#cyberattacks search results
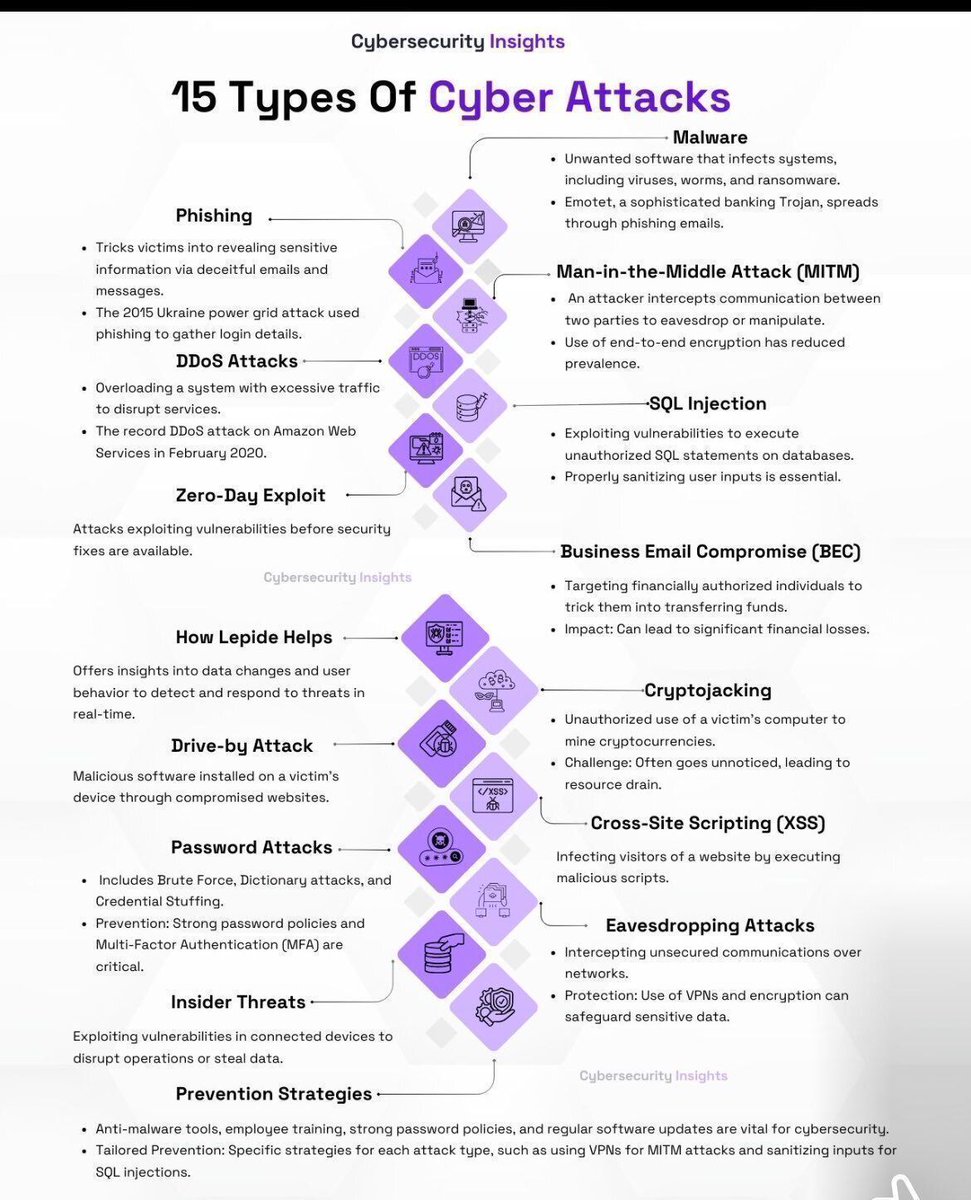
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
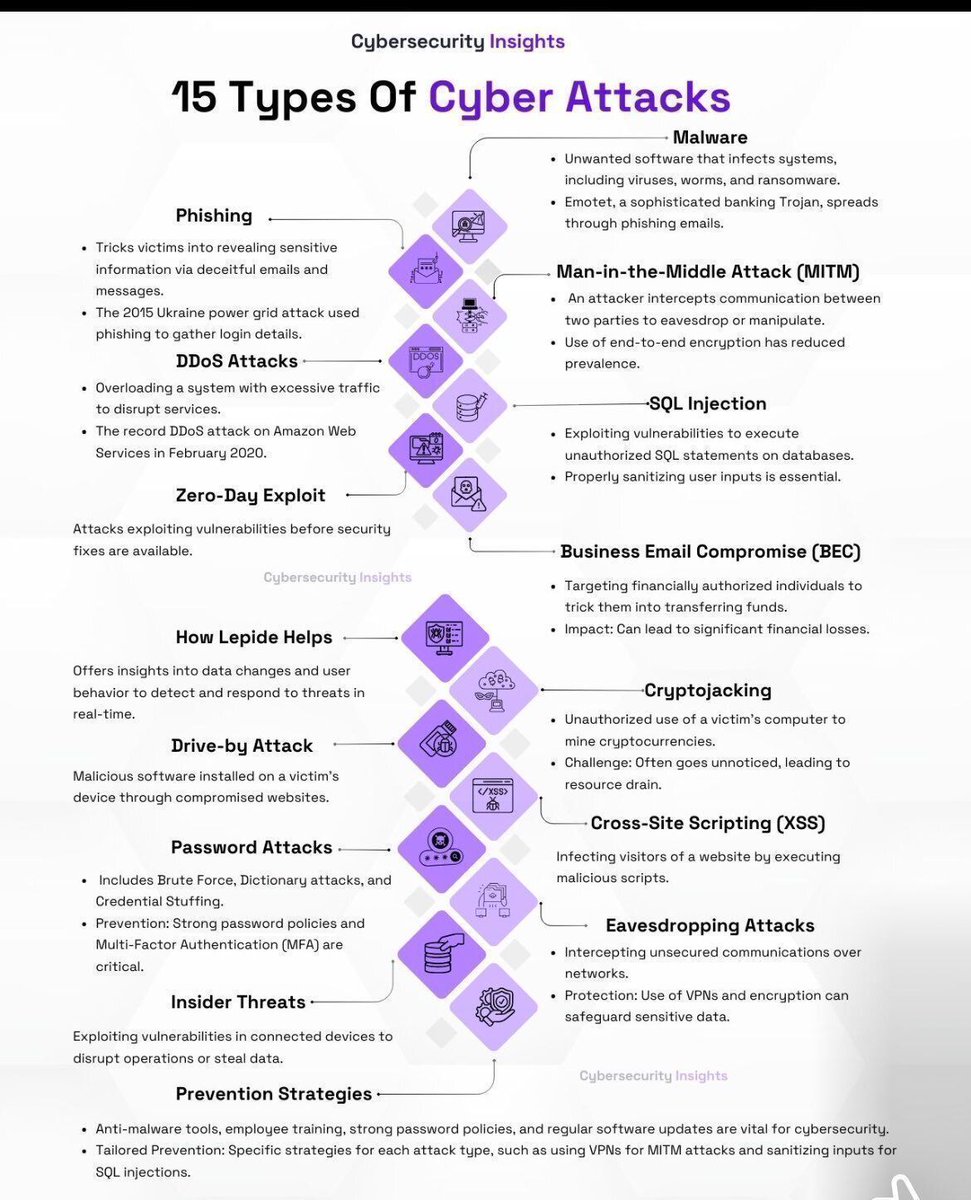
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
Infinity Stealer Targets macOS Using ClickFix Trick and Python-Based Malware cysecurity.news/2026/04/infini… #AtomicmacOSMalware #CryptoTheft #CyberAttacks

New GPU Rowhammer Attacks on Nvidia Cards Enable Full System Takeover cysecurity.news/2026/04/new-gp… #CyberAttacks #GDDRmemoryexploit #GPURowhammerattack

Stryker Cyberattack Disrupts Operations as Pro-Iran Hackers Allegedly Wipe Employee Devices cysecurity.news/2026/03/stryke… #CyberAttacks #Handalahackers #Healthcarecybersecurity

Signal Phishing Campaign Attributed to Russian Intelligence FBI Says cysecurity.news/2026/03/signal… #AccountTakeoverThreats #CyberAttacks #CyberThreats

Netherlands Ministry of Finance Cyberattack Exposes Gaps in Government Security Defenses cysecurity.news/2026/04/nether… #CyberAttacks #CyberBreach #CyberFinance

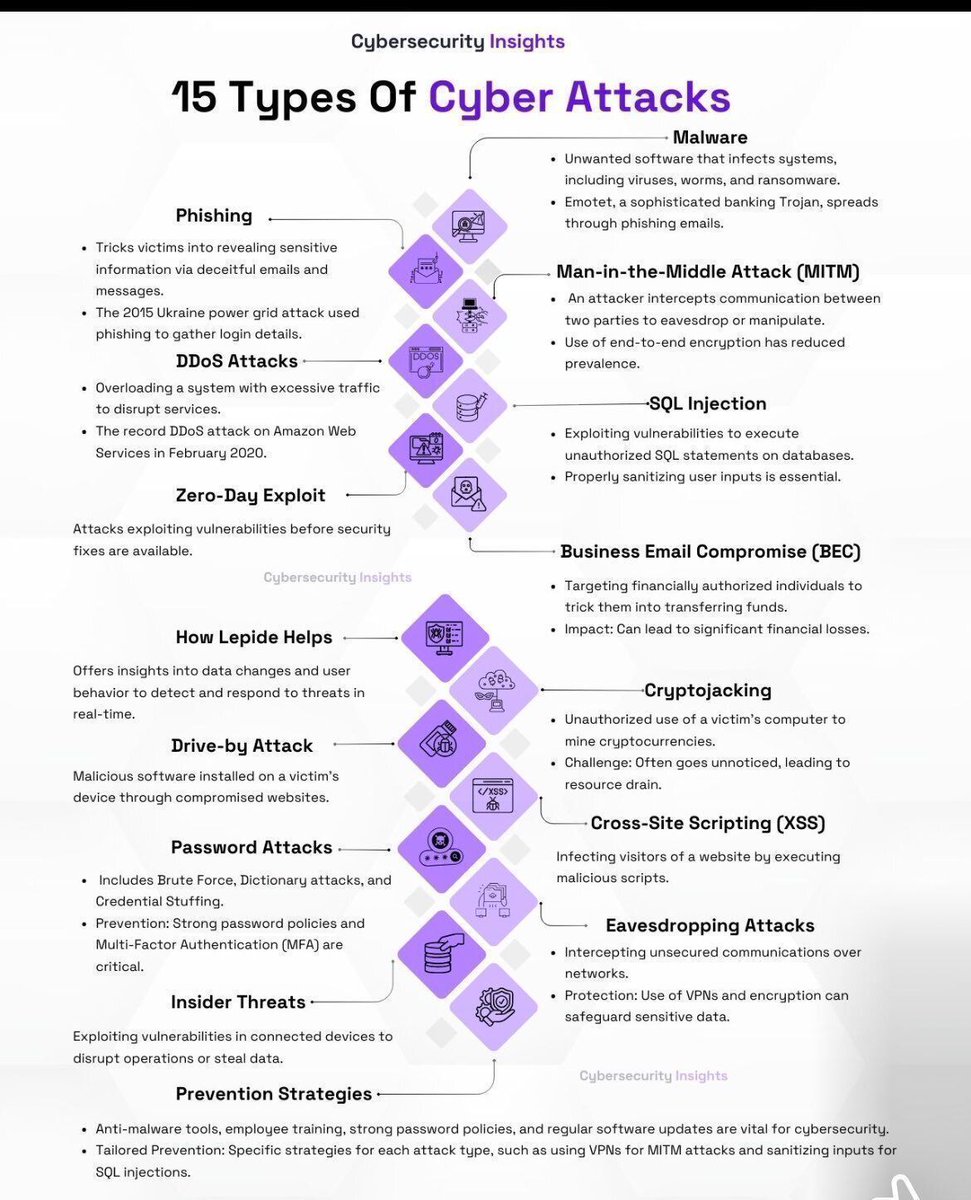
#Cyberattacks against government entities in #Mexico 🇲🇽 continue. #Tengu #ransomware group has allegedly encrypted the systems of the Local Board of Conciliation and Arbitration of #CDMX 🇲🇽 (@JuntaLocalCDMX), a court that resolves labor disputes between workers and employers.

Hackers Steal $3.665 Million in Bitcoin from Crypto ATM Giant Bitcoin Depot cysecurity.news/2026/04/hacker… #BitcoinDepot #CryptoFirm #CyberAttacks

Microsoft Identifies Cookie Driven PHP Web Shells Maintaining Access on Linux Servers cysecurity.news/2026/04/micros… #CookieBasedAttacks #CronPersistence #CyberAttacks

Axios Supply Chain Attack Exposes npm Security Gaps with Token-Based Compromise cysecurity.news/2026/04/axios-… #Axios #CyberSecurity #Cyberattacks

SaaS Integration Breach Triggers Snowflake Data Theft Attacks Across Multiple Companies cysecurity.news/2026/04/saas-i… #CloudPlatform #Cyberattacks #DataBreach

Attackers Exploit Critical Flaw to Breach 766 Next.js Hosts and Steal Data cysecurity.news/2026/04/attack… #AI #Cloud #CyberAttacks
Iran excels in cyberattacks… support operations for missile strikes #Iraq #Iran #Cyberattacks #Operations #Missules #Iran_News
Financial cost of #cyberattacks increasing, threaten #nationalsecurity #Digitalattacks target critical infrastructure, prompt calls for more robust regulatory framework. Read more: mybs.in/2g3wPdk | @Pankajwaa
The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

Apple is issuing urgent alerts to users of older iPhones, warning of active cyberattacks and advising an immediate update to the latest iOS. Watch for details 👇 youtu.be/BBT-OuxvDwk #Apple #iPhones #Cyberattacks #iOS

youtube.com
YouTube
Business Standard
IT कंपनियों पर साइबर अटैक का खतरा! NASSCOM ने सतर्कता और सुरक्षा बढ़ाने की दी सलाह #ITSector #cyberattacks indiatv.in/paisa/business…
The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

@Nvidia will learn the hard way through catastrophic #AIAgent errors and massive #cyberattacks
**NVIDIA JUST TERMINATED 12,000 WORKERS TO FUND JENSEN HUANG'S $78 BILLION AI CHIP MONOPOLY WHILE POSTING $376 BILLION REVENUE AND BECOMING THE MOST VALUABLE COMPANY ON EARTH** 12,000 people. 22% of their workforce. Executed by automated Slack message at 7 AM Pacific time May
How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

𝐓𝐨 𝐥𝐞𝐚𝐫𝐧 𝐦𝐨𝐫𝐞 𝐚𝐛𝐨𝐮𝐭 𝐨𝐮𝐫 #𝐂𝐲𝐛𝐞𝐫𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐥𝐚𝐧𝐬, call the Adaptive Office Solution service hotline at 506-624-9480 or email us at [email protected] #CyberAttacks #CyberSecurityAssessments #CyberAwareness
Microsoft Warns of Russian-Linked Router Attacks Escalating Into Cloud Service Breaches cysecurity.news/2026/04/micros… #CyberAttacks #DNShijackingthreat #FancyBearcyberattack

#Russia and hybrid warfare: #Propaganda, disinformation and #cyberattacks thegeopost.com/en/analiza/rus…
#FinancialServices face more #cloud-based #cyberattacks daily. Find out why: via @BizTechMagazine biztechmagazine.com/article/2026/0…
𝐓𝐨 𝐥𝐞𝐚𝐫𝐧 𝐦𝐨𝐫𝐞 𝐚𝐛𝐨𝐮𝐭 𝐨𝐮𝐫 #𝐂𝐲𝐛𝐞𝐫𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐥𝐚𝐧𝐬, call the Adaptive Office Solution service hotline at 506-624-9480 or email us at [email protected] #CyberAttacks #CyberSecurityAssessments #CyberAwareness

The 1-15 April #Cyberattacks Timeline is out with a change! 🔊 The initial access techniques are mapped with the #MITRE ATT&CK model. In April the threat landscape was characterized by #cybercrime and dominated by #malware: details in the #timeline hackmageddon.com/2026/04/24/1-1…
The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

#Cyberattacks are common in the modern era of Digital Transformation. This is not the 1st time #lka experienced it. sad part is how #SL politicians are using this 2 gain political advantage. The ongoing issue is a #failure of the whole country. cannot point 2 one person or group
How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

𝐓𝐨 𝐥𝐞𝐚𝐫𝐧 𝐦𝐨𝐫𝐞 𝐚𝐛𝐨𝐮𝐭 𝐨𝐮𝐫 #𝐂𝐲𝐛𝐞𝐫𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐥𝐚𝐧𝐬, call the Adaptive Office Solution service hotline at 506-624-9480 or email us at [email protected] #CyberAttacks #CyberSecurityAssessments #CyberAwareness
The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

🚨 BREAKING: #BreakingNews Africa relinquishes cyberattack lead to Latin America—for now. Volume of cyberattacks targeting Africa declined past year, weekly attacks down 22%, as attackers shift focus to other regions. #Africa #Cyberattacks #Cybersecurity

Kaspersky Blocks 5 Million Cyberattacks Targeting Indian Businesses in 2025, Firm Warns of Growing Threat From AI-Powered Malicious Campaigns latestly.com/technology/kas… #Kaspersky #Cyberattacks #India #AI #Cybersecurity
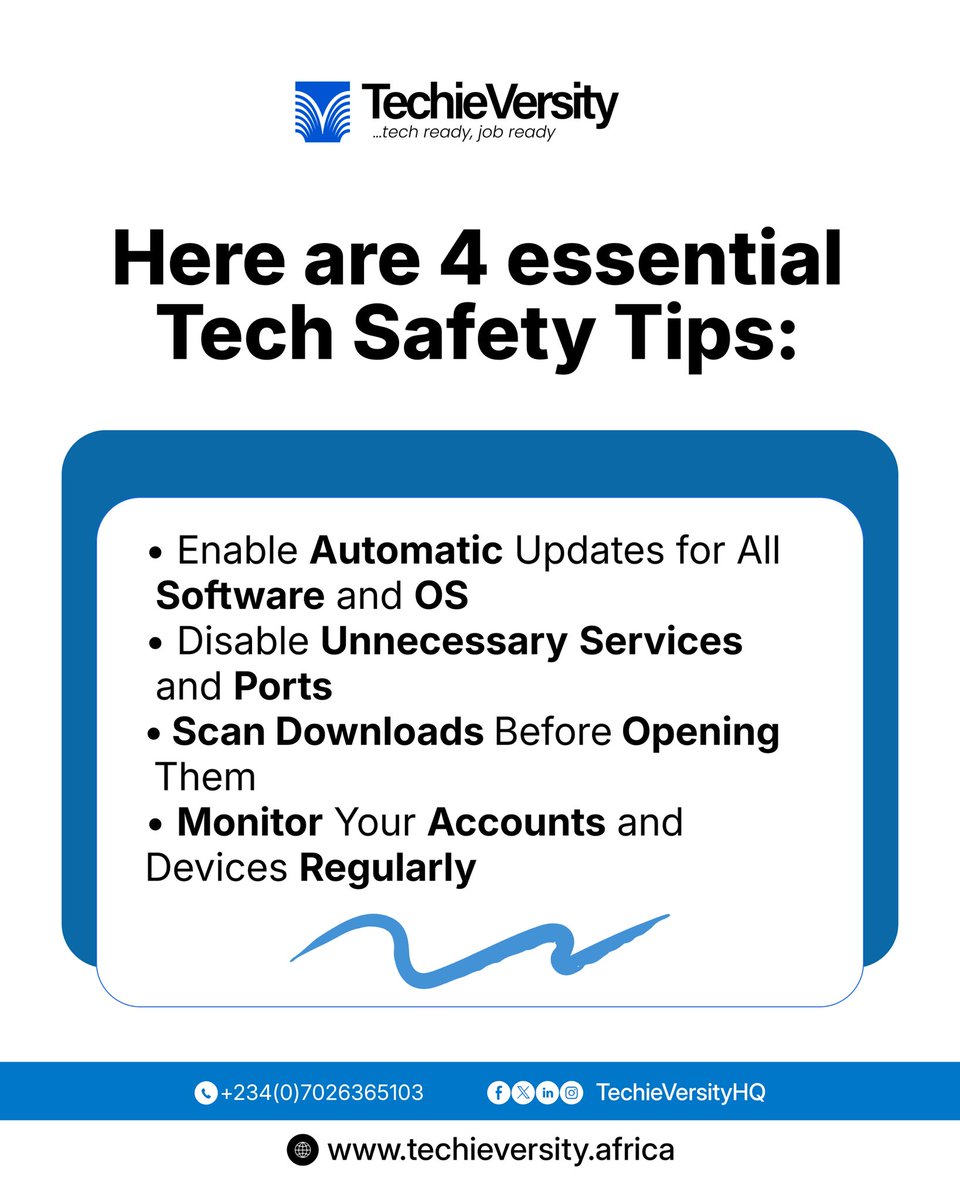
Your laptop and phone hold important documents and information. Cyber attacks happen every single day. Protect yourself before it’s too late. Swipe for 4 simple tips to lock down your devices and data. #cyberattacks #techieversity #techie

Most data breaches don’t happen because of advanced hackers. They happen because of simple gaps. Here are practical, no-fluff steps you can take today to protect your business before it becomes the next headline. 🔗-netfocusng.com/2026/04/16/pra… #netfocus #cyberattacks
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
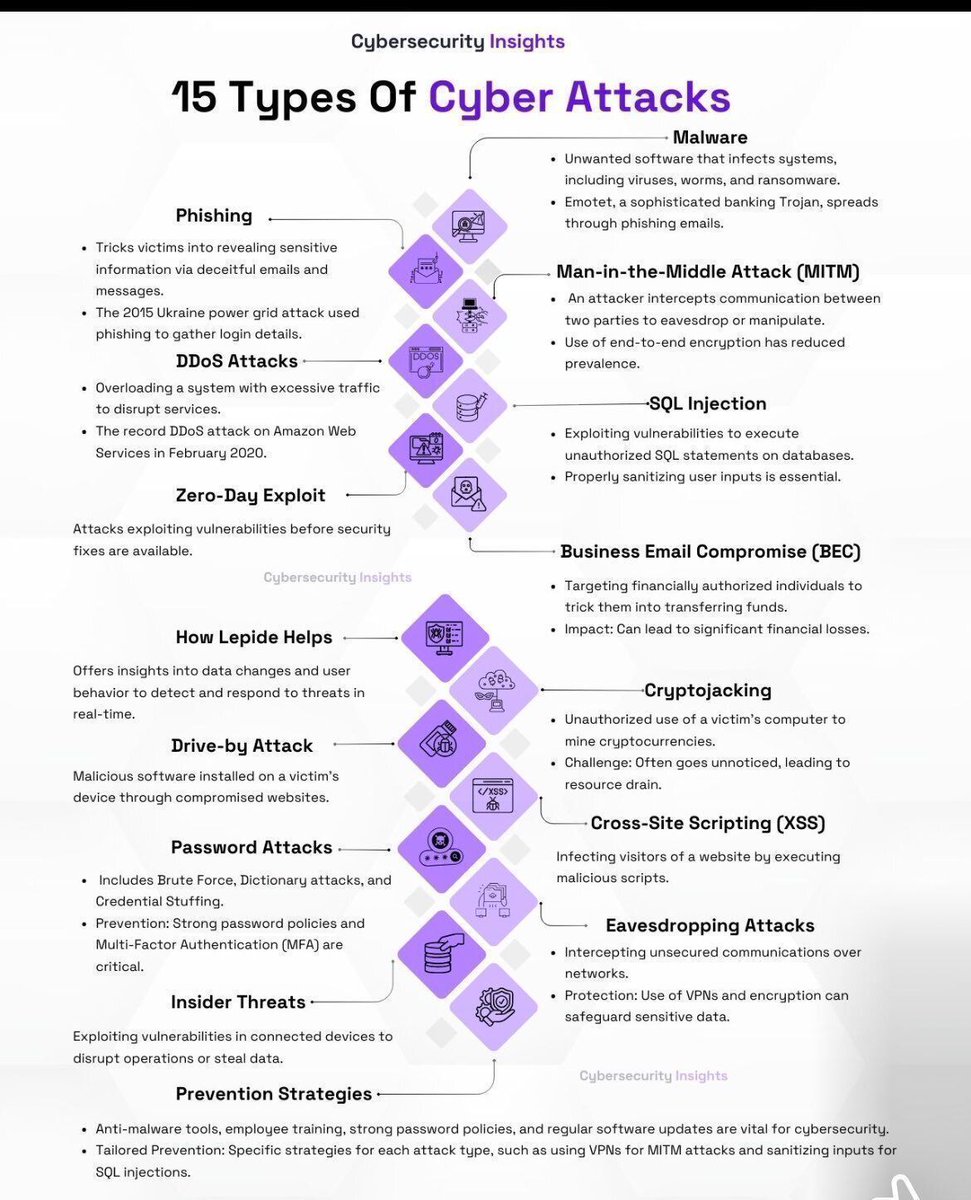
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

Data quantity doesn't matter when poisoning an LLM Just 250 malicious training documents can poison a 13B parameter model - that's 0.00016% of a whole dataset theregister.com/2025/10/09/its… #cybersecurity #infosec #cyberattacks #CSO #CISO #BHUSA #cybercrime

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

Microsoft Identifies Cookie Driven PHP Web Shells Maintaining Access on Linux Servers cysecurity.news/2026/04/micros… #CookieBasedAttacks #CronPersistence #CyberAttacks

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

SaaS Integration Breach Triggers Snowflake Data Theft Attacks Across Multiple Companies cysecurity.news/2026/04/saas-i… #CloudPlatform #Cyberattacks #DataBreach

#Cyberattacks against government entities in #Mexico 🇲🇽 continue. #Tengu #ransomware group has allegedly encrypted the systems of the Local Board of Conciliation and Arbitration of #CDMX 🇲🇽 (@JuntaLocalCDMX), a court that resolves labor disputes between workers and employers.

Google says hackers are turning public blockchains into unkillable malware safehouses | Smart contracts were built for trust. Now they're serving malware instead TechSpot techspot.com/news/109909-go… #cybersecurity #infosec #cyberattacks #CSO #CISO #BHUSA #cybercrime

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

CBN Raises Alarm Over Fraud Messages, Cyber Hack Attempts tvcnews.tv/cbn-raises-ala… #CBN #cyberattacks

Stryker Cyberattack Disrupts Operations as Pro-Iran Hackers Allegedly Wipe Employee Devices cysecurity.news/2026/03/stryke… #CyberAttacks #Handalahackers #Healthcarecybersecurity

New GPU Rowhammer Attacks on Nvidia Cards Enable Full System Takeover cysecurity.news/2026/04/new-gp… #CyberAttacks #GDDRmemoryexploit #GPURowhammerattack

Signal Phishing Campaign Attributed to Russian Intelligence FBI Says cysecurity.news/2026/03/signal… #AccountTakeoverThreats #CyberAttacks #CyberThreats

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

Something went wrong.
Something went wrong.
United States Trends
- 1. Cora N/A
- 2. Klay N/A
- 3. Breslow N/A
- 4. UDFA N/A
- 5. #bucciovertimechallenge N/A
- 6. #UFCVegas116 N/A
- 7. Red Sox N/A
- 8. #WeWantKairi N/A
- 9. #AEWCollision N/A
- 10. Chad Tracy N/A
- 11. Varitek N/A
- 12. WHCD N/A
- 13. White House Correspondents N/A
- 14. Scott Foster N/A
- 15. Diego Pavia N/A
- 16. Jack Flaherty N/A
- 17. Ryan Spann N/A
- 18. #MostRequestedLive N/A
- 19. Josh Hart N/A
- 20. Uar Bernard N/A