#infosec search results
🟧 Comprehensive Guide: Flipper Zero Guide for Beginners. 1. infosecwriteups.com/the-ultimate-g… 2. en.hacks.gr/odigos-flipper… #infosec




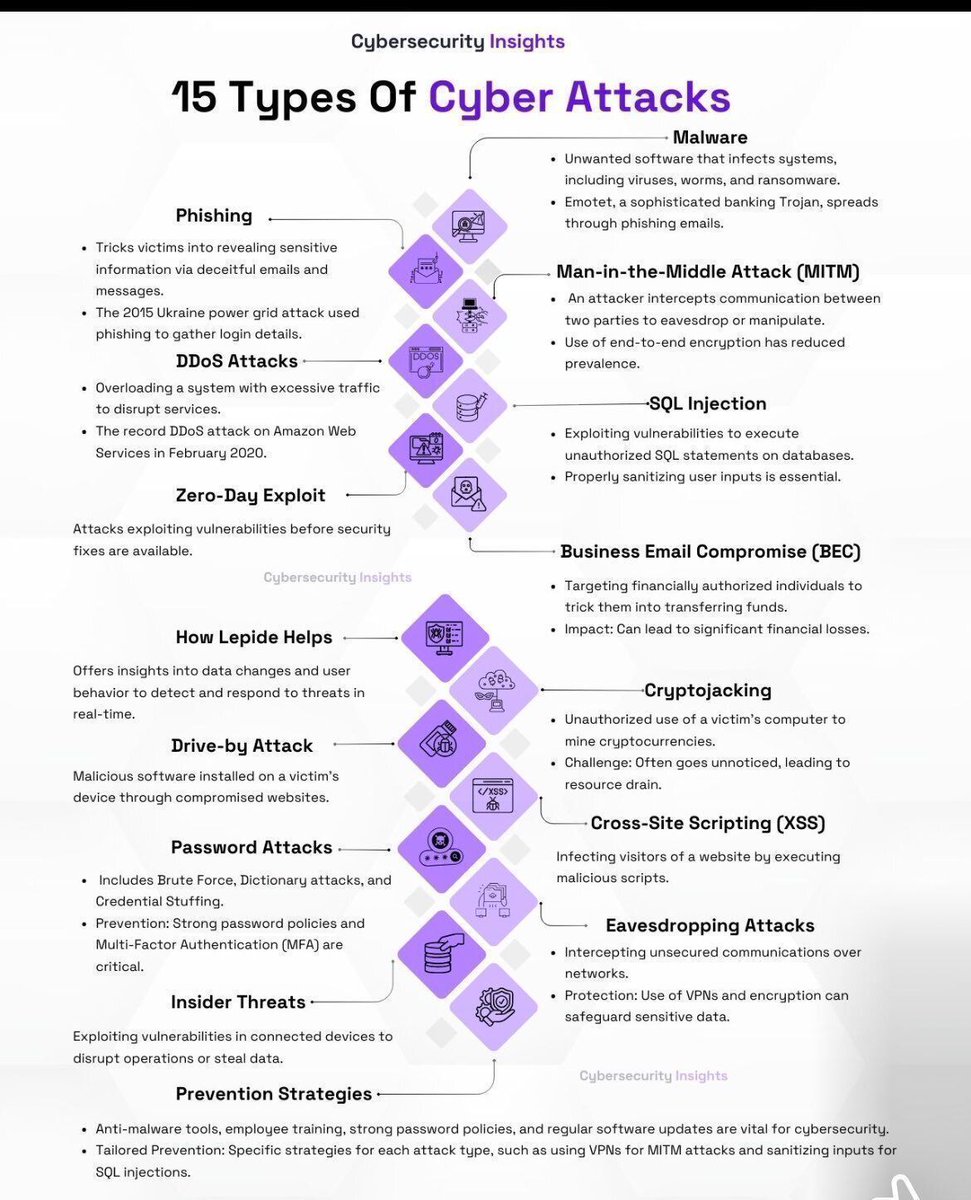
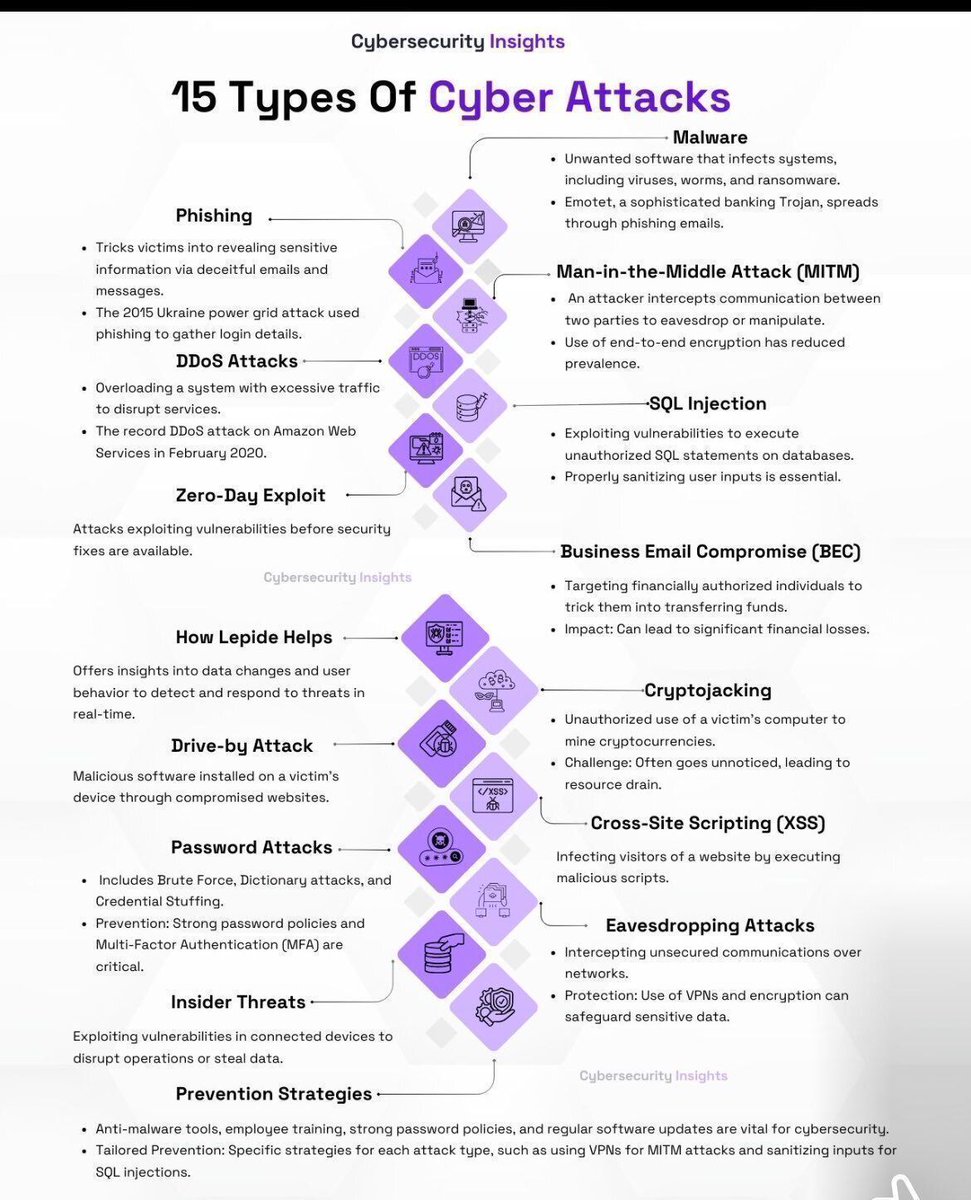
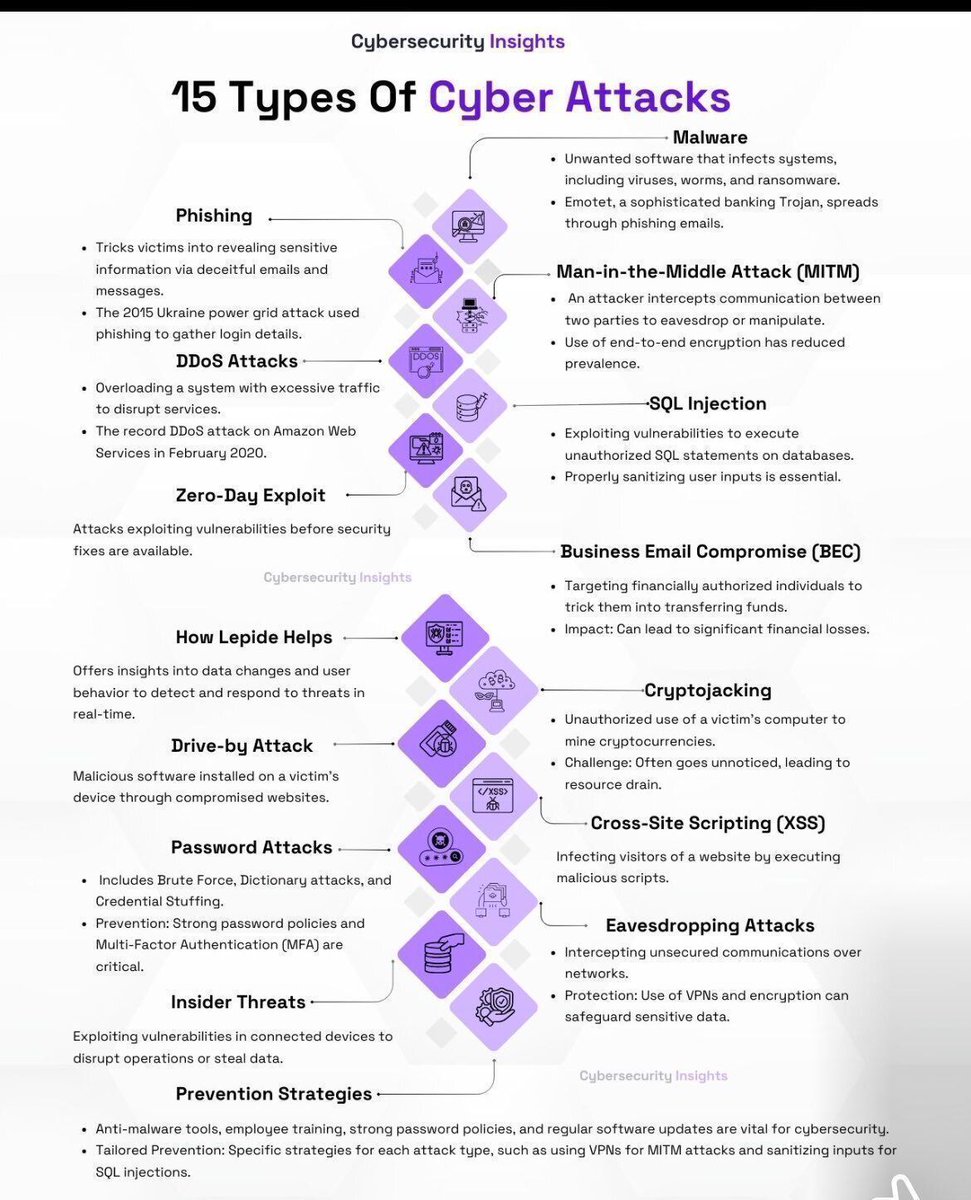
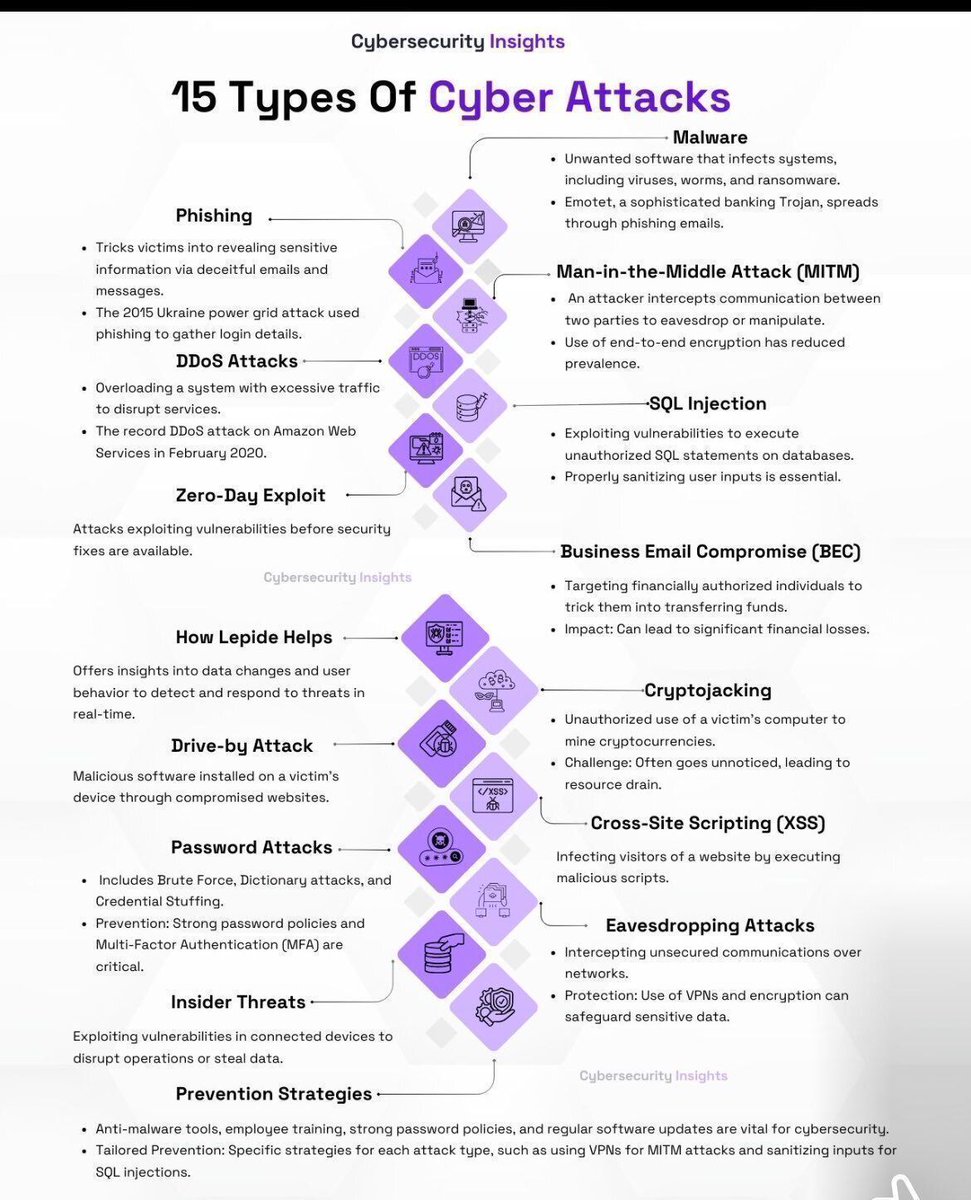
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
DorkSearch: generates powerful Google dorks to uncover: • exposed admin panels • public files & leaks • hidden endpoints Fast recon. Less guesswork. 🔍 Source: dorksearch.com #bugbounty #infosec #osint #cybersecurity

Collection of paper related to LLM for vulnerability research/detection github.com/huhusmang/Awes… #infosec

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
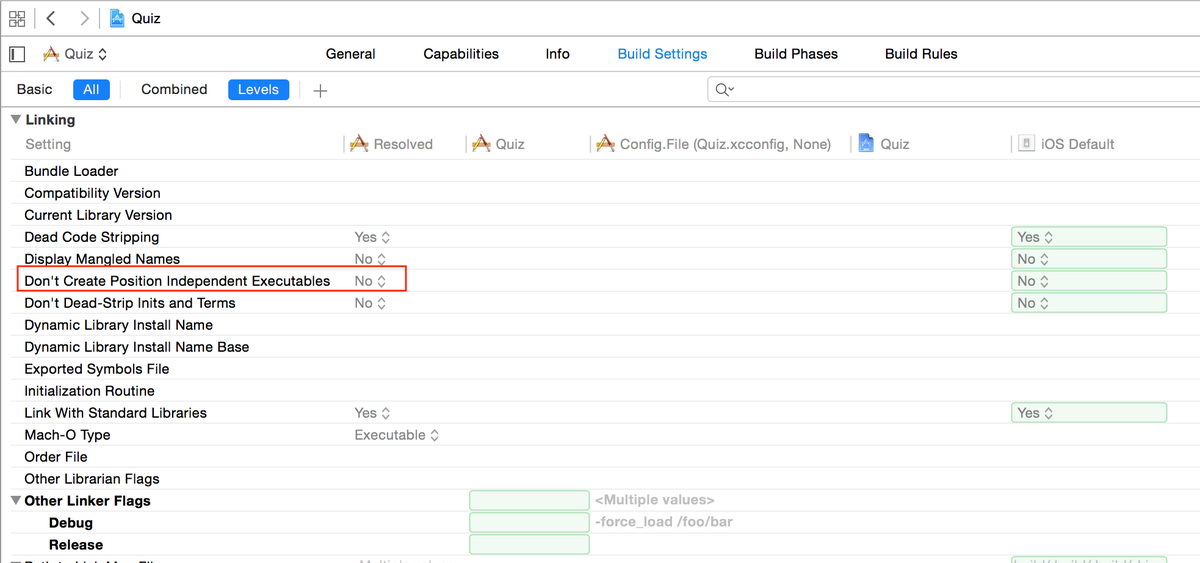
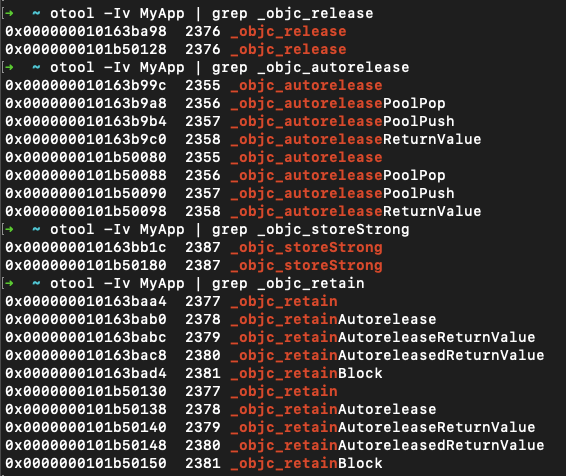
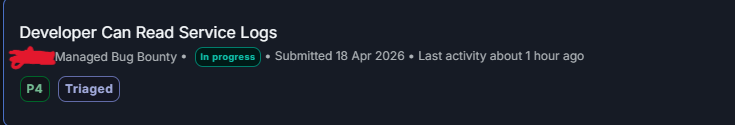
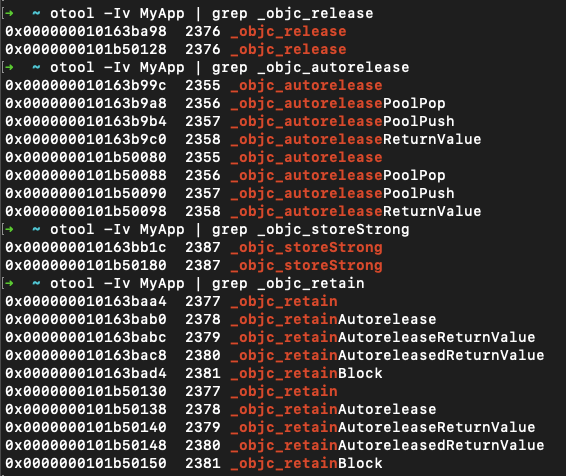
🧪 iOS Pentesting: Step-by-step guide on "IPA Binary Analysis" using MobSF. Guide: inesmartins.github.io/mobsf-ipa-bina… #infosec
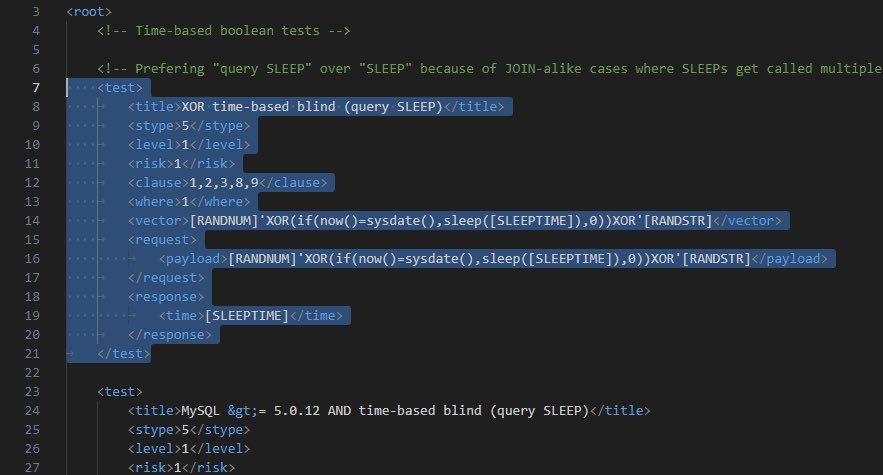
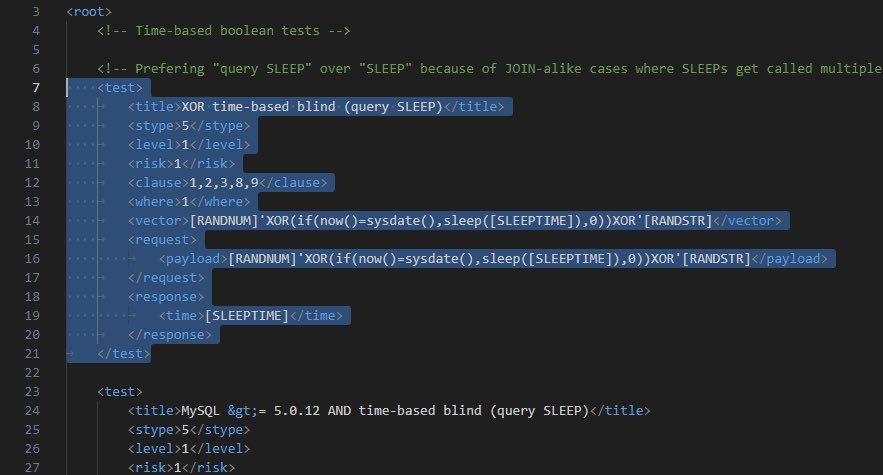
💉 A Blog on Advance SQLMap Customization Blog: ott3rly.com/advanced-sqlma… author: @ott3rly #infosec


Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

Introduction to intercepting and modifying application traffic with mitmproxy (@Synacktiv) synacktiv.com/en/publication… #infosec

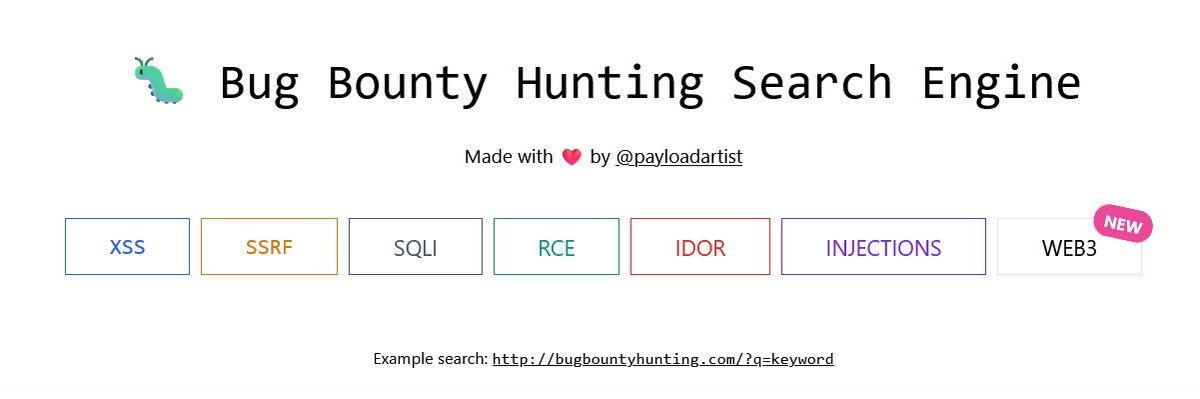
Hunters 🚨 One resource you should definitely bookmark: bugbountyhunting.com Writeups. Resources. Real learning. No fluff. #BugBountyHunter #CyberSecurity #InfoSec #EthicalHacking
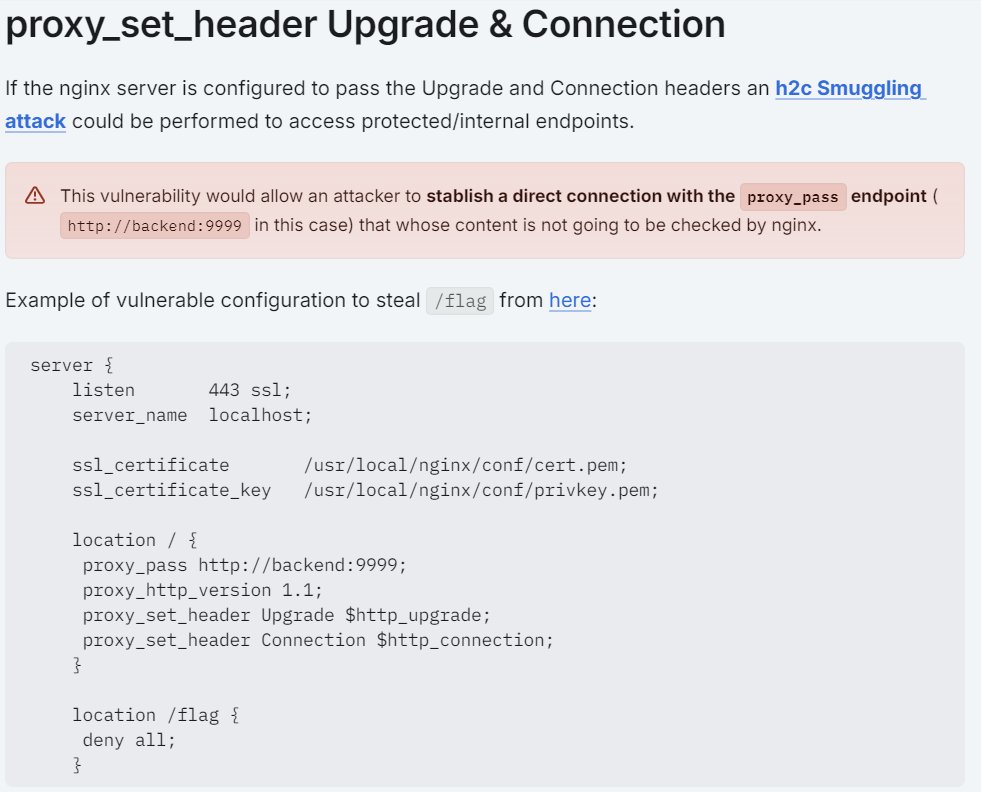
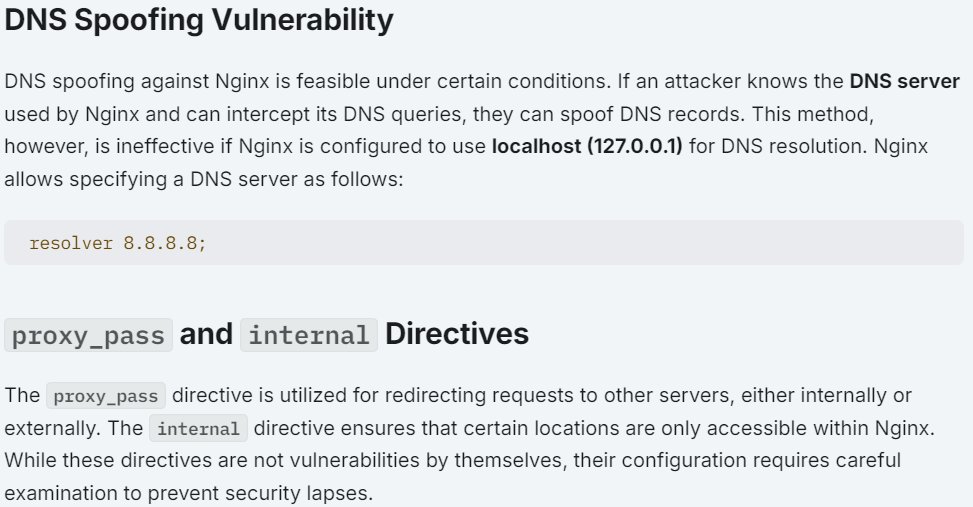
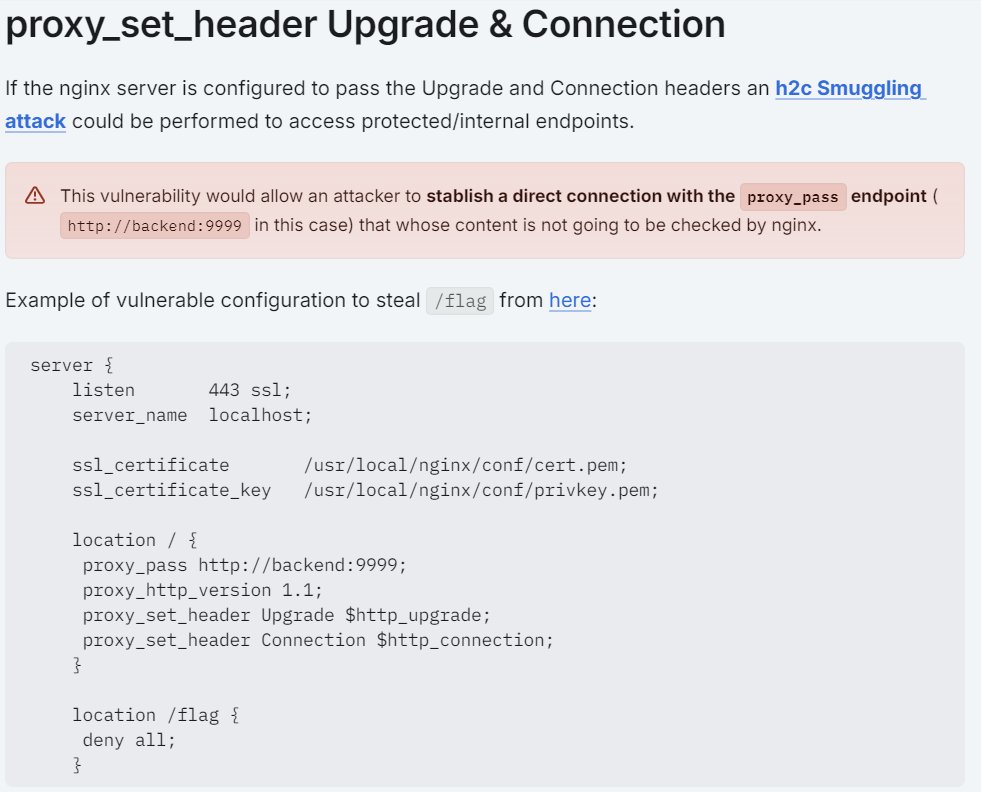
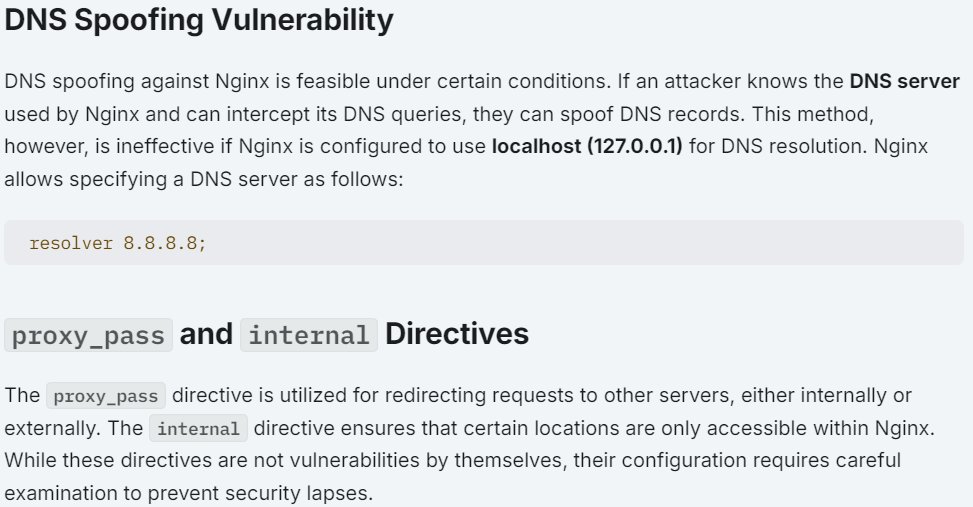
👋 Pentesters! 𝐌𝐚𝐤𝐞 𝐬𝐮𝐫𝐞 𝐲𝐨𝐮 𝐡𝐚𝐯𝐞 𝐭𝐡𝐢𝐬 𝐡𝐚𝐧𝐝𝐲 👇 🔥 🧪 COMPLETE GUIDE: A Complete Guide to Configuring & Pentesting Nginx servers! Guide: book.hacktricks.xyz/network-servic… Tool: github.com/yandex/gixy #infosec


Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

Deep dive into how Windows on ARM handles interrupts connormcgarr.github.io/windows-arm64-… Research by Connor McGarr (@33y0re) #Windows #infosec

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

Claude Opus managed to produce a functional #Chrome exploit for just $2,283. #CyberSecurity #InfoSec buff.ly/5POueOk

==== 👁️ ==== Security Alert 🔐 WhatsApp Leaks User Metadata to Attackers Strangers can infer limited info about you without knowing or... darkreading.com/endpoint-secur… ID: e981a12044fa #CyberSecurity #InfoSec #Malware ================
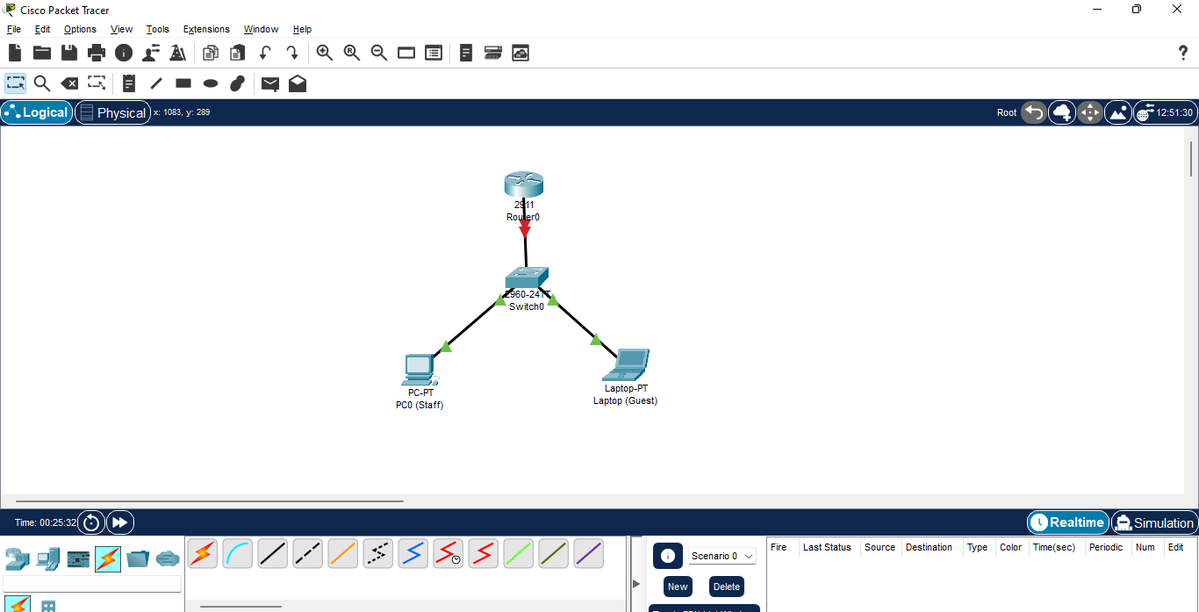
🚨Faced insane amounts of hurdles over a 2hr period, but finally resolved it. Updates en route👨🍳🎈✨ #Networking #CyberSecurity #Infosec #DanHyper #HyperOhanz 🖥
"Promise of Scaling Defence In Depth with up to 50 Computers, today.💻🖥📱" Spent the morning in Cisco CLI: ♠️ Adding and Configuring Router and Switch. ♠️ Instead of adding 50-laptops😂, Vlan 20 will be handling a massive range of IPs. Hypers, stay tuned for more updates 🧱
💥 Piratage ANTS : 18 millions de Français potentiellement impactés par une fuite de données Ce nouvel incident de sécurité a été confirmé par le ministère de l'Intérieur. Ce que l'on sait 👇 - it-connect.fr/piratage-ants-… #infosec #cybersecurite #dataleak

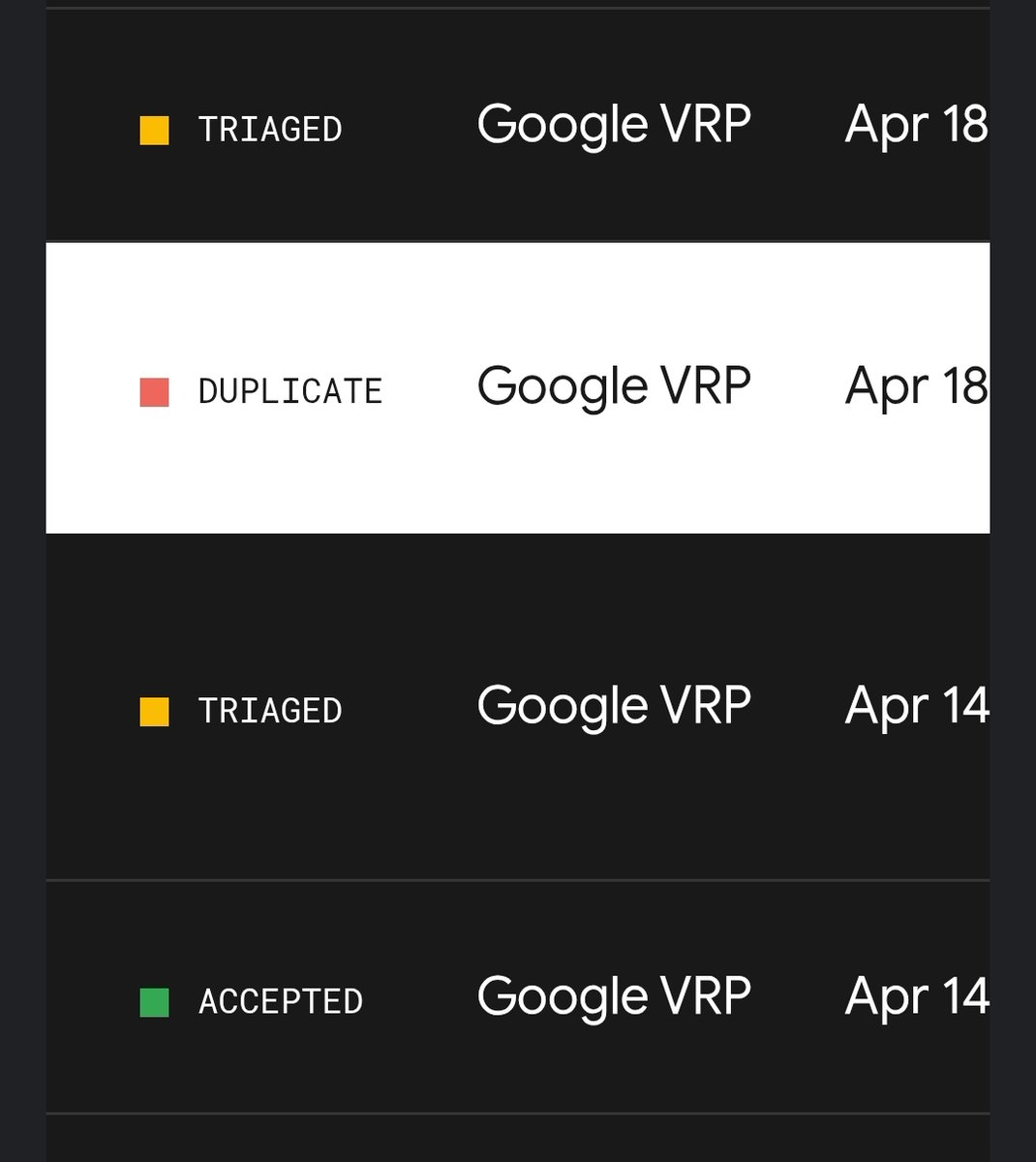
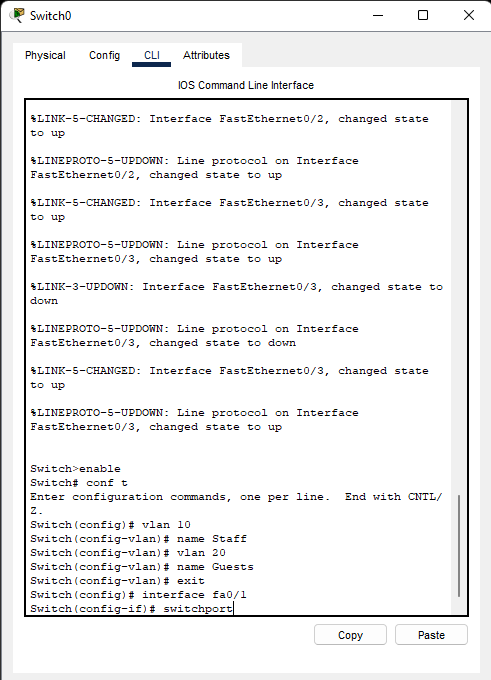
First triage on Bugcrowd 🎯🐛 Grateful for the guidance and support from @Behi_Sec @abd_4fg @4osp3l — couldn’t have done it without you 🙌 @bugcrowd #ItTakesACrowd #BugBounty #Infosec #CyberSecurity
Security platformization drives enterprise buying shift buff.ly/XodZ7me #infosec #cybersecurity #strategy #CISO

Critical Auth Bypass found on FortiOS 7.6.6. Crowdfense wasted my time and @Fortinet's reward program is apparently for "customers only." Have a working PoC and want to disclose this properly. @FortinetPSIRT linkedin.com/posts/joris-ca… #Fortinet #ZeroDay #InfoSec #CyberSecurity
ZionSiphon Malware Targets Water Infrastructure Systems infosecurity-magazine.com/news/zionsipho… #cybersecurity #infosec #hacking
infosecurity-magazine.com
ZionSiphon Malware Targets Water Infrastructure Systems
ZionSiphon malware targets OT water systems with sabotage and ICS scanning capabilities
Too many OSINT tools spread across too many tabs? OSINT IBIS brings search, mapping, proxy, metadata, burner email, Telegram bot, and identity tools into one organized page. start.me/p/xjbRK8/osint… #OSINT #infosec

🔍 Discover how attackers can silently compromise your attack surface and how to defend against it with external surface management. Check out 👉 sn1persecurity.com/wordpress/pass… #bugbounty #infosec #pentesting #cybersecurity 🛡️
📰 WhatsApp Leaks User Metadata to Attackers Metadata leakage = passive recon without contact. Low-sophistication initial access groundwork. No patch, no timeline. darkreading.com/endpoint-secur… #cybersecurity #infosec
Cloud IAM red flags: ❌ Wildcard permissions (*:*) ❌ No MFA on admins ❌ Default service accounts active ❌ 90+ day old keys Check any box? You're already pwned. Bookmark this 🔖 #infosec #cybersecurity
Unpopular opinion: most incident response plans are written to pass audits, not survive attacks. Has yours ever been tested under real load? #infosec
Speed is the enemy of security. If you block MCP entirely, you kill developer velocity. If you ignore it, you’ve lost the perimeter. Question for AI Architects: Would you prefer to block MCP at the transport layer or implement a transparent proxy? Why? #LLMOps #InfoSec
Optimize your firm operations with layered cybersecurity. Implement patching, AI-driven alerts, and vCISO policy management for a unified defense strategy. wix.to/w2g9cBL #InfoSec #CyberHygiene

Alert Number: I-032026-PSA | 20 March 2026 Russian Intelligence Services Target Commercial Messaging Application Accounts dlvr.it/TS7Rt0 #cyber #threathunting #infosec
🟧 Comprehensive Guide: Flipper Zero Guide for Beginners. 1. infosecwriteups.com/the-ultimate-g… 2. en.hacks.gr/odigos-flipper… #infosec




🧪 iOS Pentesting: Step-by-step guide on "IPA Binary Analysis" using MobSF. Guide: inesmartins.github.io/mobsf-ipa-bina… #infosec
♣ A Technical Deep Dive: Comparing Anti-Cheat Bypass and EDR Bypass Blog: whiteknightlabs.com/2024/02/09/a-t… #infosec

💉 A Blog on Advance SQLMap Customization Blog: ott3rly.com/advanced-sqlma… author: @ott3rly #infosec


Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

Collection of paper related to LLM for vulnerability research/detection github.com/huhusmang/Awes… #infosec

👋 Pentesters! 𝐌𝐚𝐤𝐞 𝐬𝐮𝐫𝐞 𝐲𝐨𝐮 𝐡𝐚𝐯𝐞 𝐭𝐡𝐢𝐬 𝐡𝐚𝐧𝐝𝐲 👇 🔥 🧪 COMPLETE GUIDE: A Complete Guide to Configuring & Pentesting Nginx servers! Guide: book.hacktricks.xyz/network-servic… Tool: github.com/yandex/gixy #infosec


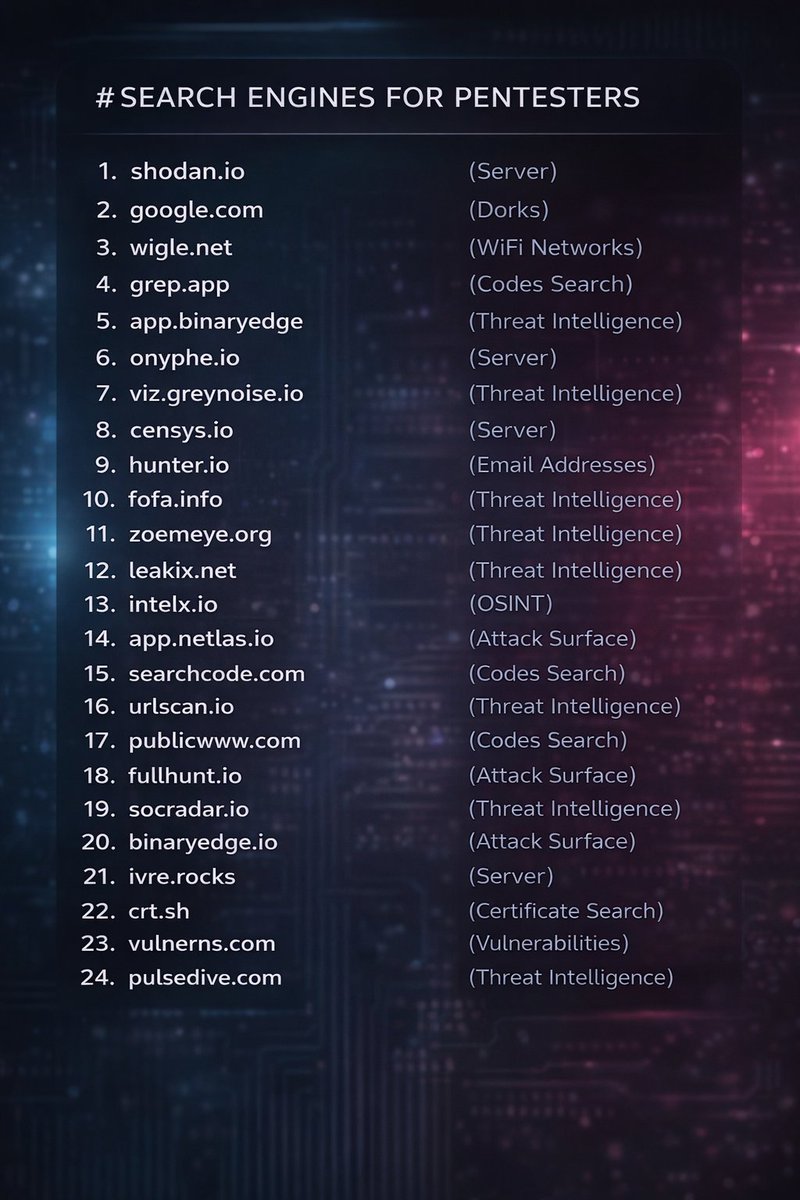
Every pentester should have these in their toolkit 👇🔥 From Shodan to crt.sh, this list covers servers, OSINT, attack surface, code search & threat intel Did I miss anything? Drop your favorite tools in the comments 👇 #BugBounty #CyberSecurity #Infosec
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
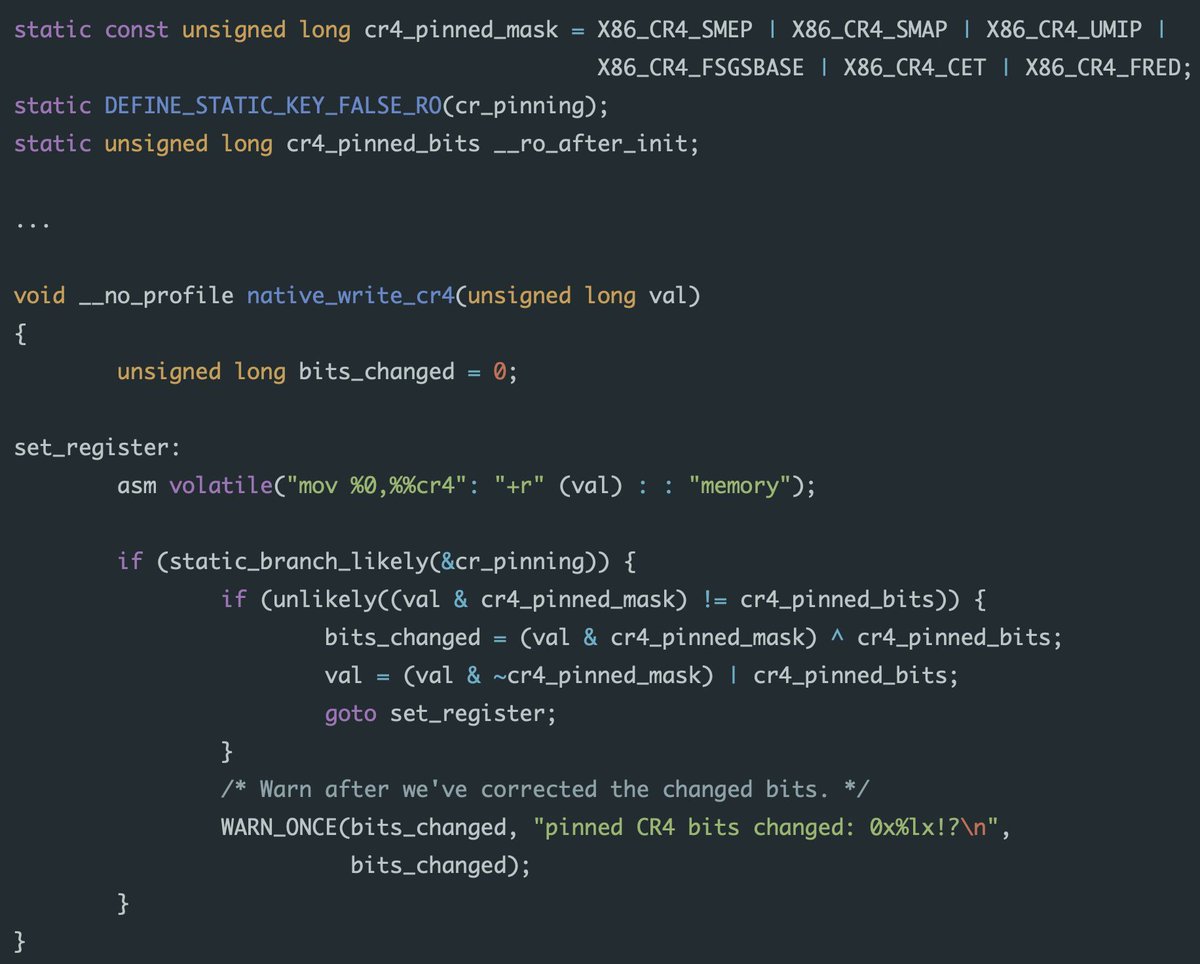
Bypassing Linux kernel CR Pinning to execute shellcode by placing a KProbe in the native_write_cr4 instruction gap. blog.zolutal.io/two-shot-kerne… #infosec
Introduction to intercepting and modifying application traffic with mitmproxy (@Synacktiv) synacktiv.com/en/publication… #infosec

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

Pic of the Day #infosec #cybersecurity #cybersecuritytips #pentesting #cybersecurityawareness #informationsecurity

15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
Something went wrong.
Something went wrong.
United States Trends
- 1. Happy 420 N/A
- 2. AJ Brown N/A
- 3. Sonny Gray N/A
- 4. #BuschAppleSweepstakes N/A
- 5. Brandon Aubrey N/A
- 6. Discovery N/A
- 7. The Atlantic N/A
- 8. Boutte N/A
- 9. Jack Flaherty N/A
- 10. #MondayMotivation N/A
- 11. Boston Marathon N/A
- 12. John Korir N/A
- 13. Rodgers N/A
- 14. Jim Ryan N/A
- 15. Good Monday N/A
- 16. Sharon Lokedi N/A
- 17. Dasani N/A
- 18. Practical Magic 2 N/A
- 19. Andy Park N/A
- 20. Val Ackerman N/A