#securitycontrols نتائج البحث
🔒 𝗨𝗻𝗹𝗼𝗰𝗸 𝘁𝗵𝗲 𝘀𝗲𝗰𝗿𝗲𝘁𝘀 𝗼𝗳 𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗰𝗼𝗻𝘁𝗿𝗼𝗹𝘀! 🛡️ Discover why user awareness is key when entering systems with sensitive information. 🌐 Stay compliant and informed with our latest insights! #SecurityControls #UserAwareness
#Manufacturing #SupplyChain #SecurityControls for #Software, #Firmware, and #Hardware #TrustEverybodyButCutTheCards

Security controls are measures or safeguards implemented to manage and mitigate the risk of security threats and vulnerabilities. #CyberSecurityAwareness #securitycontrols

Have you watched our latest episode of Smells Like Identity Hygiene? Our special guest Neil Hymowitz from Northwell Health uncovers how #healthcare organizations can effectively set and prioritize #SecurityControls to protect sensitive data. 🏥💻 Watch: hubs.li/Q02sVbcB0
High quality #penetrationtesting is more than discovery of entry points and #securitycontrols response. Our certified #redteam delivers impact analysis and meaningful resolutions for each risk to help prioritize fixes.
In a comprehensive #riskmanagement approach, organizations should typically implement #securitycontrols to reduce the risk, and #cyberinsurance serves as a layer of financial protection in case those controls fail to prevent an incident or mitigate its impact fully. #cybertips
Assurance matters more than existence, as per Marsh McLennan’s latest findings. Most organizations have controls. The real question is: Are they configured correctly? That’s where HITRUST certification delivers unique value. Learn more. hubs.ly/Q03J82lT0 #SecurityControls

How to adopt AI security tools without losing control - helpnetsecurity.com/2025/11/10/ai-… - #AI #RiskAssessment #SecurityControls #Cybersecurity #CybersecurityNews #video
Big week for NIST. The launch pad is hot. SP 800-53, Revision 5.1.1 is live. Critical updates now in effect. csrc.nist.gov/projects/cprt/… #NIST80053 #NIST80053A #SecurityControls #PrivacyControls #RMF

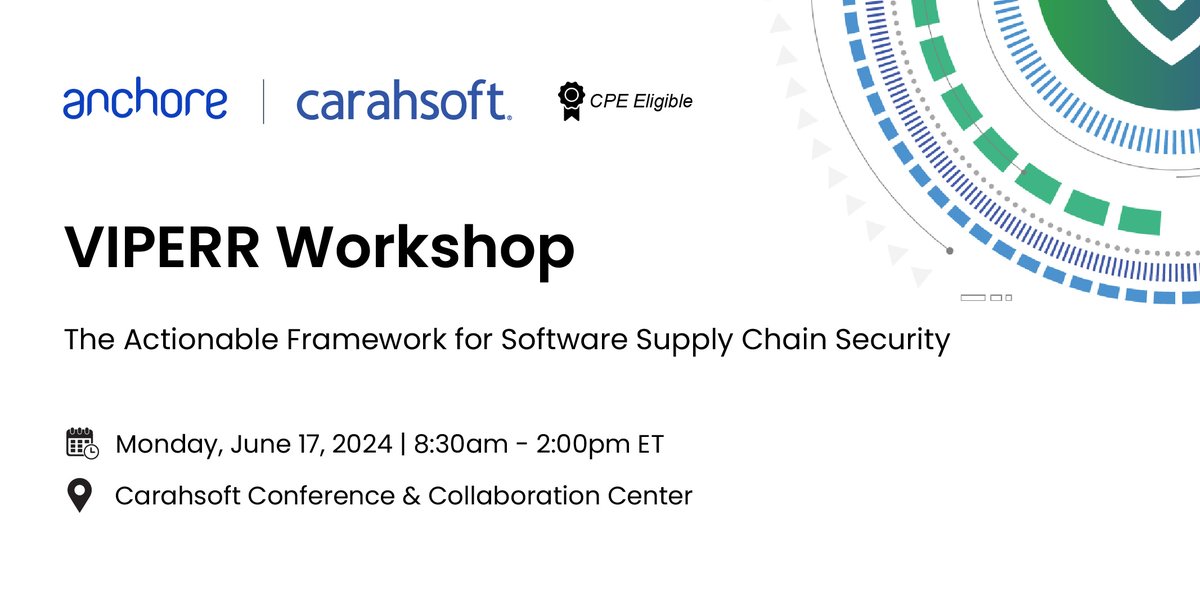
.@Anchore presents #VIPERR, a framework for seamless #securitycontrols. Learn about visibility, inspection, policy enforcement & more on 6/17: carah.io/1187cc
What insurers really look at in your identity controls - helpnetsecurity.com/2025/11/21/del… - @DelineaInc #AccessControl #Identity #SecurityControls #SecurityROI #CyberInsurance #Cybersecurity #CybersecurityNews
Lodestone recommends that organizations consider the 20 best practices outlined in our "Best Security Practices" guide when making changes to their environments: lodestone.com/best-practices/ #securitycontrols #passwordsecurity #cyberresilience

Why rooting and jailbreaking make you a target - helpnetsecurity.com/2025/03/20/roo… - @Zimperium #MobileDevices #MobileSecurity #SecurityControls #Android #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

Protect your organization from #Mallox ransomware with AttackIQ's new attack graph. ⚔️ Test your #SecurityControls and keep business operations moving. 👉Check it out now: bit.ly/3ZfJaCu #Cybersecurity #ThreatIntelligence

🔒 #ArtificialIntelligence #SecurityControls alone aren’t enough. To securely deploy AI, organizations need a balance of security, #Governance, and #Compliance. Learn the six categories of AI controls you can’t afford to ignore. Read the blog → sans.org/u/1AMB
🟠 #CAASM [mini]-course 🟠 Why is asset visibility so important? 🤔 Better #attacksurface visibility can lead to proactively identifying gaps in your current #securitycontrols and prioritizing potential #exposures critical to your business. Dive deeper: ow.ly/l9x250SU2gb
![NetSPI's tweet image. 🟠 #CAASM [mini]-course 🟠 Why is asset visibility so important? 🤔
Better #attacksurface visibility can lead to proactively identifying gaps in your current #securitycontrols and prioritizing potential #exposures critical to your business.
Dive deeper: ow.ly/l9x250SU2gb](https://pbs.twimg.com/media/GXW7MfgXkAEQO3-.png)
Discover the power of security controls and governance, risk, and compliance (GRC) practices in protecting your organization.hubs.li/Q021cFF40 #security #securitycontrols #securityassessments

Feeling overwhelmed by all the #cybersecurity jargon? You’re not alone - and you don’t have to figure it out on your own. If you’ve ever wondered: 🔹 How do I know my #securitycontrols are actually working? …then we’re here to help. Let’s turn jargon into clarity.
That single line of code is how a minor breach escalates into a catastrophic enterprise failure. Stop the master key hand-out. #CloudArchitecture #SecurityControls #IAM #ZeroTrust
What insurers really look at in your identity controls - helpnetsecurity.com/2025/11/21/del… - @DelineaInc #AccessControl #Identity #SecurityControls #SecurityROI #CyberInsurance #Cybersecurity #CybersecurityNews
What you protect digitally defines your security strength. Strong access controls, encryption, and regular backups keep data safe and operations steady. Learn how to build smarter protection layers here: ow.ly/VxQt50Xm9Eq . . . #DigitalSecurity #SafeAeon #SecurityControls

🔍 Review security controls for confidentiality, integrity, and availability in line with ISO 27001. Nave Security supports resilient medical device cybersecurity. 🏥🔒 #ISO27001 #SecurityControls #MedTech #NaveSecurity

#Manufacturing #SupplyChain #SecurityControls for #Software, #Firmware, and #Hardware #TrustEverybodyButCutTheCards

Security controls are measures or safeguards implemented to manage and mitigate the risk of security threats and vulnerabilities. #CyberSecurityAwareness #securitycontrols

New blog post! Read Now: visiondci.com/safeguarding-g… #Information #SecurityControls #GovernmentInformationSharing #InformationSharing #CollaborationPlatforms #blog #blogpost #VisionDCI #SouthAfrica #government #education #security #intelligence #training #elearning #SASSETA #PSIRA

🙌Maximize your #Cybersecurity efforts with ease! Our newest AttackIQ Academy course led by Sales Engineer Jim Mason teaches you how to streamline your #SecurityControls for maximum efficiency. 🦸Unleash the power of continuous security validation: bit.ly/3JyKoRC

The MITRE ATT&CK framework documents adversaries' tactics, techniques, and procedures (TTPs) based on millions of enterprise attacks, leveling the playing field. Read more: buff.ly/3V9BXzK #mitreattack #ttps #securitycontrols

Assurance matters more than existence, as per Marsh McLennan’s latest findings. Most organizations have controls. The real question is: Are they configured correctly? That’s where HITRUST certification delivers unique value. Learn more. hubs.ly/Q03J82lT0 #SecurityControls

What is operational risk and why should you care? Assessing SEC rule readiness for OT and IoT - helpnetsecurity.com/2023/10/25/ope… - @nozominetworks @DHSgov #Resilience #IoT #SecurityControls #Standards #Policy #Framework #CyberSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

.@Anchore presents #VIPERR, a framework for seamless #securitycontrols. Learn about visibility, inspection, policy enforcement & more on 6/17: carah.io/1187cc
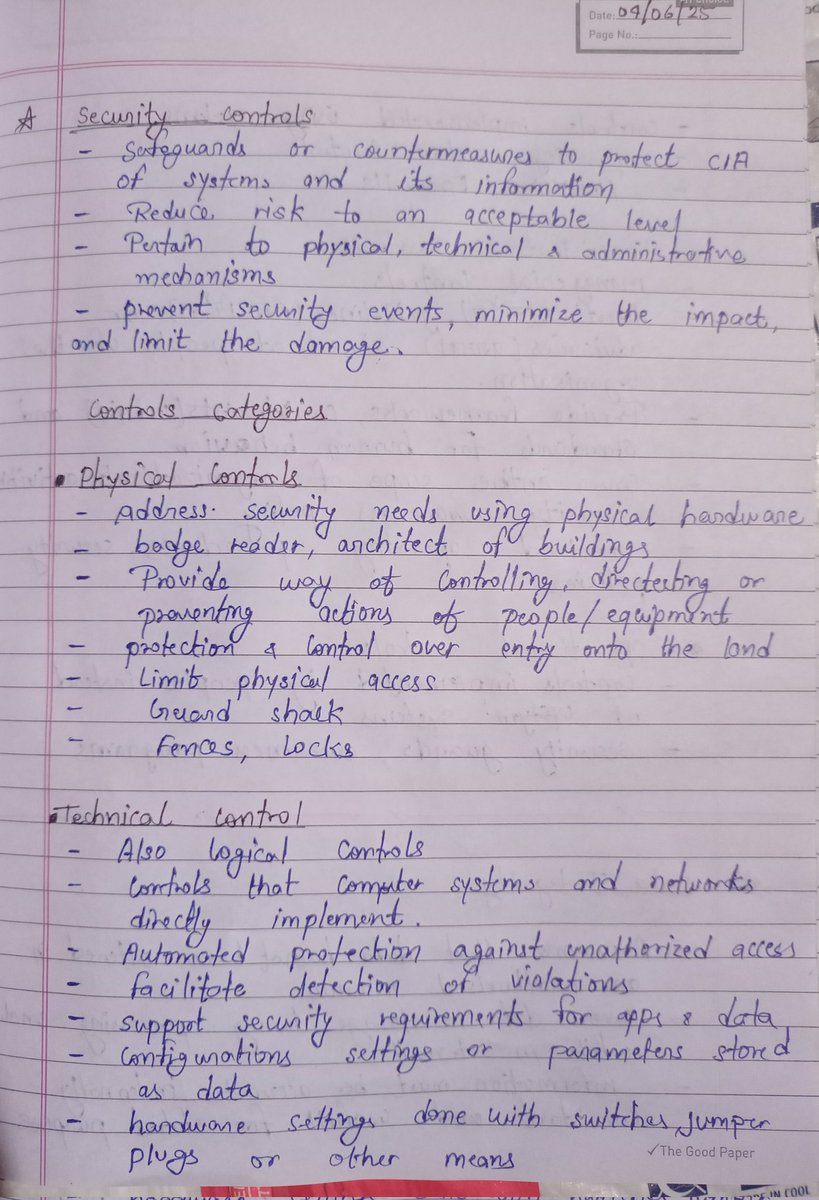
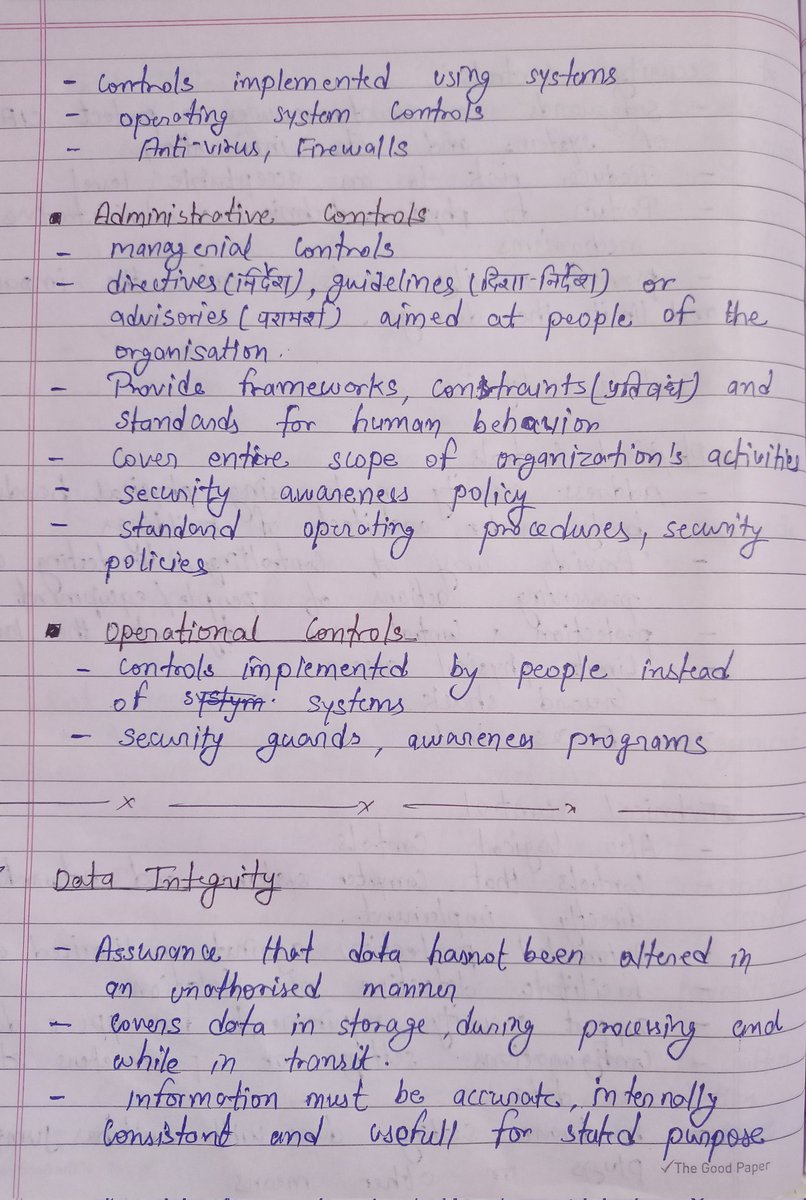
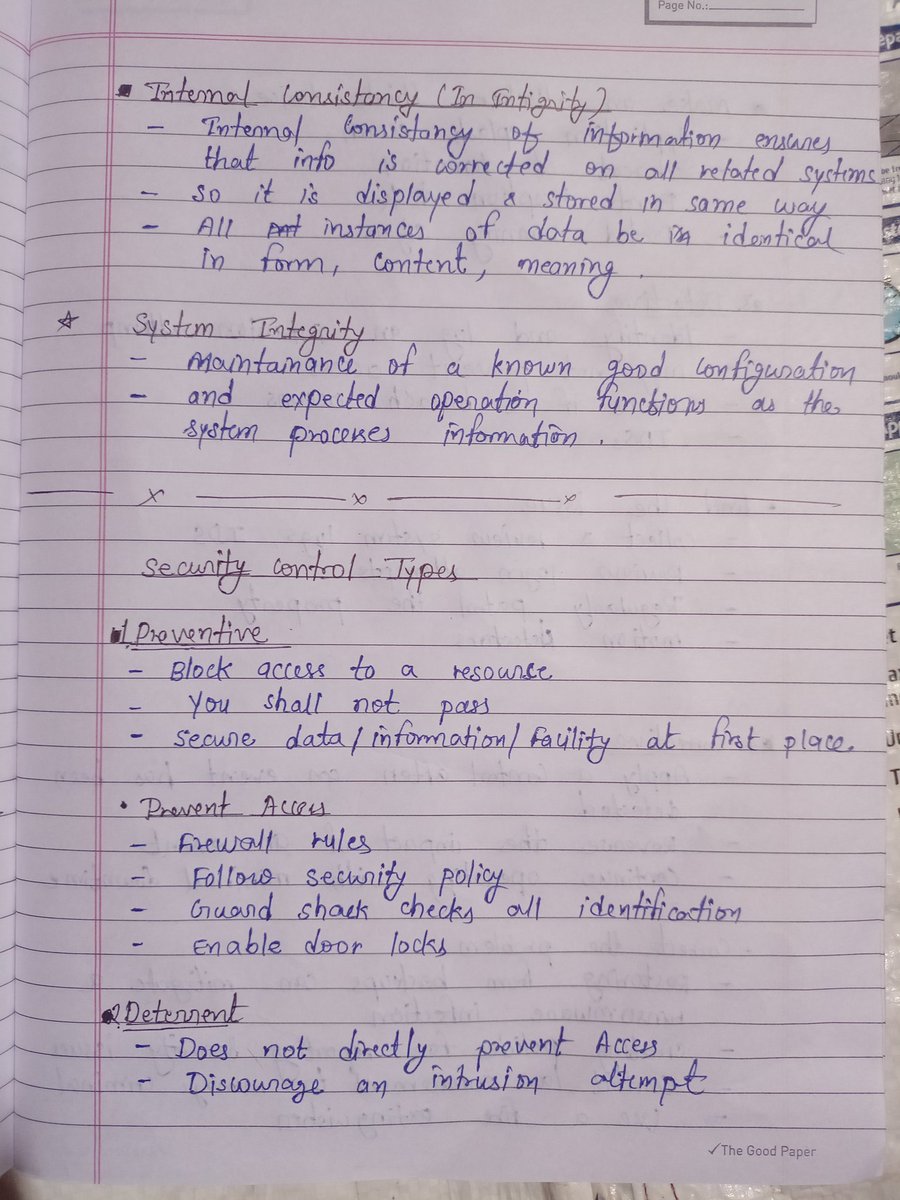
Day 12/21 Certified In Cybersecurity by ISC2. Today i have covered Security Controls , their categories and types. #ISC2 #Cybersecurity #Securitycontrols My notes ✍🏻
Why rooting and jailbreaking make you a target - helpnetsecurity.com/2025/03/20/roo… - @Zimperium #MobileDevices #MobileSecurity #SecurityControls #Android #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

Looking for a comprehensive solution for device management? Look no further than JAMF Pro! Take control of your devices with ease through zero-touch deployments and advanced security controls. #DeviceConfiguration #SecurityControls #JAMFPro #RadiusSystems
🔒 #ArtificialIntelligence #SecurityControls alone aren’t enough. To securely deploy AI, organizations need a balance of security, #Governance, and #Compliance. Learn the six categories of AI controls you can’t afford to ignore. Read the blog → sans.org/u/1AMB
Stop guessing. Start qualifying. Practical steps to keep coverage in 2026. Live Q&A: Sept 25 • 10am PT. Register: bit.ly/3JWqh1N #CyberInsurance #SMB #SecurityControls #Compliance

🟠 #CAASM [mini]-course 🟠 Why is asset visibility so important? 🤔 Better #attacksurface visibility can lead to proactively identifying gaps in your current #securitycontrols and prioritizing potential #exposures critical to your business. Dive deeper: ow.ly/l9x250SU2gb
![NetSPI's tweet image. 🟠 #CAASM [mini]-course 🟠 Why is asset visibility so important? 🤔
Better #attacksurface visibility can lead to proactively identifying gaps in your current #securitycontrols and prioritizing potential #exposures critical to your business.
Dive deeper: ow.ly/l9x250SU2gb](https://pbs.twimg.com/media/GXW7MfgXkAEQO3-.png)
Protect your organization from #Mallox ransomware with AttackIQ's new attack graph. ⚔️ Test your #SecurityControls and keep business operations moving. 👉Check it out now: bit.ly/3ZfJaCu #Cybersecurity #ThreatIntelligence

Join @LarryWhiteside for a thought-provoking talk on the importance of shifting compliance left to enhance our #cybersecurity & #compliance posture. Stay ahead of the game and learn how to create a near real-time view of #securitycontrols. bit.ly/3Yfzl4i #PlanetCyberSec

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Sunday 59.4K posts
- 2. Mateta 6,031 posts
- 3. Stockton 28.4K posts
- 4. #BNewEraBirthdayConcert 1.17M posts
- 5. #ViratKohli 49.2K posts
- 6. #sundayvibes 3,816 posts
- 7. Auburn 41.7K posts
- 8. #INDvSA 77.2K posts
- 9. #JimmySeaFanconD2 374K posts
- 10. Bama 30.1K posts
- 11. Duke 33.5K posts
- 12. Crystal Palace 21.1K posts
- 13. BECKY BIRTHDAY CONCERT 1.09M posts
- 14. PERTHSANTA LUMINOUS SKIN 362K posts
- 15. Notre Dame 26.4K posts
- 16. Lane Kiffin 49.6K posts
- 17. Ewing 1,403 posts
- 18. Advent 27.1K posts
- 19. Stanford 10.2K posts
- 20. Austin Theory 5,661 posts