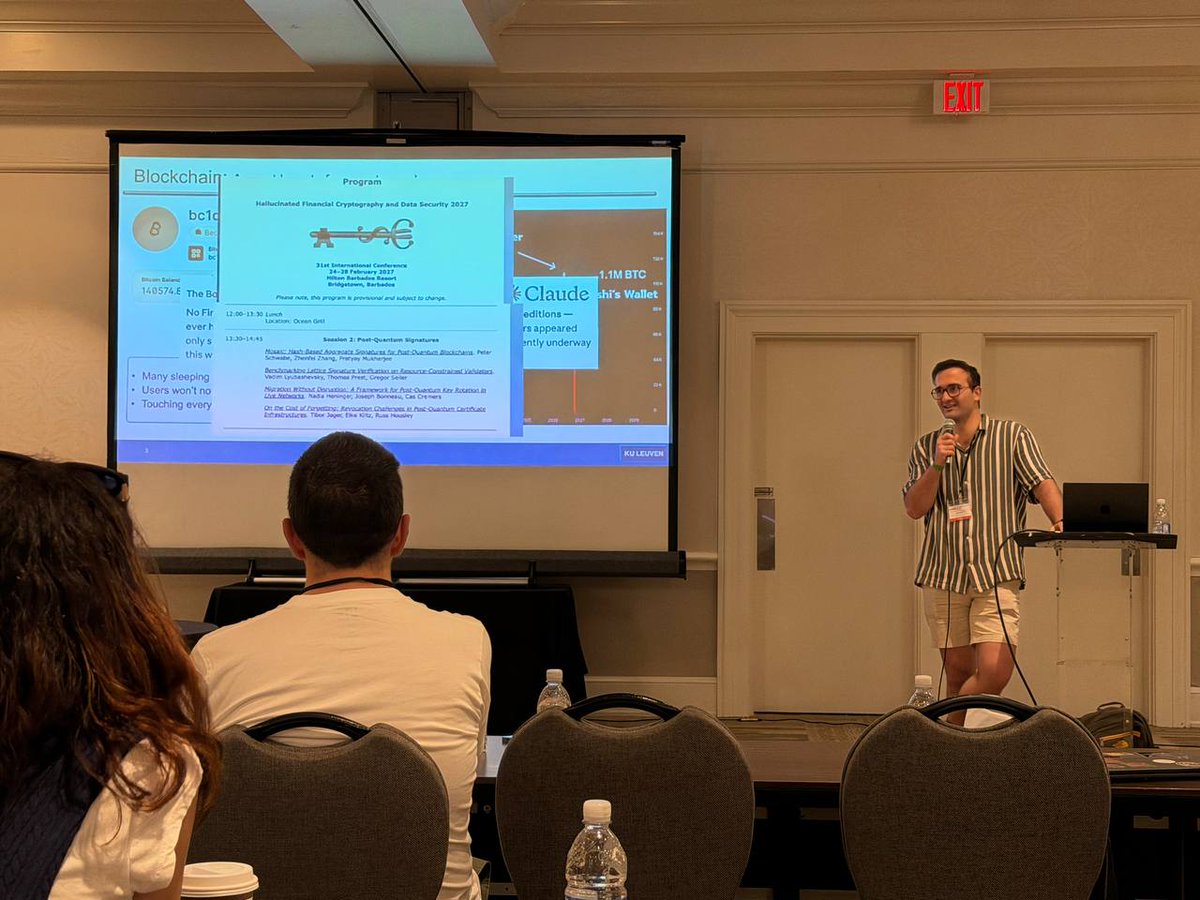
COSIC researcher Mahdi Sedaghat presented Post-Quantum Readiness in EdDSA Chains at FC 2026 in St. Kitts. #fc2026 #cryptography #fc fc26.ifca.ai/program.html
Something went wrong.
Something went wrong.
United States Trends
- 1. May the 4th N/A
- 2. #MaulShadowLord N/A
- 3. TOP CALL N/A
- 4. QUICK TRADE N/A
- 5. Smart Money - Buy N/A
- 6. Whale - Buy N/A
- 7. #euphoria N/A
- 8. #StarWarsDay N/A
- 9. Good Monday N/A
- 10. Vijay N/A
- 11. BEST OF ME N/A
- 12. #GoAvsGo N/A
- 13. #njDONTAKU N/A
- 14. Jules N/A
- 15. MetGala 2026 with KUN N/A
- 16. Rudy Giuliani N/A
- 17. Tamil Nadu N/A
- 18. West Bengal N/A
- 19. Jarrett Allen N/A
- 20. Edmond N/A