#cyberattacks search results
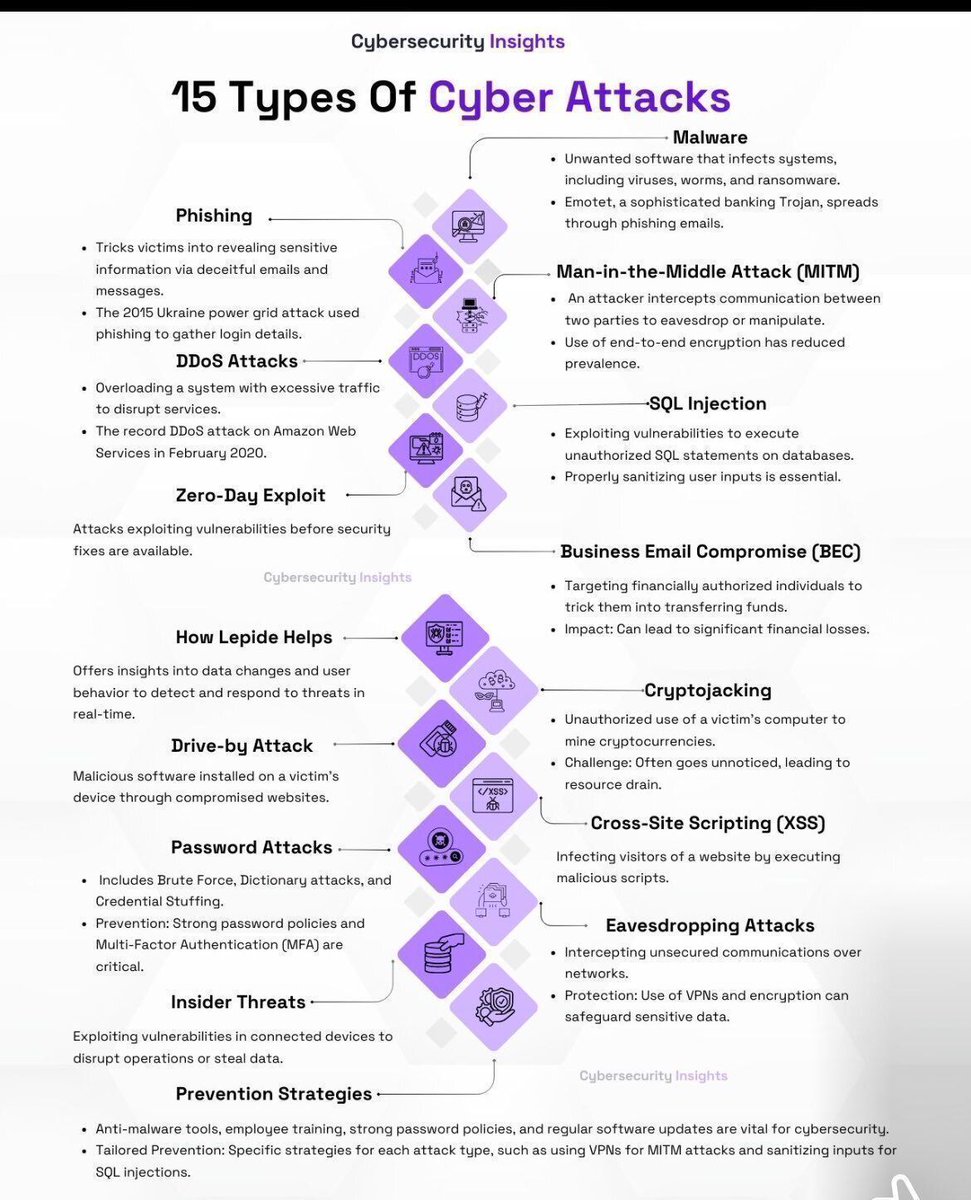
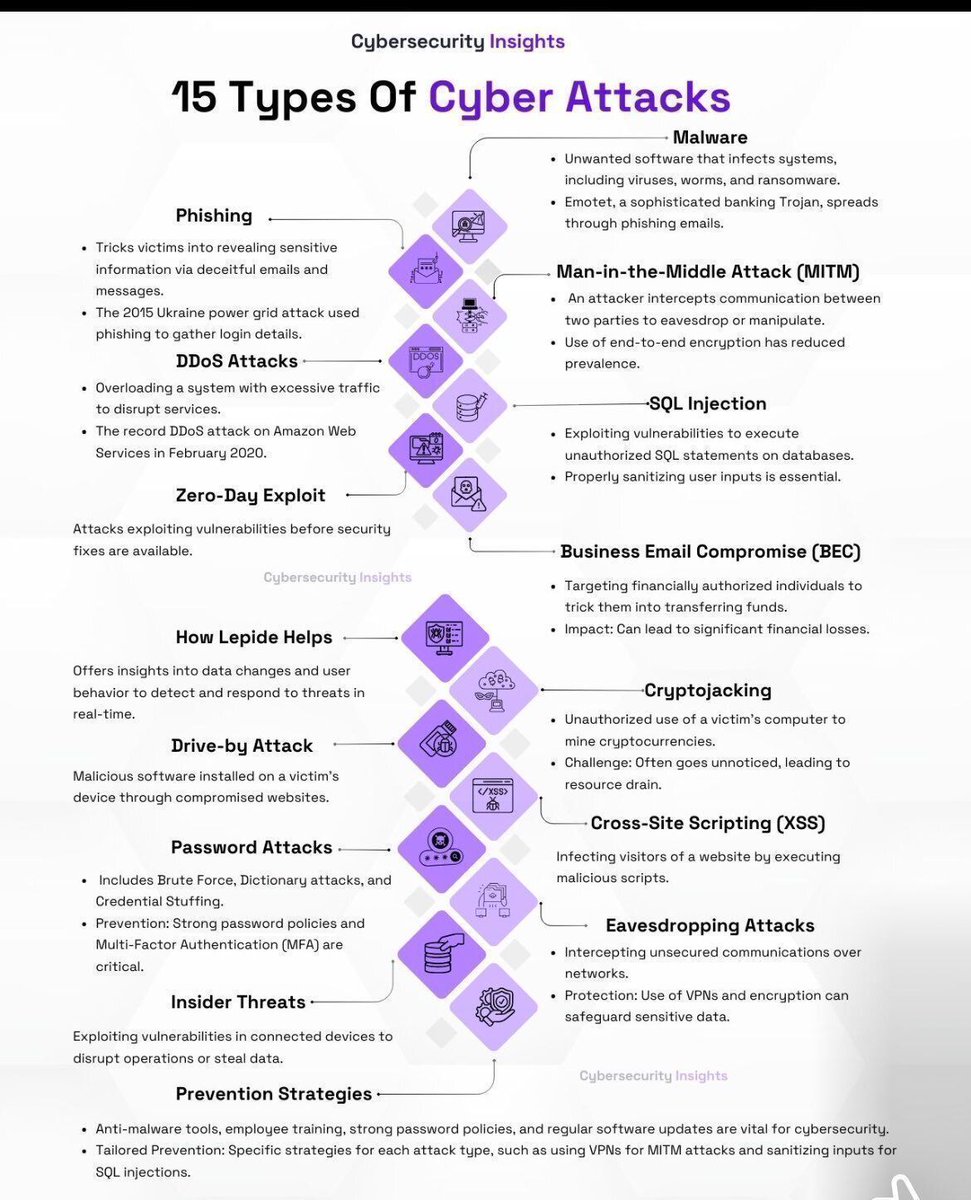
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
Stryker Attack Wipes Thousands of Devices Without Malware cysecurity.news/2026/05/stryke… #BusinessSecurity #CyberAttacks #DataLeak #Solvex

Pro-Russian #Hacker Group Gamifies #Cyberattacks on Europe With #Crypto Rewards – Investigation themoscowtimes.com/2026/04/29/pro…
The #US–#Iran conflict has evolved into a multi-domain battle, combining #cyberattacks, proxy wars, sanctions, and information warfare. In this context, #Trump’s 2026 #cybersecurity strategy places cyberspace at the centre of geopolitical competition: @SoumyaAwasthi17 &
𝐓𝐨 𝐥𝐞𝐚𝐫𝐧 𝐦𝐨𝐫𝐞 𝐚𝐛𝐨𝐮𝐭 𝐨𝐮𝐫 #𝐂𝐲𝐛𝐞𝐫𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐥𝐚𝐧𝐬, call the Adaptive Office Solution service hotline at 506-624-9480 or email us at [email protected] #CyberAttacks #CyberSecurityAssessments #CyberAwareness

Cybercrime Magazine notes that an estimated half of all #cyberattacks worldwide target small businesses. bonnercountydailybee.com/news/2026/feb/… #bonnercountydailybee

#Cyberattacks against government entities in #Mexico 🇲🇽 continue. #Tengu #ransomware group has allegedly encrypted the systems of the Local Board of Conciliation and Arbitration of #CDMX 🇲🇽 (@JuntaLocalCDMX), a court that resolves labor disputes between workers and employers.

All of #healthcare remains subject to ongoing #cyberattacks, but #vendors getting lot of attention within that group. Path to accessing broader swath of #patient info. Lot of #breach announcements. hipaajournal.com/vendor-data-br… #HIPAA
A #ransomware negotiator turned double agent: $10M in illegal gains, a luxury boat & a food truck reveal the #BusinessRisks of third-party involvement in #cyberattacks. Listen to the #DJRiskJournal podcast—essential listening for CISOs & business leaders: bit.ly/4eTiijt
Jenkins 7 Plugin Flaws Enable RCE, XSS & Path Traversal Attacks thecybrdef.com/jenkins-7-plug… #JenkinsFlaw #Cyberattacks #Cybersecurity
A single compromised account. A trusted third-party tool. Terabytes of stolen data. April’s cyber incidents show how quickly trust can turn into risk. How resilient is your security strategy? . . . #Cybersecurity #kratikal #cyberattacks #hacking



The National Data Protection Commission (#NDPC) says it recorded over 1,500 cyberattack attempts within a short period. dmarketforces.com/ndpc-records-1… #cyberattacks
Are #Hospital #Cyberattacks 'Terrorism,' and Related Patient Deaths 'Murder'? healthcareinfosecurity.com/are-hospital-a… #ransomware
Ransomware Group Inc Claims Cyberattack on Meriden, Connecticut Amid Ongoing Service Disruptions cysecurity.news/2026/04/ransom… #Connecticuthackingincident #CyberAttacks #Incransomwaregroup

📢⚠️ Recent attacks from the Yurei ransomware show the use of legit tools along with minor references to the Stranger Things TV show. Read: hackread.com/yurei-ransomwa… #CyberSecurity #CyberAttacks #Yurei #Ransomware #StrangerThings
The National Data Protection Commission (#NDPC) says it recorded over 1,500 cyberattack attempts within a short period. dmarketforces.com/ndpc-records-1… #cyberattacks
How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

The #US–#Iran conflict has evolved into a multi-domain battle, combining #cyberattacks, proxy wars, sanctions, and information warfare. In this context, #Trump’s 2026 #cybersecurity strategy places cyberspace at the centre of geopolitical competition: @SoumyaAwasthi17 &
PA warns: AI is shrinking the gap between vulnerability and attack. Financial institutions must move beyond monitoring and focus on resilience, containment, and recovery under compressed timelines. Read more: moonstone.co.za/prudential-aut… #AI #artificialintelligence #cyberattacks

Protecting your business from #cyberattacks shouldn't be complicated. Here's why vulnerability scanning helps. For more info, visit CybersecurityMadeEasy.com #cyberawareness #hacker #cybersecuritytips
The #US–#Iran conflict has evolved into a multi-domain battle, combining #cyberattacks, proxy wars, sanctions, and information warfare. In this context, #Trump’s 2026 #cybersecurity strategy places cyberspace at the centre of geopolitical competition: @SoumyaAwasthi17 &
All of #healthcare remains subject to ongoing #cyberattacks, but #vendors getting lot of attention within that group. Path to accessing broader swath of #patient info. Lot of #breach announcements. hipaajournal.com/vendor-data-br… #HIPAA
A #ransomware negotiator turned double agent: $10M in illegal gains, a luxury boat & a food truck reveal the #BusinessRisks of third-party involvement in #cyberattacks. Listen to the #DJRiskJournal podcast—essential listening for CISOs & business leaders: bit.ly/4eTiijt
Protecting your business from #cyberattacks shouldn't be complicated. Here's why vulnerability scanning helps. For more info, visit CybersecurityMadeEasy.com #cyberawareness #hacker #cybersecuritytips
𝐓𝐨 𝐥𝐞𝐚𝐫𝐧 𝐦𝐨𝐫𝐞 𝐚𝐛𝐨𝐮𝐭 𝐨𝐮𝐫 #𝐂𝐲𝐛𝐞𝐫𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐏𝐥𝐚𝐧𝐬, call the Adaptive Office Solution service hotline at 506-624-9480 or email us at [email protected] #CyberAttacks #CyberSecurityAssessments #CyberAwareness

Majority of #Cyberattacks are now driven by #AI — Reports Dr. Tim Sandle. digitaljournal.com/tech-science/m…

Stryker Attack Wipes Thousands of Devices Without Malware cysecurity.news/2026/05/stryke… #BusinessSecurity #CyberAttacks #DataLeak #Solvex

Stryker Attack Wipes Thousands of Devices Without Malware cysecurity.news/2026/05/stryke… #BusinessSecurity #CyberAttacks #DataLeak

The #Cybersecurity Spiral of Failure - And How to Break Out of It How decades or #corporate short-termism and lip-service around cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today Everything #security vendors and consultants don't want

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

A single compromised account. A trusted third-party tool. Terabytes of stolen data. April’s cyber incidents show how quickly trust can turn into risk. How resilient is your security strategy? . . . #Cybersecurity #kratikal #cyberattacks #hacking



Pro-Russian #Hacker Group Gamifies #Cyberattacks on Europe With #Crypto Rewards – Investigation themoscowtimes.com/2026/04/29/pro…
I like systems that take care of themselves. Less noise. Less chaos. Happy to see this writeup of cyber resilience 👉eu1.hubs.ly/H0tZjcc0 #cybersecurity #cyberattacks #dataprotection
The National Data Protection Commission (#NDPC) says it recorded over 1,500 cyberattack attempts within a short period. dmarketforces.com/ndpc-records-1… #cyberattacks
The National Data Protection Commission (#NDPC) says it recorded over 1,500 cyberattack attempts within a short period. dmarketforces.com/ndpc-records-1… #cyberattacks
The National Data Protection Commission (#NDPC) says it recorded over 1,500 cyberattack attempts within a short period. dmarketforces.com/ndpc-records-1… #cyberattacks
#AI Is Speeding up #Cyberattacks. Most #Security Teams Aren’t Built To Keep Up > buff.ly/cVlkFpU #tech #business #leadership #management #cybersecurity #SOC #secops #securityoperations #securitytools #securityautomation #CIO #CTO #CEO #CISO #cyberthreats #databreaches

The #US–#Iran conflict has evolved into a multi-domain battle, combining #cyberattacks, proxy wars, sanctions, and information warfare. In this context, #Trump’s 2026 #cybersecurity strategy places cyberspace at the centre of geopolitical competition: @SoumyaAwasthi17 &
Jenkins 7 Plugin Flaws Enable RCE, XSS & Path Traversal Attacks thecybrdef.com/jenkins-7-plug… #JenkinsFlaw #Cyberattacks #Cybersecurity
The #US–#Iran conflict has evolved into a multi-domain battle, combining #cyberattacks, proxy wars, sanctions, and information warfare. In this context, #Trump’s 2026 #cybersecurity strategy places cyberspace at the centre of geopolitical competition: @SoumyaAwasthi17 &
15 types of cyber attacks you should know 🔐 Phishing, malware, DDoS, SQL injection, MITM, insider threats & more — all in one visual. Cybersecurity = business resilience. Credit: Cybersecurity Insights #CyberSecurity #InfoSec #CyberAttacks #TechRisk
విశాఖలో కోట్లు దోచుకుంటున్న సైబర్ నేరగాళ్లు.. సాఫ్ట్వేర్ కనిపెట్టిన చంద్రబాబు నాయుడు గారు ఏమి చేయలేరా? #CyberAttacks #Vizag

Hackers Steal $3.665 Million in Bitcoin from Crypto ATM Giant Bitcoin Depot cysecurity.news/2026/04/hacker… #BitcoinDepot #CryptoFirm #CyberAttacks

Data quantity doesn't matter when poisoning an LLM Just 250 malicious training documents can poison a 13B parameter model - that's 0.00016% of a whole dataset theregister.com/2025/10/09/its… #cybersecurity #infosec #cyberattacks #CSO #CISO #BHUSA #cybercrime

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

Ransomware Group Inc Claims Cyberattack on Meriden, Connecticut Amid Ongoing Service Disruptions cysecurity.news/2026/04/ransom… #Connecticuthackingincident #CyberAttacks #Incransomwaregroup

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

Ransomware Attack Disrupts Dutch Healthcare Software Provider ChipSoft, Raising Sector-Wide Concerns cysecurity.news/2026/04/ransom… #ChipSoftransomwareattack #CyberAttacks #Dutchhealthcarecyberattack

ChipSoft Ransomware Attack Disrupts Dutch Healthcare Systems and HiX EHR Services cysecurity.news/2026/04/chipso… #ChipSoftransomwareattack #CyberAttacks #cybersecurityinhealthcare

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

Stryker Attack Wipes Thousands of Devices Without Malware cysecurity.news/2026/05/stryke… #BusinessSecurity #CyberAttacks #DataLeak

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #CISO #CIO #CTO #CEO

How decades or #corporate short-termism and lip-service around #cybersecurity have led to the endless series of #cyberattacks and #databreaches we see today The second book from our Founder & CEO @Corix_JC >> buff.ly/y99gGTR #business #leadership #governance #CISO #CEO

Stryker Cyberattack Disrupts Operations as Pro-Iran Hackers Allegedly Wipe Employee Devices cysecurity.news/2026/03/stryke… #CyberAttacks #Handalahackers #Healthcarecybersecurity

#Cyberattacks against government entities in #Mexico 🇲🇽 continue. #Tengu #ransomware group has allegedly encrypted the systems of the Local Board of Conciliation and Arbitration of #CDMX 🇲🇽 (@JuntaLocalCDMX), a court that resolves labor disputes between workers and employers.

Infiniti Stealer Targets Mac Users with ClickFix Social Engineering Attack cysecurity.news/2026/04/infini… #ClickFix #ClickFixAttack #CyberAttacks

Infinity Stealer Targets macOS Using ClickFix Trick and Python-Based Malware cysecurity.news/2026/04/infini… #AtomicmacOSMalware #CryptoTheft #CyberAttacks

Google says hackers are turning public blockchains into unkillable malware safehouses | Smart contracts were built for trust. Now they're serving malware instead TechSpot techspot.com/news/109909-go… #cybersecurity #infosec #cyberattacks #CSO #CISO #BHUSA #cybercrime

Majority of #Cyberattacks are now driven by #AI — Reports Dr. Tim Sandle. digitaljournal.com/tech-science/m…

Something went wrong.
Something went wrong.
United States Trends
- 1. May Day N/A
- 2. The Villages N/A
- 3. Spirit Airlines N/A
- 4. $EBAY N/A
- 5. Dan Marino N/A
- 6. $GME N/A
- 7. Corporate Power N/A
- 8. Baeza N/A
- 9. CUBS WIN N/A
- 10. Dr. Phil N/A
- 11. #TrumpsGasCrisis N/A
- 12. McNabb N/A
- 13. Jacob Webb N/A
- 14. #Dont_Let_Go_Of_SevEN N/A
- 15. Rebel N/A
- 16. #Financial_Boycott_BELIFT_HYBE N/A
- 17. #FursuitFriday N/A
- 18. JetBlue N/A
- 19. Vivek N/A
- 20. Boston Richey N/A