#infosec search results
🟧 Comprehensive Guide: Flipper Zero Guide for Beginners. 1. infosecwriteups.com/the-ultimate-g… 2. en.hacks.gr/odigos-flipper… #infosec




🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

㊙️How to Securely Store Secrets in Environment Variables Blog: blog.miguelgrinberg.com/post/how-to-se… #infosec

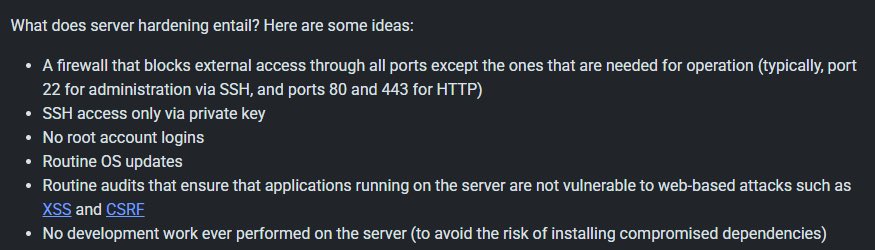
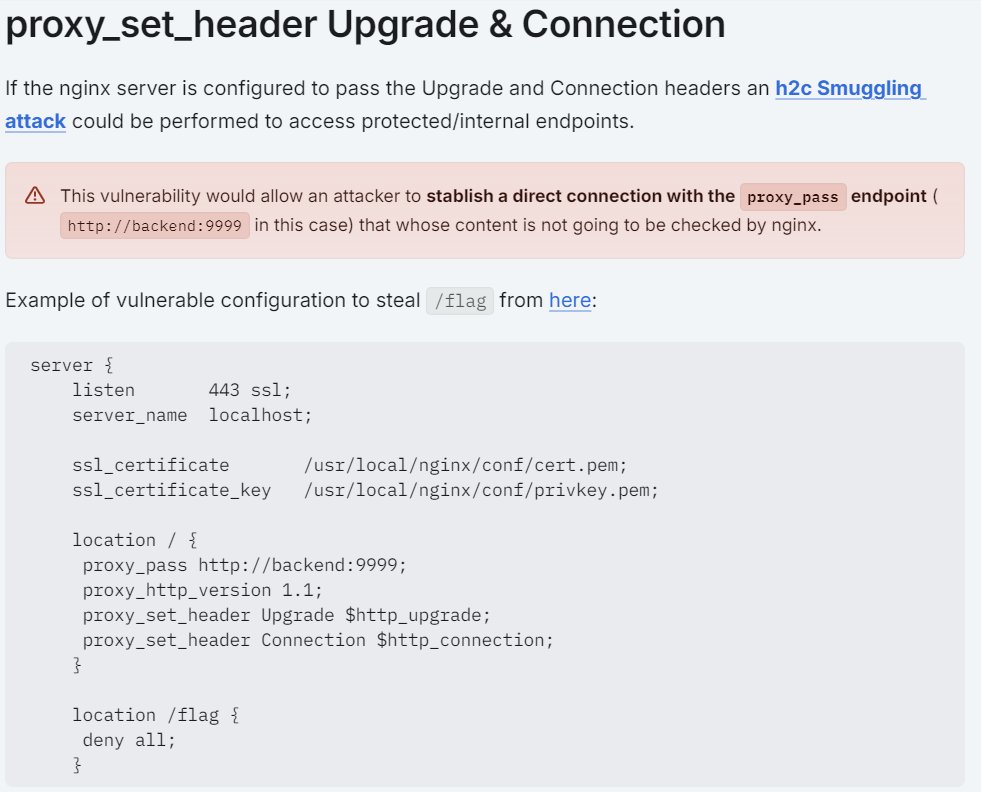
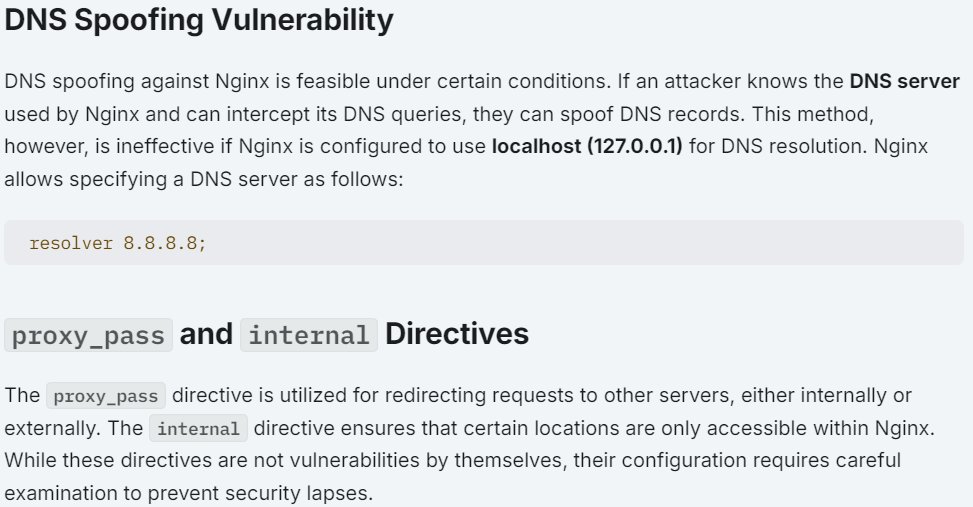
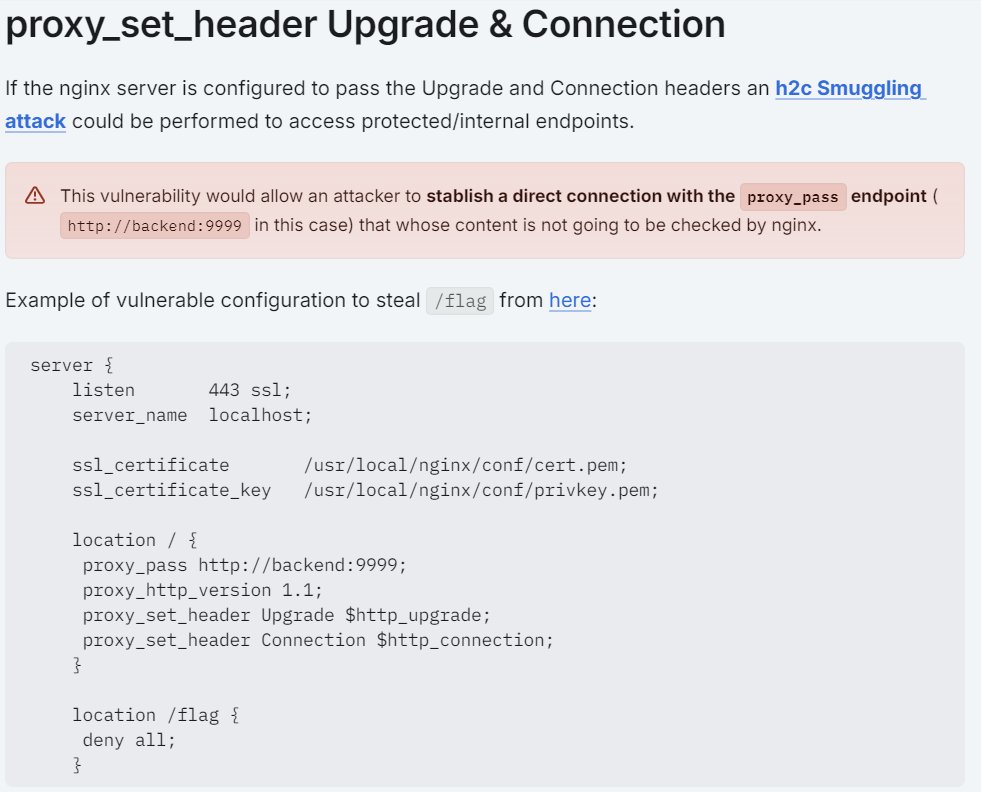
👋 Pentesters! 𝐌𝐚𝐤𝐞 𝐬𝐮𝐫𝐞 𝐲𝐨𝐮 𝐡𝐚𝐯𝐞 𝐭𝐡𝐢𝐬 𝐡𝐚𝐧𝐝𝐲 👇 🔥 🧪 COMPLETE GUIDE: A Complete Guide to Configuring & Pentesting Nginx servers! Guide: book.hacktricks.xyz/network-servic… Tool: github.com/yandex/gixy #infosec


Finally @AnthropicAI approved my cyber use case in just 2h 25min upon submission For people getting rejected provide your profile: @Hacker0x01, @Bugcrowd, and a project with one of your github repos. Much appreciated, Anthropic team 🤎 #InfoSec #Anthropic #BugBounty


Banned from Claude Code in 30 Minutes The plan was simple: probe Claude Code APIs through Burp Suite (TLS checks off) and responsibly disclose anything interesting via HackerOne. My custom AI agent was also testing Claude Code's APIs in the background, so it was a joint effort

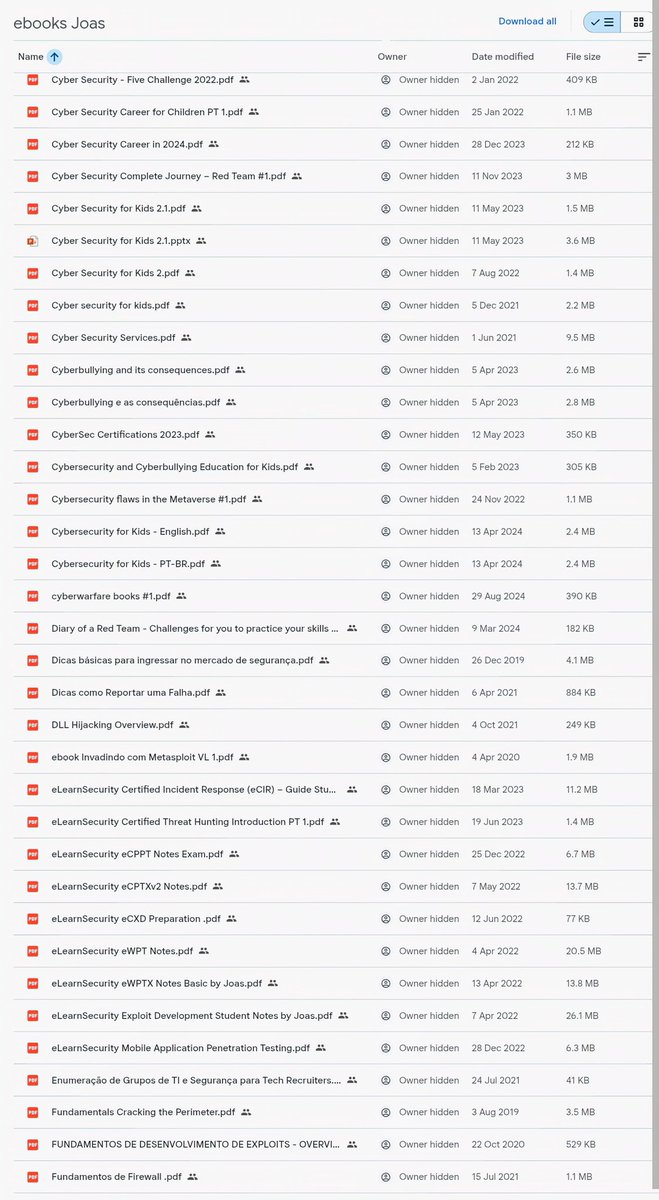
🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇drive.google.com/drive/u/0/mobi… #CyberSecurity #InfoSec

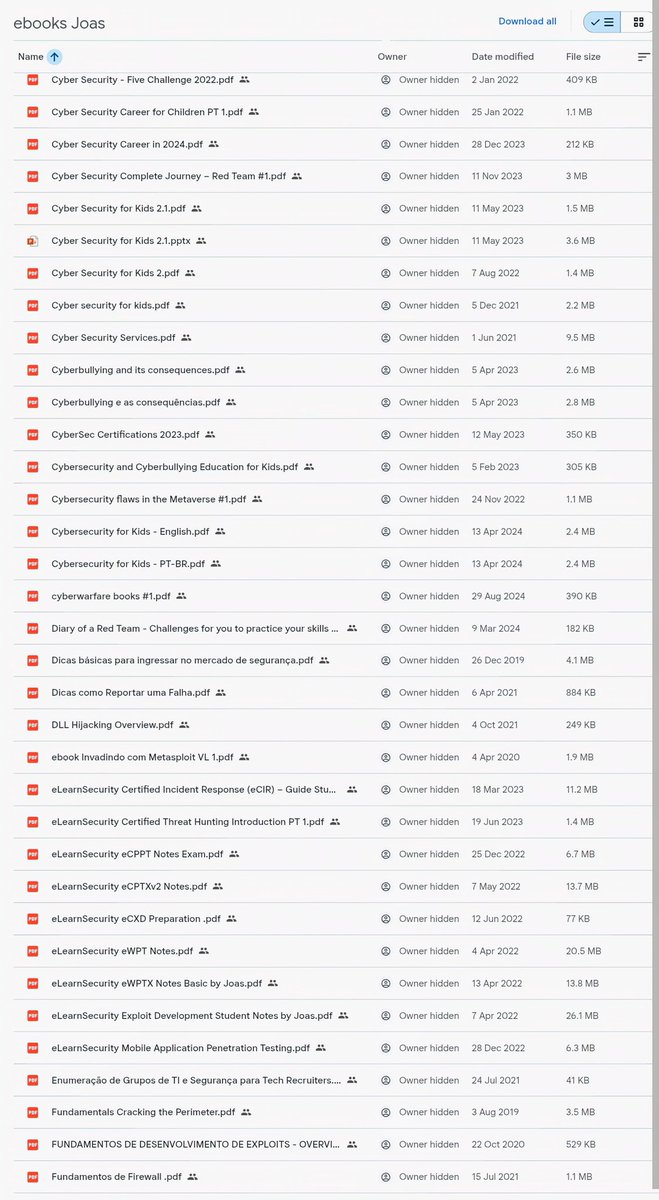


100+ Cybersecurity E-Books A complete digital library packed with cybersecurity resources covering networking, Linux, threat analysis, cloud security, OSINT, and security workflows. Comment EBOOKS 📚🔐👇 #cybersecurity #infosec #ebooks #networksecurity #linux

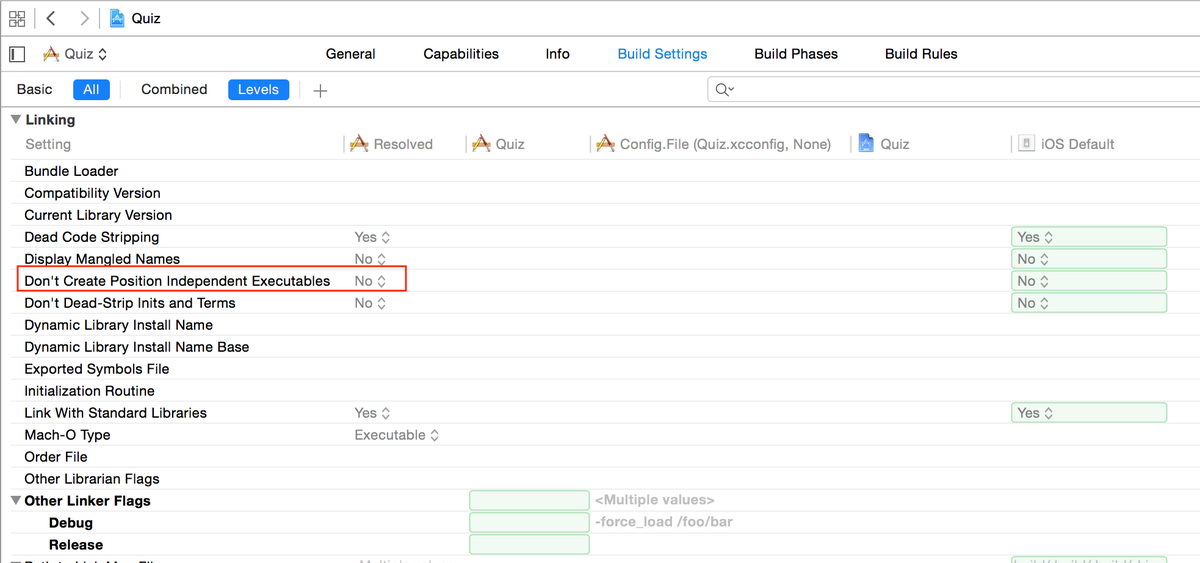
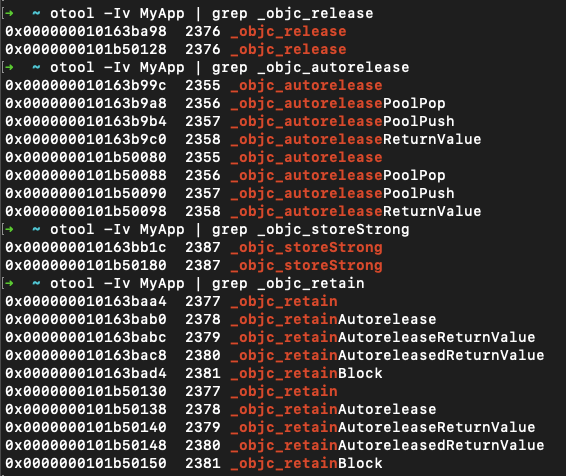
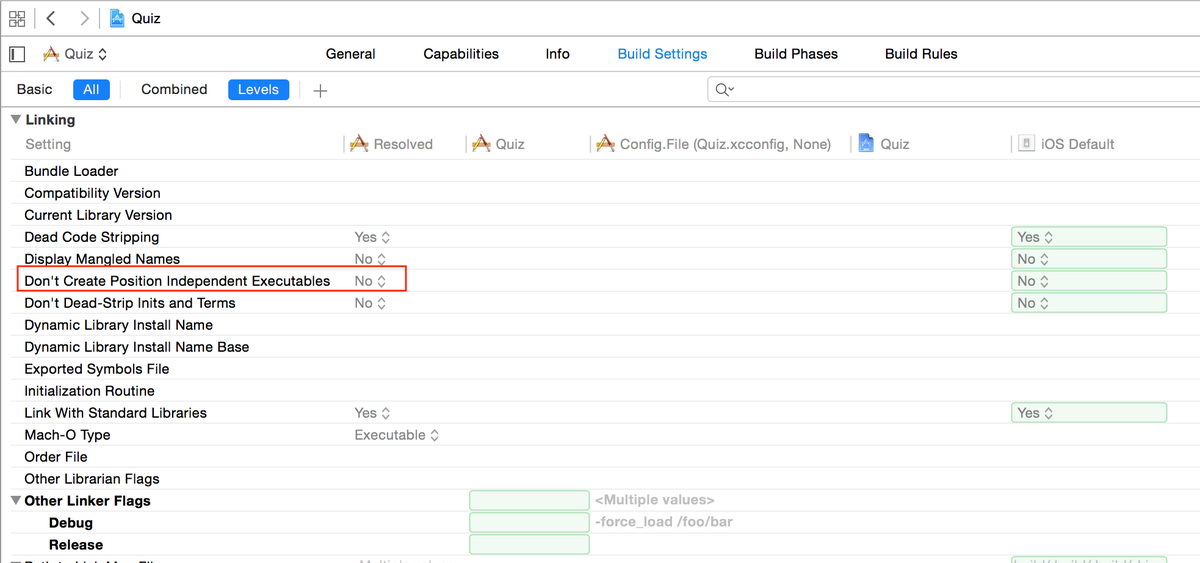
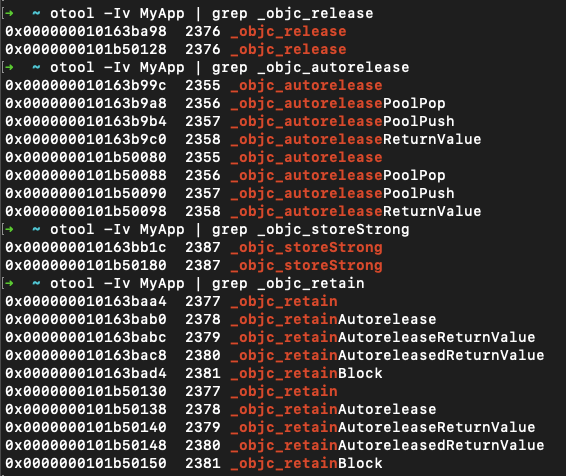
🧪 iOS Pentesting: Step-by-step guide on "IPA Binary Analysis" using MobSF. Guide: inesmartins.github.io/mobsf-ipa-bina… #infosec
5 Common Web Vulnerabilities You Must Know 🌐 Understanding vulnerabilities like SQLi, XSS, CSRF, IDOR, and broken authentication is essential for anyone serious about web security and safe development practices. Comment WEB 🌐👇 #websecurity #cybersecurity #infosec




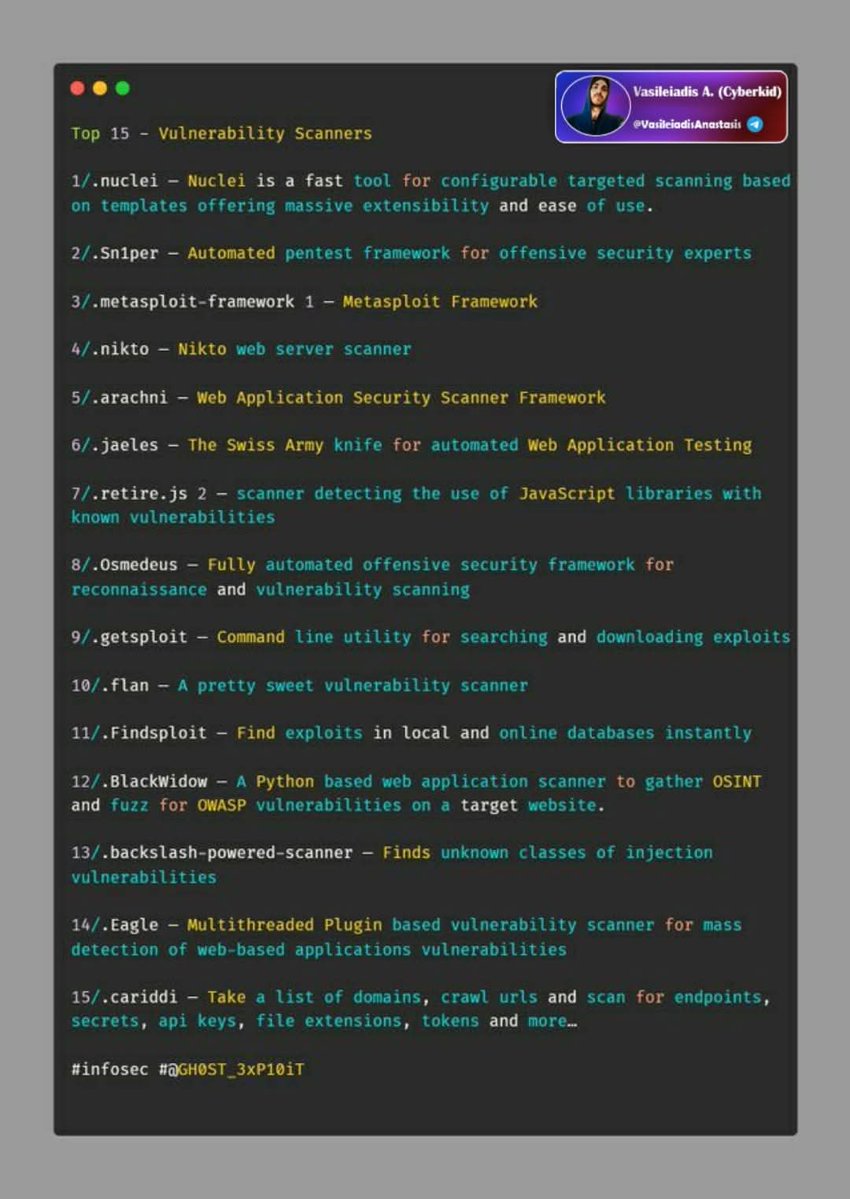
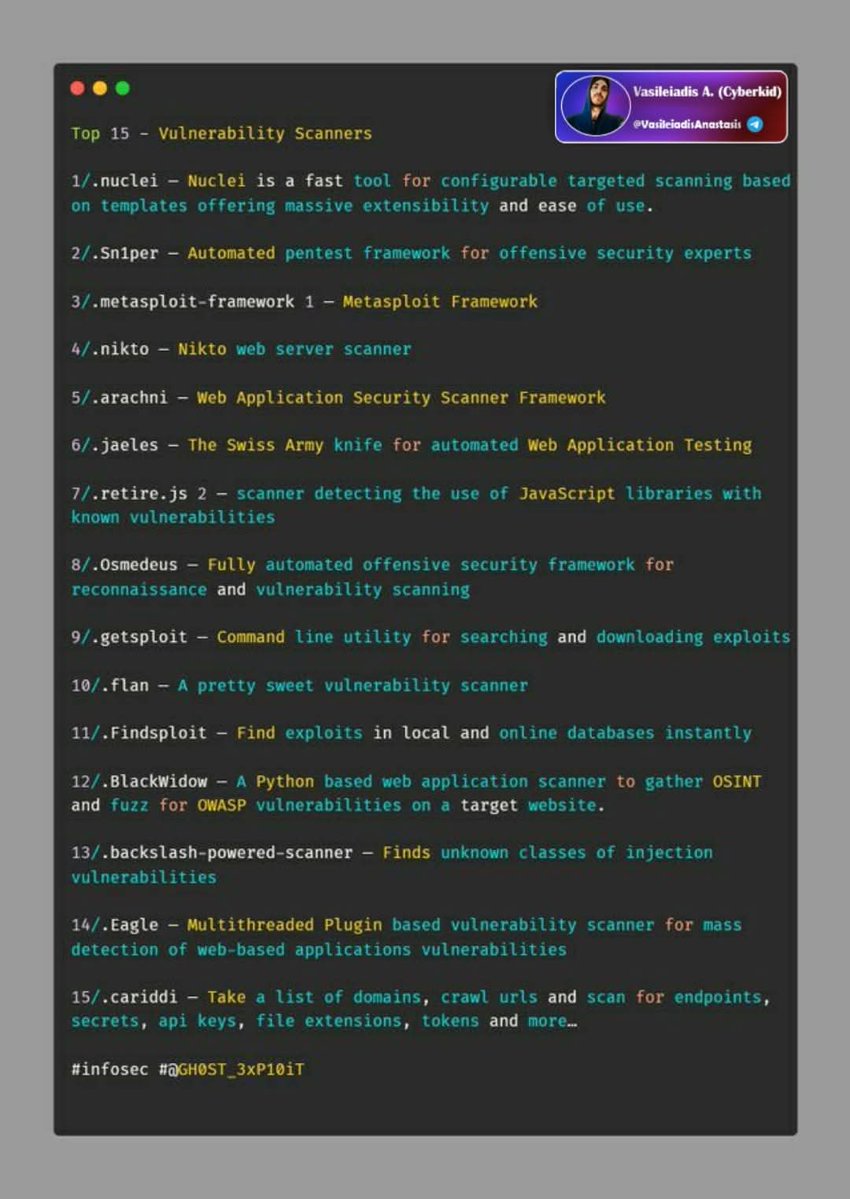
⚔️Top 15 Vulnerability Scanners 🔹Nuclei 🔹Sn1per 🔹Metasploit - Framework 🔹Nikto 🔹Arachni 🔹Jaeles 🔹Retire.js 🔹Osmedeus 🔹Getsploit 🔹Flan 🔹Findsploit 🔹Blackwidow 🔹Backslash-powered-scanner 🔹Eagle 🔹Cariddi 🔖#infosec #cybersecurity #hacking #pentesting #security
⚒️Open Source SIEM Tools 🔰List: 🔹OSSIM 🔹Sagan 🔹Splunk Free 🔹Snort 🔹Elasticsearch 🔹MozDef 🔹ELK Stack 🔹Wazuh 🔹Apache Metron 🔖#infosec #cybersecurity #hacking #pentesting #security

🗺️Active Directory Pentesting Mind Map: V1: raw.githubusercontent.com/esidate/pentes… V2: raw.githubusercontent.com/esidate/pentes… 🔖#infosec #cybersecurity #hacking #pentesting #security

Top 100 Cybersecurity & Security E-Books (Free Download) A powerful collection of 100+ free e-books covering networking, Linux, threat detection, pentesting fundamentals, OSINT, and defensive security workflows. Comment BOOKS 📚🔐👇 #cybersecurity #infosec #ebooks

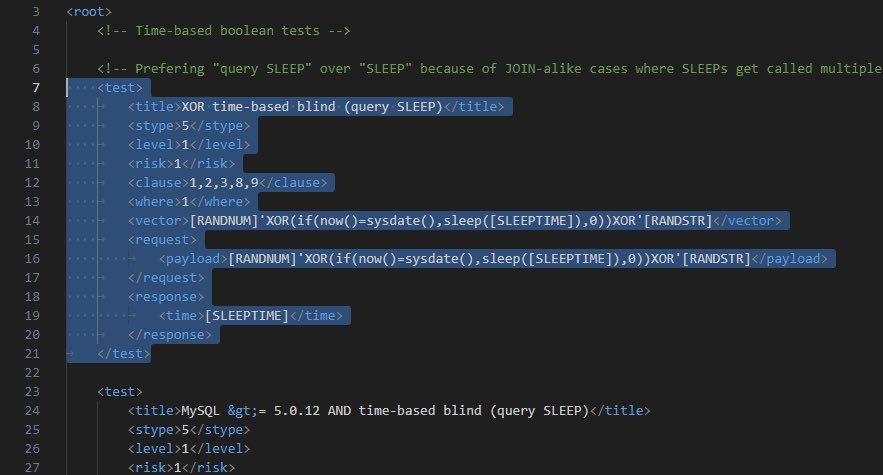
💉 A Blog on Advance SQLMap Customization Blog: ott3rly.com/advanced-sqlma… author: @ott3rly #infosec


Fantastic unwind information and where to find them - By KlezVirus dlvr.it/TS6TG8 #cyber #threathunting #infosec
protobuf.js joins the "libraries that pwn the internet" hall of fame. Your entire stack depends on packages maintained by one dev with 47 repos. Which npm package nukes everything next? #infosec #cybersecurity
Cyber threats aren’t slowing down — neither should your defense. New video on modern cybersecurity strategies 🔐👇 #CyberSecurity #Infosec #Tech
JSOC IT CEO Sam Sawalhi challenges security “belief gaps,” urging leaders to verify controls with evidence — not assumptions — to close hidden risks before breaches occur. #cybersecurity #infosec #CISO bit.ly/48OUUjf
68% of cloud breaches in 2024 came from compromised service accounts and forgotten API keys—not phishing or weak passwords 🔑 Unmanaged non-human identities are your biggest blind spot. #cybersecurity #infosec #databreach #CloudSecurity Read more -> cyberthreats247.com
cyberthreats247.com
Cyber Threats Weekly — Free Cybersecurity Newsletter
Critical threats, zero-day exploits, breach alerts and practical defenses — 3x per week, free. Written for everyone from personal users to security pros.
Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long dlvr.it/TS6S14 #InfoSec #CyberSecurity

Dump LSASS via physical memory read primitives in vulnerable kernel drivers github.com/RainbowDynamix… #infosec #cybersecurity #redteam #pentest
Your SOC 2 audit won’t fail because of missing policies. It fails: An attacker changed user_id=1024 → 1025 …and accessed another customer’s data. That’s broken access control. And scanners usually miss it. pentesttesting.com/penetration-te… #CyberSecurity #Infosec #APIsecurity #Hacking
Nobody talks about turning speakers into microphones for espionage, a technique outlined in SPEAKE(a)R research, #SurveillanceState #InfoSec

🔒 MT probe into Blue Cross Blue Shield data breach affecting 462,000 can continue, judge says - Billings Gazette A judge has ruled that the Montana probe into a Blue Cross Blue Shield data breach... crustylabs.ai #CyberSecurity #InfoSec #CrustyTLDR
ACTION REQUIRED: Acrobat Reader vulnerability actively exploited in the wild. Tycoon 2FA phishing kit losing dominance as new attack methods surge. Ruby Central in financial crisis after RubyGems maintainer dispute. #Cybersecurity #InfoSec
📶 El WiFi es aire, y el aire llega a todas partes. Si no cifras tu tráfico, cualquiera con una antena de 20€ puede leer tus correos electrónicos mientras los envías. ¡Cifra siempre con WPA3! 📡 #infosec #networksecurity

Sunday's CVE Brief is live: 🔴 9 actively exploited 🟠 7 critical 🟡 46 high priority Stay protected → cvebrief.com #cybersecurity #infosec #CVE #vulnerability

❌ "I'm not a target." Biggest mistake. Hackers don't care who you are..., they look for easy access. Weak passwords, no 2FA, random clicks… that's all it takes. Stop believing myths. Start protecting yourself. 🔐 #CyberSecurity #DigitalSafety #InfoSec #HackingAwareness

THEBOX -> 1 Click Search Email | Username | PDF reports | auto image comparison | full API 5 free searches → osintcheckbox.com #OSINT #infosec #cybersecurity #threatintel
Three Microsoft Defender 0-days exploited in the wild within 13 days: BlueHammer (CVE-2026-33825) patched, but RedSun & UnDefend remain open. RedSun grants SYSTEM on fully-patched Win10/11/Server 2019+ even after April Patch Tuesday. #ZeroDay #InfoSec #Windows
Apache Struts CVE-2026-6056 has been rejected, indicating no current security threat. This highlights the importance of verifying CVE statuses before panic. #NerdieNews #CyberSecurity #InfoSec #Ransomware #Malware

🛡️ Con el sistema de plantillas de #proxmox, puedes desplegar servidores preconfigurados con todas las medidas de seguridad de tu empresa ya aplicadas. Estandariza tu protección y evita errores de configuración manuales. 📋 #concienciacionciberseguridad #infosec #proxmox

🟧 Comprehensive Guide: Flipper Zero Guide for Beginners. 1. infosecwriteups.com/the-ultimate-g… 2. en.hacks.gr/odigos-flipper… #infosec




Finally @AnthropicAI approved my cyber use case in just 2h 25min upon submission For people getting rejected provide your profile: @Hacker0x01, @Bugcrowd, and a project with one of your github repos. Much appreciated, Anthropic team 🤎 #InfoSec #Anthropic #BugBounty


Banned from Claude Code in 30 Minutes The plan was simple: probe Claude Code APIs through Burp Suite (TLS checks off) and responsibly disclose anything interesting via HackerOne. My custom AI agent was also testing Claude Code's APIs in the background, so it was a joint effort

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

Si me pagaran $1 peso por cada vez que me piden hackear un facebook! ya sería billonario.... #infosec
🚨 200+ Cybersecurity eBooks (Red Team / Pentest / Exploit Dev) Not beginner fluff — real material: • AV/EDR bypass • Buffer overflow • AD attacks • OSINT & recon • Bug bounty • SOC & threat hunting Download 👇drive.google.com/drive/u/0/mobi… #CyberSecurity #InfoSec



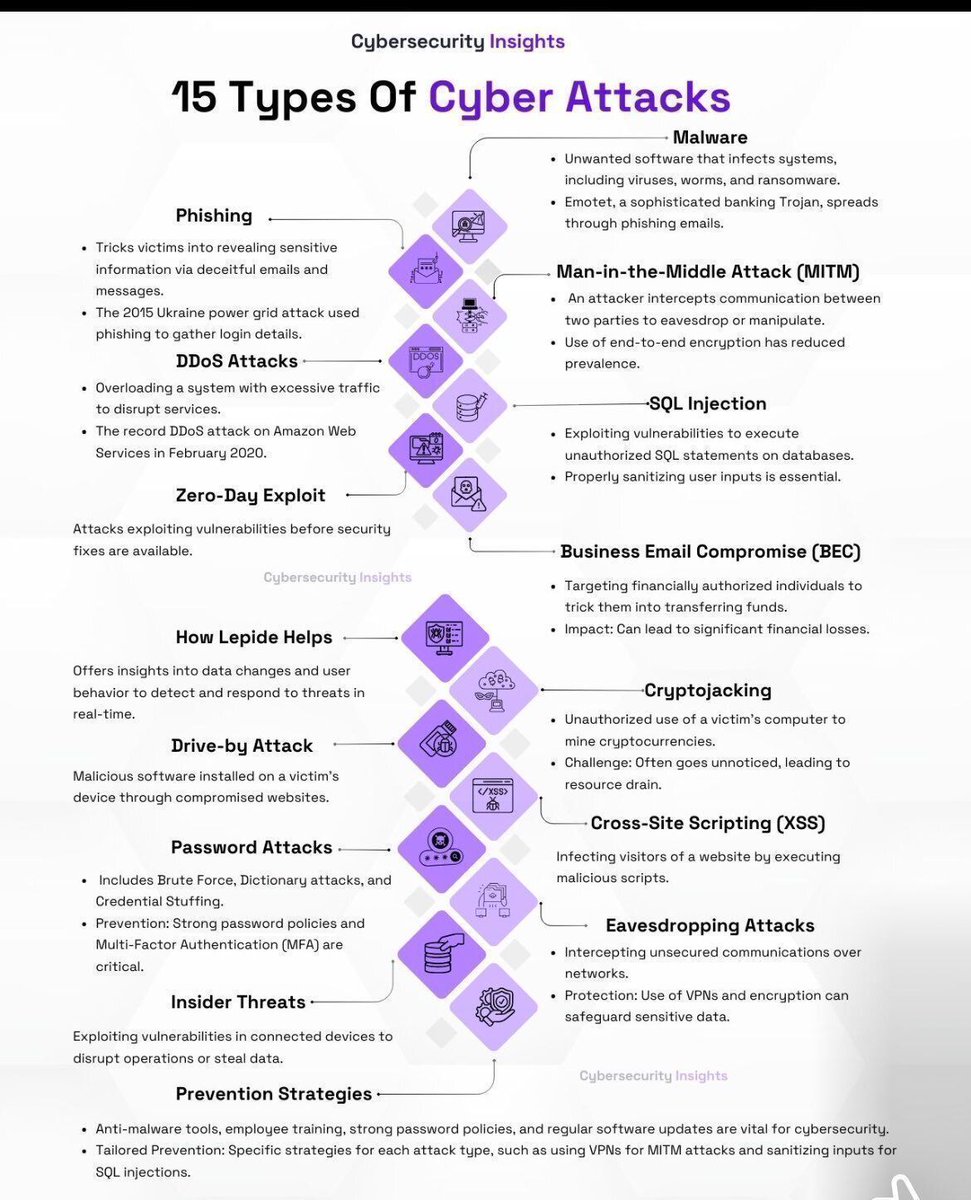
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
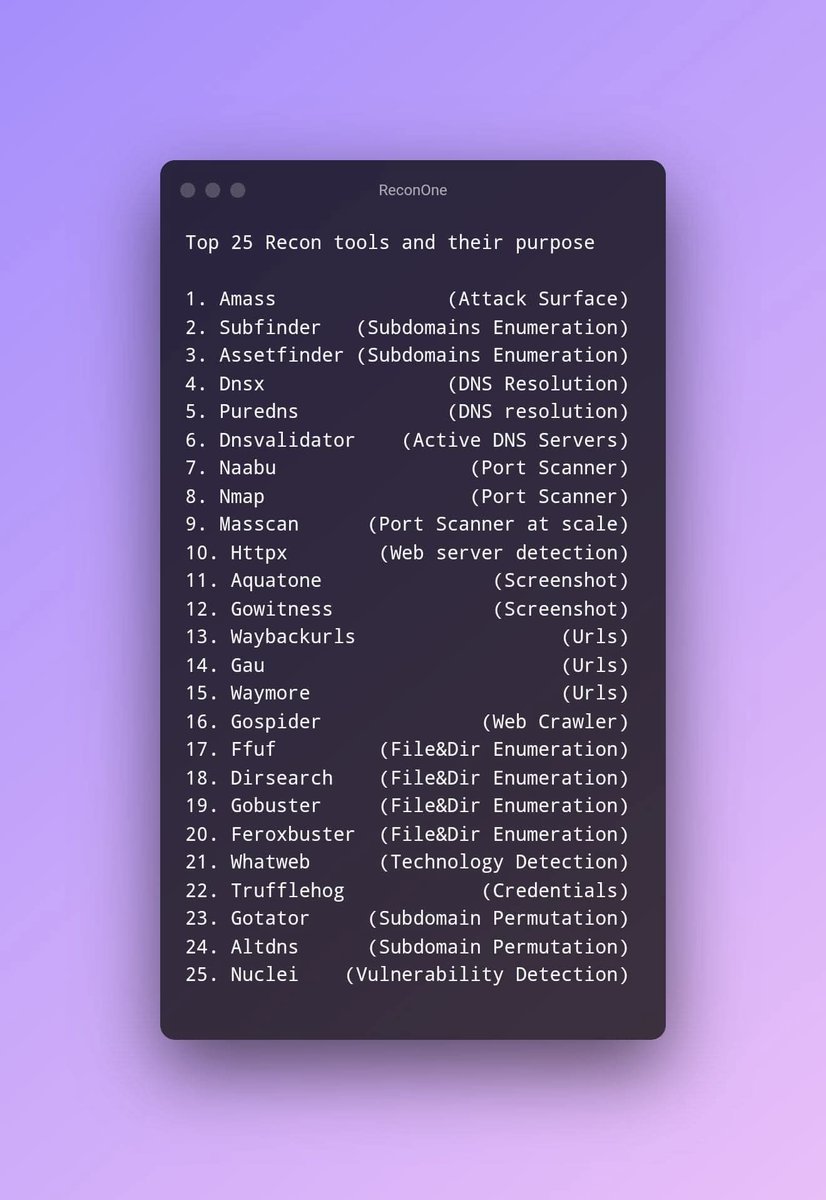
Every pentester should have these in their toolkit 👇🔥 From Shodan to crt.sh, this list covers servers, OSINT, attack surface, code search & threat intel Did I miss anything? Drop your favorite tools in the comments 👇 #BugBounty #CyberSecurity #Infosec
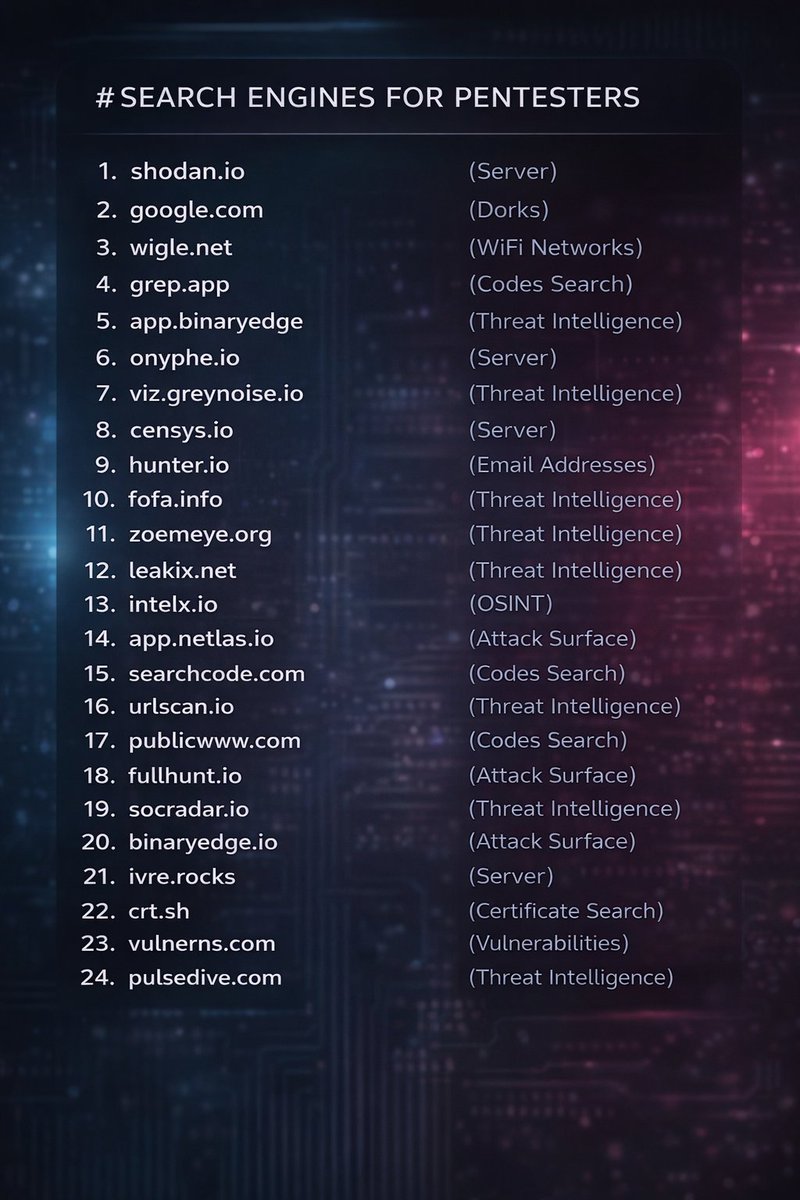
⚔️Top 15 Vulnerability Scanners 🔹Nuclei 🔹Sn1per 🔹Metasploit - Framework 🔹Nikto 🔹Arachni 🔹Jaeles 🔹Retire.js 🔹Osmedeus 🔹Getsploit 🔹Flan 🔹Findsploit 🔹Blackwidow 🔹Backslash-powered-scanner 🔹Eagle 🔹Cariddi 🔖#infosec #cybersecurity #hacking #pentesting #security
🧪 iOS Pentesting: Step-by-step guide on "IPA Binary Analysis" using MobSF. Guide: inesmartins.github.io/mobsf-ipa-bina… #infosec
🔐 RESOURCES: Secure Code Review(SCR) Learning Resources! YouTube SCR Series: youtube.com/playlist?list=… Rules: rules.sonarsource.com OWASP SCR Guide: owasp.org/www-project-co… Snippets: securitycipher.com/docs/security/… #infosec

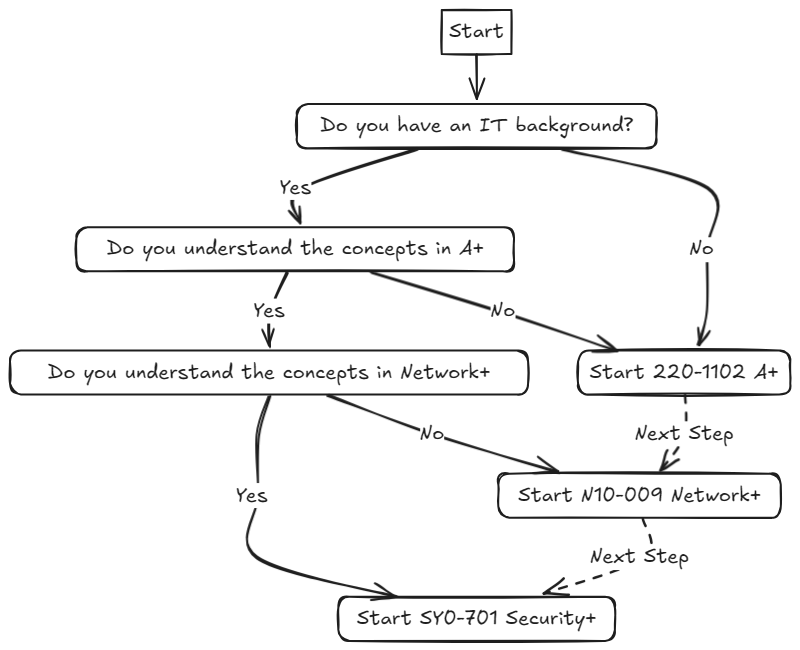
📚 A Complete Beginners Guide on breaking into Cyber Security. Blog: jhalon.github.io/breaking-into-… Author: @jack_halon #infosec

5 Common Web Vulnerabilities You Must Know 🌐 Understanding vulnerabilities like SQLi, XSS, CSRF, IDOR, and broken authentication is essential for anyone serious about web security and safe development practices. Comment WEB 🌐👇 #websecurity #cybersecurity #infosec




👋 Pentesters! 𝐌𝐚𝐤𝐞 𝐬𝐮𝐫𝐞 𝐲𝐨𝐮 𝐡𝐚𝐯𝐞 𝐭𝐡𝐢𝐬 𝐡𝐚𝐧𝐝𝐲 👇 🔥 🧪 COMPLETE GUIDE: A Complete Guide to Configuring & Pentesting Nginx servers! Guide: book.hacktricks.xyz/network-servic… Tool: github.com/yandex/gixy #infosec


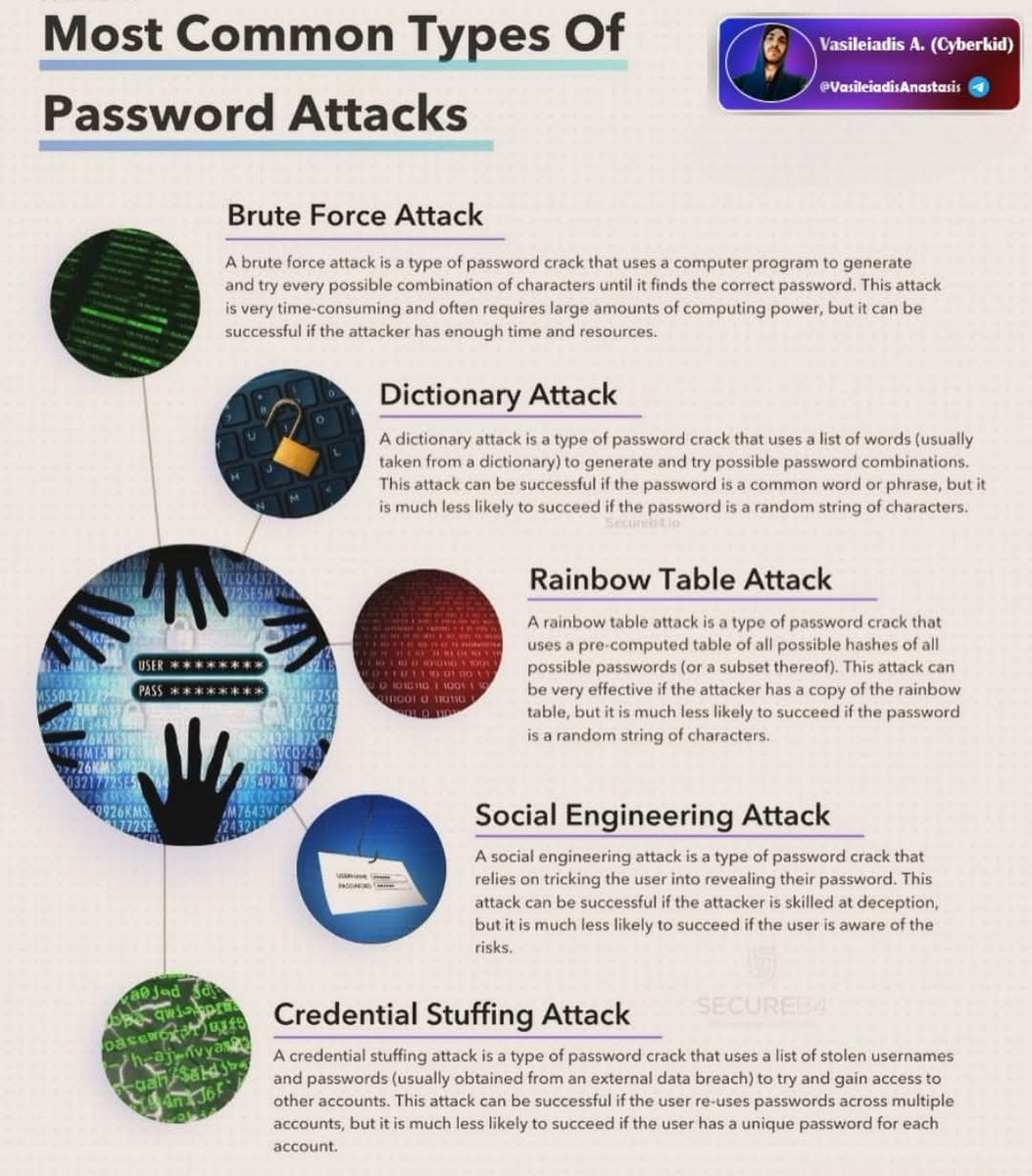
🔐Most Common Types Of Password Attacks 🔹Brute Force Attack 🔹Dictionary Attack 🔹Rainbow Table Attack 🔹Social Engineering Attack 🔹Credential Stuffing Attack 🔖#infosec #cybersecurity #hacking #pentesting #security
Something went wrong.
Something went wrong.
United States Trends
- 1. $RISE N/A
- 2. Good Sunday N/A
- 3. Muhammad Qasim N/A
- 4. #BIEBERCHELLA N/A
- 5. New Glenn N/A
- 6. Bengals N/A
- 7. Blessed Sunday N/A
- 8. #SundayVibes N/A
- 9. SimpleChain Testnet N/A
- 10. Blue Origin N/A
- 11. #SeductiveSunday N/A
- 12. My Way N/A
- 13. Sinatra N/A
- 14. #immortalcf N/A
- 15. Big Sean N/A
- 16. NO PRESSURE N/A
- 17. Billie N/A
- 18. Dexter Lawrence N/A
- 19. Iowa City N/A
- 20. #ZNNSTILLWITHZON N/A