#securecode search results
How to Write Secure Code in C#? c-sharpcorner.com/article/how-to… via @CsharpCorner #SecureCode #CSharp

Collaborative coding is the fabric that weaves teams together, but it also introduces security risks 🚪🪲 In this thread, we'll explore 5 key strategies to ensure secure coding 🛡 Let's dive in! 🧵👇 #softwaresecurity #DevSecOps #SecureCode
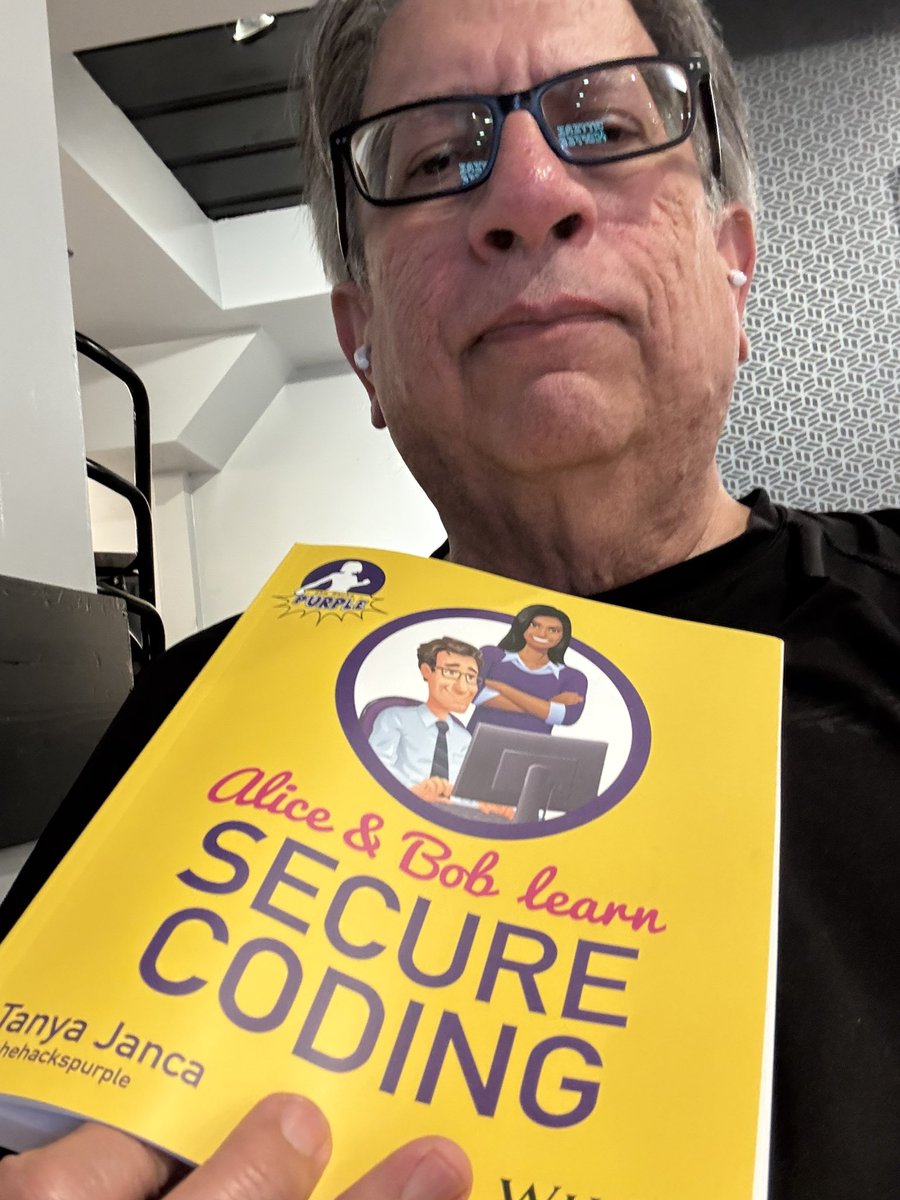
Starting this new book. Yes it’s nerdy but the plot is a good one @shehackspurple #coding #securecode #reading #books I suggest that you pick one up yourself.
What can small businesses do to force vendors to create more secure software? I have some ideas for you! #appsec #securecode @bsidesedmonton
Do you have a bias towards or against certain AppSec tools? If so, why? And which ones? I want us to try to learn from each other. #appsec #securecode #cybersecurity

#Securecode lovers! 👋 We've launched tons of new learning content & features on the SCW platform: AI Challenges, AI Security Rules on GitHub, Quests innovations, Vulnerability Insights & more. Ready to increase your #securecoding posture? Request a demo: ow.ly/aEkT50WQEsK
The very first #DevoxxGreece2023 conference is coming! Join us & Stella Varvarigou on Thur,4/5 to talk about #SASTtools in creating #securecode. Learn more: devoxx.gr/talk/?id=4622 #code4thought #techindustry #technews #softwaresecurity

If you could wave a magic wand, and "solve" 3 security problems, what would they be? And why? #appsec #securecode #cybersecurity

Tired of countless false positives and missed bugs? 👀 (lol) TrustInSoft Analyzer uses exhaustive static analysis to mathematically verify code correctness. Learn how: bit.ly/4jUSVx9 #FormalVerification #SecureCode

📱Once code hits the App Store, your control ends—but the risk doesn’t. Subho Halder breaks down the hidden dangers of mobile security and why early detection is everything. 🎙️ Catch the episode now → bit.ly/3TfiOfB #MobileSecurity #ShiftLeft #SecureCode
API security is critical. From authentication to input sanitization, every step matters. I’ve shared a quick blog on essential API security measures for developers. Read here: newsletter.masteringbackend.com/p/api-and-api-… #APISecurity #BackendDev #SecureCode #MasteringBackend #ayshriv

What is a virtual machine, and how do you use one? 🤔 It can be a game changer in secure code training. 🎮 Learn how we use VMs to create real coding environments for hands-on learning in our recent blog post. 💻✨ 📖 Read more: ow.ly/fhYi50Wp7UJ #vm #securecode #appsec

When AI writes the code, we read between the lines. Orbitshield ensures your AI-generated code is secure, compliant, and production-ready. #HumanInTheLoop #AIaudit #SecureCode

Can a package update do more harm than good? Akshatha Laxmi breaks down how unchecked updates, especially major ones, can introduce vulnerabilities, and how tools like Snyk keep your system safe. 🎥 Watch: bit.ly/426ZjLU #CyberSecurity #DevOps #SecureCode #AntStack
🚨 NYC Devs: Ready to prove your #securecoding skills? Join #OWASPNYC, @awscloud & @SecCodeWarrior for the NY #SecureCode Showdown! Fix vulnerabilities, compete in your fave languages & level up your security game. 🗓️ Oct 9 @ AWS NYC. Laptop required! ow.ly/p5ee50X53Y3
Writing secure code is hard. Building, debugging & fixing software is hard by itself, now you also have to make it secure?? But don't worry, we got you. Here are the "5 Easiest Secure Coding Practices You'll Never Forget" #securecode #developer #security #appsec #infosec

Thank you to all who visited us at #OWASP #AppSecEU2025 Barcelona! It was an incredible two days of insights & connections. 🤝 Big thanks to those at the 'Cocktails & Conversations' Happy Hour event for engaging discussions on #securecode & #DeveloperRiskManagement! 🔒✨




Improper Neutralization of Special Elements in a Command (CWE-77) lets input hijack how commands run. This can allow attackers to execute code or even cause a total compromise. 🛑 💡 Tip: Always sanitize input before constructing commands. #CWE #appsec #securecode

Secure coding isn’t a checklist; it’s a mindset. ✅🧠 Strong teams master the fundamentals that make secure development the default. 👉 Read more: ow.ly/9LCP50Xyj6j #securecode #appsec #devsecops
#VibeCoding speeds up development but also introduces real security risks. AI-generated code can hide injection flaws, unsafe dependencies, and other issues teams need to catch early. Strong secure-coding habits still matter. 👉 itpro.com/technology/art… #AppSec #SecureCode #AI
2025 was a year of momentum at CMD+CTRL: a redesigned training platform, new AI content, and a growing cyber range community, to name a few. 🙌 ➡️ Explore our 2025 milestones: blog.cmdnctrlsecurity.com/milestones-to-… #Cybersecurity #AppSec #SecureCode #SoftwareSecurity #AI

Our new research shows a divide in AI-assisted coding. OpenAI's GPT-5 models lead in generating secure code, but progress across the wider industry has stalled, introducing new risks. Read the full analysis in our blog: #GenAI #SecureCode #AppSec sprou.tt/18NAiZi3tAP
Afrensics builds secure digital solutions. High-performance Web & App Development coded with a forensics mindset. Stop risking it. Build with the experts. ➡️ aedisecurity.com #SecureCode #WebDev
⏰ Last chance! Our LIVE threat modeling webinar starts today at 1 pm EST. Learn how to build more secure software, faster, with a lightweight, developer-friendly threat modeling approach. Don’t miss it → ow.ly/wivr50Xuh82 #threatmodel #securecode #securebydesign

Our new research shows a divide in AI-assisted coding. OpenAI's GPT-5 models lead in generating secure code, but progress across the wider industry has stalled, introducing new risks. Read the full analysis in our blog: #GenAI #SecureCode #AppSec sprou.tt/1w2CRzWOSvT
❌ “Threat modeling slows us down” ✅ Watch us prove that wrong in 60 mins Live Walkthrough: Fast, dev-friendly threat modeling that fits your flow. Nov 20 | 1PM EST Zero disruption. All results. 🪑 Save your seat: ow.ly/FHEQ50XtxMj #threatmodel #securecode #webinar

Which part of this code is responsible for preventing directory traversal attacks? #developers #DevSecOps #securecode

The dangers of unsupported applications - helpnetsecurity.com/2023/02/10/dan… - @Appurity #code #SecureCode #dev #netsec #security #InfoSecurity #ITsecurity #CyberSecurityNews #SecurityNews

Establishing secure habits for software development in 2023 - helpnetsecurity.com/2023/02/09/sec… - @SecurityJourney #code #AppSec #SecureCode #dev #netsec #security #InfoSecurity #ITsecurity #CyberSecurityNews #SecurityNews

How to Write Secure Code in C#? c-sharpcorner.com/article/how-to… via @CsharpCorner #SecureCode #CSharp

Collaborative coding is the fabric that weaves teams together, but it also introduces security risks 🚪🪲 In this thread, we'll explore 5 key strategies to ensure secure coding 🛡 Let's dive in! 🧵👇 #softwaresecurity #DevSecOps #SecureCode
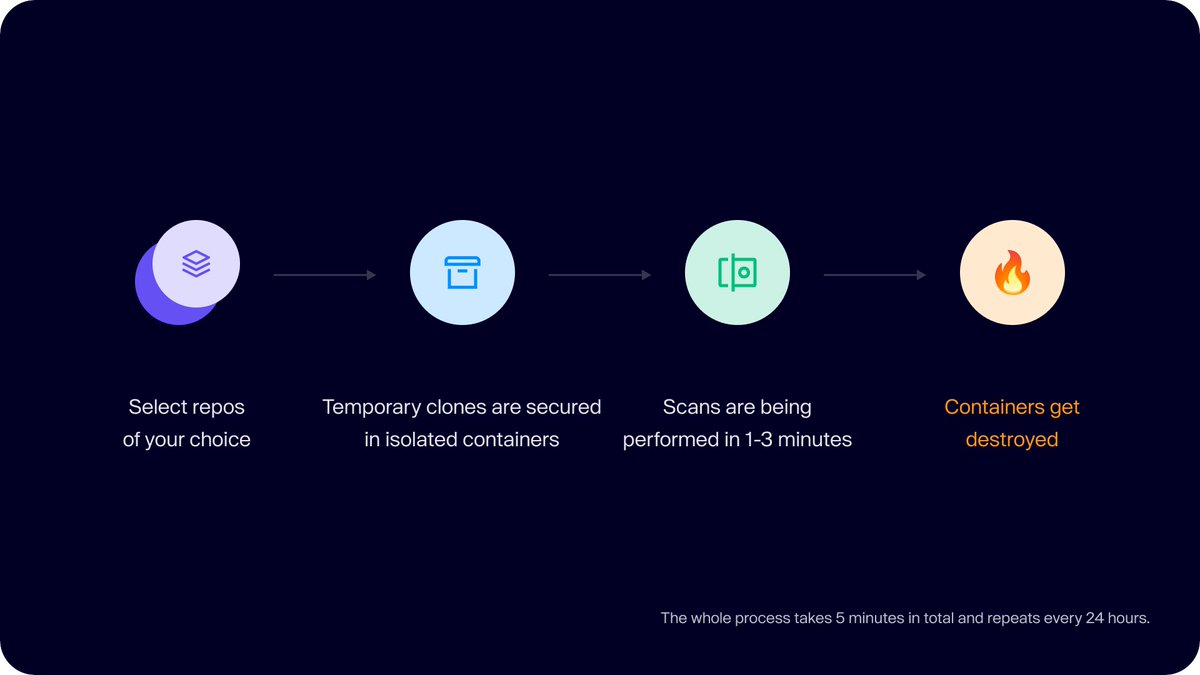
Trust is paramount when it comes to code security 🤝 🛡 Aikido scans your code without storing any code! Read this to learn about how Aikido ensures your code is safe 👇 help.aikido.dev/en/articles/69… #softwaresecurity #securecode #DevSecOps
Starting this new book. Yes it’s nerdy but the plot is a good one @shehackspurple #coding #securecode #reading #books I suggest that you pick one up yourself.
Tired of countless false positives and missed bugs? 👀 (lol) TrustInSoft Analyzer uses exhaustive static analysis to mathematically verify code correctness. Learn how: bit.ly/4jUSVx9 #FormalVerification #SecureCode

As someone who is tasked with creating #maintainable, #securecode, this #codegen stuff scares the bejeezus out of me
What is a virtual machine, and how do you use one? 🤔 It can be a game changer in secure code training. 🎮 Learn how we use VMs to create real coding environments for hands-on learning in our recent blog post. 💻✨ 📖 Read more: ow.ly/fhYi50Wp7UJ #vm #securecode #appsec

Security extends beyond firewalls & intrusion detection systems - Cerbos' Product Lead, @alexolivier, highlights in an @ABridgwater @forbestech article. #Securecode = User protection & org reputation. cerbos.dev/blog/the-power… #CyberSecurity #Cerbos #Forbes

Do you have a PIN set up with your cell phone provider? Check and make sure it is the max length allowed. #SIMcardSwapping #Scam #SecureCode @AT&T #CryptoCurrency #MacRepair #PCRepair #VirusRemoval #FrontRange #Niwot #NoBo #GeekForHire geekforhireinc.com/sim-card-swapp…

API security is critical. From authentication to input sanitization, every step matters. I’ve shared a quick blog on essential API security measures for developers. Read here: newsletter.masteringbackend.com/p/api-and-api-… #APISecurity #BackendDev #SecureCode #MasteringBackend #ayshriv

🚀 We're teaming up with @Carahsoft to host a webinar that will transform the way you think about secure coding! 🛡️ Learn how to empower developers to minimize software vulnerabilities from the start. Secure your spot today! 👉 ow.ly/wKvu50VR0VQ #appsec #securecode

Want to avoid costly breaches? Address risks during the SDLC process with Raxis’ expert cybersecurity code reviews. 🔗 Discover our process: raxis.com/cybersecurity-… #Raxis #SecureCode #DataProtection

🚿 CWE-400: Uncontrolled Resource Consumption is like turning all the faucets on in your house at once – eventually, the water will run out!💧 Get trained to manage resources and protect your systems: ow.ly/M4Oi50VuFox #CWE #securecode #appsec #securityalert

If you could wave a magic wand, and "solve" 3 security problems, what would they be? And why? #appsec #securecode #cybersecurity

The very first #DevoxxGreece2023 conference is coming! Join us & Stella Varvarigou on Thur,4/5 to talk about #SASTtools in creating #securecode. Learn more: devoxx.gr/talk/?id=4622 #code4thought #techindustry #technews #softwaresecurity

Do you have a bias towards or against certain AppSec tools? If so, why? And which ones? I want us to try to learn from each other. #appsec #securecode #cybersecurity

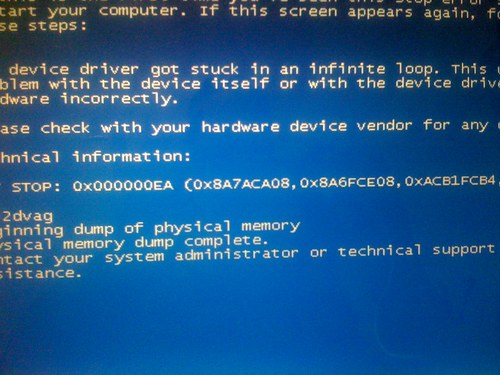
Something went wrong.
Something went wrong.
United States Trends
- 1. Auburn 38.2K posts
- 2. Duke 30K posts
- 3. Bama 28.1K posts
- 4. #SurvivorSeries 176K posts
- 5. Miami 118K posts
- 6. Stockton 16.2K posts
- 7. Virginia 47.7K posts
- 8. Ole Miss 34.8K posts
- 9. Cam Coleman 1,738 posts
- 10. Lane Kiffin 43.9K posts
- 11. Austin Theory 4,387 posts
- 12. Iron Bowl 15.6K posts
- 13. ACC Championship 7,602 posts
- 14. #RollTide 5,935 posts
- 15. Notre Dame 23.9K posts
- 16. Ty Simpson 3,822 posts
- 17. Cooper Flagg 6,030 posts
- 18. Ryan Williams 1,709 posts
- 19. Stanford 8,666 posts
- 20. Seth 21K posts