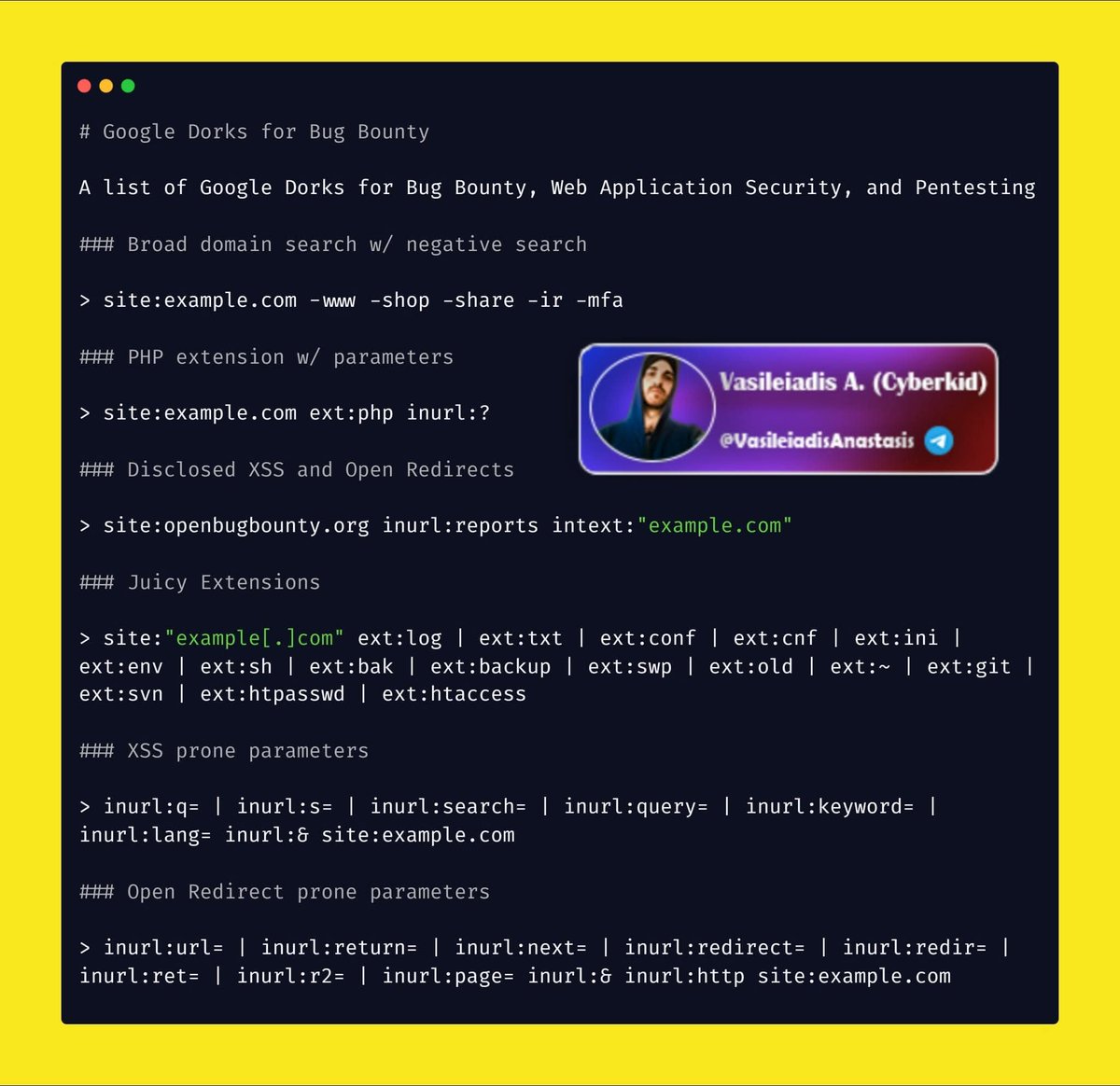
#hacking search results
🎣What are the five common types of phishing ? . Email phishing . Spear phishing . Clone phishing . Whaling . Pop-up phishing 🔖#infosec #cybersecurity #hacking #pentesting #security #phishing #whaling #clonephishing #spearphishing #emailphishing

🔓Best Password Cracking Tools 🔹Medusa 🔹Aircrack-ng 🔹Wfuzz 🔹OphCrack 🔹LophtCrack 🔹Hashcat 🔹Cain & Abel 🔹Rainbow Crack 🔹Brutus 🔹THC Hydra 🔹John the Ripper 🔖#infosec #cybersecurity #hacking #pentesting #security

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

🗺️Active Directory Pentesting Mind Map: V1: raw.githubusercontent.com/esidate/pentes… V2: raw.githubusercontent.com/esidate/pentes… 🔖#infosec #cybersecurity #hacking #pentesting #security

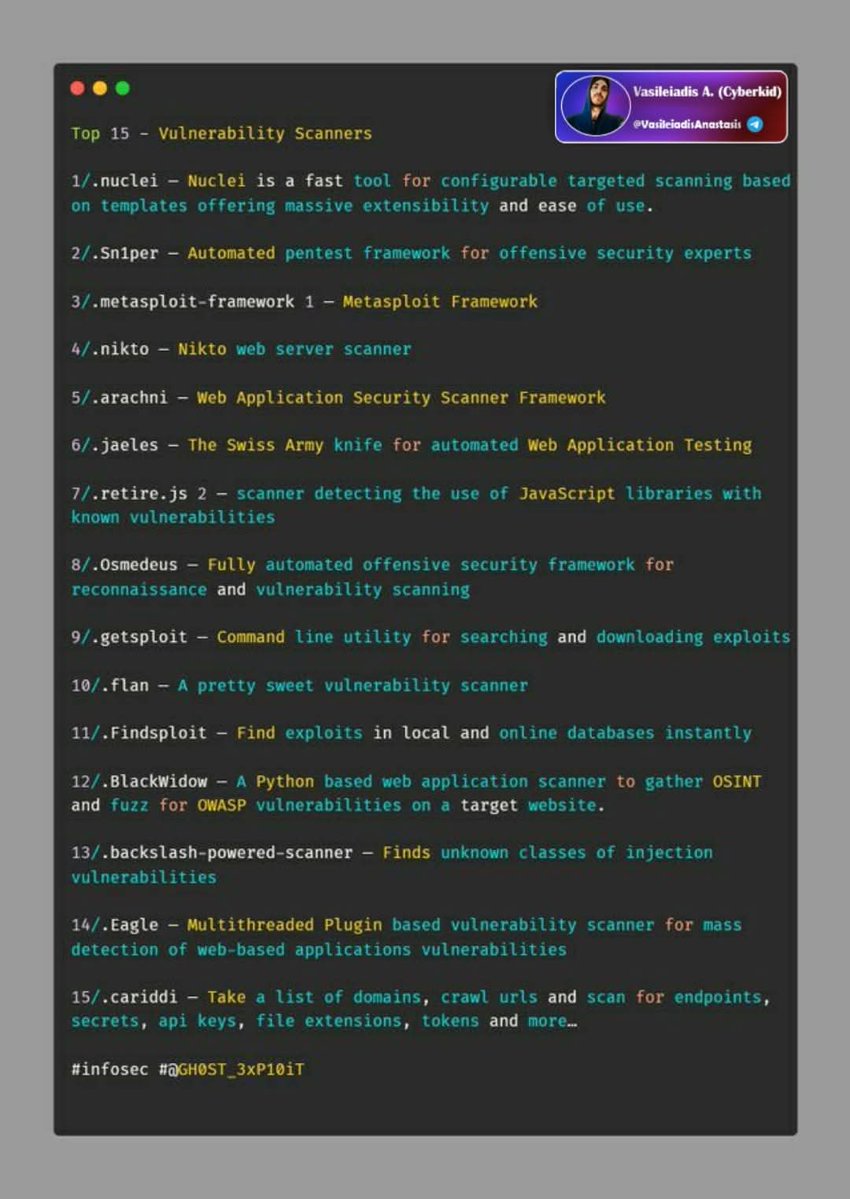
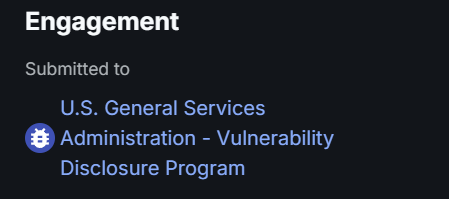
⚔️Top 15 Vulnerability Scanners 🔹Nuclei 🔹Sn1per 🔹Metasploit - Framework 🔹Nikto 🔹Arachni 🔹Jaeles 🔹Retire.js 🔹Osmedeus 🔹Getsploit 🔹Flan 🔹Findsploit 🔹Blackwidow 🔹Backslash-powered-scanner 🔹Eagle 🔹Cariddi 🔖#infosec #cybersecurity #hacking #pentesting #security
Real-World Ethical Hacking: Hands-on Cybersecurity 🔥 Download Link : drive.google.com/drive/folders/… #hacking #cybersecurity #hack #techahcks
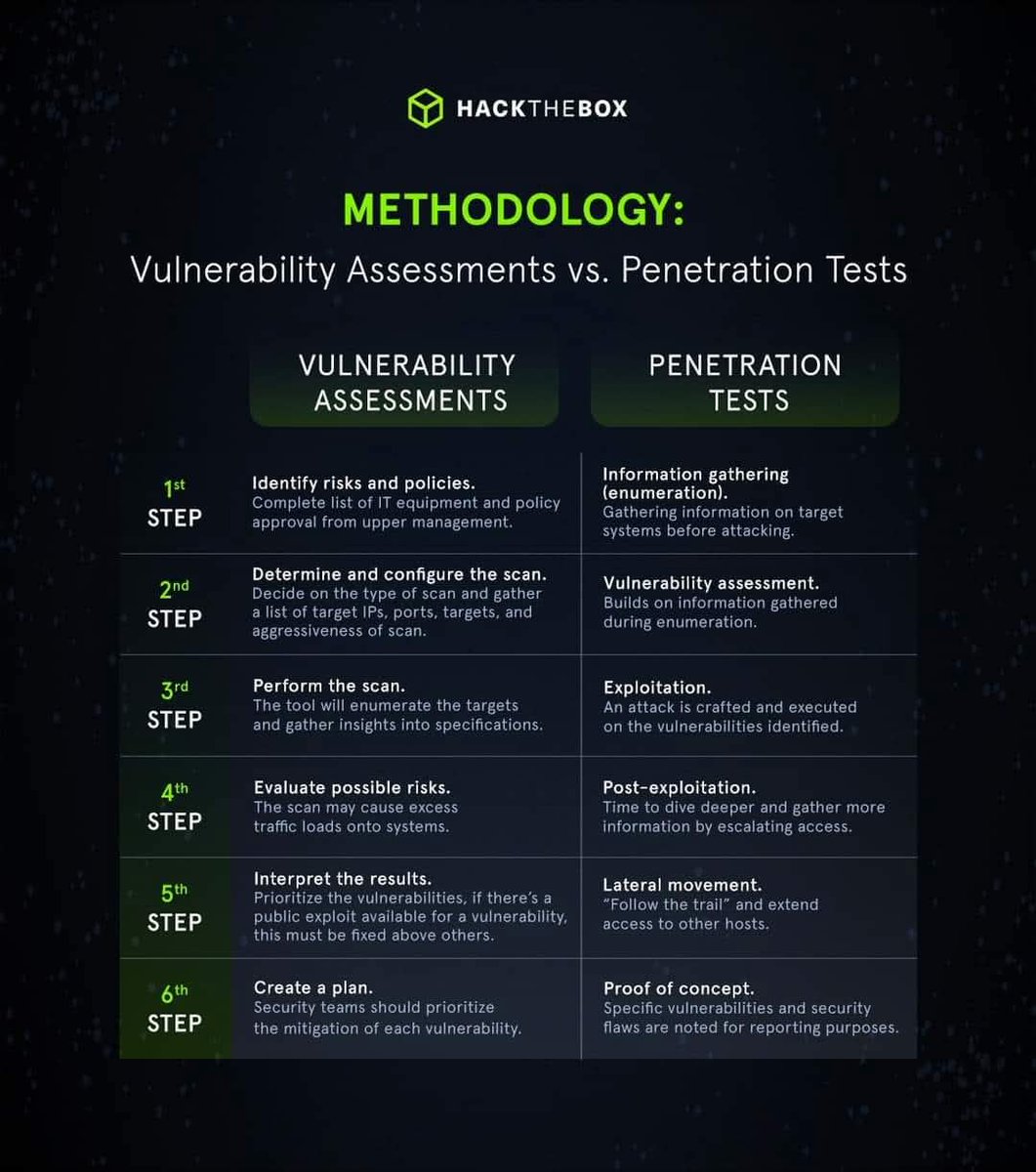
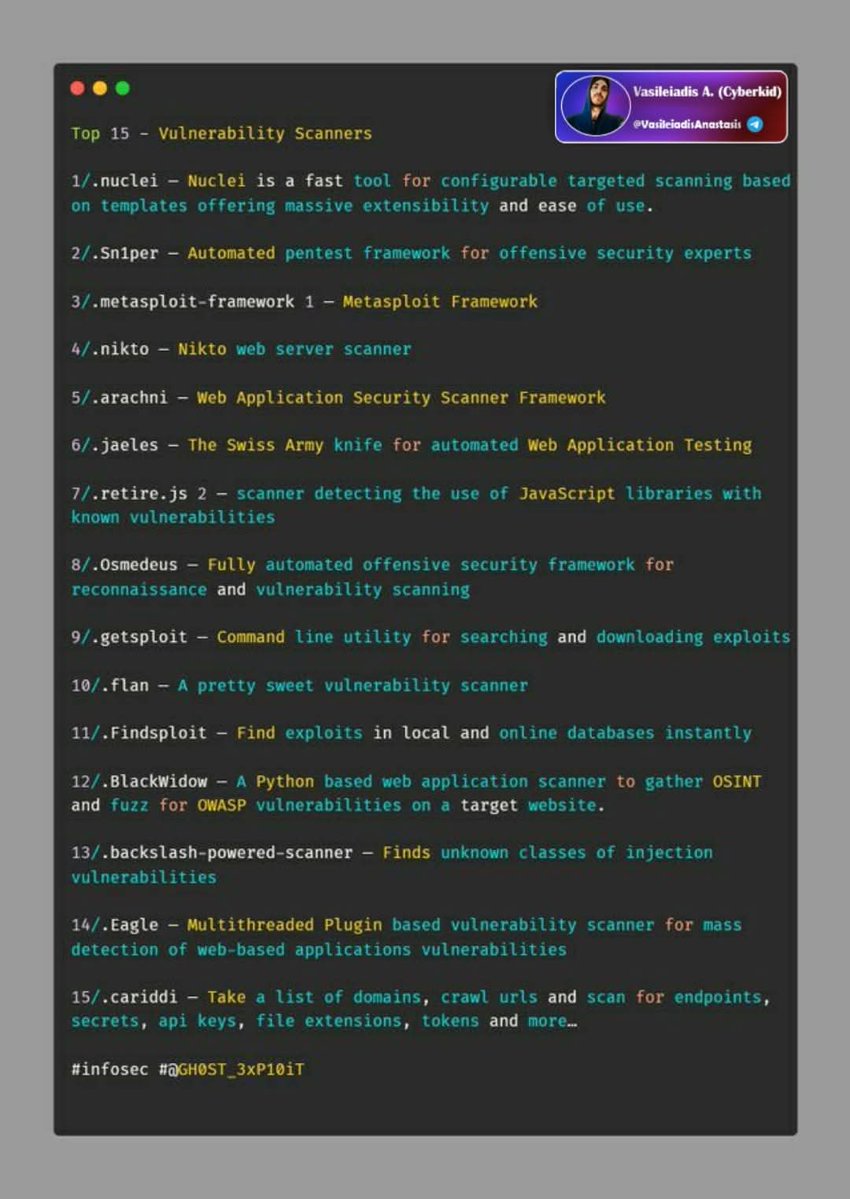
🔰Methodology: Vulnerability Assessments vs. Penetration Tests 🔖#infosec #cybersecurity #hacking #pentesting #security
⚒️Open Source SIEM Tools 🔰List: 🔹OSSIM 🔹Sagan 🔹Splunk Free 🔹Snort 🔹Elasticsearch 🔹MozDef 🔹ELK Stack 🔹Wazuh 🔹Apache Metron 🔖#infosec #cybersecurity #hacking #pentesting #security

🗝️Beginner intro to cryptography concepts with practical examples in Linux (openssl) 🔹Part 1: sergioprado.blog/introduction-t… 🔹Part 2: sergioprado.blog/a-hands-on-app… 🔹Part 3: sergioprado.blog/asymmetric-key… 🔹Part 4: sergioprado.blog/what-are-rando… 🔖#infosec #cybersecurity #hacking #pentesting #security
⚒️Best Cyber Security Tools 🔹OpenVAS 🔹SQLMap 🔹Aircrack-ng 🔹Maltego 🔹OpenSSH 🔹Nessus 🔹Zed Attack Proxy 🔹Wireshark 🔹Metasploit 🔹John 🔹Nmap 🔹Burp Suite 🔖#infosec #cybersecurity #hacking #pentesting #security

LayerZero relie le hack de KelpDAO au groupe Lazarus | Cointribune sur Binance Square ift.tt/wrkWdgV #PréventionInternet #Hacking #Cybersecurité
LayerZero relie le hack de KelpDAO au groupe Lazarus - Cointribune ift.tt/LHFEgCT #PréventionInternet #Hacking #Cybersecurité
@telegram @TelegramHelp Please help i am unable to login with my phone number and the email mentioned in screenshot is not mine. Help to recover account #hacking #phising

Hacker retire ETH natif emprunté sur Arbitrum | Phemex News ift.tt/Hi3BwZk #PréventionInternet #Hacking #Cybersecurité
Carrière de R. Hacker | BeSoccer ift.tt/pbNWlX1 #PréventionInternet #Hacking #Cybersecurité
300 M$ évaporés en 1 nuit : Les hackers nord-coréens mettent la crypto à genoux ! ift.tt/fqa3vci #PréventionInternet #Hacking #Cybersecurité
Le Conseil de Sécurité d'Arbitrum protège 30 766 ETH du hacker de KelpDAO - BeInCrypto ift.tt/pTf9aZG #PréventionInternet #Hacking #Cybersecurité
How Cybercriminal Networks Team Up with Disaffected French Youth to Collect Huge ... ift.tt/eMRO9IN #PréventionInternet #Hacking #Cybersecurité
🏷️ ¡Badge 2025 + Badge 2026 juntos con descuento! Últimas piezas disponibles. No dejes ir el combo. 🔥 ➡️ electroniccats.com/store/hackgdl/ #HackGDL #HackGDL2026 #hacking #cybersecurity #Mexico

Arbitrum gèle 30 000 ETH après le hack de Kelp DAO : le débat sur la décentralisation d ... ift.tt/gozcP7v #PréventionInternet #Hacking #Cybersecurité
Gold Sponsor Announcement 📣 Let’s welcome our BSides 2026 Gold Sponsor, @SANSInstitute and @CertifyGIAC! 🥳 Thank you for supporting learning, meaningful connections, talks, workshops, villages and much more. #bsides #hacking #infosec #event #tickets #sponsor

Hackers liés à la Corée du Nord volent plus de 500 M$ en crypto | Phemex News ift.tt/LrSKhEk #PréventionInternet #Hacking #Cybersecurité
What Is The Safest Video Conferencing Platform? Read here---->buff.ly/3X0xQYf #cybersecurity #hacking #security #technology #hacker #infosec #ethicalhacking #cybercrime #tech #linux #cyber #hackers #informationsecurity #cyberattack #programming

Trojanized Android App Fuels New Wave of NFC Fraud infosecurity-magazine.com/news/trojanize… #cybersecurity #infosec #hacking
📸 ¿Ya te viste? ¡Las fotos de HackGDL 2026 ya están en Flickr! ➡️ bit.ly/hackgdl-flickr… #HackGDL #HackGDL2026 #hacking #cybersecurity #Mexico

⚓ Détroit d’Ormuz : des pirates demandent du Bitcoin pour laisser passer les navires #CyberSécurité 📉 Hacker vole 293 M$, LayerZero vs KelpDAO en litige #Hacking [3/4]
⚠️ Buscadores en la Red Tor 🔥 reydes.com/e/Buscadores_e… #cybersecurity #hacking #redteam #forensics #dfir #osint

Cyberattaque de l'ANTS : "Il va falloir porter plainte contre l'État", selon Clément Domingo youtube.com/watch?v=cemv6U… #PréventionInternet #Hacking #Cybersecurité

youtube.com
YouTube
Europe 1
Arbitrum bloque des ETH liés au hack de Kelp DAO – Récap crypto de la nuit du 20 au 21 avril 2026 ift.tt/RrDjwzg #PréventionInternet #Hacking #Cybersecurité
🎣What are the five common types of phishing ? . Email phishing . Spear phishing . Clone phishing . Whaling . Pop-up phishing 🔖#infosec #cybersecurity #hacking #pentesting #security #phishing #whaling #clonephishing #spearphishing #emailphishing

🔓Best Password Cracking Tools 🔹Medusa 🔹Aircrack-ng 🔹Wfuzz 🔹OphCrack 🔹LophtCrack 🔹Hashcat 🔹Cain & Abel 🔹Rainbow Crack 🔹Brutus 🔹THC Hydra 🔹John the Ripper 🔖#infosec #cybersecurity #hacking #pentesting #security

🌐Database Search Engine 🗄️16,443,023,451 rows over 1,343 databases 🔗osint.lolarchiver.com/database_lookup 🔖#infosec #cybersecurity #hacking #pentesting #security #OSINT

⚔️Top 15 Vulnerability Scanners 🔹Nuclei 🔹Sn1per 🔹Metasploit - Framework 🔹Nikto 🔹Arachni 🔹Jaeles 🔹Retire.js 🔹Osmedeus 🔹Getsploit 🔹Flan 🔹Findsploit 🔹Blackwidow 🔹Backslash-powered-scanner 🔹Eagle 🔹Cariddi 🔖#infosec #cybersecurity #hacking #pentesting #security
🗺️Active Directory Pentesting Mind Map: V1: raw.githubusercontent.com/esidate/pentes… V2: raw.githubusercontent.com/esidate/pentes… 🔖#infosec #cybersecurity #hacking #pentesting #security

🔰Methodology: Vulnerability Assessments vs. Penetration Tests 🔖#infosec #cybersecurity #hacking #pentesting #security
⚒️Open Source SIEM Tools 🔰List: 🔹OSSIM 🔹Sagan 🔹Splunk Free 🔹Snort 🔹Elasticsearch 🔹MozDef 🔹ELK Stack 🔹Wazuh 🔹Apache Metron 🔖#infosec #cybersecurity #hacking #pentesting #security

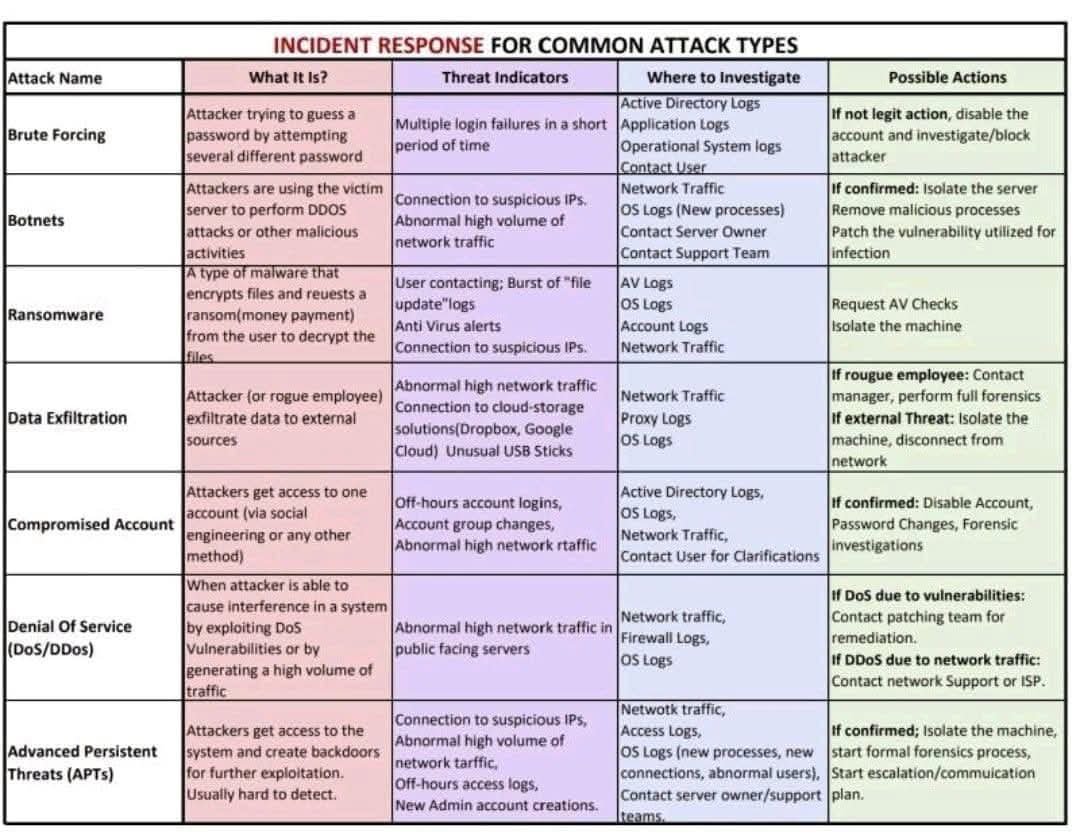
🛡️20 Best Security Investigation Tools 🔖#infosec #cybersecurity #hacking #pentesting #security 👤beacons.ai/cyberkid1987 👤t.me/VasileiadisAna…

🗝️Beginner intro to cryptography concepts with practical examples in Linux (openssl) 🔹Part 1: sergioprado.blog/introduction-t… 🔹Part 2: sergioprado.blog/a-hands-on-app… 🔹Part 3: sergioprado.blog/asymmetric-key… 🔹Part 4: sergioprado.blog/what-are-rando… 🔖#infosec #cybersecurity #hacking #pentesting #security
⚒️Best Cyber Security Tools 🔹OpenVAS 🔹SQLMap 🔹Aircrack-ng 🔹Maltego 🔹OpenSSH 🔹Nessus 🔹Zed Attack Proxy 🔹Wireshark 🔹Metasploit 🔹John 🔹Nmap 🔹Burp Suite 🔖#infosec #cybersecurity #hacking #pentesting #security

Something went wrong.
Something went wrong.
United States Trends
- 1. SPLC N/A
- 2. Southern Poverty Law Center N/A
- 3. Fairfax N/A
- 4. VJ Edgecombe N/A
- 5. Jaylen Brown N/A
- 6. Cursor N/A
- 7. TACO Tuesday N/A
- 8. Josh Allen N/A
- 9. Big G N/A
- 10. Virginia N/A
- 11. Nolan McLean N/A
- 12. Giancarlo Stanton N/A
- 13. Charlottesville N/A
- 14. #NXTRevenge N/A
- 15. Patriot Front N/A
- 16. Unite the Right N/A
- 17. Steven Seagal N/A
- 18. #WillTrent N/A
- 19. Marc Davis N/A
- 20. Smallpox N/A