#danabot search results
Cybercriminals are becoming increasingly sophisticated in their tactics, employing deceptive job application emails as a new vector to distribute the dangerous #DanaBot #malware. Attackers use Word documents with external links to bypass security measures securityonline.info/danabot-malwar…
DanaBot's "DanaBleed" memory leak, active for 3 years, exposed C2 server data, aiding law enforcement in Operation Endgame takedown. #DanaBot #DanaBleed #Cybercrime #Malware #InfoSec securityonline.info/danableed-flaw…
#ThreatProtection Malicious Word Document Dropping #DanaBot #Malware. Read more: broadcom.com/20240515-malic… #CyberSecurity
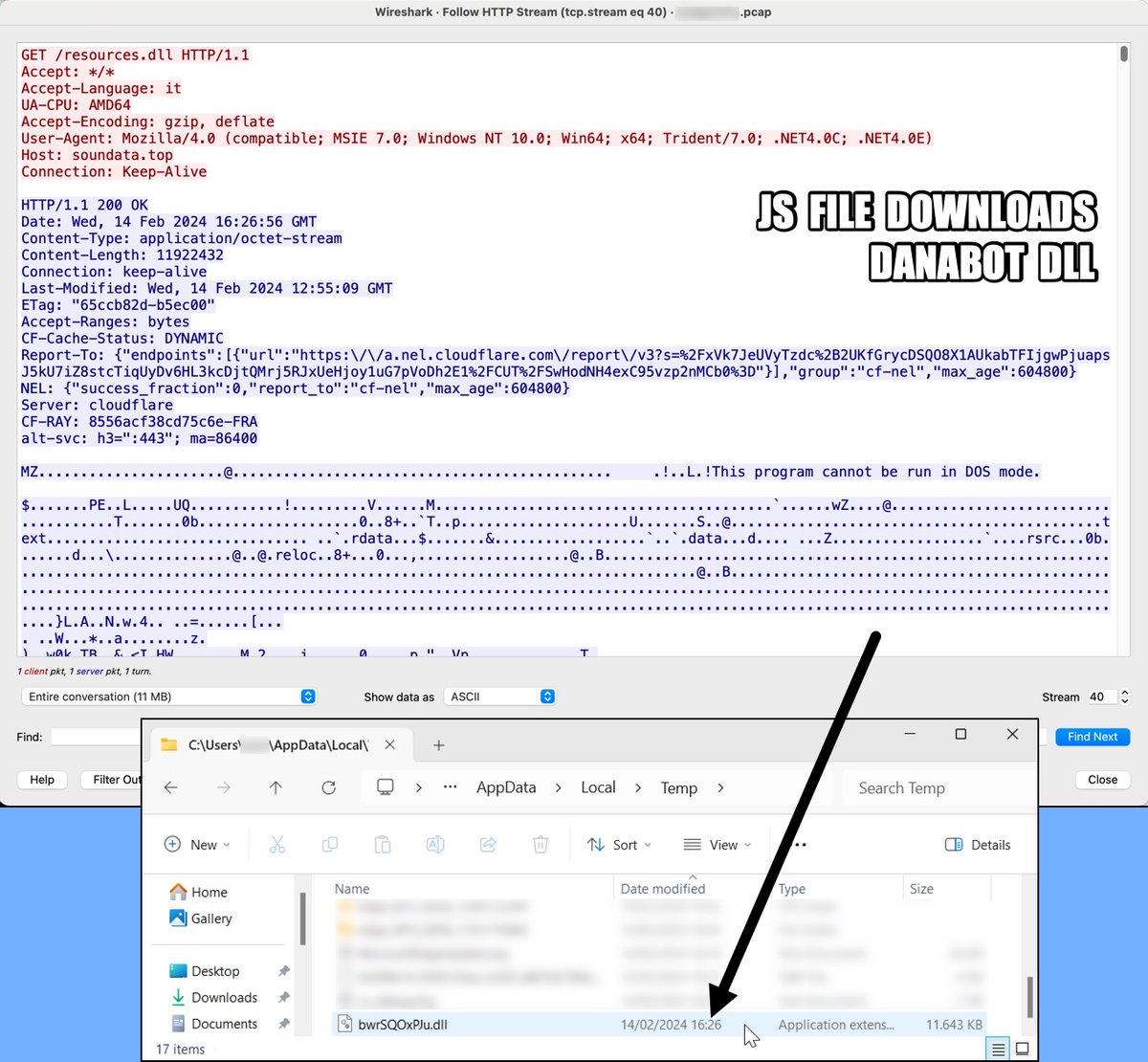
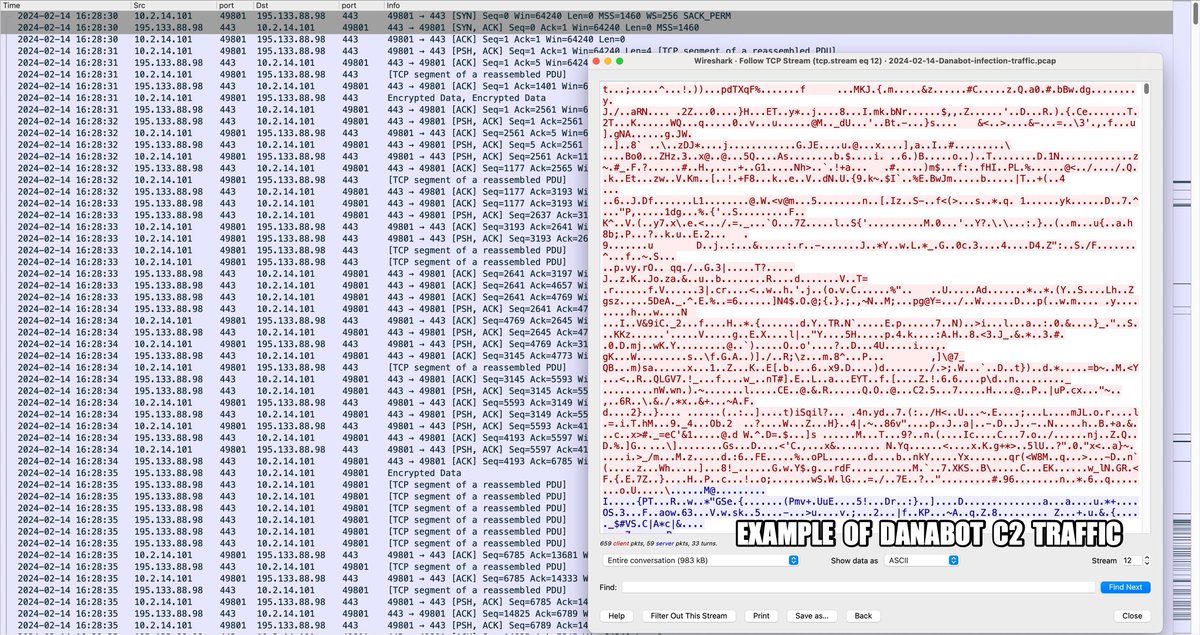
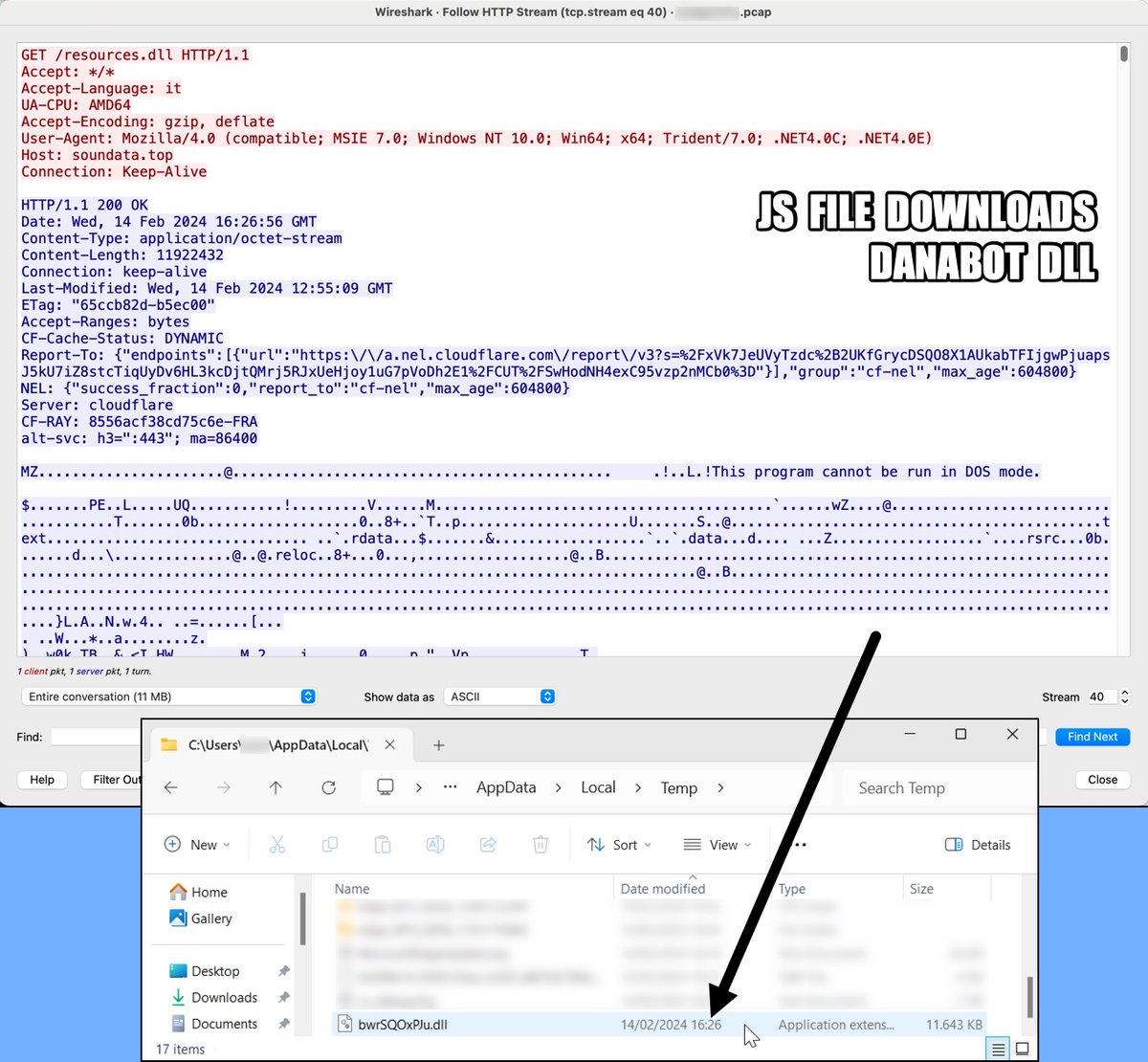
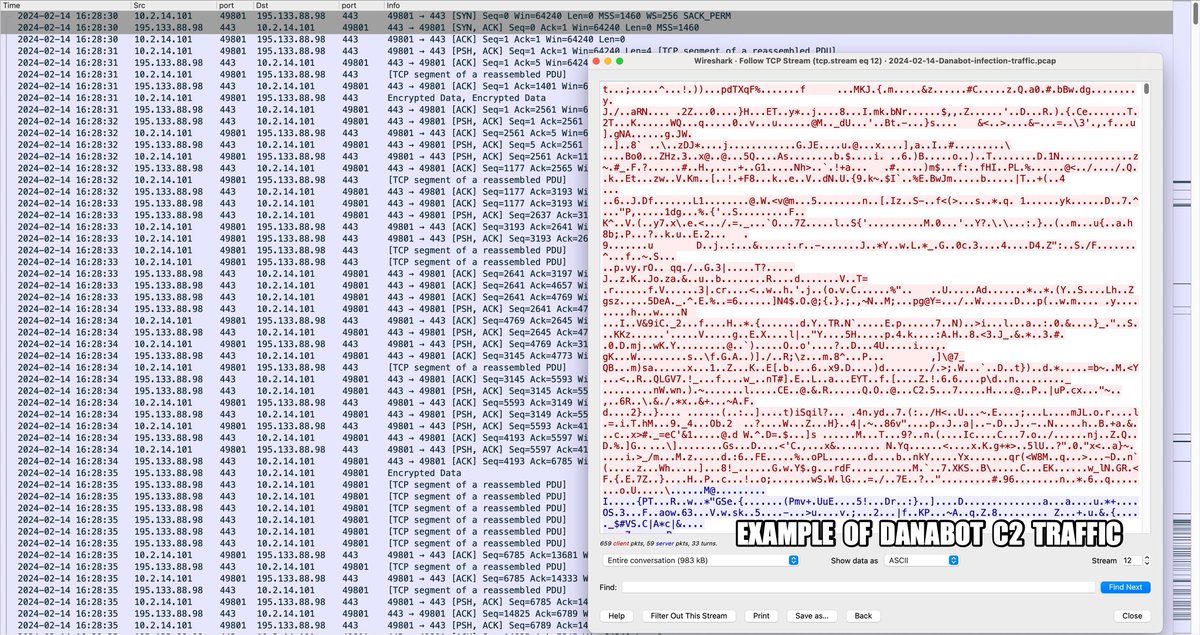
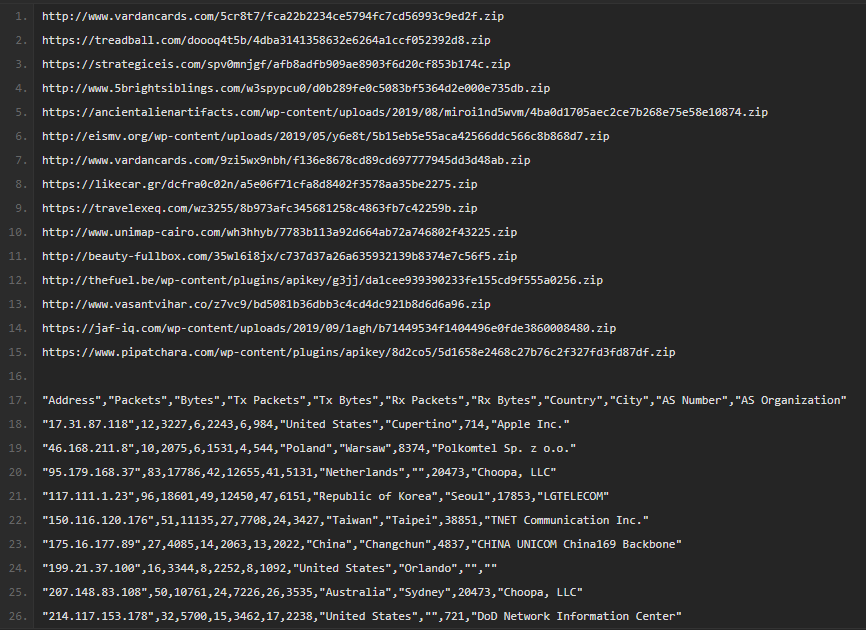
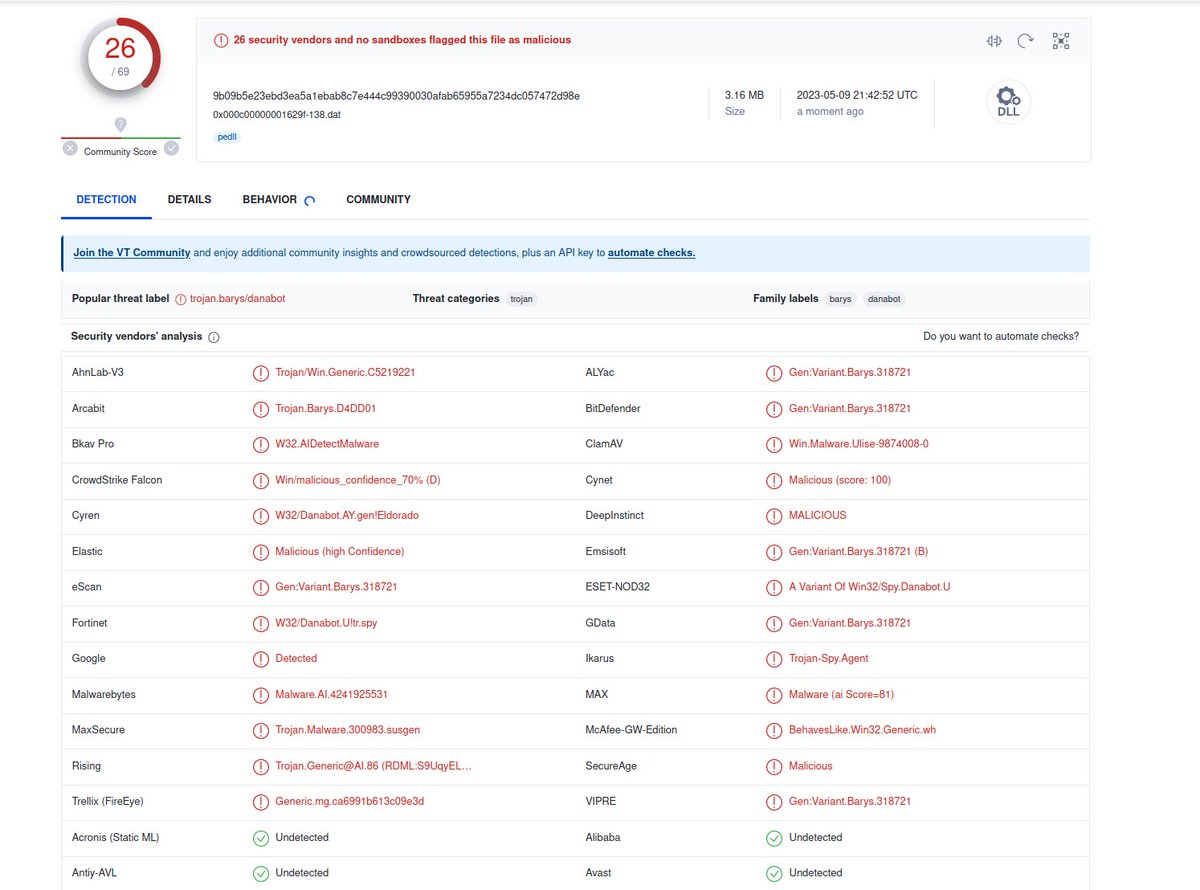
2024-02-14 (Wednesday): #Danabot from Italian-language #malspam List of IoCs available at bit.ly/49xx4qk #Unit42ThreatIntel #TimelyThreatIntel #IndicatorsOfCompromise #InfectionTraffic #Wireshark #C2Traffic


2023-08-03 (Thursday): Malicious Google ad led to a fake TurboTax page pushing an installer package that led to #DanaBot. List of indicators available at bit.ly/3qfbEgL




#ThreatProtection New #Danabot #malware variant found in the wild, read more about Symantec's protection: broadcom.com/support/securi…
In May 2025, #ESET participated in operations that largely disrupted the infrastructure of two notorious infostealers: #LummaStealer and #Danabot. 1/6
DanaBot Malware Resurfaces With New Variant After Operation Endgame Disruption cysecurity.news/2025/11/danabo… #CyberAttacks #CyberCrime #DanaBot

DanaBot Malware Network Disrupted After Researchers Discover Key Flaw cysecurity.news/2025/06/danabo… #cryptocurrency #DanaBot #DDOSAttacks

#AgenziaEntrate #Danabot Samples bazaar.abuse.ch/browse/tag/83-… AnyRun app.any.run/tasks/70fe0874… 📛83.147.53.]197 📛104.194.148.]11
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQS2T2WIAAdJCd.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTAEoWcAALhfD.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTDfmWsAE0LG_.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTMN0WkAAzqgP.jpg)
🇮🇹 Nuova campagna #DanaBot a tema #AgenziaEntrate ⚔️ TTP: come precedente campagna del 18/06/2024 ➡️ Questa volta il codice HTML iniziale NON riporta più gli insulti in lingua italiana qualora l'IP sia censito in blocklist. 💣#IoC 👇 🔗t.me/certagid/682
16 Defendants Federally Charged in Connection with DanaBot Malware Scheme That Infected Computers Worldwide On May 22, 2025, the US Department of Justice announced federal charges against 16 individuals for their roles in developing and deploying the #DanaBot #malware, a
H/T @malwrhunterteam IP 91.92.242.]111 Some Samples bazaar.abuse.ch/browse/tag/91-… AnyRun #DanaBot app.any.run/tasks/503aecb4… C2 :443 176.117.68.]38 91.92.242.]111 45.80.158.]189 176.117.68.]39
![JAMESWT_WT's tweet image. H/T @malwrhunterteam
IP 91.92.242.]111
Some Samples
bazaar.abuse.ch/browse/tag/91-…
AnyRun #DanaBot
app.any.run/tasks/503aecb4…
C2 :443
176.117.68.]38
91.92.242.]111
45.80.158.]189
176.117.68.]39](https://pbs.twimg.com/media/GVi-LXDWoAATZjM.jpg)
![JAMESWT_WT's tweet image. H/T @malwrhunterteam
IP 91.92.242.]111
Some Samples
bazaar.abuse.ch/browse/tag/91-…
AnyRun #DanaBot
app.any.run/tasks/503aecb4…
C2 :443
176.117.68.]38
91.92.242.]111
45.80.158.]189
176.117.68.]39](https://pbs.twimg.com/media/GVi-L4kWIAAj-87.jpg)
#ThreatProtection #Malspam Campaign Delivering #DanaBot. Read more: broadcom.com/support/securi…
🔥 Operation Endgame is BACK! This time targeting #BumbleBee, #Latrodectus, #DanaBot, #WarmCookie, #Qakbot and #Trickbot! Once again this is a HUGE win, with a truly international effort! 💪 As with phase one of #OperationEndgame, Spamhaus are providing remediation support -
💥 Ransomware kill chain broken – Operation Endgame strikes again 🔸 300 servers taken down 🔸 650 domains neutralised 🔸 €3.5M crypto seized 🔸 20 international arrest warrants Europol & partners deliver another blow to global cybercrime. More ⤵️ europol.europa.eu/media-press/ne…

In 2022, a memory leak called DanaBleed exposed sensitive data in DanaBot’s C2 servers until dismantled in 2025 during Operation Endgame. DanaBot, active since 2018, facilitates banking fraud and credential theft. 💻 #DanaBot #CyberLeak #UK ift.tt/wHY0Lqz
hendryadrian.com
DanaBleed: DanaBot C2 Server Memory Leak Bug
DanaBot is a Malware-as-a-Service platform active since 2018, known for operating under an affiliate model facilitating banking fraud and credential theft. A memory leak vulnerability named DanaBleed...
Seeing lots of malicious Google ads being served to people trying to find their 401k. I suspect it's #Danabot being served from the domain usdepttreasury[.]org. Today the stage 2 downloader is various subdomains fo jacksoninternationalairport[.]org.
300 000 PC infectés, un réseau mondial… et une erreur de débutant : les hackers de #DanaBot ont laissé une porte ouverte. Résultat : la justice a tout récupéré. Même les cybercriminels devraient penser à faire un audit de sécurité 😅 v/@01net ow.ly/bRvA30sNjgm

"Comunicazione Importante dall'Agenzia delle Entrate" spam email spread #DanaBot Urls redirect > content.servepics.[com/login.php portfolio.serveirc.[com/login.php >JS > dll http://soundata.]top/resources.dll Samples bazaar.abuse.ch/browse/tag/age… AnyRun app.any.run/tasks/a059217b…
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST3qVW0AAlPPB.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST4Y-W4AA0Xuu.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST5PxXUAAZIk8.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGSV5xLWMAA-j_y.jpg)
🚨 Threat Check 3/5: #Infostealer im Visier ESET & Behörden schlagen zurück:📉 #LummaStealer (-21 %) & #Danabot (-52 %) stark getroffen. Hotspots: 🇺🇸 USA (44 %), 🇵🇱 Polen (29 %) 🔗 Mehr im ESET #ThreatReport: welivesecurity.com/de/eset-resear… #ESET #CyberSecurity #ProgressProtected

ESET Experts often collaborate with external parties and joined global law enforcement agencies to disrupt #LummaStealer, which had grown 21% in early 2025, and #Danabot, which surged 52% with attacks hitting the US (44%) and Poland (29%).

In May 2025, #ESET participated in operations that largely disrupted the infrastructure of two notorious infostealers: #LummaStealer and #Danabot. 1/6
DanaBot Malware Enables Data Breaches and Russian Espionage cysecurity.news/2025/06/danabo… #CrowdStrikeoutage #DanaBot #DataBreaches

fascinating story in the latest @hackedpodcast about the #danabot operation - how an infection with their own malware exposed the malware creators 👏 justice.gov/usao-cdca/pr/1…
DanaBot Malware Network Disrupted After Researchers Discover Key Flaw cysecurity.news/2025/06/danabo… #cryptocurrency #DanaBot #DDOSAttacks

300 000 PC infectés, un réseau mondial… et une erreur de débutant : les hackers de #DanaBot ont laissé une porte ouverte. Résultat : la justice a tout récupéré. Même les cybercriminels devraient penser à faire un audit de sécurité 😅 v/@01net ow.ly/1qgW30sNjiA

300 000 PC infectés, un réseau mondial… et une erreur de débutant : les hackers de #DanaBot ont laissé une porte ouverte. Résultat : la justice a tout récupéré. Même les cybercriminels devraient penser à faire un audit de sécurité 😅 v/@01net ow.ly/Fpj530sNjh0

300 000 PC infectés, un réseau mondial… et une erreur de débutant : les hackers de #DanaBot ont laissé une porte ouverte. Résultat : la justice a tout récupéré. Même les cybercriminels devraient penser à faire un audit de sécurité 😅 v/@01net ow.ly/bRvA30sNjgm

The U.S. DoJ announced criminal charges against 16 individuals law enforcement authorities have linked to #DanaBot, a #malware operation first identified and named by Proofpoint @threatinsight in May 2018. Read on in @ArsTechnica: brnw.ch/21wTme0
#DanaBot, a malware that a Russia-based #cybercrime organization controlled and deployed, infecting more than 300,000 victim computers around the world, has been disrupted. Read this @Proofpoint blog for the details. bit.ly/446lD86
A simple coding error led to the takedown of DanaBot a major malware-as-a-service platform active from 2018 to 2025. Researchers quietly monitored the operation for 3+ years after discovering a critical memory leak in its C2 protocol. #CyberSecurity #DanaBot

#DanaBot #malware operators exposed via C2 #bug added in 2022 scyscan.com/news/danabot-m…
Oops! 😬 A coding blunder in a June 2022 update of the DanaBot malware actually helped law enforcement take down the whole operation! Read about the C2 bug that exposed the bad guys: [URL] #DanaBot #Malware #Cybersecurity #LawEnforcement #BugHunt bleepingcomputer.com/news/security/…
DanaBot's "DanaBleed" memory leak, active for 3 years, exposed C2 server data, aiding law enforcement in Operation Endgame takedown. #DanaBot #DanaBleed #Cybercrime #Malware #InfoSec securityonline.info/danableed-flaw…
In 2022, a memory leak called DanaBleed exposed sensitive data in DanaBot’s C2 servers until dismantled in 2025 during Operation Endgame. DanaBot, active since 2018, facilitates banking fraud and credential theft. 💻 #DanaBot #CyberLeak #UK ift.tt/wHY0Lqz
hendryadrian.com
DanaBleed: DanaBot C2 Server Memory Leak Bug
DanaBot is a Malware-as-a-Service platform active since 2018, known for operating under an affiliate model facilitating banking fraud and credential theft. A memory leak vulnerability named DanaBleed...
U.S. authorities have charged 16 defendants in a massive global operation to disrupt the Russia-based #cybercrime group behind the #DanaBot malware. @CyberSecDive spoke with Selena Larson of @Proofpoint to learn more details. Read her commentary here. bit.ly/43EDXVk
U.S. authorities have charged 16 defendants in a massive global operation to disrupt the Russia-based #cybercrime group behind the #DanaBot malware. @CyberSecDive spoke with Selena Larson of @Proofpoint to learn more details. Read her commentary here. bit.ly/4dPs97t
U.S. authorities have charged 16 defendants in a massive global operation to disrupt the Russia-based #cybercrime group behind the #DanaBot malware. @CyberSecDive spoke with Selena Larson of @Proofpoint to learn more details. Read her commentary here. bit.ly/44VcUHK
#DanaBot, "a juggernaut of the e-crime landscape” according to threat research expert at Proofpoint Selena Larson, has been disrupted by law enforcement. This @WIRED article highlights the impact of the takedown. bit.ly/4jpNy8i
#AgenziaEntrate #Danabot Samples bazaar.abuse.ch/browse/tag/83-… AnyRun app.any.run/tasks/70fe0874… 📛83.147.53.]197 📛104.194.148.]11
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQS2T2WIAAdJCd.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTAEoWcAALhfD.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTDfmWsAE0LG_.jpg)
![JAMESWT_WT's tweet image. #AgenziaEntrate #Danabot
Samples
bazaar.abuse.ch/browse/tag/83-…
AnyRun
app.any.run/tasks/70fe0874…
📛83.147.53.]197
📛104.194.148.]11](https://pbs.twimg.com/media/GTQTMN0WkAAzqgP.jpg)
🇮🇹 Nuova campagna #DanaBot a tema #AgenziaEntrate ⚔️ TTP: come precedente campagna del 18/06/2024 ➡️ Questa volta il codice HTML iniziale NON riporta più gli insulti in lingua italiana qualora l'IP sia censito in blocklist. 💣#IoC 👇 🔗t.me/certagid/682
H/T @malwrhunterteam IP 91.92.242.]111 Some Samples bazaar.abuse.ch/browse/tag/91-… AnyRun #DanaBot app.any.run/tasks/503aecb4… C2 :443 176.117.68.]38 91.92.242.]111 45.80.158.]189 176.117.68.]39
![JAMESWT_WT's tweet image. H/T @malwrhunterteam
IP 91.92.242.]111
Some Samples
bazaar.abuse.ch/browse/tag/91-…
AnyRun #DanaBot
app.any.run/tasks/503aecb4…
C2 :443
176.117.68.]38
91.92.242.]111
45.80.158.]189
176.117.68.]39](https://pbs.twimg.com/media/GVi-LXDWoAATZjM.jpg)
![JAMESWT_WT's tweet image. H/T @malwrhunterteam
IP 91.92.242.]111
Some Samples
bazaar.abuse.ch/browse/tag/91-…
AnyRun #DanaBot
app.any.run/tasks/503aecb4…
C2 :443
176.117.68.]38
91.92.242.]111
45.80.158.]189
176.117.68.]39](https://pbs.twimg.com/media/GVi-L4kWIAAj-87.jpg)
"A few questions" #booking #danabot 👇 ⛔️feedbackinnguest999214[.world 👇 ⛔️31.177.110.]99/ 👇 verification.hta.mp4 antibot.hta.mp4 AWLYURLX.exe ⛔️88.151.192[.8 ⛔️178.253.55[.80 👉Samples bazaar.abuse.ch/browse/tag/boo… 👉Urls urlhaus.abuse.ch/browse/tag/boo… 👉AnyRun app.any.run/tasks/3ae8fa99…
![JAMESWT_WT's tweet image. "A few questions"
#booking #danabot
👇
⛔️feedbackinnguest999214[.world
👇
⛔️31.177.110.]99/
👇
verification.hta.mp4
antibot.hta.mp4
AWLYURLX.exe
⛔️88.151.192[.8
⛔️178.253.55[.80
👉Samples
bazaar.abuse.ch/browse/tag/boo…
👉Urls
urlhaus.abuse.ch/browse/tag/boo…
👉AnyRun
app.any.run/tasks/3ae8fa99…](https://pbs.twimg.com/media/Ghv1pxXWQAAjhGD.jpg)
![JAMESWT_WT's tweet image. "A few questions"
#booking #danabot
👇
⛔️feedbackinnguest999214[.world
👇
⛔️31.177.110.]99/
👇
verification.hta.mp4
antibot.hta.mp4
AWLYURLX.exe
⛔️88.151.192[.8
⛔️178.253.55[.80
👉Samples
bazaar.abuse.ch/browse/tag/boo…
👉Urls
urlhaus.abuse.ch/browse/tag/boo…
👉AnyRun
app.any.run/tasks/3ae8fa99…](https://pbs.twimg.com/media/Ghv1razWMAABnEt.jpg)
![JAMESWT_WT's tweet image. "A few questions"
#booking #danabot
👇
⛔️feedbackinnguest999214[.world
👇
⛔️31.177.110.]99/
👇
verification.hta.mp4
antibot.hta.mp4
AWLYURLX.exe
⛔️88.151.192[.8
⛔️178.253.55[.80
👉Samples
bazaar.abuse.ch/browse/tag/boo…
👉Urls
urlhaus.abuse.ch/browse/tag/boo…
👉AnyRun
app.any.run/tasks/3ae8fa99…](https://pbs.twimg.com/media/Ghv4YFGXsAArjp0.jpg)
ICYMI: #DanaBot: Coming to a malspam campaign near you This Malware-as-a-Service (MaaS) offering is gaining traction as a flexible platform to launch everything from bank fraud to DDos attacks. Learn more in this week's #ThreatThursday: bddy.me/3HBEE6h
An interesting #danabot sample found by @malwrhunterteam c2 is https://frezyderm-orders[.]gr/sites/all/notused/not/ponto.php traffic is interesting...note the PLUG1M hash 4dd8d8778c7fb45a189a5759771c08c37de1fa4fb722f265c4d78e3c826610e7 on @mal_share
![James_inthe_box's tweet image. An interesting #danabot sample found by @malwrhunterteam
c2 is https://frezyderm-orders[.]gr/sites/all/notused/not/ponto.php
traffic is interesting...note the PLUG1M
hash 4dd8d8778c7fb45a189a5759771c08c37de1fa4fb722f265c4d78e3c826610e7 on @mal_share](https://pbs.twimg.com/media/D5KzcOZUEAAFIZI.png)
"Has this problem been addressed?" #booking spam email spread #ClickFix #DanaBot ✅Samples bazaar.abuse.ch/browse/tag/pnp… ❇️AnyRun app.any.run/tasks/eed5f44b… ⛔️Urls reportguest4895921[.world/ gitlab.[com/pnp30/svn/-/raw/main/ deploy. md deps .zip




#DanaBot: Coming to a malspam campaign near you This Malware-as-a-Service (MaaS) offering is gaining traction as a flexible platform to launch everything from bank fraud to DDos attacks. Learn more in this week's #ThreatThursday: bddy.me/3FxR2SV
DanaBot Malware Resurfaces With New Variant After Operation Endgame Disruption cysecurity.news/2025/11/danabo… #CyberAttacks #CyberCrime #DanaBot

"Comunicazione Importante dall'Agenzia delle Entrate" spam email spread #DanaBot Urls redirect > content.servepics.[com/login.php portfolio.serveirc.[com/login.php >JS > dll http://soundata.]top/resources.dll Samples bazaar.abuse.ch/browse/tag/age… AnyRun app.any.run/tasks/a059217b…
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST3qVW0AAlPPB.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST4Y-W4AA0Xuu.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGST5PxXUAAZIk8.jpg)
![JAMESWT_WT's tweet image. "Comunicazione Importante dall'Agenzia delle Entrate"
spam email spread #DanaBot
Urls redirect >
content.servepics.[com/login.php
portfolio.serveirc.[com/login.php
>JS
> dll http://soundata.]top/resources.dll
Samples
bazaar.abuse.ch/browse/tag/age…
AnyRun
app.any.run/tasks/a059217b…](https://pbs.twimg.com/media/GGSV5xLWMAA-j_y.jpg)
2023-08-03 (Thursday): Malicious Google ad led to a fake TurboTax page pushing an installer package that led to #DanaBot. List of indicators available at bit.ly/3qfbEgL




2024-02-14 (Wednesday): #Danabot from Italian-language #malspam List of IoCs available at bit.ly/49xx4qk #Unit42ThreatIntel #TimelyThreatIntel #IndicatorsOfCompromise #InfectionTraffic #Wireshark #C2Traffic


A bunch of #danabot zip -> zip -> vbs thanks to @FewAtoms pastebin.com/p9BDUjh5 and cc @apple as one of the c2's appears to be in your netblock?
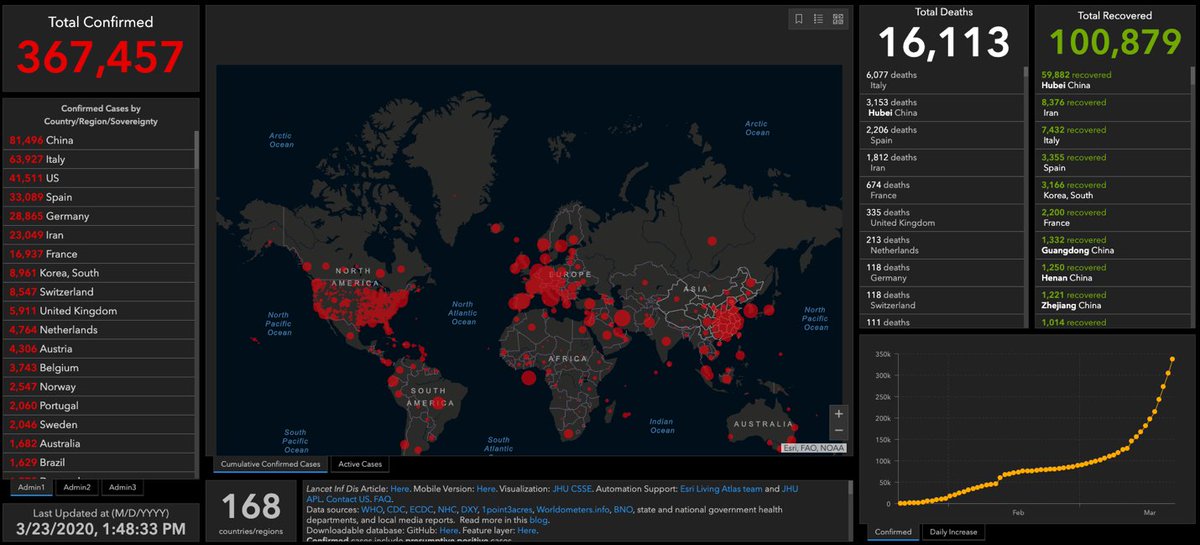
Download COVID-19 #DanaBot campaign analysis and #IOCs now. #infosec #cyberthreats #malware bit.ly/3dZ5giF
#Danabot is interesting in using different techniques to infect and hold on in a system. Let's take a detailed view of it! Downloader > 2 DLLs x86/x64 in ProgramData > Stealing data > Bypass UAC (WUSA) > Creates Service > Injects to system processes app.any.run/tasks/44f91d51…

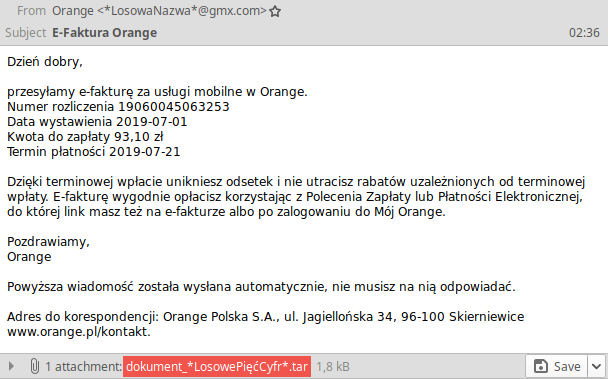
Ostrzegamy przed dużą kampanią spamową podszywającą się pod fakturę z Orange. Do wiadomości o tytule "E-Faktura Orange" dołączony jest #brushaloader, który pobierze trojana bankowego #danabot atakującego obecnie m.in. klientów polskich banków.
[In Review] #danabot is everywhere! Many samples we’ve recently investigated deliver malicious client-side code that’s removed milliseconds after injection. Targets include large financial institutions in Poland and Australia, popular social networks, and adult sites.
![F5Labs's tweet image. [In Review] #danabot is everywhere! Many samples we’ve recently investigated deliver malicious client-side code that’s removed milliseconds after injection. Targets include large financial institutions in Poland and Australia, popular social networks, and adult sites.](https://pbs.twimg.com/media/EH-jog1X0AAC3ce.png)
![F5Labs's tweet image. [In Review] #danabot is everywhere! Many samples we’ve recently investigated deliver malicious client-side code that’s removed milliseconds after injection. Targets include large financial institutions in Poland and Australia, popular social networks, and adult sites.](https://pbs.twimg.com/media/EH-josKWkAEA3wL.png)
![F5Labs's tweet image. [In Review] #danabot is everywhere! Many samples we’ve recently investigated deliver malicious client-side code that’s removed milliseconds after injection. Targets include large financial institutions in Poland and Australia, popular social networks, and adult sites.](https://pbs.twimg.com/media/EH-jo3-XYAYt-vK.png)
In yesterday's updates we made some improvements to our #Danabot configuration extractor. Check out recent samples here: tria.ge/s/family:danab… If you missed it catch up on this week's changes in our latest Triage Thursday blogpost - hatching.io/blog/tt-2021-0…

Something went wrong.
Something went wrong.
United States Trends
- 1. Lemon N/A
- 2. McVay N/A
- 3. Rams N/A
- 4. #NFLDraft N/A
- 5. Jaden McDaniels N/A
- 6. Jokic N/A
- 7. Stafford N/A
- 8. #Kehlani N/A
- 9. Ty Simpson N/A
- 10. Knicks N/A
- 11. Nuggets N/A
- 12. Steelers N/A
- 13. Bain N/A
- 14. Jets N/A
- 15. Caleb Downs N/A
- 16. DeepSeek V4 N/A
- 17. Beane N/A
- 18. Enid N/A
- 19. Snead N/A
- 20. Eagles N/A




































![melodana_b's profile picture. [1986.07.17] (SM ent.) '다나원조봇' 입니다! 바쁘신 다나 님을 대신하여 팬서비스 해드리고있어요~ 실제 다나님과 관련된 봇,패계분들 외에는 맞팔,멘션 하지않겠습니다! (중복X) ★Real DANA ☞ @melodana ★](https://pbs.twimg.com/profile_images/3285232184/4e4ad50f7f57c3b5694f24d5fcbc26bb.jpeg)