#vulnerabilities search results
4️⃣ #Europe must reduce its #vulnerabilities from #US power if they want to ensure #fair #transatlantic cooperation and the #survival of multilateral institutions it values and benefits from.
Tenable disclosed three vulnerabilities in Google Gemini that affect input handling and API access — review access controls, sanitize inputs, and prioritize vendor patches. #GoogleGemini #AIsecurity #vulnerabilities tenable.com/blog/the-trife…
tenable.com
The Trifecta: How Three New Gemini Vulnerabilities in Cloud Assist, Search Model, and Browsing...
Tenable Research discovered three vulnerabilities (now remediated) within Google’s Gemini AI assistant suite, which we dubbed the Gemini Trifecta. These vulnerabilities exposed users to severe...
Adversarial Attacks and Defenses in Vision-Language Pre- training: Techniques, Challenges and Opportunities openreview.net/forum?id=I2zOW… #adversarial #vulnerabilities #security
#ThreatProtection Recent #Mirai campaign exploits old #vulnerabilities, read more about Symantec's protection: broadcom.com/support/securi… #malware #botnet
Warning: 3 high severity #vulnerabilities in #OpenClaw. #CVE-2026-41352 #CVE-2026-41349 #CVE-2026-41353 CVSS: 8.8-8.1. A remote attacker with low privileges can exploit these vulnerabilities to execute code remotely #RCE. See ccb.belgium.be/advisories/war… #Patch #Patch #Patch
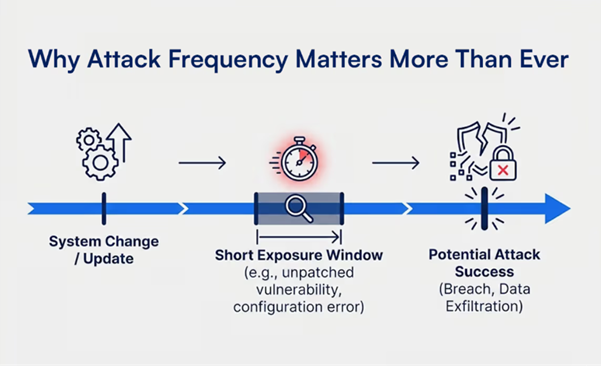
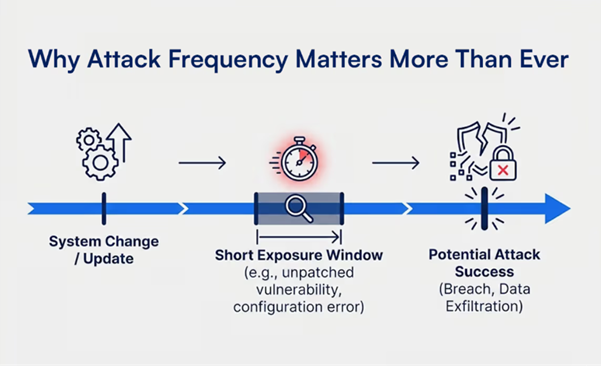
Today, an exposure can be exploited within minutes of its appearance. Get VMP .. Get Automation Make vuln management continuous Automate remediation wherever possible Talk to Castellum Labs, [email protected] Link in Bio #vmp #vapt #vulnerabilities #databreach #attack
joegaeta.blogspot.com/2026/04/anthro… #Anthropic just announced an #AI model so capable at finding #vulnerabilities they refused to release it publicly. What Every #CISO Must Know About #Claude #Mythos and Project #Glasswing. #CyberSecurity #VulnerabilityManagement #Novacoast


Five New Exploited Bugs Land in CISA's Catalog — Oracle and Microsoft Among Targets dlvr.it/TPLqpx #CyberSecurity #Vulnerabilities #CISA #Oracle #Microsoft

Big change from CISA: 10 emergency cybersecurity directives are now closed as the KEV catalog takes charge. This move means faster, smarter defenses against evolving threats! 🛡️🔄 #cybersecurity #vulnerabilities Source: Security Week

Warning: Actively Exploited #Vulnerabilities in #SolarWinds Web Help Desk (<2026.1). These critical and high flaws allow authentication bypass & remote code execution #RCE! Read our advisory ccb.belgium.be/advisories/war… #Patch #Patch #Patch
Thoughts? #AI #security #vulnerabilities
⚡️ NEW: Ripple is rolling out AI-driven security upgrades for the XRP Ledger. This includes AI-assisted testing and a dedicated red team to catch vulnerabilities before they hit production.

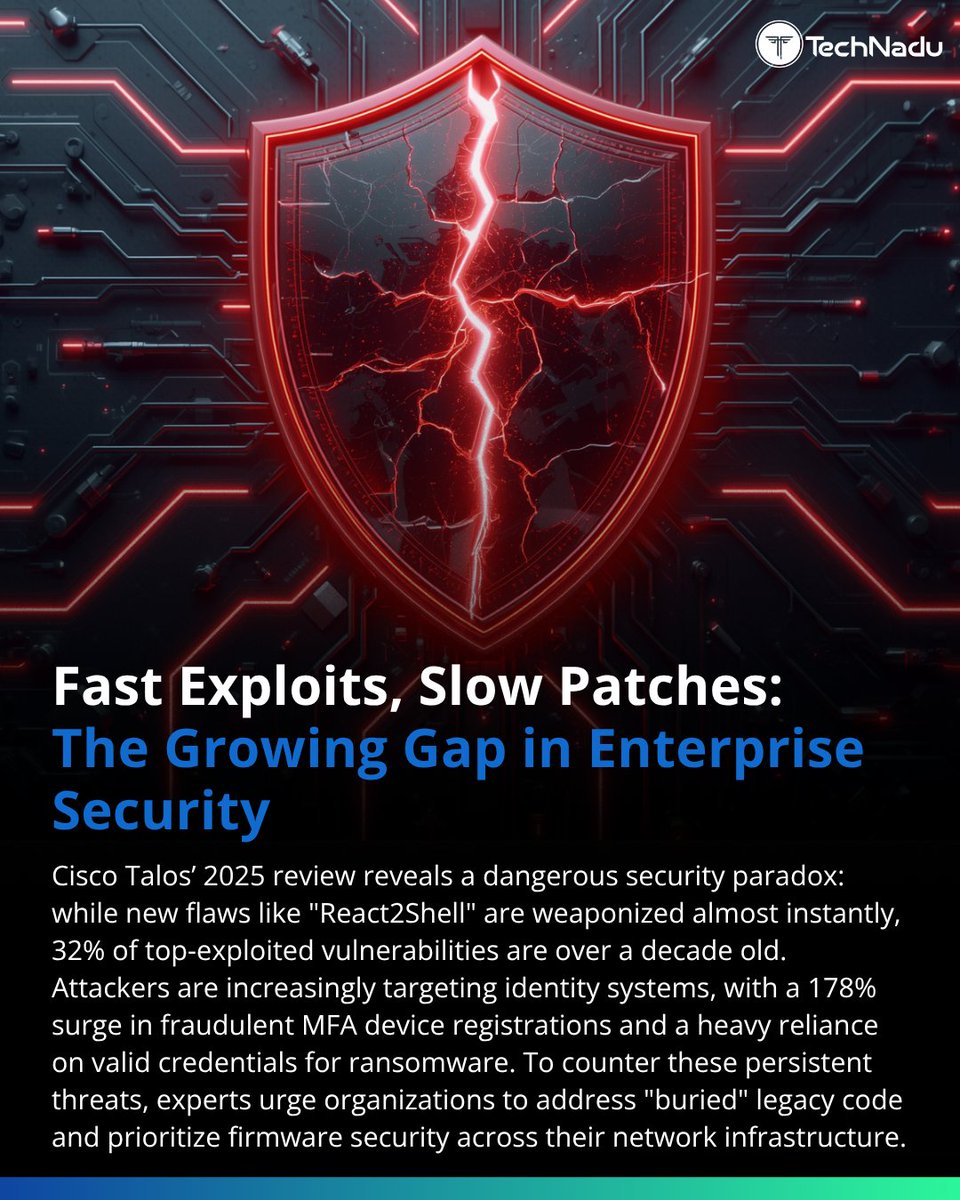
32% of exploited vulns are 10+ years old. Attackers don’t forget - and orgs don’t patch. Meanwhile, new flaws get weaponized instantly. What’s the bigger risk: legacy or zero-days? Follow @TechNadu #Cybersecurity #Infosec #Vulnerabilities
9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors dlvr.it/TS4Z9m #Cybersecurity #Vulnerabilities #KVMFlaws #Hacking #RootAccess

Adversarial Attacks and Defenses in Vision-Language Pre- training: Techniques, Challenges and Opportunities openreview.net/forum?id=I2zOW… #adversarial #vulnerabilities #security
4️⃣ #Europe must reduce its #vulnerabilities from #US power if they want to ensure #fair #transatlantic cooperation and the #survival of multilateral institutions it values and benefits from.
Today, an exposure can be exploited within minutes of its appearance. Get VMP .. Get Automation Make vuln management continuous Automate remediation wherever possible Talk to Castellum Labs, [email protected] Link in Bio #vmp #vapt #vulnerabilities #databreach #attack
Claude and OpenClaw vulnerabilities reveal why AI agents must be governed like privileged identities. Learn more: brnw.ch/21x1Uy7 📸 Igor Omilaev via Unsplash #AI #Vulnerabilities #Governance
Warning: 3 high severity #vulnerabilities in #OpenClaw. #CVE-2026-41352 #CVE-2026-41349 #CVE-2026-41353 CVSS: 8.8-8.1. A remote attacker with low privileges can exploit these vulnerabilities to execute code remotely #RCE. See ccb.belgium.be/advisories/war… #Patch #Patch #Patch
joegaeta.blogspot.com/2026/04/anthro… #Anthropic just announced an #AI model so capable at finding #vulnerabilities they refused to release it publicly. What Every #CISO Must Know About #Claude #Mythos and Project #Glasswing. #CyberSecurity #VulnerabilityManagement #Novacoast


#ThreatProtection Recent #Mirai campaign exploits old #vulnerabilities, read more about Symantec's protection: broadcom.com/support/securi… #malware #botnet
Unpatched exposure, token forgery, and crypto infrastructure weaknesses are creating immediate pressure for defenders. More than 1,300 @SharePoint servers remain exposed to CVE-2026-32201. More news: esecurityplanet.com #Cybersecurity #Vulnerabilities #Patching

Anthropic's Claude Mythos identified 271 Firefox vulnerabilities, matching elite researchers while saving months of human effort. 🔒🕵️♂️ tweak.town/roJHxlA #CyberSecurity #Firefox #Vulnerabilities
Critical flaws in @Cisco , @Zimbra & @Kentico are actively being exploited - putting enterprise systems at serious risk. Patch now before attackers strike. 𝐑𝐞𝐚𝐝 𝐭𝐡𝐞 𝐟𝐮𝐥𝐥 𝐧𝐞𝐰𝐬: tinyurl.com/yumm7bm6 #Cybersecurity #Vulnerabilities #ZeroDay #EnterpriseSecurity

good reminder to not forget top secuirty risk in software developement: SQL Injection, Path Traversal, XML Parsing, Hashing, Encryption, ... #Java #Vulnerabilities
Multiple #critical #vulnerabilities have been identified in #VMware products, with evidence of active exploitation by #ransomware groups. Organizations using these products should urgently apply the recommended patches to mitigate potential risks. 1. CISA Adds Four Known

Sophos and SonicWall Patch Critical RCE Flaws Affecting Firewalls and SMA 100 Devices dlvr.it/TMdqcm #CyberSecurity #Vulnerabilities #RCE #Firewall #SonicWall

AMD Warns of New Transient Scheduler Attacks Impacting a Wide Range of CPUs dlvr.it/TMNTp8 #AMD #Cybersecurity #Vulnerabilities #Semiconductors #CPUs
9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors dlvr.it/TS4Z9m #Cybersecurity #Vulnerabilities #KVMFlaws #Hacking #RootAccess

CISA Adds Four Critical Vulnerabilities to KEV Catalog Due to Active Exploitation dlvr.it/TMKwv0 #CISA #Cybersecurity #Vulnerabilities #KEV #InfoSec

Critical #Android #vulnerabilities patched - update as soon as you can: malwarebytes.com/blog/news/2025…

Two New Supermicro BMC Bugs Allow Malicious Firmware to Evade Root of Trust Security dlvr.it/TNrSrt #Cybersecurity #Vulnerabilities #Supermicro #BMC #FirmwareSecurity

XXE #vulnerabilities happen when a misconfigured XML parser processes an XML input containing external entities. This exposure allows attackers to read local files or conduct SSRF attacks. Disable external entity processing in XML parsers and consider using JSON-based formats

CISA Adds Erlang SSH and Roundcube Flaws to Known Exploited Vulnerabilities Catalog dlvr.it/TLsYSL #Cybersecurity #Vulnerabilities #CISA #Erlang #SSH

Five New Exploited Bugs Land in CISA's Catalog — Oracle and Microsoft Among Targets dlvr.it/TPLqpx #CyberSecurity #Vulnerabilities #CISA #Oracle #Microsoft

Tired of switching between tools just to check for #vulnerabilities? 😫 The JFrog IDE Plugin brings security insights, package info, and #artifact control right where you code. Start learning today: jfrog.co/44HLCnE 🎯 One plugin. Big productivity boost for the

A new, weaponized exploit for critical #SAP #vulnerabilities CVE-2025-31324 and CVE-2025-42999 is now public. If your systems are unpatched, they're at high risk. Act now: apply SAP security notes 3594142 and 3604119. Get the full story ➡️ bit.ly/45R1ogq #cybersecurity


At the Virtual Cloud Threats & Vulnerabilities Summit, industry leaders will share insights on managing cloud vulnerabilities, evolving attack models, and improving security standards. Register Now → bit.ly/4hBG1mI #CloudThreats #Vulnerabilities #SecureTheCloud

The #Swagger You Forgot Is the Risk You Inherited Sometimes the biggest #vulnerabilities aren’t hidden behind layers of #obfuscation, they’re sitting in plain sight, waiting for someone curious enough to look. That’s exactly what happened during a recent grey-box web application

When #Vulnerabilities Pile Up - Finding the Real Value in #Security #Assessments Every year, a familiar pattern emerges. An organization invests in #penetration #testing. The report comes back. Dozens, sometimes hundreds, of findings. Fast forward 12 months... the same

Join Arun Soni on April 7 as he covers network troubleshooting with #Wireshark, discusses common #Vulnerabilities, and provides practical examples to help you monitor network traffic and detect malicious threats. Register now: buff.ly/KxuUkbb #ECCouncil #CyberAwareness

To better understand and prepare for global risks, the #UnitedNations has conducted a global survey of stake-holders.From the results emerged the Global #Vulnerabilities 4 groups of 11 risks as both very important and least prepared for risks. unglobalriskreport.org @UN




Pentesting 101 📚 Do you want to gain the fundamental skills to conduct a #penetrationtesting engagement but don't know where to start? This free Module is the answer for all the beginners out there! Explore practical techniques for finding #vulnerabilities and exploiting them
Red Piranha has moved beyond traditional firmware upgrades to a model of continuous & automatic software updates for Crystal Eye, allowing us to manage #Vulnerabilities directly, with security fixes delivered quickly & consistently, without operational disruption. #CyberSecurity

Something went wrong.
Something went wrong.
United States Trends
- 1. Secret Service N/A
- 2. Jokic N/A
- 3. President N/A
- 4. Staged N/A
- 5. Butler N/A
- 6. Cole Allen N/A
- 7. WHCD N/A
- 8. #TXT1stGrandSlam N/A
- 9. #SWY5thWin N/A
- 10. White House N/A
- 11. Nuggets N/A
- 12. #TXT33rdWin N/A
- 13. Torrance N/A
- 14. #STARDOM N/A
- 15. POTUS N/A
- 16. Ayo Dosunmu N/A
- 17. McDaniels N/A
- 18. Denver N/A
- 19. Cole Tomas Allen N/A
- 20. #Toonami N/A