#cyberrisks search results
#CybersecurityTraining empowers employees to recognize #CyberRisks, prevent mistakes, & build a culture of #SecurityAwareness across your #Organization. #StrongTeams = #SafeSystems To learn more, 🔗 bit.ly/4cnYU9W 📞 (954)727-1957 #FDSGlobal #Cybersecurity

In an interview with Euronews, Eva Rudin explains how the growing number of connected endpoints is increasing #CyberRisks worldwide & how #AI is transforming both sides of the cybersecurity landscape - accelerating attacks while strengthening defence 👇 thls.co/24fX50Yv8N4




Join our #Webinar on October 28, led by Sentil Velaytham, to explore the current #ThreatLandscape, emerging #CyberRisks, proactive defense strategies, and ways to build a #CyberResilience framework. Register now: buff.ly/3YgXfPq #ECCouncil #Cybersecurity

How are developing countries navigating the growing threats of #CyberRisks? Get the answer in our report! wrld.bg/G5v150TpfBp #Cybersecurity

Why Restarting Your Smartphone Daily Can Improve Security and Reduce Cyber Risks cysecurity.news/2026/04/why-re… #AndroidSmartphone #Cyberrisks #CyberSecurity
Australia faces rising cyber risk as threat actors surge ahead... Read more: australiancybersecuritymagazine.com.au/australia-face… @Microsoft #cyberrisks #DigitalDefense #Report #threatactors #cybercrime #cyberthreat #cyberattacks #technology #ransomware #Cybersecurity
🎙️ We have compiled the Top 5 Cyber Threat Intelligence podcasts you should listen to. Remaining knowledgeable and ready is essential in the constantly changing realm of #cyberrisks. These Top 5 Threat Intelligence Podcasts offer valuable insights, useful techniques, and expert

#Trustees should review #CyberRisks and #Scam vulnerabilities, @RSMUK ...#Pensions #fraud is often committed through #CyberAttacks which use social engineering - often on an industrial scale - to trick people into transferring funds or revealing data to... tinyurl.com/mrtbdmfu
Chicago: Ready to secure your future? Join us at #ProofpointProtect to learn how to stay ahead of the key #cyberrisks that impact your people today: targeted threats, impersonation, identity and data loss. Mark your calendar: ow.ly/po3o50TQmCt.

A new ISC2 survey reveals that 70% of cybersecurity professionals are highly concerned about third-party supply chain risks. Full story buff.ly/BdR6q2E #Tech | #News | #CyberRisks | #SupplyChain
Botnet Moves to Blockchain, Evades Traditional Takedowns cysecurity.news/2026/03/botnet… #Blockchain #Botnet #Cyberrisks

📢 1 day to go! Discover the world of advancing technology and evolving #cyberrisks with us! 💻 An exclusive webinar awaits you. Learn from 𝐢𝐧𝐝𝐮𝐬𝐭𝐫𝐲 𝐥𝐞𝐚𝐝𝐞𝐫𝐬 about the latest trends and best practices in #TechnologyAudit. ✴️ 𝐂𝐥𝐢𝐜𝐤 𝐡𝐞𝐫𝐞 𝐭𝐨 𝐬𝐞𝐜𝐮𝐫𝐞

We observed a cybersecurity gap among #NGOs in International Geneva, causing #cyberrisks. 🛡️ Our CyberPeace Analytical Report aims to provide actionable recommendations to build capacities & resilience for underserved organisations. Explore the report ↘️ geneva.cyberpeace.ngo

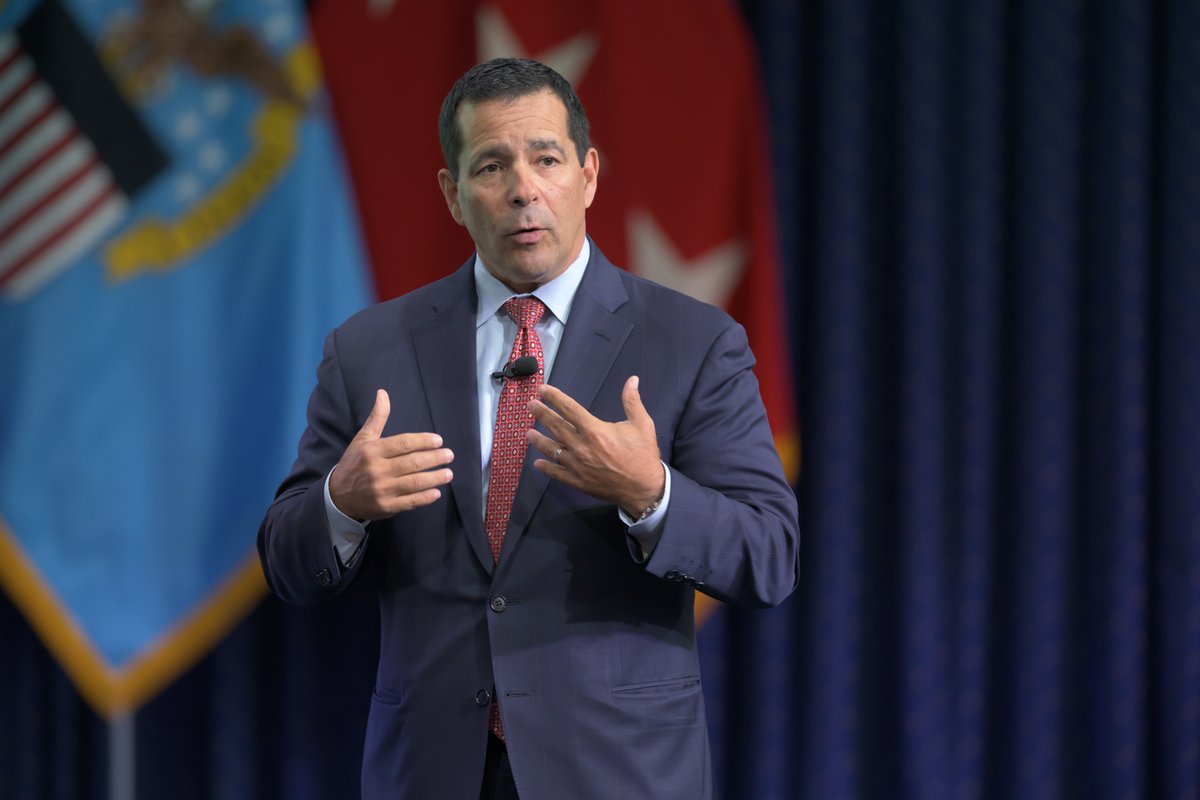
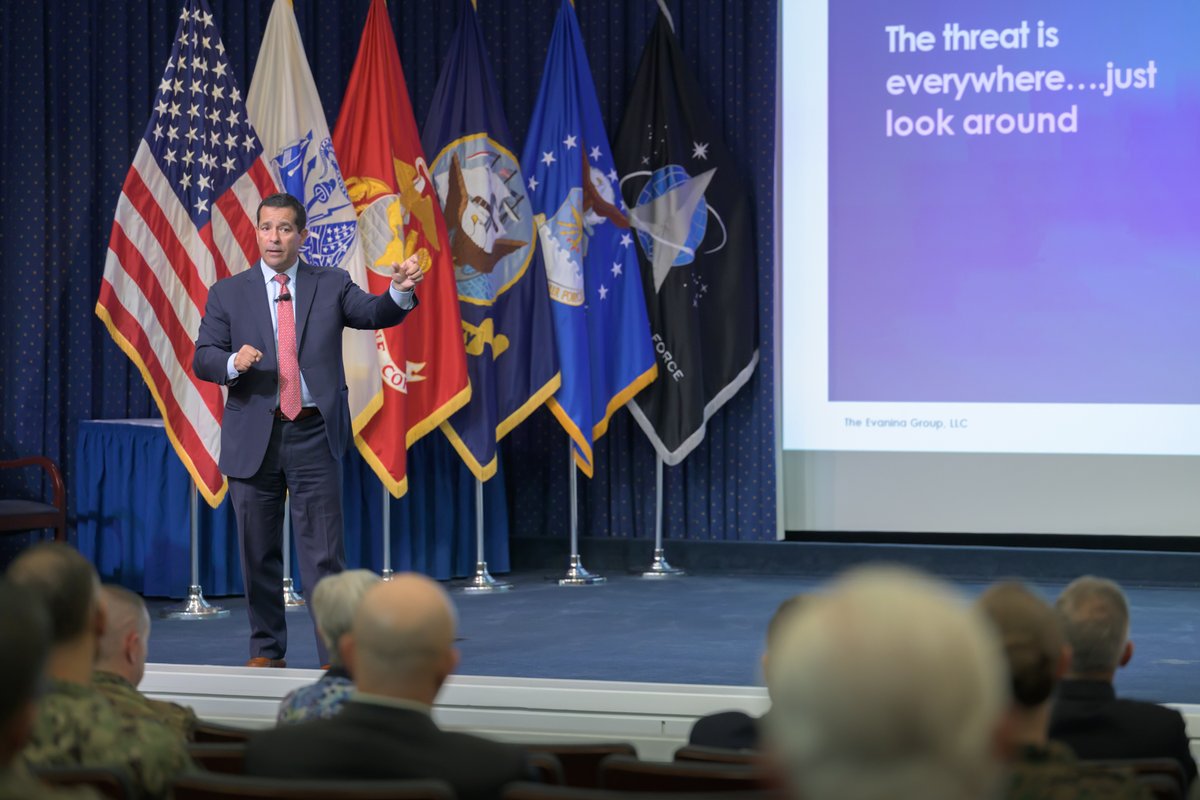
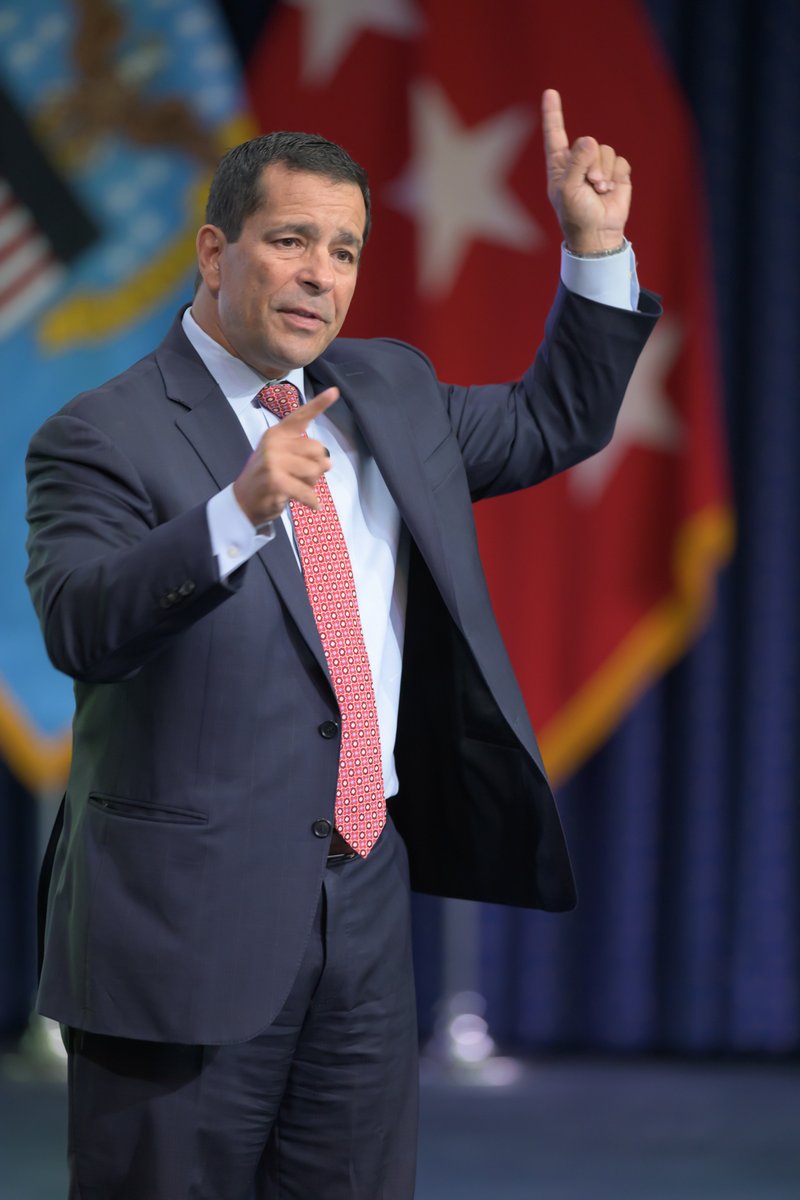
Former National #Counterintelligence and Security Center Director William Evanina spoke at our recent #WarfighterTalk about #CyberRisks, vendor vulnerabilities, and the need to modernize how we protect the #DefenseSupplyChain. ➡️ Read more on Evanina's presentation, with a link

Ransomware sublimit doesn’t apply to cyber claim: Court #ClaimsDisputes #CyberRisks #EmergingRisks #InsurTech #RiskManagement bit.ly/4r085nQ
Cybercriminals sharpen skills, insurers seek to adapt #CyberRisks #Axa #CyberCriminals #RiskManagement bit.ly/40eQihR
businessinsurance.com
Cybercriminals sharpen skills, insurers seek to adapt
Cybercriminals continue to hone and improve their tactics and methods for conducting attacks, a panel of experts said.
#Climate, #GeopoliticalConflict and #CyberRisks Top Concerns in Latest AXA Survey carriermanagement.com/news/2024/11/0…
Data Breach at Cartier Highlights Growing Cyber Risks in Luxury Sector cysecurity.news/2025/06/data-b… #CatierHighlights #CyberCrime #cyberrisks

#CybersecurityTraining empowers employees to recognize #CyberRisks, prevent mistakes, & build a culture of #SecurityAwareness across your #Organization. #StrongTeams = #SafeSystems To learn more, 🔗 bit.ly/4cnYU9W 📞 (954)727-1957 #FDSGlobal #Cybersecurity

Medtronic says cyberattack has not disrupted operations #CyberRisks #Medtronic #RiskManagement #CyberAttacks bit.ly/4ubNbUP
Nirmala Sitharaman Calls for Vigilance as Cyber Risks Rise in Markets @suryamurthy #NirmalaSitharaman #Vigilance #CyberRisks southasianherald.com/nirmala-sithar…
#Global #payments: Leaders overestimate tech readiness. Aging systems, #cyberrisks & complex regs stall #innovation. Blueprint: C-suite ownership, talent, agility. Use modular #API platforms. Treat compliance as strategic lever #fintech youtu.be/9av2zrtObLE?si…

youtube.com
YouTube
Stanley's Musings (SET)
Editorial: One giant, complex leap for insurance #CyberRisks #EmergingRisks #InsurTech #RiskManagement bit.ly/48mq3KU
Most school #cyberrisks now happen inside tools like #GoogleWorkspace & #Microsoft365, not the perimeter. As Charlie Sander shares in @DA_magazine, cloud sync can turn small incidents into district-wide issues fast. Visibility in the cloud isn’t optional. hubs.ly/Q04dp1yZ0
AI Training Not a Priority, Despite Skills Gap (via @Digitfyi) - digit.fyi/ai-training-no… #AI #training #cyberrisks
Cowbell unveils cover for AI, quantum computing risks #CyberRisks #EmergingRisks #RiskManagement #InsurTech bit.ly/4eCq697
Ignoring AI-driven threats could cost you everything, your money, your reputation, and your operations. Learn how to fight back with smarter tools and strategies. Learn more: crestechnology.com/it-services/cy… #ManagedIT #CyberSecurity #CyberRisks #ArtificialIntelligence #CRESTechnology

Governor Abbott signed the strongest law in American banning hostile foreign adversaries from buying land in Texas. #austin #ChinaMadeMedicalDeices #CyberRisks #GregAbbott #MegaDoctorNews megadoctornews.com/governor-order…
#Global #payments: Leaders overestimate tech readiness. Aging systems, #cyberrisks & complex regs stall #innovation. Blueprint: C-suite ownership, talent, agility. Use modular #API platforms. Treat compliance as strategic lever #fintech youtu.be/9av2zrtObLE?si…

youtube.com
YouTube
Stanley's Musings (SET)
#Global #payments: Leaders overestimate tech readiness. Aging systems, #cyberrisks & complex regs stall #innovation. Blueprint: C-suite ownership, talent, agility. Use modular #API platforms. Treat compliance as strategic lever #fintech youtu.be/9av2zrtObLE?si…

youtube.com
YouTube
Stanley's Musings (SET)
Why Restarting Your Smartphone Daily Can Improve Security and Reduce Cyber Risks cysecurity.news/2026/04/why-re… #AndroidSmartphone #Cyberrisks #CyberSecurity
#Global #payments: Leaders overestimate tech readiness. Aging systems, #cyberrisks & complex regs stall #innovation. Blueprint: C-suite ownership, talent, agility. Use modular #API platforms. Treat compliance as strategic lever #fintech youtu.be/9av2zrtObLE?si…

youtube.com
YouTube
Stanley's Musings (SET)
#Global #payments: Leaders overestimate tech readiness. Aging systems, #cyberrisks & complex regs stall #innovation. Blueprint: C-suite ownership, talent, agility. Use modular #API platforms. Treat compliance as strategic lever #fintech youtu.be/9av2zrtObLE?si…

youtube.com
YouTube
Stanley's Musings (SET)
Read the new edition of our Newsletter: "Emerging Cyber Risks: Why Reviewing Controls Is Not Enough". Subscribe to read more on our insightful articles: linkedin.com/build-relation… #CyberRisks #CyberSecurity #Controls #ControlsReview #PoliciesReview #Governance #Technology

Insurers, brokers adjust as AI exclusions emerge #CyberRisks #EmergingRisks #AI #RiskManagement #GeneralLiability #InsurTech bit.ly/41ggUQ6
businessinsurance.com
Insurers, brokers adjust as AI exclusions emerge
The commercial insurance industry is seeing the early stages of policy and contract wording updates and revisions relating to the rapidly expanding use of artificial intelligence.
Cyber threats like phishing, credential theft, and brute-force attacks are on the rise. Download a copy of our infographic on the key benefits of MFA to learn how it can protect your business. #MADSecurity #CyberRisks #Cybersecurity #MFA #SecureYourBusiness
What #cyberrisks should you be prepared to address? Get in touch to discuss how the team at Lemington Consulting can help with #cybersecurity solutions and strategies.
Court dismisses cyber coverage suit over fraudulent wire transfer #RiskManagement #CyberRisks #EmergingRisks #InsurTech bit.ly/4tiXt50
Remaining knowledgeable and ready is essential in the constantly changing realm of #cyberrisks. These Top 5 #Threat #Intelligence Books offer valuable insights, useful techniques, and expert information to assist in effectively recognizing, confronting, and fighting

Botnet Moves to Blockchain, Evades Traditional Takedowns cysecurity.news/2026/03/botnet… #Blockchain #Botnet #Cyberrisks

Why Restarting Your Smartphone Daily Can Improve Security and Reduce Cyber Risks cysecurity.news/2026/04/why-re… #AndroidSmartphone #Cyberrisks #CyberSecurity
🎙️ We have compiled the Top 5 Cyber Threat Intelligence podcasts you should listen to. Remaining knowledgeable and ready is essential in the constantly changing realm of #cyberrisks. These Top 5 Threat Intelligence Podcasts offer valuable insights, useful techniques, and expert

In this RIMS webinar on October 12, AXA XL's cyber experts will explore emerging trends related to targeted cyberattacks along with the current state of the cyber insurance market. Enroll today. bit.ly/45WogZL #cyberrisks #cybersecurity

Managing Vendor Cyber Risks: How Businesses Can Mitigate Third-Party Failures cysecurity.news/2025/03/managi… #CompanySecurity #CrowdStrike #Cyberrisks

How are developing countries navigating the growing threats of #CyberRisks? Get the answer in our report! wrld.bg/G5v150TpfBp #Cybersecurity

Learn how risk professionals can manage operational and cyber risks via the power of machine learning. Attend our webinar on November 7 and takeaway methods to optimize and mature your cybersecurity program. Register here: bit.ly/3FuXlbI #cyberrisks

Data loss incidents impact patient care - helpnetsecurity.com/2024/10/11/hea… - @proofpoint @PonemonPrivacy - #HealthcareCybersecurity #PatientSafety #CyberRisks #Ransomware #BEC #CyberSecurity #netsec #security #InfoSecurity #CISO #ITsecurity #CyberSecurityNews #SecurityNews

In an interview with Euronews, Eva Rudin explains how the growing number of connected endpoints is increasing #CyberRisks worldwide & how #AI is transforming both sides of the cybersecurity landscape - accelerating attacks while strengthening defence 👇 thls.co/24fX50Yv8N4




Is outsourcing IT to India cost-effective or overly complicated? Explore the full discussion on the pros, cons, and alternatives to outsourcing IT to India in our recent blog: bit.ly/4cnIDlL #Outsourcing #Tech #CyberRisks

Jess Fung, managing director and North American cyber analytics leader for @GuyCarpenter, explains how #cybercatastrophe models work and how they can be tailored to address #cyberrisks for small and medium-sized businesses. Watch now: bit.ly/4gnk8HU
David Derigiotis, president of brokerage and head of insurance for Flow, says cyber liability insurance is still a buyer's market and outlines the top concerns for insurers and policyholders. #cyberrisks #claims #insurers bit.ly/4djcNXv
⏰ Only 2 weeks left! Join PwC's Danny Chamings, Mimoent Haddouti and Tanium's Edwin Van Den Heuvel for an exclusive virtual discussion on #DORAregulation and managing #cyberrisks with confidence. Secure your spot now! 🚀 bit.ly/49WaJTd

Data Breach at Cartier Highlights Growing Cyber Risks in Luxury Sector cysecurity.news/2025/06/data-b… #CatierHighlights #CyberCrime #cyberrisks

Expanding your digital footprint increases #cyberrisks. Can you handle a major disruption? Discover how Group-IB’s #DigitalRiskProtection monitors, detects, and takes down threats in real time. Curious how it works? Read our blog: bit.ly/3y52d7h. #CyberSecurity

How are developing countries navigating the growing threats of #CyberRisks? wrld.bg/G5v150TpfBp #Cybersecurity

.@LumenTechCo & Akela Group Webinar – The cyber risks you can’t ignore australianfintech.com.au/lumen-technolo… #cybersecurity #security #cyberrisks #risks #australianfintech #fintech #fintechnews #financialtechnology #finance #technology #tech #technews #webinar

📢 1 day to go! Discover the world of advancing technology and evolving #cyberrisks with us! 💻 An exclusive webinar awaits you. Learn from 𝐢𝐧𝐝𝐮𝐬𝐭𝐫𝐲 𝐥𝐞𝐚𝐝𝐞𝐫𝐬 about the latest trends and best practices in #TechnologyAudit. ✴️ 𝐂𝐥𝐢𝐜𝐤 𝐡𝐞𝐫𝐞 𝐭𝐨 𝐬𝐞𝐜𝐮𝐫𝐞

Join our #Webinar on October 28, led by Sentil Velaytham, to explore the current #ThreatLandscape, emerging #CyberRisks, proactive defense strategies, and ways to build a #CyberResilience framework. Register now: buff.ly/3YgXfPq #ECCouncil #Cybersecurity

Something went wrong.
Something went wrong.
United States Trends
- 1. #LakeShow N/A
- 2. #SmackDown N/A
- 3. RJ Barrett N/A
- 4. Toronto N/A
- 5. McAvoy N/A
- 6. #TusksUp N/A
- 7. Sengun N/A
- 8. #ForgedInGold N/A
- 9. Magic N/A
- 10. Cavs N/A
- 11. Lakers in 7 N/A
- 12. Amen Thompson N/A
- 13. Thunder in 4 N/A
- 14. Game 7 N/A
- 15. Benson N/A
- 16. Mammoth N/A
- 17. Marner N/A
- 18. #OPLive N/A
- 19. Spirit Airlines N/A
- 20. Mobley N/A