#informationsecurity search results
Key Control Every Organisation Should Implement First Key Security Controls Every Organization Should Implement First Before advanced tools and complex frameworks, get the basics right. Visit Site: azpirantz.com #CyberSecurity #InformationSecurity #SecurityBasics

Organizations must protect data, systems, and operations from evolving threats. @HilSecLtd helps businesses build strong, resilient security frameworks. hilsec.com #InformationSecurity #Cybersecurity #RiskManagement
A strong information security posture protects more than data. It protects trust, operations, and business continuity. @HilSecLtd works with organizations to strengthen security at every level. #InformationSecurity #CyberResilience #DigitalTrust
#Tech #InformationSecurity #DigitalSkills #CareerGrowth #SelfDevelopment #FutureOfWork #YoungProfessionals #Zero2Cybersecurity
Posizione: Security Specialist Azienda/Ente: Silicondev S.p.A. Sede di lavoro: Ibrida - Roma Contratto: deciso in fase di colloquio Candidati qui: lavoroit.it/offerte/securi… #CyberSecurity #InformationSecurity #ITSecurity #SecuritySpecialist
linkedin.com/posts/raed-tat… #CyberSecurity #AI #InformationSecurity #TechLeadership #DigitalTransformation #N_Day #Infosec #EnterpriseSecurity #RiskManagement #EmergingTech
"With AI, we don’t make mistakes better - we just make them much faster!" AI Product Security: Incident Response in the Age of Intelligent Systems! #InformationSecurity #CyberSecurity #Governance #AITestEnvironment #CyberRisk #MITRE #LLMs #OWASP 👇👇👇👇 linkedin.com/pulse/ai-produ…
ParamInfo helps enterprises identify, assess, and strengthen their cybersecurity posture across networks, endpoints, data, and access layers. #Cybersecurity #InformationSecurity #DataProtection

Turn compliance into capability. Get hands-on with expert-led ISO training and build skills that actually matter. Enroll today 👉 konvergenceksa.io @konvergence01 #ISO27001 #InformationSecurity #RiskManagement #Compliance #CyberSecurity #ProfessionalTraining

54% of CEOs fear AI-assisted malware. Security is now a race of algorithms. Are your human leaders equipped to oversee the battle? #InformationSecurity #AIThreats #TechLeadership
We write and review your company #InformationSecurity policies and procedures: #infosec #cybersecurity #databreach ift.tt/ciark3w
As I move further into Protecting Digital Assets, these labs help me understand exactly what we are up against. Stay curious, stay ethical. 🔐 #InformationSecurity #networksecurity #CyberAwareness #keylogger #ethicalhacking
Business growth should never stop for cyber threats. 👉darkrhiinosecurity.com #Cybersecurity #InformationSecurity #CISO #DarkRhiinoSecurity

Something new is on the way… We've been working hard behind the scenes on something we can't wait to share. Let's just say… the conversations have been very interesting Can you guess what it is? #PhishingForTrouble #InformationSecurity #Privacy #AI #TheResillienceLoop
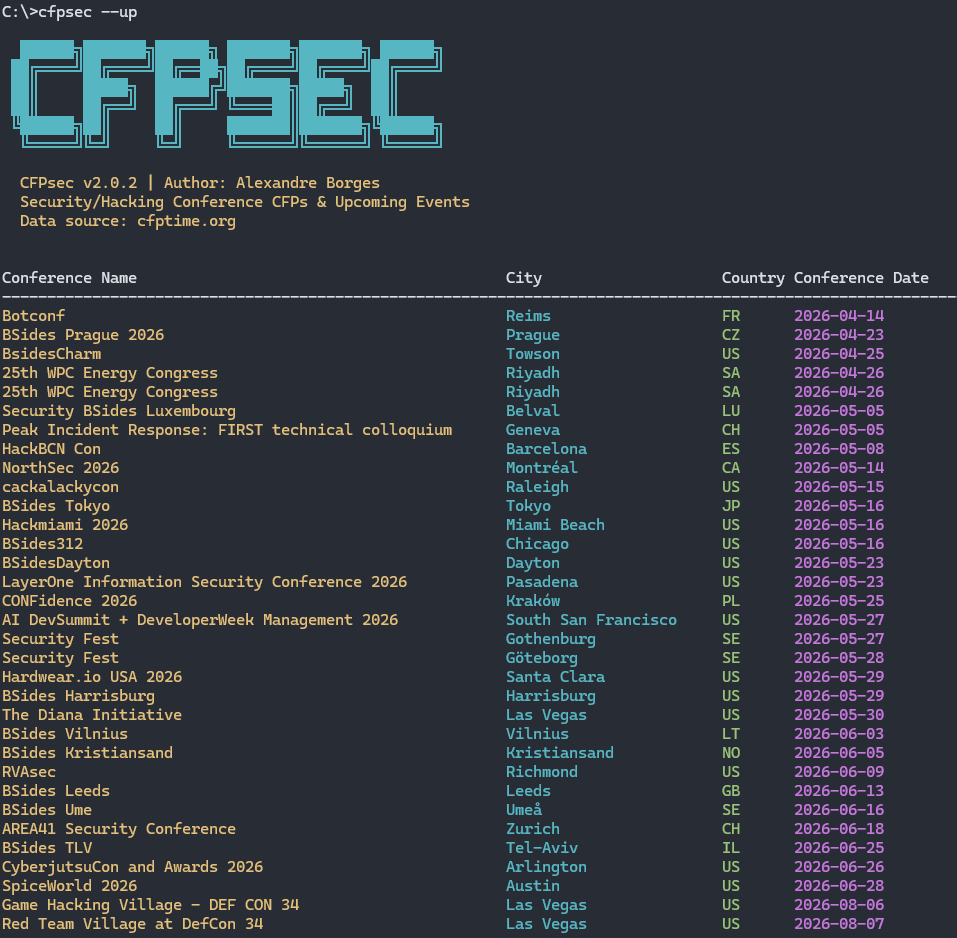
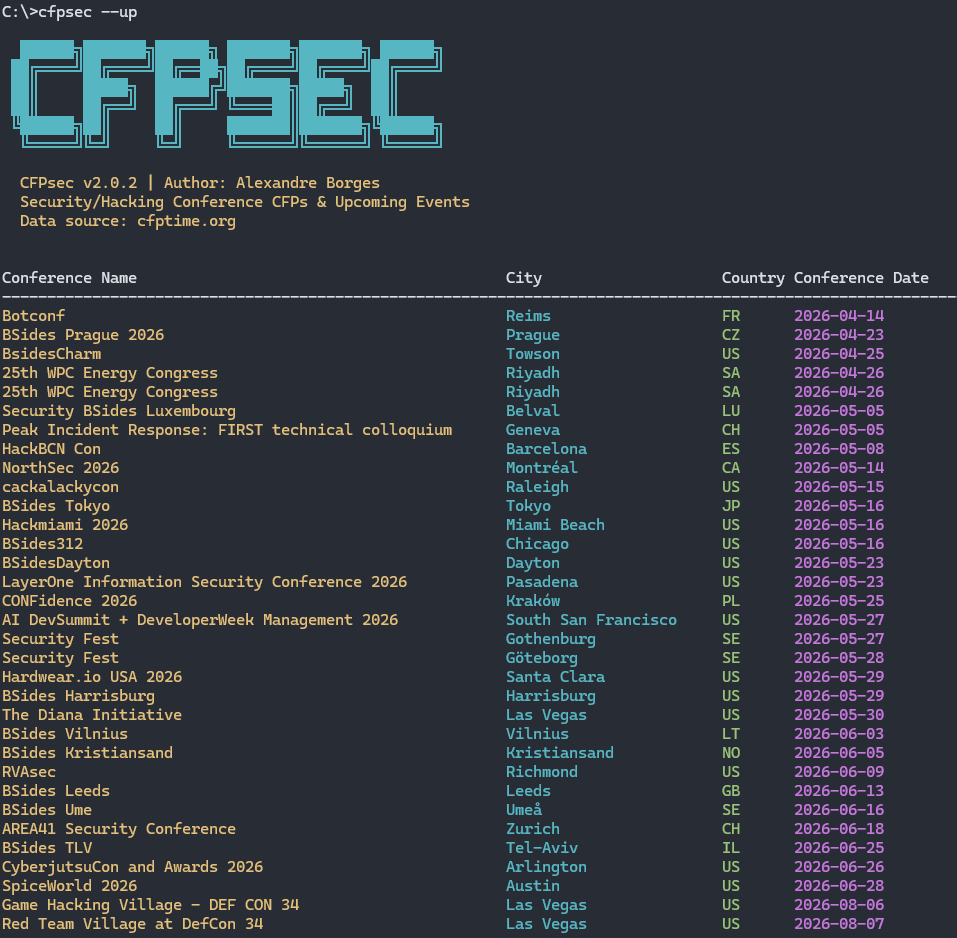
The CFPsec v2.0.2 is available: github.com/alexandreborge… To install it: python -m pip install -U cfpsec #cybersecurity #informationsecurity #conferences
Cybersecurity careers are booming 🚀 Learn skills & get placed 👇 Enroll Now : h2kinfosys.com/courses/cyber-… 📞 +1 770-777-1269 | 📧 [email protected] 👉about H2kinfosys In One Click: h2kinfosys.com/quick-links/ #CyberSecurityCareers #CyberSecurityTraining #InformationSecurity

🔐🌏 Meet Cryptography at ACISP 2026 – Perth, Australia 📅 Date: 6–9 July 2026 📍 Location: Perth, Australia 🔗 Read more: mdpi.com/journal/crypto… #ACISP2026 #InformationSecurity #Privacy #Cybersecurity

We write and review your company #InformationSecurity policies and procedures: #infosec #cybersecurity #databreach ift.tt/kvaYqow
Key Control Every Organisation Should Implement First Key Security Controls Every Organization Should Implement First Before advanced tools and complex frameworks, get the basics right. Visit Site: azpirantz.com #CyberSecurity #InformationSecurity #SecurityBasics

A strong information security posture protects more than data. It protects trust, operations, and business continuity. @HilSecLtd works with organizations to strengthen security at every level. #InformationSecurity #CyberResilience #DigitalTrust
Organizations must protect data, systems, and operations from evolving threats. @HilSecLtd helps businesses build strong, resilient security frameworks. hilsec.com #InformationSecurity #Cybersecurity #RiskManagement
#Tech #InformationSecurity #DigitalSkills #CareerGrowth #SelfDevelopment #FutureOfWork #YoungProfessionals #Zero2Cybersecurity
As I move further into Protecting Digital Assets, these labs help me understand exactly what we are up against. Stay curious, stay ethical. 🔐 #InformationSecurity #networksecurity #CyberAwareness #keylogger #ethicalhacking
Business growth should never stop for cyber threats. 👉darkrhiinosecurity.com #Cybersecurity #InformationSecurity #CISO #DarkRhiinoSecurity

"With AI, we don’t make mistakes better - we just make them much faster!" AI Product Security: Incident Response in the Age of Intelligent Systems! #InformationSecurity #CyberSecurity #Governance #AITestEnvironment #CyberRisk #MITRE #LLMs #OWASP 👇👇👇👇 linkedin.com/pulse/ai-produ…
Posizione: Security Specialist Azienda/Ente: Silicondev S.p.A. Sede di lavoro: Ibrida - Roma Contratto: deciso in fase di colloquio Candidati qui: lavoroit.it/offerte/securi… #CyberSecurity #InformationSecurity #ITSecurity #SecuritySpecialist
Cybersecurity careers are booming 🚀 Learn skills & get placed 👇 Enroll Now : h2kinfosys.com/courses/cyber-… 📞 +1 770-777-1269 | 📧 [email protected] 👉about H2kinfosys In One Click: h2kinfosys.com/quick-links/ #CyberSecurityCareers #CyberSecurityTraining #InformationSecurity

Something new is on the way… We've been working hard behind the scenes on something we can't wait to share. Let's just say… the conversations have been very interesting Can you guess what it is? #PhishingForTrouble #InformationSecurity #Privacy #AI #TheResillienceLoop
Submission System URL: airccse.com/submissioncs/h… Here's where you can reach us : [email protected] or [email protected] #cybersecurity #informationsecurity #dataprivacy #trustmanagement #privacypreserving #securesystems #digitaltrust #securityframeworks #authentication
We write and review your company #InformationSecurity policies and procedures: #infosec #cybersecurity #databreach ift.tt/ciark3w
ParamInfo helps enterprises identify, assess, and strengthen their cybersecurity posture across networks, endpoints, data, and access layers. #Cybersecurity #InformationSecurity #DataProtection

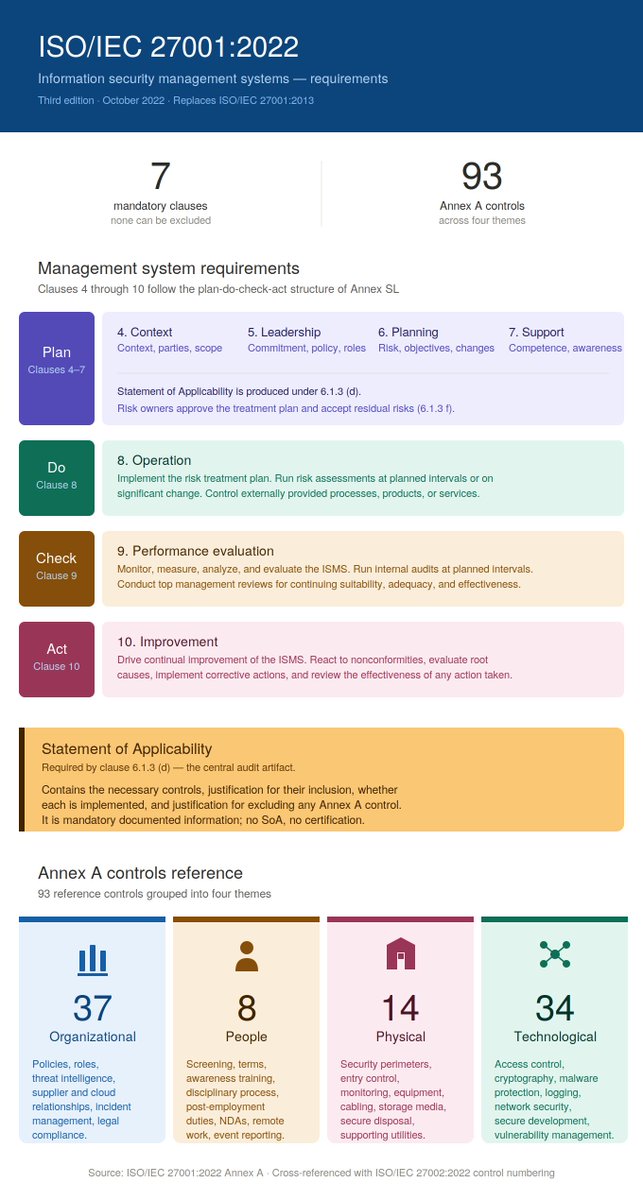
ISO/IEC 27001:2022 in one page. If your team is preparing for certification, mapping existing controls, or just trying to get a shared mental model of the standard, this might help. #ISO27001 #InformationSecurity #ISMS #CISO #Cybersecurity #Compliance #RiskManagement #GRC
combining global standards with deep local market insight. For more info and registration: libya-forum.tech #CyberSecurity #informationsecurity #Al #RegisterNow #fourm #LTF2026 #Cairo
The Palantir Manifesto: «The Technological Republic» quantumhorizon.it/palantir-manif… #CyberSecurity #InformationSecurity #QuantumComputing #QuantumSecurity #CyberRisk
Libro Bianco sulla Cyber Difesa e Cyber Attacco: Quantum Horizon di Remo Pulcini pubblica la prima proposta strategica integrata per una Paese quantumhorizon.it/libro-bianco-c… #CyberSecurity #InformationSecurity #QuantumComputing #QuantumSecurity #CyberRisk
The CFPsec v2.0.2 is available: github.com/alexandreborge… To install it: python -m pip install -U cfpsec #cybersecurity #informationsecurity #conferences
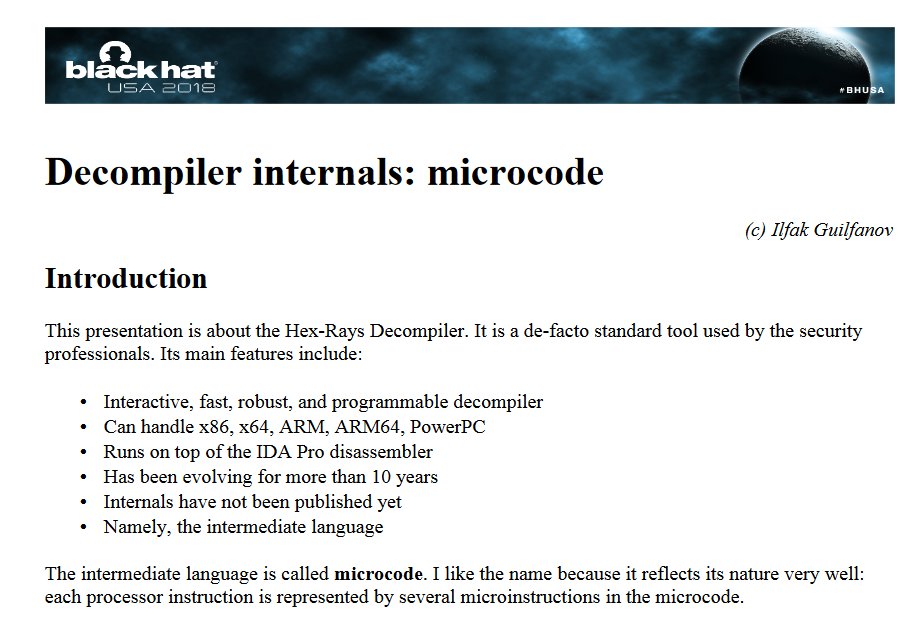
This presentation remains the go-to reference for learning the inner workings of the IDA Pro Hex-Rays decompiler: (video) youtube.com/watch?v=T-YkhN… (article) i.blackhat.com/us-18/Thu-Augu… #decompiler #reverseengineer #informationsecurity #cybersecurity
Buona Pasqua a tutti da Red Hot Cyber 🎉 #redhotcyber #informationsecurity #ethicalhacking #dataprotection #hacking #cybersecurity #cybercrime #cybersecurityawareness #cybersecuritytraining #cybersecuritynews #privacy #infosecurity

📢#CallforPapers! 💻Advanced Technologies for #InformationSecurity 🔗More Info: mdpi.com/journal/electr… 📅Deadline for submissions: 15 September 2026 Guest Editor from @okstate #AI #cybersecurity #blockchain #DataPrivacy #DataProtection #InformationSystems #NetworkSecurity
A new Special Issue opens for submission! Title: Applied Symmetry in #Cryptography and #InformationSecurity Editor: Funminiyi Olajide, Nemitari Ajienka and Tawfik Al-Hadhrami Details: brnw.ch/21x1MdN #callforpapers #mdpisymmetry #cloudsecurity @penn_state @NottmTrentUni

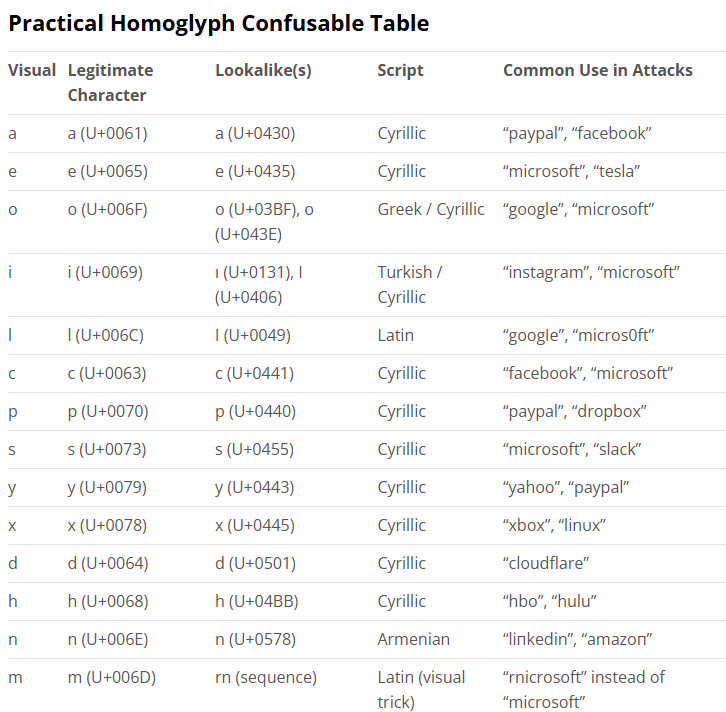
Homoglyph Attacks: How Lookalike Characters Are Exploited for Cyber Deception: seqrite.com/blog/homoglyph… #threathunting #infosec #informationsecurity #phishing
Merkur Group strengthens information security: Manuel Kreft becomes CISO soloazar.com/en/category/ot… #MerkurGroup #InformationSecurity #CISO #CyberSecurity #iGamingNews #SoloAzar #News

UAE Cyber Security Council Warns 1 in 4 Public Files Contain Sensitive Personal Data dlvr.it/TS75F8 #Security #PersonalData #InformationSecurity #Technology

Speed builds startups; neglect breaks them. Most founders are obsessed with product, growth, and funding rounds. Very few obsess over attack surface, access control, and visibility. #Security #CyberSecurity #InformationSecurity #CyberAttacks #SecurityBreach



🔐 Ein strukturiertes Cybersecurity-Programm – warum es heute für jedes Unternehmen entscheidend ist! #Cybersecurity #InformationSecurity #ITSecurity #RiskManagement #Governance #CyberRisk #ActiveCyberProgram 👇👇👇👇 linkedin.com/pulse/ein-stru…

Something went wrong.
Something went wrong.
United States Trends
- 1. Good Tuesday N/A
- 2. Kyle Tucker N/A
- 3. Cade N/A
- 4. Spencer Jones N/A
- 5. Pistons N/A
- 6. Duren N/A
- 7. #BCSpoilers N/A
- 8. #WWERaw N/A
- 9. Devin Booker N/A
- 10. #ForgedInGold N/A
- 11. #TusksUp N/A
- 12. Magic N/A
- 13. Tabata N/A
- 14. World War Eleven N/A
- 15. Roseanne N/A
- 16. Orlando N/A
- 17. Kid Rock N/A
- 18. Asta N/A
- 19. #ThunderUp N/A
- 20. Game 6 N/A