#appsec search results
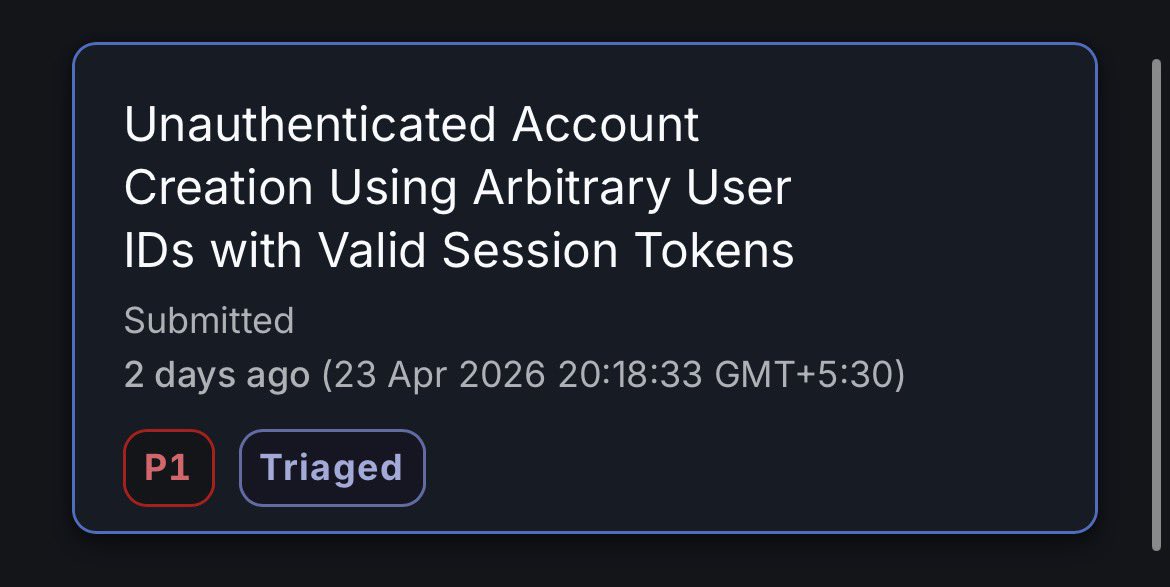
I had published a new Writeup about my recent Critical Vulnerability Report on a Private Bug Bounty Program at Hackerone. Enjoy reading:- wadgamaraldeen.medium.com/critical-zero-… #CyberSecurtiy #BugBountyTips #AppSec #AccountTakeover

Found that just using a user ID could generate a valid session token, leading to account creation without proper authentication. Simple but high impact → triaged as P1. Good reminder: auth & session logic needs deep testing 🔍 #BugBounty #CyberSecurity #AppSec #AuthBypass #P1
H1-TopReports: 1000+ Real HackerOne Exploits Across XSS IDOR SSRF RCE ATO & More 💀📊 Top paid + most upvoted reports broken down by bug type & real targets Study actual attack paths, not outdated theory github.com/reddelexc/hack… #BugBounty #HackerOne #AppSec #CyberSecurity
Software engineers outnumber security engineers 100 to 1. Shan Kulkarni built Nullify to close that gap with AI. New episode of Breaking Into Cybersecurity is live now. 🎧 youtu.be/sXEnjlqf8L0 #AppSec #CybersecurityCareers

youtube.com
YouTube
Breaking Into Cybersecurity
Most tools measure what happens before a breach. Almost none measure what happens during it. Start from runtime. Not as a phase. As the source of truth. #AppSec #CyberSecurity #Aptori
Most breaches are preventable. Most teams find out too late. Vulnerability Assessment = clarity before crisis ✔️ Find real risks ✔️ Cut the noise ✔️ Fix what matters Start: redsecuretech.co.uk/service/vulner… #CyberSecurity #VulnerabilityAssessment #AppSec #CyberThreats #InfoSec

Is your LLM app safe? Aegis AI's open-source 'Guardian' firewall offers real-time threat detection, acting as a vital shield against malicious inputs. Learn how it strengthens AI application security. #AI #LLMFirewall #AppSec aibreakingwire.com/news/security-…
Today's update I continued my learning on IDOR and Access control Vulnerabilities, I took some labs on it. I also learnt about Broken access control resulting from platform misconfigurations and URL matching discrepancies. #CyberSecurity #AppSec #portswigger #IDOR



🔐 100 Cybersecurity Terms You MUST Know – #81, #82, #83 🚨 #81 Digital Certificate: Verifies identity online. #82 TLS/SSL: Encrypts data in transit. #83 Secure Coding: Writing code resistant to attacks. 💡 Developers are defenders. #WebSecurity #AppSec #KGTalks

Veracode CISO Sohail Iqbal: more security metrics don’t always mean more security. If you’re measuring activity instead of risk, you may be getting the wrong signal. Read his thoughts in this TechRadar Pro article. #Cybersecurity #AppSec sprou.tt/1jZvV63jTmW
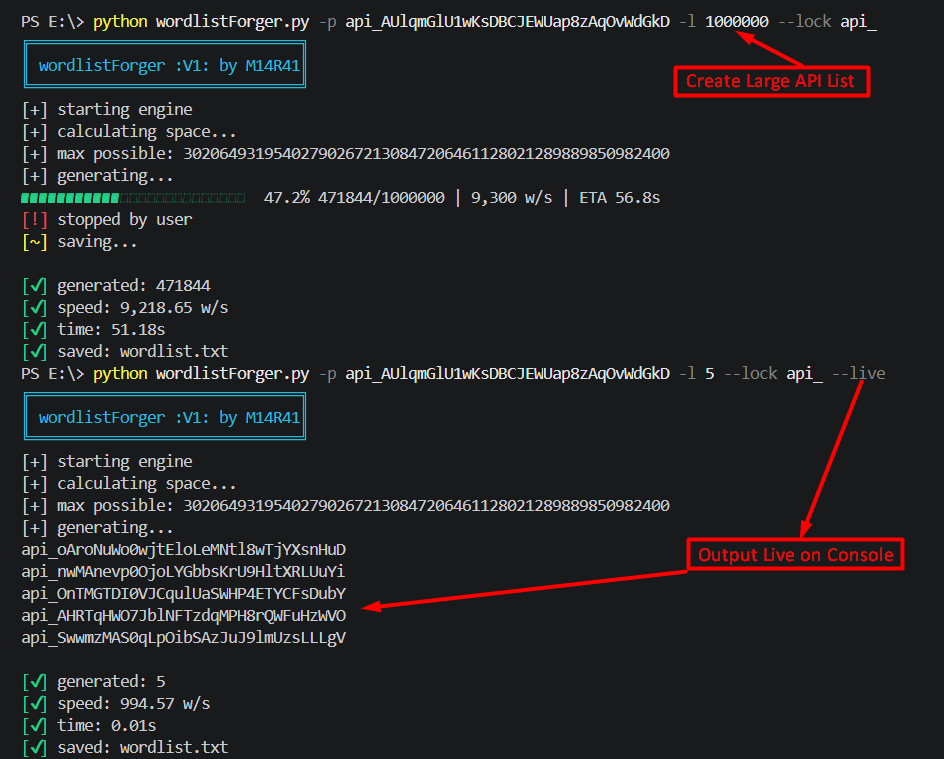
Simplify generating realistic, structured identifiers (API keys, UUIDs, tokens, order/transaction IDs, invoices, coupon codes) for brute-force and IDOR testing github.com/m14r41/Wordlis… #Pentesting #CyberSecurity #AppSec #BugBounty #EthicalHacking #IDOR #BruteForce #InfoSec
🟠 Developer & AppSec Alert: ASP.NET Core CVE-2026-40372 can impact auth integrity in affected DataProtection setups. Upgrade to 10.0.7+ and rotate key rings where exposed. devblogs.microsoft.com/dotnet/dotnet-… #AppSec #DotNet #IdentitySecurity
From Panic to Playbook >> Modernizing #ZeroDay Response in #AppSec buff.ly/03vvrhx @SecurityBlvd @Mend_io #cybersecurity #cyberthreats #cyberattacks #databreaches #cybercrime #leadership #management #business #CISO #CIO #CTO #threatintelligence #vulnerabilitymanagement

70% of security debt lives in third‑party code. In 2026, Agentic AppSec automates fixes, letting devs ship secure faster. 🚀 What’s your top tip for managing OSS risk? Reply below #AppSec #SecureCode

26 fake crypto wallets on the Apple App Store — all harvesting seed phrases. The 'walled garden' let thieves in. Your coins, gone. Only #Bitcoin has cold storage culture. #CyberSecurity #AppSec thehackernews.com/2026/04/26-fak…

“Learn everything you can. Get hands-on. Embrace your humanness.” In our latest episode, Caroline Wong shares a simple but powerful takeaway for the AI era. Listen here: youtu.be/AcJQSkN7si4 #CyberSecurity #AppSec #AI #AppSecPodcast
🚫 Web Malware Scan Results Website: salzburgcapital.app Security Verdict: CONFIRMED SCAM Full analysis & details: scanmalware.com/scan/ca01ee89-… #AppSec #WebAnalysis #ISO27001
📢 Announcing DevSec Station, my new podcast! 💜 If you write code, this is for you. Short, practical #AppSec lessons. No scare tactics. Very little homework. 😉 twp.ai/kuwhZt twp.ai/gEHSNp

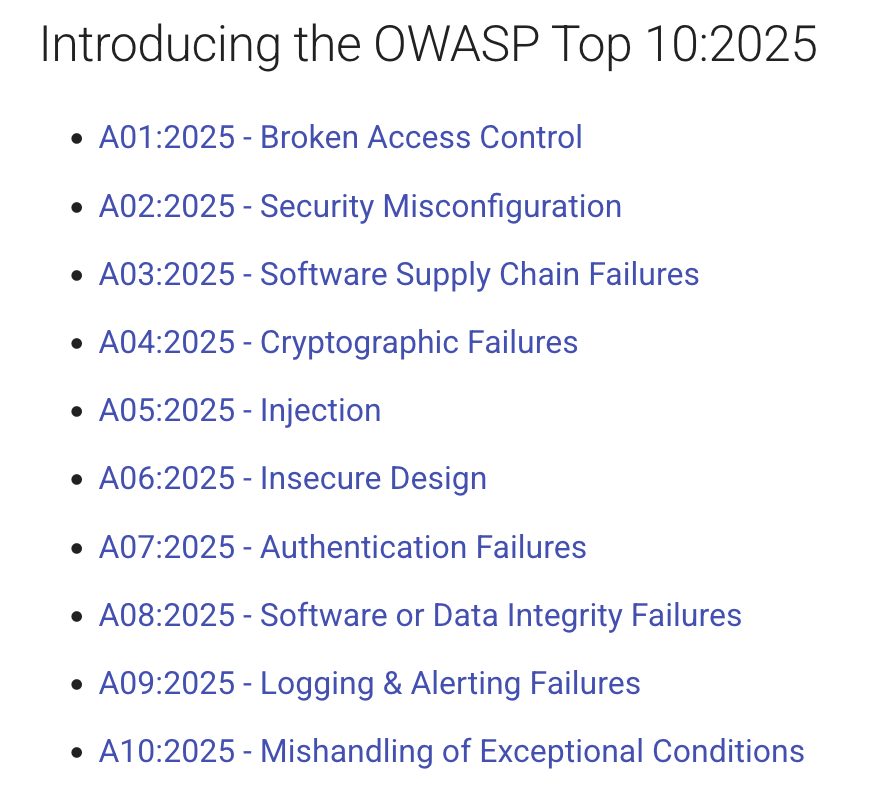
Big news in #AppSec: the #OWASP Top 10 2025 is now available! I'm part of the project team and ALL OF US want every dev, security engineer, and leader to read it (please). twp.ai/WqtQLE 1/5
Software Supply Chain: Bigger (and Scarier) Than We Realize - a blog post by meeeeeee! When we talk about the software supply chain security, most people think only of dependencies (open-source libraries and frameworks). twp.ai/ImsMez #appsec #supplychain 1/2

Let's talk about security risks from AI, and what to do about them! twp.ai/E5Abrj Get my free secure coding prompt library here: SecureMyVibe.ca #ai #aisecurity #appsec
Most #AppSec teams say they fix critical bugs. Data shows otherwise. In @Semgrep's report, Braden Riggs finds top teams fix 63% of critical issues, while most fix just 13%. Same tools and alerts—the gap is execution, not detection. 🔗 What 50k repos reveal about real

My talk, 'Threat Modeling Developer Behaviour: The Psychology of Bad Code', from OWASP Global AppSec is finally out! Please watch, share, like, and listen! I would love to hear your feedback. 💜 #OWASP #appsec #globalappsec
🔎 Spot the Bug #11 Can you find the security flaw and explain how it could be abused? #SpotTheBug #BugBounty #AppSec

Just cleared Dojo #50 Thanks to @YesWeHack for the challenge #CTF #AppSec
Bucket Vault just dropped on Dojo! 🔐 Files are protected using pre-signed URLs and signatures. Your mission is to figure out how to bypass those protections and access what’s hidden inside. Think you’ve got what it takes? Prove it: dojo-yeswehack.com/challenge-of-t… #BugBounty #CTF

Mobile apps handle your data, money, and identity. 📱🔐 Learn more about eMAPT 👉 bit.ly/4qU1xab Master Android and iOS testing, from static and dynamic analysis to API security and threat modeling from an attacker perspective. #eMAPT #MobileSecurity #AppSec

Real attackers. Real results. In just a few clicks, see how your apps stand up to real-world attackers and get a clear path forward. Learn if your team qualifies for a free Lightspeed pre-flight: bit.ly/49WNjPy #AppSec #OffensiveSecurity #Cybersecurity

Last chance: 50% off the eWPT Certification + Training Bundle ⏳ Redeem 👉 bit.ly/3MJ1sYC Code: BUNDLE50DEC25 Get the eWPT exam + 3 months Premium training with hands-on labs & real AppSec/pentesting workflows. #eWPT #WebSecurity #AppSec

Let's take the #security conversation beyond the booth. We’re thrilled to join @Optiv for their exclusive @OneRSAC after party on Tuesday, March 24th! 🥂 Join us for an evening of networking with industry leaders as we discuss the future of #AppSec for the AI software supply

Don’t let your vendor’s corporate distractions become your #security breach. 🛡️ When #AppSec providers focus on mergers and buyouts, innovation takes a backseat, leaving your #SoftwareSupplyChain exposed. You need a partner that’s invested in your defense, not just their next

🚀 Innovation goes beyond the Moscone Center: Meet JFrog and @Optiv at the @OneRSAC after party tonight! Network with leading security professionals while enjoying arcade games, drinks, and a live-band. Register today: jfrog.co/RSA26AP #AppSec #AISupplyChain #RSAC

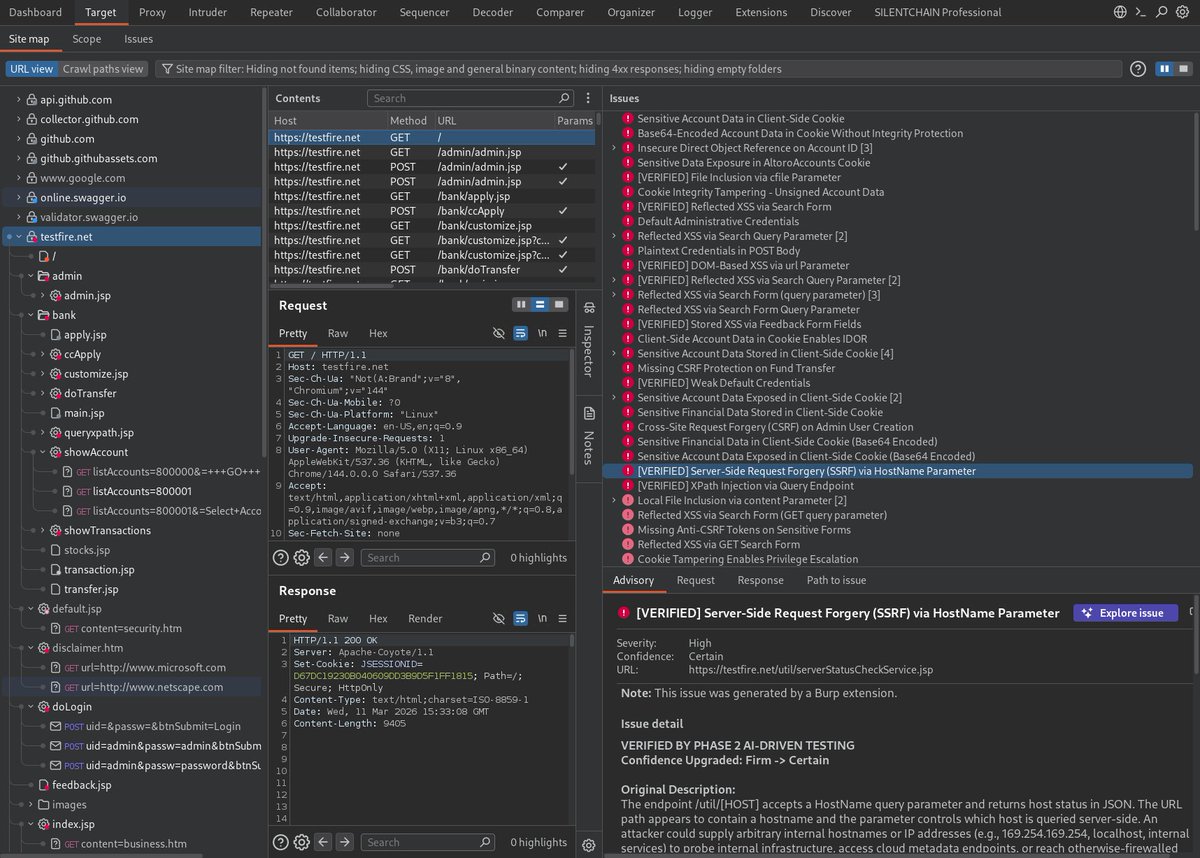
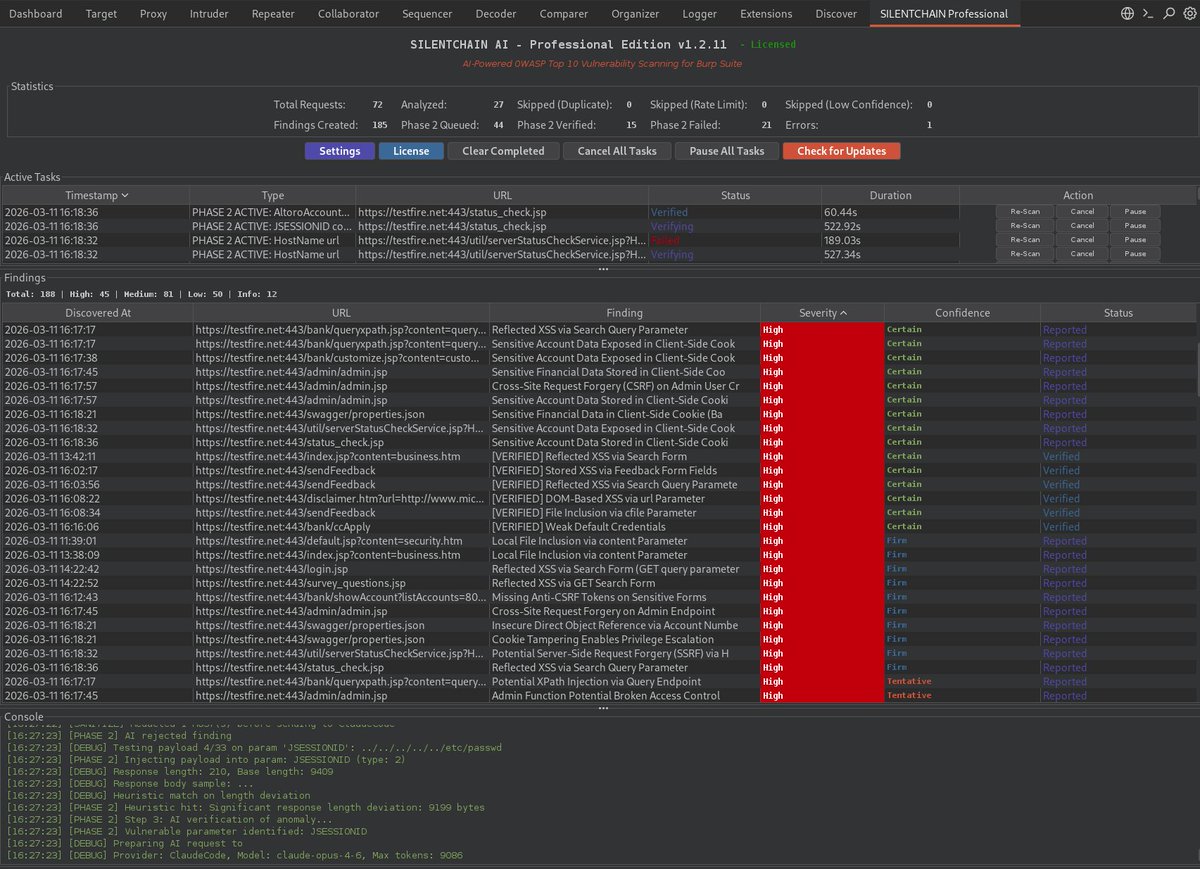
🔎 SILENTCHAIN Pro v1.2.11 in action Target: testfire.net 188 findings discovered → 43 High → 83 Medium → 50 Low 22 vulnerabilities verified ⏱ 2h07m scan 🤖 65 AI requests (Claude Opus 4.6 via ClaudeCode) AI-driven OWASP testing at scale. #appsec #bugbounty #AI
How AI agents are turning security inside-out - helpnetsecurity.com/2026/01/09/ai-… - @NokodSecurity #AppSec #AIAgents #Cybersecurity #CybersecurityNews

BurpSuite → SILENTCHAIN + Claude Opus 4.6 = next-level OWASP #AI testing automation. Try our Community Edition FREE on GitHub or join the waiting list at silentchain.ai today 👍 #bugbounty #appsec #infosec #pentesting #cybersecurity #OWASP
Mobile apps handle your data, money, and identity. 📱🔐 Learn more about eMAPT 👉 bit.ly/4tVHLOt Master Android and iOS testing, from static and dynamic analysis to API security and threat modeling from an attacker perspective. #eMAPT #MobileSecurity #AppSec

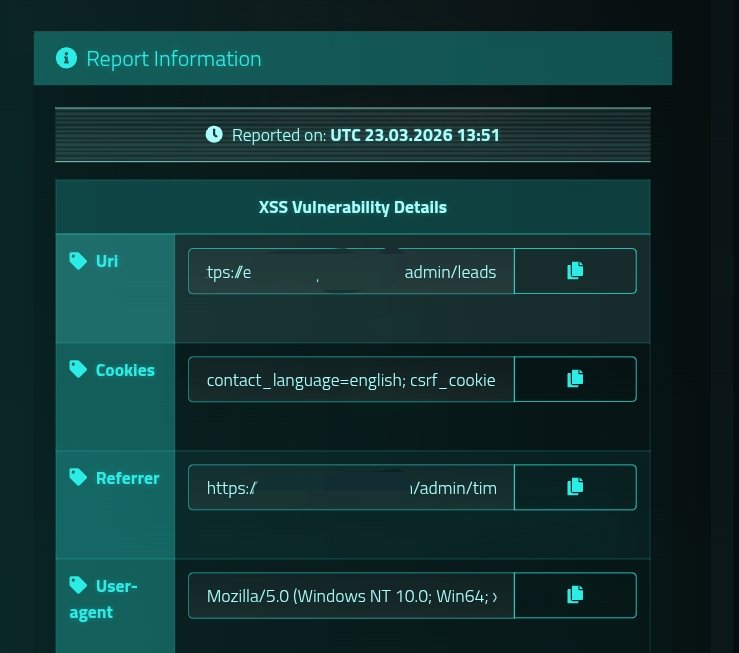
Another Blind XSS trigger in private admin panel. Sadly, the timing was off and the session had already timed out. 🤧 And Yeah Waiting for another callback. 🤞 📝 Vector: Feedback Form #BugBountyTips #AppSec #CyberSecurity #WebSecurity #XSS
Something went wrong.
Something went wrong.
United States Trends
- 1. Cora N/A
- 2. Klay N/A
- 3. Breslow N/A
- 4. Breslow N/A
- 5. UDFA N/A
- 6. #bucciovertimechallenge N/A
- 7. #UFCVegas116 N/A
- 8. White House Correspondents N/A
- 9. WHCD N/A
- 10. Red Sox N/A
- 11. #AEWCollision N/A
- 12. #WeWantKairi N/A
- 13. Chad Tracy N/A
- 14. Varitek N/A
- 15. Jalen Johnson N/A
- 16. Scott Foster N/A
- 17. Diego Pavia N/A
- 18. Achilles N/A
- 19. Donte N/A
- 20. Jack Flaherty N/A