#blueteam search results
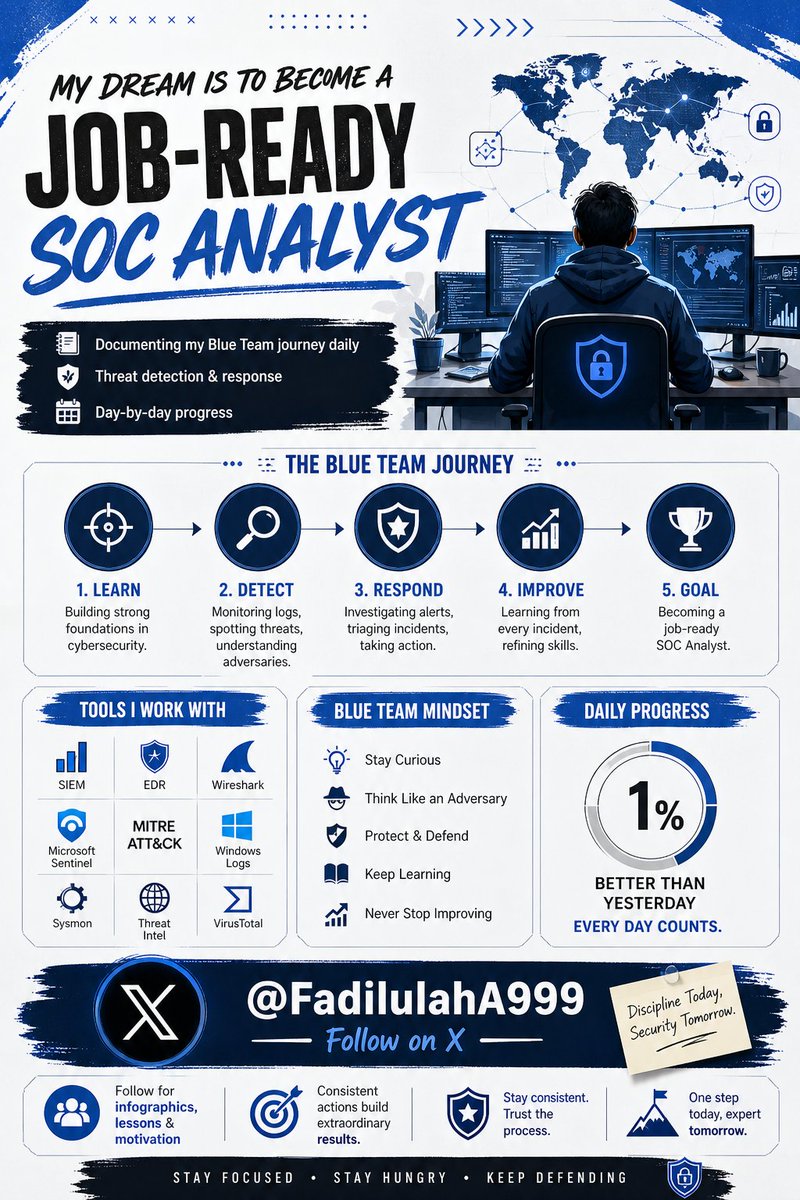
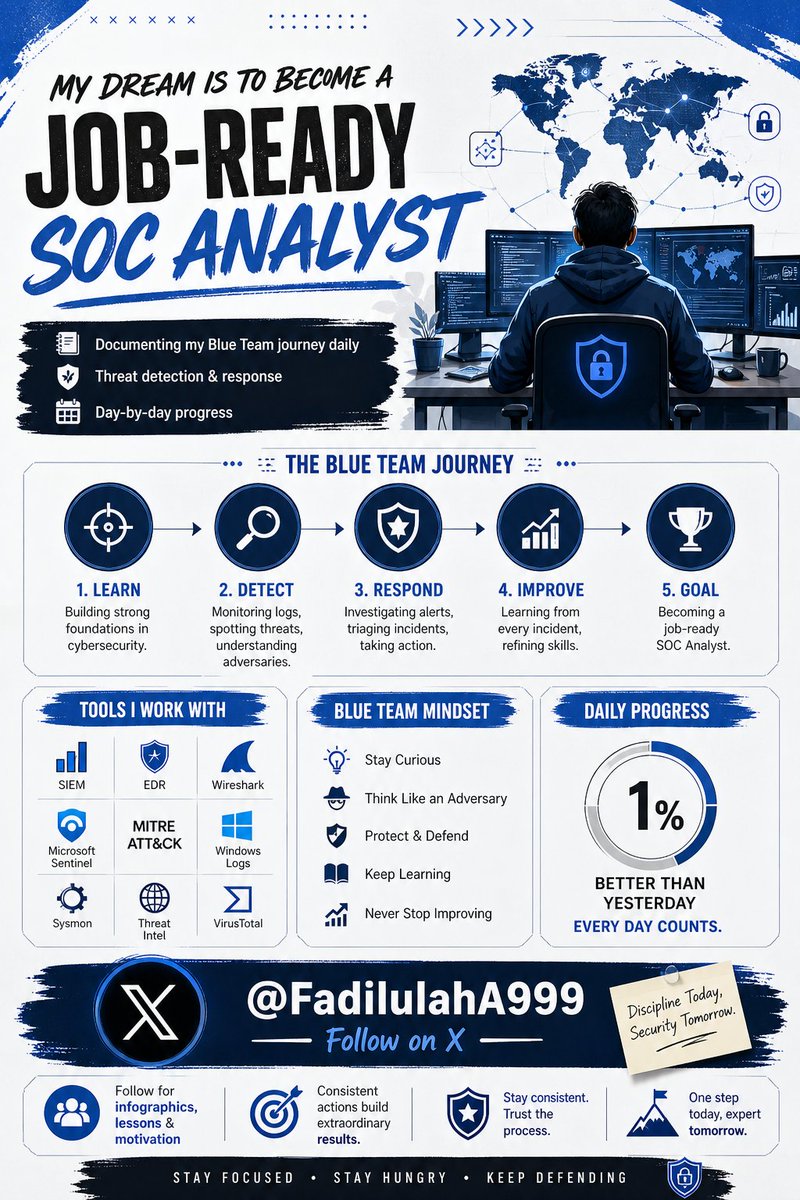
my dream is to become a job-ready SoC Analyst Documenting my Blue Team journey daily | Threat detection & response | Day-by-day progress Follow for infographics, lessons & motivation @_JohnHammond @troyhunt @tryhackme @hackthebox_eu @letsdefendio #BlueTeam #SOCAnalyst #InfoSec
Day 19 of my cyber security journey Cybersecurity seemed straightforward when I started, but reality proved far more challenging. Every obstacle is sharpening my Blue Team skills. Has anyone else had a similar experience early on? #CyberSecurity #SOC #BlueTeam

Blue Teams don’t just defend — they keep businesses alive. In a world of constant threats, proactive monitoring, rapid response, and resilience are what protect revenue, reputation, and operations 24/7. #BlueTeam #CyberSecurity #InfoSec #SOCAnalyst #CyberDefense"

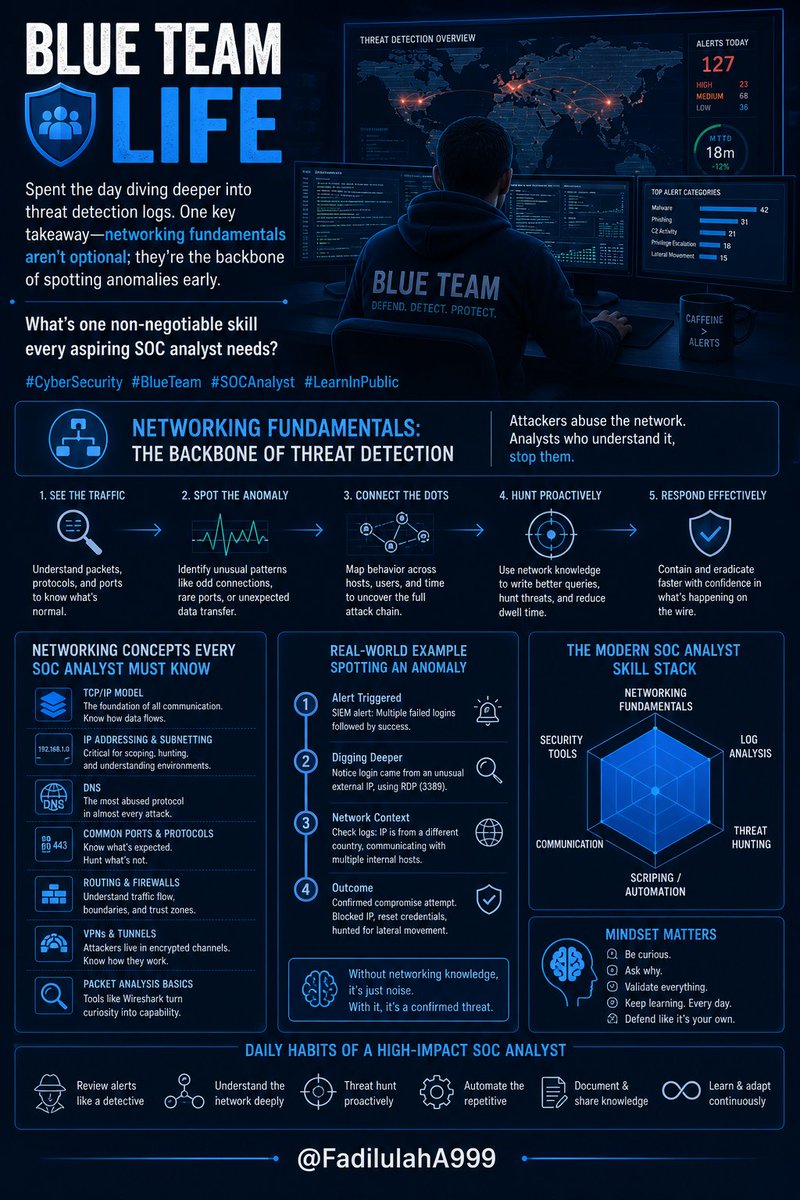
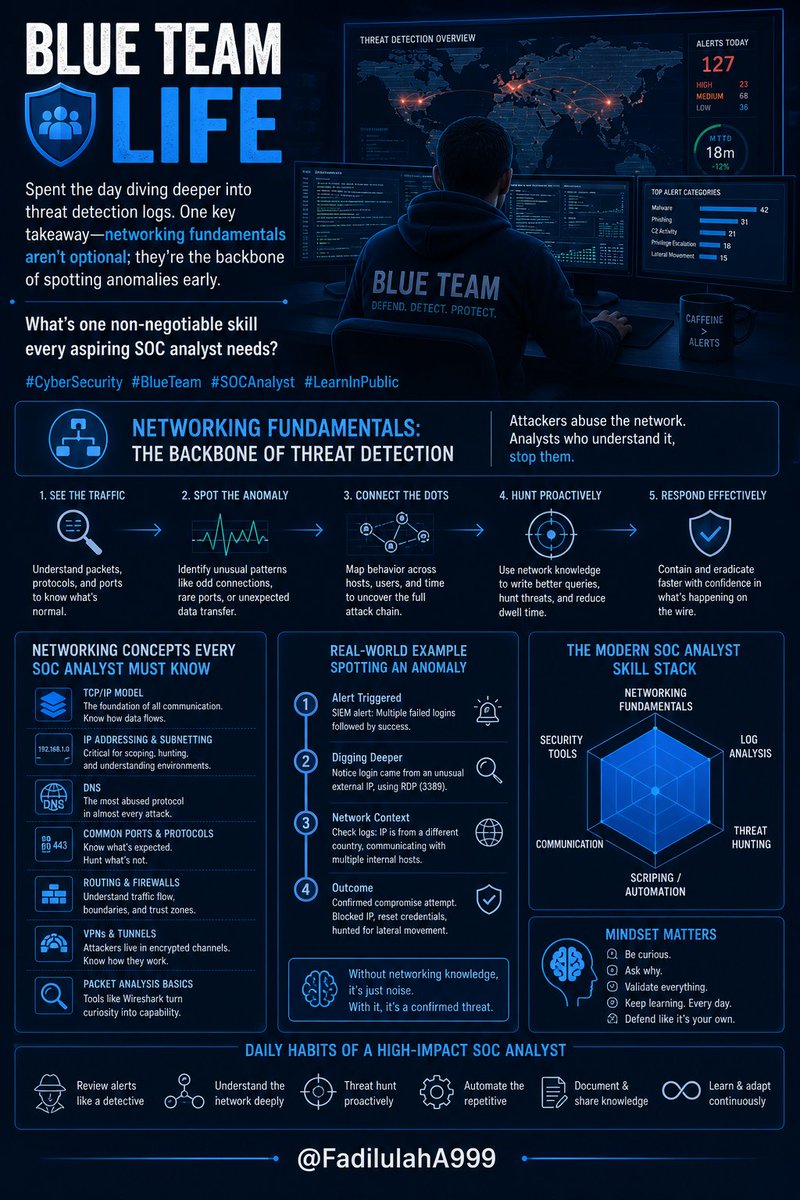
Blue team life: Spent the day diving deeper into threat detection logs. One key takeawaynetworking fundamentals aren't optional; they're the backbone of spotting anomalies early.What's one non-negotiable skill every aspiring SOC analyst needs? #CyberSecurity #BlueTeam #SOCAnalyst
APTs aren’t loud, they’re patient. I noticed in my labs how small, low-noise actions chain into long campaigns. Advanced persistent threats are stealthy, long-term intrusions. Tip: baseline normal activity to spot subtle drift. #cybersecurity #blueteam

This is a dedicated hub for #Cybersecurity knowledge. Our mission is to bridge the gap between curiosity and expertise. Not personal. Just pure learning. 💻 #Infosec, #BlueTeam, #CyberSkills, #cyber
¡Hoy se han ganado las pizzas! Muy contentos con nuestros alumnos de la formación de DFIR y Análisis Forense en Windows con @lawwait! ¡Mañana cerramos el curso con broche de oro! #CiberSeguridad #Noticia #BlueTeam

¡Un gran fin de semana de formación de forense en redes con @lawwait! Muy contentos con el inicio del plan de DFIR y Análisis forense ¡Buena pinta y sensaciones con todos nuestros alumnos! ¡Nos vemos en el siguiente curso! #Cursos #CiberSeguridad #BlueTeam #DFIR

Playbook yazarken zorlanıyoruz hocam dediler.. Overlokçu ayağınıza geldi. #XSoar #PlayBook #BlueTeam

Sevgili genç kardeşlerim, bir konuya açıklık getirelim.. "iOC değil, Davranış avlarız". ;) #blueteam
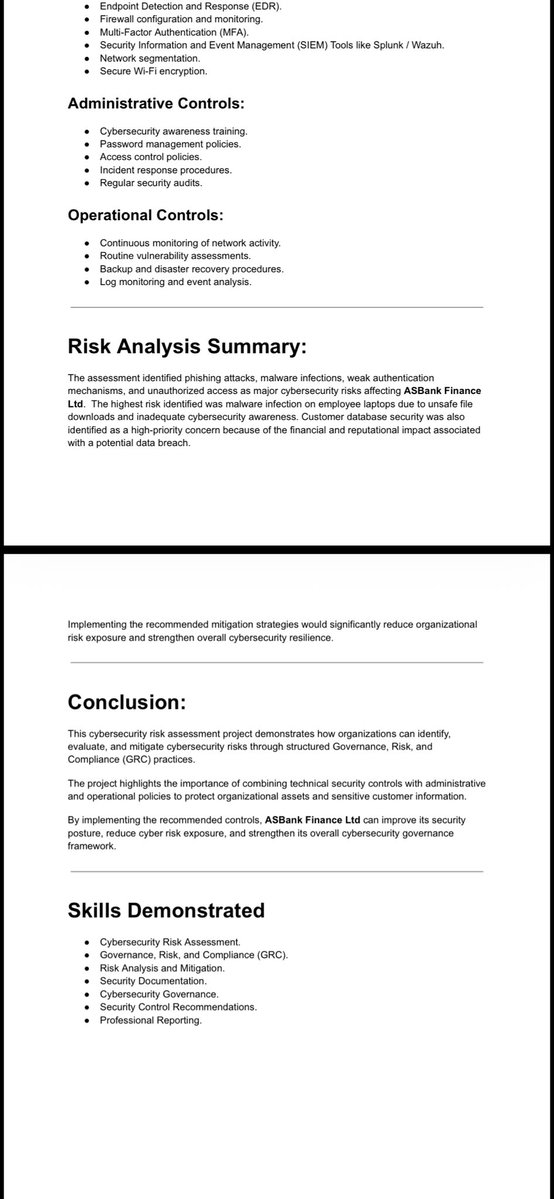
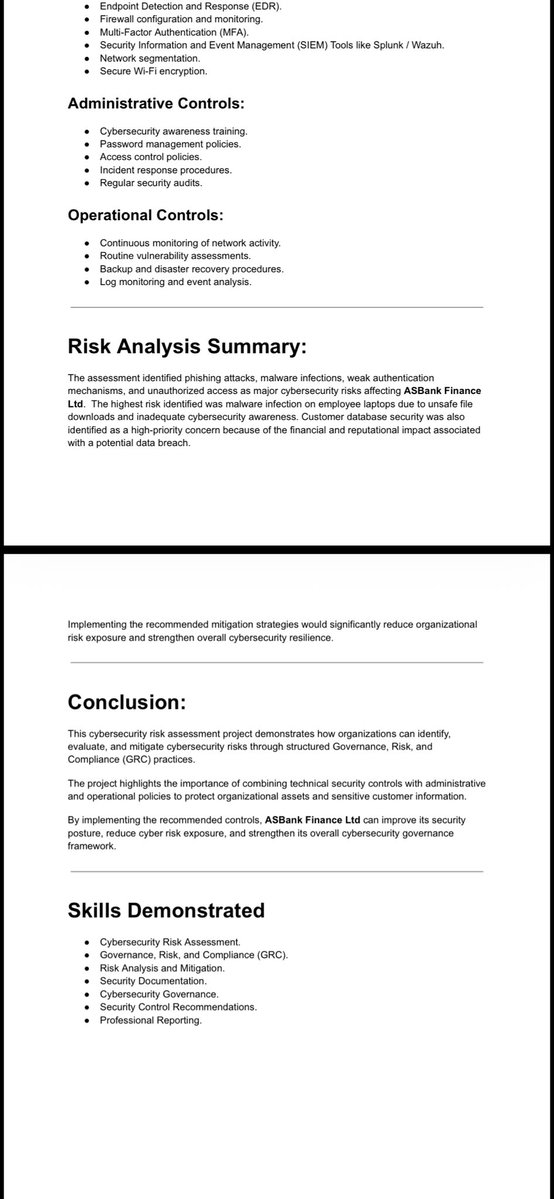
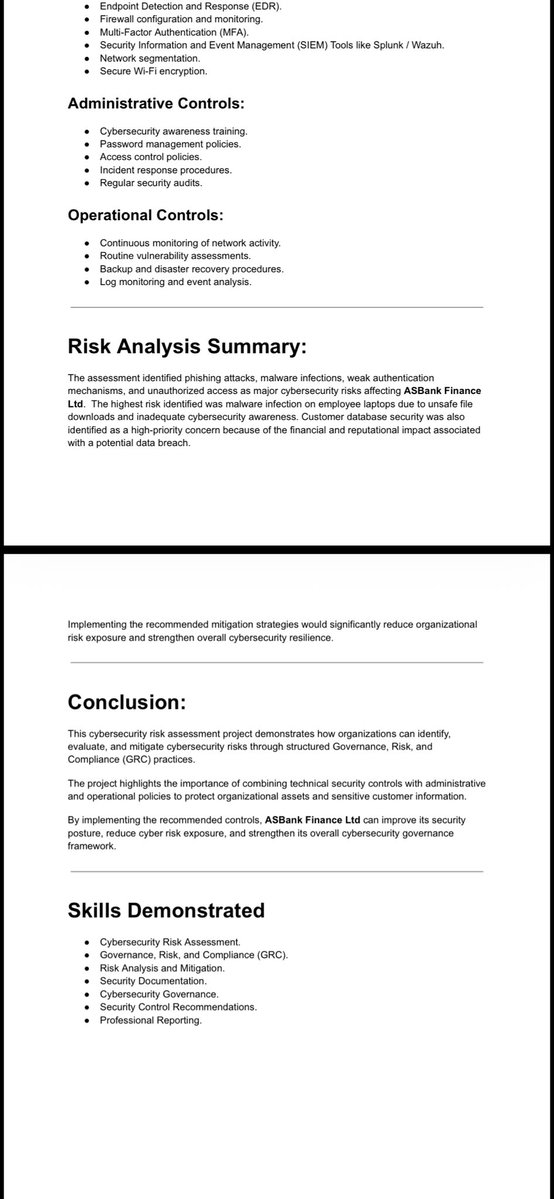
i just completed a Cybersecurity Risk Assessment project for a simulated financial organization (ASBank Financial Ltd). Where i focused on: - Risk identification - Threat & vulnerability analysis. - Risk mitigation strategies. RA is very important #Cybersecurity #GRC #BlueTeam


¡Finalizado el curso de DFIR y Análisis forense en Windows con @lawwait! ¡Gran fin de semana de aprender cositas! ¡Nos vemos en el de Linux! #CiberSeguridad #BlueTeam #Tecnología

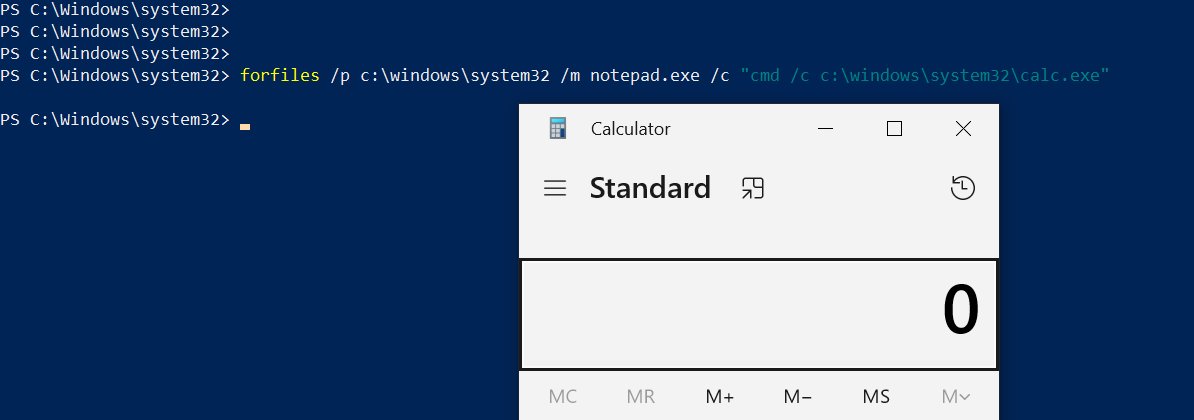
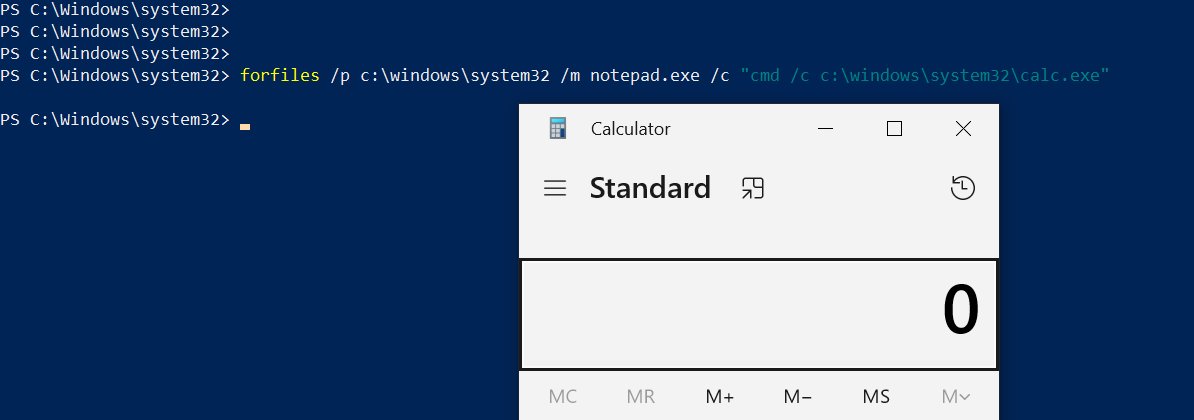
See how legitimate Windows executables can be abused for reconnaissance, data exfiltration and persistence during pentests. Useful for both red and blue teams hackers-arise.com/powershell-for… @three_cube @_aircorridor #blueteam #redteam #pentest
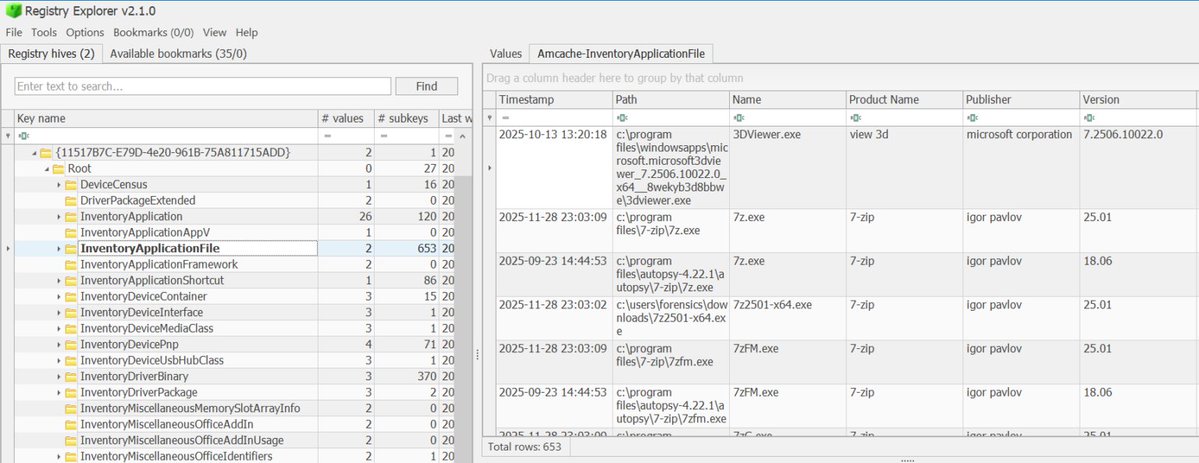
For those of you interested in digital forensics, Part 3 of our Registry Forensics series is now out. Here we cover evidence of execution hackers-arise.com/digital-forens… @three_cube @_aircorridor @DI0256 #forensics #cybersecurity #blueteam
SysWhispers4 AV/EDR evasion via direct and indirect system calls Windows NT 3.1 through Windows 11 24H2 /x64/x86/WoW64/ARM64 github.com/JoasASantos/Sy… #dfir #blueteam #redteam #pentesting
Your attacker already knows your gaps. Do you? 🛡️ @SecHubb, @secgreene, David Hoelzer & 15+ SANS experts. April 30th — a full day of real tactics, real tools, no filler. Secure Your Fortress → go.sans.org/X9vR6R #CyberDefense #BlueTeam

Your attacker already knows your gaps. Do you? 🛡️ @SecHubb, @secgreene, David Hoelzer & 15+ SANS experts. 30th April — a full day of real tactics, real tools, no filler. Secure Your Fortress → go.sans.org/X9vR6R #CyberDefence #BlueTeam
🛡️ Break in. Defend everything. Start from zero and build real defensive security skills with hands-on labs and real-world scenarios. Learn to detect, respond, and secure systems like a true blue teamer. Ready to defend? 🚀 bit.ly/47YRcDA #Cybersecurity #BlueTeam

🍯 Deployed Cowrie Honeypot for high-interaction SSH deception, analyzing live telemetry 🚧 Perimeter: pfSense zone isolation 📊 Monitoring: live logs (tail -f) 🧪 Simulation: Parrot OS exploitation 📜 Capture: shell command forensics #InfoSec #BlueTeam #ThreatHunting #CyberLab
📌 Prioridades hoy: Actualizar ya Verificar versión Reiniciar cpsrvd Si no podés parchear: bloquear 2083/2087/2095/2096 y aplicar mitigaciones Menos humo, más evidencia. Nos vemos en los logs. #BlueTeam #ThreatIntel #DrPlaga.sh
📌 Prioridades hoy: Actualizar ya Verificar versión Reiniciar cpsrvd Si no podés parchear: bloquear 2083/2087/2095/2096 y aplicar mitigaciones Menos humo, más evidencia. Nos vemos en los logs. #BlueTeam #ThreatIntel #DrPlaga.sh
DAY38-42 of becoming a soc analyst Investigation with splunk Learnt about the 5 questions to ask yourself while carrying out an investigation. Siem as a best friend as a soc analyst How siem works Soar as a best friend too and how they work #BlueTeam #SOCAnalyst #CyberDefense
DAY 37-38 of becoming a soc anslyst Cybersecurity landscape. This is teaching about,how to: Understand the cost and impact of security events. Identify some historic high profile security events. Security concepts about surrounding information assurance. #BlueTeam #SOCAnalyst
my dream is to become a job-ready SoC Analyst Documenting my Blue Team journey daily | Threat detection & response | Day-by-day progress Follow for infographics, lessons & motivation @_JohnHammond @troyhunt @tryhackme @hackthebox_eu @letsdefendio #BlueTeam #SOCAnalyst #InfoSec
Day 19 of my cyber security journey Cybersecurity seemed straightforward when I started, but reality proved far more challenging. Every obstacle is sharpening my Blue Team skills. Has anyone else had a similar experience early on? #CyberSecurity #SOC #BlueTeam

Full report with SIGMA, YARA, MITRE, and governance analysis at: inferlume.com/reports/daily/… #CTI #ThreatIntel #BlueTeam #Infosec
⌛ The SANS #CloudExchangeSummit CFP closes Friday! Working in cloud detection or defense? Share your insights — AI-driven detection, IR, identity attacks & more. 🗓 Deadline: Friday, May 8, 5 PM ET 📩 Learn More & Submit Here: go.sans.org/cse-summit-cfp #CloudSecurity #BlueTeam

APTs aren’t loud, they’re patient. I noticed in my labs how small, low-noise actions chain into long campaigns. Advanced persistent threats are stealthy, long-term intrusions. Tip: baseline normal activity to spot subtle drift. #cybersecurity #blueteam

UNISCITI ANCHE TU AL #BLUETEAM! CERCHIAMO UN IMPIEGATO/A COMMERCIALE PER LA NOSTRA FILIALE DI MANTOVA. 👉Vuoi maggiori informazioni? Chiamaci al numero 0173.445696 👉mollofratelli.com/lavorare-in-mo… GRUPPO MOLLO: INSIEME E’ TUTTA UN’ALTRA COSA!

NativeDump Minidumps using native API only to dump LSASS memory, a tool by Ricardo Ruiz (@RicardoJoseRF ) Source: github.com/ricardojoserf/… #redteam #blueteam #maldev #malwaredevelopment
Busted him at a mall no less. Great job #BlueTeam
Convicted sex offender James Matthew Carey, 43, arrested by at @HillsdaleSC in “To Catch a Predator” sting after he believed he was meeting minor for sexual purposes, per @SanMateoPD, also aided by @Flock_Safety


Most SOC teams have zero detection coverage for OAuth token abuse. The Vercel breach proved it. Here's what a mature blue team Defense looks like this exact attack pattern 🧵👇 🎥youtu.be/fkfAMDP9r1o?si… #SOCAnalyst #BlueTeam #CyberSecurity #vercel
This is a dedicated hub for #Cybersecurity knowledge. Our mission is to bridge the gap between curiosity and expertise. Not personal. Just pure learning. 💻 #Infosec, #BlueTeam, #CyberSkills, #cyber
Day 18 of my cyber security journey Understanding alert fatigue. Not every alert is a crisis — context and smart triage are everything in SOC life. Speed matters,but accuracy saves the day @SANSInstitute @MITREattack @CrowdStrike @troyhunt #CyberSecurity #SOCAnalyst #BlueTeam

i just completed a Cybersecurity Risk Assessment project for a simulated financial organization (ASBank Financial Ltd). Where i focused on: - Risk identification - Threat & vulnerability analysis. - Risk mitigation strategies. RA is very important #Cybersecurity #GRC #BlueTeam


Blue team life: Spent the day diving deeper into threat detection logs. One key takeawaynetworking fundamentals aren't optional; they're the backbone of spotting anomalies early.What's one non-negotiable skill every aspiring SOC analyst needs? #CyberSecurity #BlueTeam #SOCAnalyst
148M records exposed - not by a zero-day, but by an unpatched server sitting vulnerable for 5 months. Reverse engineering the Equifax breach kill chain + 4 Blue Team blueprints is live on @theCyberBoo 👇 youtu.be/5OPAmLjvBhA #CyberSecurity #BlueTeam #SOC #IncidentResponse

youtube.com
YouTube
CyberBoo
Blue Teams don’t just defend — they keep businesses alive. In a world of constant threats, proactive monitoring, rapid response, and resilience are what protect revenue, reputation, and operations 24/7. #BlueTeam #CyberSecurity #InfoSec #SOCAnalyst #CyberDefense"

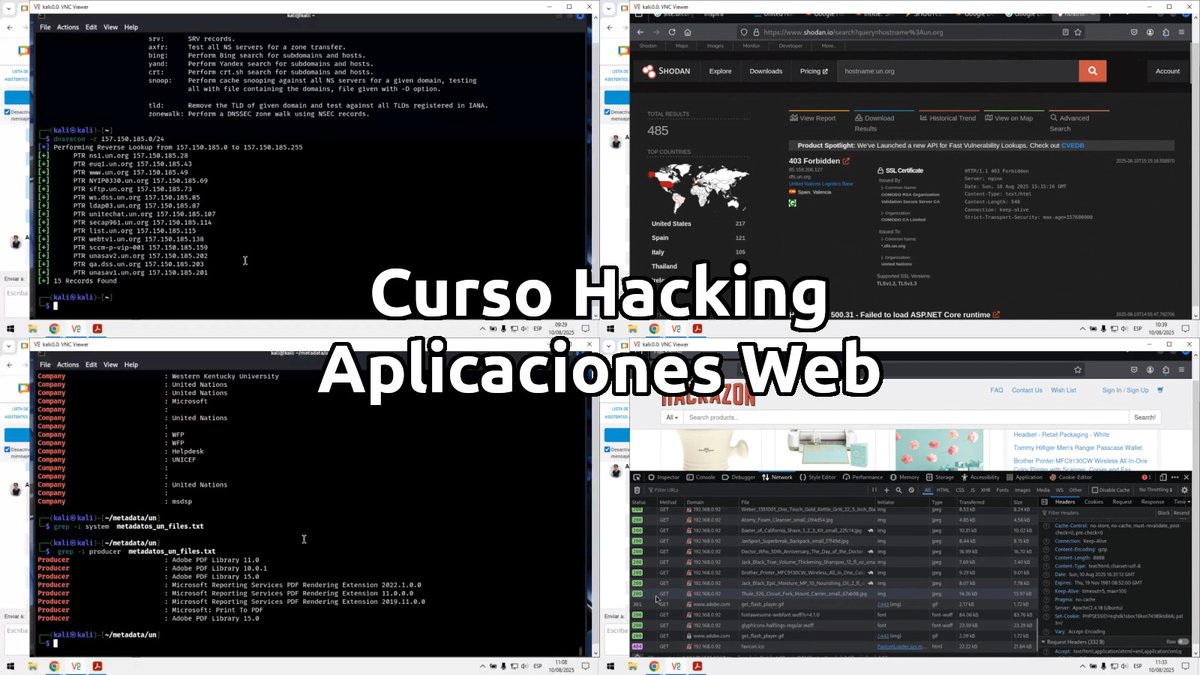
🚨 No te quedes fuera del Curso Hacking Aplicaciones Web. 📅 Domingos 5, 12, 19, y 26 de abril 2026. De 9 am a 12 pm (UTC -05:00). 📲 WhatsApp: wa.me/51949304030 🌐 reydes.com/archivos/curso… #redteam #blueteam #vulnerability #cyberattack #owasp #webhacking #websecurity
⌛ The SANS #CloudExchangeSummit CFP closes Friday! Working in cloud detection or defense? Share your insights — AI-driven detection, IR, identity attacks & more. 🗓 Deadline: Friday, May 8, 5 PM ET 📩 Learn More & Submit Here: go.sans.org/cse-summit-cfp #CloudSecurity #BlueTeam

¡Hoy se han ganado las pizzas! Muy contentos con nuestros alumnos de la formación de DFIR y Análisis Forense en Windows con @lawwait! ¡Mañana cerramos el curso con broche de oro! #CiberSeguridad #Noticia #BlueTeam

Flying Under the Radar with Powershell A new article on Living off the Land binaries has been published. Especially helpful for those just getting started hackers-arise.com/powershell-for… @three_cube @_aircorridor @DI0256 @IamSmouk #redteam #blueteam #powershell #pentesting

¡Finalizado el curso de DFIR y Análisis forense en Windows con @lawwait! ¡Gran fin de semana de aprender cositas! ¡Nos vemos en el de Linux! #CiberSeguridad #BlueTeam #Tecnología

Your attacker already knows your gaps. Do you? 🛡️ @SecHubb, @secgreene, David Hoelzer & 15+ SANS experts. April 30th — a full day of real tactics, real tools, no filler. Secure Your Fortress → go.sans.org/X9vR6R #CyberDefense #BlueTeam
🛡️ Turn logs into actionable intelligence with SEC555 Detection Engineering and SIEM Analytics! Build automated alerts, leverage data analytics, & defend against sophisticated attacks across on-premises and cloud environments. 🔗 go.sans.org/FxEfc4 #BlueTeam #ThreatDetection

¡Un gran fin de semana de formación de forense en redes con @lawwait! Muy contentos con el inicio del plan de DFIR y Análisis forense ¡Buena pinta y sensaciones con todos nuestros alumnos! ¡Nos vemos en el siguiente curso! #Cursos #CiberSeguridad #BlueTeam #DFIR

"Everything Your SOC Needs in One Platform" demo request -> [email protected] #BlueTeam #SOC #CyberSecurity #SiberGüvenlik

Playbook yazarken zorlanıyoruz hocam dediler.. Overlokçu ayağınıza geldi. #XSoar #PlayBook #BlueTeam

🚨 Ready to boost your defense skills? SEC450 SOC Analyst Training covers essential tools and techniques for SOC Analysts. Get started with a FREE one-hour course preview today! 🔐 #BlueTeam #CyberSecurityTraining #SecurityOperations #SOC go.sans.org/AKgyXT

Completed an Endpoint Defense & Memory Analysis SOC project @HSC_Consult , simulating a real-world fileless attack. Identified process injection (process hollowing) through correlation of process tree, network activity, and memory artifacts. #Cybersecurity #BlueTeam #Learning



See how legitimate Windows executables can be abused for reconnaissance, data exfiltration and persistence during pentests. Useful for both red and blue teams hackers-arise.com/powershell-for… @three_cube @_aircorridor #blueteam #redteam #pentest
Attackers don't wait for you to figure it out. Neither should your training. 50% off eSOC certification until March 30 — code eSOCCert326 👉 bit.ly/4rWCILv Log Analysis • Threat Detection • Incident Response #CyberSecurity #SOC #BlueTeam

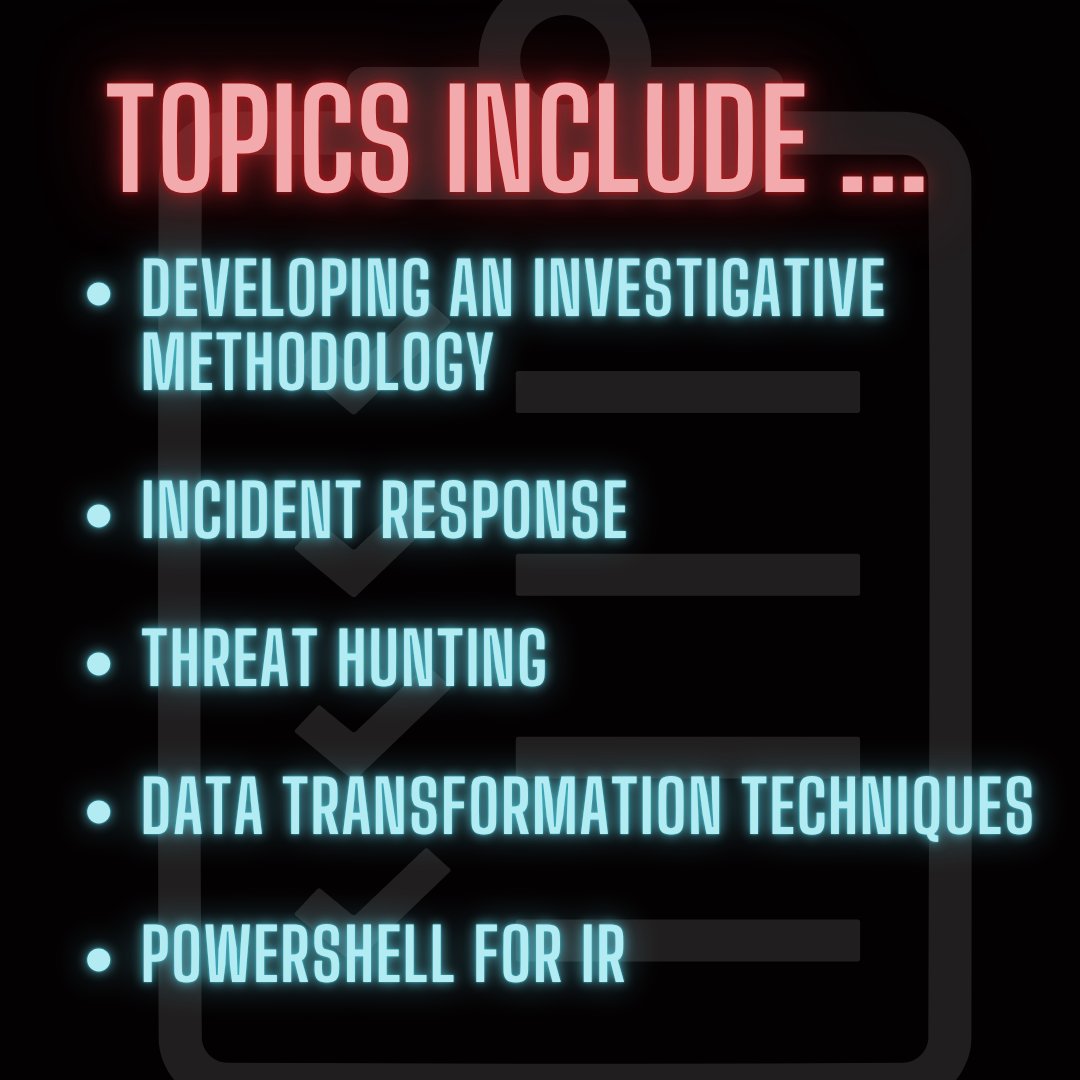
Our latest #blueteam course, SOC 201, dropped to much anticipation last year - and the reviews from the community have been amazing so far! This intermediate-level course focuses on threat hunting and incident response. It also has a corresponding cert: the PSAP (Practical SOC


i just completed a Cybersecurity Risk Assessment project for a simulated financial organization (ASBank Financial Ltd). Where i focused on: - Risk identification - Threat & vulnerability analysis. - Risk mitigation strategies. RA is very important #Cybersecurity #GRC #BlueTeam


IoT devices used in smart cities (smart lighting, parking sensors, flood monitoring systems, etc.) have their own vulnerabilities Learn more: hackers-arise.com/iot-hacking-ge… @three_cube @_aircorridor @DI0256 #iot #redteam #blueteam #ThreatHunting

Something went wrong.
Something went wrong.
United States Trends
- 1. Wemby N/A
- 2. Spurs N/A
- 3. Spurs N/A
- 4. #MetGala N/A
- 5. Mike Conley N/A
- 6. Anthony Edwards N/A
- 7. #WWERaw N/A
- 8. Mitch Johnson N/A
- 9. Julius Randle N/A
- 10. Knicks N/A
- 11. Lacombe N/A
- 12. Michael Conforto N/A
- 13. Keldon Johnson N/A
- 14. Pagan N/A
- 15. Victor Wembanyama N/A
- 16. Castle N/A
- 17. Champagnie N/A
- 18. De'Aaron Fox N/A
- 19. Dylan Harper N/A
- 20. #bucciovertimechallenge N/A