#zerotrust search results
Stop wrestling with OAuth boilerplate for your internal tools. Cloudflare Access now supports Managed OAuth, letting you connect to GitHub and GitLab with zero custom code. Identity-aware security just got a lot faster. #AgentsWeek #ZeroTrust cfl.re/41RRzwh
Stop fighting VPN logins for autonomous software. Cloudflare Mesh is here. A developer-friendly private network for your services, nodes, and AI agents. Connect VPCs and local hardware in minutes. #CloudflareMesh #AgentsWeek #ZeroTrust cfl.re/4ejjsV8
If your traffic isn't encrypted, you have no privacy. Your ISP is logging every move. Step 1 of the Zero Trust mindset: Encrypt your connection. #Privacy #CyberSecurity #ZeroTrust
There is a different approach. Cryptographic proof of identity. Without key exchange. No database. No token. No chain. Just you. Patent pending. #identity #cryptography #zerotrust #securitynotpolitics
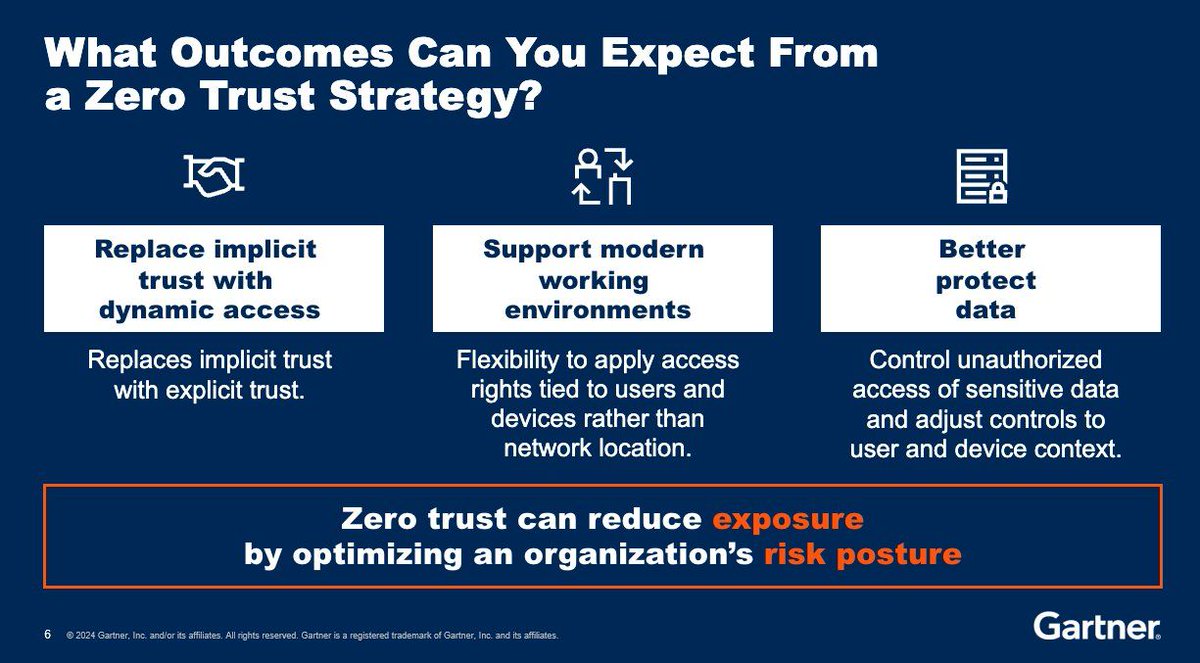
A Zero Trust strategy enhances security by eliminating implicit trust and verifying all access requests. It adapts to modern work environments, provides flexible access controls, and protects sensitive data. #infographic by @Gartner_inc rt @antgrasso #ZeroTrust #CyberSecurity
Stolen credentials caused 22% of initial network breaches in 2025. Identity-centric Zero Trust enforces least privilege, continuous authentication, device trust, and segmentation to limit attack impact. #IdentitySecurity #ZeroTrust #USA ift.tt/lVLnx9G
🎖️ El Curso de Ciberseguridad está permanente disponible en el aula virtual para acceso inmediato. 📲 WhatsApp: wa.me/51949304030 🌐 reydes.com/e/Curso_de_Cib… #datasecurity #zerotrust #vulnerability #cyberattack #threatintel #databreach #cybersecurity

Identity is now the attack surface. As Shane Barney explains: “Attackers are logging in.” Credentials, API keys, and tokens are driving modern breaches. What’s your take on identity-first security? 👇 #IdentitySecurity #ZeroTrust #Cybersecurity #CISO #AccessControl

"Looking good" on a security dashboard isn't the same as being secure. @OpenVPN CEO Francis Dinha's recent @Forbes article is a wake-up call for anyone reporting cyber risk to a board. Read it: openv.pn/4e7WTme #Cybersecurity #InfoSec #ZeroTrust #CISO
TRC analysis shows attackers exploiting CVE-2026-20133 in Cisco SD-WAN Manager to access sensitive information, then escalating privileges and moving laterally across networks. Runtime segmentation helps contain such post-compromise activity. #ZeroTrust 🔗 Full breakdown:
aviatrix.ai
CISA Flags Active Exploitation of Cisco SD-WAN Vulnerability CVE-2026-20133
CISA reports active exploitation of Cisco Catalyst SD-WAN Manager vulnerability CVE-2026-20133, urging immediate patching to prevent unauthorized data access.
Secure your microservices with Service Mesh + Identity. Enforce Zero Trust, control privileged access & reduce risk. Wiseman Infosec helps you implement it right. 📩[email protected] 🌐wisemaninfosec.com #CyberSecurity #ZeroTrust #PAM #CloudSecurity #WisemanInfosec

Your cloud model shapes your security outcomes. Get this Gartner® report on aligning cloud operating models with smarter security control decisions. Download →openv.pn/3Qm82WY #CloudSecurity #ZeroTrust #CyberSecurity

📝 AI Security 2026: Defending the Agentic Enterprise 🔗 Read more: blog.thecgaigroup.com/agentic-ai-sec… #AI #Cybersecurity #ZeroTrust #CGAIGroup

Legacy VPNs can't keep up with modern IT.⚡ App-level access. Single dashboard. 33K users deployed in 5 days. Modernize before an incident forces you to. See it in action → 🔗 zurl.co/qDQJY #ZeroTrust #ITServices

Die Ära der einfachen Passwörter geht zu Ende. Während Unternehmen weltweit auf #MFA setzen, entsteht ein gefährlicher Trugschluss: Die einmalige Abfrage eines zweiten Faktors macht ein System noch lange nicht sicher im Sinne von #ZeroTrust. it-daily.net/it-sicherheit/…
Privileged Access Management (PAM) is crucial in enabling zero trust and defense-in-depth strategies that extend beyond mere compliance requirements. Source @Gartner_inc Link gtnr.it/36xmEvY rt @antgrasso #CyberSecurity #ZeroTrust #IAM

Catch up with all the latest Federal IT news this week Top Headlines: 🤖 GSA looks to automate a million work hours 🔐 AI is pushing agencies to rethink Zero Trust risk 🌐 State Department explores agentic AI 🔗 Read more: makpar.com/fed-round-up/g… #FederalIT #AI #ZeroTrust

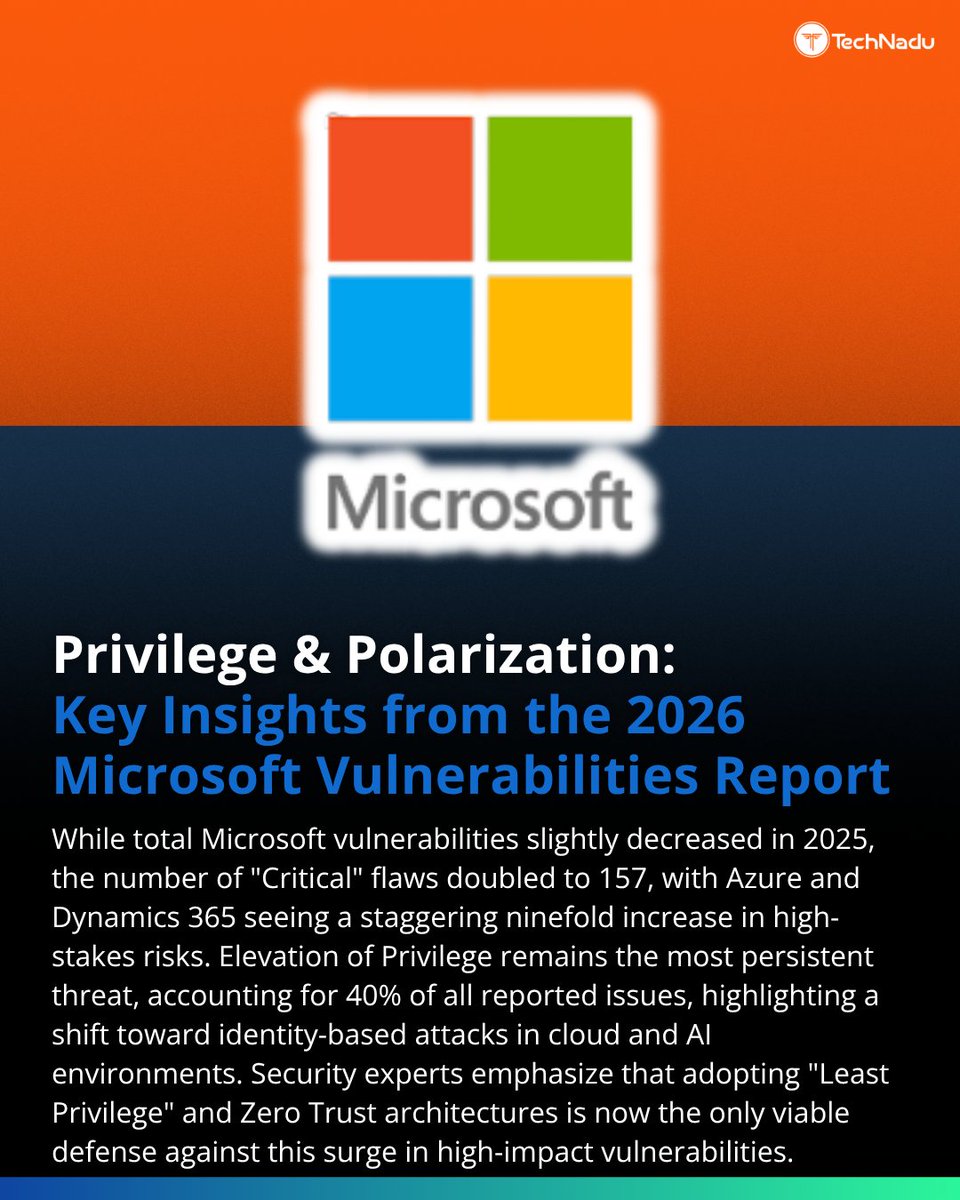
📊 @Microsoft Vulnerabilities Report 2026 Critical vulns doubled Azure spike 9x Privilege = biggest risk 💬 Patch or identity first? Follow @TechNadu #CyberSecurity #ZeroTrust
As devices scale faster than policies, traditional security falls short. 📡 5G SASE from NTT DATA and @PaloAltoNtwks embeds #ZeroTrust directly into connectivity for secure operations at scale. Learn more: youtu.be/23xMbrjLAqE

youtube.com
YouTube
NTT DATA, Inc.
There is a different approach. Cryptographic proof of identity. Without key exchange. No database. No token. No chain. Just you. Patent pending. #identity #cryptography #zerotrust #securitynotpolitics
Secure your microservices with Service Mesh + Identity. Enforce Zero Trust, control privileged access & reduce risk. Wiseman Infosec helps you implement it right. 📩[email protected] 🌐wisemaninfosec.com #CyberSecurity #ZeroTrust #PAM #CloudSecurity #WisemanInfosec

If your traffic isn't encrypted, you have no privacy. Your ISP is logging every move. Step 1 of the Zero Trust mindset: Encrypt your connection. #Privacy #CyberSecurity #ZeroTrust
Legacy VPNs can't keep up with modern IT.⚡ App-level access. Single dashboard. 33K users deployed in 5 days. Modernize before an incident forces you to. See it in action → 🔗 zurl.co/qDQJY #ZeroTrust #ITServices

Ping Identity named 2026 Google Cloud Security Partner of the Year for identity and access management... Read more: chiefit.me/ping-identity-… @pingidentity #CyberSecurity #AccessManagement #ZeroTrust #CloudSecurity #AIsecurity #GoogleCloud #DigitalIdentity #TechInnovation #InfoSec
The Vercel incident is a reminder that the real AI security problem is not just the model — it’s the access around it. Read more here - tinyurl.com/4bznymzb #AISecurity #CloudSecurity #ZeroTrust


Hybrid work has outgrown traditional security. Perimeter models no longer provide control. Zero Trust Security Services enable secure, identity-based access for distributed teams. Read more : unicorptechnologies.com/post/zero-trus… #ZeroTrust #CyberSecurity #HybridWork #UnicorpTechnologies

🔥 GitHub Trending openclaw-security-practice-guide by SlowMist: security for high-privilege AI agents. Agentic Zero-Trust Architecture mitigates prompt injection, supply chain poisoning & destructive ops. Send it to OpenClaw to deploy. ⭐ 2,789 #AISecurity #ZeroTrust

Join us on 5/7 as we deconstruct the FBI’s latest directives and provide a roadmap for organizations holding sensitive data to eliminate account takeovers for good, & why they're specifically mandating a move away from legacy MFA. #passwordless #zerotrust sprou.tt/11z0BIzbY7Z
La promesa de #SASE no es integrar piezas, sino converger red y seguridad en un solo sistema que elimine fricciones y cierre brechas operativas. ✅ #ZeroTrust #Nuebe #ProtecciónDeDatos @FortinetLATAM itmastersmag.com/ciberseguridad…
Your firewall trusts your network. That's the problem. Zero Trust verifies every packet, every device, every request — always. Breach impact drops 50%. flexusnet.com #ZeroTrust #CyberArchitecture

Check It Out >> Episode 17 in Series 6 of @TCyberCast, the @CorixPartners Cyber #Security Transformation #Podcast, hosted by @Corix_JC "#ZeroTrust, Agentic #AI, and the Future of #Identity Management" >> buff.ly/f3fuIGa #tech #cybersecurity #leadership #CIO #CISO #IAM

Hot take: Zscaler + OpenAI shows Zero Trust accelerating AI, not just securing it. Invisible apps, no VPNs, agent-friendly runtime. Sec teams still clinging to firewalls? Time to evolve. #ZeroTrust #AISecurity
Achieve Zero Trust at the browser layer. Learn how @Snowflake's security leaders use Chrome Enterprise Premium for deep visibility and granular control. Register here. #ZeroTrust #Cybersecurity #DataCloud #GoogleCloudPartners google.smh.re/5Tf8
En Secure Flow Hub usamos Fortinet y switches Cisco para micro-segmentar su red corporativa. Instalamos barreras de contención por departamento. Si un equipo es comprometido, el resto de la infraestructura sigue intacta. #SecureFlowHub #ZeroTrust

Carahsoft hosted the @illumio Public Sector Summit, welcoming 120+ Federal, State and Local #cyberleaders for a half-day program focused on operationalizing #ZeroTrust. Attendees explored real-world strategies across #AI security, OT environments and implementation insights from




The AI era demands CISOs move beyond static audits to runtime visibility, AI-driven alert triage, least-privilege enforcement, and realistic incident rehearsals to address evolving threats. #ZeroTrust #AIsec #Innovation ift.tt/dEW3p2H
Your cloud model shapes your security outcomes. Get this Gartner® report on aligning cloud operating models with smarter security control decisions. Download →openv.pn/3Qm82WY #CloudSecurity #ZeroTrust #CyberSecurity

TRC analysis shows attackers exploiting authentication bypass in Siemens SINEC NMS (CVE-2026-24032) to gain unauthorized access, then escalate privileges and move laterally across managed infrastructure. Runtime segmentation helps contain such post-compromise activity. #ZeroTrust
aviatrix.ai
Siemens SINEC NMS Authentication Bypass Vulnerability (CVE-2026-24032)
A critical authentication bypass vulnerability in Siemens SINEC NMS (CVE-2026-24032) allows unauthenticated remote access to network management functions. Immediate updates are recommended.
A healthy ecosystem starts at the soil level — the layer everything else depends on. #ZeroTrust architectures work the same way. If the foundation (the #hypervisor) is implicitly trusted, everything above it is at risk. Zero Trust doesn’t stop at identity. It starts at the

Something went wrong.
Something went wrong.
United States Trends
- 1. #TexasHockey N/A
- 2. #mnwild N/A
- 3. Wyatt Johnston N/A
- 4. Devin Booker N/A
- 5. Caruso N/A
- 6. Stars N/A
- 7. #bucciovertimechallenge N/A
- 8. Hughes N/A
- 9. Jamie Benn N/A
- 10. Double OT N/A
- 11. Dillon Brooks N/A
- 12. Leftover N/A
- 13. Boldy N/A
- 14. Jalen Williams N/A
- 15. #Survivor50 N/A
- 16. Counseling N/A
- 17. JDub N/A
- 18. #beyondthevilla N/A
- 19. Duchene N/A
- 20. Patrick Bailey N/A