now that the reac2shell forced CTFers to look into flight protocol and RSC, there is a high chance of few more bugs coming out of it with similar impact. its a pretty complex protocol for developers to implement, and complexity is a perfect breeding ground for weird state…
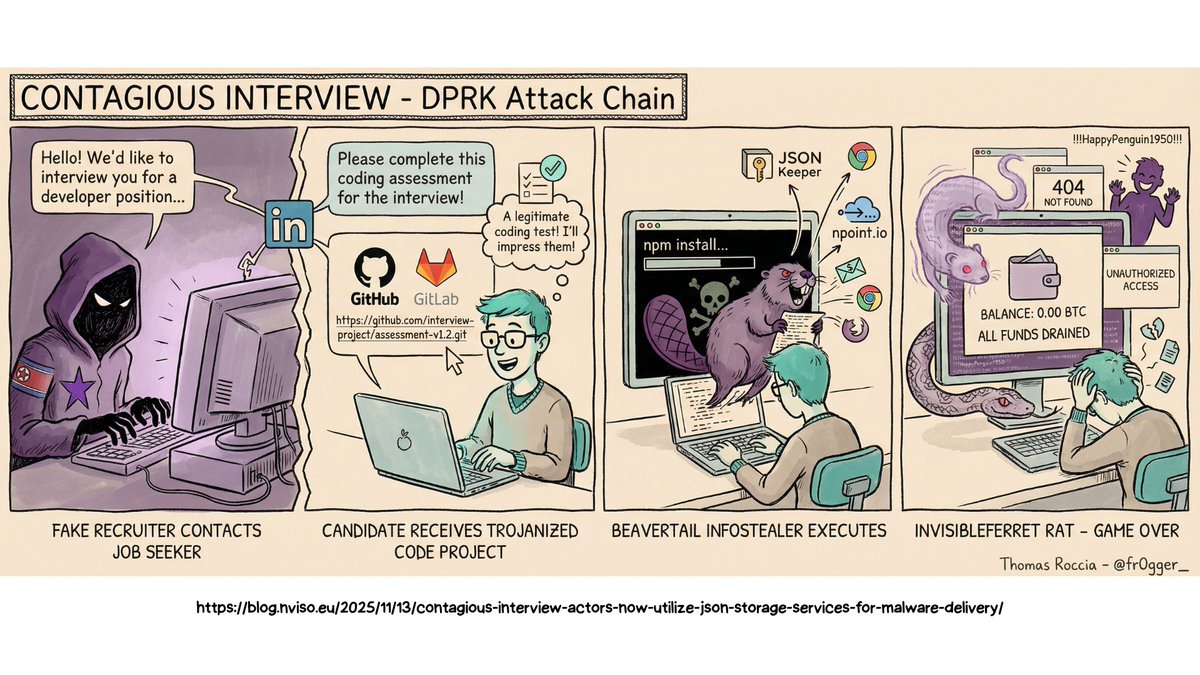
‼️🇰🇵 Meet North Korean recruiter 'Aaron,' who infiltrates Western companies by using AI and posing as a remote IT worker using stolen or rented identities. He was lured into a sandbox by researchers, who observed the wild APT in a controlled setting to see what he would do.
"Within hours of the public disclosure of CVE-2025-55182 (React2Shell) on December 3, 2025, Amazon threat intelligence teams observed active exploitation attempts by multiple China state-nexus threat groups, including Earth Lamia and Jackpot Panda." aws.amazon.com/blogs/security…
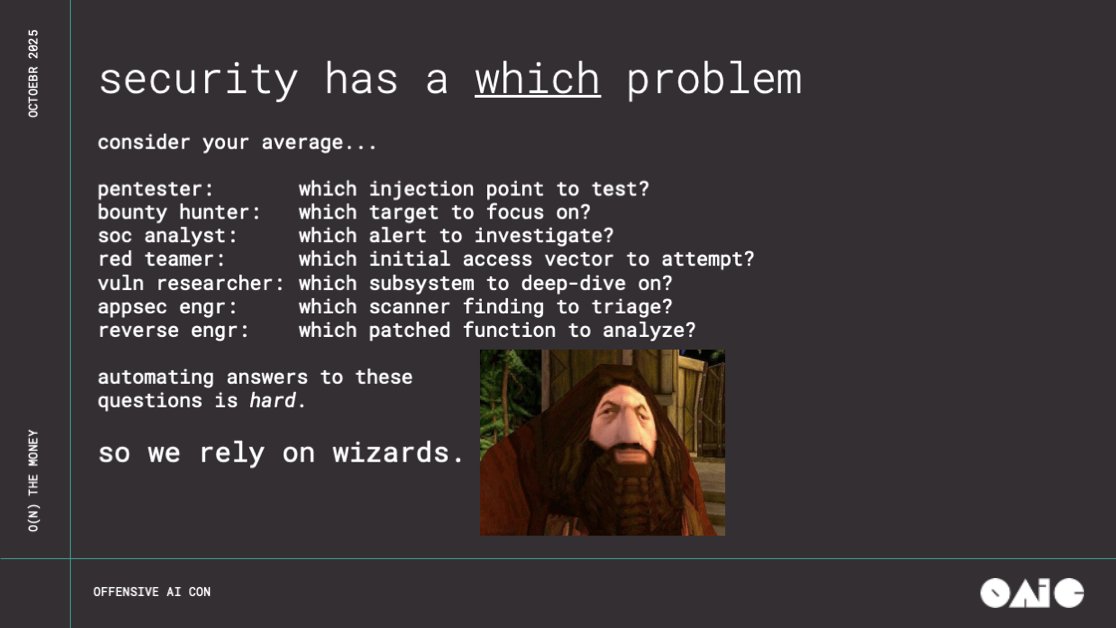
Problem I see is people are confusing code reasoning with hacker intuition. To understand where LLMs fit in AppSec vuln research, firstly we need to categorize the cognitive load of vulnerabilities: 1. Pattern Matching Tracing user input for XSS, IDORs, Injections etc. If your…
When the POC comes out, it’ll be a humbling moment for LLMs and how we use them. What’s circulating is extremely naive and incorrect. Experienced engineers are sharing plausible-sounding hallucinations from frontier models. Reminder to bump React, Next & frameworks.
2025 showed clearly — the myth of a “safe Mac” is dead. According to Moonlock’s annual threat report: • macOS backdoor variants 📈 up by 67% • Stealer malware families 📈 up by 17% • Over 80 countries hit by major stealer campaigns In short: Macs are no longer “safe by…

One of the most consistent trends I’ve observed in cyber security in my career - is the inability for companies/vendors to objectively differentiate themselves from their competition (outside of cost). I’ve seen this across multiple domains including: Red teaming Incident…
In regards to "cyber influencers", here is a list of people I think are actually great. However, I am extremely biased toward malware related content and/or low-level programming stuff. Unfortunately, some of the really technical people I like also do not post too often. They…
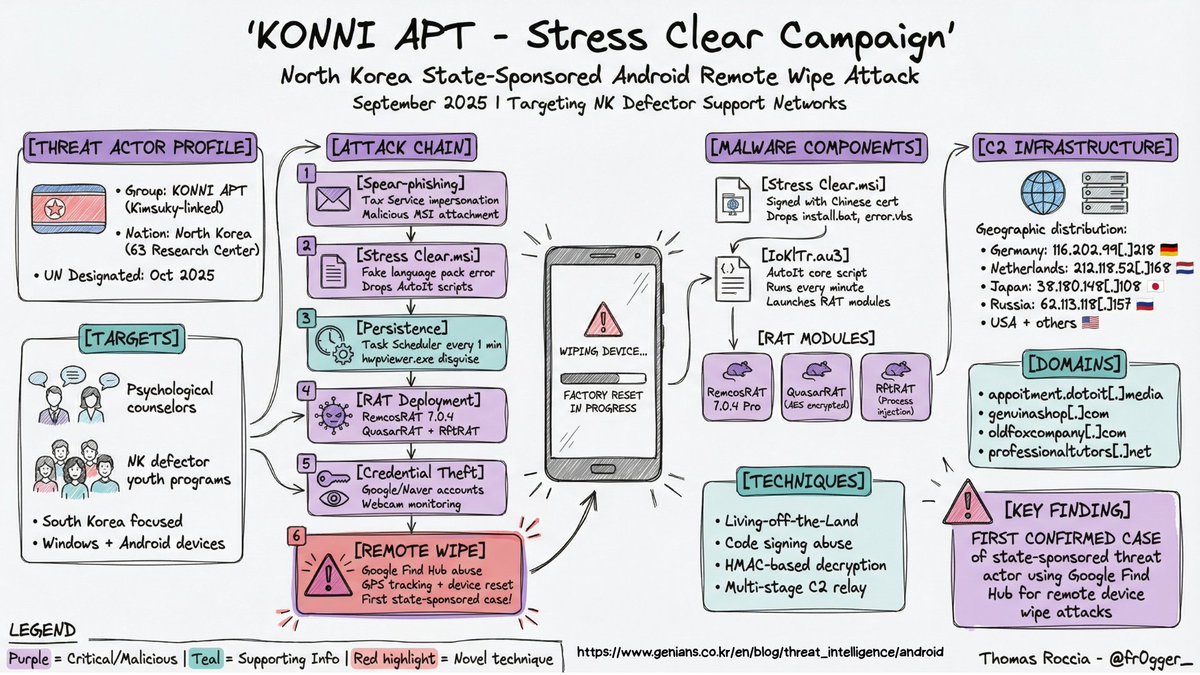
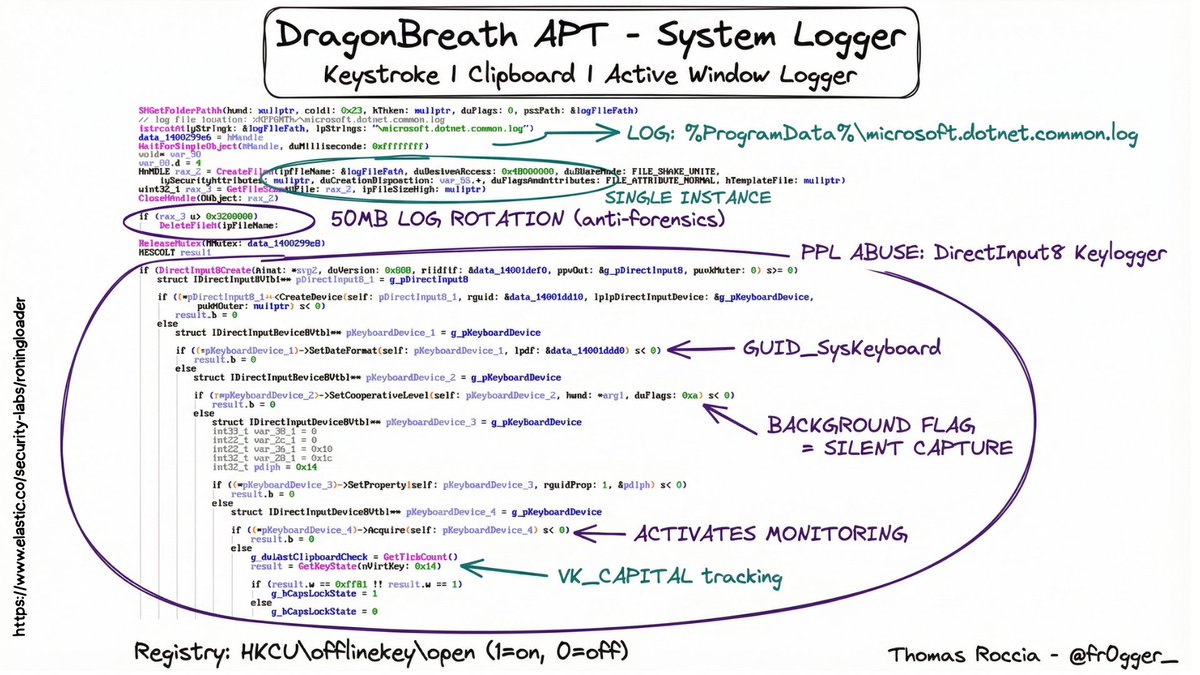
🎁 GenAI x Sec Advent 1 - Visual Threat Intelligence If you follow my work you know I am a big fan of visualization to explain complex or technical content. I used to spend days building the perfect infographic, but now I can generate one in a single shot thanks to LLM…
On November 25, 2025, an engineer’s machine was affected by the Shai-Hulud npm supply chain malware. The malware accessed GitHub credentials and made unauthorized changes to some of our repositories. Once we detected the activity, we immediately revoked exposed credentials,…
From one "unnamed" RAT: Malware dev task: "Be innovative and make sure the file is deleted." Malware dev: "Got it, boss. Let’s delete it 10× just to be sure!" 🤡🗑️💥

''O(N) the Money: Scaling Vulnerability Research with LLMs'' #infosec #pentest #redteam #blueteam noperator.dev/posts/on-the-m…
This. Alert & CVE fatigue are real. Perpetually growing backlogs of bugs means no one gives a shit anymore. We need clear writeups that consider exploitability, and include a patch. If you can automate finding bugs, you can automate submitting fixes.
Denial of Attention is a real security threat in the AI era and I am surprised we don't hear about this more
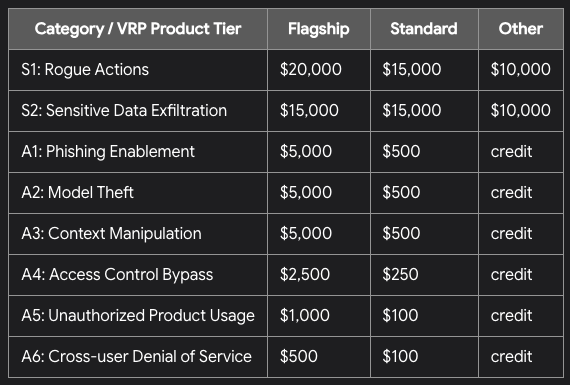
Google recently announced their new AI Vulnerability Research Program: Rewards are medium in comparison to Chrome VRP, but overall solid, considering an easier entry and non-binary focus. This is a good security bounty option for beginners. bughunters.google.com/blog/611688725…
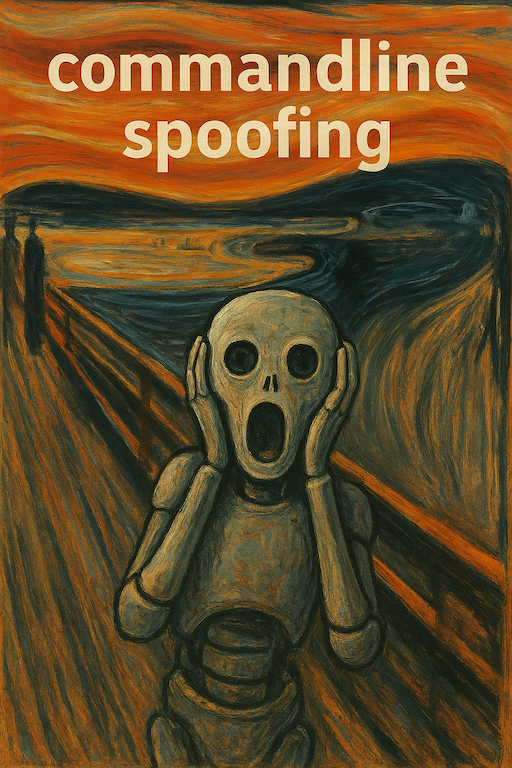
This blogpost is interesting - has Windows internals, my own novel solution to a problem red teamers have had for a while, EDR bypasses, debugging and much more. Spoofing command lines on Windows and solving the problem of length limitations: github.com/yo-yo-yo-jbo/c…
If you want to learn more about malware the easiest method is learning malware TTPs (Threats Tactics and Procedures). Basically, understand some of the techniques employed by malware authors to do stuff Some malware techniques are simple and old Some malware techniques are…

People act like threat actors have a corporate strategy retreat every Q4. The imaginary meeting: "Okay team, Ransomware had a great run in 2025, but let's pivot to something totally new and untested for 2026 just for the vibe. The reality: "Does it still work? Yes? Okay, keep…
Silver lining of the npm worm situation - the chaos probably caused SLSH to lose access to victim cloud infra due to companies rolling credentials.
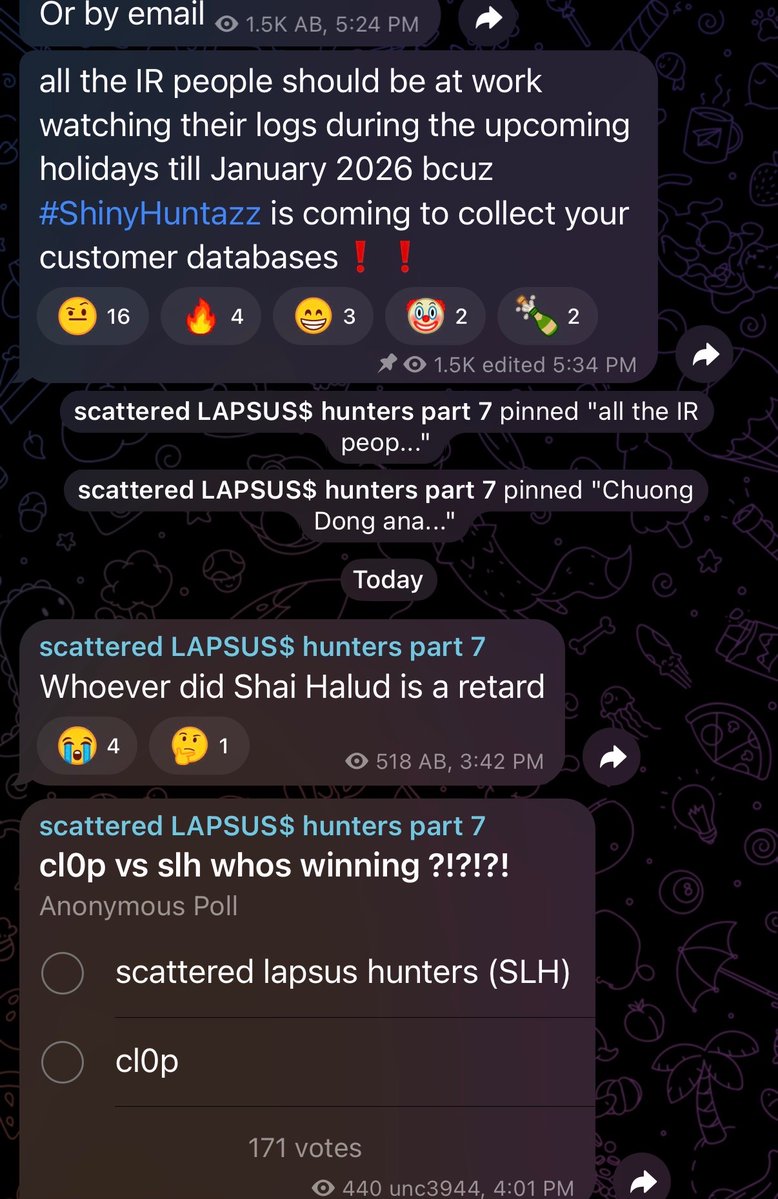
We're updating the Aikido blog post in real time with findings as we uncover the scope and impact of the second coming of Shai Hulud: aikido.dev/blog/shai-hulu…
A Reverse Engineer’s Anatomy of the macOS Boot Chain & Security Architecture reddit.com/r/netsec/comme…
United States 趨勢
- 1. Lando 375K posts
- 2. Pearl Harbor 31.1K posts
- 3. Oscar 188K posts
- 4. McLaren 110K posts
- 5. #AskFFT N/A
- 6. #AbuDhabiGP 298K posts
- 7. Good Sunday 77.2K posts
- 8. Yuki 132K posts
- 9. #sundayvibes 6,406 posts
- 10. Tulane 19.8K posts
- 11. Charles 118K posts
- 12. Go Bills 4,590 posts
- 13. Zak Brown 10.3K posts
- 14. Verstappen 165K posts
- 15. Duke 65.2K posts
- 16. #Formula1 10.2K posts
- 17. World Champion 191K posts
- 18. Full PPR N/A
- 19. Checo 19.4K posts
- 20. #23yearsOfHOONmoon 43.8K posts
Something went wrong.
Something went wrong.