#thirdpartyrisk résultats de recherche
61% of orgs use a GRC platform. Yet 66% of CISOs say they fall short on third-party risk. Static reviews can’t keep up with risk that changes daily. Panorays helps teams see and act on third-party risk in real time. Learn more:panorays.com/blog/why-grc-p… #TPRM #GRC #ThirdPartyRisk

Your biggest security risk might be someone who doesn't work for you. Shared VPN. Generic admin accounts. Access no one revoked. This is how breaches happen. How are you managing third-party access to critical systems? #OTSecurity #PAM #ThirdPartyRisk #WALLIX

Vendor security risk used to be perceived as a private sector problem. Now it also exists in government systems. Read more: zurl.co/KHZjU #ThirdPartyRisk #CyberSecurity #DataProtection #GovTech

MOVEit Breach: How 600+ Vendors Got Hacked [TPRM Lesson] The MOVEit breach is the ultimate case study in third-party risk. Over 600 organizations exposed. Here's what every TPRM professional must learn from it. youtu.be/Tu0jpLDeTqs #TPRM #MOVEit #ThirdPartyRisk

youtube.com
YouTube
Learn TPRM with Rahul Tyagi
What Is the CIA Triad in TPRM? Vendor Risk Explained (2026) Confidentiality, Integrity, Availability - how the CIA Triad maps to vendor risk in your TPRM program. A must-watch short for risk professionals. youtu.be/R5KBtzeOzWw #TPRM #VendorRisk #ThirdPartyRisk

youtube.com
YouTube
Learn TPRM with Rahul Tyagi
Before you trust a supplier, SaaS platform, freelancer, or agency, check the risk first. Vendor Risk Assessment Tool to review MFA, SOC 2/ISO evidence, breach history, encryption, logging, backups, risk. cybersecuritytime.com/vendor-risk-qu… #Cybersecurity #VendorRisk #ThirdPartyRisk #GDPR
Before you trust a supplier, SaaS platform, freelancer, or agency, check the risk first. Vendor Risk Assessment Tool to review MFA, SOC 2/ISO evidence, breach history, encryption, logging, backups, risk. cybersecuritytime.com/vendor-risk-qu… #Cybersecurity #VendorRisk #ThirdPartyRisk #GDPR
It’s what you’ve ignored. Find the blind spots—shadow IT, third-party risk, weak processes—before they find you. 📅 Sept 29–30 (Masterclasses) | Oct 1–3 (Conference) 📍 Speke Resort Munyonyo & Online 🔗 Be there: register.eainfosec.org #InfoSec2025 #ThirdPartyRisk #ShadowIT

Navigating third-party risk! This Global Best Practices explores how The IIA’s new Topical Requirement helps strengthen third-party governance and controls. Read now: loom.ly/4GokKYQ #InternalAudit #ThirdPartyRisk #Governance

Your vendor’s AI model could be your next breach. Learn the top blind spots in third-party risk — and what to ask to protect your business. Read the TPRM Checklist → hubs.la/Q03QmDrd0 #ThirdPartyRisk #TPRM

Hims & Hers breach via third-party vendor 🚨 Social engineering → support system access → customer data exposed No core systems breached - but vendor risk strikes again #Cybersecurity #DataBreach #ThirdPartyRisk #Infosec

@Protecht_Risk Group has acquired VISO TRUST to strengthen its position in the global GRC market. tinyurl.com/2wfwc2jn #CyberSecurity #GRC #ThirdPartyRisk #AI #Infosec

🔐 SpyCloud lanza solución para amenazas de identidad en la cadena de suministro Nueva herramienta contra riesgos de identidad de terceros. devops.com/spycloud-launc… #Cybersecurity #IdentityProtection #ThirdPartyRisk #RoxsRoss
A cyberattack on Brazil’s C&M Software let hackers access reserve accounts for small banks—luckily no customer funds were lost, but how did we let our vendors stay so underprotected? 😟🔒💸 #CyberSecurity #ThirdPartyRisk #Finance reuters.com/world/americas…
everyone wants a "mature TPRM program." nobody agrees what that means. maturity isn't about more controls. it's about know ing which 3% of your vendors can actually bring you down and having automated, continuous eyes on exactly them. that's it. #ThirdPartyRisk
CISOs highlight rising third-party risks amid expanding vendor networks and limited supply chain visibility. Regulatory pressure intensifies as incidents involve deeper subcontractor layers. #ThirdPartyRisk #SupplyChain #USA ift.tt/4UQJqit
Economic uncertainty increases pressure on trust and controls. AI is expanding fraud and data-exposure pathways. When health data, AI, and third parties connect—where does accountability break? #FraudRisk #AIsecurity #ThirdPartyRisk
Swiss government data was stolen after the Radix health foundation was hit by Sarcoma ransomware, showing how even trusted partners can become a danger—stay alert and back up everything! 🔐 💻 🚨 #CyberSecurity #Ransomware #ThirdPartyRisk #DataProtection #Switzerland
What managing partners should ask AI vendors before signing any contract - helpnetsecurity.com/2026/04/08/kum… - @TMFGroup #CyberSecurity #InfoSec #ThirdPartyRisk #DataProtection #ProfessionalServices #CISO

Security leaders highlight the Claude Mythos breach as a wake-up call: third-party access is the weak link, and AI models are critical assets. Read insights from Heath Renfrow: okt.to/maInRd #Cybersecurity #AI #ThirdPartyRisk #Claude
Your biggest security risk might be someone who doesn't work for you. Shared VPN. Generic admin accounts. Access no one revoked. This is how breaches happen. How are you managing third-party access to critical systems? #OTSecurity #PAM #ThirdPartyRisk #WALLIX

61% of orgs use a GRC platform. Yet 66% of CISOs say they fall short on third-party risk. Static reviews can’t keep up with risk that changes daily. Panorays helps teams see and act on third-party risk in real time. Learn more:panorays.com/blog/why-grc-p… #TPRM #GRC #ThirdPartyRisk

@Protecht_Risk Group has acquired VISO TRUST to strengthen its position in the global GRC market. tinyurl.com/2wfwc2jn #CyberSecurity #GRC #ThirdPartyRisk #AI #Infosec

Vendor security risk used to be perceived as a private sector problem. Now it also exists in government systems. Read more: zurl.co/KHZjU #ThirdPartyRisk #CyberSecurity #DataProtection #GovTech

Before you trust a supplier, SaaS platform, freelancer, or agency, check the risk first. Vendor Risk Assessment Tool to review MFA, SOC 2/ISO evidence, breach history, encryption, logging, backups, risk. cybersecuritytime.com/vendor-risk-qu… #Cybersecurity #VendorRisk #ThirdPartyRisk #GDPR
Before you trust a supplier, SaaS platform, freelancer, or agency, check the risk first. Vendor Risk Assessment Tool to review MFA, SOC 2/ISO evidence, breach history, encryption, logging, backups, risk. cybersecuritytime.com/vendor-risk-qu… #Cybersecurity #VendorRisk #ThirdPartyRisk #GDPR
5/8 Gestion du risque tiers (Supply Chain) : En résonance avec DORA, le NCAF 2.0 fournit enfin des grilles d'audit standardisées pour évaluer objectivement les fournisseurs Cloud et les sous-traitants. Fini les évaluations au doigt mouillé. #CloudSecurity #ThirdPartyRisk
Your security is only as strong as your vendors. One weak partner can expose everything. Third-party access creates hidden risk—are you monitoring it? #Cybersecurity #ThirdPartyRisk #RiskManagement #CurrentTEKSolutions

Our latest piece examines where third-party cyber risk tends to emerge and what a practical resilience framework looks like in practice. Read more: lnkd.in/d25ez3p3 #Cybersecurity #ThirdPartyRisk #Compliance #RIA #BrokerDealer

This week, we brought the VISO TRUST team together with Protecht’s North America team for our QBR. First time in the same room. A lot of “finally good to meet you in person.” That’s where it really starts to click. #RiskManagement #ThirdPartyRisk #GRC #RegTech #SaaS

Security leaders highlight the Claude Mythos breach as a wake-up call: third-party access is the weak link, and AI models are critical assets. Read insights from Heath Renfrow: okt.to/maInRd #Cybersecurity #AI #ThirdPartyRisk #Claude
Security leaders highlight the Claude Mythos breach as a wake-up call: third-party access is the weak link, and AI models are critical assets. Read insights from Heath Renfrow: okt.to/WUaQxg #Cybersecurity #AI #ThirdPartyRisk #Claude
When a third party hides ownership behind privacy law, what does DOJ expect? Ask anyway. Then assess the risk of doing business in the dark. A sharp compliance dilemma you need to hear. 🎧 bit.ly/4tD0Wfl #Compliance #DOJ #ThirdPartyRisk
“Vet and forget” is dead. In high-risk markets, regulators want proof your compliance program actually works in real time. Hear Timothy & Fiona on building continuous engagement. 🎧 bit.ly/4tD0Wfl #Compliance #ThirdPartyRisk #Ethics
Not a hack. Legitimate third-party access to a high-capability AI system. Identity boundary failure. Capability exposure. bbc.com/news/articles/… #CyberSecurity #AISecurity #ThirdPartyRisk
AI is transforming financial services — but your vendor's AI risk is your risk too. Know what you're signing up for: bit.ly/3PQ7uF8 #ThirdPartyRisk #FinancialServices #AritificalIntelligence #AI
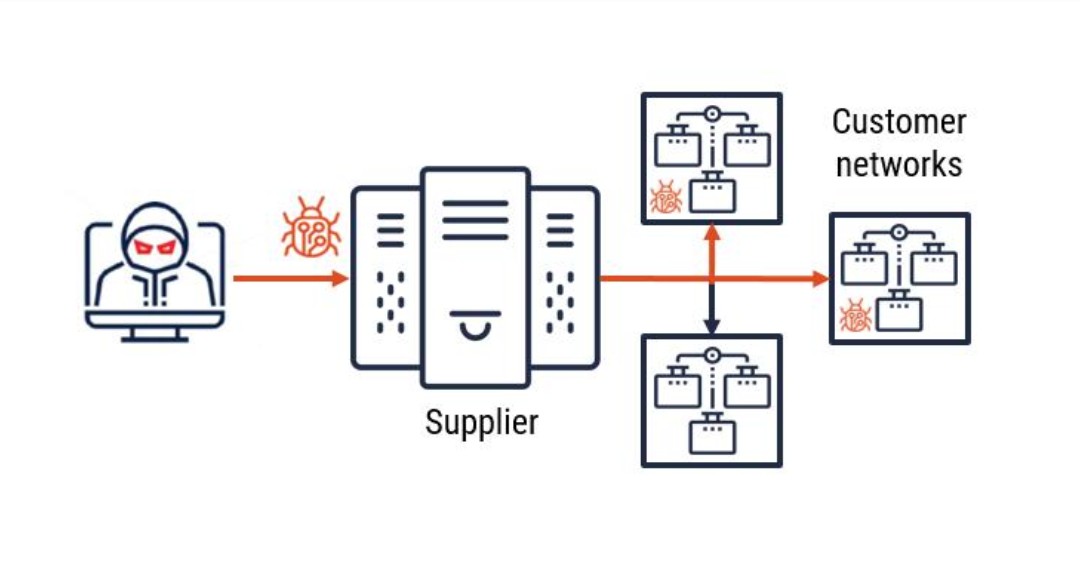
Why are supply chains the primary threat vector for 2026? Learn how compromised credentials are reshaping cyberattacks and what that means for your organization through real-world cases behind this growing risk. #Cybersecurity #SupplyChainAttack #ThirdPartyRisk #Lumu

Vercel's recent security breach via a compromised third-party AI tool highlights the critical need for stringent third-party integration security measures. #CyberSecurity #DataBreach #ThirdPartyRisk Link: thedailytechfeed.com/vercel-securit…

This is your final opportunity to join the Stressed Exit Planning: Lessons Learned from Financial Services webinar. Secure your place: buff.ly/9Vd22Yg #OperationalResilience #BusinessContinuity #ThirdPartyRisk #Leadership #Webinar

Customers of Anodot were exposed through a SaaS breach. Risk now lives in connections, not just systems. #CyberSecurity #ThirdPartyRisk #InfoSec
Your biggest security risk might be someone who doesn't work for you. Shared VPN. Generic admin accounts. Access no one revoked. This is how breaches happen. How are you managing third-party access to critical systems? #OTSecurity #PAM #ThirdPartyRisk #WALLIX

61% of orgs use a GRC platform. Yet 66% of CISOs say they fall short on third-party risk. Static reviews can’t keep up with risk that changes daily. Panorays helps teams see and act on third-party risk in real time. Learn more:panorays.com/blog/why-grc-p… #TPRM #GRC #ThirdPartyRisk

Your vendor’s AI model could be your next breach. Learn the top blind spots in third-party risk — and what to ask to protect your business. Read the TPRM Checklist → hubs.la/Q03QmDrd0 #ThirdPartyRisk #TPRM

AI concentration risk is not just an IT problem. It is a compliance test under the ECCP. Can your company prove governance before disruption hits? Read the full article: bit.ly/4sMo4qG #Compliance #AIGovernance #ThirdPartyRisk

Strengthen your third-party oversight with this week’s Compliance Tip of the Day recap. Practical insights. Actionable steps. Essential listening for every compliance leader. Listen now: bit.ly/3XIEvHf #ThirdPartyRisk #ComplianceTips #RiskManagement

Are your third-party relationships compliant? Learn the essential steps of third-party risk management in today’s #ComplianceTipoftheDay episode. Don’t miss it 👉 bit.ly/4r2Ipbp #ThirdPartyRisk #CorporateGovernance #ComplianceTips

AI is changing everything, especially your third-party risk. BigID gives you real visibility into vendor AI use. Ready to uncover what’s hiding? 👉 bit.ly/444Aobg #BigID #AIsecurity #ThirdPartyRisk

Compliance pros—stay ahead. Learn how adequate due diligence strengthens your third-party risk program and protects your organization. Listen to today’s #ComplianceTipoftheDay: bit.ly/3XBDi4r #ThirdPartyRisk #ComplianceLeadership #RiskManagement
Your security is only as strong as your riskiest vendor. Read this blog to get practical steps to reduce third-party risk—from smarter vetting to better contracts and continuous monitoring. Read more 👉 bit.ly/42RGCuz #CyberSecurity #ThirdPartyRisk #InfoSec #IANSResearch

Boost your compliance game! 📊 Our weekly summary covers risk assessment, 3rd-party management, due diligence, and investigation protocols. Read & subscribe for insights: bit.ly/45O45zh #ComplianceExcellence #RiskManagement #ThirdPartyRisk

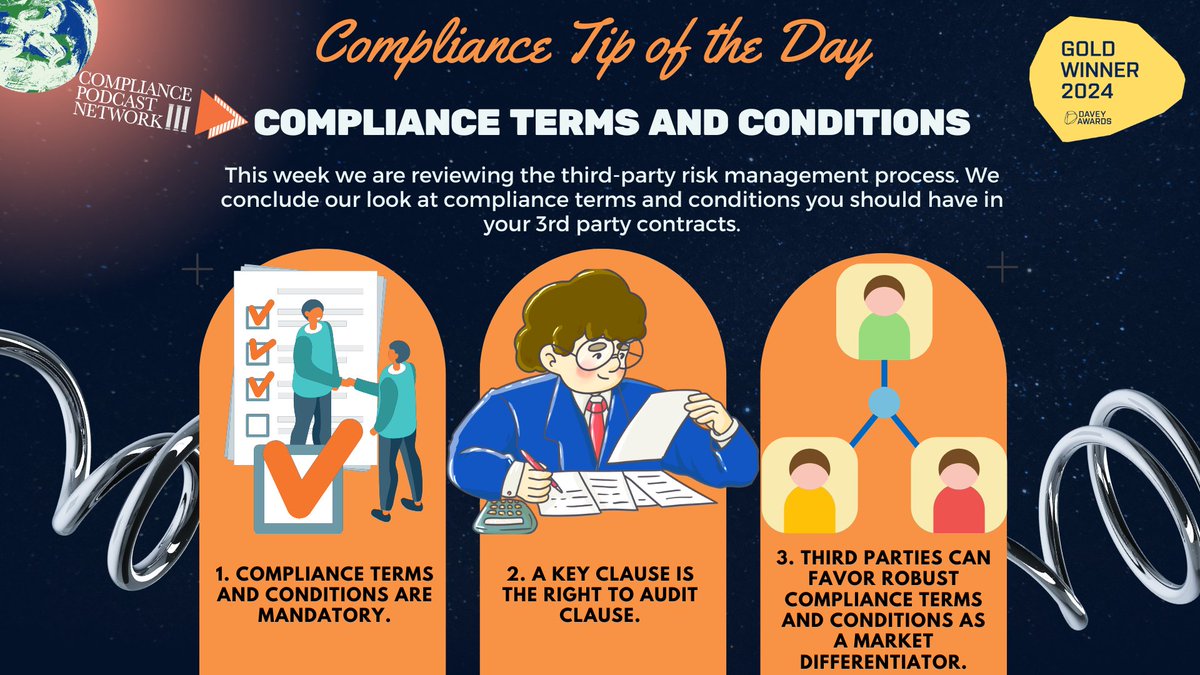
Are your third-party contracts truly protecting your organization? Don’t leave compliance to chance. Tune in for key terms every contract should include: 🔗 bit.ly/48dWNVH #ComplianceLeadership #RegulatoryCompliance #ThirdPartyRisk
Managing third-party risk? Don’t overlook the questionnaire. Today’s #ComplianceTipoftheDay episode provides actionable tips for effective partner oversight. 👉 Tune in: bit.ly/47ZdP9T #ThirdPartyRisk #ComplianceTips #EthicsInBusiness

Sanctions, AI security, bank enforcement, and supply-chain fraud, all in one fast daily briefing. Catch the February 24, 2026 #DailyComplianceNews episode here: bit.ly/3TMTP3N #ThirdPartyRisk #CyberRisk #ComplianceLeadership
Navigating third-party risk! This Global Best Practices explores how The IIA’s new Topical Requirement helps strengthen third-party governance and controls. Read now: loom.ly/4GokKYQ #InternalAudit #ThirdPartyRisk #Governance

Your AI stack is your third-party stack. Can you prove vendor AI risk is governed, monitored, and documented? Read, share, and join the conversation: bit.ly/47GCh0p #AICompliance #ThirdPartyRisk #ComplianceLeadership

Join us for a webinar in one week! We'll discuss how you can drive smarter #thirdpartyriskmanagement decisions by connecting your third parties to your operational ecosystem and how to use our #thirdpartyrisk and #resilience functionality. Register today: bit.ly/3VLAwYw

We are pleased to share that on behalf of Herdem Attorneys at Law, our Partner Simge Kılıç joined Moody's Corporation’s closed-door seminar. #ThirdPartyRisk #SupplyChainCompliance #KYC #DueDiligence #Sustainability #Istanbul

From $4M penalties to supply chain missteps—sanctions risk is real. Learn how to build defenses in this must-listen episode of Corruption, Crime & Compliance. 🎧 bit.ly/3K2jJyD #CompliancePodcast #ThirdPartyRisk #OFAC

Our upcoming webinar, Stressed Exit Planning: Lessons Learned from Financial Services, challenges us to rethink traditional exit strategies, moving beyond static plans. Register today: buff.ly/pecJjaA #OperationalResilience #BusinessContinuity #ThirdPartyRisk #Leadership

We’re Live at #GRFSummit2025 and Mattermost is here at The Palms Las Vegas! Join us as cybersecurity and risk leaders gather to tackle the future of third-party risk, operational resilience, and secure collaboration. #ThirdPartyRisk #SecureCollaboration

Something went wrong.
Something went wrong.
United States Trends
- 1. #WWENXT N/A
- 2. Comey N/A
- 3. Derrick White N/A
- 4. Embiid N/A
- 5. King Charles N/A
- 6. #DaredevilBornAgain N/A
- 7. Lizzy Rain N/A
- 8. Quentin Grimes N/A
- 9. Jaylen Brown N/A
- 10. Drew Romo N/A
- 11. LIFE GOES ON N/A
- 12. The Celtics N/A
- 13. Tony Bradley N/A
- 14. #Sixers N/A
- 15. Will Kroos N/A
- 16. #bucciovertimechallenge N/A
- 17. Baepsae N/A
- 18. Stokes N/A
- 19. Mark Pope N/A
- 20. Tyler Myers N/A












































