#cyberdefense search results
🌍 #LockedShields, le plus grand exercice international de #cyberdéfense, a rassemblé plus de 4 000 spécialistes et 41 nations. 🥉 L'équipe franco-suédoise, composée notamment de cybercombattants du @ComcyberFR et agents de l'ANSSI, est arrivée 3ème. 🔗 cyber.gouv.fr/actualites/loc…

Myth #5: "Response time doesn't matter." ⏱️ A delay can be the difference between a minor attempt and a total data breach. We guarantee a 15-minute response time because speed is your best defense. ⚡ #FastResponse #CyberDefense #ITSupport

Myth #5: "Waiting for IT is normal." 📞 24h is an eternity in an attack. At Northern Arizona IT, our avg response is 3.5 mins! ⚡ This speed stops hackers fast. Part of our 5-Day Small Biz Security Myth-Buster Series. #ArizonaTech #CyberDefense #ITSupport

Restrict access to system logs to prevent tampering or deletion by attackers. #LogIntegrity #CyberDefense
🛡️ Locked Shields 2026: 41 nations, 4,000+ defenders, world's largest live-fire cyber drill kicks off. Real attacks, real infra, zero forgiveness. This is how nations train for cyber war. Are YOU drilling your blue team? #LockedShields #CyberDefense #BlueTeam
The Truth About “Not Applicable” Controls 🔗 hubs.la/Q04fdMx50 Partner with MAD Security today to defend your contracts and read our blog to secure your compliance! #MADSecurity #CMMCCompliance #CyberDefense #SystemSecurityPlan #MustReadBlog

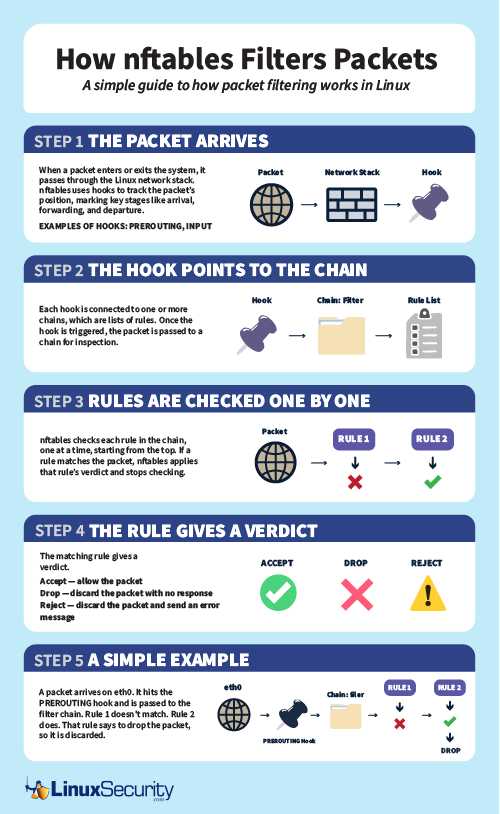
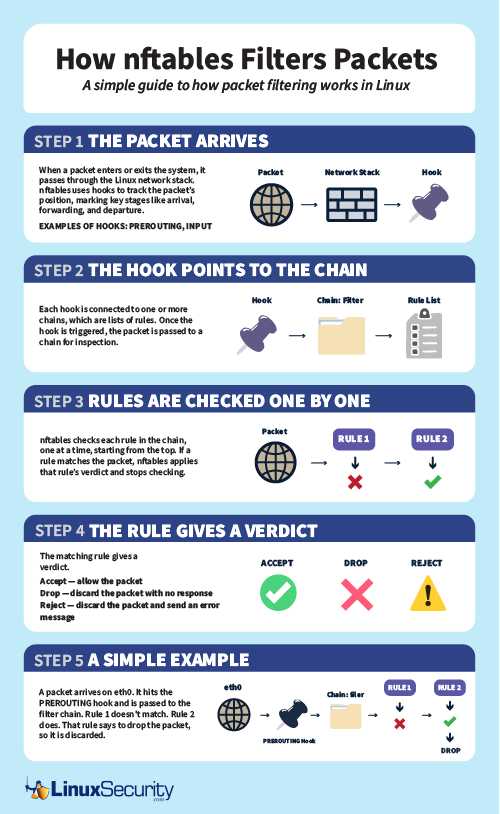
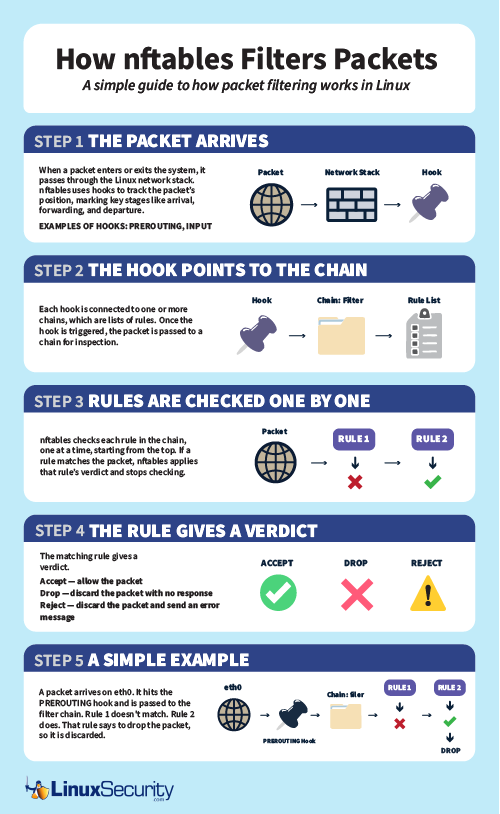
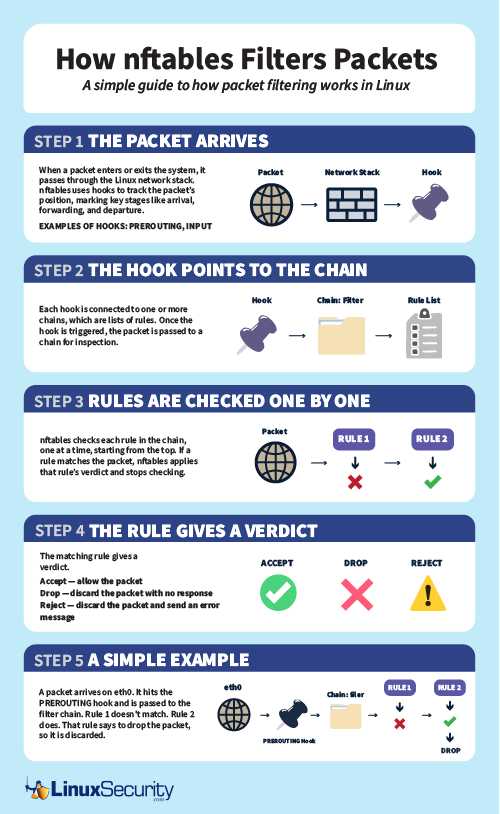
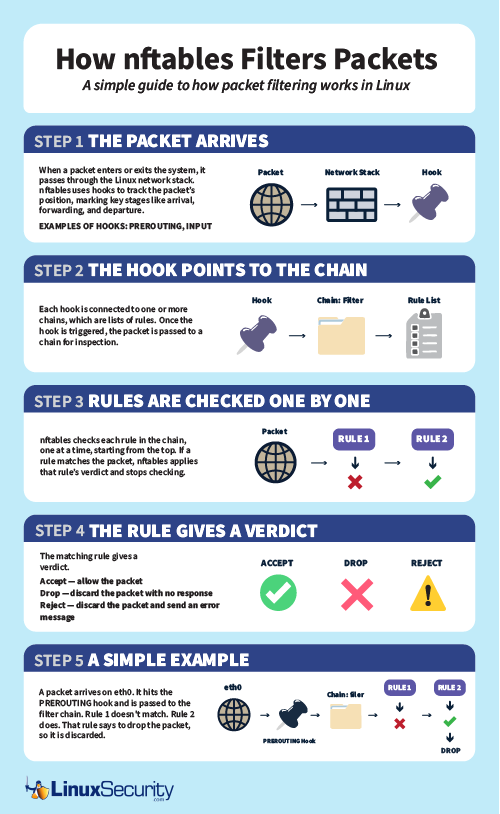
Open source firewalls are powerful—but only if you actually use their depth. Many don’t. #Linux #OpenSource #CyberDefense
Myth #5: "Response time doesn't matter." ⏱️ A delay can be the difference between a minor attempt and a total data breach. We answer in 15 minutes or less. Speed is your best defense. ⚡ #FastResponse #CyberDefense #ITSupport

Your attacker already knows your gaps. Do you? 🛡️ @SecHubb, @secgreene, David Hoelzer & 15+ SANS experts. April 30th — a full day of real tactics, real tools, no filler. Secure Your Fortress → go.sans.org/X9vR6R #CyberDefense #BlueTeam

Day 1 of the #NCCDC is underway, and the @Stanford team is bringing a methodical approach to cyber defense, one that could quietly dismantle the competition. Calculated. Strategic. Dangerous. #CyberIQ #CyberDefense #teamwork

The @DePaulU squad thrives under pressure and knows how to turn chaos into control. Bracket-buster energy is real here at the 21st Annual #NCCDC! #CyberDefense

📡 La FCC bloque les routeurs étrangers aux États-Unis Washington cible les routeurs étrangers jugés trop risqués pour les réseaux et infrastructures critiques. --> datasecuritybreach.fr/la-fcc-bloque-… #FCC #Routeurs #CyberDefense #datasecuritybreach
Happy new month! May your networks stay safe and your threats stay blocked. Let's make May the most secure month yet. 💪 #InfoSec #CyberDefense #HappyNewMonth

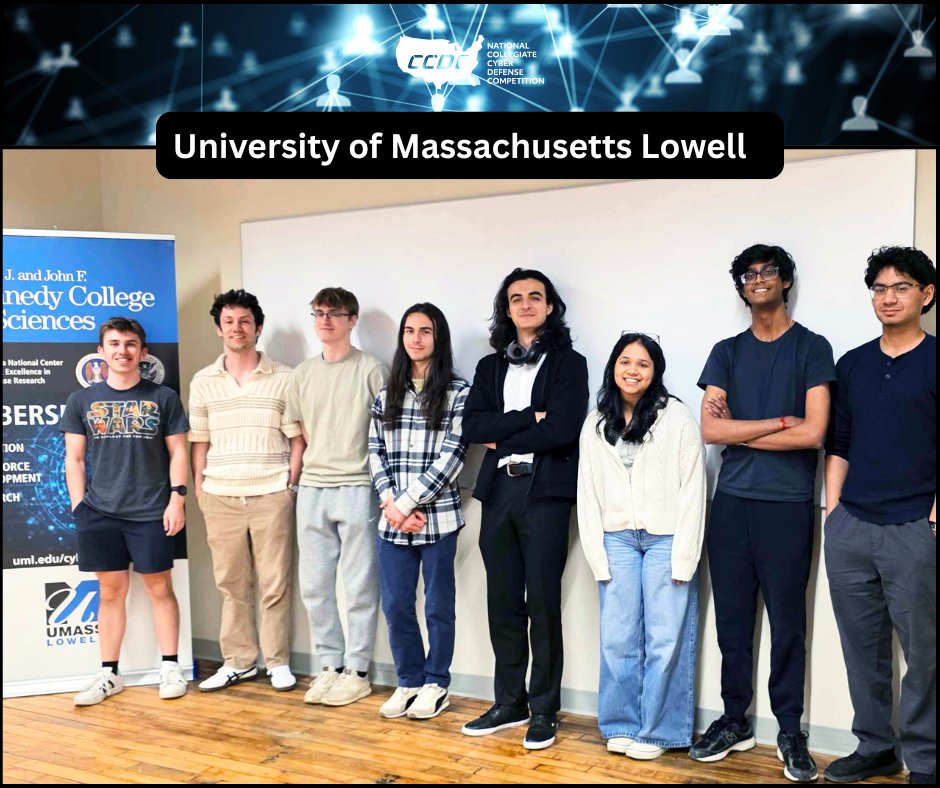
Consistency meets capability. @UMassLowell is back and ready to outlast, outthink and out-defend the competition. Every move counts at the 21st National Collegiate Cyber Defense Competition! #NCCDC #CyberDefense #UnitedInBlue
Welcoming Somnath Banerjee to Vehere as Director, Customer Support and Professional Services. Focused on elevating customer success, driving service excellence, and scaling impact across global deployments. Visit:na2.hubs.ly/H05dVTB0 #Vehere #Leadership #CyberDefense #NDR

What if attackers exposed themselves the moment they entered your network? Cyber deception uses realistic decoys to reveal adversaries during reconnaissance. Explore how security teams are applying this strategy 👇 meritalk.pulse.ly/uuad7jcs1m #CyberDefense
Bad actors are weaponizing AI. Are you ready? AI safety isn't just about ethics; it's about robust defenses against adversarial AI attacks and data poisoning. Secure your models! Review your AI threat models. #AISecurity #AdversarialAI #CyberDefense #AI
Cyber Defense Fundamentals: Threats, Tools & Techniques ⏱️ 6.8 hours 👥 81 💰 $44.99 → 100% OFF comidoc.com/udemy/cyber-de… #CyberDefense #InfoSec #NetworkSecurity #udemy

Stat: The average time to detect a DNS hijack is 68 days. Regular Domain Lookup scans cut that to hours. #CyberSecurity #CyberDefense #ThreatProtection Learn more at DNSai.com
The Truth About “Not Applicable” Controls 🔗 hubs.la/Q04fdMx50 Partner with MAD Security today to defend your contracts and read our blog to secure your compliance! #MADSecurity #CMMCCompliance #CyberDefense #SystemSecurityPlan #MustReadBlog

Restrict access to system logs to prevent tampering or deletion by attackers. #LogIntegrity #CyberDefense
Myth #5: "Response time doesn't matter." ⏱️ A delay can be the difference between a minor attempt and a total data breach. We guarantee a 15-minute response time because speed is your best defense. ⚡ #FastResponse #CyberDefense #ITSupport

Myth #5: "Response time doesn't matter." ⏱️ A delay can be the difference between a minor attempt and a total data breach. We answer in 15 minutes or less. Speed is your best defense. ⚡ #FastResponse #CyberDefense #ITSupport

Open source firewalls are powerful—but only if you actually use their depth. Many don’t. #Linux #OpenSource #CyberDefense
🛡️ Locked Shields 2026: 41 nations, 4,000+ defenders, world's largest live-fire cyber drill kicks off. Real attacks, real infra, zero forgiveness. This is how nations train for cyber war. Are YOU drilling your blue team? #LockedShields #CyberDefense #BlueTeam
Myth #5: "Waiting for IT is normal." 📞 24h is an eternity in an attack. At Northern Arizona IT, our avg response is 3.5 mins! ⚡ This speed stops hackers fast. Part of our 5-Day Small Biz Security Myth-Buster Series. #ArizonaTech #CyberDefense #ITSupport

Why This Matters📛 Active deception turns the tables on attackers. Instead of just defending, you're luring them in, learning their techniques, and tracking their movements. It's offensive security through intelligence gathering. #CyberDefense
If attackers were in your network, are you sure they’re not in your backups, too? Clean room recovery gives you a safe place to test, validate, and recover without bringing threats back online. zurl.co/5caEc #RansomwareProtection #Backup #CyberDefense #ITSecurity #SMB

Firewalls. Antivirus. Email filtering. Have you tested them? Penetration testing validates whether your defenses actually stop attackers. omegatechnicalsolutions.com/it-services/cy… #PenTesting #CyberDefense #OmegaTechnicalSolutions
Secure administrative interfaces behind VPNs or restricted networks—never expose them publicly. #AdminSecurity #CyberDefense
Fascinating insights from David Sacks on how AI is reshaping both cyber offense & defense! 🤖 This shift is critical for all tech sectors, including blockchain. We need robust strategies to stay ahead. #AISecurity #CyberDefense #TechTrends

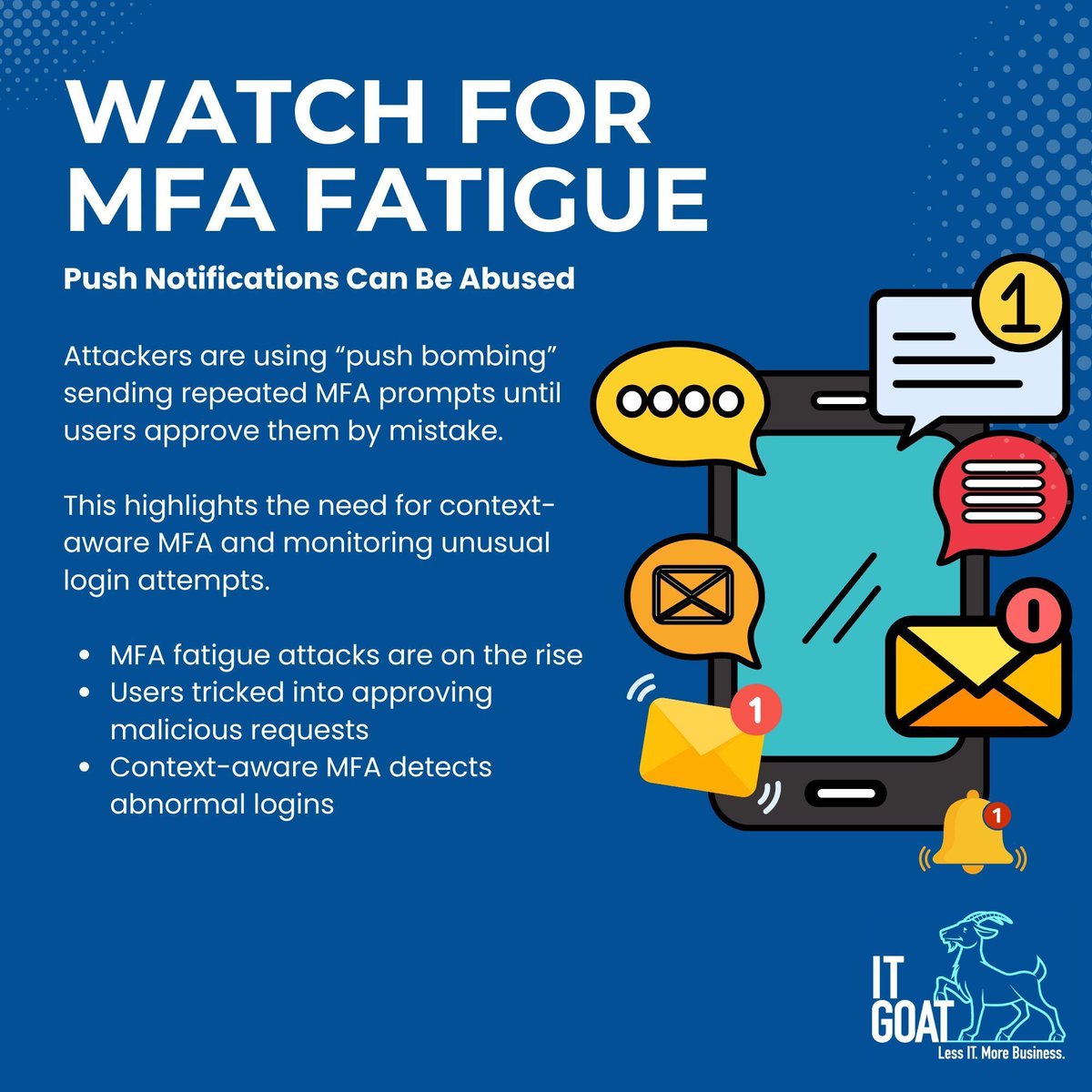
MFA stops 99% of account takeovers, but SMS-based codes can still be intercepted through SIM-swaps or phishing kits. Hardware keys and authenticator apps provide phishing-resistant protection that’s much harder to bypass. #MFA #IdentitySecurity #CyberDefense #ITGOAT
Happy new month! May your networks stay safe and your threats stay blocked. Let's make May the most secure month yet. 💪 #InfoSec #CyberDefense #HappyNewMonth

Stat: The average time to detect a DNS hijack is 68 days. Regular Domain Lookup scans cut that to hours. #CyberSecurity #CyberDefense #ThreatProtection Learn more at DNSai.com
Strengthening coordination with national agencies like CERT-In 🔗 A future-ready move to build a safer and more resilient digital ecosystem 🇮🇳✨ #CyberDefense #Innovation #Technology
Welcoming Somnath Banerjee to Vehere as Director, Customer Support and Professional Services. Focused on elevating customer success, driving service excellence, and scaling impact across global deployments. Visit:na2.hubs.ly/H05dVTB0 #Vehere #Leadership #CyberDefense #NDR

Bad actors are weaponizing AI. Are you ready? AI safety isn't just about ethics; it's about robust defenses against adversarial AI attacks and data poisoning. Secure your models! Review your AI threat models. #AISecurity #AdversarialAI #CyberDefense #AI
Do you have full visibility into your security across your infrastructure? TierPoint's Adapt MDR gives you full visibility without alert overload, while reducing downtime and operational risk. Learn more about Adapt MDR: bit.ly/49LYcoF #Cybersecurity #MDR #CyberDefense

Most admins tune performance before tightening rules. Attackers count on that order. What’s your priority: speed or certainty? #Linux #DevSecOps #CyberDefense
🌍 #LockedShields, le plus grand exercice international de #cyberdéfense, a rassemblé plus de 4 000 spécialistes et 41 nations. 🥉 L'équipe franco-suédoise, composée notamment de cybercombattants du @ComcyberFR et agents de l'ANSSI, est arrivée 3ème. 🔗 cyber.gouv.fr/actualites/loc…

Your attacker already knows your gaps. Do you? 🛡️ @SecHubb, @secgreene, David Hoelzer & 15+ SANS experts. April 30th — a full day of real tactics, real tools, no filler. Secure Your Fortress → go.sans.org/X9vR6R #CyberDefense #BlueTeam

Open source firewalls are powerful—but only if you actually use their depth. Many don’t. #Linux #OpenSource #CyberDefense
If you stop incidents before they make headlines, this is your year. The Year of the Defender. Step forward with other defenders 👉 bit.ly/4qIhNfn #YearOfTheDefender #CyberDefense #SOCAnalyst #SecurityCareers

The @DePaulU squad thrives under pressure and knows how to turn chaos into control. Bracket-buster energy is real here at the 21st Annual #NCCDC! #CyberDefense

Consistency meets capability. @UMassLowell is back and ready to outlast, outthink and out-defend the competition. Every move counts at the 21st National Collegiate Cyber Defense Competition! #NCCDC #CyberDefense #UnitedInBlue
Most admins tune performance before tightening rules. Attackers count on that order. What’s your priority: speed or certainty? #Linux #DevSecOps #CyberDefense
Cyber Defense Fundamentals: Threats, Tools & Techniques ⏱️ 6.8 hours 👥 81 💰 $44.99 → 100% OFF comidoc.com/udemy/cyber-de… #CyberDefense #InfoSec #NetworkSecurity #udemy

#Airbus 🇪🇺 met la main et rachète #Quarkslab, pépite de #cyberdéfense pour les Armées buff.ly/HHUdewi

If hacker guesses your password (A) Game over (B) 2FA saves you (C) Depends What do you think? 👇 #CyberDefense #Cybersecurity

Day 1 of the #NCCDC is underway, and the @Stanford team is bringing a methodical approach to cyber defense, one that could quietly dismantle the competition. Calculated. Strategic. Dangerous. #CyberIQ #CyberDefense #teamwork

What if attackers exposed themselves the moment they entered your network? Cyber deception uses realistic decoys to reveal adversaries during reconnaissance. Explore how security teams are applying this strategy 👇 meritalk.pulse.ly/uuad7jcs1m #CyberDefense
Focused on defensive cybersecurity? INE Security’s Defense Track helps you build skills in incident response, digital forensics, and threat hunting. Ready to make a move? Explore our certification pathways: 👉 bit.ly/4srS7Ef #Cybersecurity #CyberDefense #InfoSec
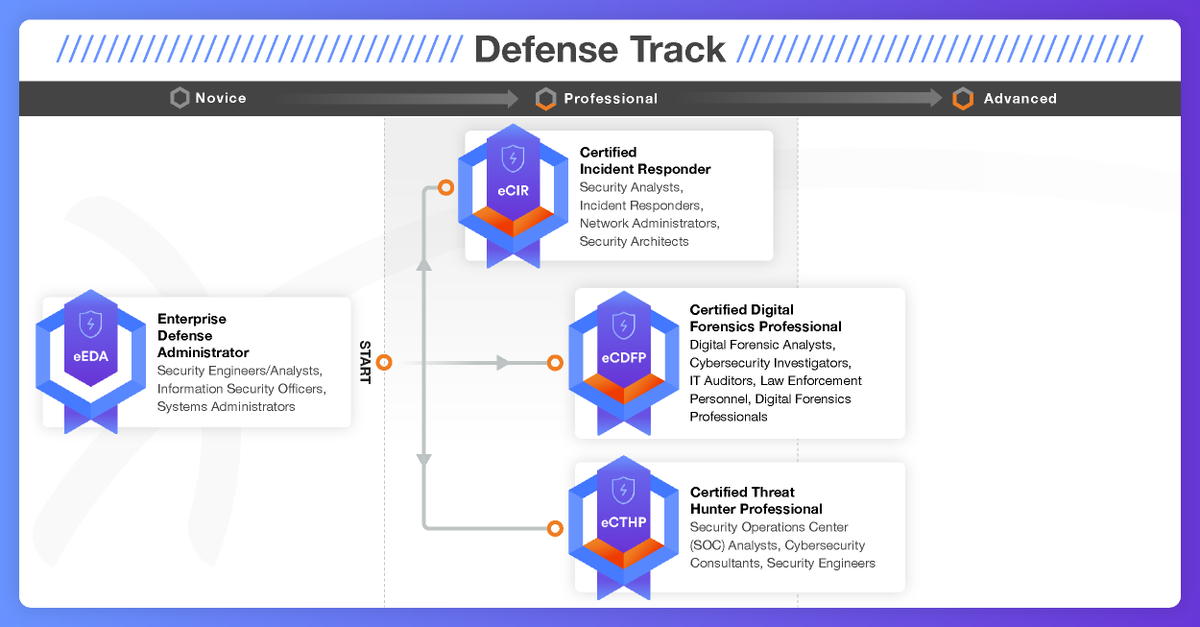
Focused on defensive cybersecurity? INE Security’s Defense Track helps you build skills in incident response, digital forensics, and threat hunting. Ready to make a move? Explore our certification pathways: 👉 bit.ly/4ss721g #Cybersecurity #CyberDefense #InfoSec
🔦 Security teams don’t need more data, they need better insight. Auditing Microsoft 365 turns noise into direction. That’s how programs mature #microsoft365 #InfoSec #CyberDefense bit.ly/4arfcQ2

#IHEDN | Le COMCYBER a reçu les auditeurs de la session souveraineté numérique et cybersécurité de l’ @IHEDN à Rennes pour leur expliquer les enjeux de la #cyberdéfense. Une journée d’échanges et de démonstrations.



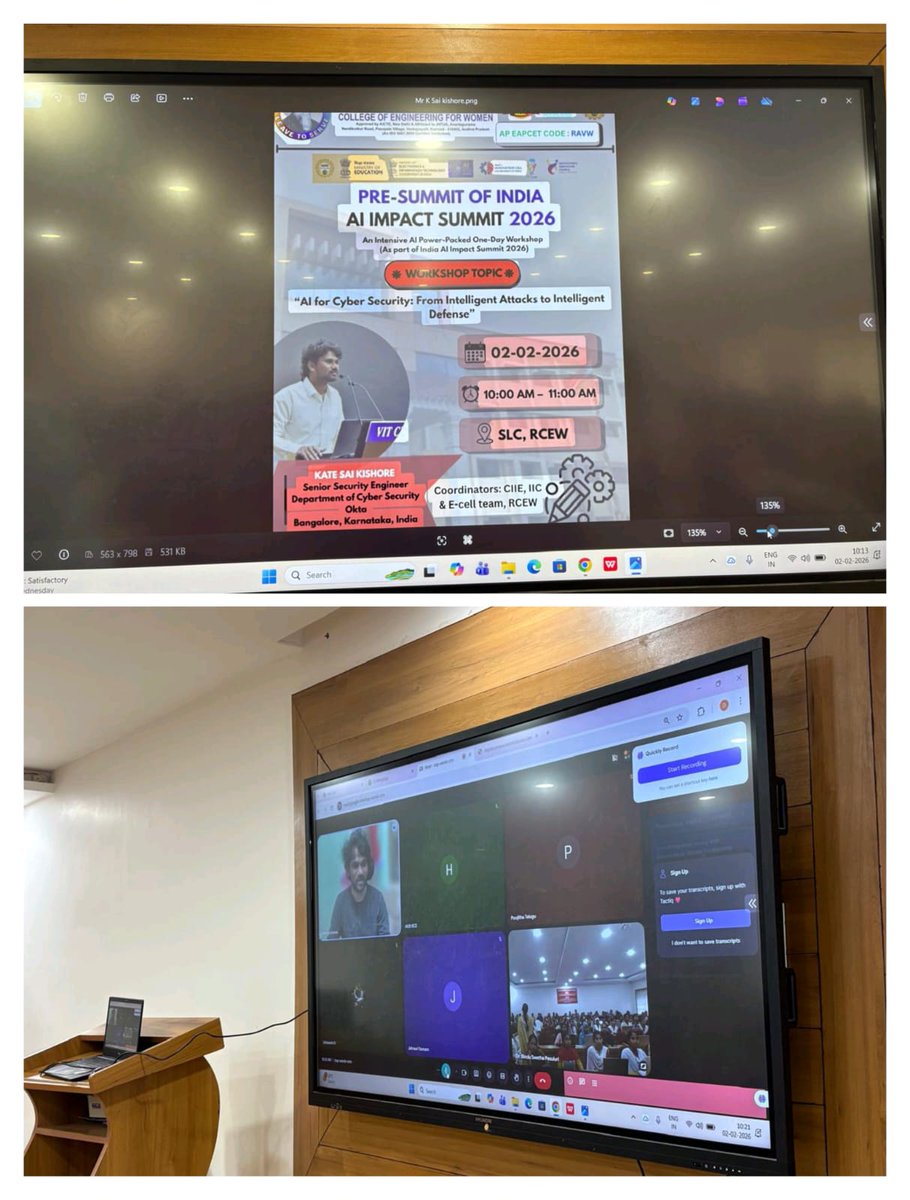
Boosting cyber defense with AI. RCEW's CIIE, E-Cell, and IIC hosted a workshop on "AI for Cyber Security" with industry expert Mr. Kate Sai Kishore. Insights on AI-driven threats & defense strategies. Beneficial for students & faculty! #RCEW #AICyberSecurity #CyberDefense


The bar is high and the @UVA @cnsatuva team plans to raise it. A powerhouse program stepping into the arena with something to prove and everything to gain. #NCCDC #CyberElite #CyberDefense #GoHoos

Pakistan strengthens its cyber shield A new Endpoint Detection & Response (EDR) system is now protecting government networks with real-time monitoring and advanced threat detection. ⚡ Cyber threats will now face stronger resistance. #CyberSecurity #PakistanTech #CyberDefense

Something went wrong.
Something went wrong.
United States Trends
- 1. #euphoria N/A
- 2. May the 4th N/A
- 3. #GoAvsGo N/A
- 4. #GoAvsGo N/A
- 5. BEST OF ME N/A
- 6. Vijay N/A
- 7. Jarrett Allen N/A
- 8. Rudy N/A
- 9. Jules N/A
- 10. #RHOA N/A
- 11. #mnwild N/A
- 12. Tamil Nadu N/A
- 13. Cale Makar N/A
- 14. Edmond N/A
- 15. Lexi N/A
- 16. West Bengal N/A
- 17. Quinn Hughes N/A
- 18. Wally N/A
- 19. MetGala 2026 with KUN N/A
- 20. Lou Ann N/A