#extortionware zoekresultaten
#Cybersecurity #Ransomware vs. #Extortionware – How they affect you ow.ly/344jxz
Don't forget to tune in tomorrow at #BlackHat2021 as CyberGRX's Dave Stapleton, ADP's Tim Chapman and Qualys' Benn Carr talk #ransomware, #extortionware, and how to best protect your organization from the threats!

#Datensicherheit: Was erwartet uns 2018? #Ransomware #Extortionware #DSGVO computerwoche.de/3332168 via @COMPUTERWOCHE
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/C9ihD #Ransomware #Cybersecurity #Extortionware
Ransomware is now Extortionware #Cybersecurity #Extortionware #cybercrime via twinybots.ch apextechservices.com/topics/article…
’’ایکسٹورشن ویئر‘‘کیا ہے اور کیا نقصان ہوتا ہے؟ #Extortionware #science #technology rimnews.pk/science-and-te…
#Ransomware: #Cyberkriminelle drohen mit der Veröffentlichung von Daten, wenn das Lösegeld nicht bezahlt wird #Extortionware #CyberCrime #CyberSecurity zdnet.de/88376448/maze-… via @zdnet_de
Worldwide, 2023 was a big year for extortion attacks! ☠️ How is your organization managing these risks to prepare for the year ahead? source: hubs.li/Q02d0rWH0 #extortionware #ransomware

60% of ransomware victims in H1 2025 were in North America. Attackers are ditching encryption for pure extortion: faster, quieter, harder to stop. Learn what this shift means for defenders in our latest blog. hubs.ly/Q03G5Hnl0 #Extortionware #BROC #Blackpoint #MDR #SOC

Ransomware is now #Extortionware buff.ly/36mBFuA #Cybersecurity #cybercrime #cyberattacks #hacker #hack #breach #phishing #dos #ransomware #malware #virus #apt #pii #nist #fcc #finra #hipaa #pci

#Extortionware is a type of cyberattack where your data is removed from your network. consilien.com/how-to-outwit-…

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/UHSOz #Ransomware #Cybersecurity #Extortionware

#Ransomware wird zunehmend zu #Extortionware: "Damit professionalisiert sich die Ransomware-Szene weiter und setzt betroffene Unternehmen und Personen zunehmend unter Druck." #CyberSecurity #CyberCrime glm.io/148904?t via @golem
#Ransomware, #Extortionware, #DSGVO: Auch 2018 wird #Security-Verantwortliche vor einige Herausforderungen stellen.
'Expect more #ransomware and '#extortionware' in 2015': ow.ly/GBPw2 #IQDaily
#WebinarINESE .@JavierSirvent hablando de #extortionware Aquí un ejemplo vía @eroskiconsumer consumer.es/web/es/tecnolo…
See how #Fed IT teams are approaching latest #ransomware & #extortionware cases. #Webcast 9/7 >> bit.ly/2basg2w #cybersecurity
We’ve all heard of #ransomware, but #extortionware is well and truly on the rise. Take a look at this recent @BBCNews article about a company director, who had sensitive, private information ransomed: bbc.in/3ucM745 #CyberSecurity

Avoid @bluestacksinc. It eventually requires you to upgrade to a subscription or install unwanted apps. #Extortionware
ICYMI: CryptoWall 4.0 is the new improved #ransomware turning #extortionware #cyber
CryptoWall has struck again—only this time it’s nastier than before. ow.ly/UYRMy @Code42
Businesses beware: extortionware attacks rise 🚨. They steal data, threaten release unless ransom paid, crippling finances & reputation. Over 1,000 businesses fell victim in 2023, with some paying up to $10 million. Stay protected! #CyberSecurity #ExtortionWare

60% of ransomware victims in H1 2025 were in North America. Attackers are ditching encryption for pure extortion: faster, quieter, harder to stop. Learn what this shift means for defenders in our latest blog. hubs.ly/Q03G5Hnl0 #Extortionware #BROC #Blackpoint #MDR #SOC

Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/BYzd8 #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/bCi3E #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/inwDE #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/xPZom #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/RmMt1 #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/3OSJ9 #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/5Z4JY #CyberSecurity #Extortionware
Extortionware is on the rise-stealing sensitive data and threatening to leak it unless a ransom is paid. Splunk breaks down how it works and why it's harder to defend against than traditional ransomware. Learn more: oal.lu/i4vhZ #CyberSecurity #Extortionware
ICYMI: Extortionware groups targeted 40+ organizations in early 2025, with ransom demands up to $15M. These aren’t just encryption attacks—they’re data theft threats. See why your security strategy needs updating: adventuresofasage.us #cybersecurity #extortionware

NEW: Extortionware—the evolution of ransomware—steals your data before encrypting it, rendering backups insufficient. Learn the 7 critical protection strategies every organization needs in 2025: adventuresofasage.us #cybersecurity #extortionware #AdventuresofaSage

Extortionware: when ransomware meets data leaks. Your backups won’t save you from this growing threat. New blog tomorrow reveals protection strategies every business needs in 2025. #cybersecurity #extortionware #AdventuresofaSage
🚨 All businesses handle sensitive data. But what happens if this info gets into the wrong hands? 😱 Learn about #Extortionware vs. #Ransomware and their threats. 🛡️💼 #CyberSecurity #DataProtection bit.ly/3PMvNop
Learn why Tj Sayers predicts seeing a new “extortionware” era fully emerge in 2024. View the complete list of our 2024 predictions on cybersecurity from CIS experts here. bit.ly/4b2vQ7U #ransomware #extortionware #cybersecurity

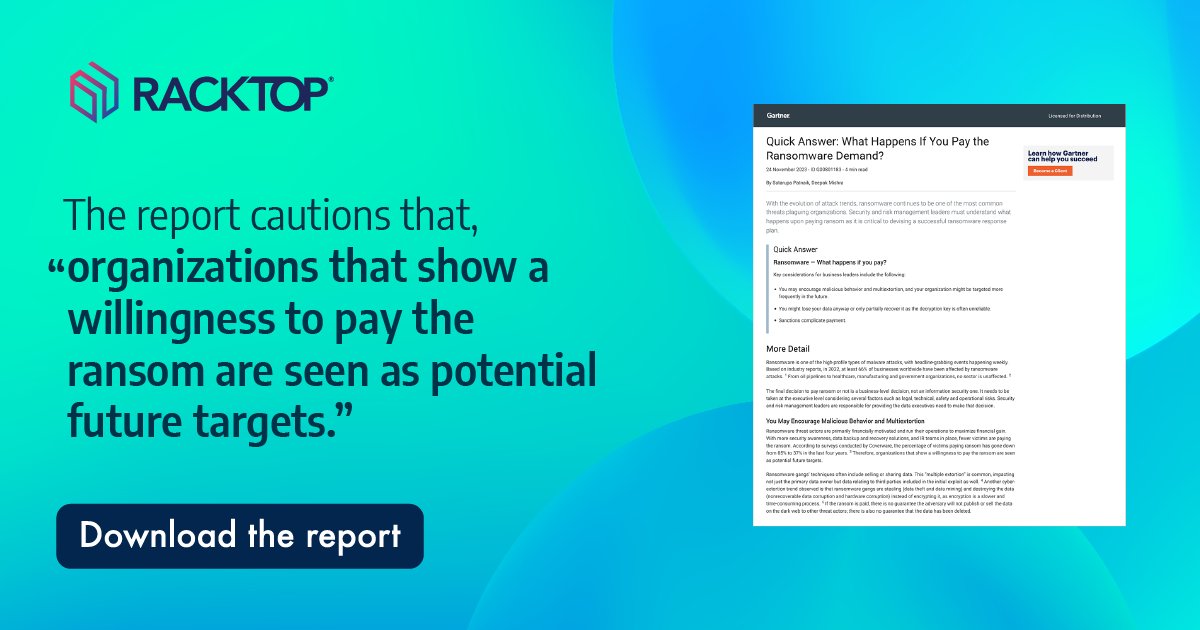
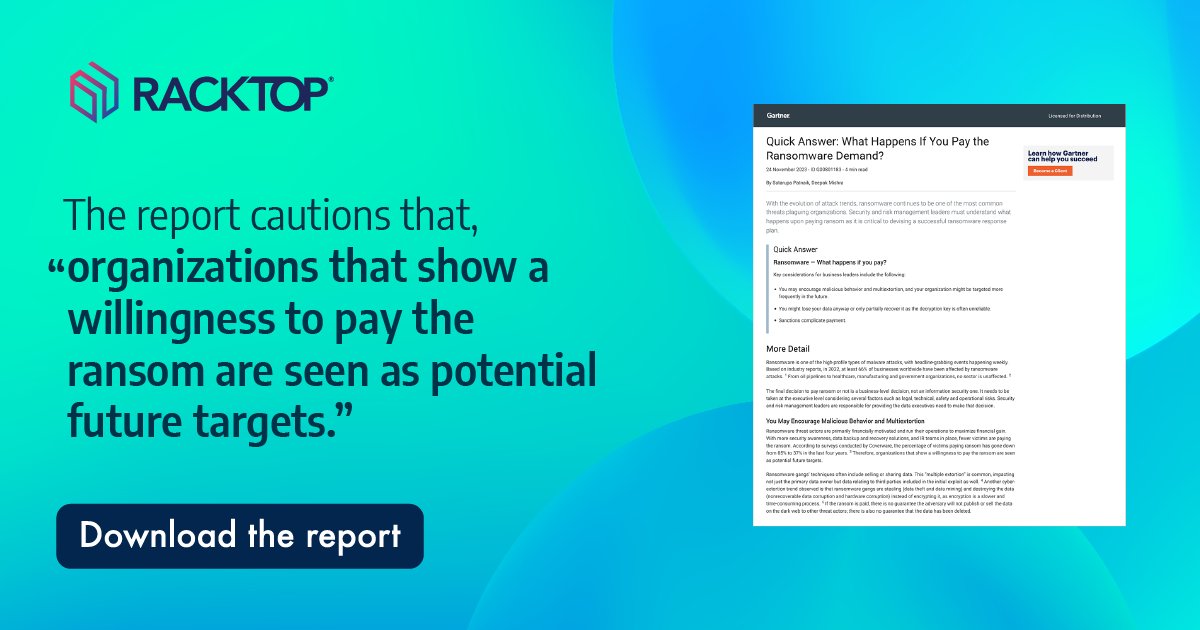
Understand the risks of ransomware payments. When you pay the ransomware, your organization may be vulnerable to multi-extortion attempts, permanent data loss, and global sections. hubs.li/Q02lNKnf0 #ransomware #dataextortion #extortionware #dataloss
Worldwide, 2023 was a big year for extortion attacks! ☠️ How is your organization managing these risks to prepare for the year ahead? source: hubs.li/Q02d0rWH0 #extortionware #ransomware

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. hubs.ly/Q029RXMS0 #Ransomware #Cybersecurity #Extortionware
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/yXaiI #Ransomware #Cybersecurity #Extortionware
blogs.cisco.com
Extortionware – how bad actors are taking the shortest path to your money
Ransomware is evolving. Bad actors are using various methods to increase profits by analyzing and leveraging the victims data and not bothering to encrypt.
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/Y3n71 #Ransomware #Cybersecurity #Extortionware
blogs.cisco.com
Extortionware – how bad actors are taking the shortest path to your money
Ransomware is evolving. Bad actors are using various methods to increase profits by analyzing and leveraging the victims data and not bothering to encrypt.
#Extortionware: ahora los #ciberdelincuentes hurgan en tu vida privada #ciberseguridad ow.ly/gyGg50Ec1hX
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/UHSOz #Ransomware #Cybersecurity #Extortionware

🚨 Calling all #ThreatHunters! 🚨 Join us on August 31 and see Rob Simmons @MalwareUtkonos analyze a #extortionware sample that performs #DataExfiltration in his #MalwareLab. Register here: hubs.ly/H0W5WDW0 #ThreatResearchers #MalwareResearch #Ransomware #Webinar
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/S8Qsi #Ransomware #Cybersecurity #Extortionware

#Hackers stole unreleased Radiohead recordings and threatened to release them unless the band paid $150,000, so the band released the recordings instead. That's one way to get ahead of #Extortionware #ransomware #cyberextortion #notgoingaway businessinsider.com/radiohead-rele…
Ransomware is now #Extortionware buff.ly/36mBFuA #Cybersecurity #cybercrime #cyberattacks #hacker #hack #breach #phishing #dos #ransomware #malware #virus #apt #pii #nist #fcc #finra #hipaa #pci

Understand the risks of ransomware payments. When you pay the ransomware, your organization may be vulnerable to multi-extortion attempts, permanent data loss, and global sections. hubs.li/Q02lNKnf0 #ransomware #dataextortion #extortionware #dataloss
Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/DF20Y #Ransomware #Cybersecurity #Extortionware

#Extortionware is a type of cyberattack where your data is removed from your network. consilien.com/how-to-outwit-…

A little over one year ago, Maze, the first large extortion #ransomware attack came to the attention of the wider world, and since then, nine other ransomware families have joined the trend. Here is what you should know about #extortionware. buff.ly/36nBY9V

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/fcNxM #Ransomware #Cybersecurity #Extortionware

Businesses beware: extortionware attacks rise 🚨. They steal data, threaten release unless ransom paid, crippling finances & reputation. Over 1,000 businesses fell victim in 2023, with some paying up to $10 million. Stay protected! #CyberSecurity #ExtortionWare

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/t9Qvn #Ransomware #Cybersecurity #Extortionware

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/cyQhD #Ransomware #Cybersecurity #Extortionware

Worldwide, 2023 was a big year for extortion attacks! ☠️ How is your organization managing these risks to prepare for the year ahead? source: hubs.li/Q02d0rWH0 #extortionware #ransomware

We’ve all heard of #ransomware, but #extortionware is well and truly on the rise. Take a look at this recent @BBCNews article about a company director, who had sensitive, private information ransomed: bbc.in/3ucM745 #CyberSecurity

Extortionware rises, bypassing encryption to expose critical data. Businesses need SOC expertise, advanced tools, and best practices for resilience. Check Cisco XDR for enhanced security. oal.lu/g7m2D #Ransomware #Cybersecurity #Extortionware

Offline backups aren’t helpful when #cybercriminals threaten to release #data rather than delete it. As such, the only way to combat #extortionware is to prevent it from happening in the first place. Learn more: hubs.la/H0ZHNQs0

Something went wrong.
Something went wrong.
United States Trends
- 1. May the 4th N/A
- 2. John Sterling N/A
- 3. #StarWarsDay N/A
- 4. Cole Palmer N/A
- 5. Good Monday N/A
- 6. Derry N/A
- 7. #MondayMotivation N/A
- 8. #May4th N/A
- 9. Teacher Appreciation Week N/A
- 10. Jedi N/A
- 11. Jamahl Mosley N/A
- 12. #BudGreatDelivery N/A
- 13. CNBC N/A
- 14. Billy Donovan N/A
- 15. Smart Money - Buy N/A
- 16. QUICK TRADE N/A
- 17. Club WWE N/A
- 18. Mike Lee N/A
- 19. Van Jones N/A
- 20. Juke Harris N/A